| File name: | b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin |
| Full analysis: | https://app.any.run/tasks/30ed7ed5-108f-4a6b-9b18-9684a6eef2f9 |
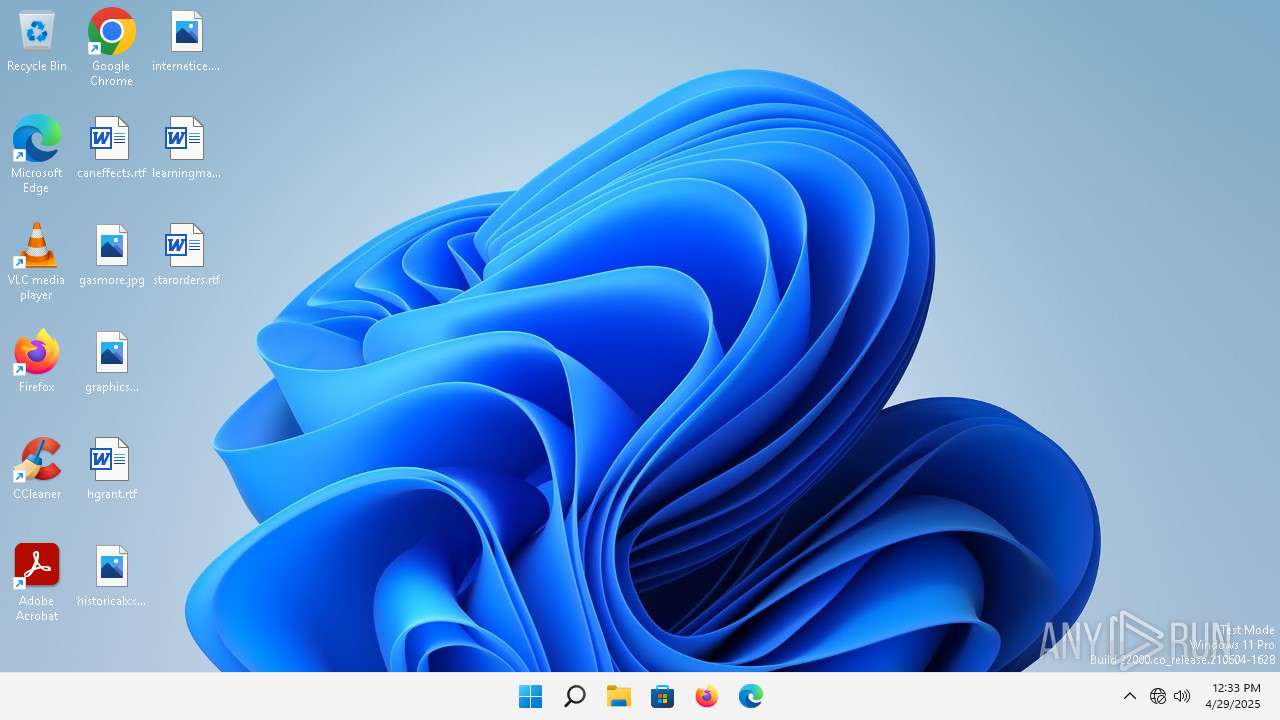
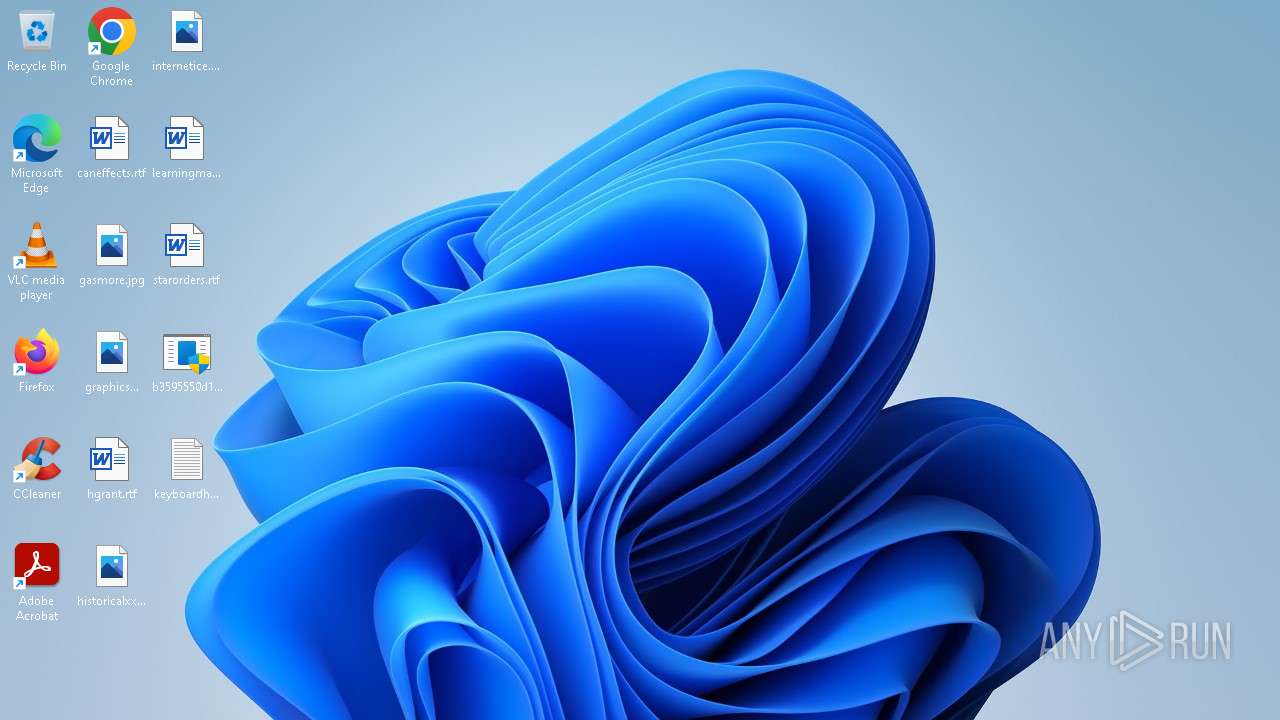
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 12:33:53 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | D2D1505A9E20A2A744A40658D92C2C27 |
| SHA1: | 00986F88825408E82173668D0B2C03EB306EA65D |
| SHA256: | B3595550D1D36A273BCB5DA10F7F0E4B014A2FF64E5980C4DAA2D59C9C1AE0E7 |
| SSDEEP: | 6144:lubYxVhnLJuutqPau7REJ5cMK4n28IHCit7mL:gbYx70tPauVETcMKS0HCrL |
MALICIOUS
Disables the Run the Start menu
- b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe (PID: 1096)
- b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe (PID: 444)
Disables the Shutdown in the Start menu
- b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe (PID: 1096)
- b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe (PID: 444)
Disables task manager
- b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe (PID: 1096)
- b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe (PID: 444)
Disables the LogOff the Start menu
- b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe (PID: 1096)
- b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe (PID: 444)
Task Manager has been disabled (taskmgr)
- b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe (PID: 444)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe (PID: 1096)
- b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe (PID: 444)
Reads the computer name
- b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe (PID: 1096)
- b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe (PID: 444)
Manual execution by a user
- b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe (PID: 1036)
- b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe (PID: 444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:03:21 02:19:05+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 111616 |
| InitializedDataSize: | 41472 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb23f |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
107
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Users\admin\Desktop\b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe" | C:\Users\admin\Desktop\b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1036 | "C:\Users\admin\Desktop\b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe" | C:\Users\admin\Desktop\b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1096 | "C:\Users\admin\Desktop\b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe" | C:\Users\admin\Desktop\b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1160 | "C:\Users\admin\Desktop\b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe" | C:\Users\admin\Desktop\b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
49
Read events
31
Write events
18
Delete events
0
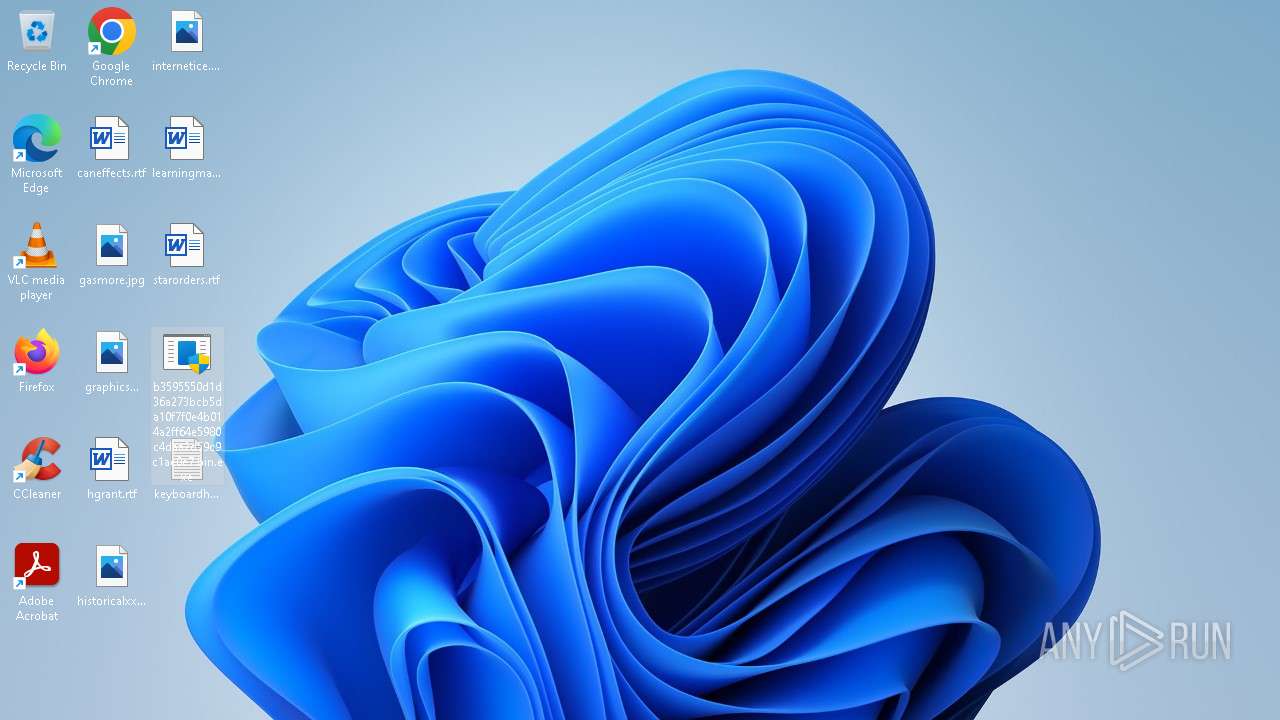
Modification events
| (PID) Process: | (1096) b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskmgr |
Value: 1 | |||
| (PID) Process: | (1096) b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableLockWorkstation |
Value: 1 | |||
| (PID) Process: | (1096) b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableChangePassword |
Value: 1 | |||
| (PID) Process: | (1096) b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableSwitchUserOption |
Value: 1 | |||
| (PID) Process: | (1096) b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoChangeStartMenu |
Value: 1 | |||
| (PID) Process: | (1096) b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoClose |
Value: 1 | |||
| (PID) Process: | (1096) b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoLogOff |
Value: 1 | |||
| (PID) Process: | (1096) b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoRun |
Value: 1 | |||
| (PID) Process: | (1096) b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoSetFolders |
Value: 1 | |||
| (PID) Process: | (444) b3595550d1d36a273bcb5da10f7f0e4b014a2ff64e5980c4daa2d59c9c1ae0e7.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskmgr |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
18
DNS requests
12
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2744 | smartscreen.exe | GET | 200 | 23.50.131.200:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e97fd6131e5dc604 | unknown | — | — | whitelisted |
2744 | smartscreen.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3640 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1352 | svchost.exe | GET | 200 | 2.16.164.42:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 208.89.74.21:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7ffa61214c1c53e3 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 208.89.74.21:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?e3701e10c494692d | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 208.89.74.21:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?e8295883656f7dad | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 208.89.74.21:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?cb47fcaae7c714cf | unknown | — | — | whitelisted |
2988 | OfficeClickToRun.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1352 | svchost.exe | 2.16.164.35:80 | — | Akamai International B.V. | NL | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2744 | smartscreen.exe | 48.209.164.47:443 | checkappexec.microsoft.com | — | US | whitelisted |
2744 | smartscreen.exe | 23.50.131.200:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
2744 | smartscreen.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5336 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3640 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3640 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2776 | svchost.exe | 13.89.179.13:443 | v10.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
v10.events.data.microsoft.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |