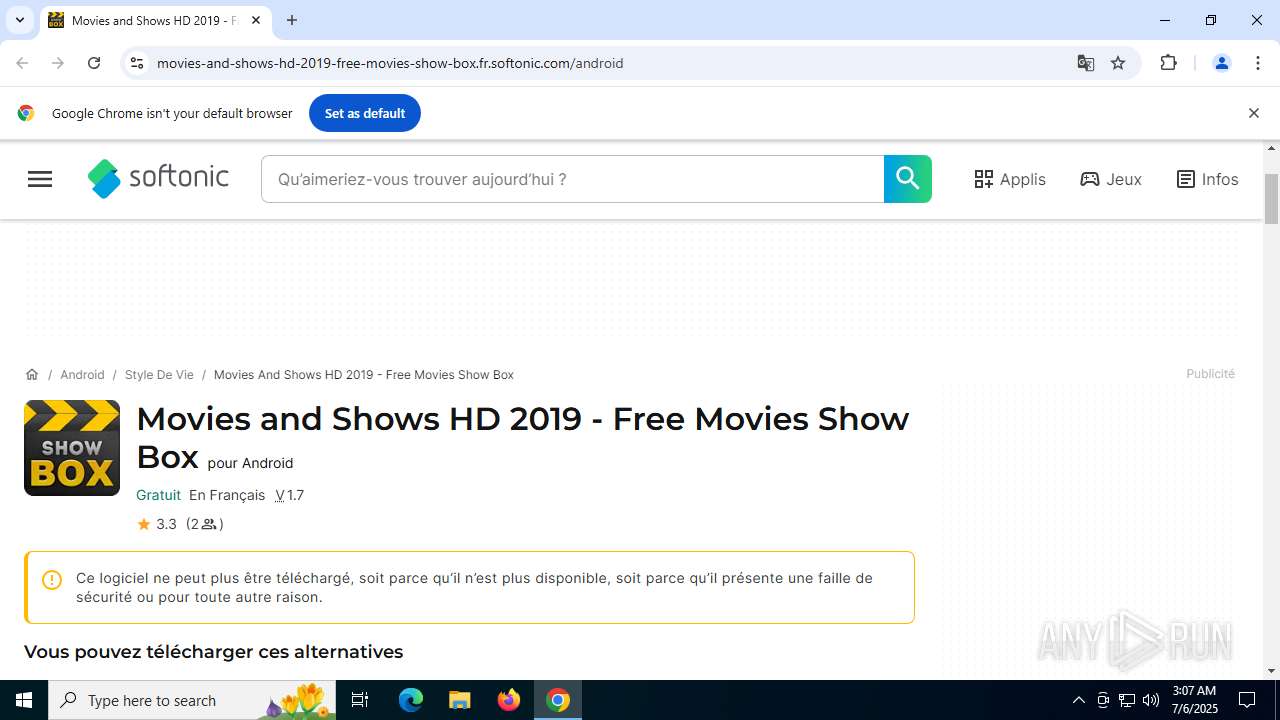
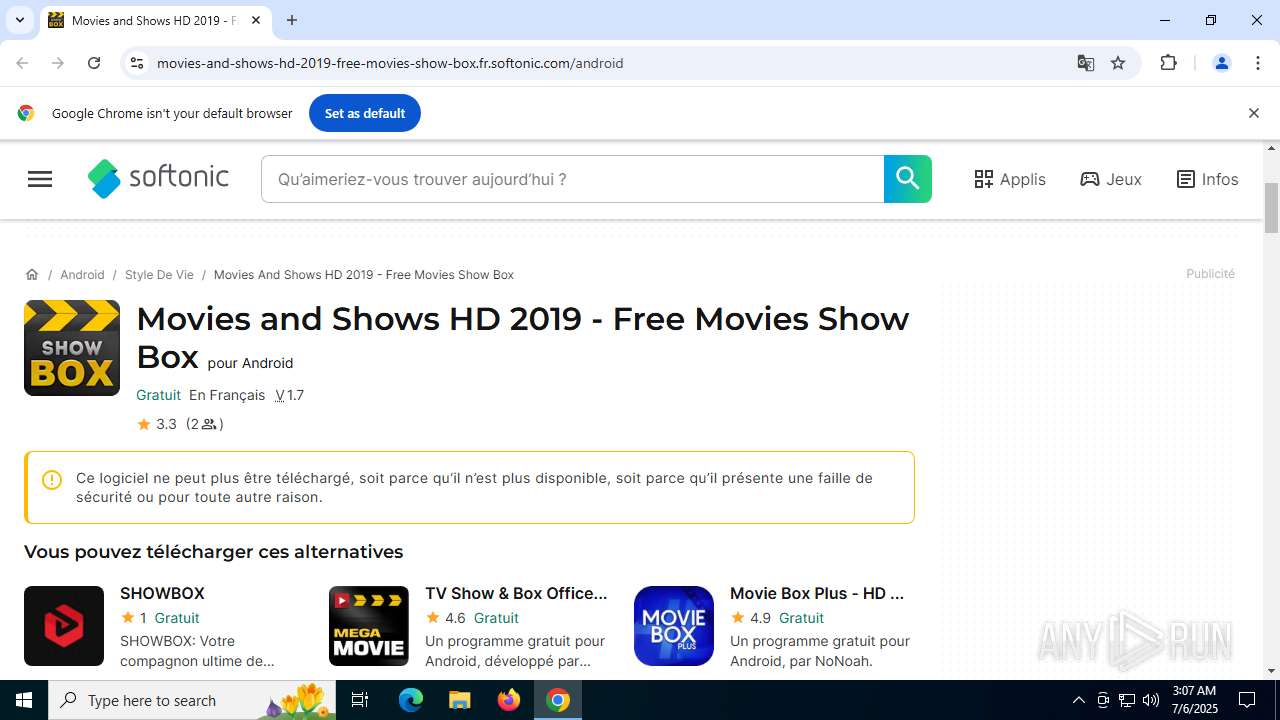
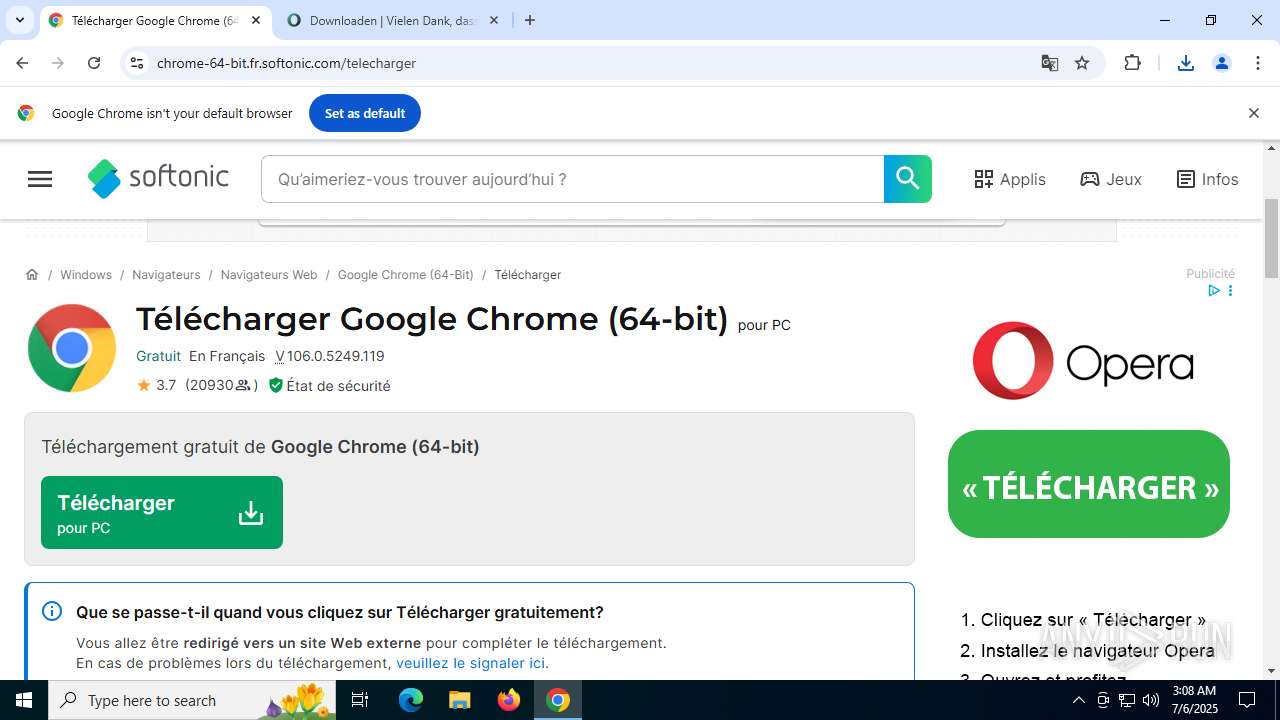
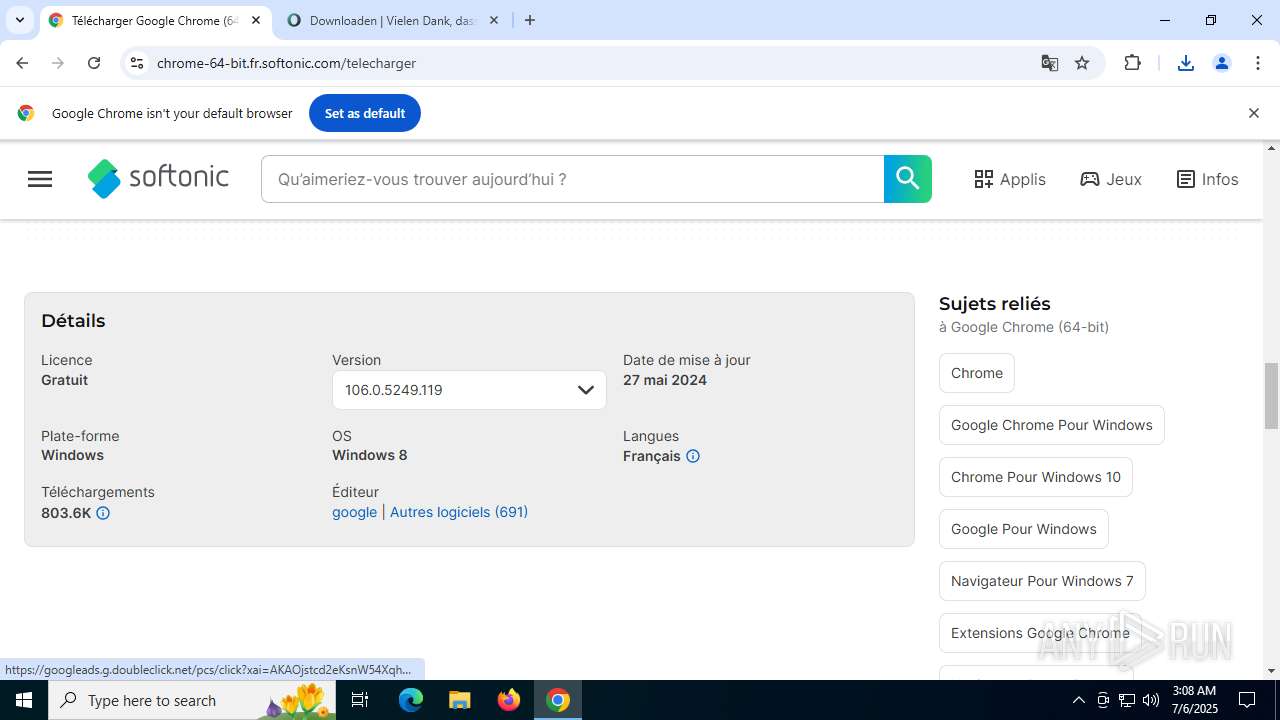
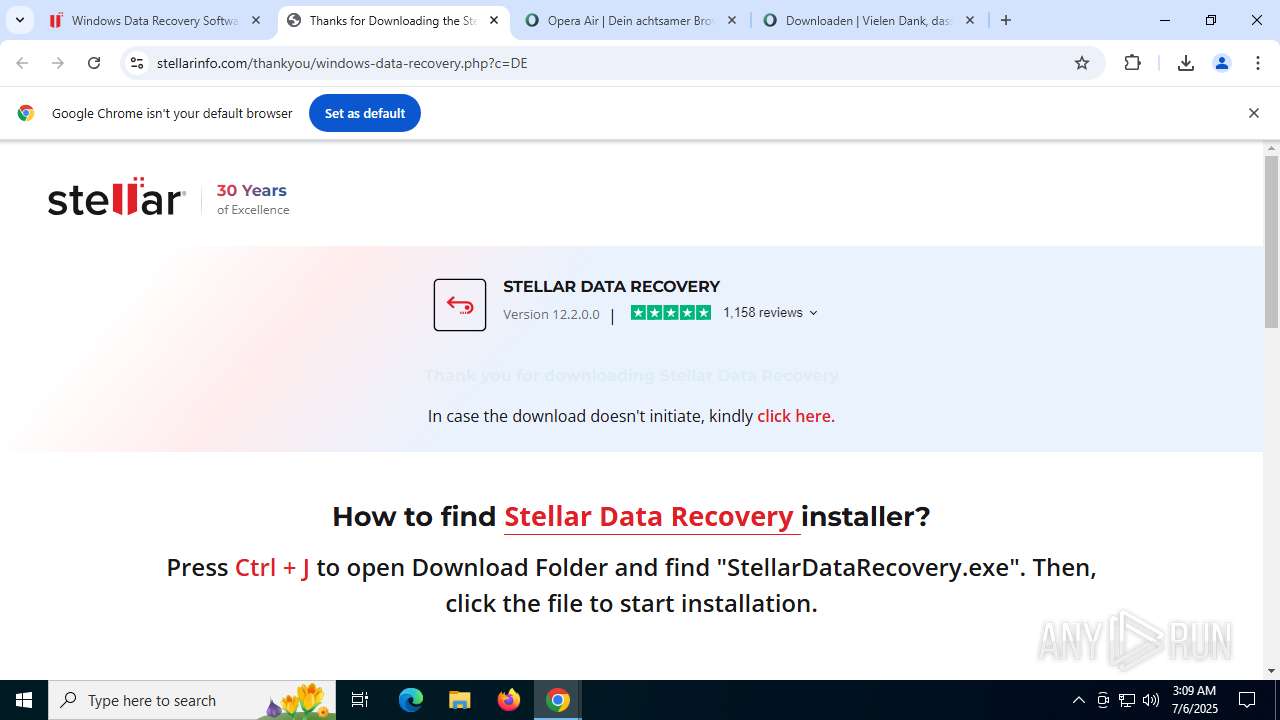
| URL: | movies-and-shows-hd-2019-free-movies-show-box.fr.softonic.com |
| Full analysis: | https://app.any.run/tasks/a5fdecce-75d9-46b7-a84d-a5911c995c34 |
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2025, 03:07:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5A957DEF754A01D425B0D96EC8BB1468 |
| SHA1: | CC81D242F475F3E7892D40544912570C149DDA9A |
| SHA256: | B35D90271386F624C57209C2EFCB6F489535F3031567A663507F8E6DE022DFBD |
| SSDEEP: | 3:3TBaNKSWxXVF8KAzZKSISXpmHLGKI:jBa/WxFWKAzZK7FLGKI |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- K-Lite_Codec_Pack_1766_Standard.tmp (PID: 2732)
SUSPICIOUS
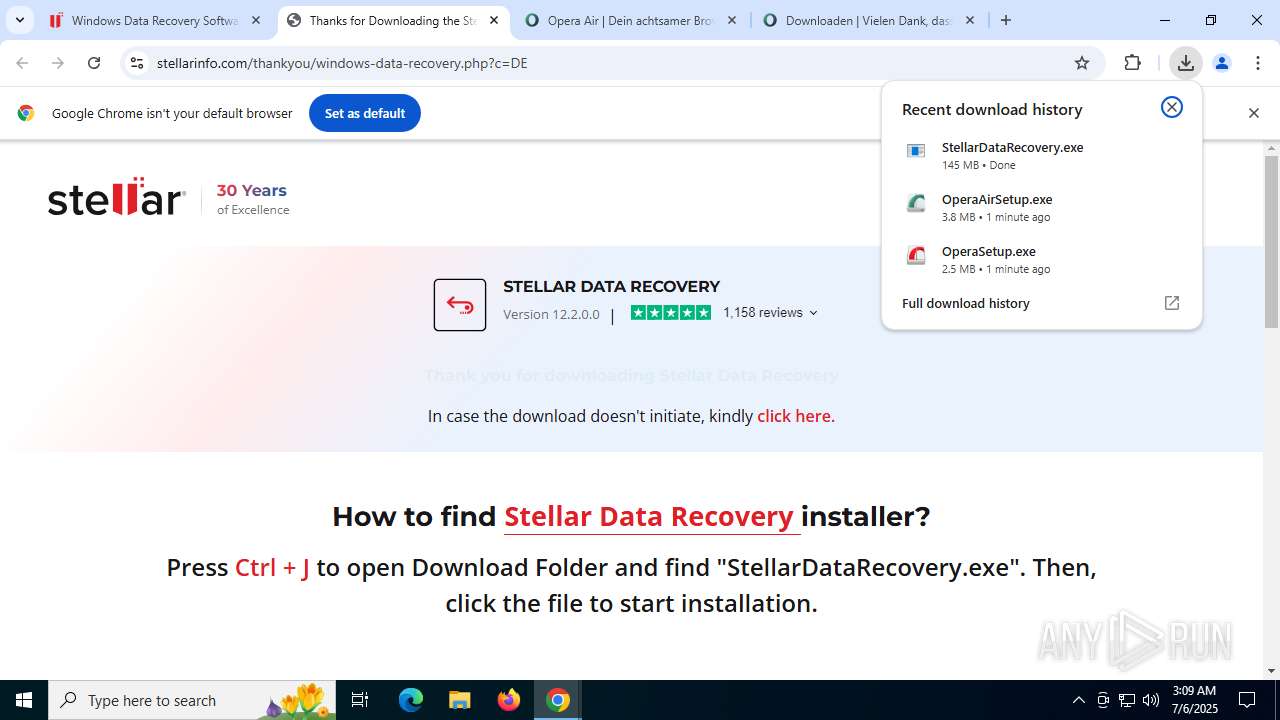
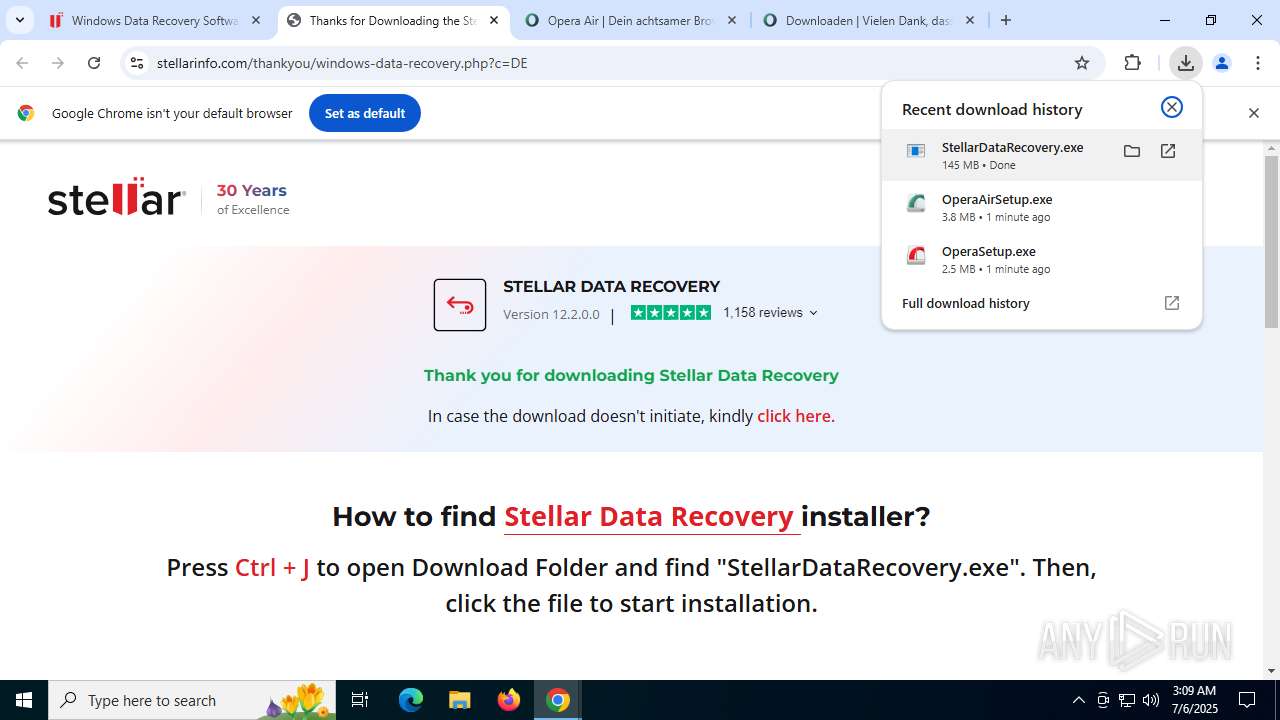
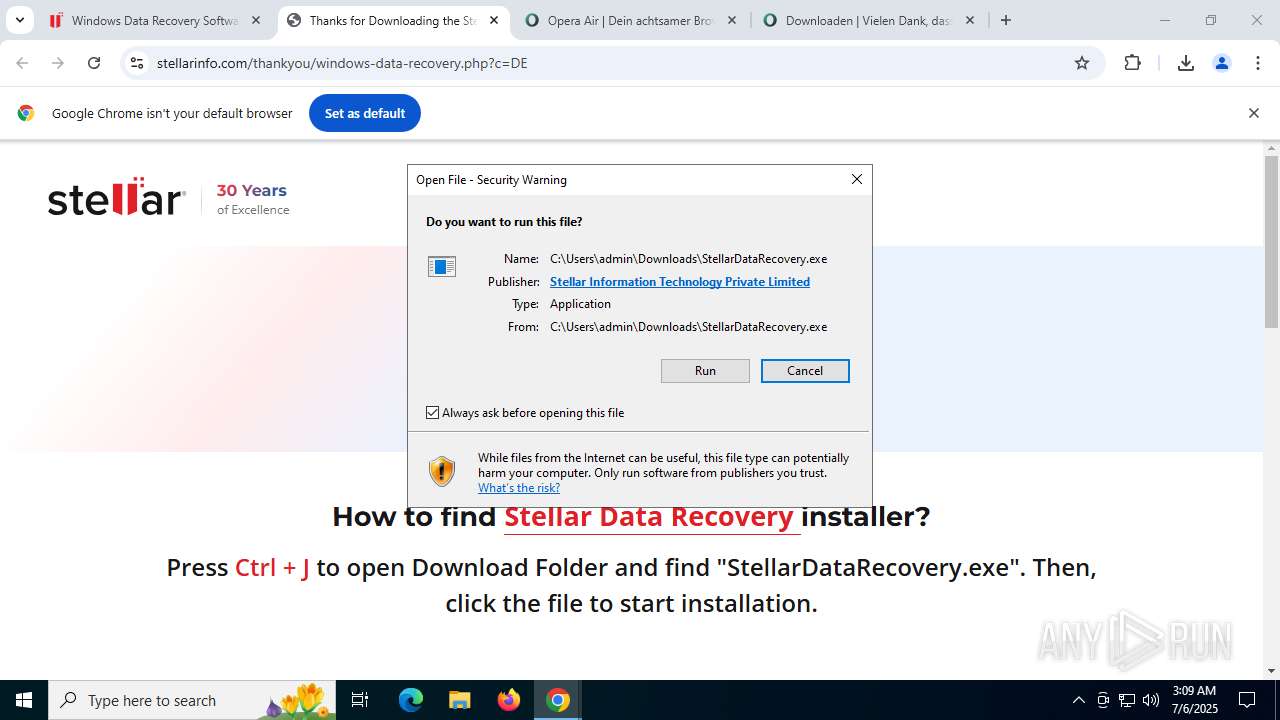
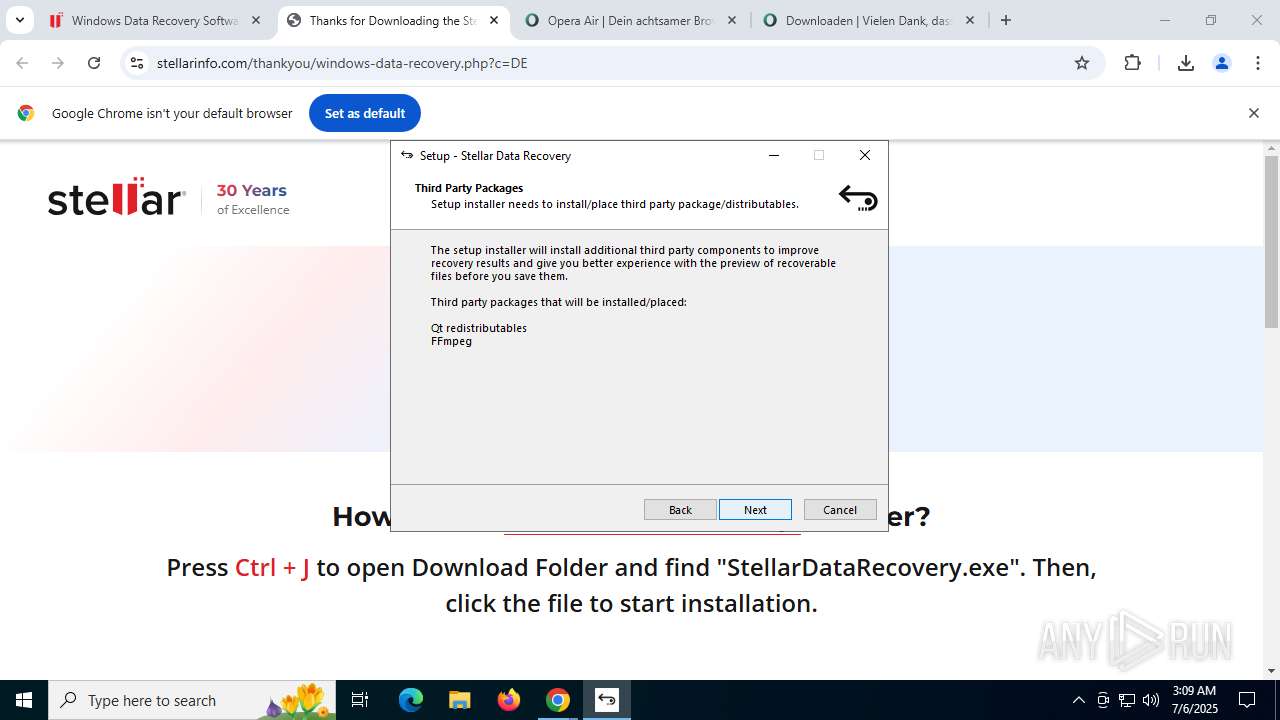
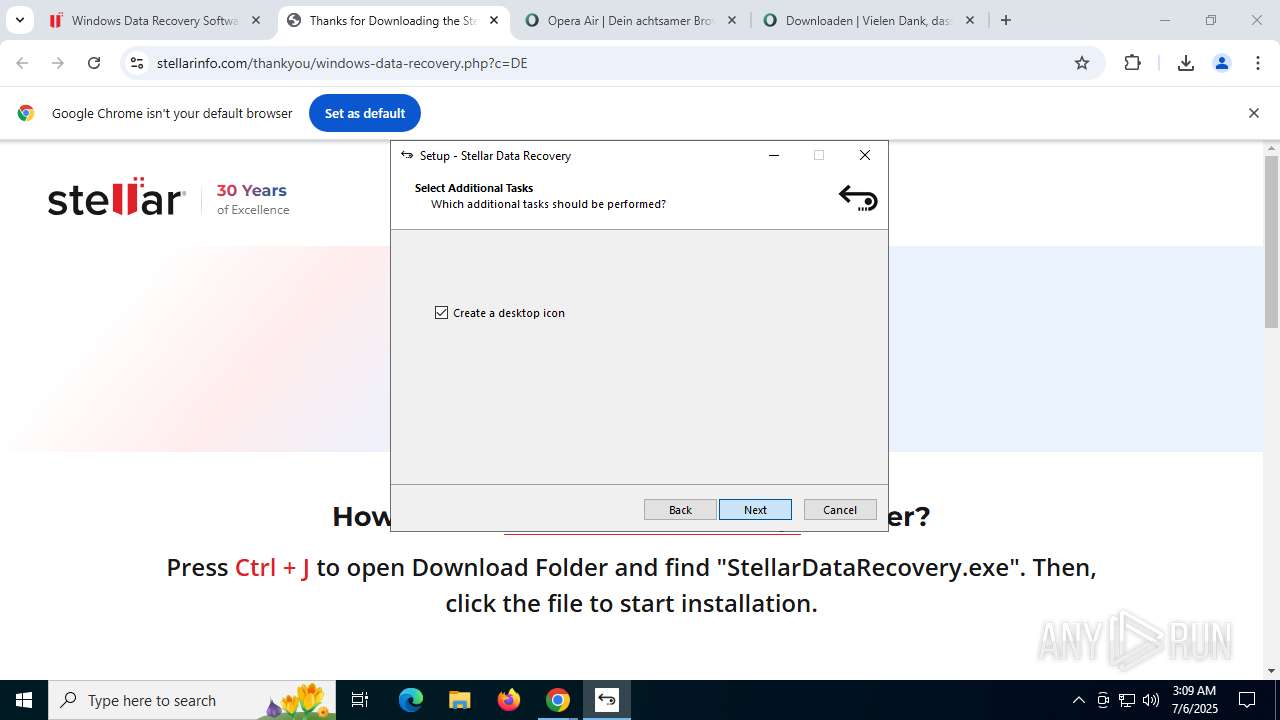
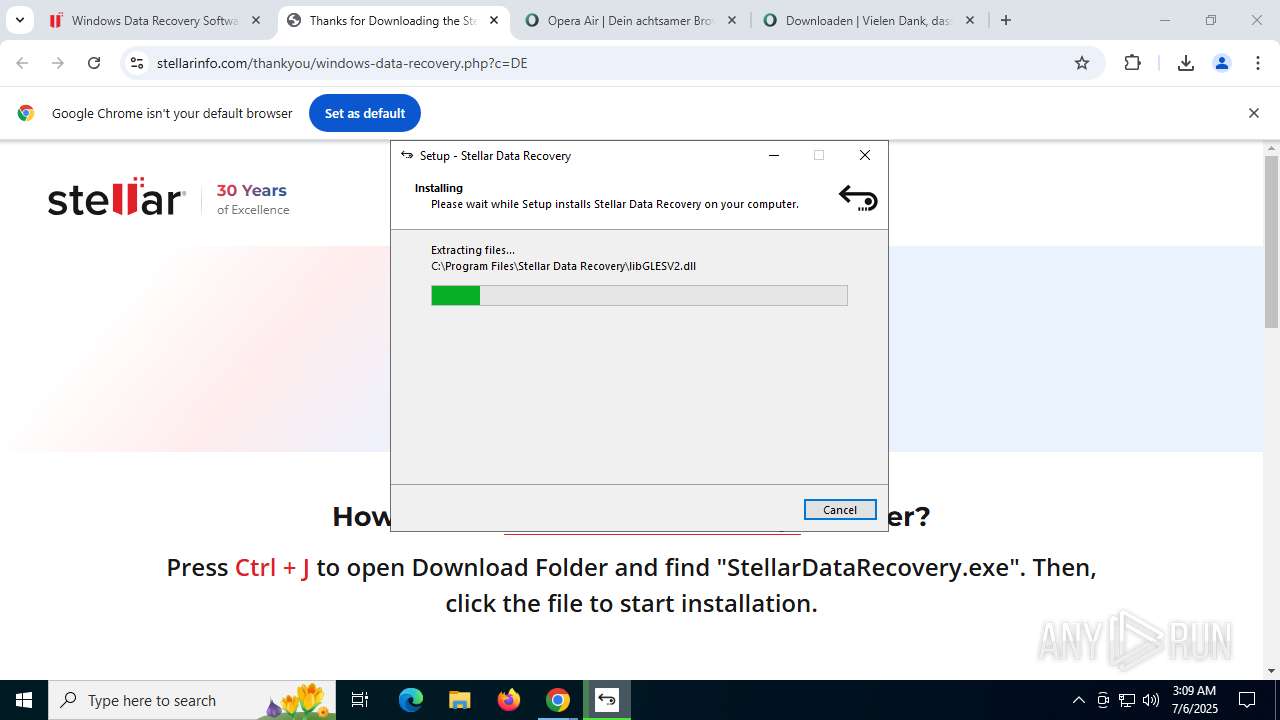
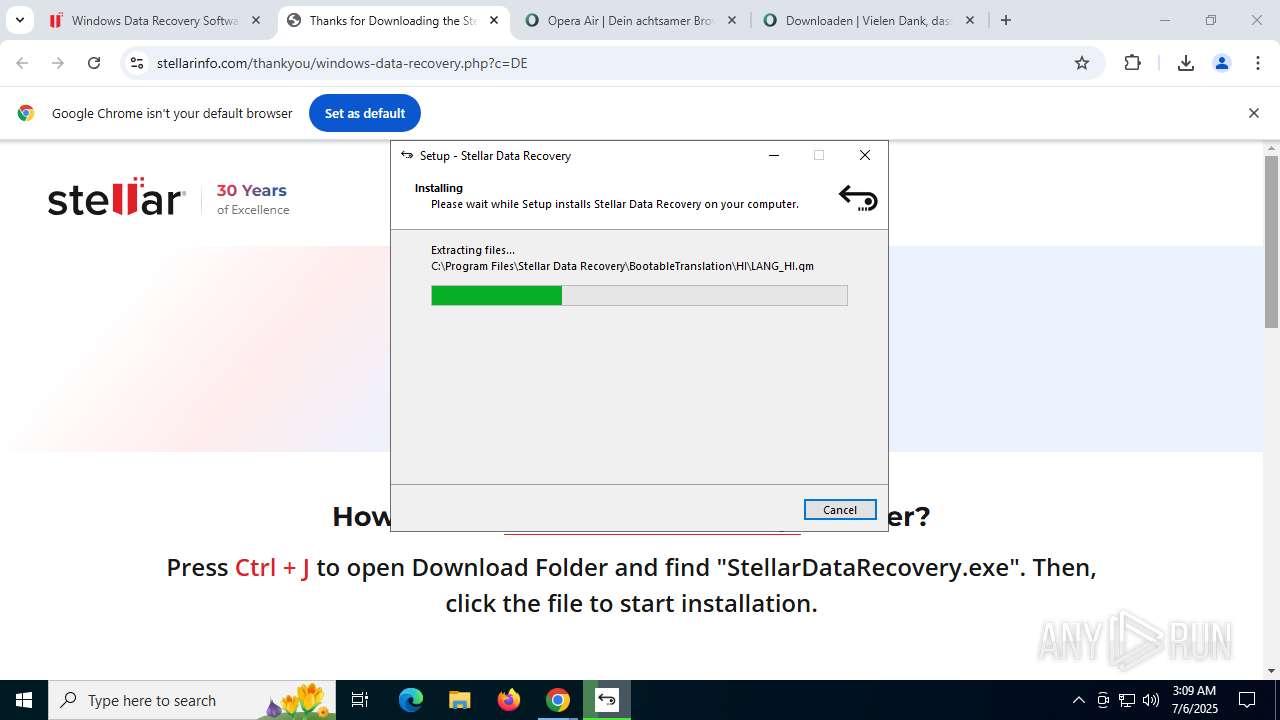
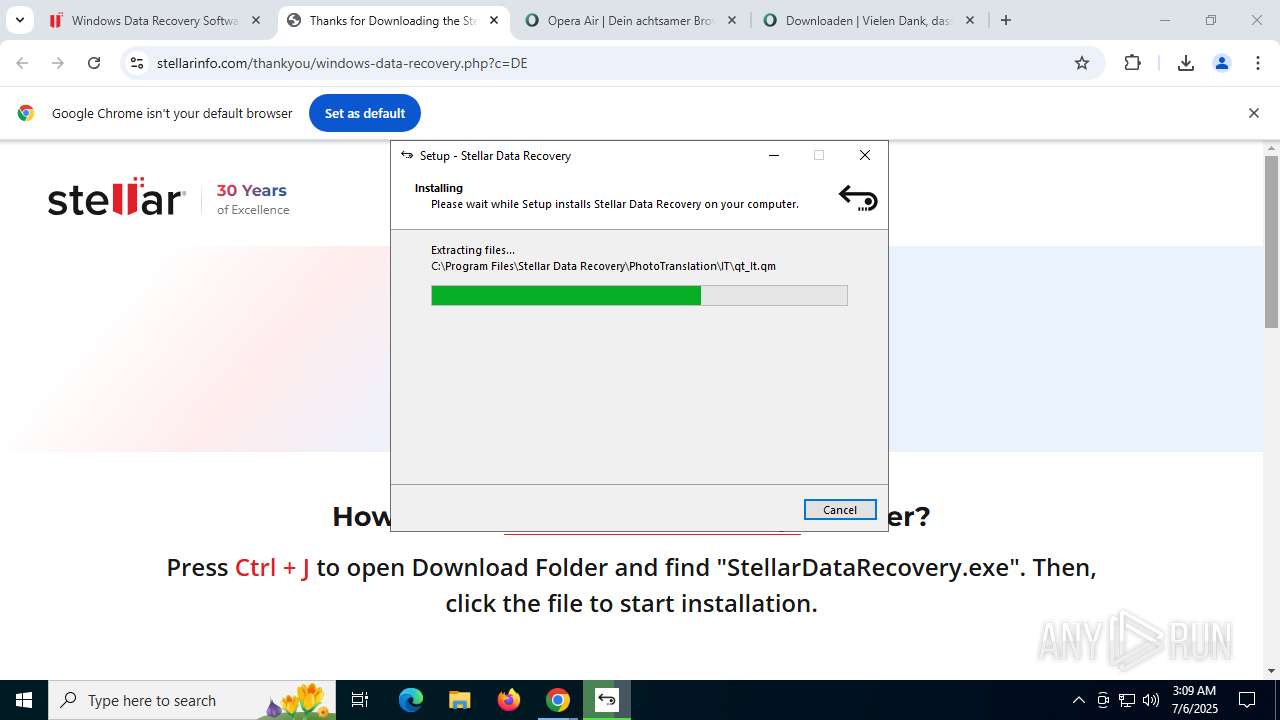
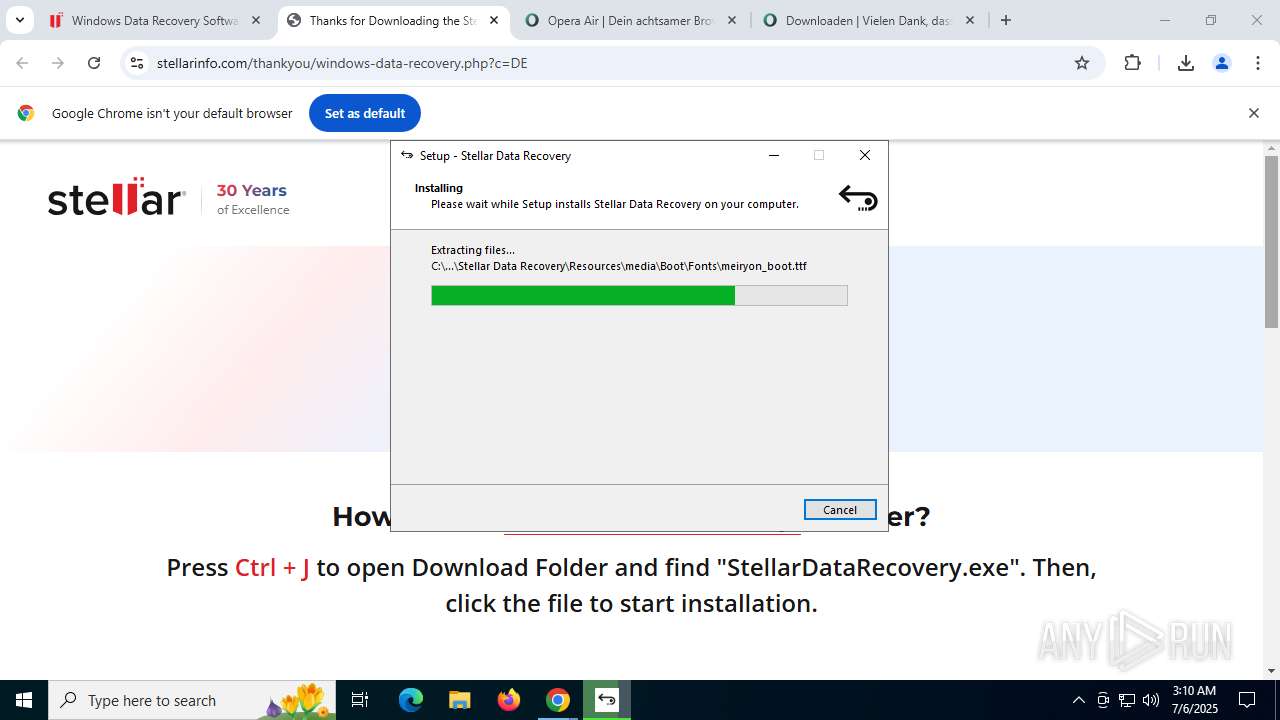
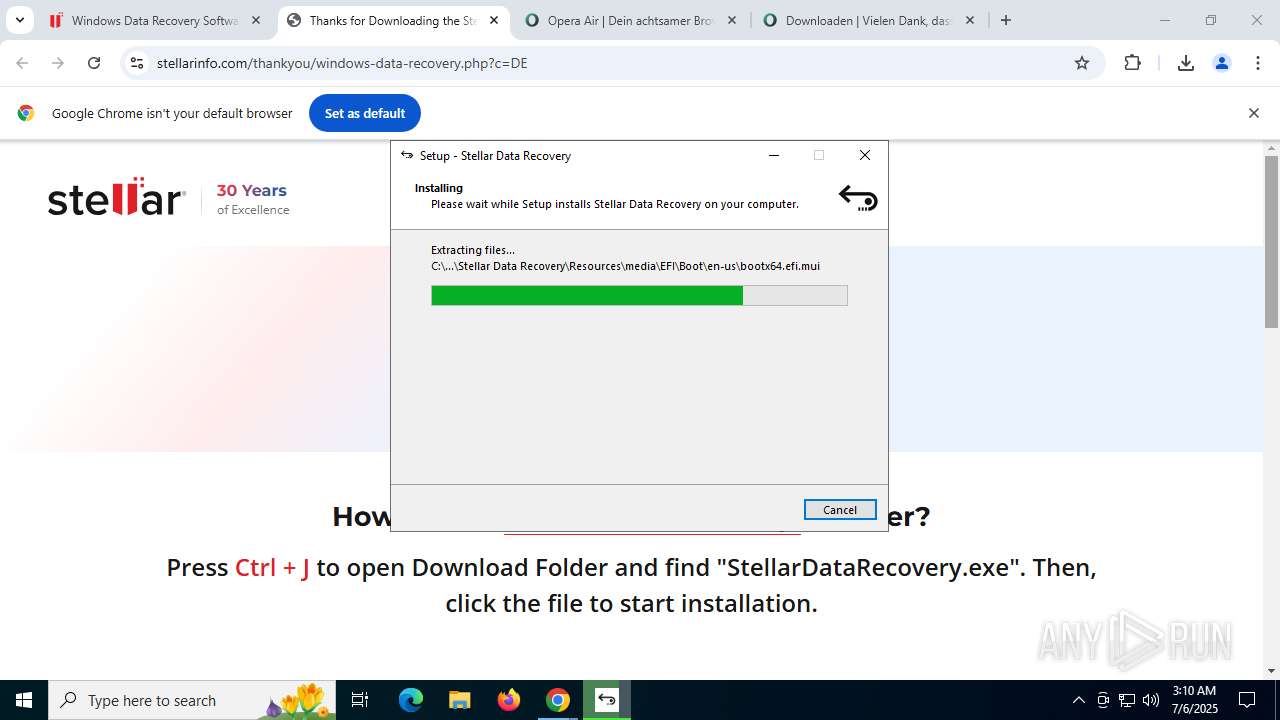
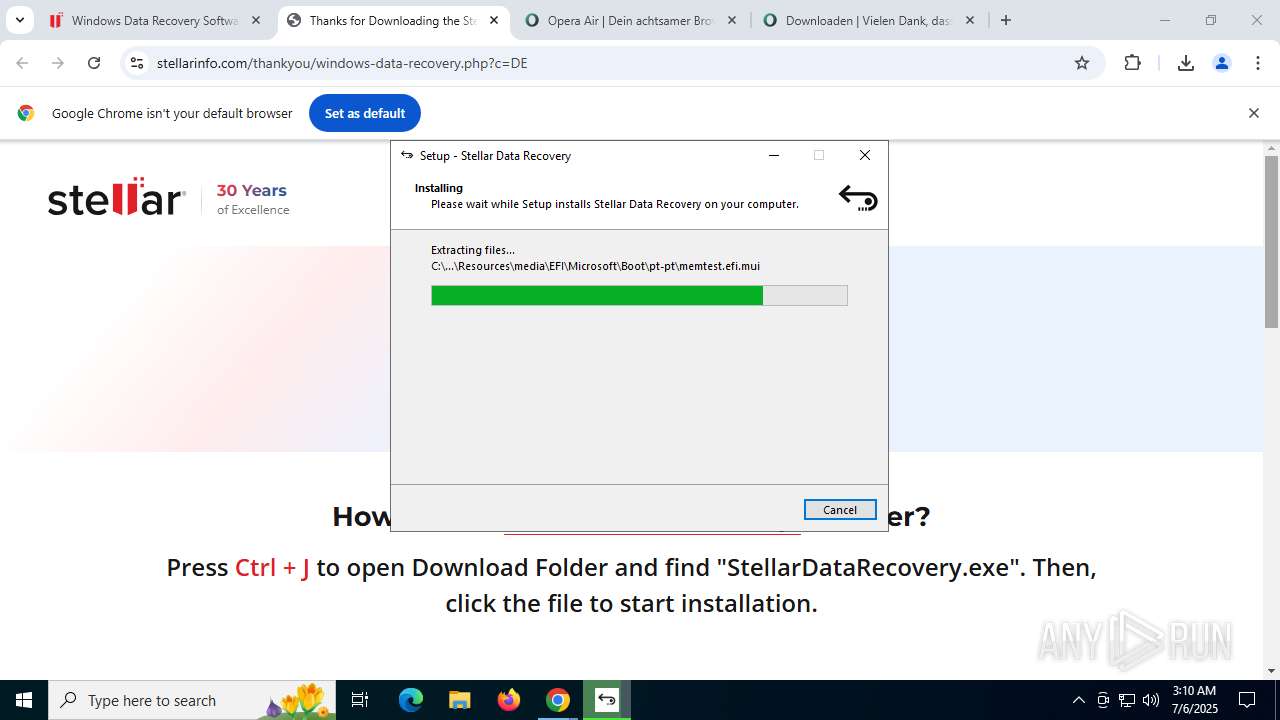
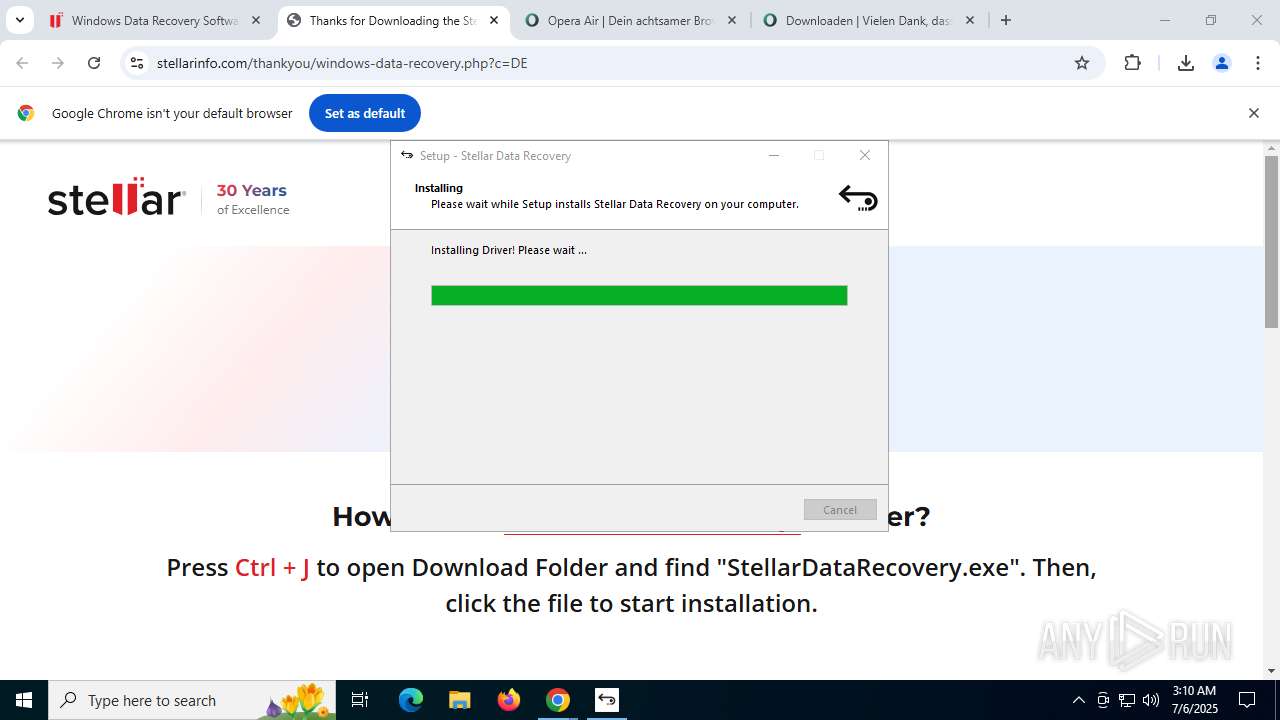
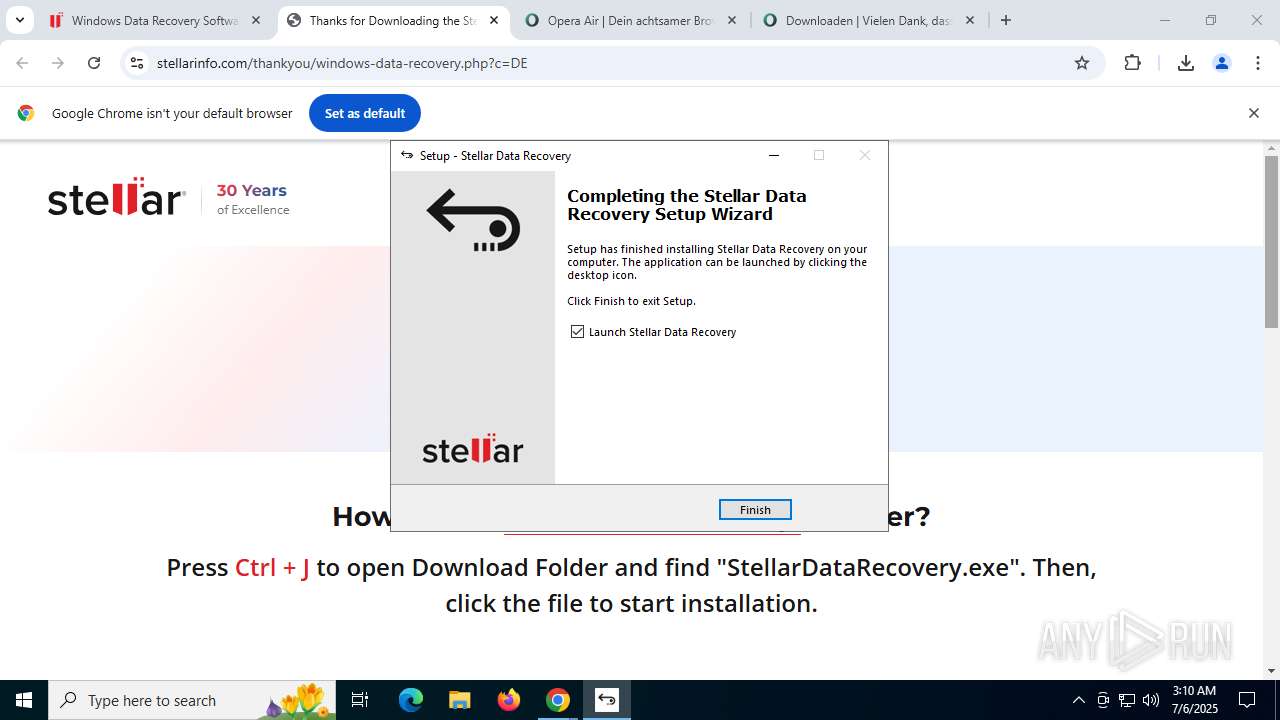
Executable content was dropped or overwritten
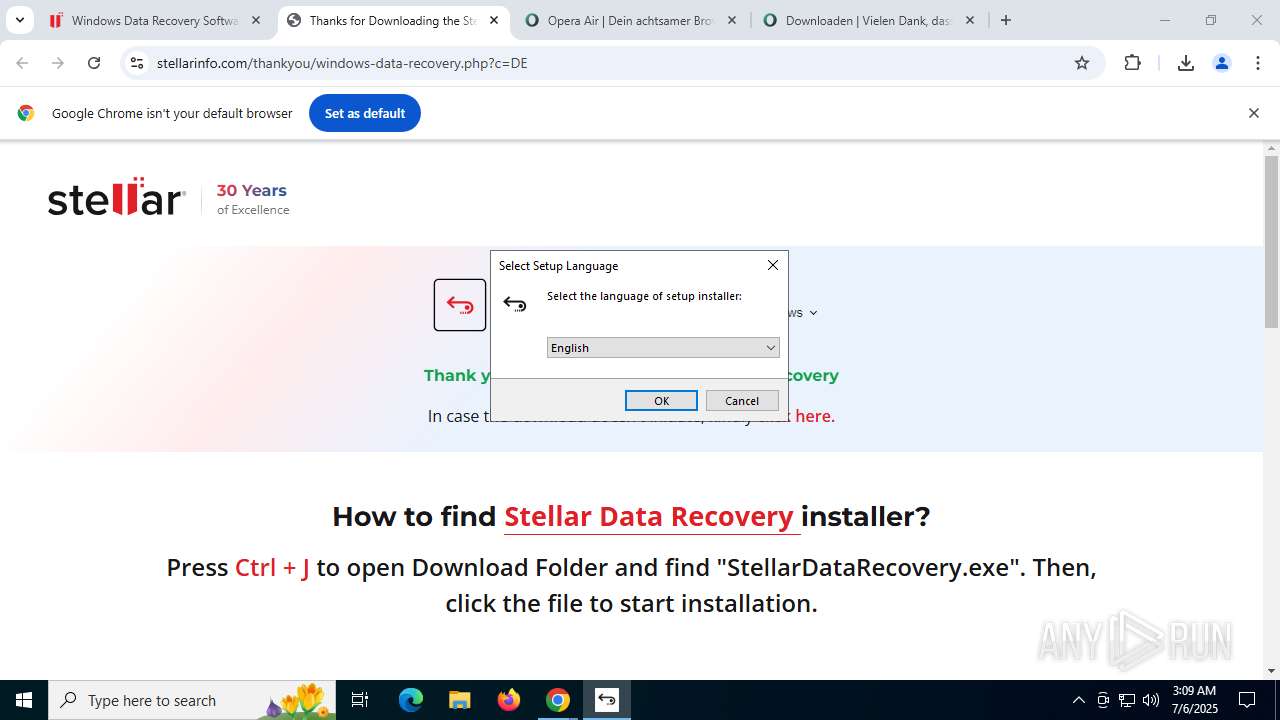
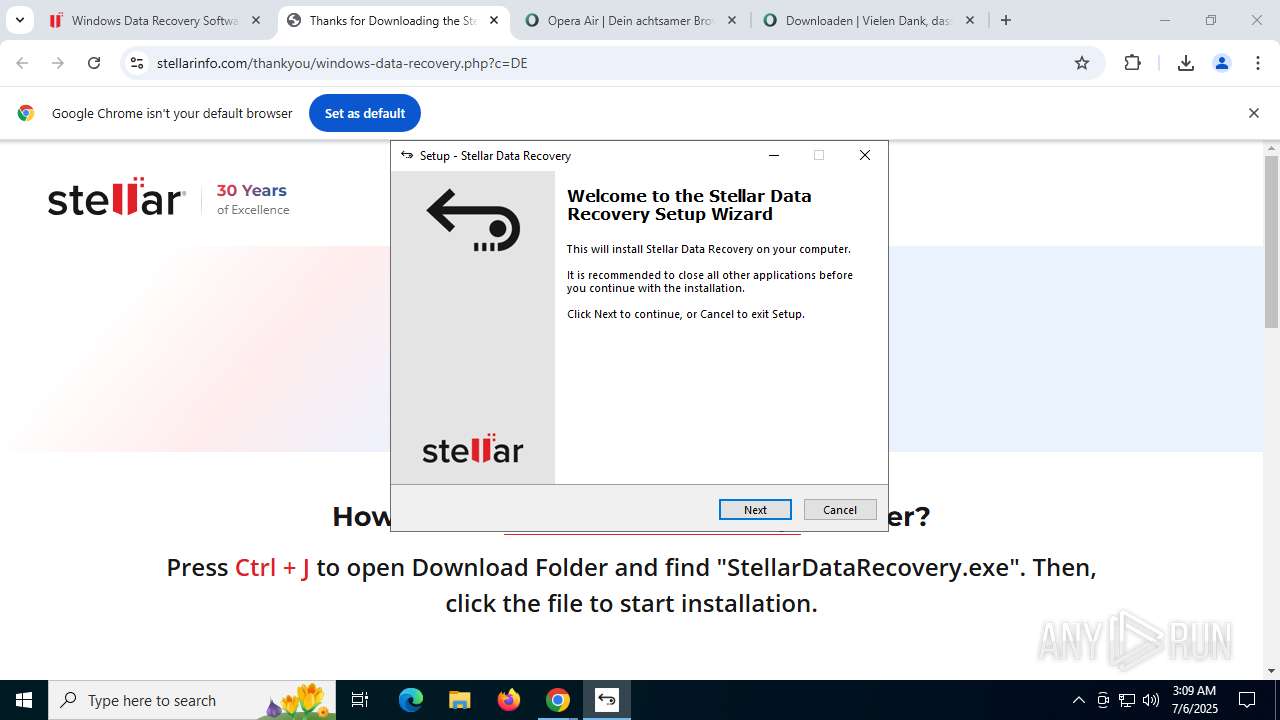
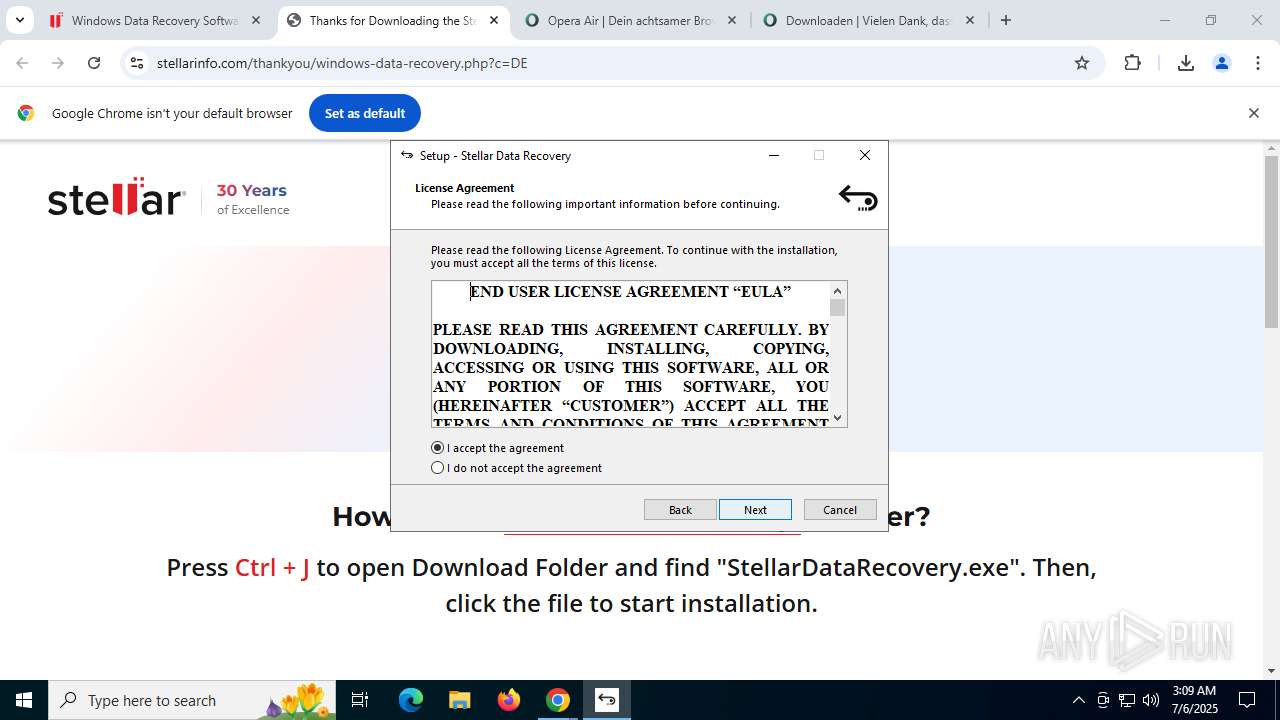
- StellarDataRecovery.exe (PID: 4116)
- StellarDataRecovery.exe (PID: 8096)
- StellarDataRecovery.tmp (PID: 7852)
- K-Lite_Codec_Pack_1766_Standard.exe (PID: 7960)
- K-Lite_Codec_Pack_1766_Standard.tmp (PID: 2732)
Reads security settings of Internet Explorer
- StellarDataRecovery.tmp (PID: 8424)
- StellarDataRecovery.tmp (PID: 7852)
Reads the Windows owner or organization settings
- StellarDataRecovery.tmp (PID: 7852)
- K-Lite_Codec_Pack_1766_Standard.tmp (PID: 2732)
Process drops legitimate windows executable
- StellarDataRecovery.tmp (PID: 7852)
The process drops C-runtime libraries
- StellarDataRecovery.tmp (PID: 7852)
Searches for installed software
- K-Lite_Codec_Pack_1766_Standard.tmp (PID: 2732)
Reads the date of Windows installation
- K-Lite_Codec_Pack_1766_Standard.tmp (PID: 2732)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 7436)
- regsvr32.exe (PID: 2704)
- regsvr32.exe (PID: 8644)
- regsvr32.exe (PID: 9188)
- regsvr32.exe (PID: 8364)
- regsvr32.exe (PID: 9108)
- regsvr32.exe (PID: 8756)
- regsvr32.exe (PID: 5284)
- regsvr32.exe (PID: 6584)
- regsvr32.exe (PID: 1580)
- regsvr32.exe (PID: 3584)
- regsvr32.exe (PID: 9028)
Changes default file association
- K-Lite_Codec_Pack_1766_Standard.tmp (PID: 2732)
INFO
Application launched itself
- chrome.exe (PID: 3736)
Executable content was dropped or overwritten
- chrome.exe (PID: 7368)
- chrome.exe (PID: 3736)
The sample compiled with english language support
- chrome.exe (PID: 7368)
- StellarDataRecovery.tmp (PID: 7852)
- K-Lite_Codec_Pack_1766_Standard.tmp (PID: 2732)
Checks supported languages
- StellarDataRecovery.tmp (PID: 8424)
- StellarDataRecovery.exe (PID: 4116)
- StellarDataRecovery.exe (PID: 8096)
- StellarDataRecovery.tmp (PID: 7852)
- K-Lite_Codec_Pack_1766_Standard.exe (PID: 7960)
- K-Lite_Codec_Pack_1766_Standard.tmp (PID: 2732)
- SetACL_x86.exe (PID: 5876)
- SetACL_x86.exe (PID: 9036)
- SetACL_x64.exe (PID: 3648)
- SetACL_x64.exe (PID: 5460)
Checks proxy server information
- slui.exe (PID: 8576)
Create files in a temporary directory
- StellarDataRecovery.exe (PID: 4116)
- StellarDataRecovery.exe (PID: 8096)
- StellarDataRecovery.tmp (PID: 7852)
- K-Lite_Codec_Pack_1766_Standard.exe (PID: 7960)
- K-Lite_Codec_Pack_1766_Standard.tmp (PID: 2732)
Reads the computer name
- StellarDataRecovery.tmp (PID: 8424)
- StellarDataRecovery.exe (PID: 8096)
- StellarDataRecovery.tmp (PID: 7852)
- K-Lite_Codec_Pack_1766_Standard.tmp (PID: 2732)
- SetACL_x86.exe (PID: 9036)
- SetACL_x64.exe (PID: 5460)
- SetACL_x64.exe (PID: 3648)
- SetACL_x86.exe (PID: 5876)
Process checks computer location settings
- StellarDataRecovery.tmp (PID: 8424)
- StellarDataRecovery.tmp (PID: 7852)
- K-Lite_Codec_Pack_1766_Standard.tmp (PID: 2732)
Reads the software policy settings
- slui.exe (PID: 8576)
- K-Lite_Codec_Pack_1766_Standard.tmp (PID: 2732)
Compiled with Borland Delphi (YARA)
- StellarDataRecovery.exe (PID: 4116)
- StellarDataRecovery.exe (PID: 8096)
- StellarDataRecovery.tmp (PID: 8424)
- StellarDataRecovery.tmp (PID: 7852)
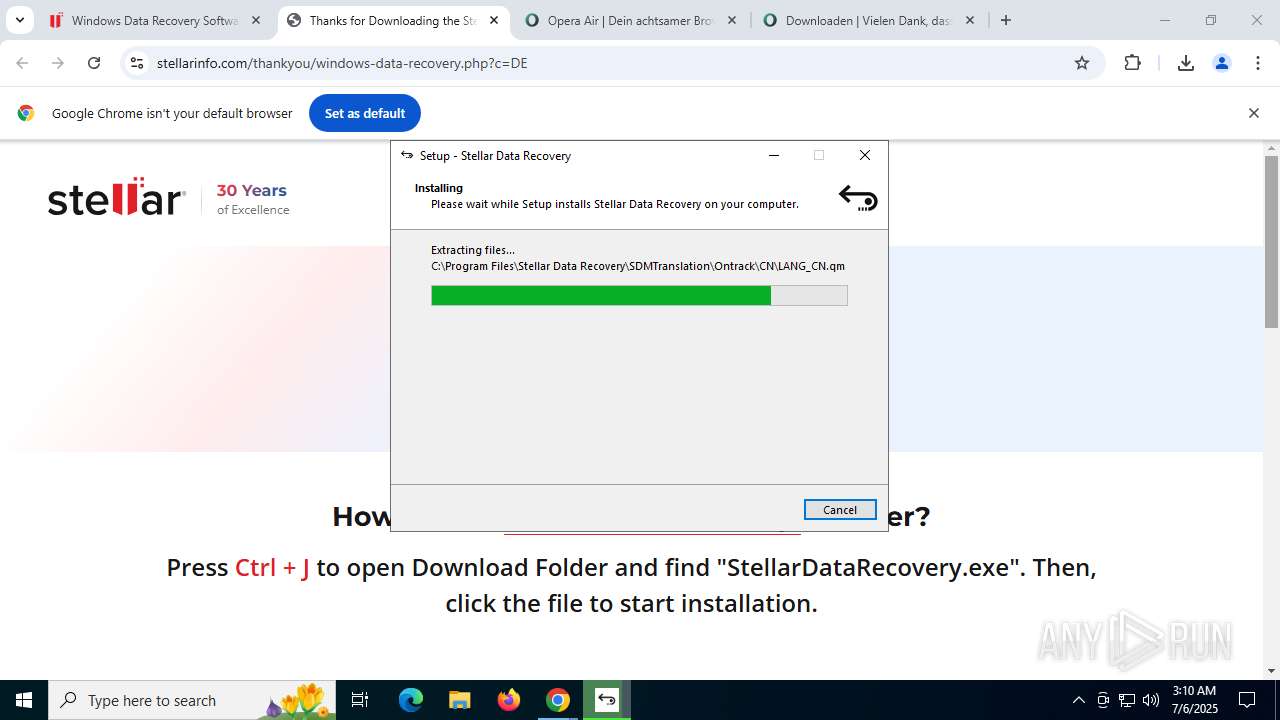
Creates files in the program directory
- StellarDataRecovery.tmp (PID: 7852)
- K-Lite_Codec_Pack_1766_Standard.tmp (PID: 2732)
- regsvr32.exe (PID: 1580)
Detects InnoSetup installer (YARA)
- StellarDataRecovery.tmp (PID: 8424)
- StellarDataRecovery.exe (PID: 4116)
- StellarDataRecovery.exe (PID: 8096)
- StellarDataRecovery.tmp (PID: 7852)
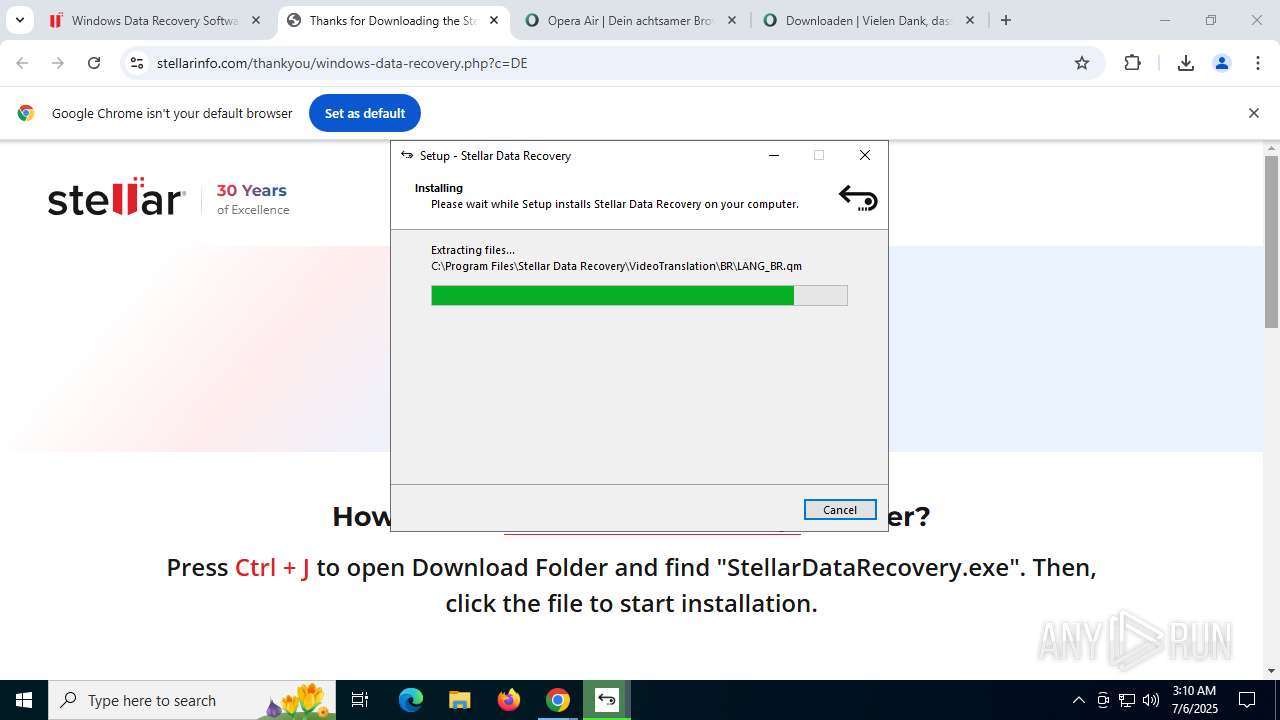
The sample compiled with spanish language support
- StellarDataRecovery.tmp (PID: 7852)
The sample compiled with french language support
- StellarDataRecovery.tmp (PID: 7852)
The sample compiled with bulgarian language support
- StellarDataRecovery.tmp (PID: 7852)
The sample compiled with Italian language support
- StellarDataRecovery.tmp (PID: 7852)
The sample compiled with german language support
- StellarDataRecovery.tmp (PID: 7852)
The sample compiled with japanese language support
- StellarDataRecovery.tmp (PID: 7852)
The sample compiled with czech language support
- StellarDataRecovery.tmp (PID: 7852)
The sample compiled with slovak language support
- StellarDataRecovery.tmp (PID: 7852)
The sample compiled with polish language support
- StellarDataRecovery.tmp (PID: 7852)
The sample compiled with swedish language support
- StellarDataRecovery.tmp (PID: 7852)
The sample compiled with portuguese language support
- StellarDataRecovery.tmp (PID: 7852)
The sample compiled with turkish language support
- StellarDataRecovery.tmp (PID: 7852)
The sample compiled with russian language support
- StellarDataRecovery.tmp (PID: 7852)
Creates a software uninstall entry
- StellarDataRecovery.tmp (PID: 7852)
- K-Lite_Codec_Pack_1766_Standard.tmp (PID: 2732)
The sample compiled with chinese language support
- StellarDataRecovery.tmp (PID: 7852)
Reads CPU info
- K-Lite_Codec_Pack_1766_Standard.tmp (PID: 2732)
The sample compiled with korean language support
- StellarDataRecovery.tmp (PID: 7852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
334
Monitored processes
193
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=2988,i,10203547314140925481,8382694415196600560,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=148 --field-trial-handle=11672,i,10203547314140925481,8382694415196600560,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=115 --field-trial-handle=7024,i,10203547314140925481,8382694415196600560,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=10144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=67 --field-trial-handle=9400,i,10203547314140925481,8382694415196600560,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=8224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=video_capture.mojom.VideoCaptureService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=7612,i,10203547314140925481,8382694415196600560,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=7080 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=130 --field-trial-handle=11020,i,10203547314140925481,8382694415196600560,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=11028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=150 --field-trial-handle=11748,i,10203547314140925481,8382694415196600560,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=7012 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6796,i,10203547314140925481,8382694415196600560,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4276 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=139 --field-trial-handle=9292,i,10203547314140925481,8382694415196600560,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=10728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1580 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files (x86)\K-Lite Codec Pack\Icaros\64-bit\IcarosPropertyHandler.dll" | C:\Windows\System32\regsvr32.exe | — | K-Lite_Codec_Pack_1766_Standard.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 980
Read events
22 518
Write events
3 397
Delete events
65
Modification events
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7S |
Value: 1 | |||
Executable files
655
Suspicious files
668
Text files
286
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1755c1.TMP | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1755c1.TMP | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF1755d0.TMP | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF1755e0.TMP | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1755e0.TMP | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1755e0.TMP | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
835
DNS requests
1 126
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8956 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
6748 | chrome.exe | GET | 200 | 142.250.185.174:80 | http://clients2.google.com/time/1/current?cup2key=8:W6PmOEYxp7yxjcOzLEGSUIg0tJppdXA0iolZqztcZOI&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4700 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8956 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
8956 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ambrwqvjn4gtyhpuw5s7peffqu_20250617.774246486.14/obedbbhbpmojnkanicioggnmelmoomoc_20250617.774246486.14_all_ENUS500000_izcccefko7yytylllztht4flui.crx3 | unknown | — | — | whitelisted |
8956 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ambrwqvjn4gtyhpuw5s7peffqu_20250617.774246486.14/obedbbhbpmojnkanicioggnmelmoomoc_20250617.774246486.14_all_ENUS500000_izcccefko7yytylllztht4flui.crx3 | unknown | — | — | whitelisted |
8956 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ambrwqvjn4gtyhpuw5s7peffqu_20250617.774246486.14/obedbbhbpmojnkanicioggnmelmoomoc_20250617.774246486.14_all_ENUS500000_izcccefko7yytylllztht4flui.crx3 | unknown | — | — | whitelisted |
8956 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ambrwqvjn4gtyhpuw5s7peffqu_20250617.774246486.14/obedbbhbpmojnkanicioggnmelmoomoc_20250617.774246486.14_all_ENUS500000_izcccefko7yytylllztht4flui.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6936 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6748 | chrome.exe | 142.250.185.174:80 | clients2.google.com | GOOGLE | US | whitelisted |
6748 | chrome.exe | 142.250.185.202:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
6748 | chrome.exe | 66.102.1.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6748 | chrome.exe | 151.101.1.91:443 | movies-and-shows-hd-2019-free-movies-show-box.fr.softonic.com | FASTLY | US | whitelisted |
6748 | chrome.exe | 151.101.1.91:80 | movies-and-shows-hd-2019-free-movies-show-box.fr.softonic.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
movies-and-shows-hd-2019-free-movies-show-box.fr.softonic.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
sdk.privacy-center.org |
| whitelisted |
rv-assets.softonic.com |
| whitelisted |
assets.sftcdn.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |