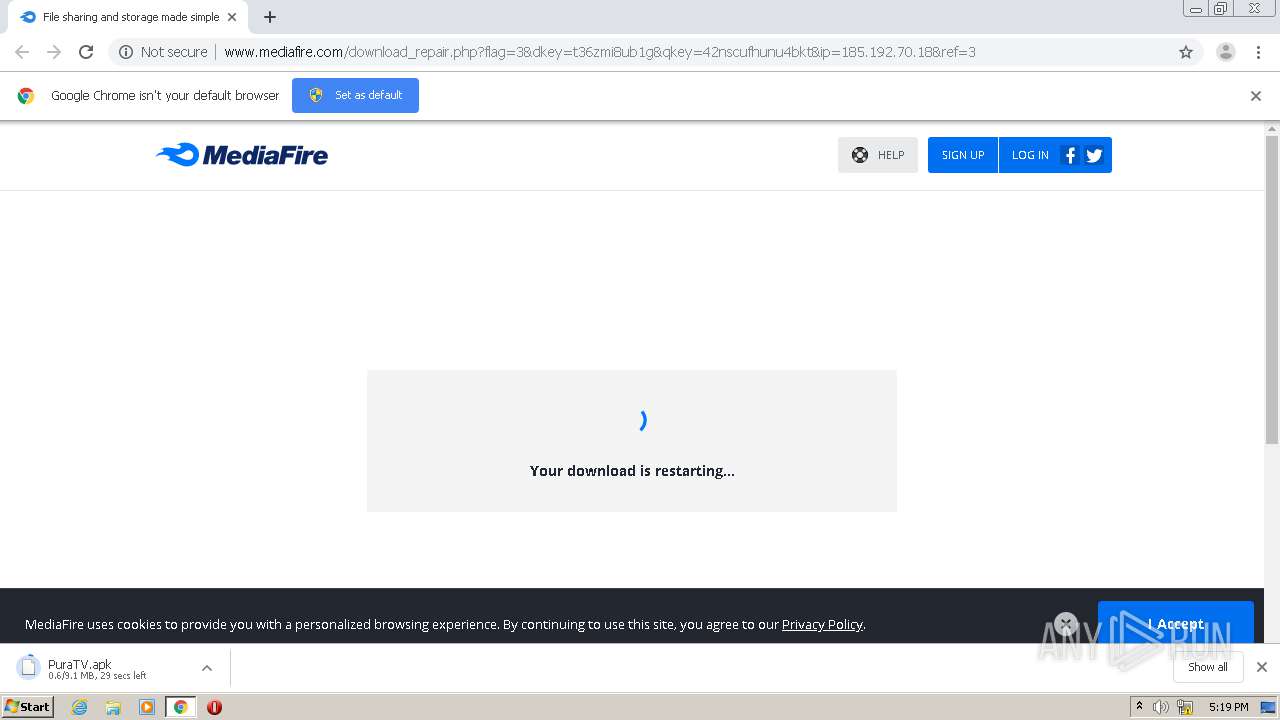
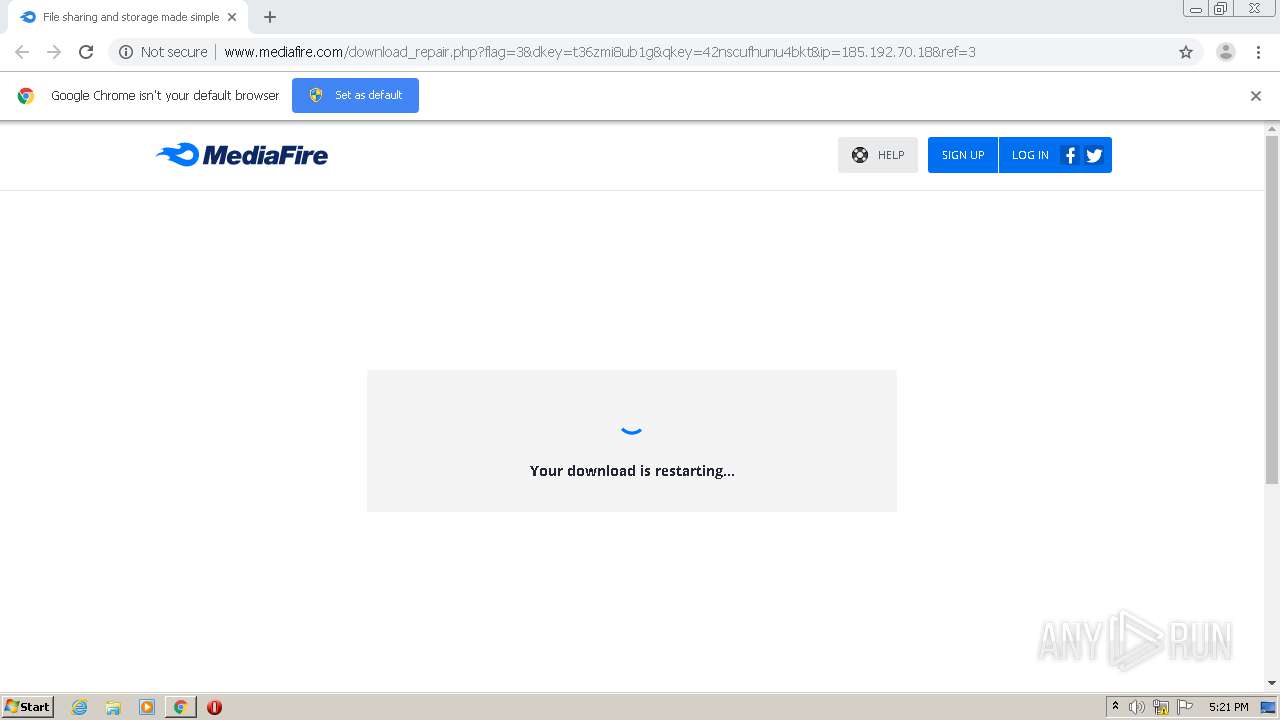
| URL: | http://download2343.mediafire.com/t36zmi8ub1gg/42nscufhunu4bkt/PuraTV.apk |
| Full analysis: | https://app.any.run/tasks/dc4ff1e8-1dab-40c3-9e52-0df17c3d4399 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2021, 17:18:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4D3BFE17ADCCF1C7164FA7D7F1FBE483 |
| SHA1: | E302721F255B2C50F209CC37FE8C31E8B29A57E2 |
| SHA256: | B34A02CA12EE6200FDAE292ECEADFBC801A15F0677C23C47E0BA6110F94CBDEC |
| SSDEEP: | 3:N1KaKE5WO6EQeGGWEkKyHRQLQbaXYEkn:CalmEQeGBEeQ7XYEkn |
MALICIOUS
No malicious indicators.SUSPICIOUS
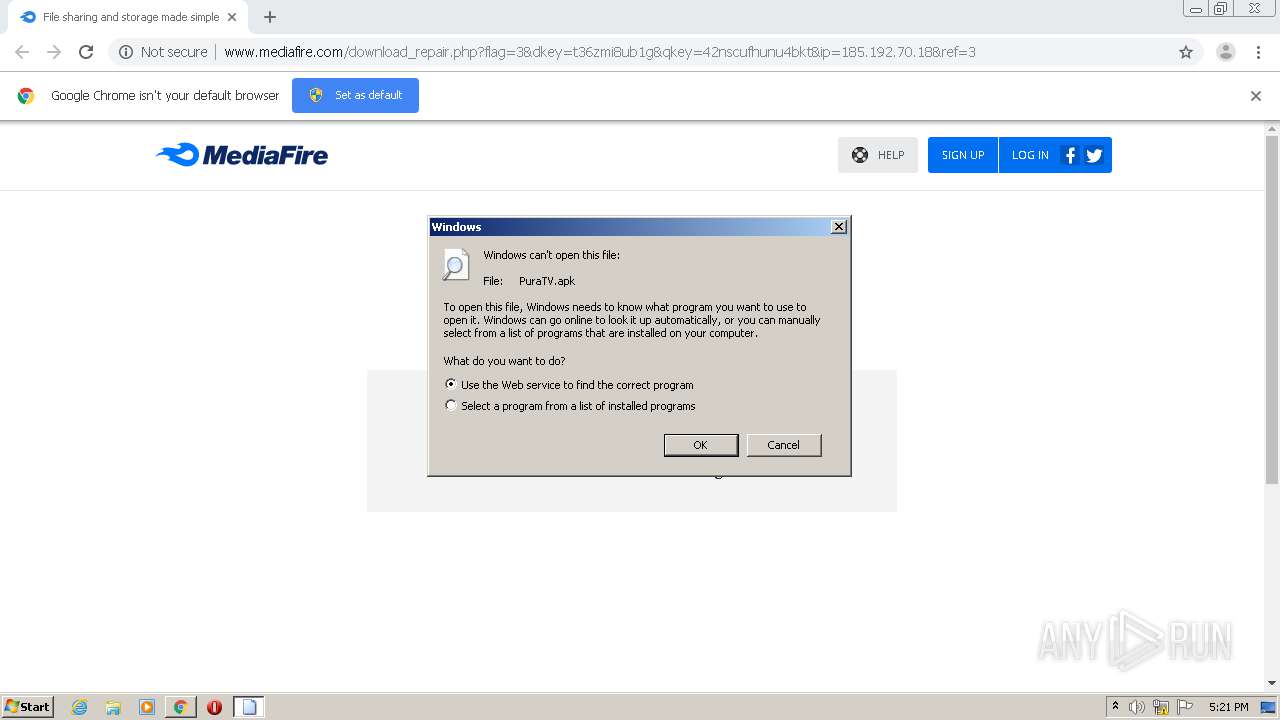
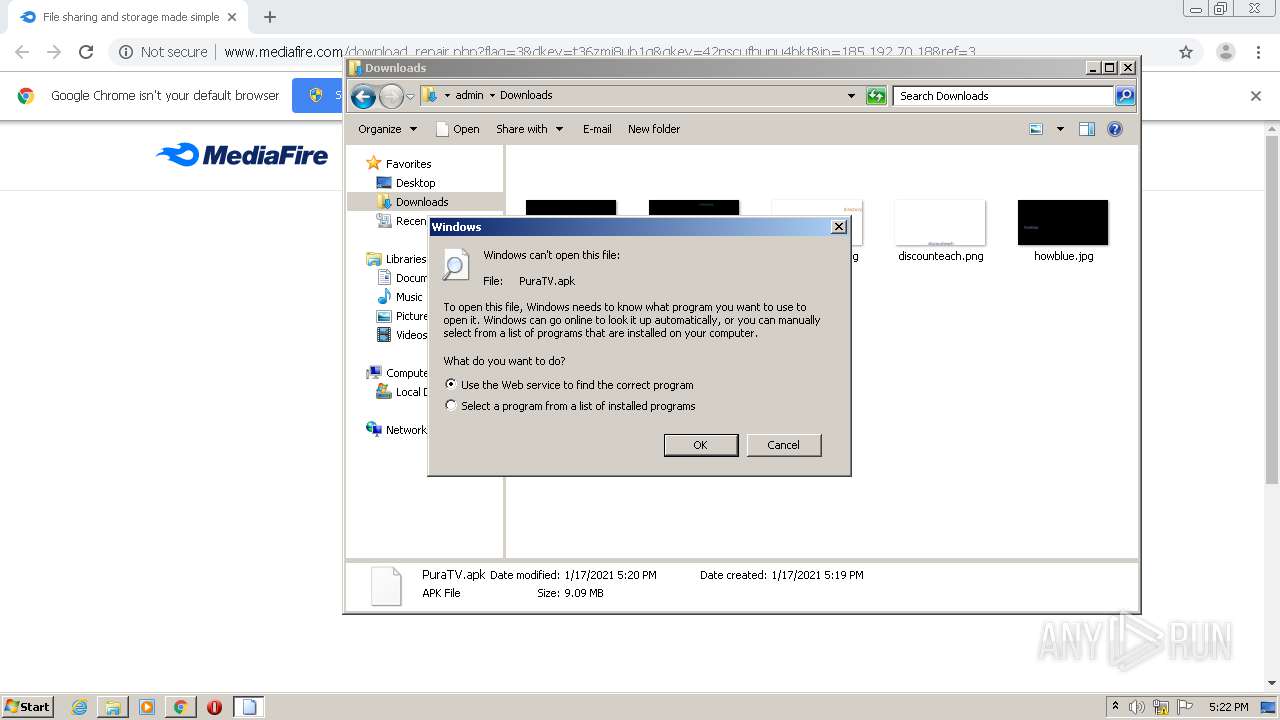
Uses RUNDLL32.EXE to load library
- chrome.exe (PID: 3744)
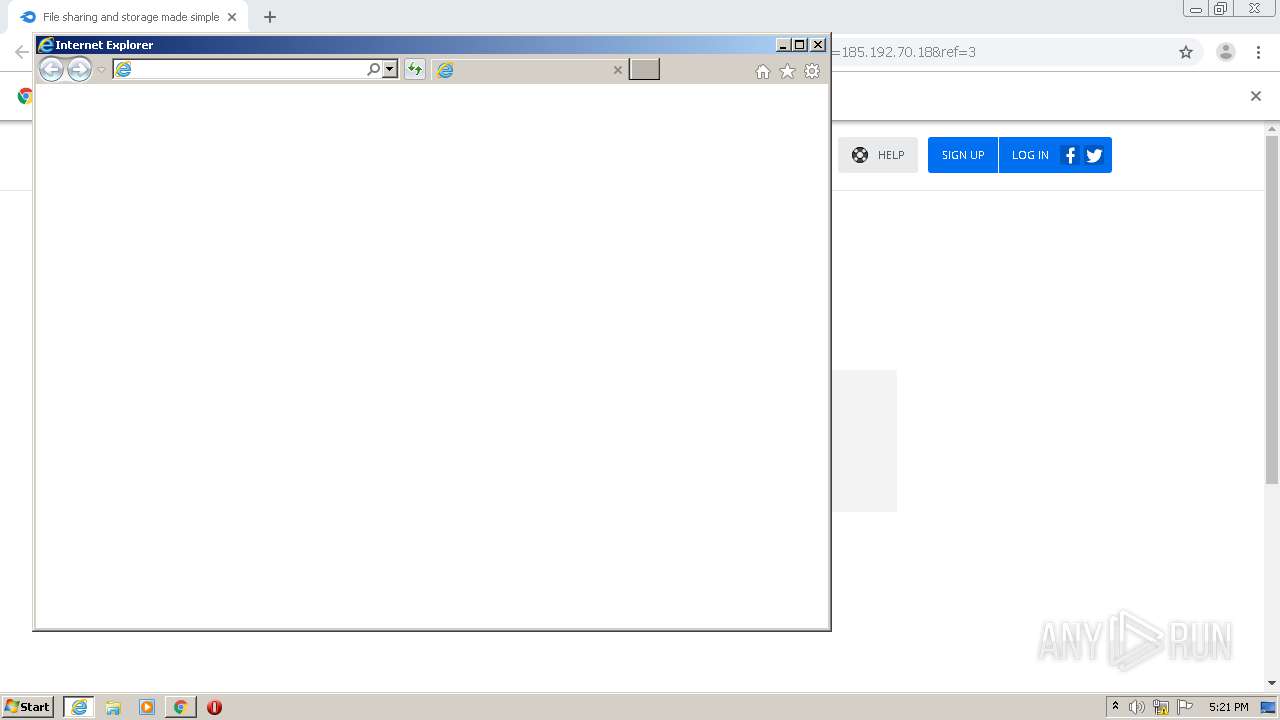
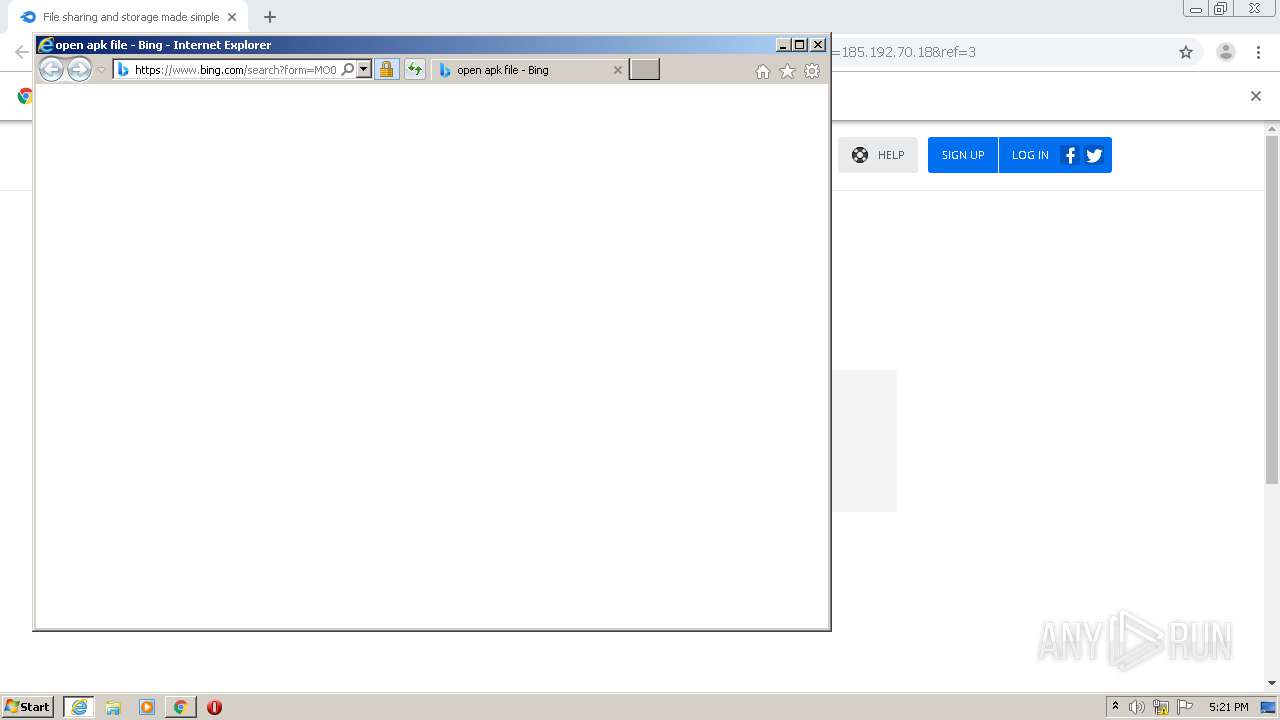
Starts Internet Explorer
- rundll32.exe (PID: 3400)
INFO
Reads the hosts file
- chrome.exe (PID: 3744)
- chrome.exe (PID: 3992)
Application launched itself
- chrome.exe (PID: 3744)
- iexplore.exe (PID: 3256)
Reads internet explorer settings
- iexplore.exe (PID: 3524)
Reads settings of System Certificates
- iexplore.exe (PID: 3256)
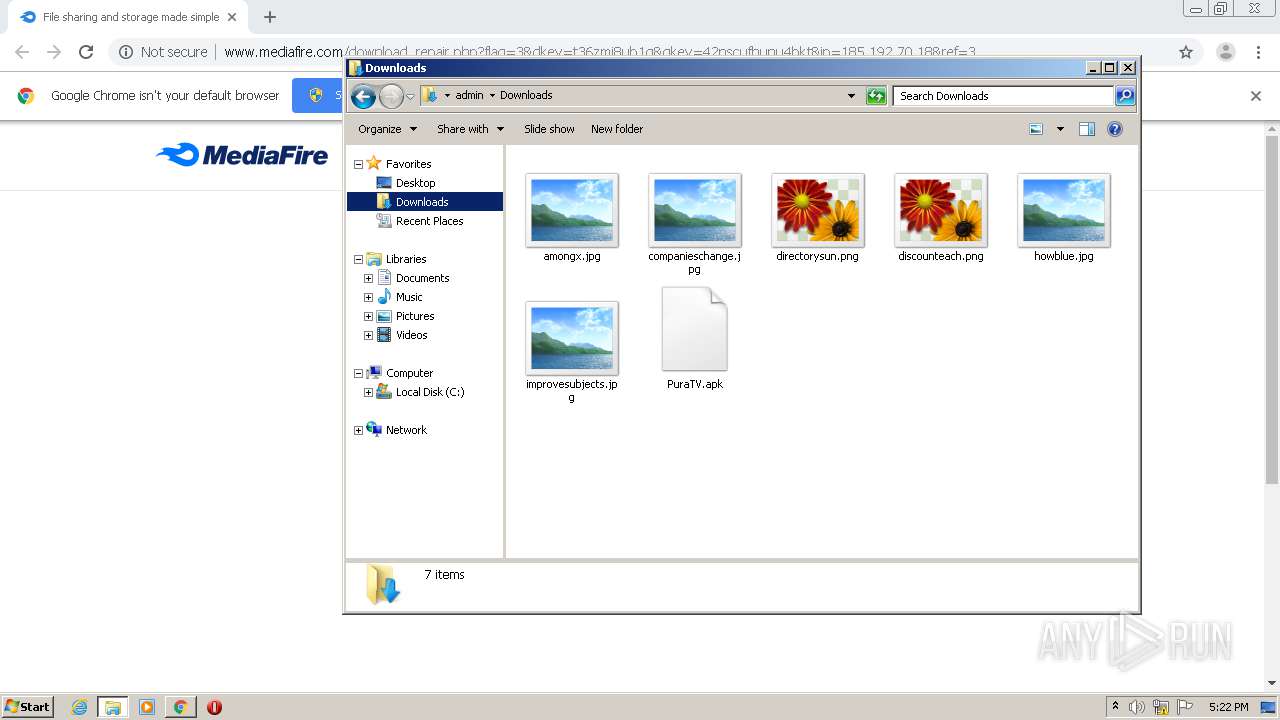
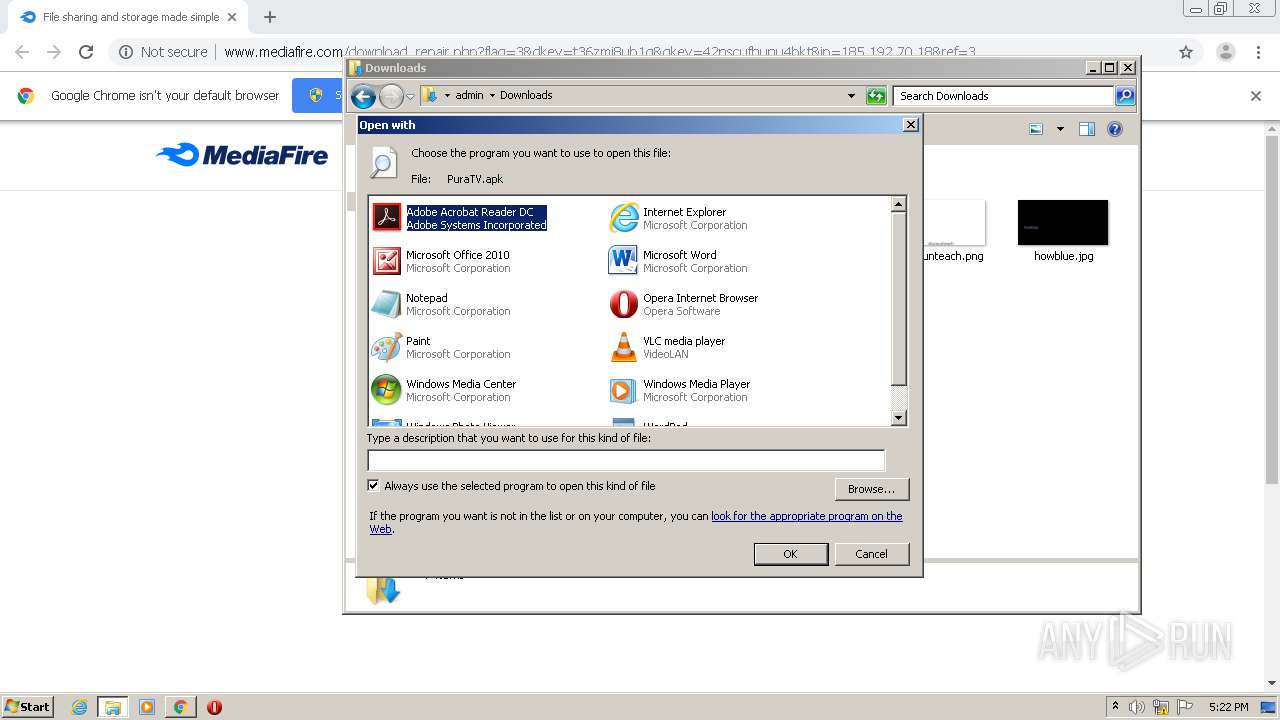
Manual execution by user
- explorer.exe (PID: 2560)
- rundll32.exe (PID: 3220)
Creates files in the user directory
- iexplore.exe (PID: 3524)
Changes internet zones settings
- iexplore.exe (PID: 3256)
Changes settings of System certificates
- iexplore.exe (PID: 3256)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3256)
Changes default file association
- rundll32.exe (PID: 3220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
17
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ed4a9d0,0x6ed4a9e0,0x6ed4a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,4411435983746757862,321042144726255275,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=726627756845612524 --mojo-platform-channel-handle=3520 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4411435983746757862,321042144726255275,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18260468664351020894 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2152 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2560 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4411435983746757862,321042144726255275,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=90205295610811239 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4411435983746757862,321042144726255275,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9589783175687949796 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2784 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
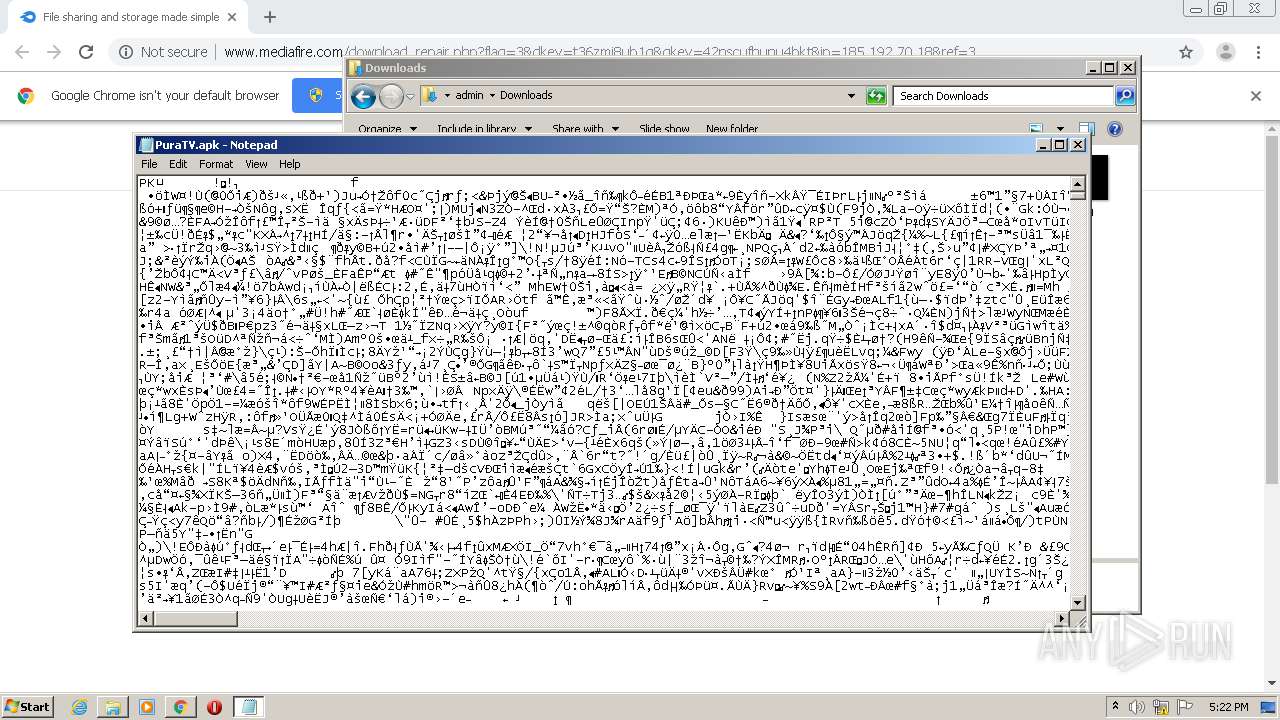
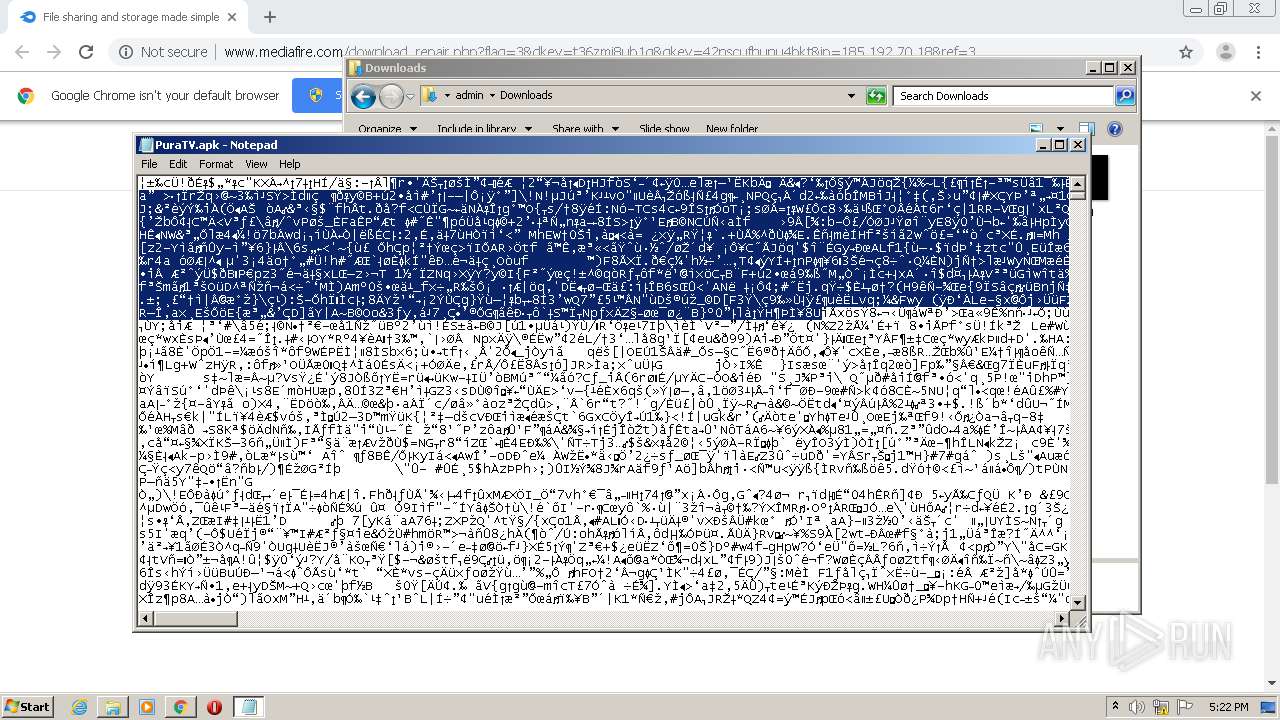
| 3112 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\PuraTV.apk | C:\Windows\system32\NOTEPAD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3220 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\PuraTV.apk | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3256 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?LinkId=57426&Ext=apk | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3400 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\PuraTV.apk | C:\Windows\system32\rundll32.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 3221225547 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 111
Read events
1 898
Write events
206
Delete events
7
Modification events
| (PID) Process: | (3744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3744-13255377555330000 |
Value: 259 | |||
| (PID) Process: | (3744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (3744) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
51
Text files
89
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60047194-EA0.pma | — | |
MD5:— | SHA256:— | |||
| 3744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9ed4a24f-92c1-4200-b164-2c7849c21bf2.tmp | — | |
MD5:— | SHA256:— | |||
| 3744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 3744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:67F45CAA18C889645F50CD6216C81E65 | SHA256:33ED82CDDDFFD55A5059C147C6CD20F66C6712314F890A39576D3C10914D0029 | |||
| 3744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 3744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF25ea0.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
58
DNS requests
36
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
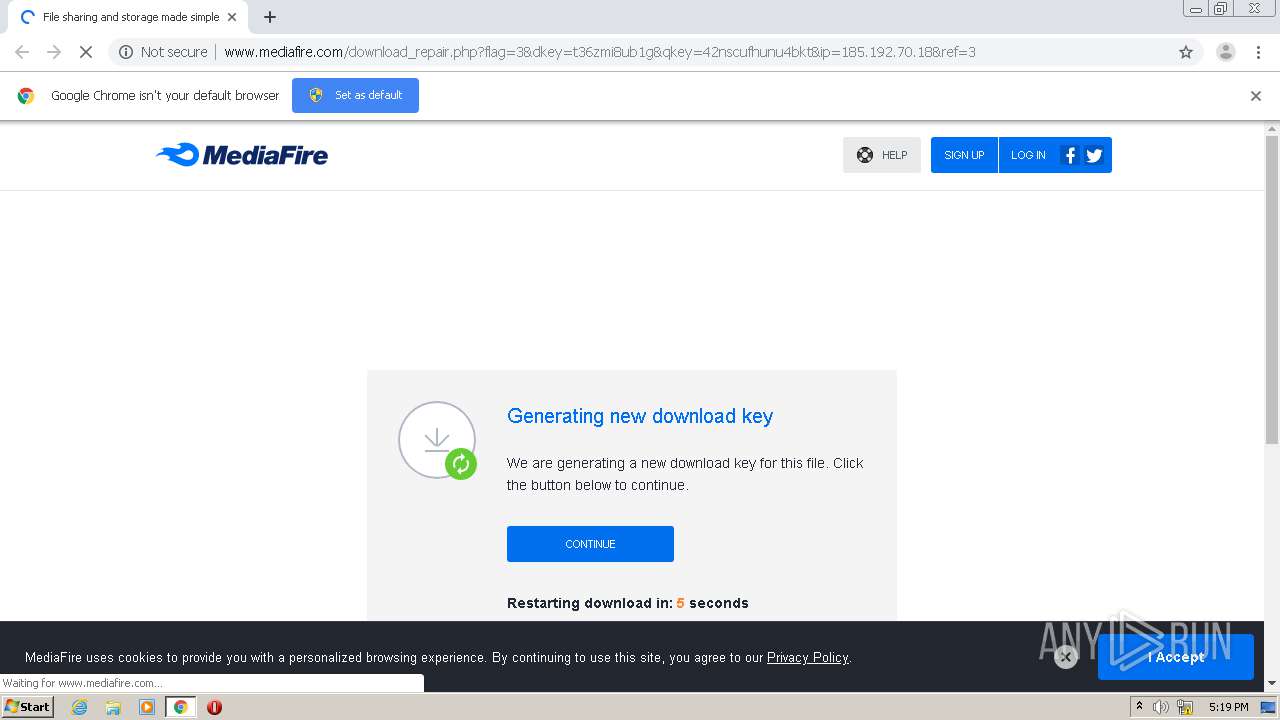
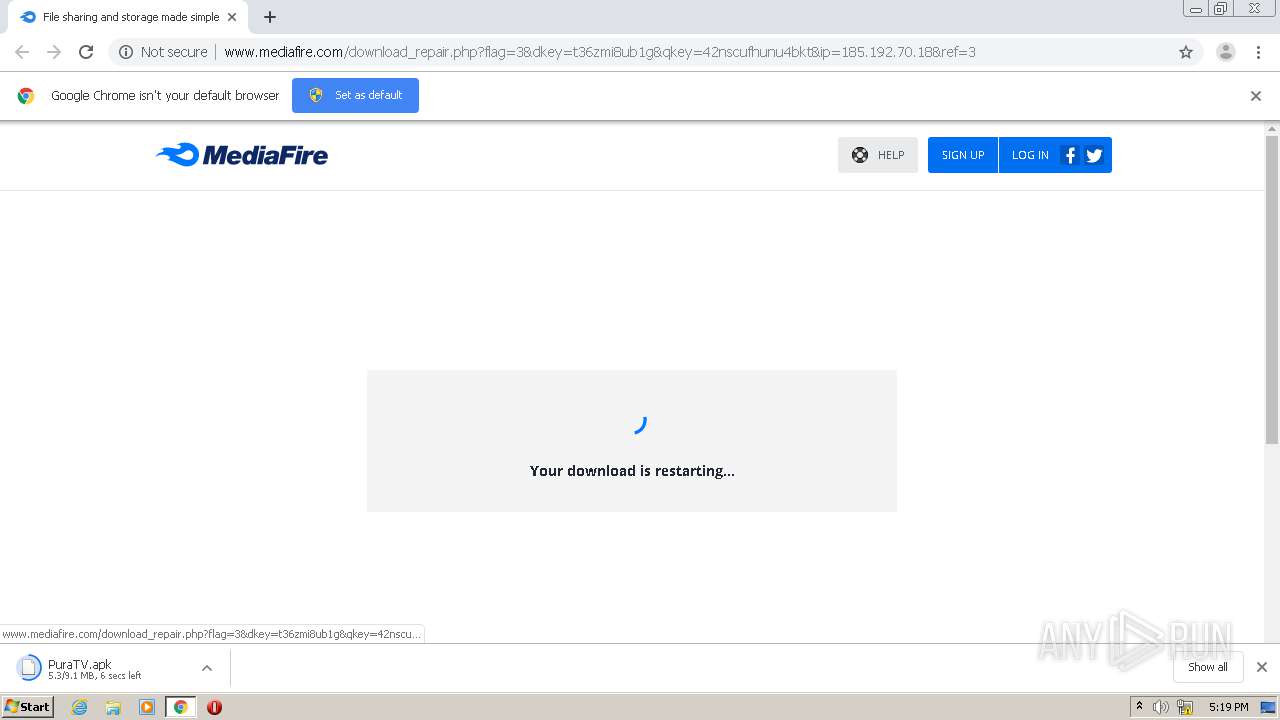
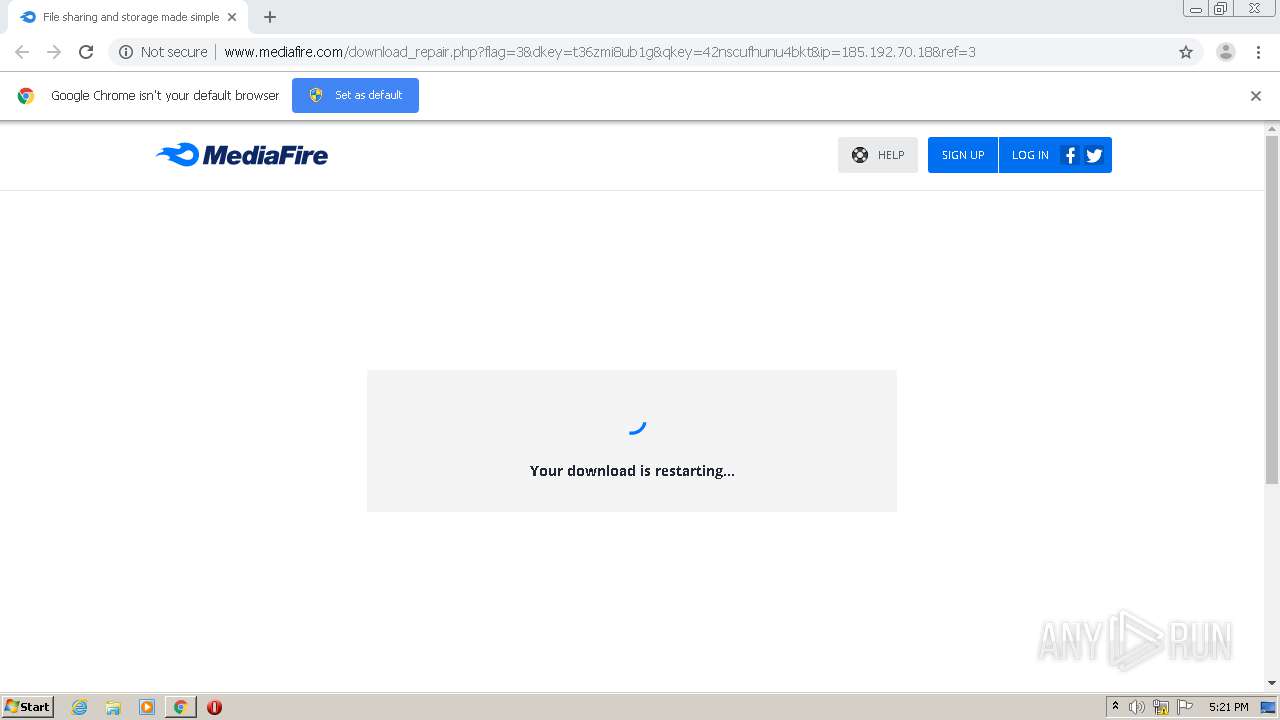
3992 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/download_repair.php?flag=3&dkey=t36zmi8ub1g&qkey=42nscufhunu4bkt&ip=185.192.70.18&ref=3 | US | html | 13.7 Kb | shared |
3992 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/css/mfv4_121718.php?ver=nonssl&date=2021-01-17 | US | text | 56.9 Kb | shared |
3992 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/header/mf_logo_u1_full_color_reversed.svg | US | image | 2.02 Kb | shared |
3992 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/js/master_121718.js | US | text | 150 Kb | shared |
3992 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/header/mf_logo_u1_full_color.svg | US | image | 2.04 Kb | shared |
3992 | chrome.exe | GET | 302 | 199.91.155.84:80 | http://download2343.mediafire.com/t36zmi8ub1gg/42nscufhunu4bkt/PuraTV.apk | US | — | — | unknown |
3992 | chrome.exe | GET | 200 | 64.233.181.95:80 | http://ajax.googleapis.com/ajax/libs/jquery/1.7.2/jquery.min.js | US | html | 33.0 Kb | whitelisted |
3992 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/images/icons/myfiles/default.png | US | image | 424 b | shared |
3992 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/icons/svg_dark/loading_indeterminate.svg | US | image | 363 b | shared |
3992 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/blank.html | US | html | 157 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3992 | chrome.exe | 199.91.155.84:80 | download2343.mediafire.com | MediaFire, LLC | US | unknown |
3992 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
3992 | chrome.exe | 104.16.202.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
3992 | chrome.exe | 173.194.195.95:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3992 | chrome.exe | 104.16.203.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
3992 | chrome.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
3992 | chrome.exe | 216.58.212.136:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3992 | chrome.exe | 64.233.181.95:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3992 | chrome.exe | 172.217.212.95:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3992 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download2343.mediafire.com |
| unknown |
accounts.google.com |
| shared |
www.mediafire.com |
| shared |
static.mediafire.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3992 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |