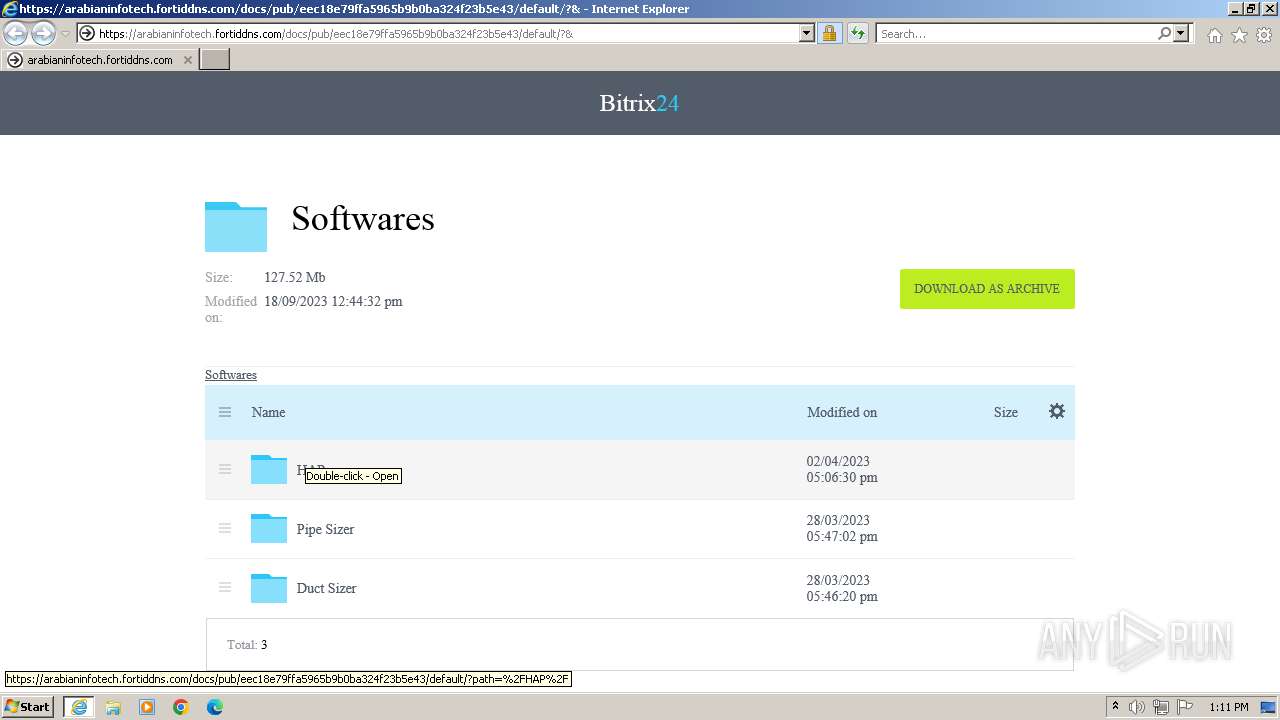
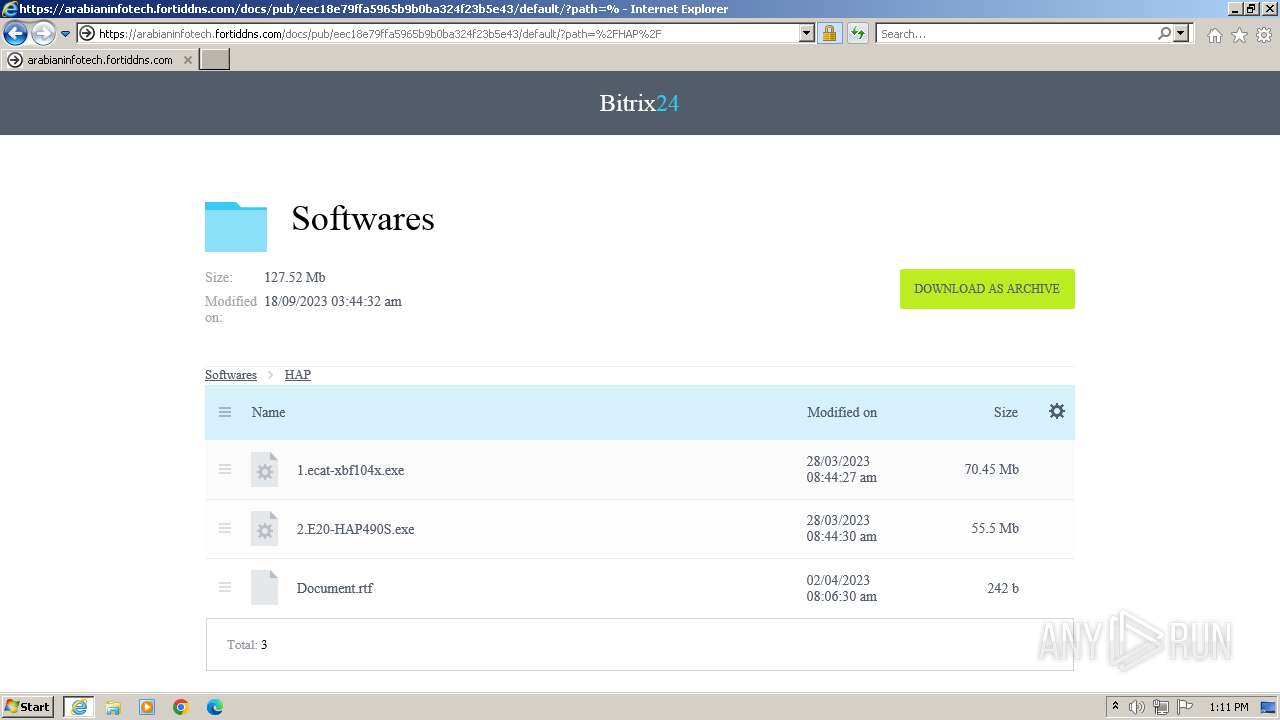
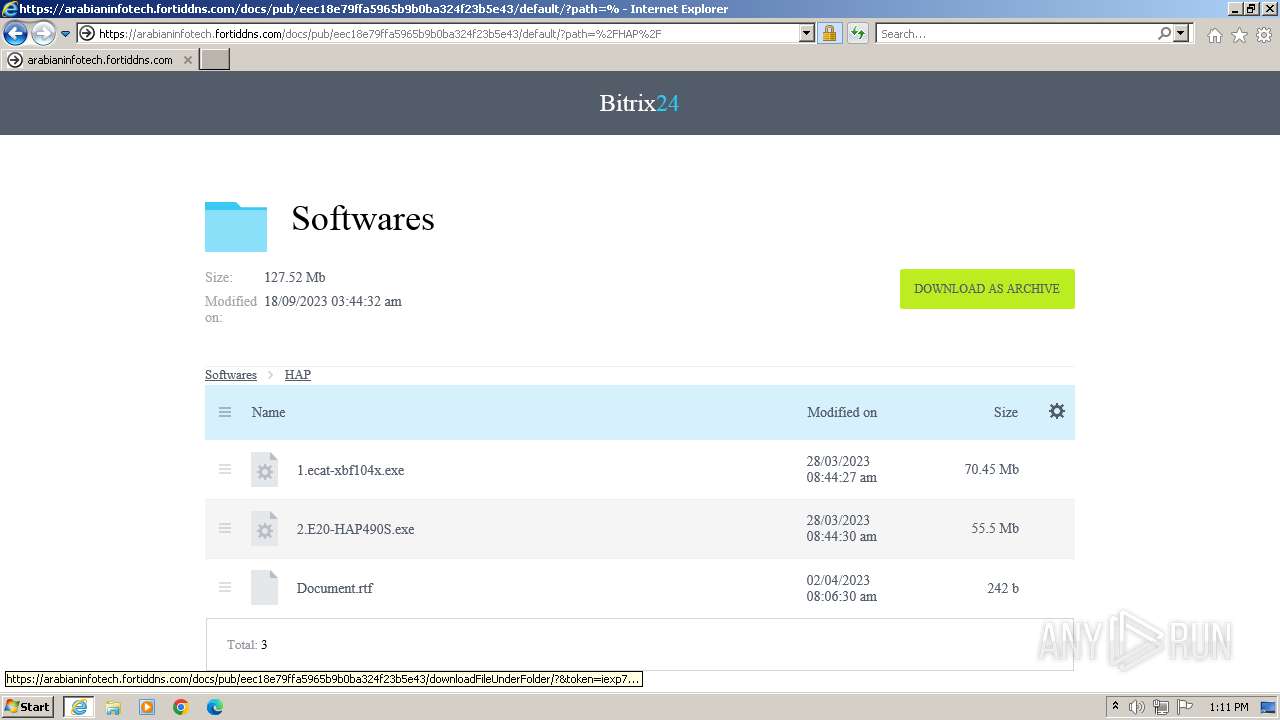
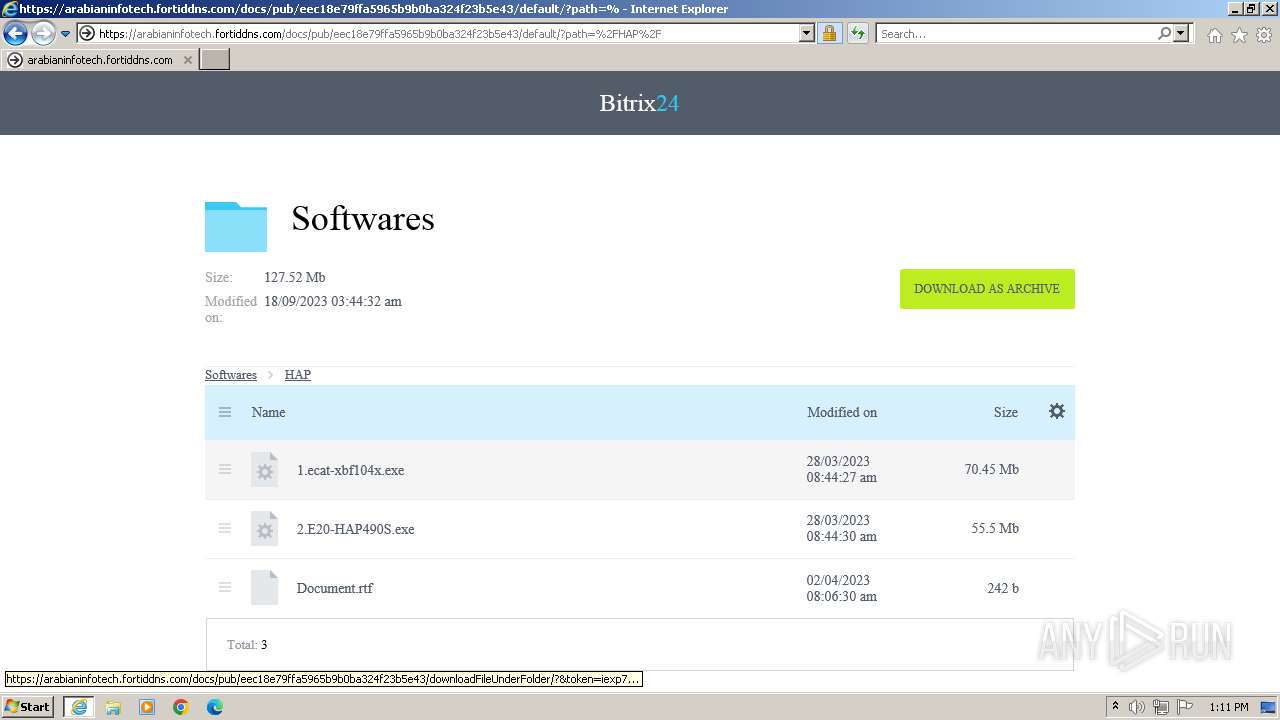
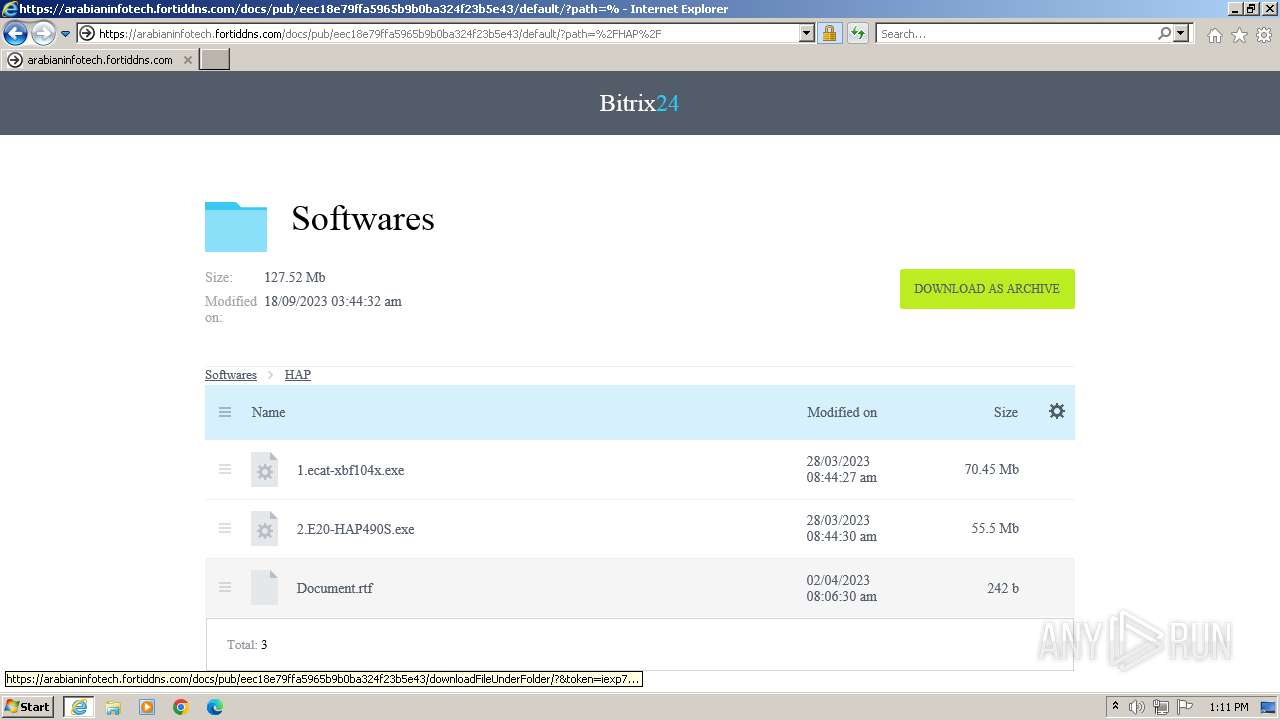
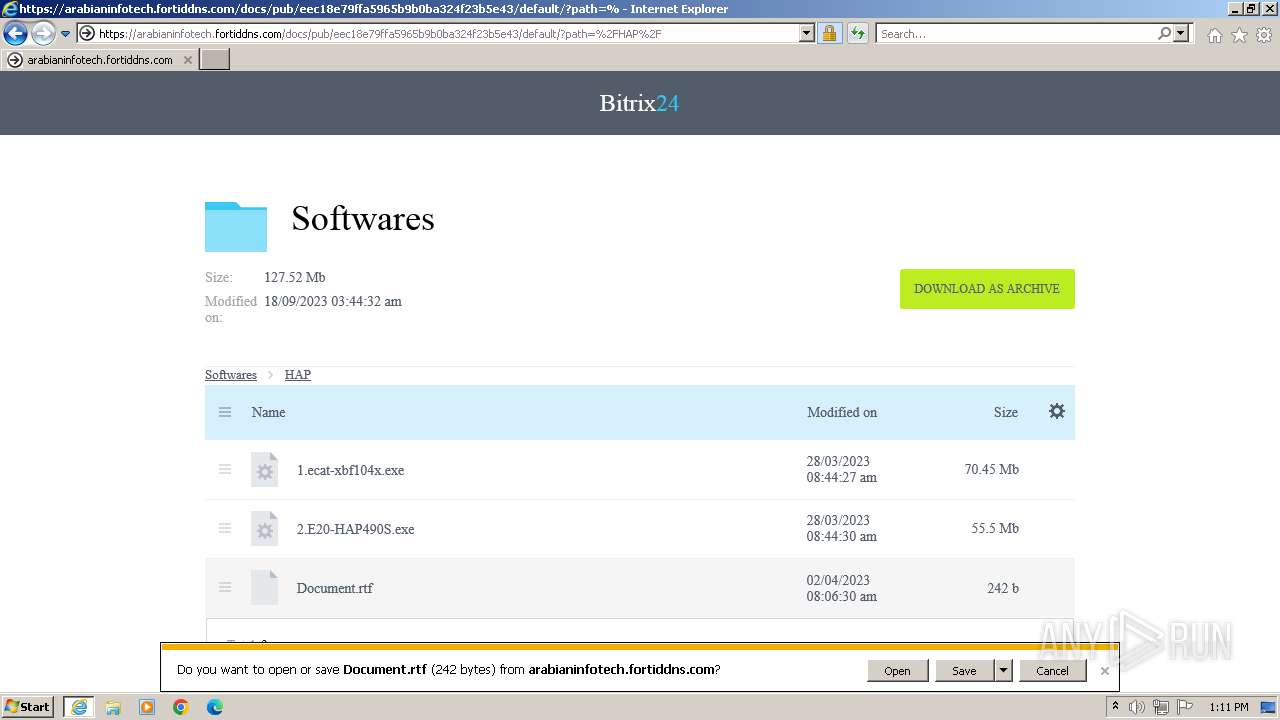
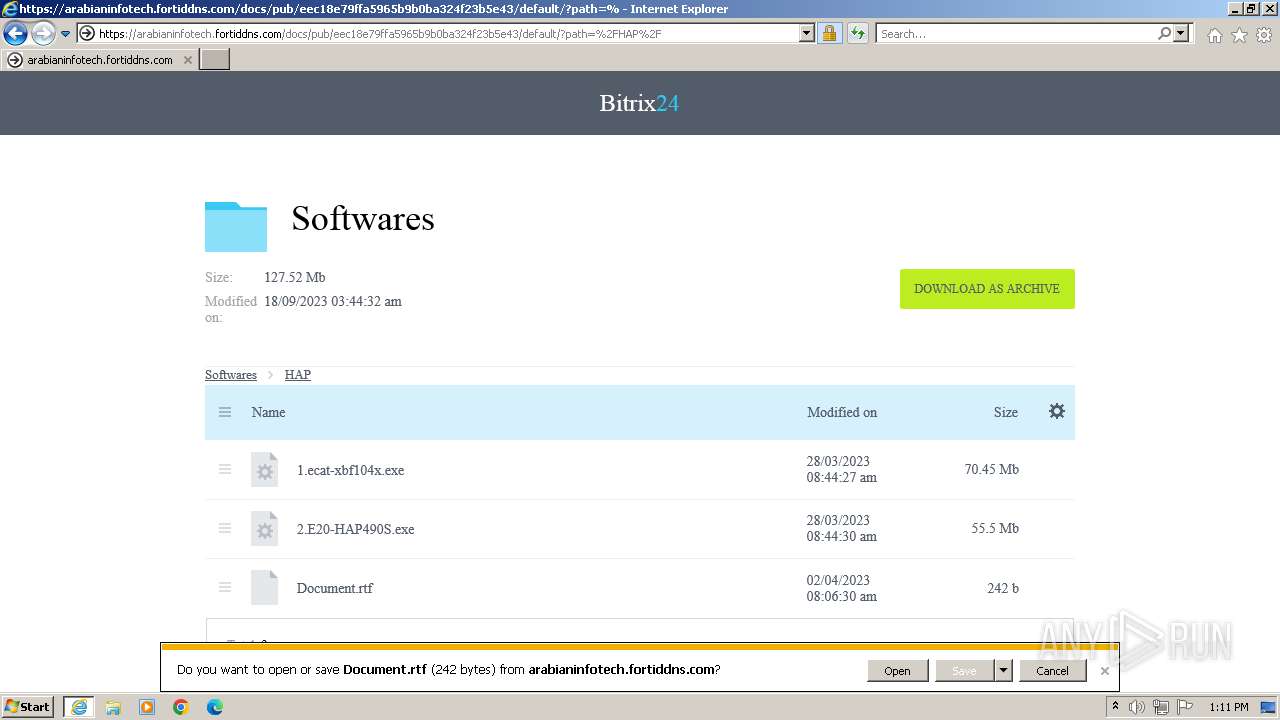
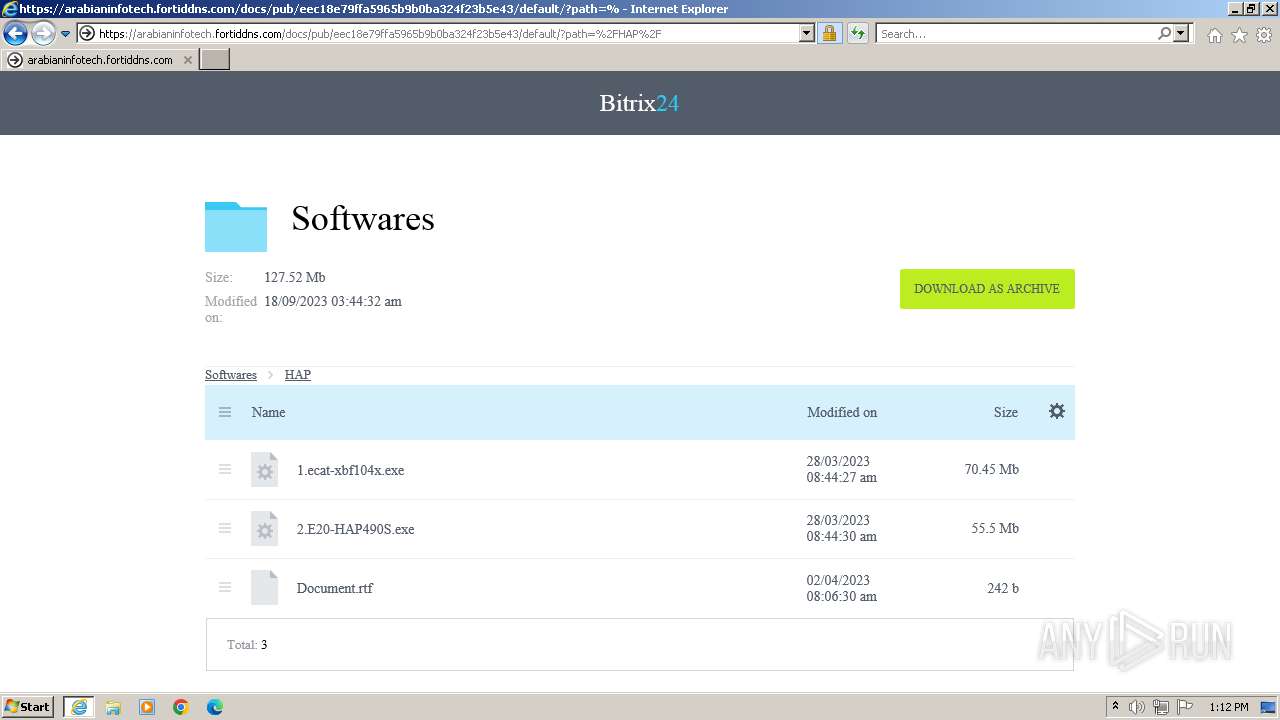
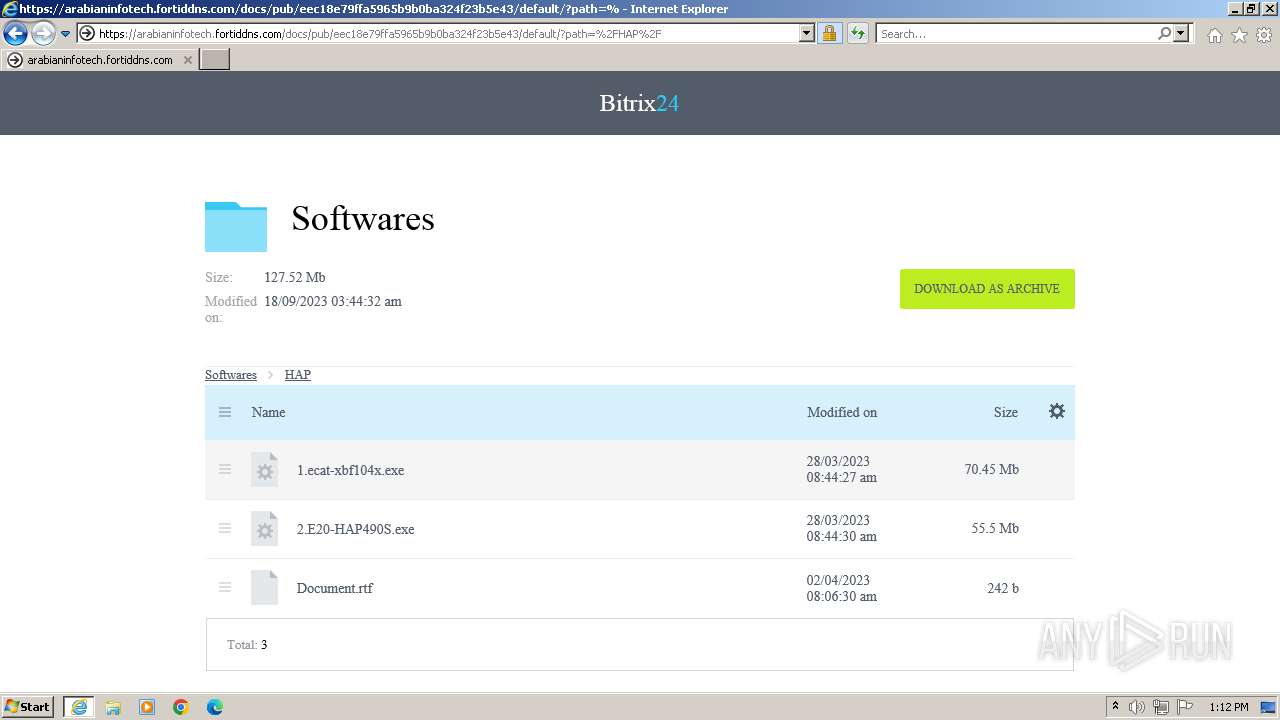
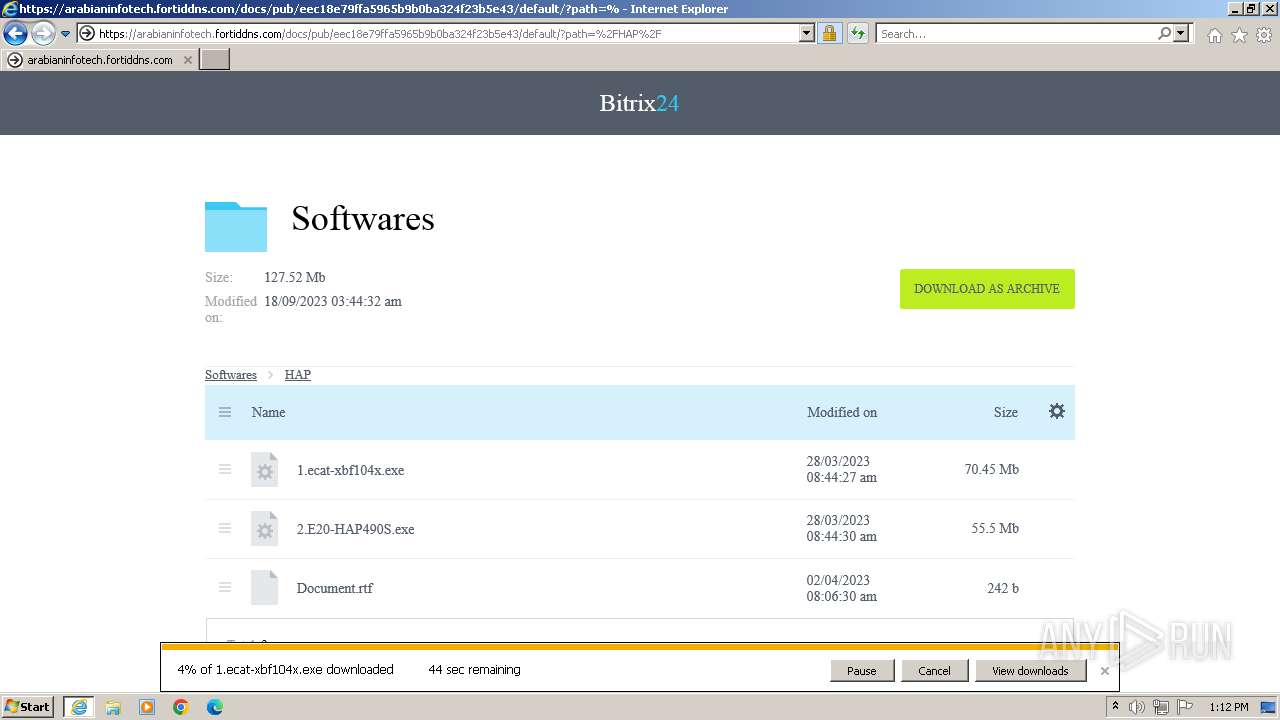
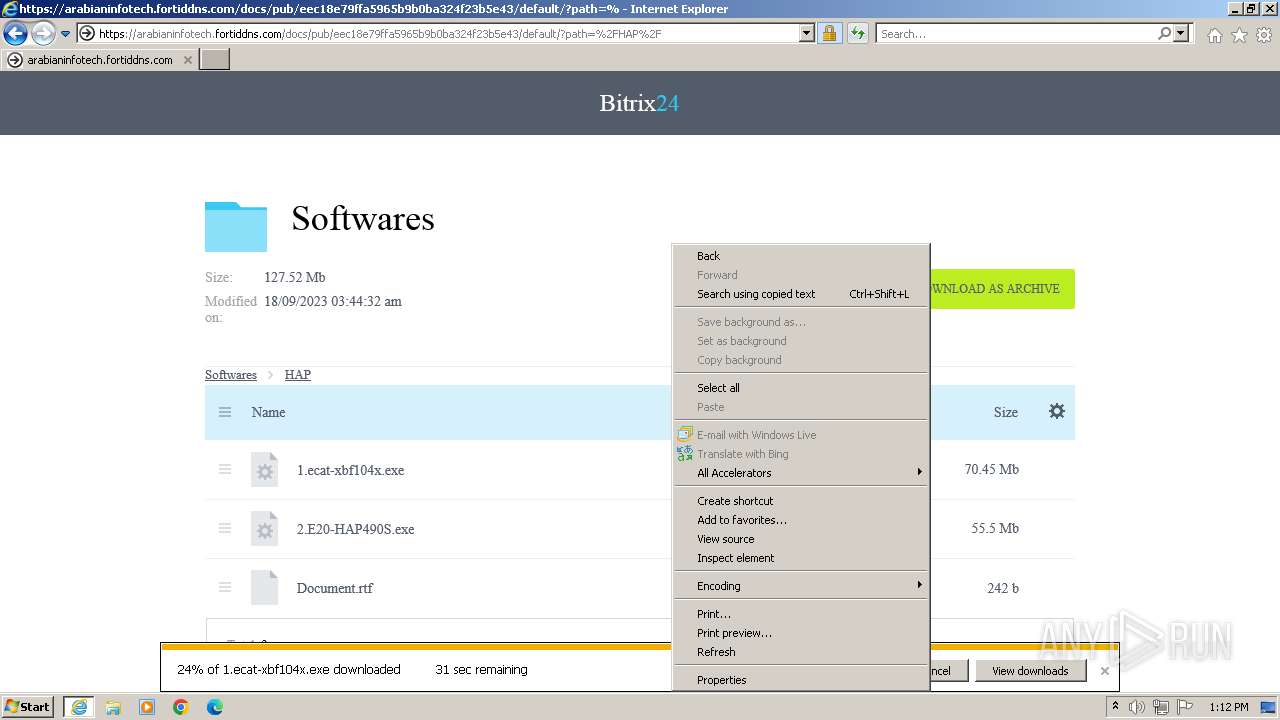
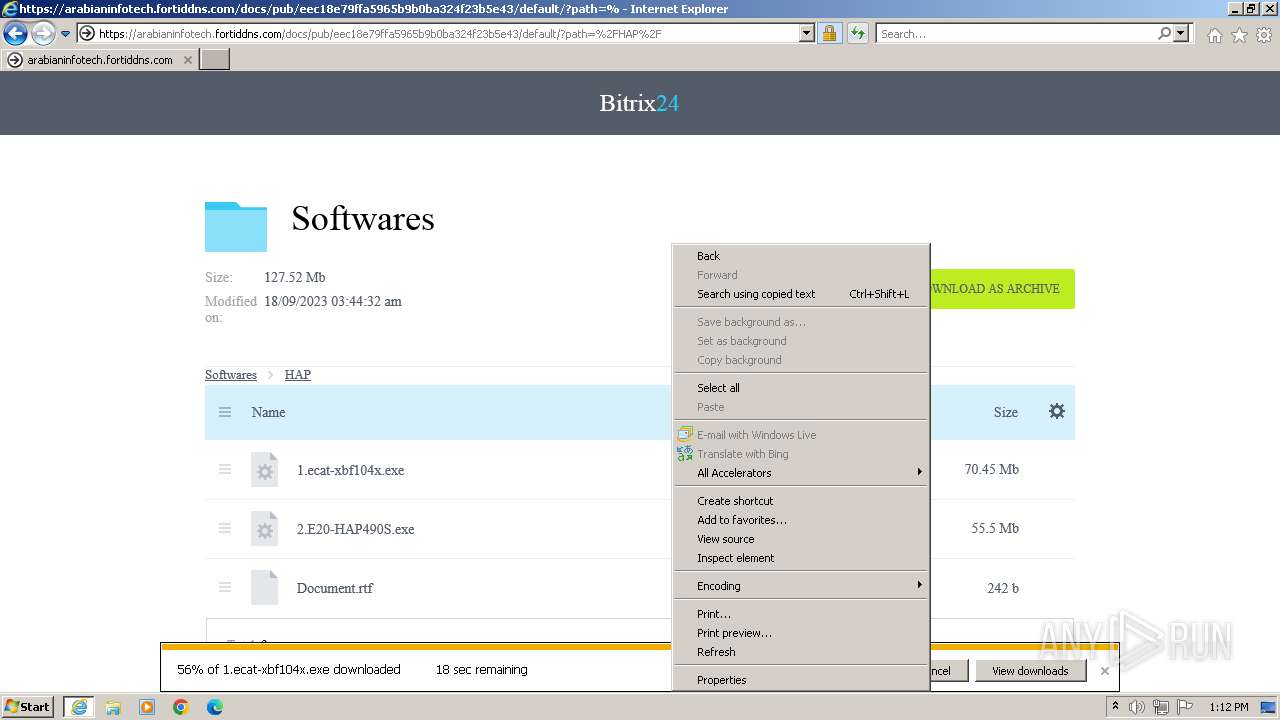
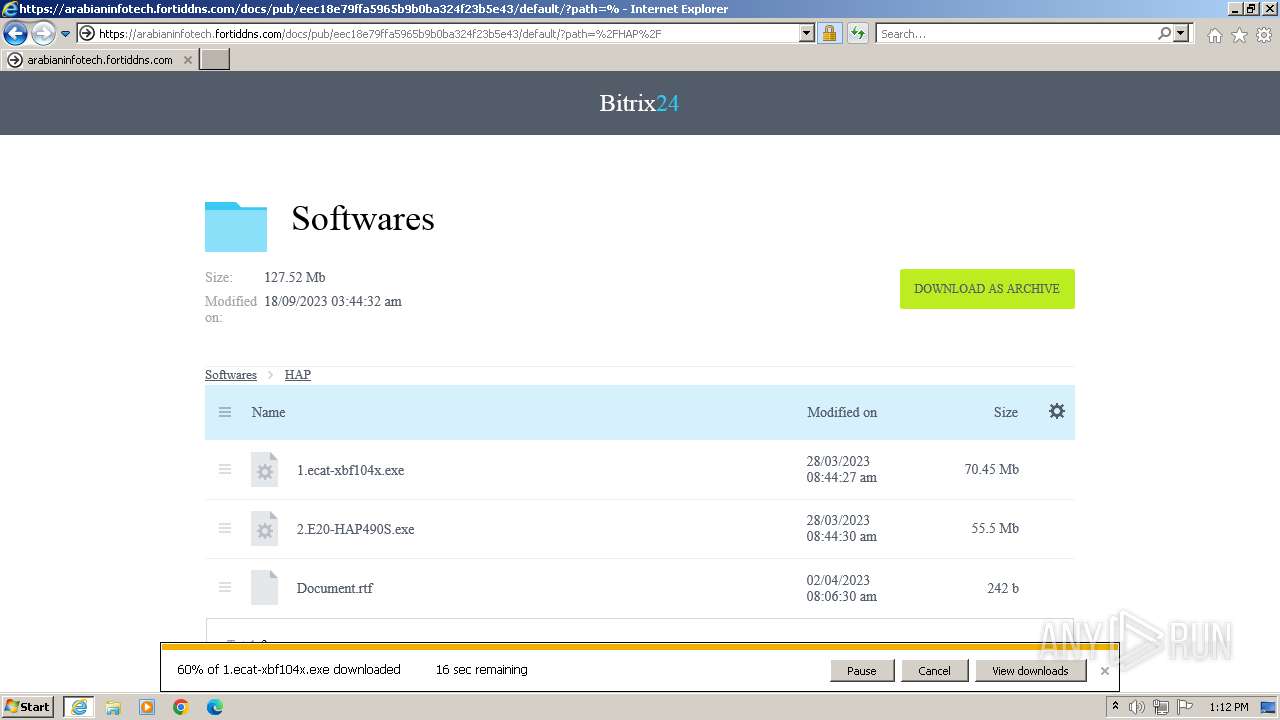
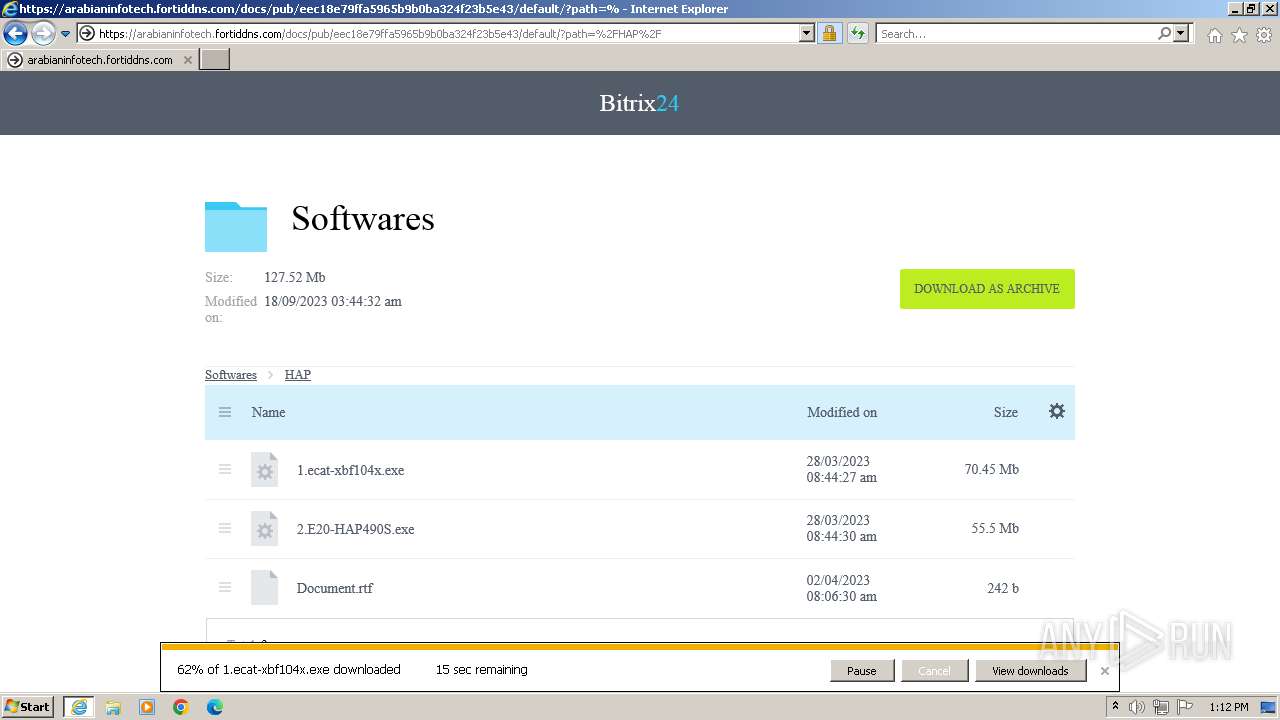
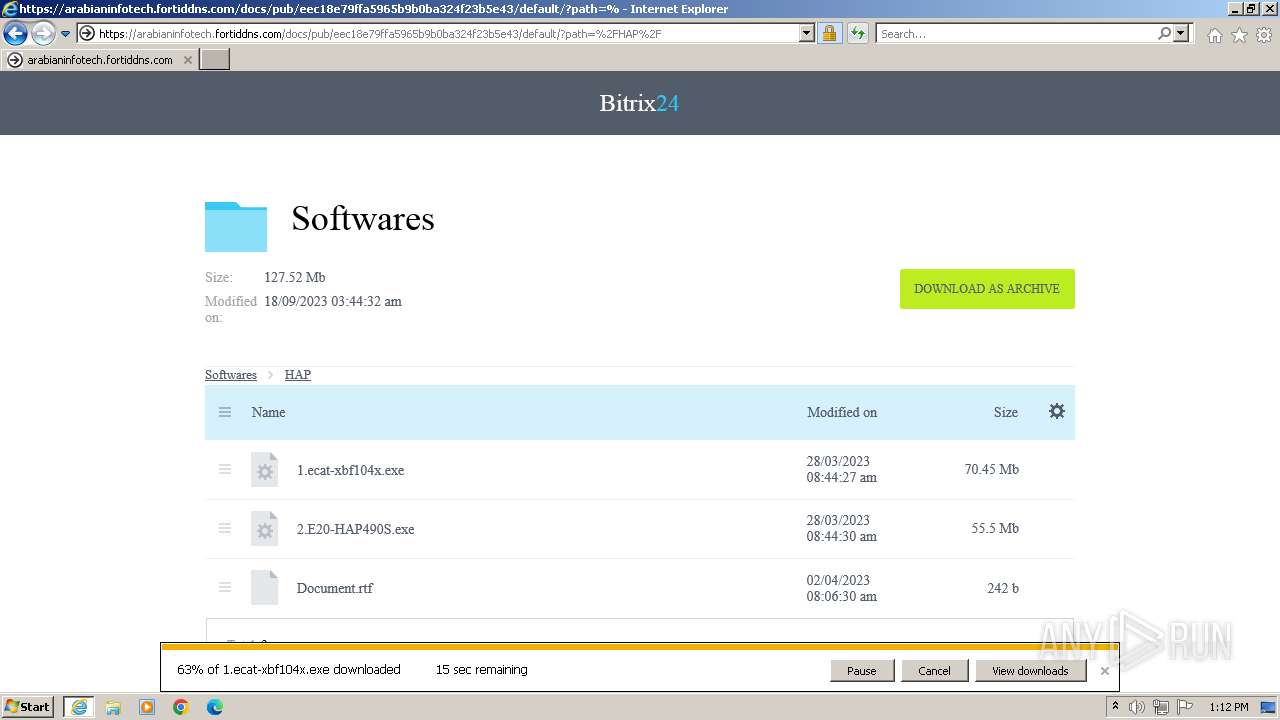
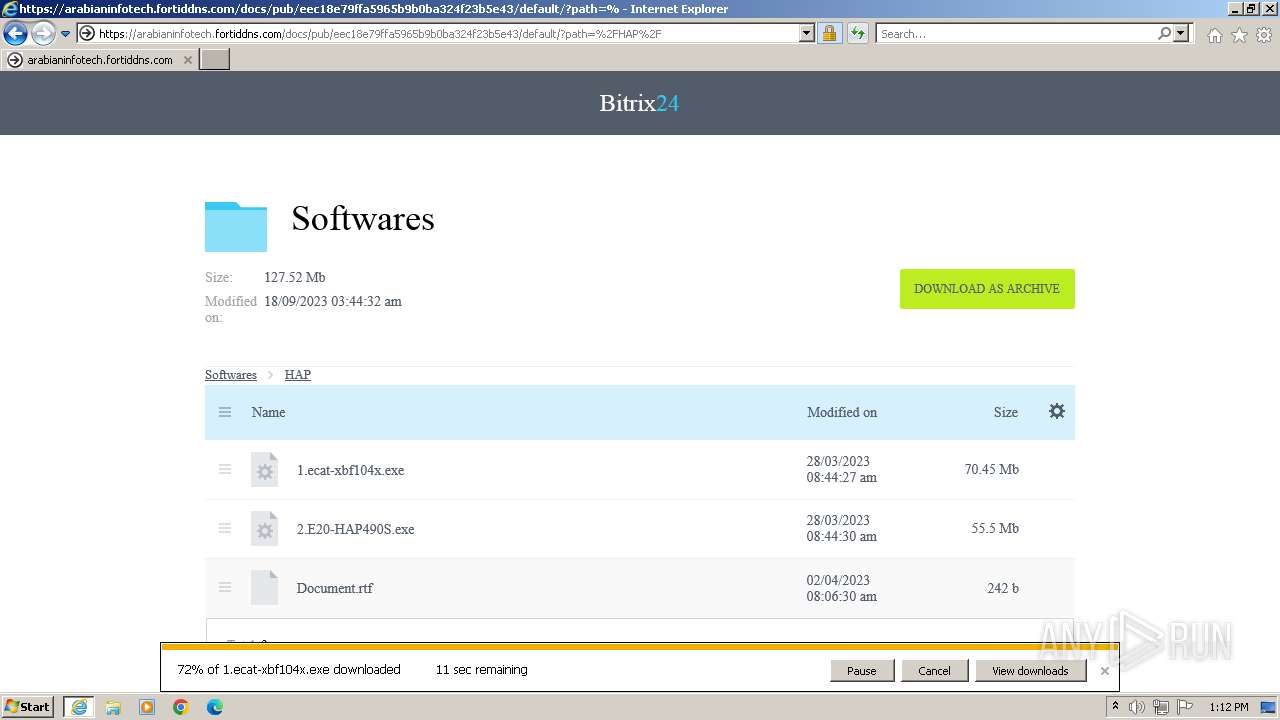
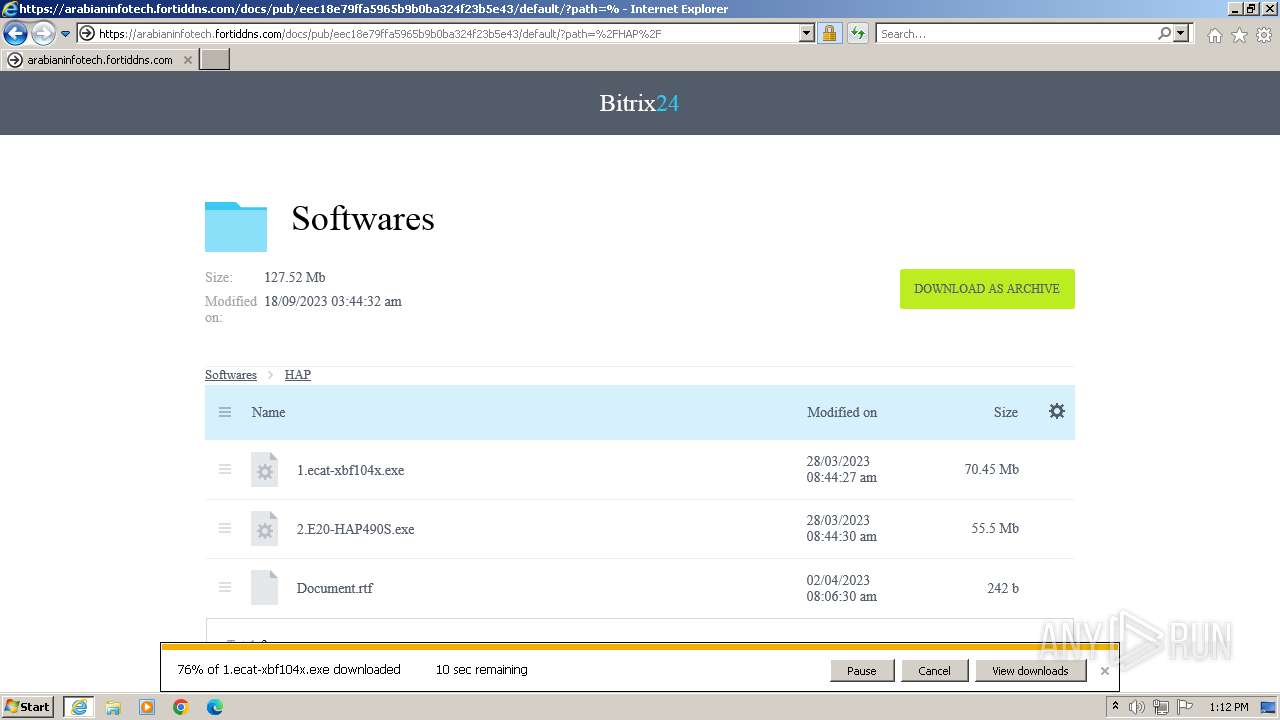
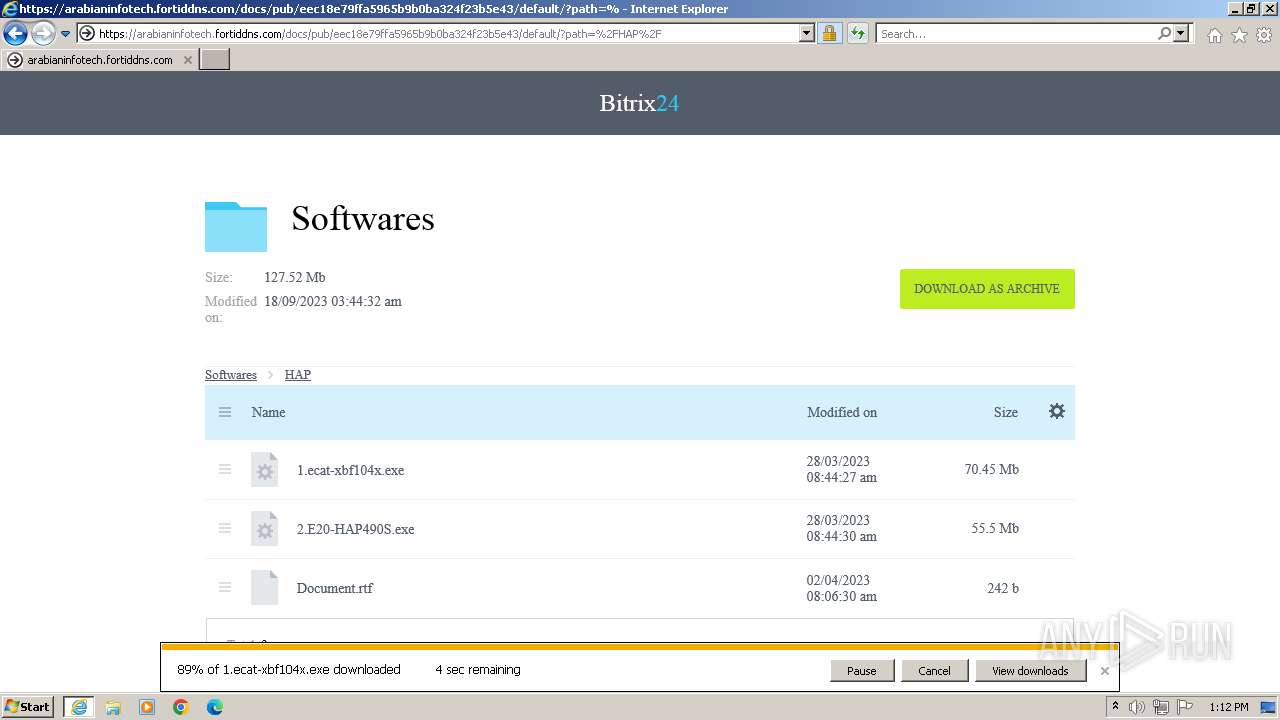
| URL: | https://arabianinfotech.fortiddns.com/~ROlah |
| Full analysis: | https://app.any.run/tasks/d59a5d08-faa1-441c-973b-74484aed4488 |
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2023, 13:11:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4EE14B2042B7A86856ACBFB71E30B49D |
| SHA1: | 90AF7B530926320585726E18F9283487B64CC5F6 |
| SHA256: | B337907132B40600B644BB7039883718CB700A4D2530576BD928969D405AB9ED |
| SSDEEP: | 3:N8fma8q7saW:2fL1tW |
MALICIOUS
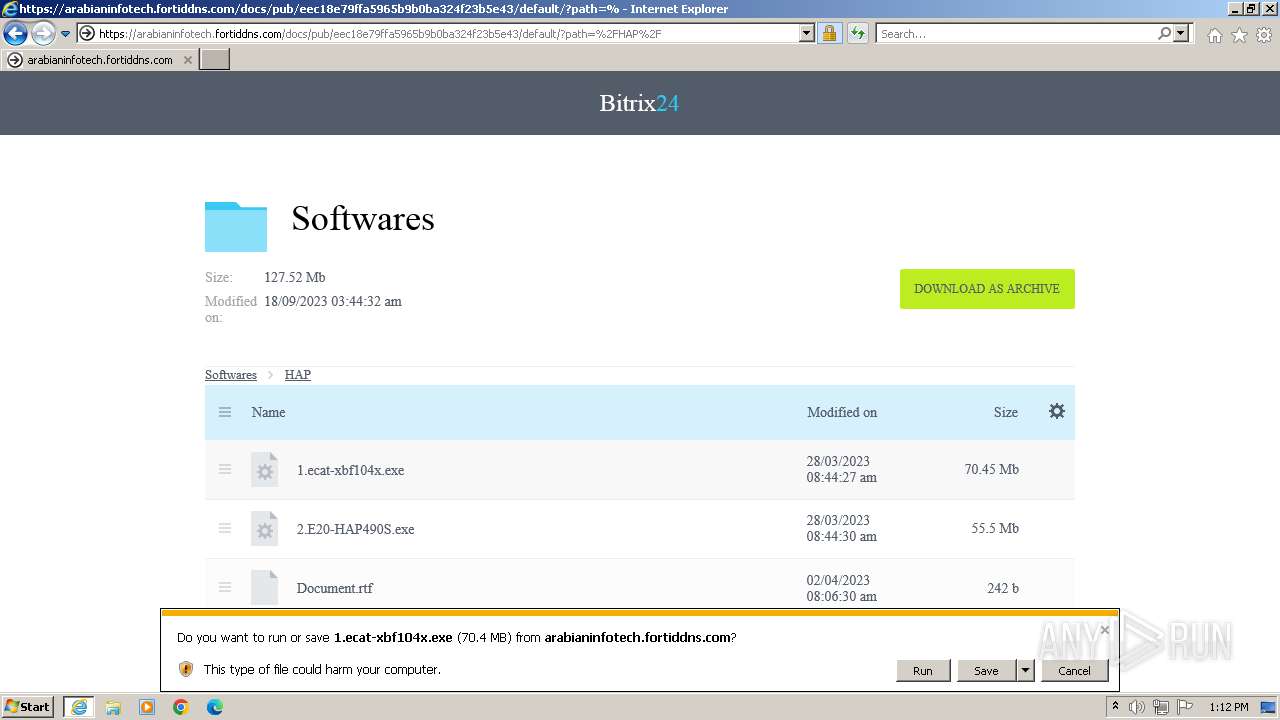
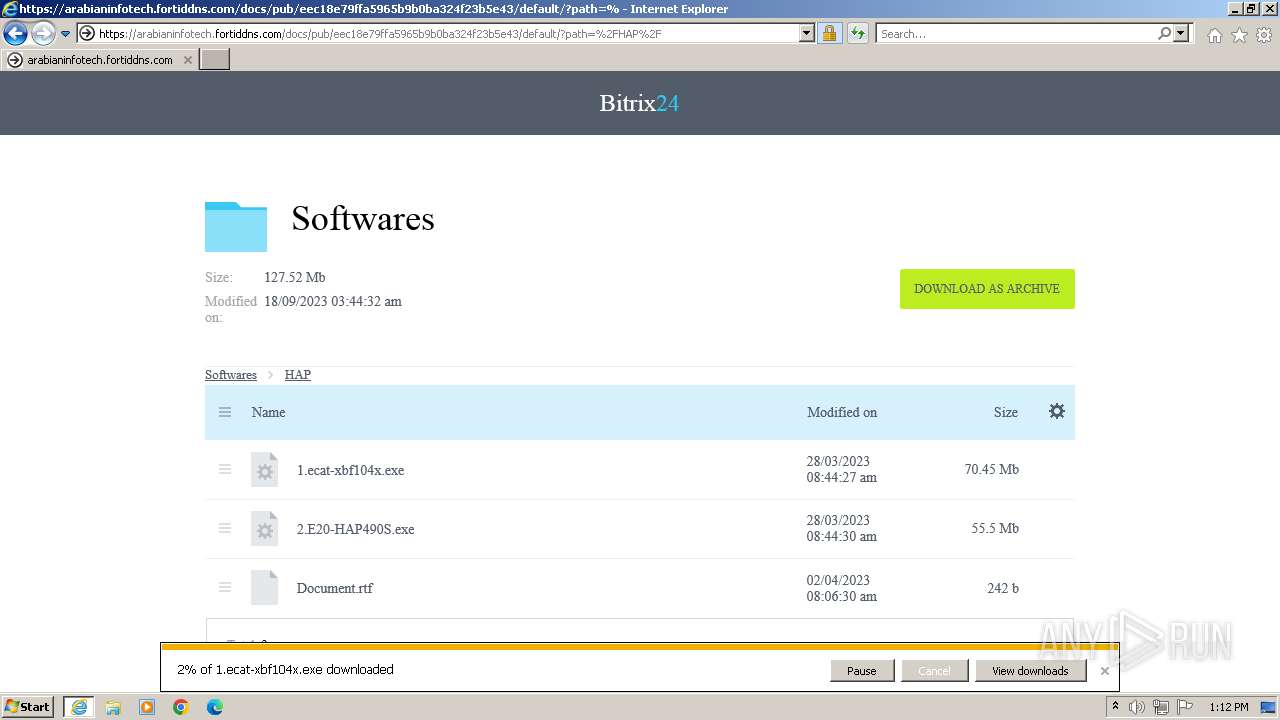
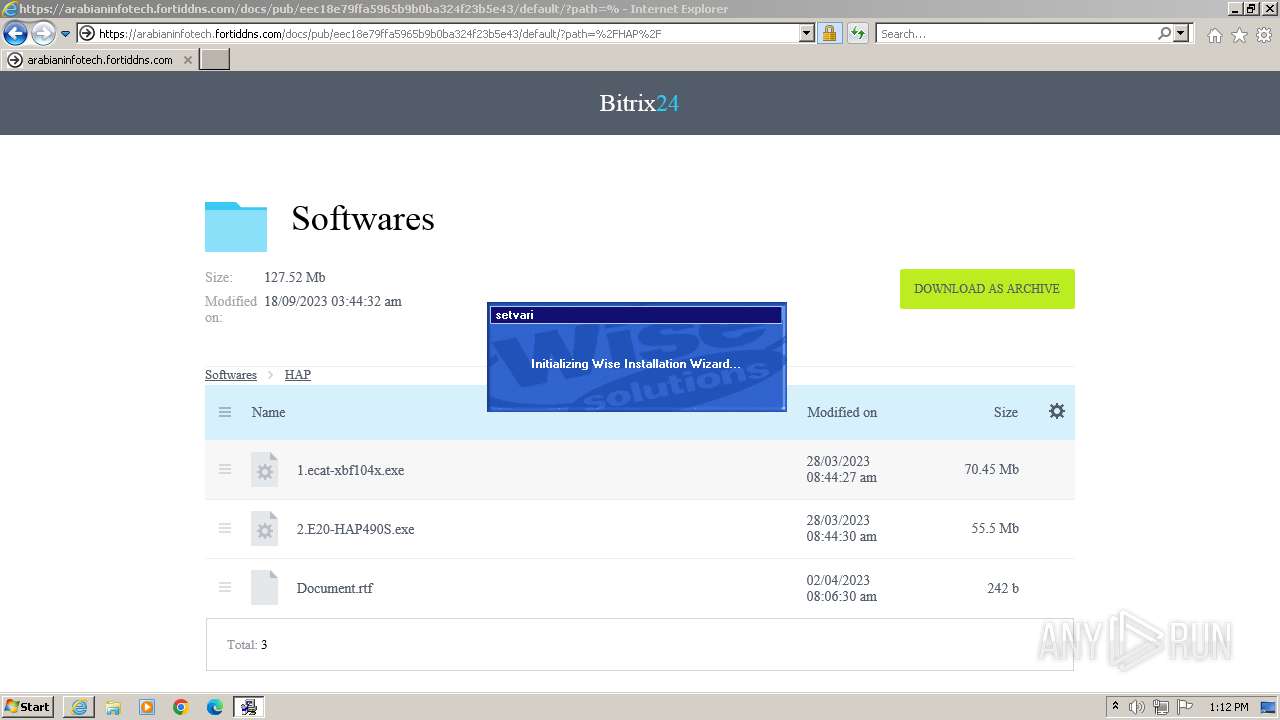
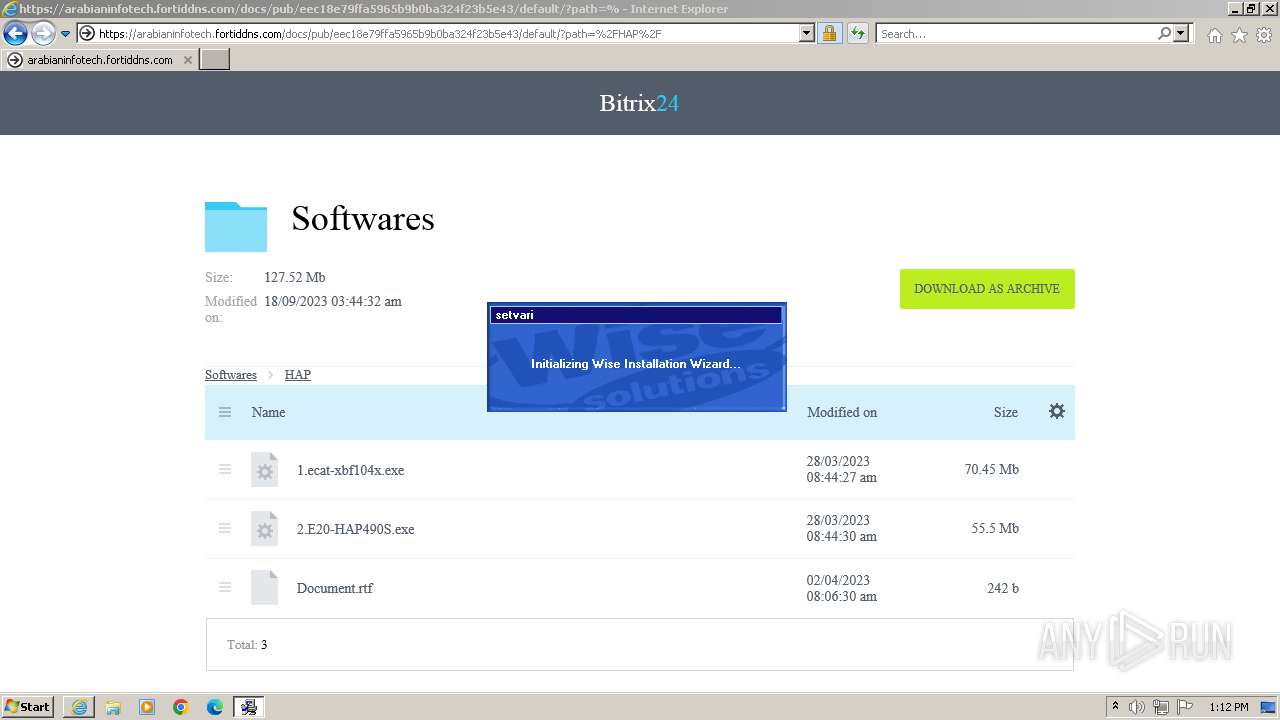
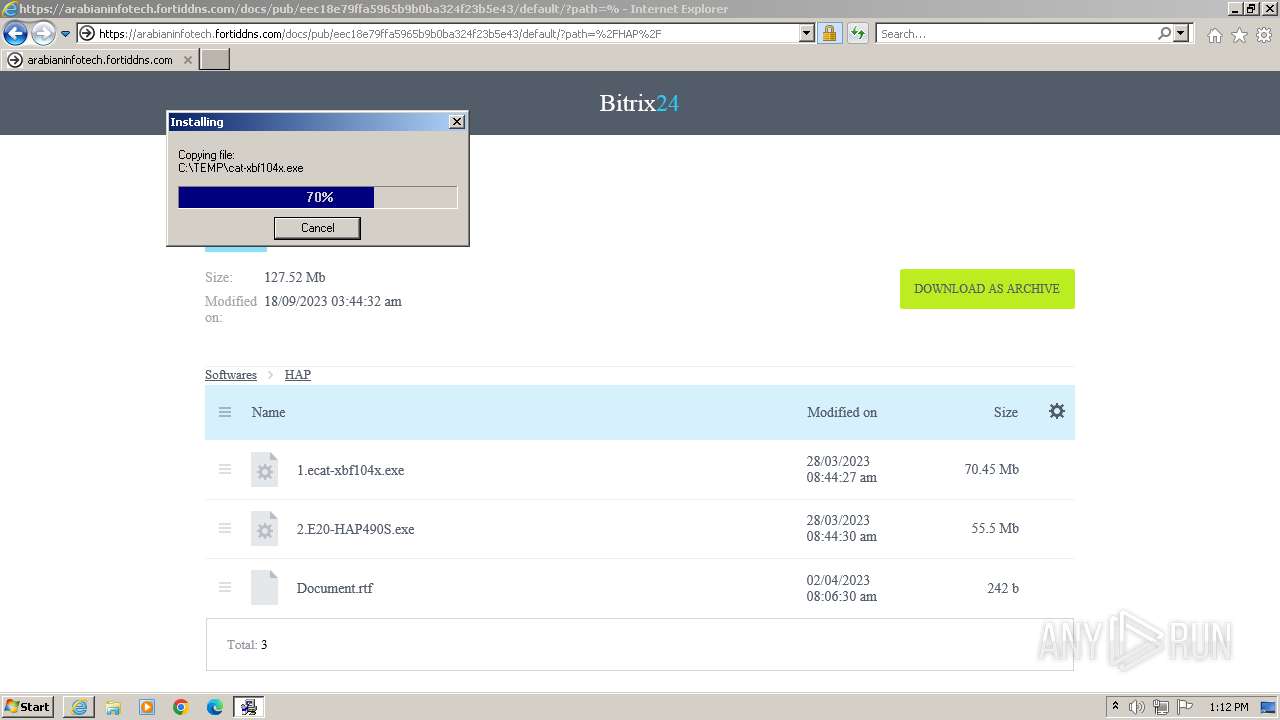
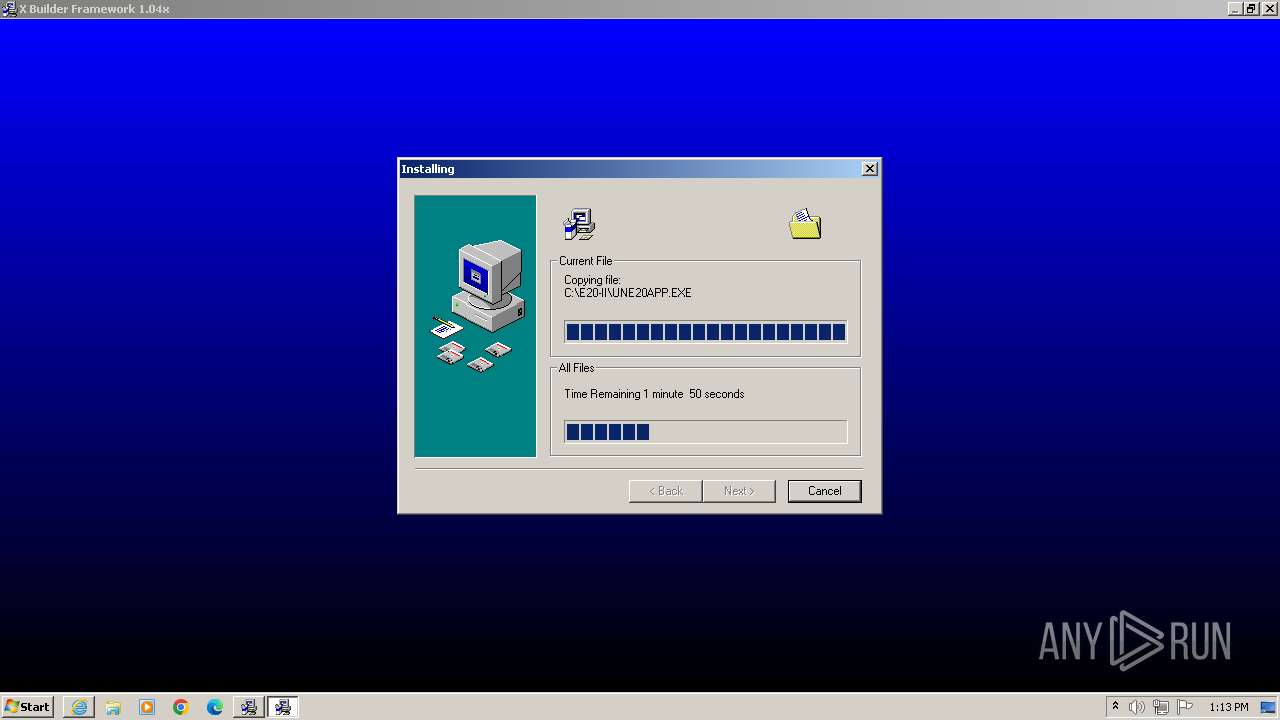
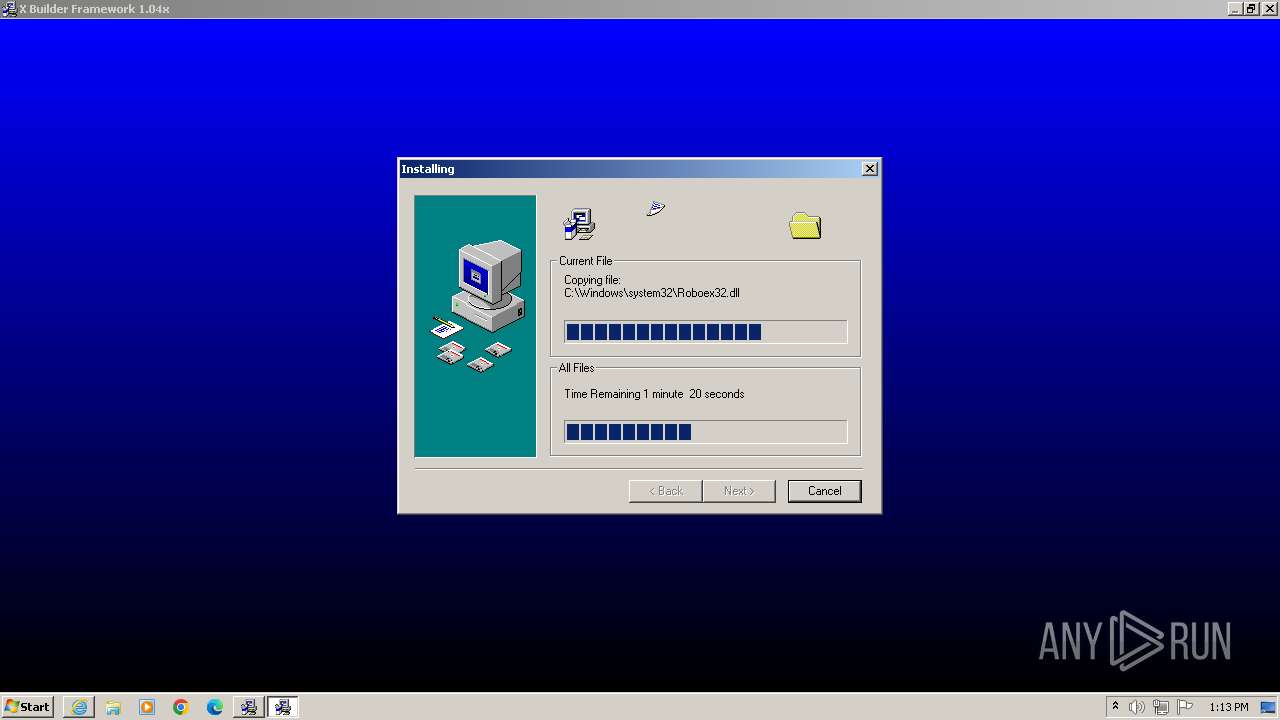
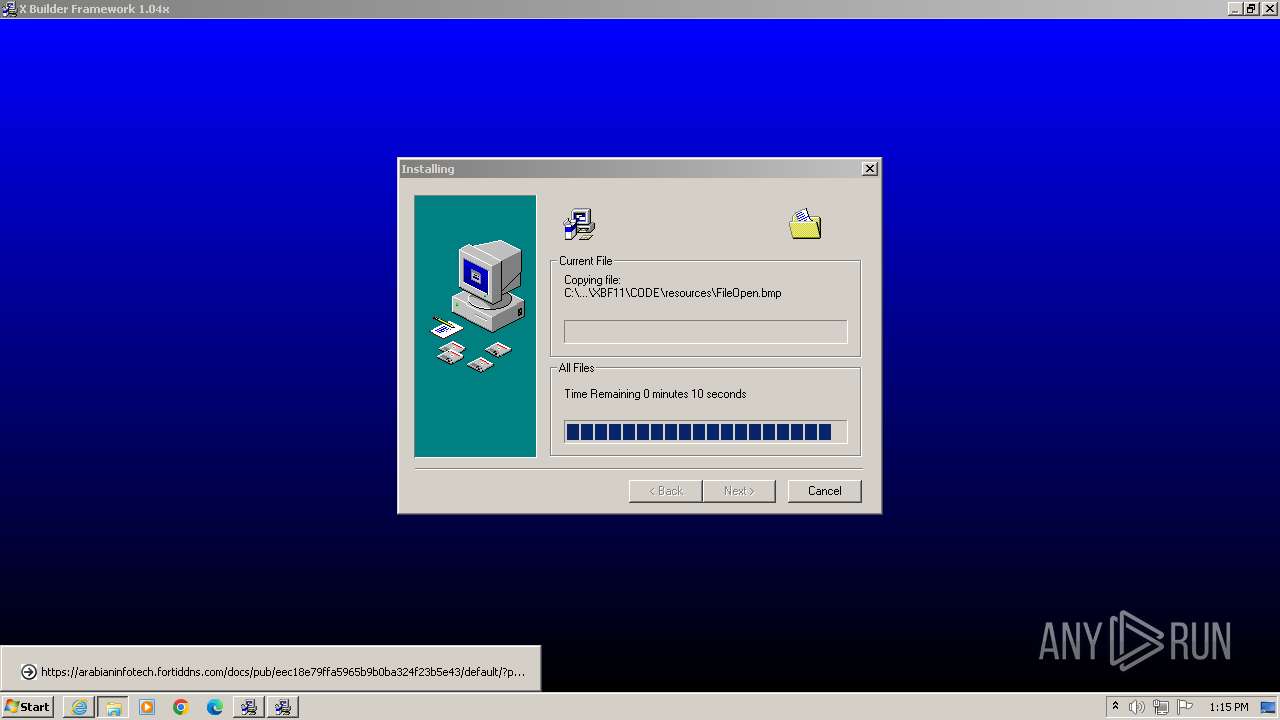
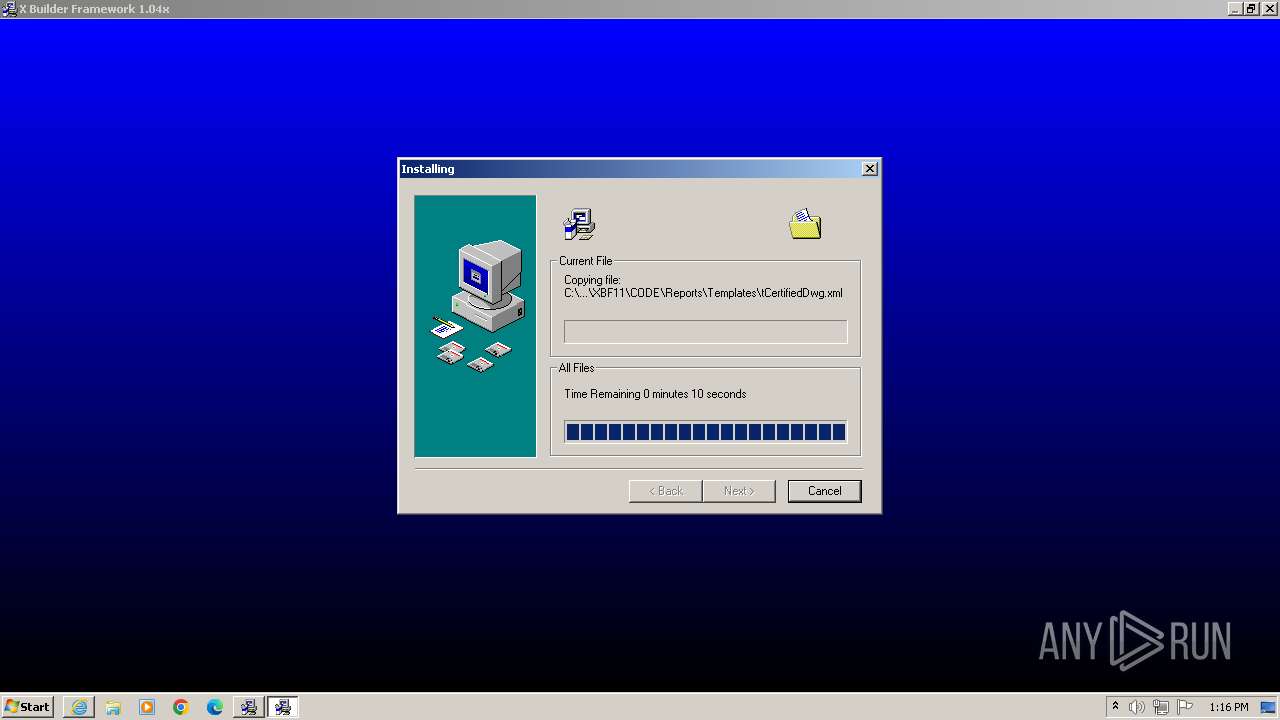
Drops the executable file immediately after the start
- 1.ecat-xbf104x.exe (PID: 3228)
- ecat-ECP211.exe (PID: 2892)
- cat-xbf104x.exe (PID: 3812)
Creates a writable file in the system directory
- cat-xbf104x.exe (PID: 3812)
- ecat-ECP211.exe (PID: 2892)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 3296)
Reads the Internet Settings
- 1.ecat-xbf104x.exe (PID: 3228)
- cat-xbf104x.exe (PID: 3812)
Starts application with an unusual extension
- ecat-ECP211.exe (PID: 2892)
- cat-xbf104x.exe (PID: 3812)
Process drops legitimate windows executable
- cat-xbf104x.exe (PID: 3812)
The process drops C-runtime libraries
- cat-xbf104x.exe (PID: 3812)
Creates/Modifies COM task schedule object
- GLJ435D.tmp (PID: 1656)
INFO
Application launched itself
- iexplore.exe (PID: 1996)
Reads the computer name
- wmpnscfg.exe (PID: 2716)
- cat-xbf104x.exe (PID: 3812)
- 1.ecat-xbf104x.exe (PID: 3228)
- ecat-ECP211.exe (PID: 2892)
- GLJE1D0.tmp (PID: 2924)
- GLJ435D.tmp (PID: 3248)
- GLJ435D.tmp (PID: 2248)
- GLJ435D.tmp (PID: 952)
- GLJ435D.tmp (PID: 1816)
- GLJ435D.tmp (PID: 3364)
- SSNDBU10.exe (PID: 3700)
- SSNDBU10.exe (PID: 2164)
- SSNDBU10.exe (PID: 1612)
- SSNDBU10.exe (PID: 1660)
- SSNDBU10.exe (PID: 2116)
- SSNDBU10.exe (PID: 2676)
- SSNDBU10.exe (PID: 732)
- GLJ435D.tmp (PID: 2504)
- GLJ435D.tmp (PID: 1700)
- GLJ435D.tmp (PID: 2236)
- GLJ435D.tmp (PID: 2552)
- SSNDBU10.exe (PID: 3788)
- GLJ435D.tmp (PID: 148)
- GLJ435D.tmp (PID: 1656)
- GLJ435D.tmp (PID: 1212)
- GLJ435D.tmp (PID: 788)
- GLJ435D.tmp (PID: 2840)
- GLJ435D.tmp (PID: 2960)
- GLJ435D.tmp (PID: 2480)
- GLJ435D.tmp (PID: 1232)
Checks supported languages
- wmpnscfg.exe (PID: 2716)
- CompatMode.exe (PID: 3536)
- ECAT271.exe (PID: 2468)
- 1.ecat-xbf104x.exe (PID: 3228)
- cat-xbf104x.exe (PID: 3812)
- FWRunning.exe (PID: 2760)
- CompatMode.exe (PID: 3724)
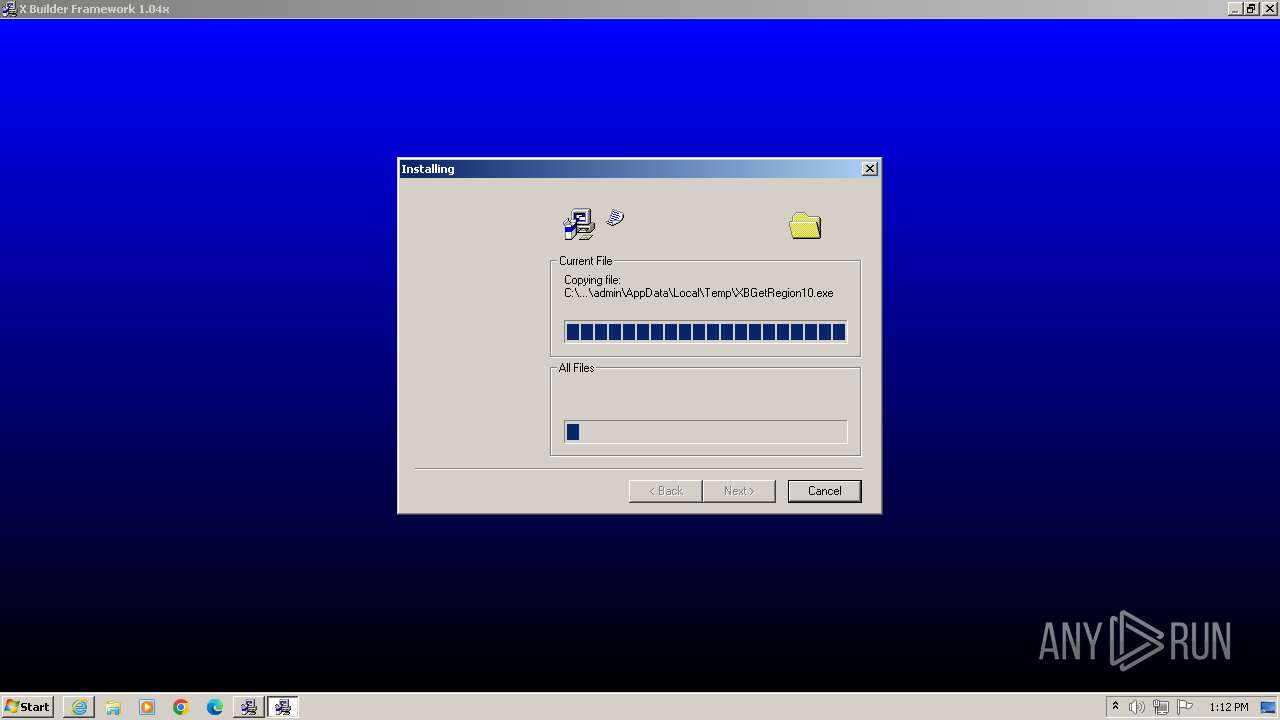
- XBGetRegion10.exe (PID: 2972)
- ecat-ECP211.exe (PID: 2892)
- GLJE1D0.tmp (PID: 2924)
- GLJ435D.tmp (PID: 3324)
- GLJ435D.tmp (PID: 3532)
- GLJ435D.tmp (PID: 3440)
- GLJ435D.tmp (PID: 2488)
- GLJ435D.tmp (PID: 284)
- GLJ435D.tmp (PID: 3256)
- GLJ435D.tmp (PID: 1436)
- GLJ435D.tmp (PID: 1888)
- GLJ435D.tmp (PID: 2368)
- GLJ435D.tmp (PID: 752)
- GLJ435D.tmp (PID: 2056)
- GLJ435D.tmp (PID: 3248)
- GLJ435D.tmp (PID: 1992)
- GLJ435D.tmp (PID: 2248)
- GLJ435D.tmp (PID: 3620)
- GLJ435D.tmp (PID: 1816)
- GLJ435D.tmp (PID: 1032)
- GLJ435D.tmp (PID: 952)
- GLJ435D.tmp (PID: 1248)
- GLJ435D.tmp (PID: 3364)
- SSNDBU10.exe (PID: 2116)
- GLJ435D.tmp (PID: 3020)
- GLJ435D.tmp (PID: 1376)
- SSNDBU10.exe (PID: 1660)
- SSNDBU10.exe (PID: 3788)
- SSNDBU10.exe (PID: 2676)
- SSNDBU10.exe (PID: 3700)
- SSNDBU10.exe (PID: 2164)
- SSNDBU10.exe (PID: 1612)
- CompatMode.exe (PID: 2836)
- GLJ435D.tmp (PID: 3072)
- GLJ435D.tmp (PID: 2504)
- GLJ435D.tmp (PID: 1700)
- GLJ435D.tmp (PID: 2176)
- GLJ435D.tmp (PID: 2236)
- GLJ435D.tmp (PID: 3828)
- GLJ435D.tmp (PID: 3904)
- SSNDBU10.exe (PID: 732)
- GLJ435D.tmp (PID: 2552)
- GLJ435D.tmp (PID: 1656)
- GLJ435D.tmp (PID: 148)
- GLJ435D.tmp (PID: 788)
- GLJ435D.tmp (PID: 1212)
- GLJ435D.tmp (PID: 924)
- GLJ435D.tmp (PID: 2960)
- GLJ435D.tmp (PID: 3004)
- GLJ435D.tmp (PID: 2840)
- GLJ435D.tmp (PID: 1128)
- GLJ435D.tmp (PID: 2480)
- CompatMode.exe (PID: 2292)
- GLJ435D.tmp (PID: 2540)
- GLJ435D.tmp (PID: 564)
- GLJ435D.tmp (PID: 2688)
- GLJ435D.tmp (PID: 1232)
- GLJ435D.tmp (PID: 2576)
- GLJ435D.tmp (PID: 2908)
- GLJ435D.tmp (PID: 1988)
- XBFTaskTool.exe (PID: 2608)
- RemovePDSG.exe (PID: 3372)
- CompatMode.exe (PID: 2928)
- XBPWUtility.exe (PID: 2196)
- CompatMode.exe (PID: 2716)
- CompatMode.exe (PID: 1760)
- XBFTaskTool.exe (PID: 3632)
- GLJ435D.tmp (PID: 2496)
- XBFTaskTool.exe (PID: 2680)
- CompatMode.exe (PID: 3452)
- CompatMode.exe (PID: 3804)
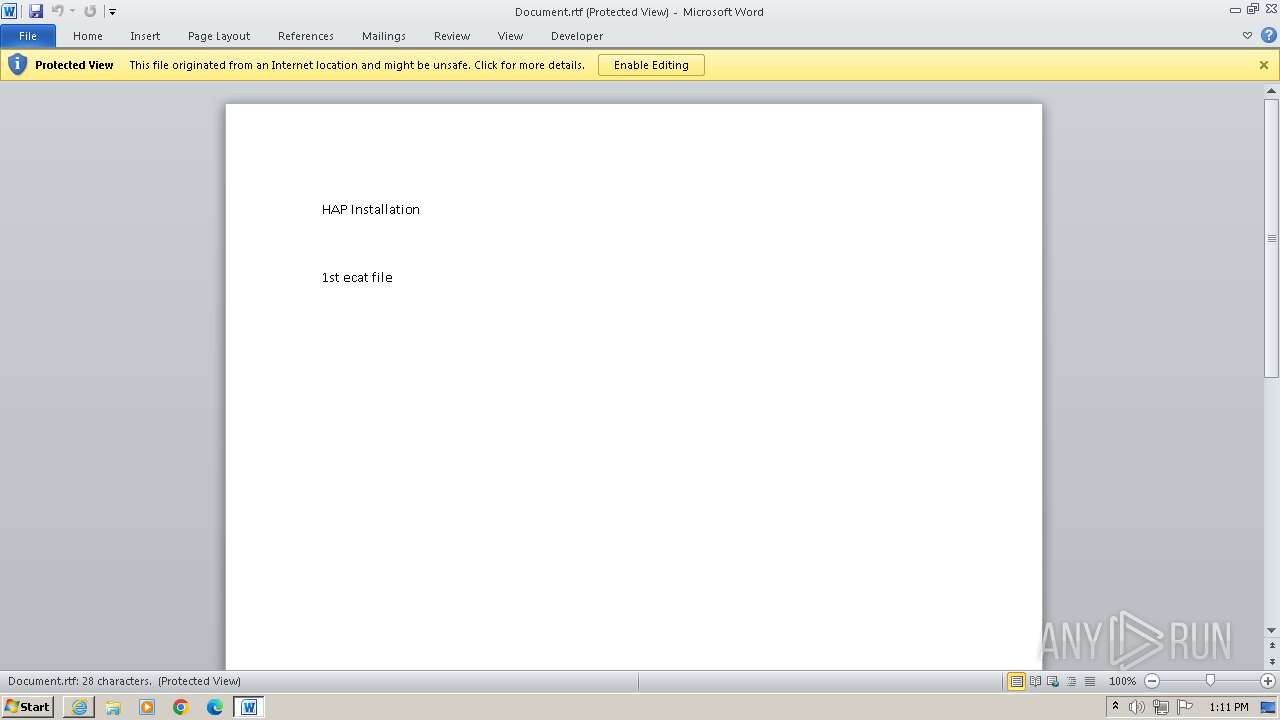
Reads Microsoft Office registry keys
- iexplore.exe (PID: 1996)
Manual execution by a user
- wmpnscfg.exe (PID: 2716)
- explorer.exe (PID: 3684)
The process uses the downloaded file
- WINWORD.EXE (PID: 3296)
- iexplore.exe (PID: 1996)
Drops the executable file immediately after the start
- iexplore.exe (PID: 2632)
Create files in a temporary directory
- 1.ecat-xbf104x.exe (PID: 3228)
- cat-xbf104x.exe (PID: 3812)
- ecat-ECP211.exe (PID: 2892)
- SSNDBU10.exe (PID: 2164)
- SSNDBU10.exe (PID: 1612)
- SSNDBU10.exe (PID: 1660)
- SSNDBU10.exe (PID: 3788)
- SSNDBU10.exe (PID: 2116)
- SSNDBU10.exe (PID: 2676)
- SSNDBU10.exe (PID: 3700)
- SSNDBU10.exe (PID: 732)
- GLJ435D.tmp (PID: 1988)
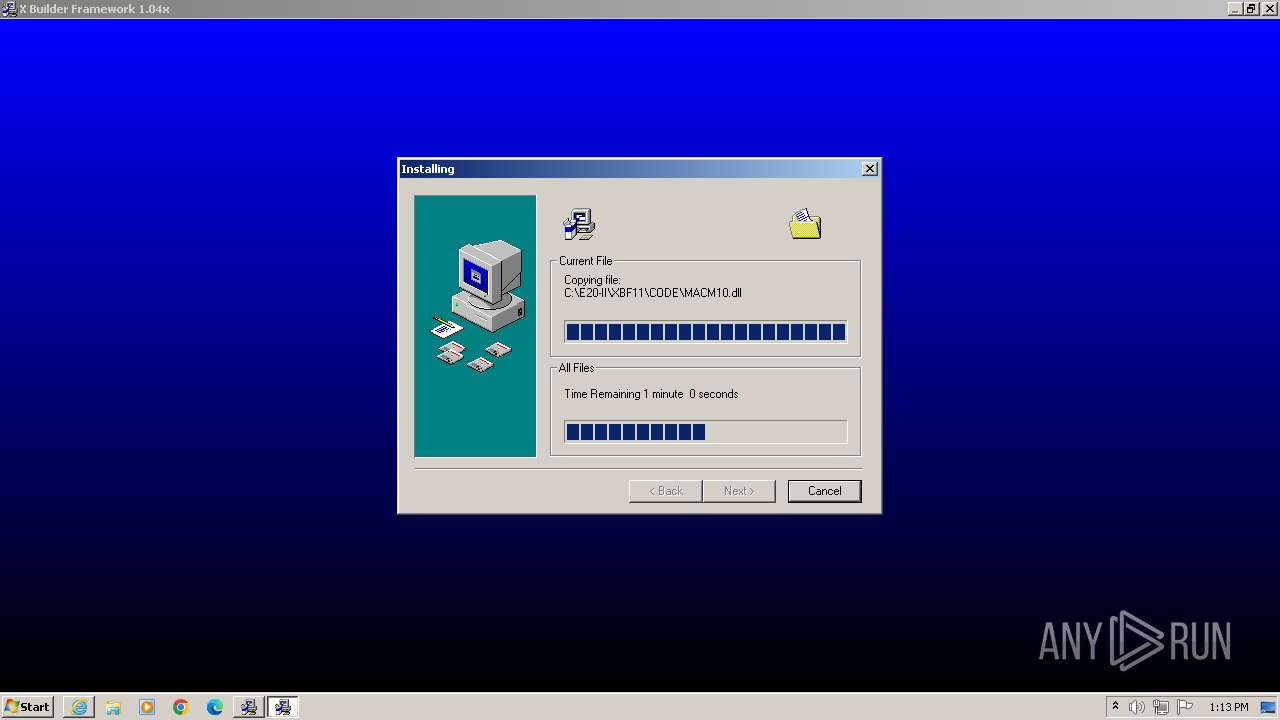
Creates files in the program directory
- cat-xbf104x.exe (PID: 3812)
Reads mouse settings
- GLJ435D.tmp (PID: 1656)
- GLJ435D.tmp (PID: 788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
129
Monitored processes
85
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp" C:\Windows\System32\MSINET.OCX | C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp | cat-xbf104x.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 284 | "C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp" C:\Windows\System32\Grid32.ocx | C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp | cat-xbf104x.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 564 | "C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp" C:\Windows\System32\wRTF2PDF01.dll | C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp | cat-xbf104x.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 732 | "C:\E20-II\SSNDBU10.exe" C:\E20-II\CSI11INS.INI | C:\E20-II\SSNDBU10.exe | cat-xbf104x.exe | ||||||||||||
User: admin Company: Carrier Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 752 | "C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp" C:\Windows\System32\Dzip32.dll | C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp | cat-xbf104x.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
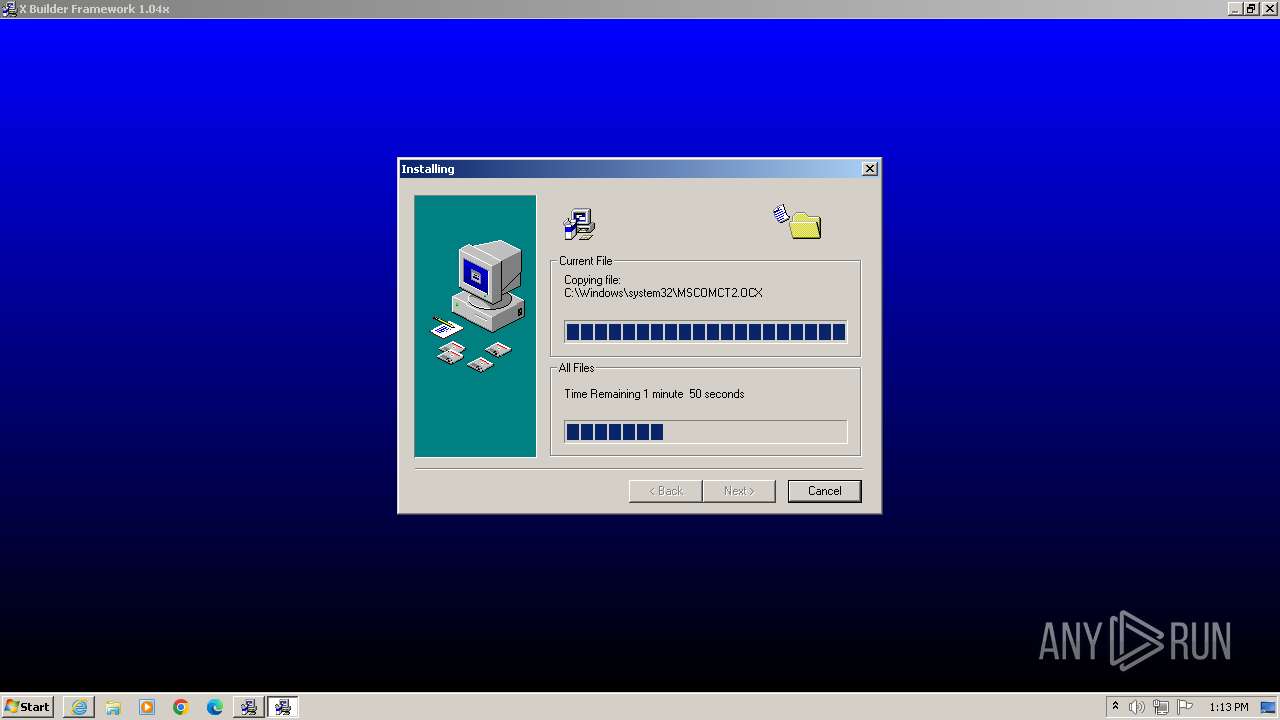
| 788 | "C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp" C:\Windows\System32\MSCOMCT2.OCX | C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp | cat-xbf104x.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 924 | "C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp" C:\Windows\System32\msxml3a.dll | C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp | cat-xbf104x.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 952 | "C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp" C:\Windows\System32\COMCT232.OCX | C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp | cat-xbf104x.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 988 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1032 | "C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp" C:\Windows\System32\Msjter32.dll | C:\Users\admin\AppData\Local\Temp\GLJ435D.tmp | cat-xbf104x.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
Total events
29 354
Read events
29 013
Write events
189
Delete events
152
Modification events
| (PID) Process: | (1996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1 086
Suspicious files
1 055
Text files
855
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2632 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\54C62B182F5BF07FA8427C07B0A3AAF8_786EA6C36BF7ABFF201B638497282D19 | binary | |
MD5:1731B881960AC78FBBC0FFE5ACDCD598 | SHA256:E8C9CB8012AA47F312FF30B97CD254470E1494D511EE1DB9E31FE7722D68AA7C | |||
| 2632 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CE7B026C819922EDB9B7ED78605E20A3_AF7F10BA33CEEF74214EEC8D707EB0CD | binary | |
MD5:224CCD57E01039272C5054629F5A4330 | SHA256:DAC048C2D1E28843EF083116B9E6AC915E960D44634AD5C903FDB8582F5989B2 | |||
| 2632 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:637B37566CF15CD6E6D43092AA2AA25E | SHA256:996D419731304DADBC20F8A3647DE3414B140ECC31FC7745C3DA0974AA923B2F | |||
| 2632 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\ui.design-tokens.min[1].css | text | |
MD5:8178992021C7160F587A2BFB4EE68011 | SHA256:82B3457E90BC5418C672127C440E8A8A9BDC72CBCDE7672ADC98BA94A7CE0334 | |||
| 2632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\kernel_ui_notification_v1[1].css | text | |
MD5:B8F681C8712865BF66D858192F28276E | SHA256:703F8B75727E28D225519AB0FAD531BCD731CBF7145C3CC2434D2CBA90DF936D | |||
| 2632 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\54C62B182F5BF07FA8427C07B0A3AAF8_786EA6C36BF7ABFF201B638497282D19 | binary | |
MD5:A8E86E44B41C4ED02AA16547FE7E7241 | SHA256:7F4350585AC67F5A6FB743369739A60F42553D137D0A7D3023824FEE2BEAA6C8 | |||
| 2632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\bitrix24-design-tokens.min[1].css | text | |
MD5:44160F099A56298219CA37C452F5D1A8 | SHA256:95A4C11BE57D915F3E67D6037E3A2E4AFA21CED834958A0AEE7AE5116D8FE33A | |||
| 2632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\main.popup.bundle.min[1].css | text | |
MD5:5881391F45CAFD2FC858E3F14E54B9F4 | SHA256:0E9B826DEA54F30650091A0547B60614C8D8C90203724AAC05F07461C68C234C | |||
| 2632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\default[1].htm | html | |
MD5:BB24E88B57FD5BCBF0466AE233D43D93 | SHA256:C6BE65F079E43DE63775010C185437CA8E22E29D6BC97AB9FEB0E5D4FBF4D5BD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
31
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2632 | iexplore.exe | GET | 200 | 184.24.77.202:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?282a5f2988aaef25 | unknown | compressed | 4.66 Kb | unknown |
1996 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
2632 | iexplore.exe | GET | 200 | 100.24.223.135:80 | http://ocsps.ssl.com/MEkwRzBFMEMwQTAJBgUrDgMCGgUABBQMDtATfnJO6JAXDQoHl8pAaJdhTQQU3QQJB6L1en1SUxKSle44gCUNplkCCAmX7RCdHwf8 | unknown | binary | 719 b | unknown |
2632 | iexplore.exe | GET | 200 | 184.24.77.202:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b27ea2cbe4dcc735 | unknown | compressed | 4.66 Kb | unknown |
2632 | iexplore.exe | GET | 200 | 100.24.223.135:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTUkpS%2BK0oZhSMx%2FmmCZ76UqdjUxQQUJhR%2B4NzXpvfi1AQn32HxwuznMsoCEEzIi4BfbVSq%2Fo8GLSr%2FMe4%3D | unknown | binary | 1.77 Kb | unknown |
1996 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 88.221.110.106:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a7e79e1b6451585f | unknown | compressed | 65.2 Kb | unknown |
1996 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
1996 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
1996 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
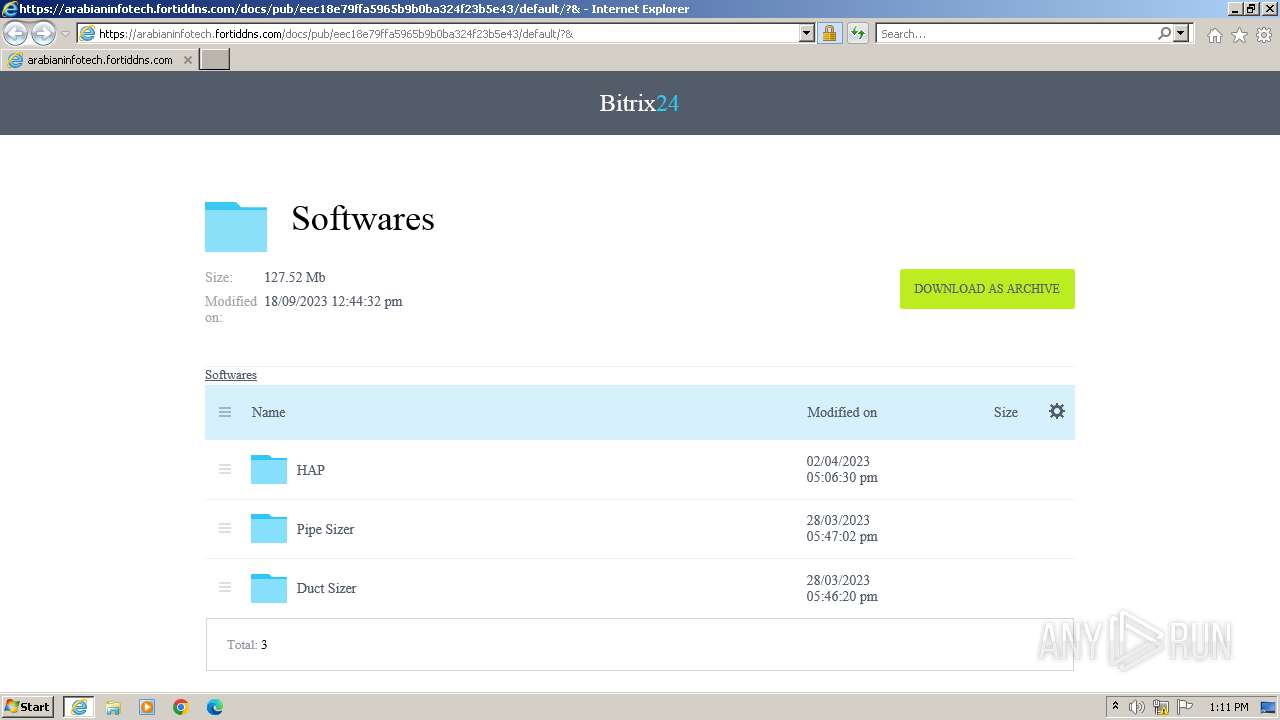
2632 | iexplore.exe | 86.98.52.11:443 | arabianinfotech.fortiddns.com | Emirates Telecommunications Corporation | AE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2632 | iexplore.exe | 184.24.77.202:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2632 | iexplore.exe | 100.24.223.135:80 | ocsps.ssl.com | AMAZON-AES | US | unknown |
1996 | iexplore.exe | 86.98.52.11:443 | arabianinfotech.fortiddns.com | Emirates Telecommunications Corporation | AE | unknown |
1996 | iexplore.exe | 92.123.104.33:443 | www.bing.com | Akamai International B.V. | DE | unknown |
1996 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
arabianinfotech.fortiddns.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsps.ssl.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
cat-xbf104x.exe | FTH: (3812): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
FWRunning.exe | FTH: (2760): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
XBGetRegion10.exe | FTH: (2972): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
CompatMode.exe | FTH: (3724): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
ecat-ECP211.exe | FTH: (2892): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
GLJE1D0.tmp | FTH: (2924): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
GLJ435D.tmp | FTH: (3248): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
GLJ435D.tmp | FTH: (1992): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
GLJ435D.tmp | FTH: (3324): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
GLJ435D.tmp | FTH: (3532): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|