| download: | Nitro_generator.exe |
| Full analysis: | https://app.any.run/tasks/f98977b7-400d-4797-82d1-7dfb31fa41dc |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2021, 15:39:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | E8254BAC078A11EF2939DC2833D7CDFB |
| SHA1: | 5A528673F24393536CE4D83A0A727813866AB89A |
| SHA256: | B33040C7C87DE8A1303BB323ADD1E768F3FEAFD05E3B208282D23E4402EE5418 |
| SSDEEP: | 49152:ksmhnqAs9pJc0dnKh+Q0N1rs+vIUSg+6+8ohnRh1Na1OKM6nYAKhFQpSH3Oh5gx9:WqXpy05Q0N1rsYSZ6BoXh1kkypSH3OhE |
MALICIOUS
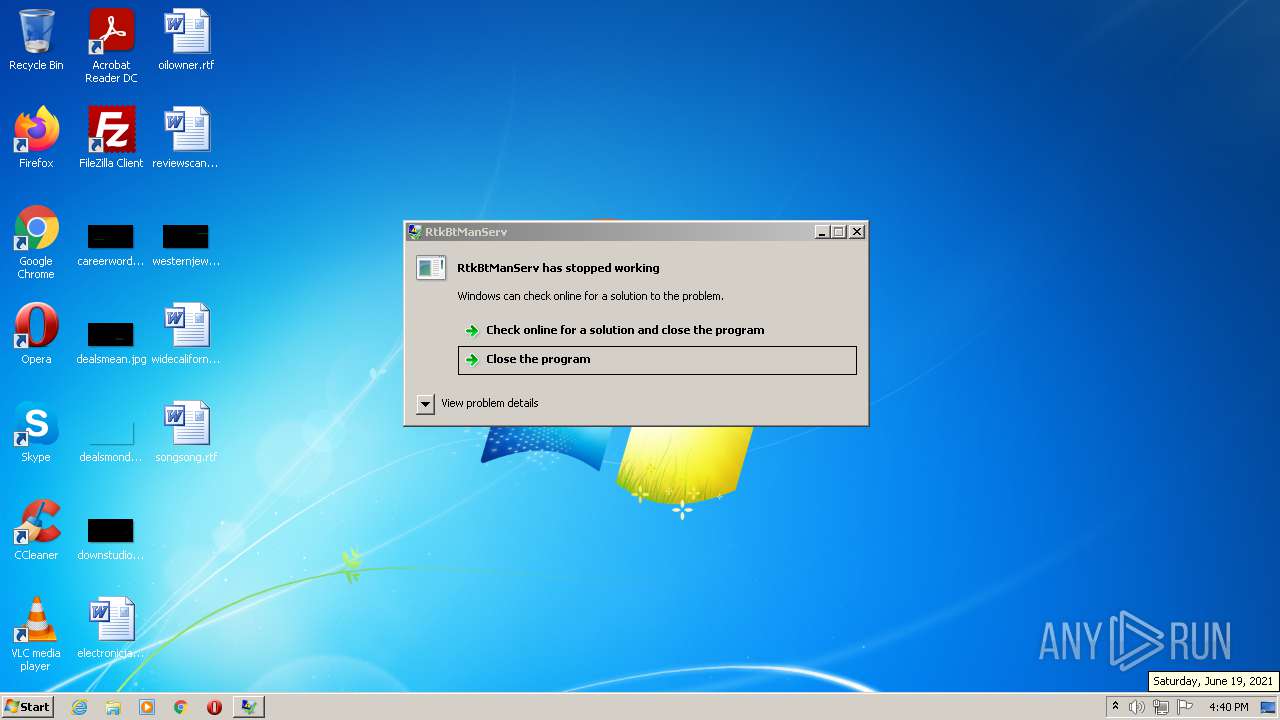
Application was dropped or rewritten from another process
- RtkBtManServ.exe (PID: 1676)
Actions looks like stealing of personal data
- RtkBtManServ.exe (PID: 1676)
Steals credentials from Web Browsers
- RtkBtManServ.exe (PID: 1676)
SUSPICIOUS
Executable content was dropped or overwritten
- Nitro_generator.exe (PID: 2720)
- RtkBtManServ.exe (PID: 1676)
Checks supported languages
- RtkBtManServ.exe (PID: 1676)
- Nitro_generator.exe (PID: 2720)
Reads the computer name
- Nitro_generator.exe (PID: 2720)
- RtkBtManServ.exe (PID: 1676)
Reads the cookies of Mozilla Firefox
- RtkBtManServ.exe (PID: 1676)
Drops a file that was compiled in debug mode
- RtkBtManServ.exe (PID: 1676)
Reads Environment values
- RtkBtManServ.exe (PID: 1676)
INFO
Reads settings of System Certificates
- RtkBtManServ.exe (PID: 1676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| OriginalFileName: | Obfuscated Name.exe |
| LegalCopyright: | |
| InternalName: | Obfuscated Name.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x2d86ae |
| UninitializedDataSize: | - |
| InitializedDataSize: | 26624 |
| CodeSize: | 2975744 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| TimeStamp: | 2021:06:10 17:40:45+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jun-2021 15:40:45 |
| Debug artifacts: |
|
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | Obfuscated Name.exe |
| LegalCopyright: | - |
| OriginalFilename: | Obfuscated Name.exe |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 10-Jun-2021 15:40:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x002D66B4 | 0x002D6800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.99849 |
.rsrc | 0x002DA000 | 0x00006410 | 0x00006600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.72856 |
.reloc | 0x002E2000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 7.88702 | 20325 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 7.82872 | 1819 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.76403 | 1200 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 7.50347 | 640 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.3141 | 62 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1676 | "C:\Users\admin\AppData\Local\Temp\RtkBtManServ.exe" ZhXl39BlhP84+Y4kurA8wpehxxqA0X22IMYZ6Vpiqs5YhQylARSwH1J093EJWN5d/9SIrR4Drk+REZikiTUDlVWoqsYKxQYueVA5fmJs7AKhnvH5GYcRM9TV0aesPT5L30V4DloJDKloFQ2rXXuuM/lB9FVgk4KfnS4bk7YcQvA= | C:\Users\admin\AppData\Local\Temp\RtkBtManServ.exe | Nitro_generator.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: RtkBtManServ Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2720 | "C:\Users\admin\AppData\Local\Temp\Nitro_generator.exe" | C:\Users\admin\AppData\Local\Temp\Nitro_generator.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
3 854
Read events
3 822
Write events
32
Delete events
0
Modification events
| (PID) Process: | (2720) Nitro_generator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2720) Nitro_generator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2720) Nitro_generator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2720) Nitro_generator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1676) RtkBtManServ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RtkBtManServ_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1676) RtkBtManServ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RtkBtManServ_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1676) RtkBtManServ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RtkBtManServ_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1676) RtkBtManServ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RtkBtManServ_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1676) RtkBtManServ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RtkBtManServ_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1676) RtkBtManServ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RtkBtManServ_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
7
Suspicious files
18
Text files
6
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1676 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\winhlp32.exe | executable | |
MD5:A776E68F497C996788B406A3DC5089EB | SHA256:071E26DDF5323DD9ED6671BCDE89DF73D78BAC2336070E6CB9E3E4B93BDE78D1 | |||
| 1676 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\xwizard.exe | executable | |
MD5:DF991217F1CFADD9ACFA56F878DA5EE7 | SHA256:DEB1246347CE88E8CDD63A233A64BC2090B839F2D933A3097A2FD8FD913C4112 | |||
| 1676 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\xwizard.cfg | text | |
MD5:AE8EED5A6B1470AEC0E7FECE8B0669EF | SHA256:3F6CA2BC068C8436044DAAB867F8FF8F75060048B29882CB2AC9FDEF1800DF9E | |||
| 1676 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\costura.costura.dll.compressed | binary | |
MD5:9AB99399CB17964E3E30B7DDEB6BB8B9 | SHA256:BDFED3E39A17DBC95D43FC5141904414A62E8B459F338F65A2F1C3D1FACDDD2F | |||
| 1676 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\bfsvc.exe | executable | |
MD5:899D3ED011EB58459B8A4FC2B81F0924 | SHA256:5E3F311AE67F046B56435067BCDD39FBF836FA0421FBC8C8B0E43E8E47524954 | |||
| 2720 | Nitro_generator.exe | C:\Users\admin\AppData\Local\Temp\RtkBtManServ.exe | executable | |
MD5:88AB0BB59B0B20816A833BA91C1606D3 | SHA256:F4FB42C8312A6002A8783E2A1AB4571EB89E92CD192B1A21E8C4582205C37312 | |||
| 1676 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\snuvcdsm.exe | executable | |
MD5:053778713819BEAB3DF309DF472787CD | SHA256:F999357A17E672E87FBED66D14BA2BEBD6FB04E058A1AAE0F0FDC49A797F58FE | |||
| 1676 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\hh.exe | executable | |
MD5:4D4C98ECA32B14AEB074DB34CD0881E4 | SHA256:4182172A01BDFC08C5CF7E8652F7D9D81858345A770E2B6B507840E4C1C7764F | |||
| 1676 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\costura.discord.net.core.dll.compressed | binary | |
MD5:4104898CA34FEBB688ED63812EFE8CF4 | SHA256:265850B1887F252E04C54F81EF872587B3CFD66B0D708621D2520BC6D4BBDCAC | |||
| 1676 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\splwow64.exe | executable | |
MD5:0D8360781E488E250587A17FBEFA646C | SHA256:EBFF7D07EFDA7245192CE6ECD7767578152B515B510C887CA2880A2566071F64 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1676 | RtkBtManServ.exe | 162.159.136.232:443 | discord.com | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
itroublvehacker.gq |
| whitelisted |
discord.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |