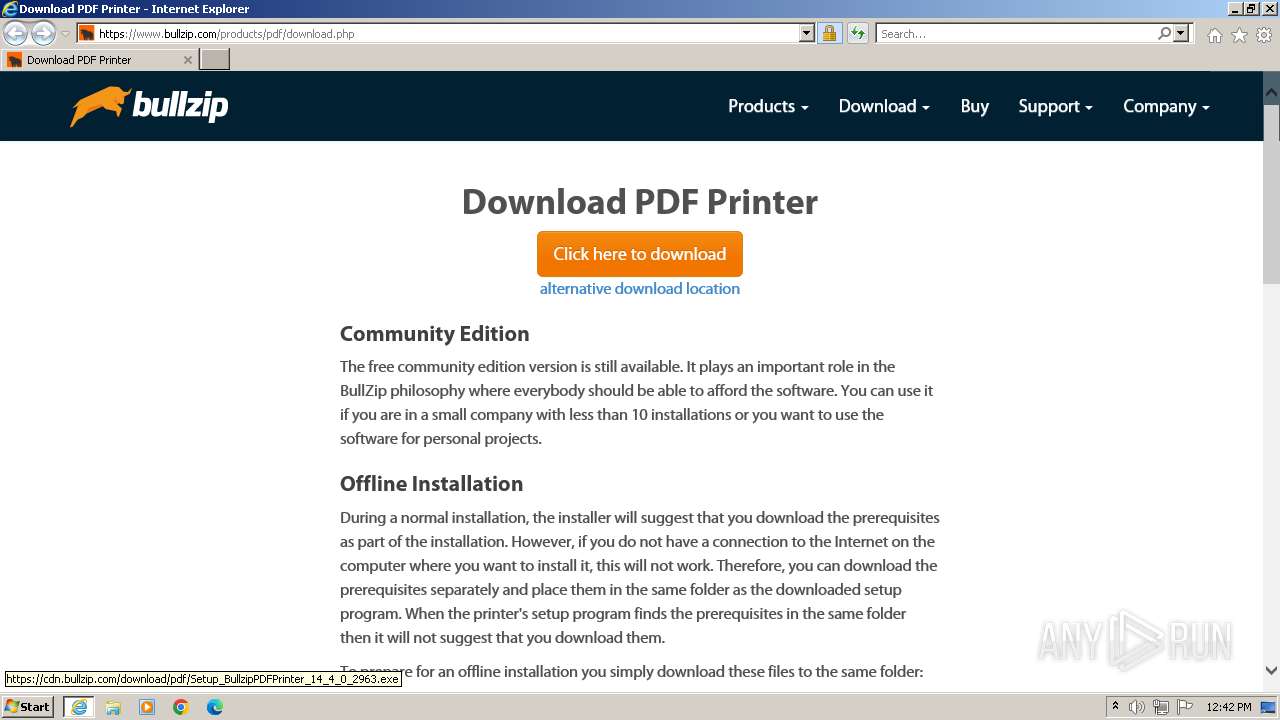
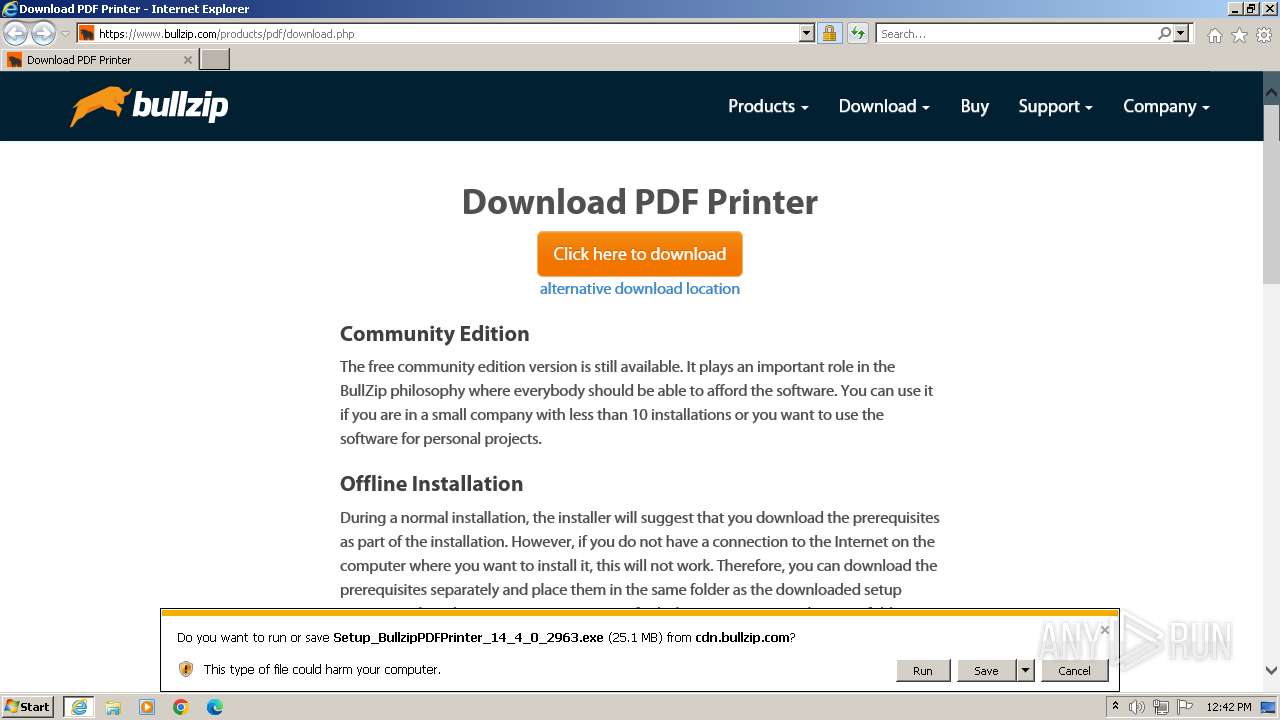
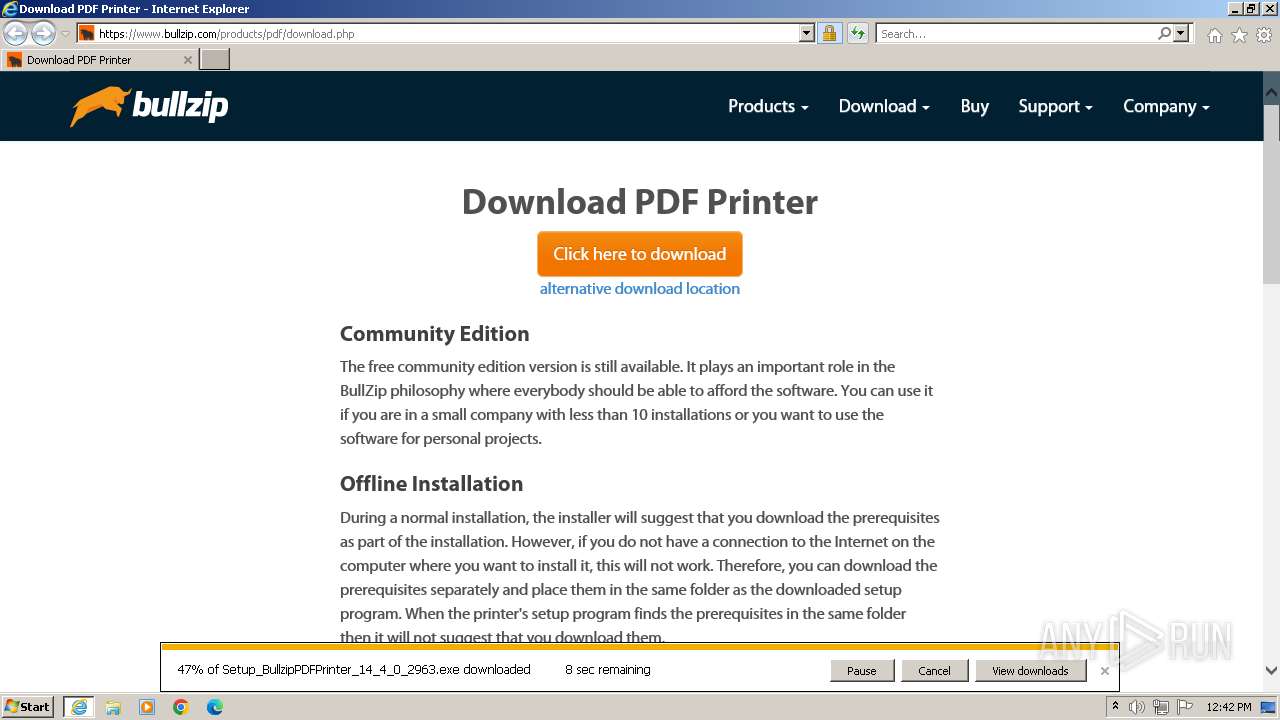
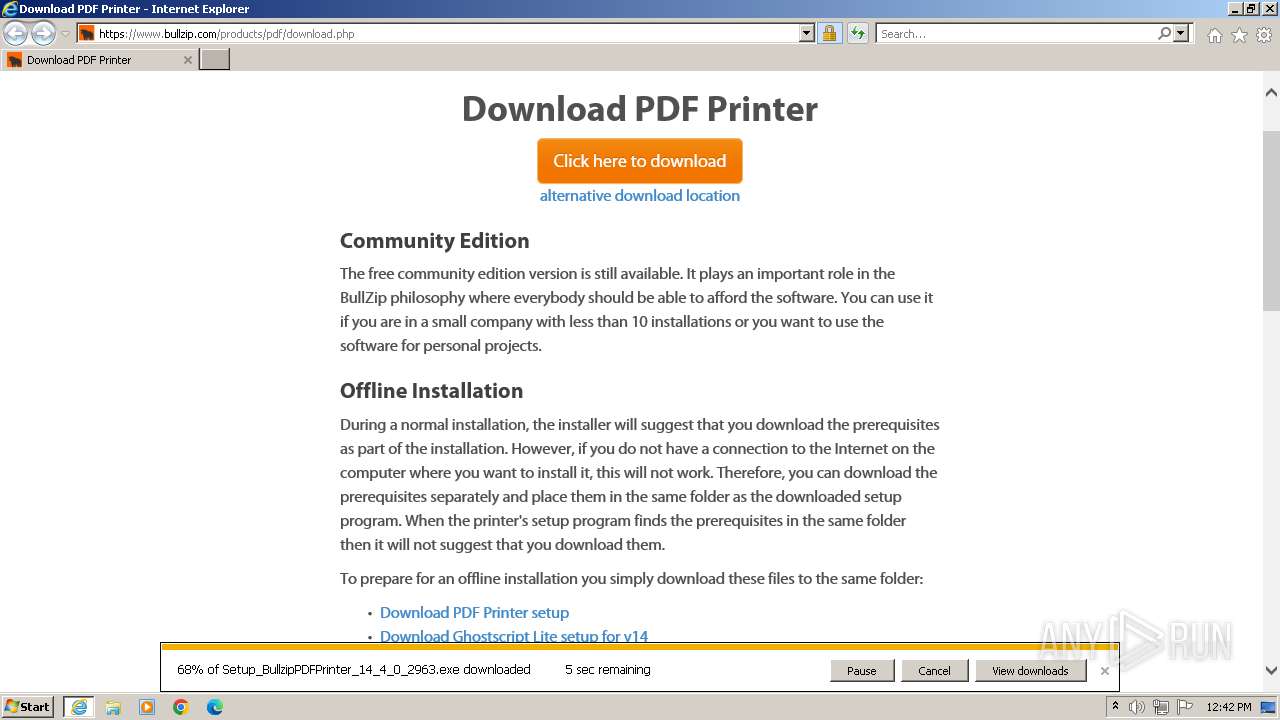
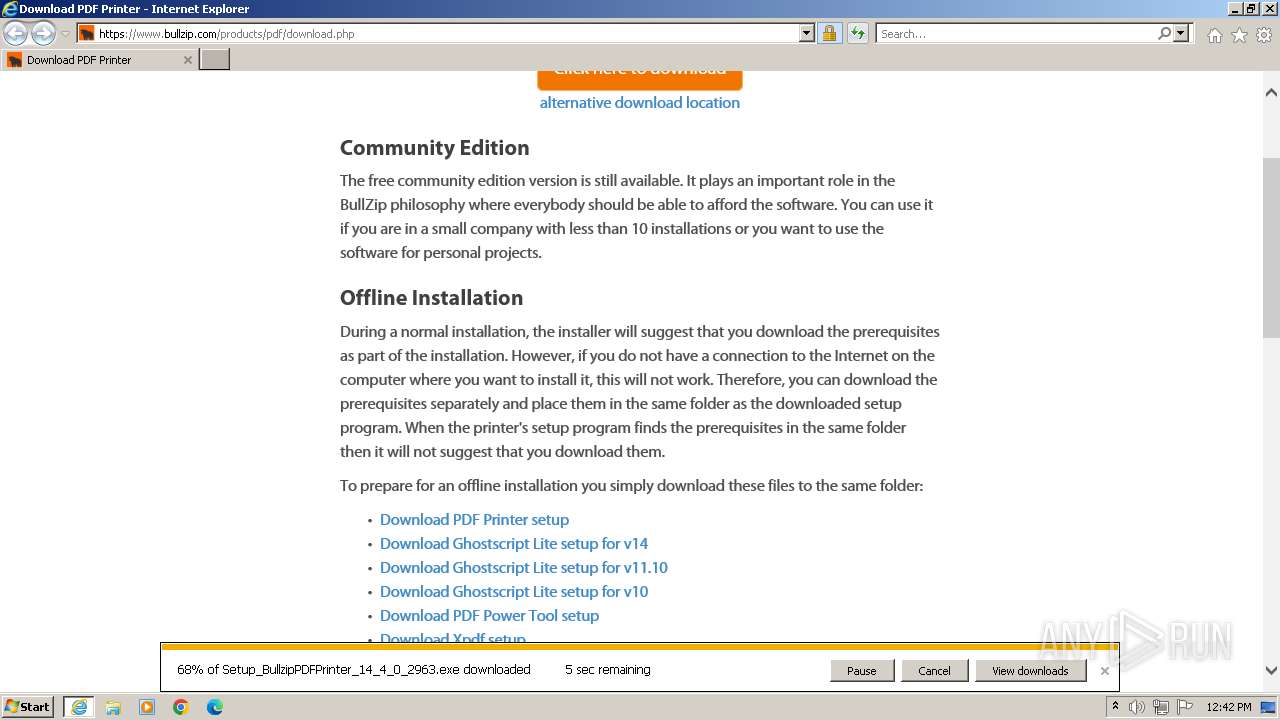
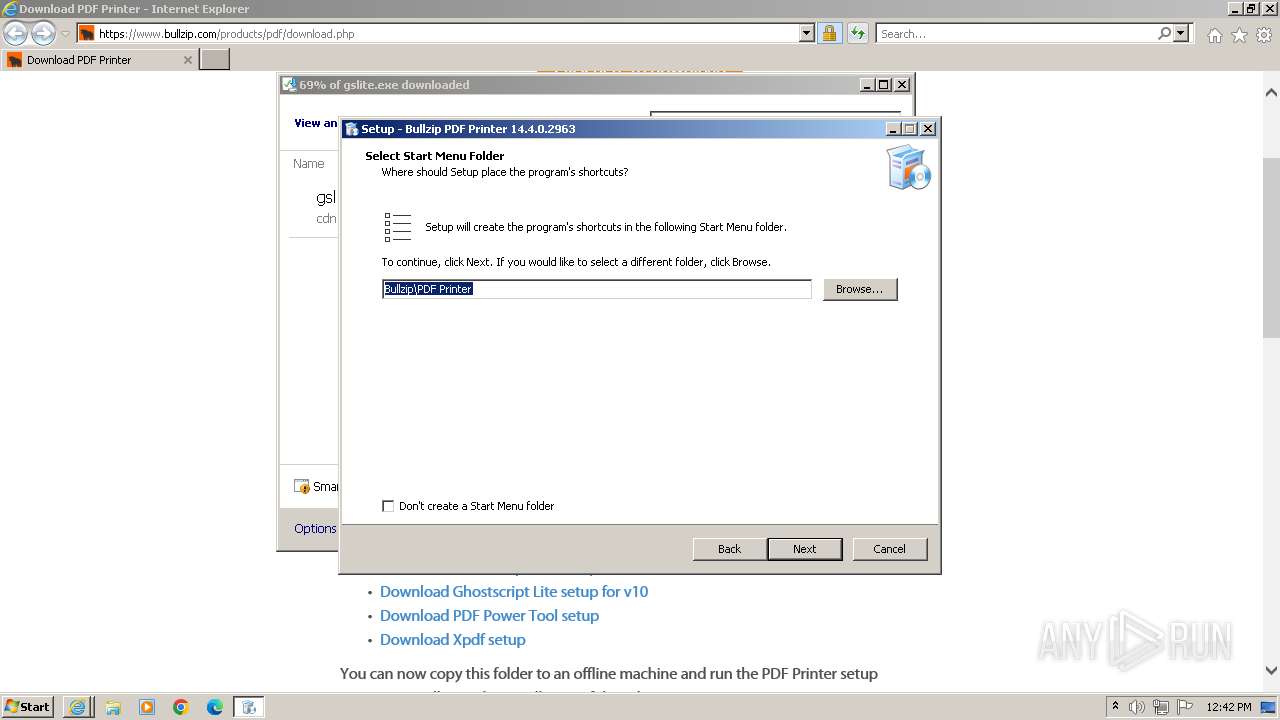
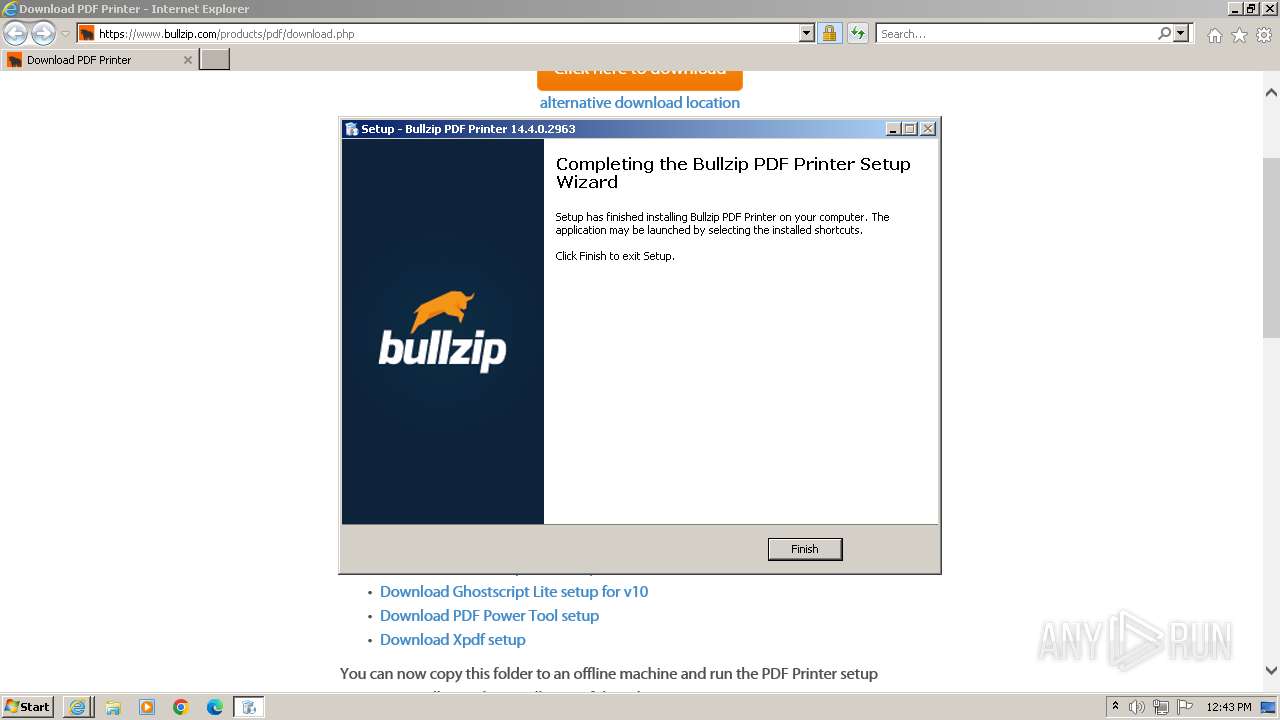
| URL: | https://www.bullzip.com/products/pdf/download.php |
| Full analysis: | https://app.any.run/tasks/d0b815b1-476a-4a42-af71-89ff12cba17f |
| Verdict: | Malicious activity |
| Analysis date: | October 31, 2023, 12:41:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | D180897784CE1FE4CC4353E9E4DFEFEE1120B5E4 |
| SHA256: | B31BDD3578F318CFB37F732EDE6F91E635D892E26B1DCE40793BB4FFAA97AC29 |
| SSDEEP: | 3:N8DSLwl4aQGRWOBWZlV:2OLwlRRWTV |
MALICIOUS
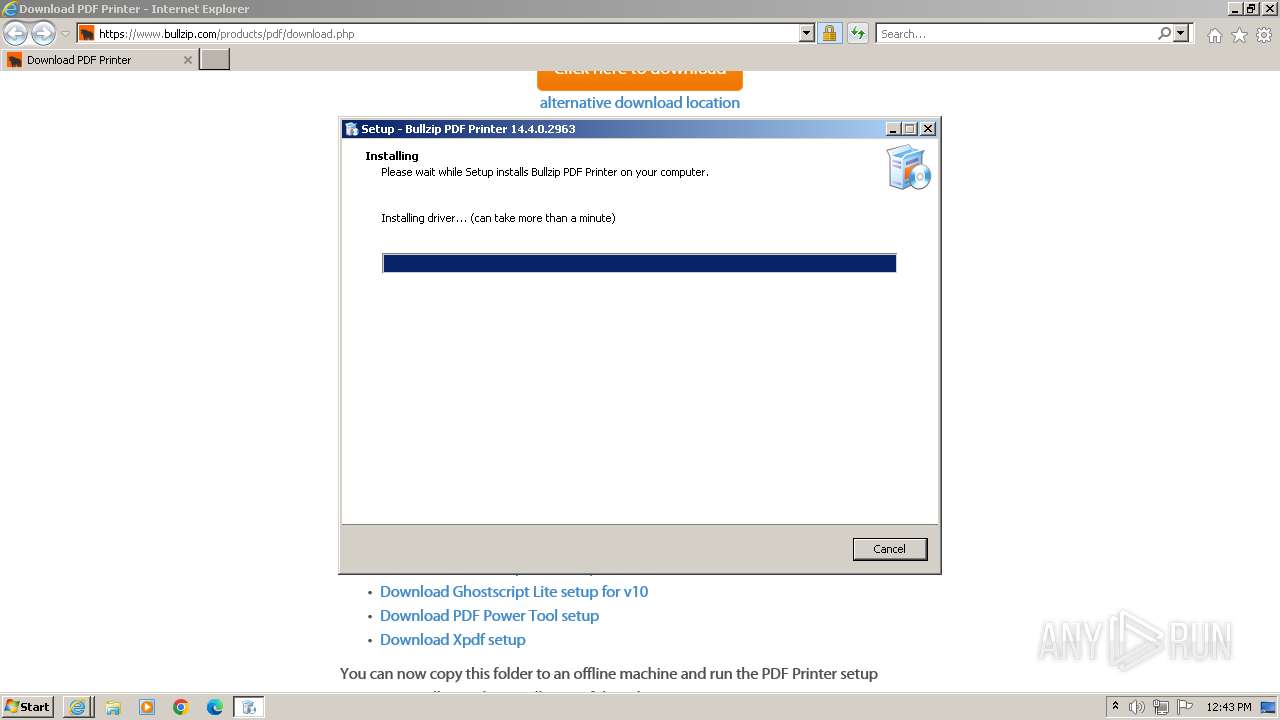
Creates a writable file the system directory
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 280)
- spoolsv.exe (PID: 988)
- PrintIsolationHost.exe (PID: 3052)
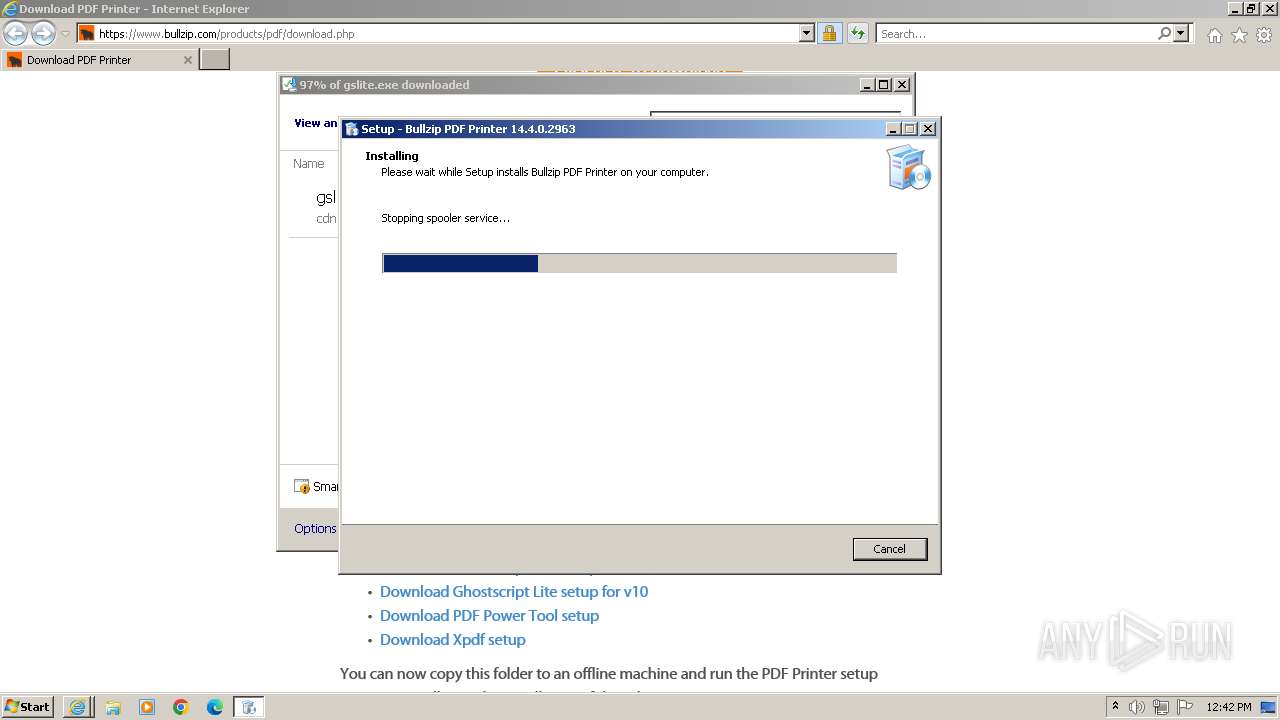
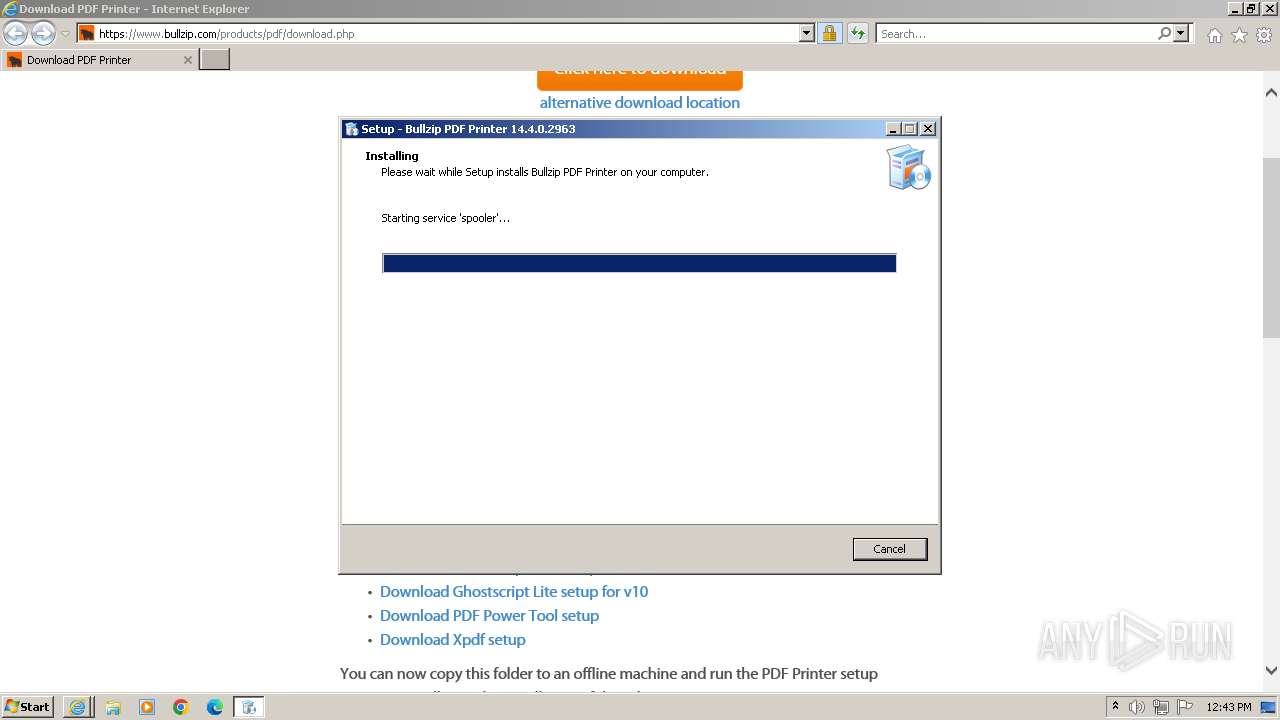
Starts NET.EXE for service management
- net.exe (PID: 2292)
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 280)
- net.exe (PID: 312)
- net.exe (PID: 2212)
- net.exe (PID: 2448)
- net.exe (PID: 2552)
- net.exe (PID: 1880)
- net.exe (PID: 3428)
- net.exe (PID: 3104)
- net.exe (PID: 3364)
- net.exe (PID: 3628)
- net.exe (PID: 2692)
- net.exe (PID: 2600)
- net.exe (PID: 3684)
- net.exe (PID: 2980)
- net.exe (PID: 2436)
- net.exe (PID: 2436)
- net.exe (PID: 3244)
- net.exe (PID: 3656)
- net.exe (PID: 2372)
- net.exe (PID: 3076)
- net.exe (PID: 3332)
- net.exe (PID: 3380)
- net.exe (PID: 1368)
- net.exe (PID: 3632)
- net.exe (PID: 4020)
- net.exe (PID: 2756)
- net.exe (PID: 1244)
- net.exe (PID: 116)
- net.exe (PID: 2760)
- net.exe (PID: 1772)
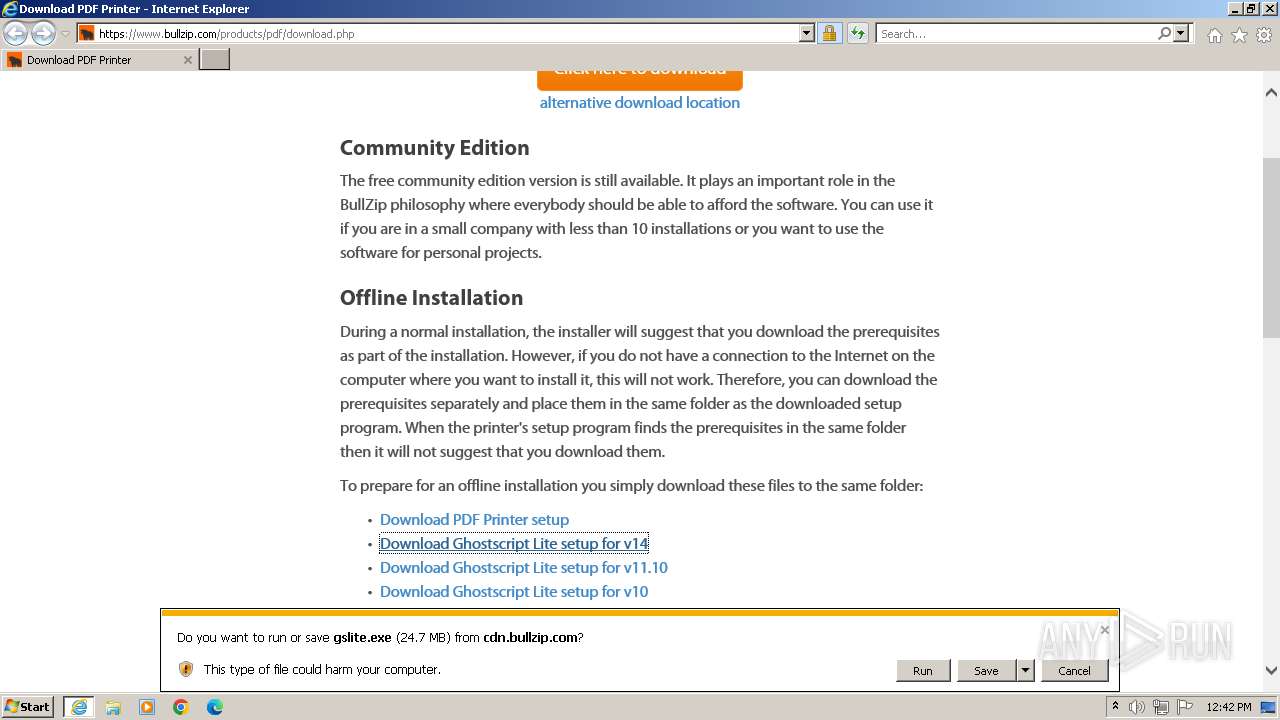
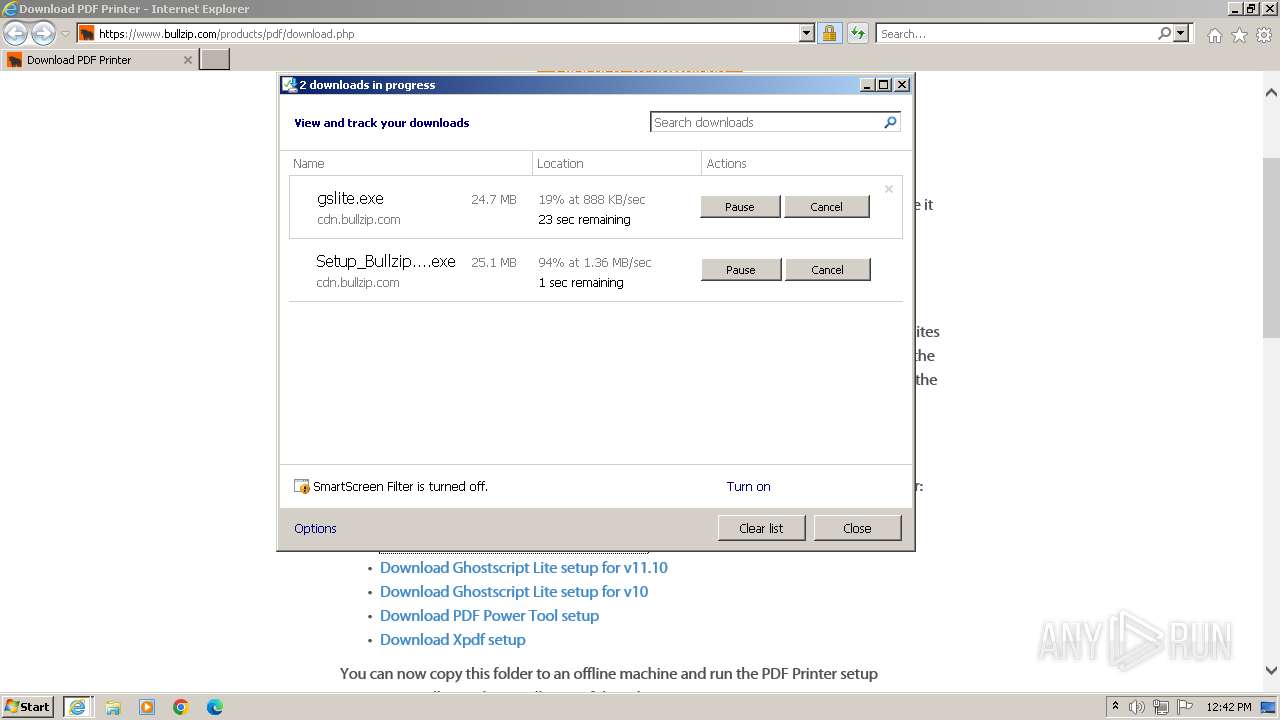
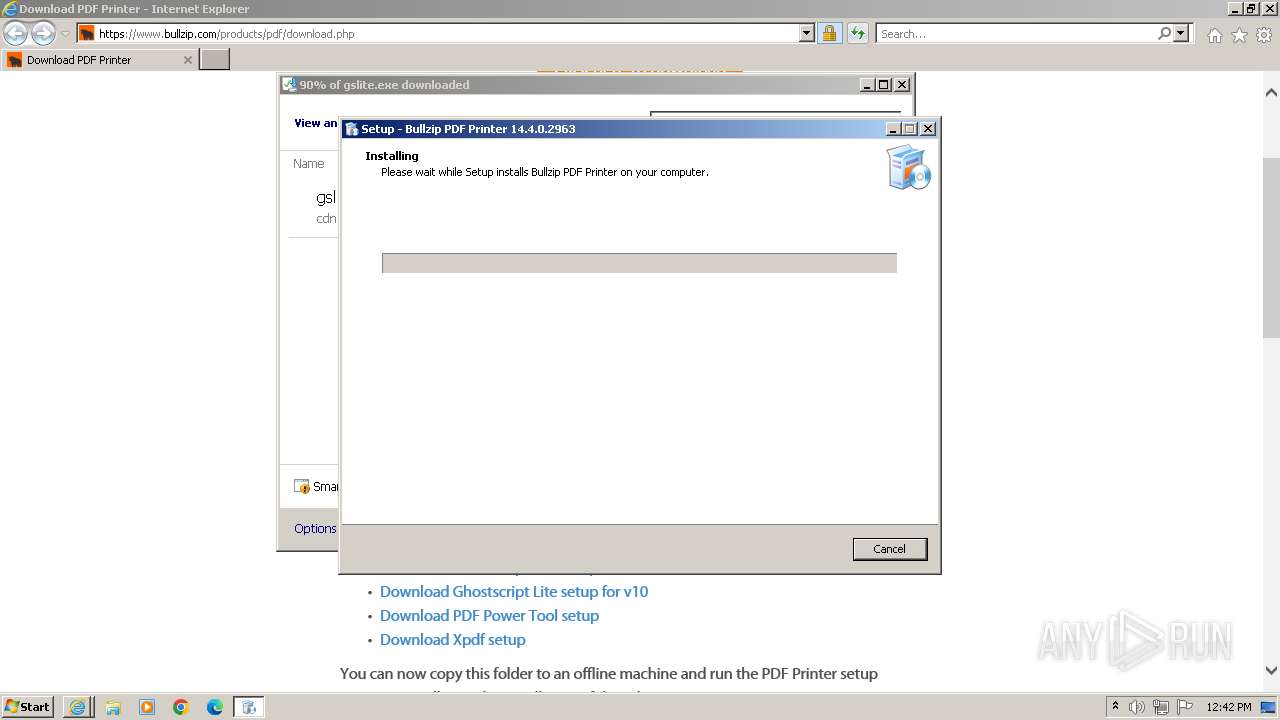
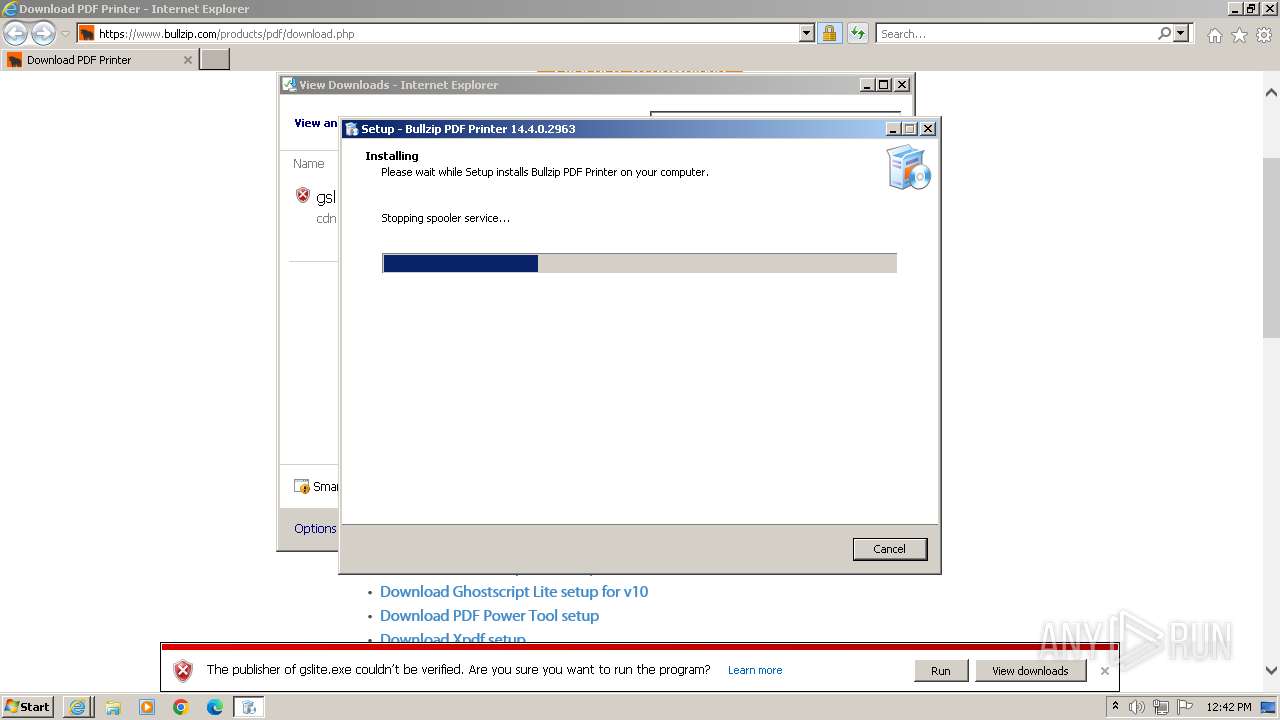
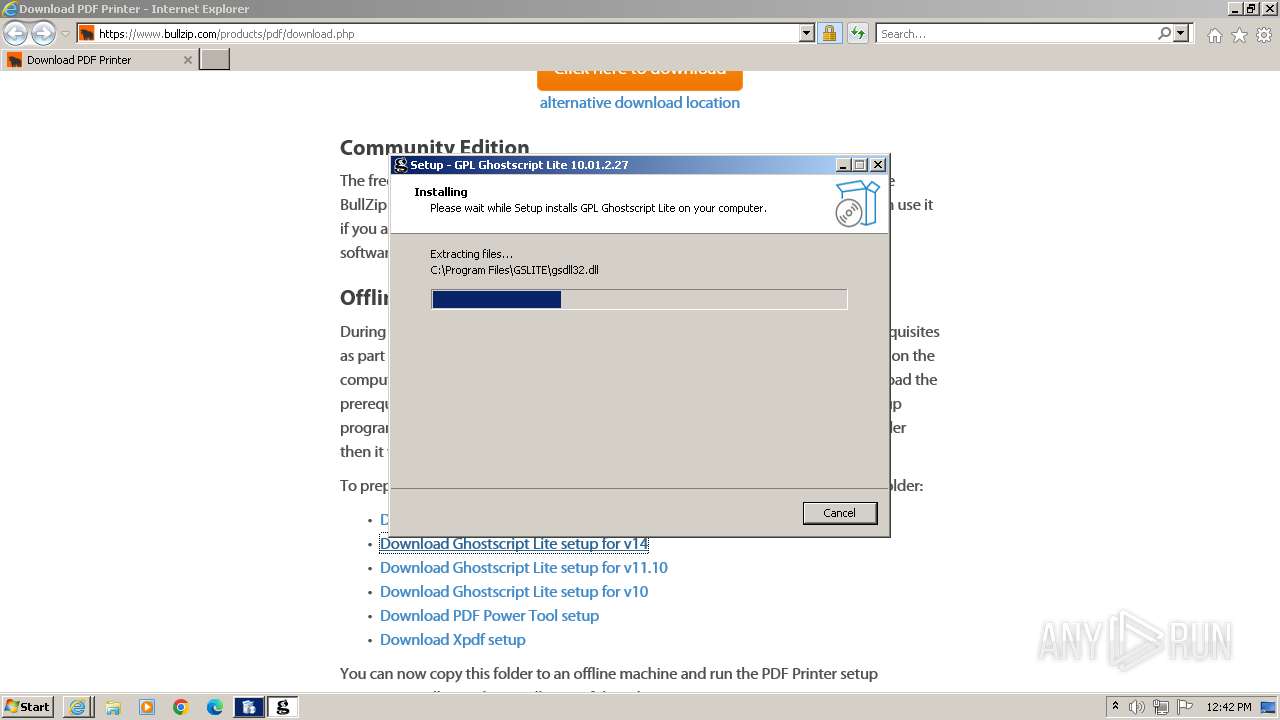
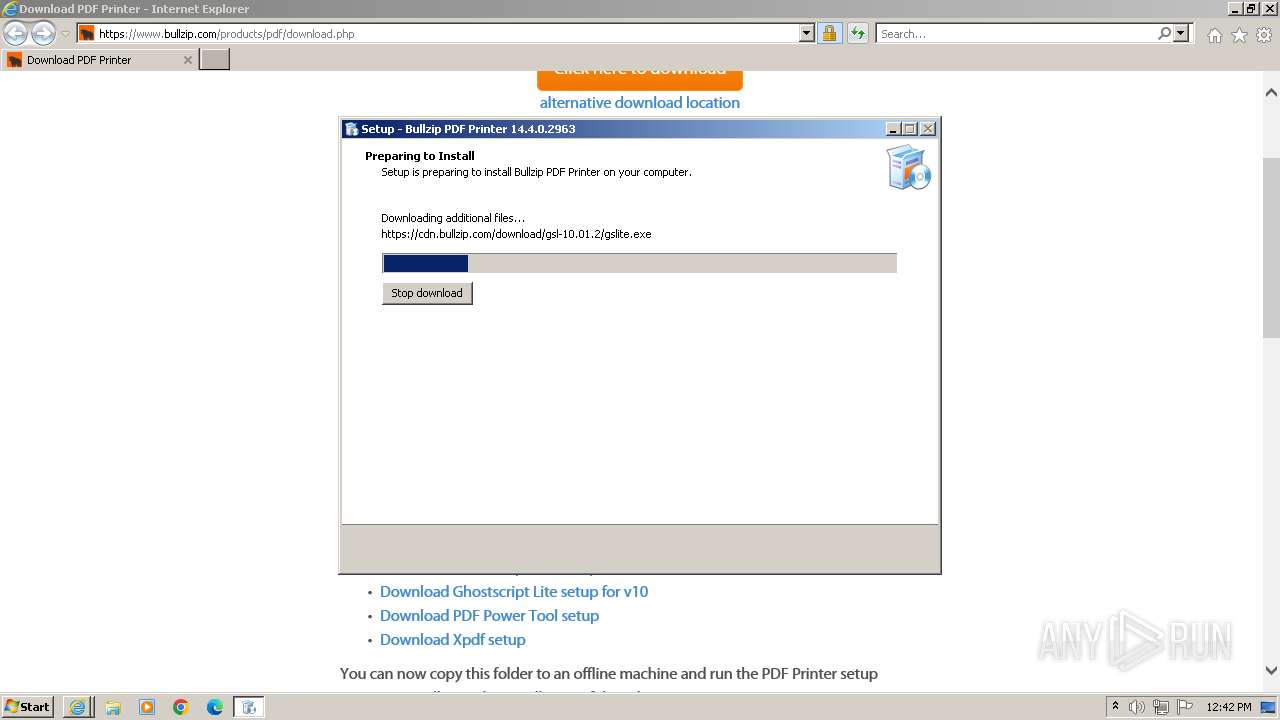
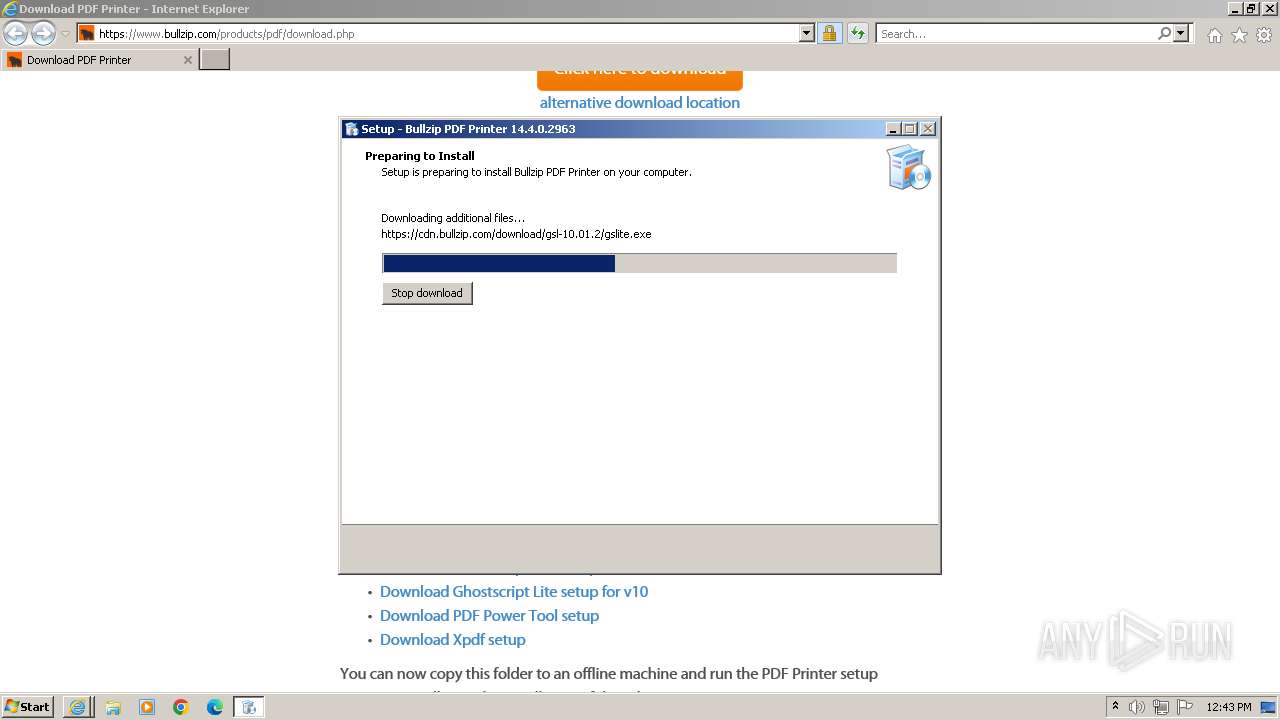
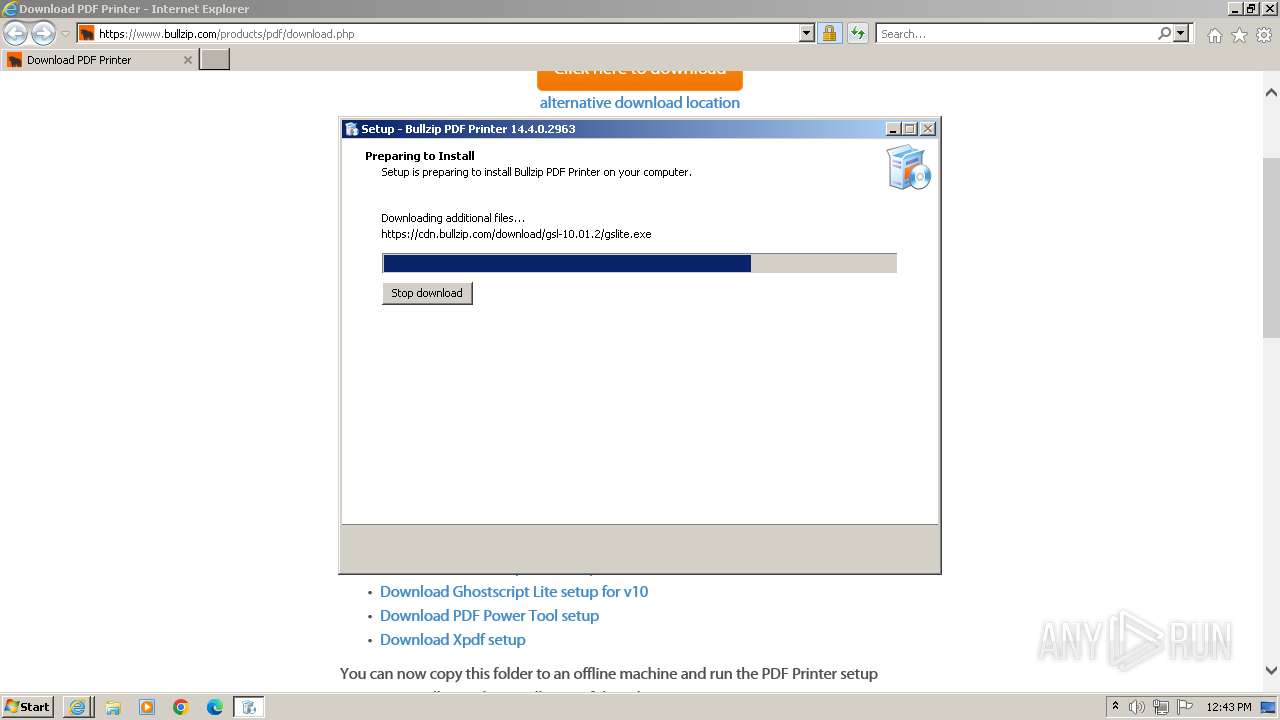
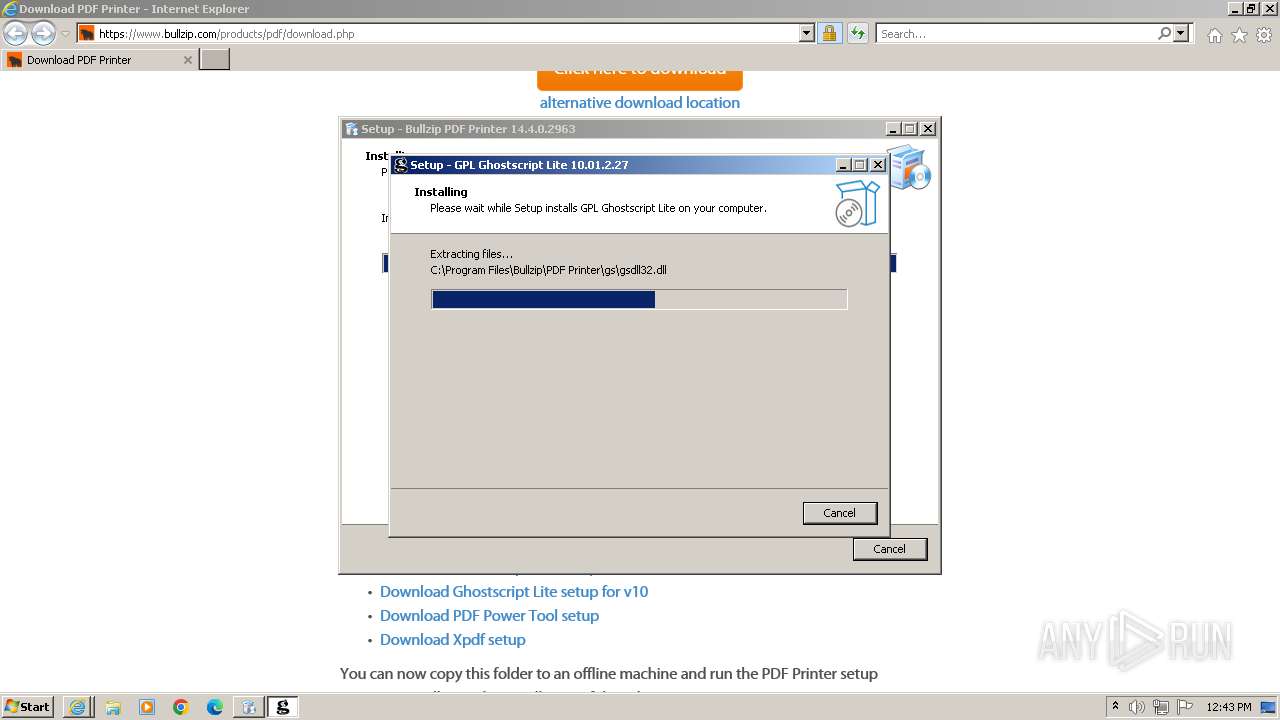
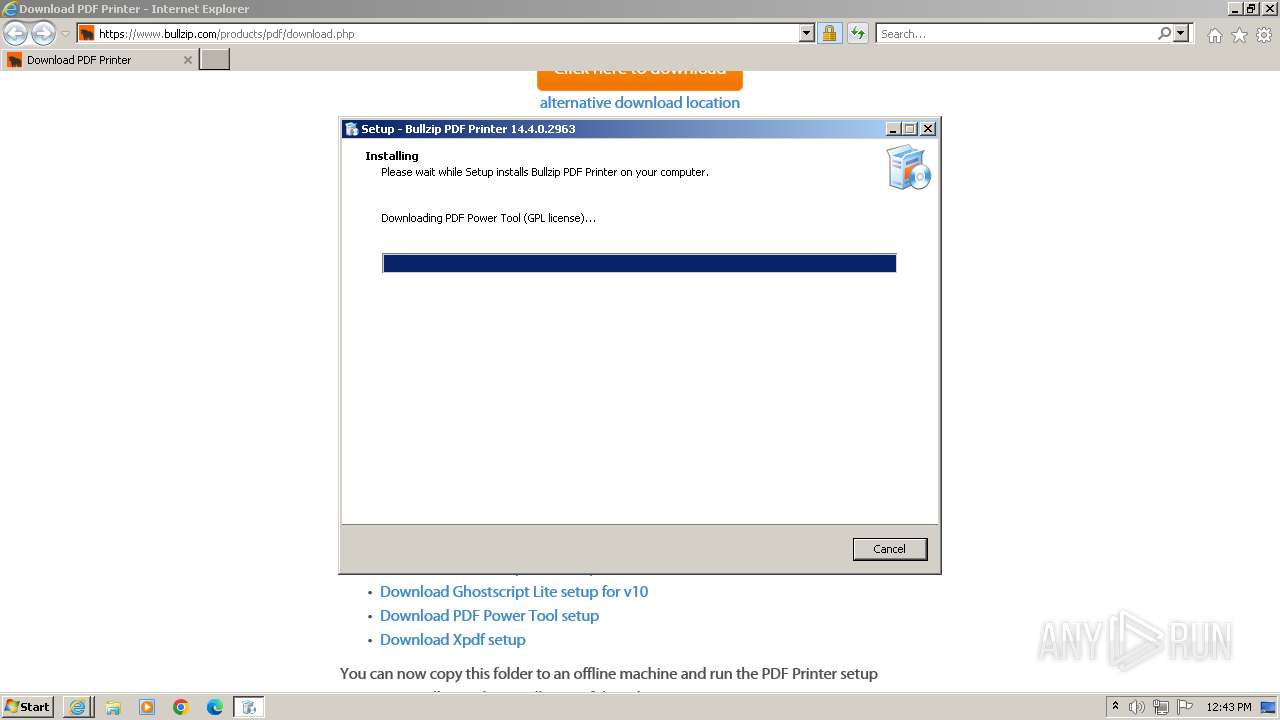
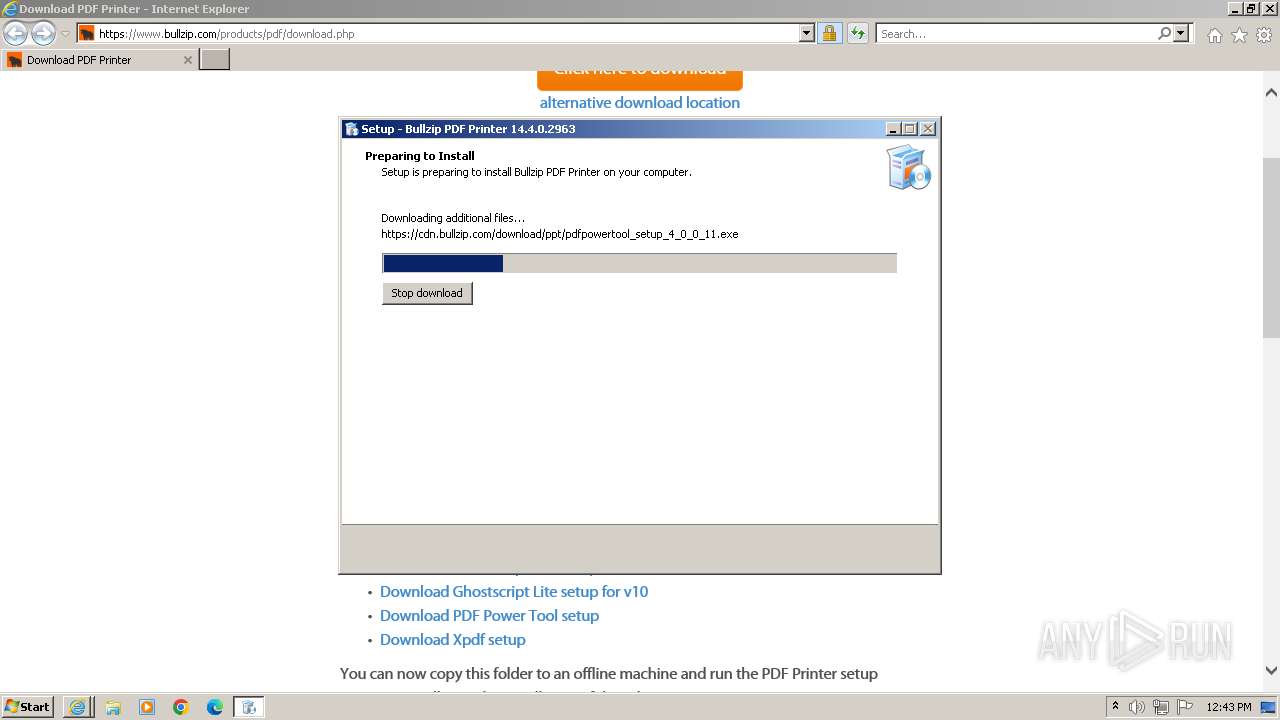
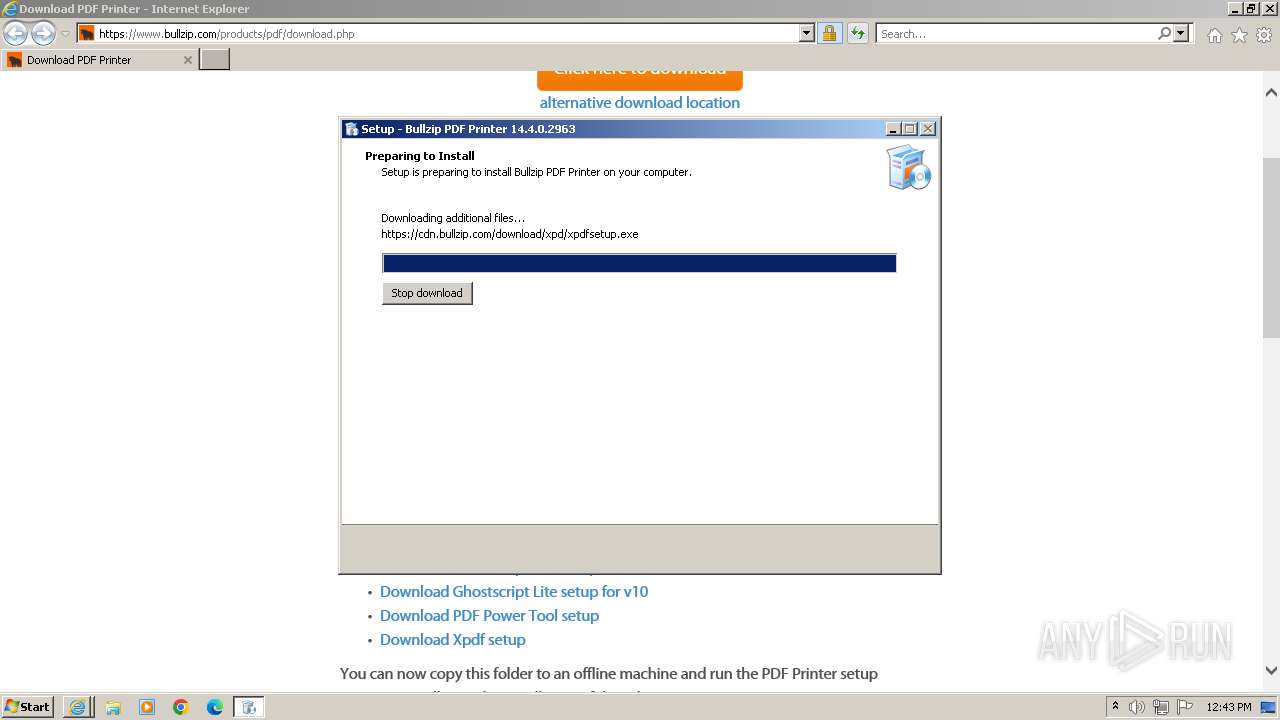
Drops the executable file immediately after the start
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 280)
- gslite.exe (PID: 3468)
- gslite.exe (PID: 1432)
- gslite.tmp (PID: 1956)
- gslite.exe (PID: 852)
- Setup_BullzipPDFPrinter_14_4_0_2963.exe (PID: 444)
- pdfpowertool_setup.exe (PID: 3256)
- Setup_BullzipPDFPrinter_14_4_0_2963.exe (PID: 3556)
- gslite.tmp (PID: 3584)
- xpdfsetup.exe (PID: 3820)
- pdfpowertool_setup.tmp (PID: 3836)
- xpdfsetup.tmp (PID: 1240)
Registers / Runs the DLL via REGSVR32.EXE
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 280)
SUSPICIOUS
Reads the Windows owner or organization settings
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 280)
- gslite.tmp (PID: 1956)
- gslite.tmp (PID: 3584)
- pdfpowertool_setup.tmp (PID: 3836)
- xpdfsetup.tmp (PID: 1240)
Process drops legitimate windows executable
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 280)
- pdfpowertool_setup.tmp (PID: 3836)
- xpdfsetup.tmp (PID: 1240)
- spoolsv.exe (PID: 988)
The process drops C-runtime libraries
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 280)
Executes as Windows Service
- spoolsv.exe (PID: 988)
- spoolsv.exe (PID: 4036)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2544)
Reads the Internet Settings
- RegAsm.exe (PID: 1252)
- RegAsm.exe (PID: 3752)
- RegAsm.exe (PID: 548)
- RegAsm.exe (PID: 1256)
- RegAsm.exe (PID: 2496)
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 280)
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 1336)
Searches for installed software
- gslite.tmp (PID: 3584)
Reads settings of System Certificates
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 280)
Adds/modifies Windows certificates
- Setup_BullzipPDFPrinter_14_4_0_2963.exe (PID: 3556)
INFO
Drops the executable file immediately after the start
- iexplore.exe (PID: 2232)
- iexplore.exe (PID: 1488)
- spoolsv.exe (PID: 988)
Application launched itself
- iexplore.exe (PID: 1488)
- msedge.exe (PID: 4092)
Reads the computer name
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 280)
- gslite.tmp (PID: 3028)
- gslite.tmp (PID: 1956)
- RegAsm.exe (PID: 548)
- RegAsm.exe (PID: 1252)
- RegAsm.exe (PID: 3752)
- RegAsm.exe (PID: 1256)
- RegAsm.exe (PID: 2496)
- gslite.tmp (PID: 3584)
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 1336)
- pdfpowertool_setup.tmp (PID: 3836)
- xpdfsetup.tmp (PID: 1240)
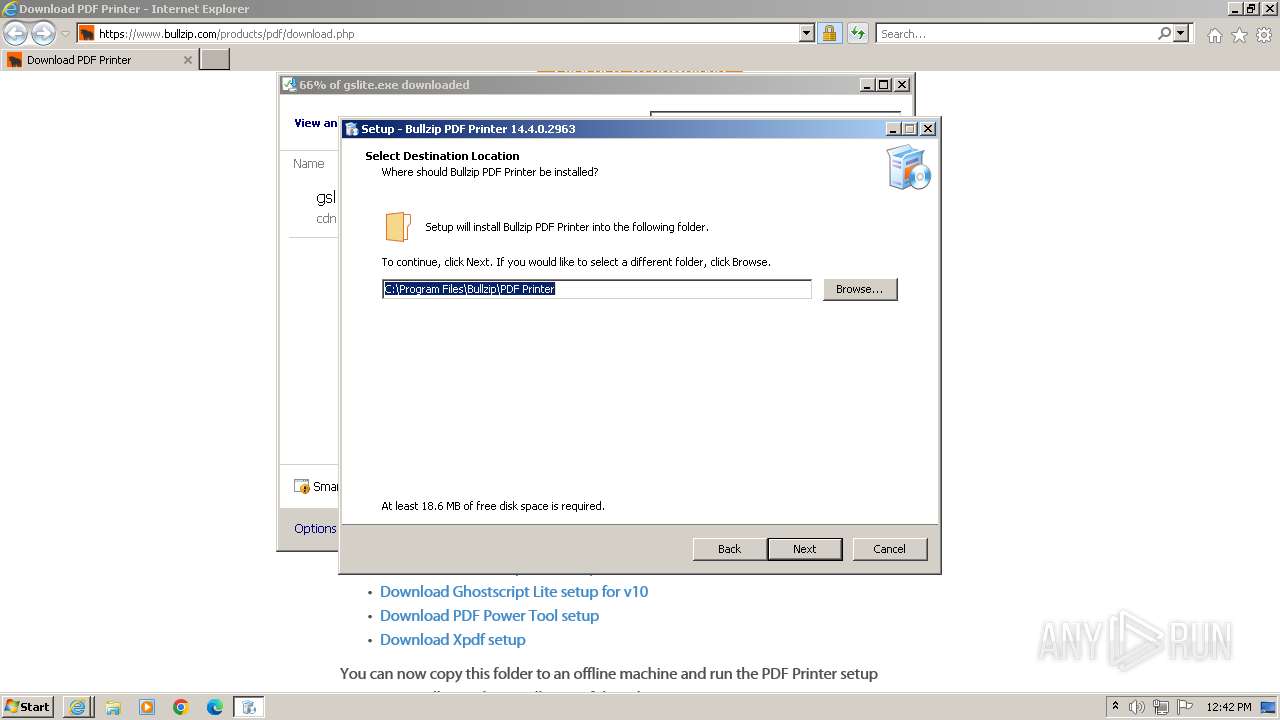
Creates files in the program directory
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 280)
- RegAsm.exe (PID: 1252)
- RegAsm.exe (PID: 3752)
- RegAsm.exe (PID: 548)
- gslite.tmp (PID: 1956)
- RegAsm.exe (PID: 2496)
- RegAsm.exe (PID: 1256)
- gslite.tmp (PID: 3584)
- pdfpowertool_setup.tmp (PID: 3836)
- xpdfsetup.tmp (PID: 1240)
Create files in a temporary directory
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 280)
- Setup_BullzipPDFPrinter_14_4_0_2963.exe (PID: 444)
- gslite.exe (PID: 1432)
- gslite.exe (PID: 3468)
- gslite.exe (PID: 852)
- Setup_BullzipPDFPrinter_14_4_0_2963.exe (PID: 3556)
- pdfpowertool_setup.exe (PID: 3256)
- pdfpowertool_setup.tmp (PID: 3836)
- xpdfsetup.exe (PID: 3820)
- xpdfsetup.tmp (PID: 1240)
Process checks computer location settings
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 280)
Reads the machine GUID from the registry
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 280)
- RegAsm.exe (PID: 548)
- RegAsm.exe (PID: 1252)
- RegAsm.exe (PID: 3752)
- RegAsm.exe (PID: 2496)
- RegAsm.exe (PID: 1256)
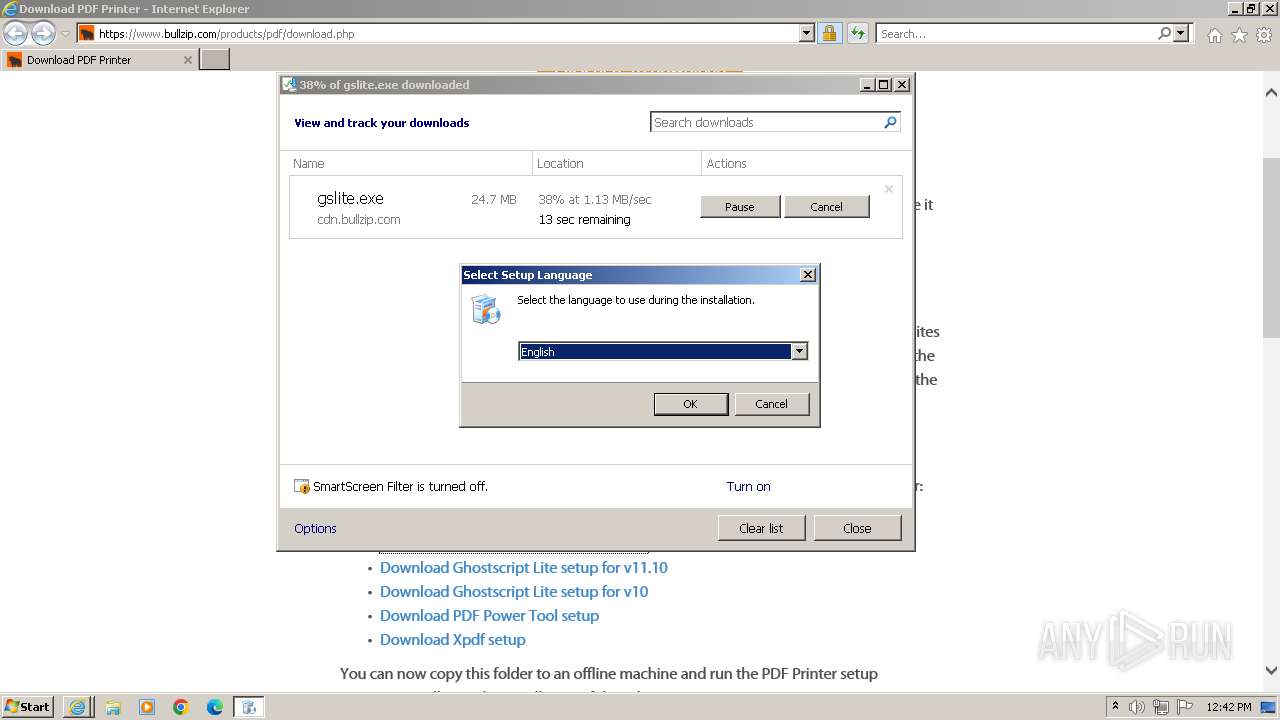
Checks supported languages
- Setup_BullzipPDFPrinter_14_4_0_2963.exe (PID: 444)
- Setup_BullzipPDFPrinter_14_4_0_2963.exe (PID: 3556)
- gslite.exe (PID: 1432)
- gslite.tmp (PID: 3028)
- gslite.exe (PID: 3468)
- gslite.tmp (PID: 1956)
- RegAsm.exe (PID: 548)
- RegAsm.exe (PID: 1252)
- RegAsm.exe (PID: 3752)
- RegAsm.exe (PID: 1256)
- RegAsm.exe (PID: 2496)
- gslite.exe (PID: 852)
- gslite.tmp (PID: 3584)
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 1336)
- Setup_BullzipPDFPrinter_14_4_0_2963.tmp (PID: 280)
- pdfpowertool_setup.exe (PID: 3256)
- pdfpowertool_setup.tmp (PID: 3836)
- xpdfsetup.tmp (PID: 1240)
- xpdfsetup.exe (PID: 3820)
The process uses the downloaded file
- iexplore.exe (PID: 1488)
Reads mouse settings
- regsvr32.exe (PID: 2544)
- regsvr32.exe (PID: 2312)
- regsvr32.exe (PID: 1140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
190
Monitored processes
111
Malicious processes
17
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Windows\system32\net.exe" STOP SPOOLER /Y | C:\Windows\System32\net.exe | — | Setup_BullzipPDFPrinter_14_4_0_2963.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
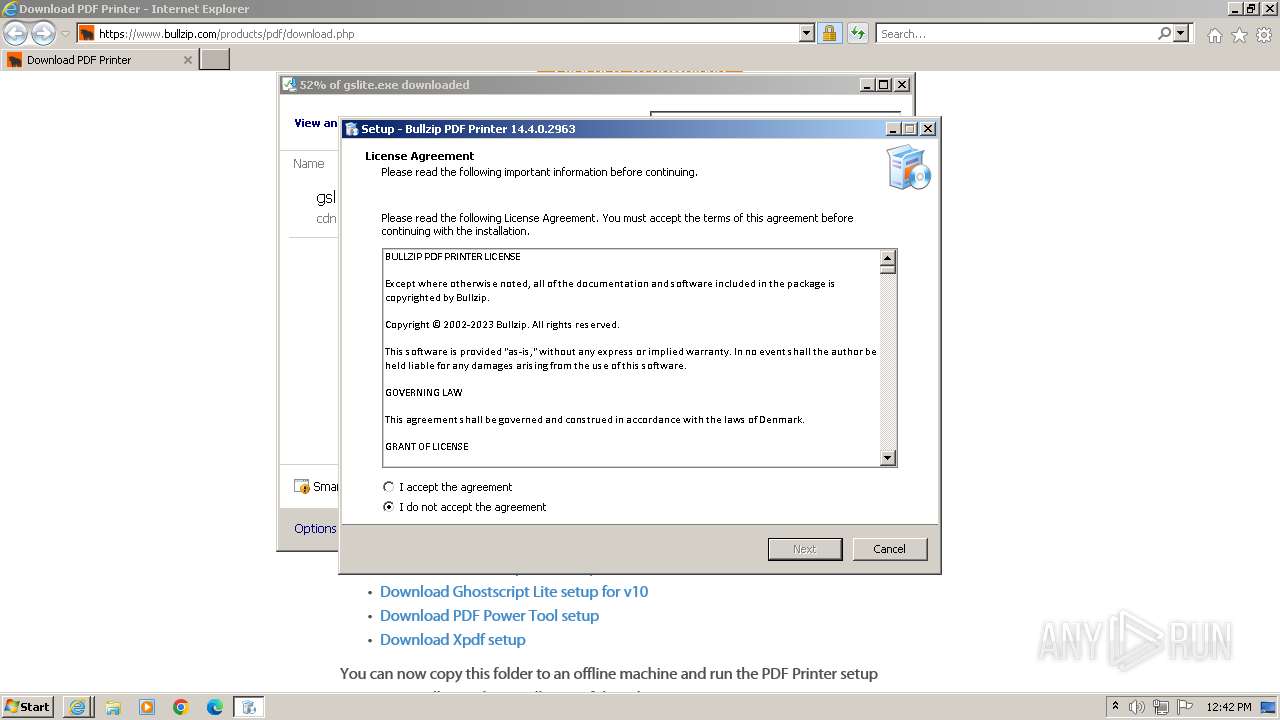
| 280 | "C:\Users\admin\AppData\Local\Temp\is-4F0IH.tmp\Setup_BullzipPDFPrinter_14_4_0_2963.tmp" /SL5="$902FC,25289818,803328,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Setup_BullzipPDFPrinter_14_4_0_2963.exe" /SPAWNWND=$30354 /NOTIFYWND=$A0372 | C:\Users\admin\AppData\Local\Temp\is-4F0IH.tmp\Setup_BullzipPDFPrinter_14_4_0_2963.tmp | Setup_BullzipPDFPrinter_14_4_0_2963.exe | ||||||||||||
User: admin Company: Bullzip Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 312 | "C:\Windows\system32\net.exe" STOP SPOOLER /Y | C:\Windows\System32\net.exe | — | Setup_BullzipPDFPrinter_14_4_0_2963.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 312 | "C:\Windows\system32\regsvr32.exe" /u /s "C:\Windows\system32\comdlg32.ocx" | C:\Windows\System32\regsvr32.exe | — | Setup_BullzipPDFPrinter_14_4_0_2963.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 316 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1436 --field-trial-handle=1288,i,8564085686442541742,17277715748373301607,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 444 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Setup_BullzipPDFPrinter_14_4_0_2963.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Setup_BullzipPDFPrinter_14_4_0_2963.exe | — | iexplore.exe | |||||||||||
User: admin Company: Bullzip Integrity Level: MEDIUM Description: Bullzip PDF Printer Setup Exit code: 0 Version: 14.4.0.2963 Modules
| |||||||||||||||
| 548 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\regasm.exe" /codebase Bullzip.PDFWriter.dll /tlb | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | Setup_BullzipPDFPrinter_14_4_0_2963.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 560 | C:\Windows\system32\net1 STOP SPOOLER /Y | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 612 | C:\Windows\system32\net1 STOP SPOOLER /Y | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 668 | C:\Windows\system32\net1 start spooler | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
29 858
Read events
28 499
Write events
552
Delete events
807
Modification events
| (PID) Process: | (1488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
214
Suspicious files
415
Text files
363
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2232 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarFD36.tmp | binary | |
MD5:9441737383D21192400ECA82FDA910EC | SHA256:BC3A6E84E41FAEB57E7C21AA3B60C2A64777107009727C5B7C0ED8FE658909E5 | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:FD5B7590BCB0A766DE512CC8A42A3126 | SHA256:FFF3AE74918CF186B0A730E95397D79764BED5CA96323CA762DED983799D65DC | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFD35.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFD56.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:E3C52199985D518C65BC56154FB452B5 | SHA256:4B3DC6472C564E30B23EEA00E6DD2DB26C9928DE15256D51BDC3D1D840D4377E | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\bootstrap-theme.min[1].css | text | |
MD5:FFB12F89F706291CB139B73C164A7722 | SHA256:34B102CB7689409FD1C3C180AEB1FD3F0B8BF0B47AB25C74C42EAFF574E661A9 | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F7677D3E72319C5221AB984EF8C2D754 | binary | |
MD5:182B87E6AE9411CDA9340AA3BF0835CF | SHA256:B24B0FCC0338B130C0E118A7BFC07BDC8A929ED0F0AD8814EAAB29D8F08DBA9D | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\jquery.min[1].js | text | |
MD5:8101D596B2B8FA35FE3A634EA342D7C3 | SHA256:540BC6DEC1DD4B92EA4D3FB903F69EABF6D919AFD48F4E312B163C28CFF0F441 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
58
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2232 | iexplore.exe | GET | 200 | 23.212.210.158:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2232 | iexplore.exe | GET | 200 | 8.238.191.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f649f4926af1fc0f | unknown | compressed | 4.66 Kb | unknown |
2232 | iexplore.exe | GET | 200 | 8.238.191.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?b15045137d61d6fd | unknown | compressed | 61.6 Kb | unknown |
2232 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDCjDk6BcP0YRJkTzSsQwBD | unknown | der | 472 b | unknown |
2232 | iexplore.exe | GET | 200 | 184.24.77.67:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgOKhxuQqQuE%2BVpxyoHt7r5aBQ%3D%3D | unknown | binary | 503 b | unknown |
2232 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEARORsnIdekJQQ2ZoJ96Gk8%3D | unknown | binary | 471 b | unknown |
2232 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
2232 | iexplore.exe | GET | 200 | 8.238.191.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0583eb51efcb6873 | unknown | compressed | 4.66 Kb | unknown |
1488 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
2232 | iexplore.exe | GET | 200 | 8.238.191.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9b9949a2d04f0403 | unknown | compressed | 61.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2232 | iexplore.exe | 8.238.191.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2232 | iexplore.exe | 23.212.210.158:80 | x1.c.lencr.org | AKAMAI-AS | AU | unknown |
2232 | iexplore.exe | 184.24.77.67:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
2232 | iexplore.exe | 46.30.213.94:443 | www.bullzip.com | One.com A/S | DK | unknown |
2232 | iexplore.exe | 142.250.186.106:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
2232 | iexplore.exe | 18.66.127.89:443 | cdn-images.mailchimp.com | AMAZON-02 | US | unknown |
2232 | iexplore.exe | 142.250.186.168:443 | www.googletagmanager.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
www.googletagmanager.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn-images.mailchimp.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
Threats
Process | Message |
|---|---|
PrintIsolationHost.exe |
Lower DWORD of elapsed time = 0
|
PrintIsolationHost.exe |
Upper DWORD of elapsed time = 0
|