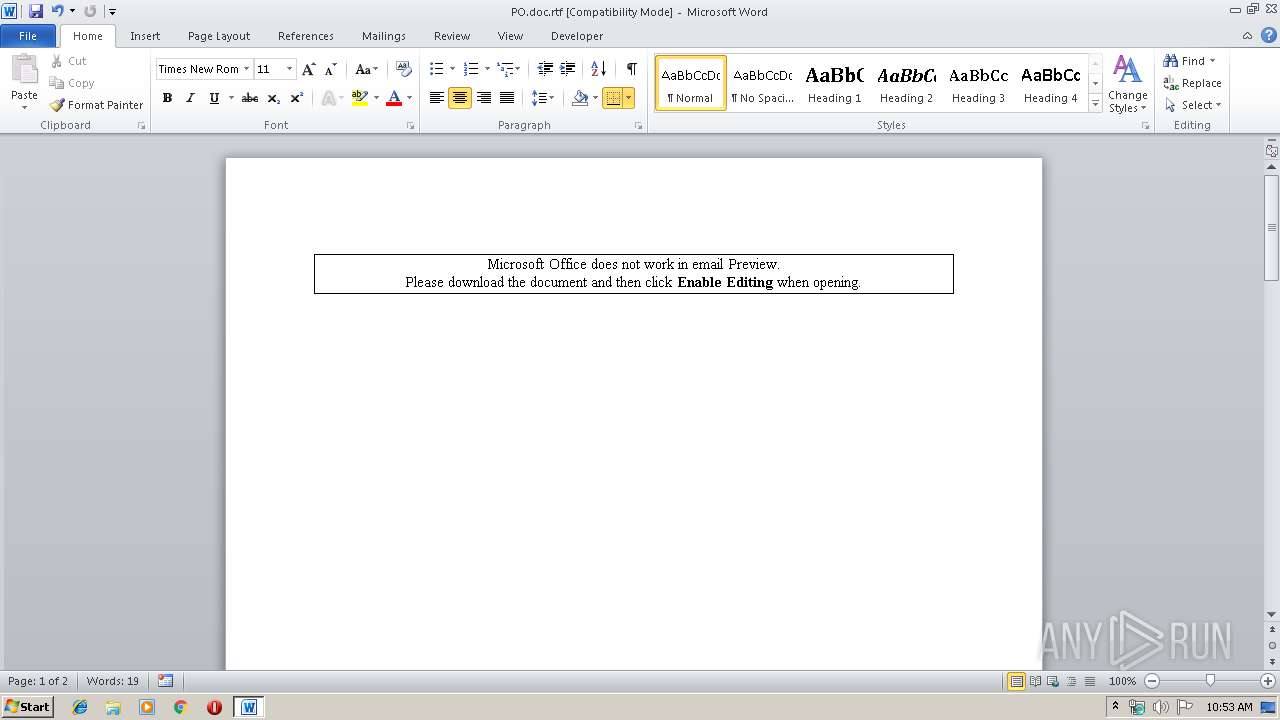
| File name: | PO.doc |
| Full analysis: | https://app.any.run/tasks/06194c03-07c4-4b9f-85b3-e86da7db685b |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 09:52:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | C3BA90B7CC89EA7B64E522F898341F42 |
| SHA1: | 900BC7477FC8A0BFE75D341006D510C6779FE47E |
| SHA256: | B30A71C5B1ABC2DAF38472BADA0209898B267C233E7E1EAD6A22B23C23AD83BB |
| SSDEEP: | 1536:mPqRSTnlqtHv9YNpRFJ7e1ehege+fDEfDNQim3O3gMSNkR1BY5YYbPFRIxPILSQl:mPq62NgmxgLSQWno |
MALICIOUS
Application was dropped or rewritten from another process
- bdjld.exe (PID: 3524)
- bdjld.exe (PID: 2488)
- bdjld.exe (PID: 2524)
- bdjld.exe (PID: 2560)
- bdjld.exe (PID: 2584)
- bdjld.exe (PID: 2612)
- bdjld.exe (PID: 2636)
- bdjld.exe (PID: 2660)
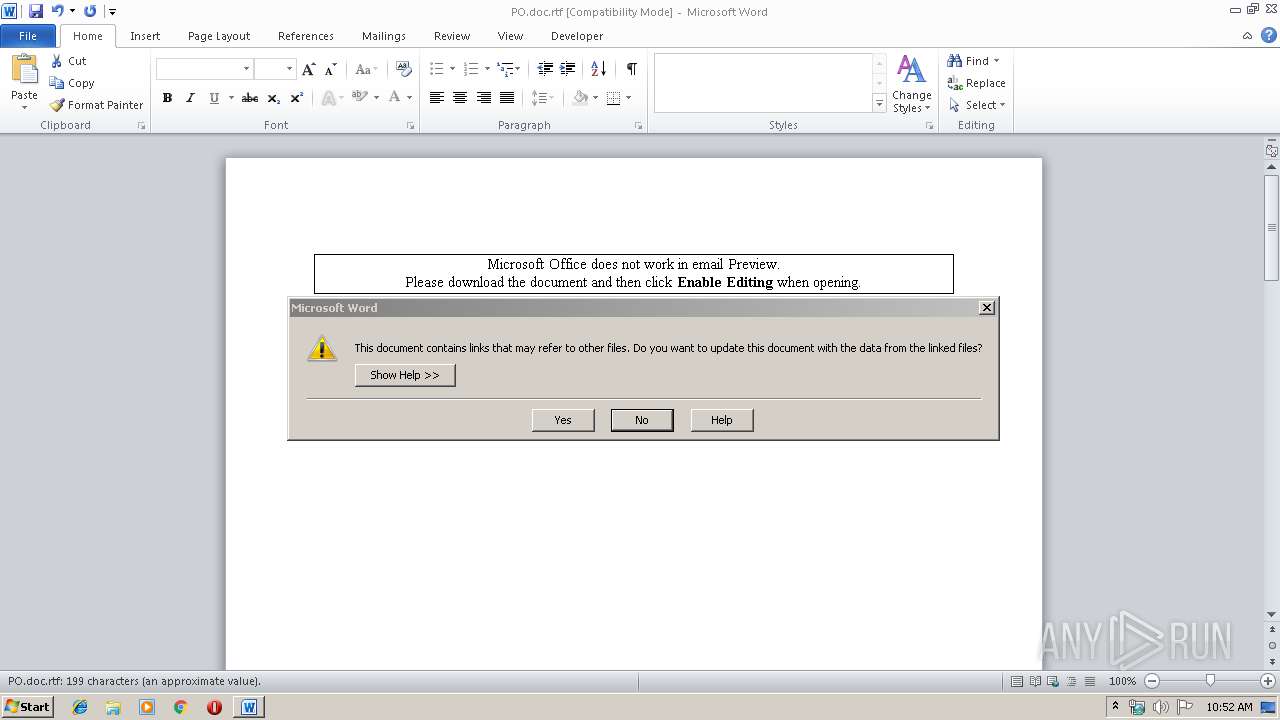
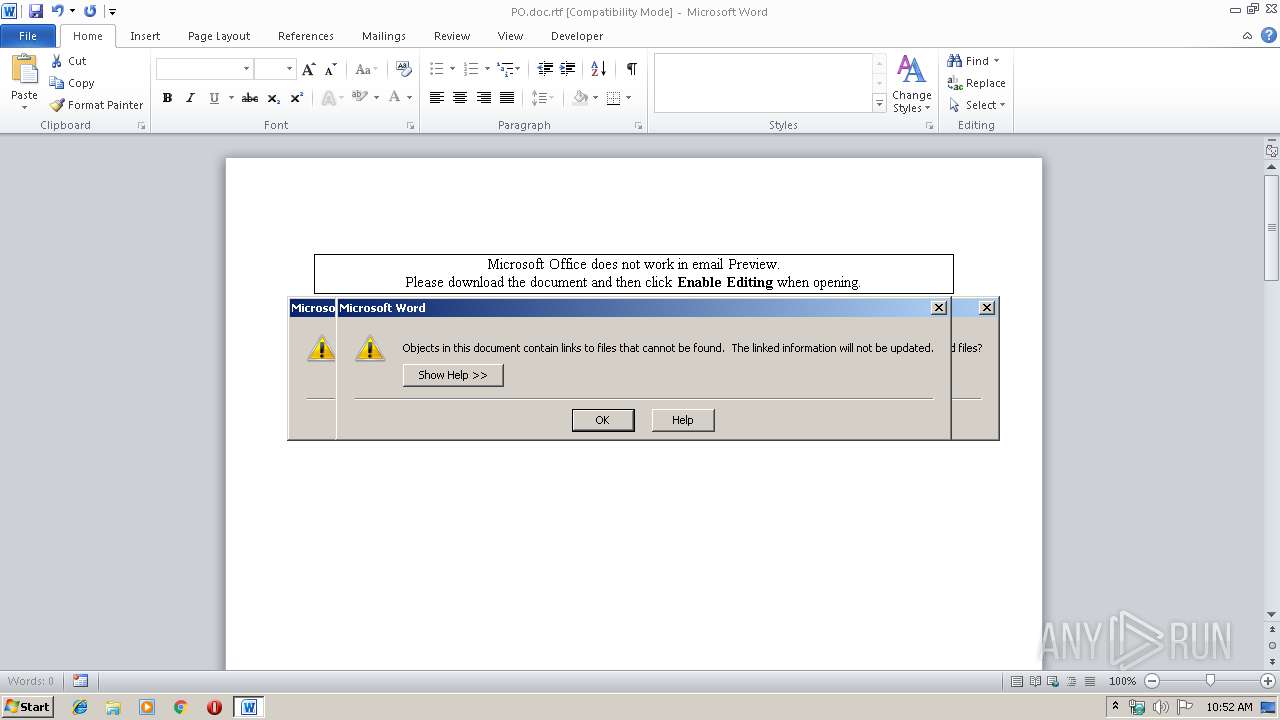
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3516)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 3516)
SUSPICIOUS
Executable content was dropped or overwritten
- bdjld.exe (PID: 3524)
Application launched itself
- bdjld.exe (PID: 3524)
INFO
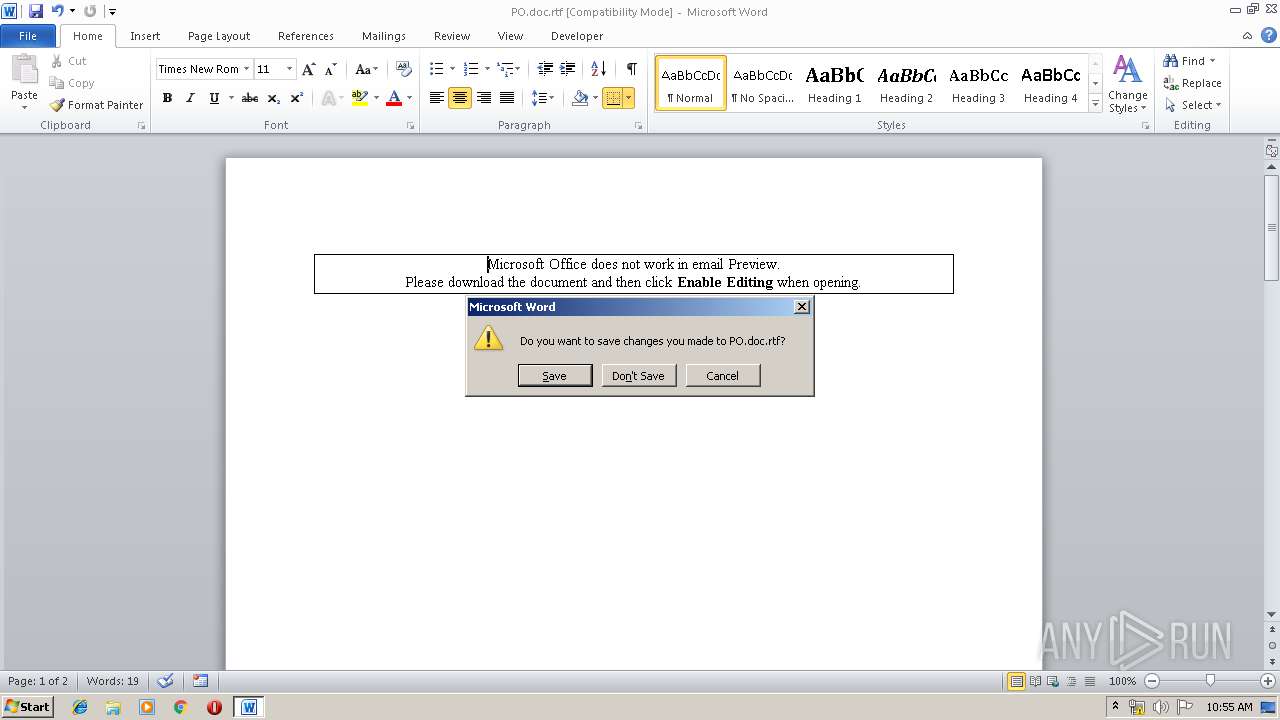
Creates files in the user directory
- WINWORD.EXE (PID: 3516)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
41
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2488 | "C:/Users/admin/AppData/Roaming/bdjld.exe" | C:\Users\admin\AppData\Roaming\bdjld.exe | — | bdjld.exe | |||||||||||
User: admin Company: Namecheap.com Integrity Level: MEDIUM Description: Dynamic DNS Client Exit code: 0 Version: 2.0.0.7 | |||||||||||||||
| 2524 | "C:/Users/admin/AppData/Roaming/bdjld.exe" | C:\Users\admin\AppData\Roaming\bdjld.exe | — | bdjld.exe | |||||||||||
User: admin Company: Namecheap.com Integrity Level: MEDIUM Description: Dynamic DNS Client Exit code: 0 Version: 2.0.0.7 | |||||||||||||||
| 2560 | "C:/Users/admin/AppData/Roaming/bdjld.exe" | C:\Users\admin\AppData\Roaming\bdjld.exe | — | bdjld.exe | |||||||||||
User: admin Company: Namecheap.com Integrity Level: MEDIUM Description: Dynamic DNS Client Exit code: 0 Version: 2.0.0.7 | |||||||||||||||
| 2584 | "C:/Users/admin/AppData/Roaming/bdjld.exe" | C:\Users\admin\AppData\Roaming\bdjld.exe | — | bdjld.exe | |||||||||||
User: admin Company: Namecheap.com Integrity Level: MEDIUM Description: Dynamic DNS Client Exit code: 0 Version: 2.0.0.7 | |||||||||||||||
| 2612 | "C:/Users/admin/AppData/Roaming/bdjld.exe" | C:\Users\admin\AppData\Roaming\bdjld.exe | — | bdjld.exe | |||||||||||
User: admin Company: Namecheap.com Integrity Level: MEDIUM Description: Dynamic DNS Client Exit code: 0 Version: 2.0.0.7 | |||||||||||||||
| 2636 | "C:/Users/admin/AppData/Roaming/bdjld.exe" | C:\Users\admin\AppData\Roaming\bdjld.exe | — | bdjld.exe | |||||||||||
User: admin Company: Namecheap.com Integrity Level: MEDIUM Description: Dynamic DNS Client Exit code: 0 Version: 2.0.0.7 | |||||||||||||||
| 2660 | "C:/Users/admin/AppData/Roaming/bdjld.exe" | C:\Users\admin\AppData\Roaming\bdjld.exe | — | bdjld.exe | |||||||||||
User: admin Company: Namecheap.com Integrity Level: MEDIUM Description: Dynamic DNS Client Exit code: 0 Version: 2.0.0.7 | |||||||||||||||
| 3516 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\PO.doc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3524 | C:\Users\admin\AppData\Roaming\bdjld.exe | C:\Users\admin\AppData\Roaming\bdjld.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Namecheap.com Integrity Level: MEDIUM Description: Dynamic DNS Client Exit code: 0 Version: 2.0.0.7 Modules
| |||||||||||||||
Total events
1 305
Read events
956
Write events
339
Delete events
10
Modification events
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | "z$ |
Value: 227A2400BC0D0000010000000000000000000000 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1328742430 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742544 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742545 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: BC0D0000D6EC4BEFCF6ED50100000000 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | j{$ |
Value: 6A7B2400BC0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | j{$ |
Value: 6A7B2400BC0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
0
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9A22.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BCED8739.png | — | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{419E9C07-E18F-4840-B2D1-BF35E6F71A7E}.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{09C38F7E-9947-4CFC-92BB-D86371DD9444}.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{3ECED218-8EC6-4994-8AD2-5212B5D13F56}.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{FDA01DE6-F224-4FA6-B68F-8274E4FEAD10}.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\bdjld.exe | executable | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$PO.doc.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Abctfhghghghghg.scT | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
0
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3516 | WINWORD.EXE | 185.234.218.37:80 | — | — | — | suspicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3516 | WINWORD.EXE | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3516 | WINWORD.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M1 |
3516 | WINWORD.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3516 | WINWORD.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M2 |
3516 | WINWORD.EXE | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |