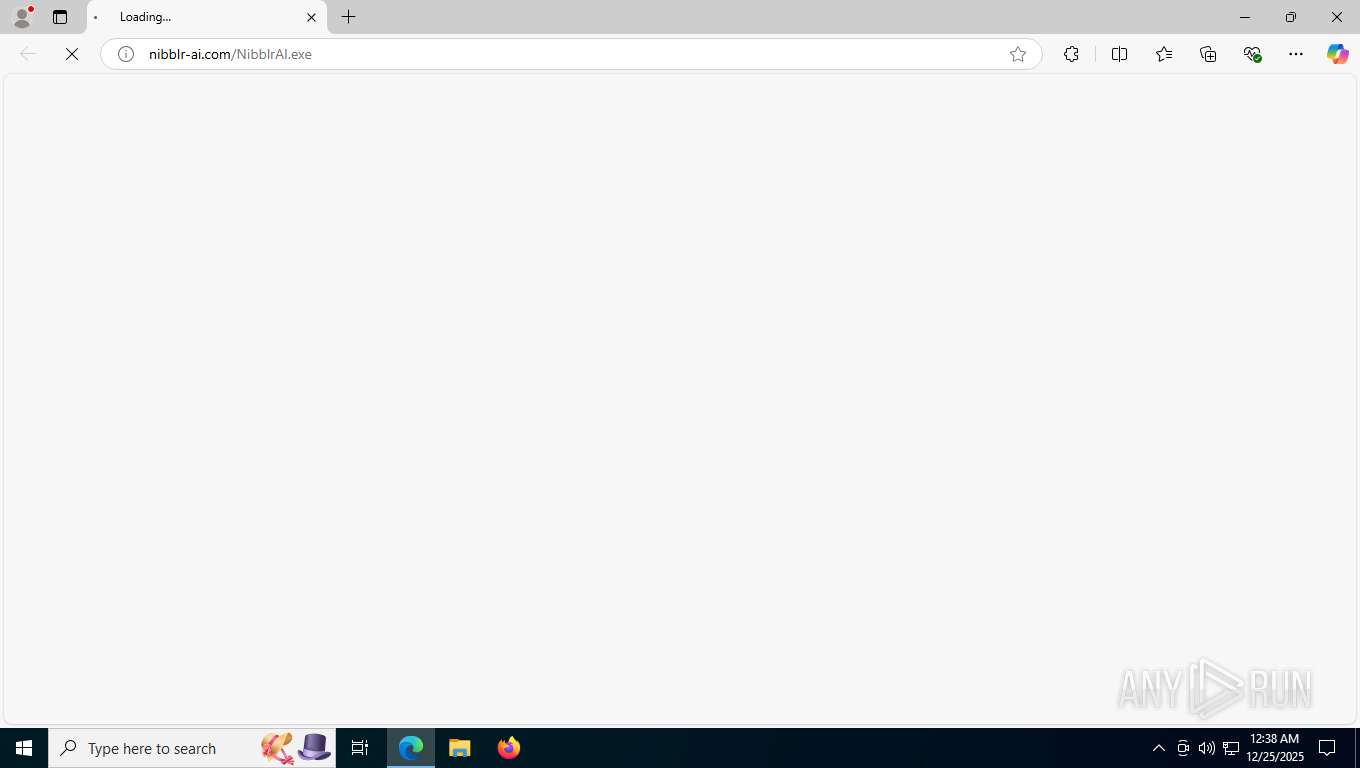
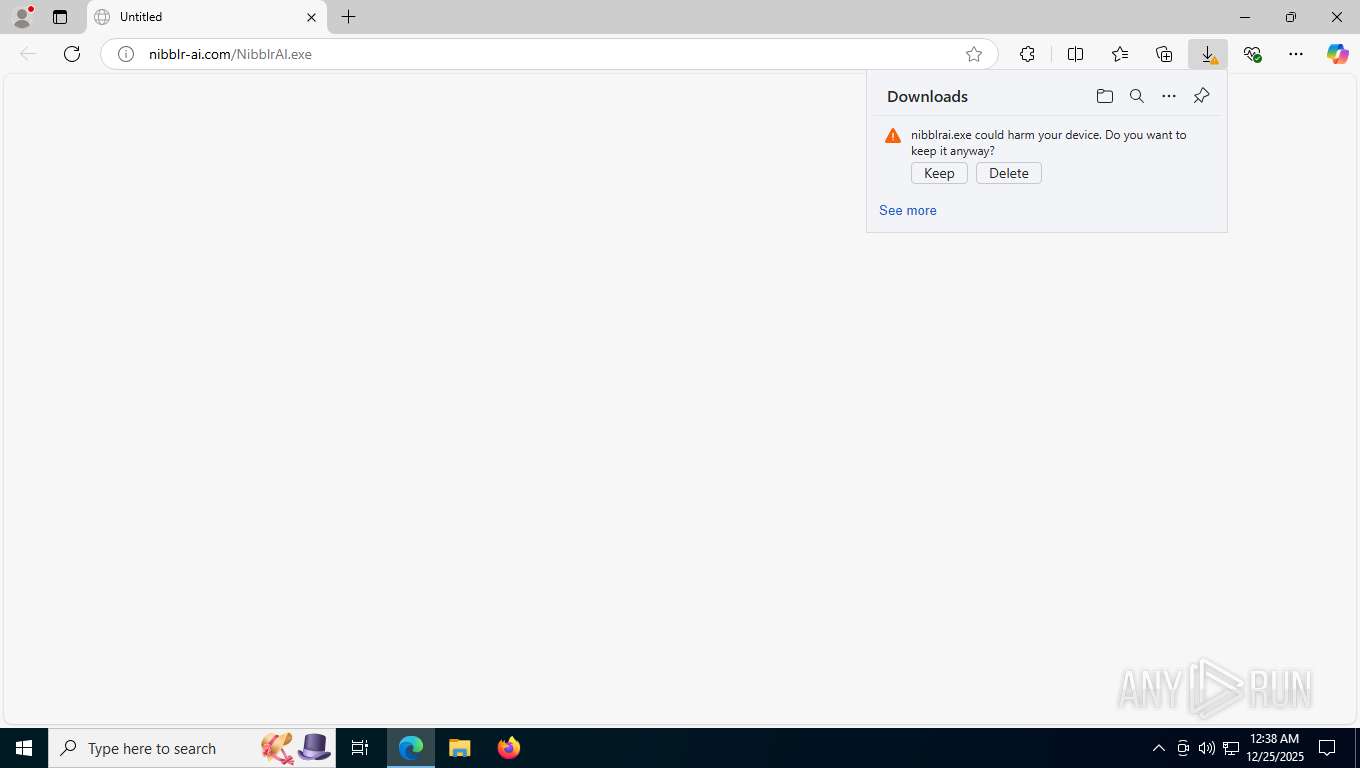
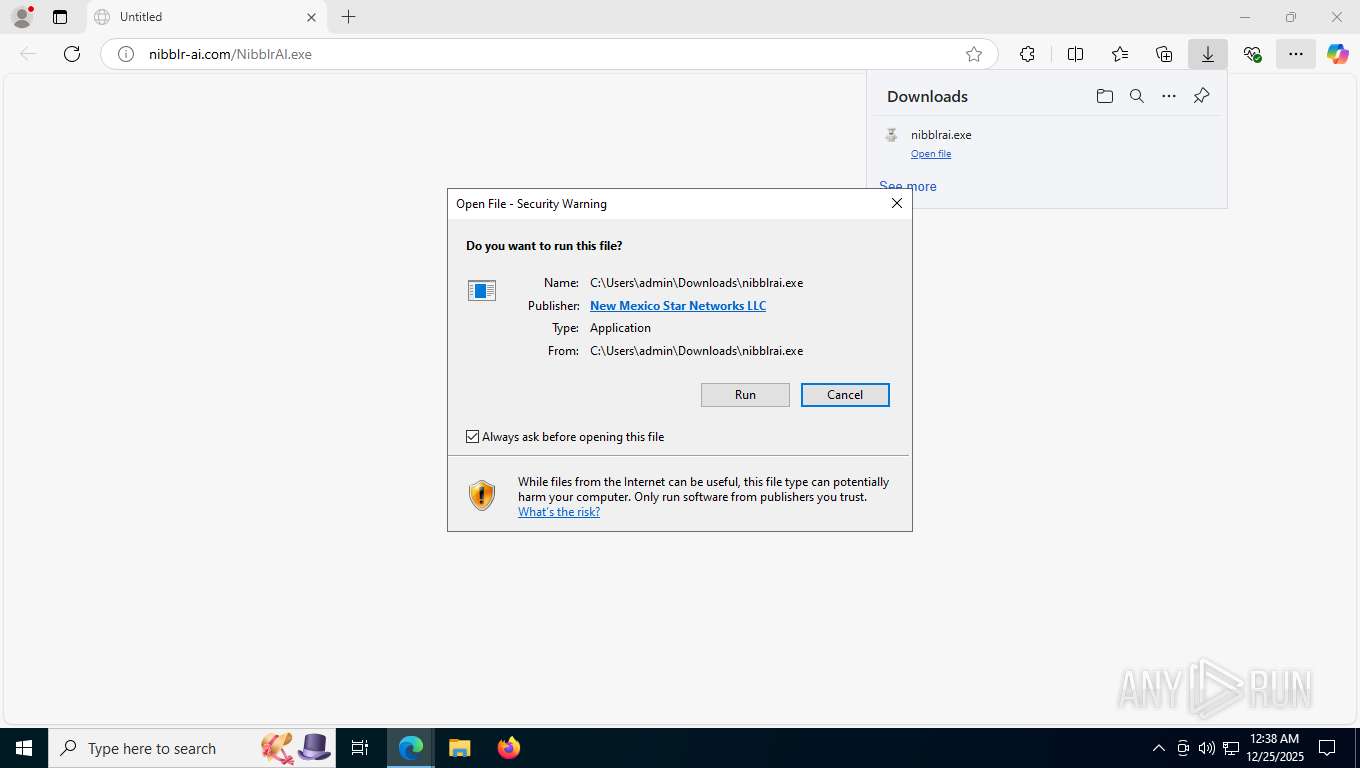
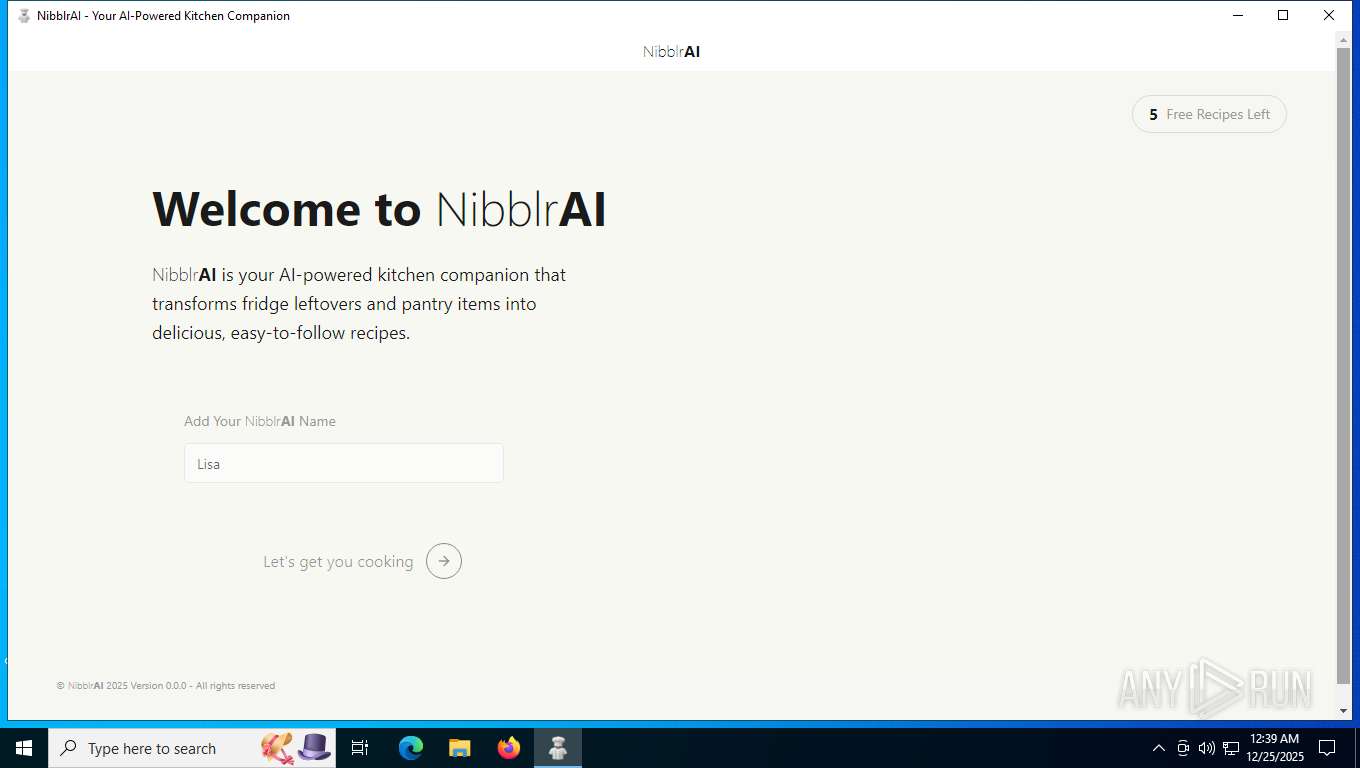
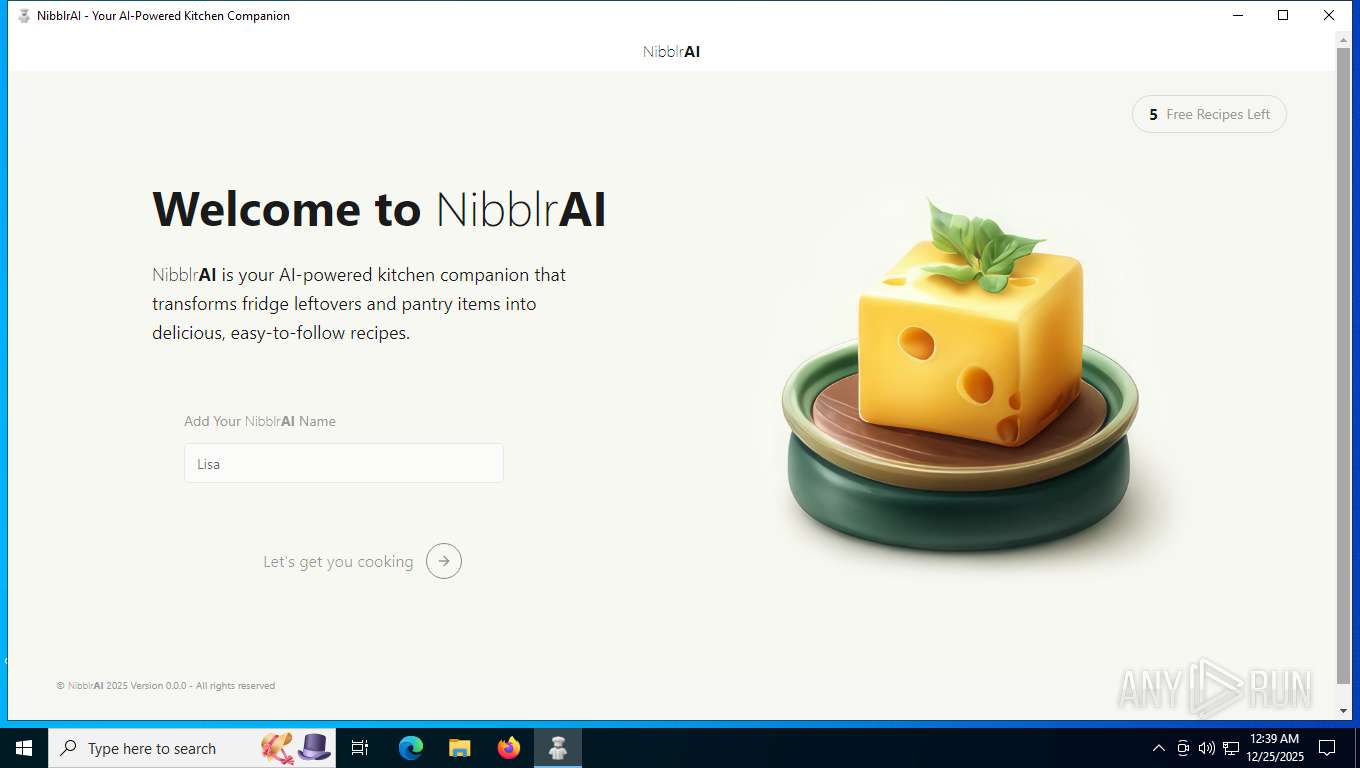
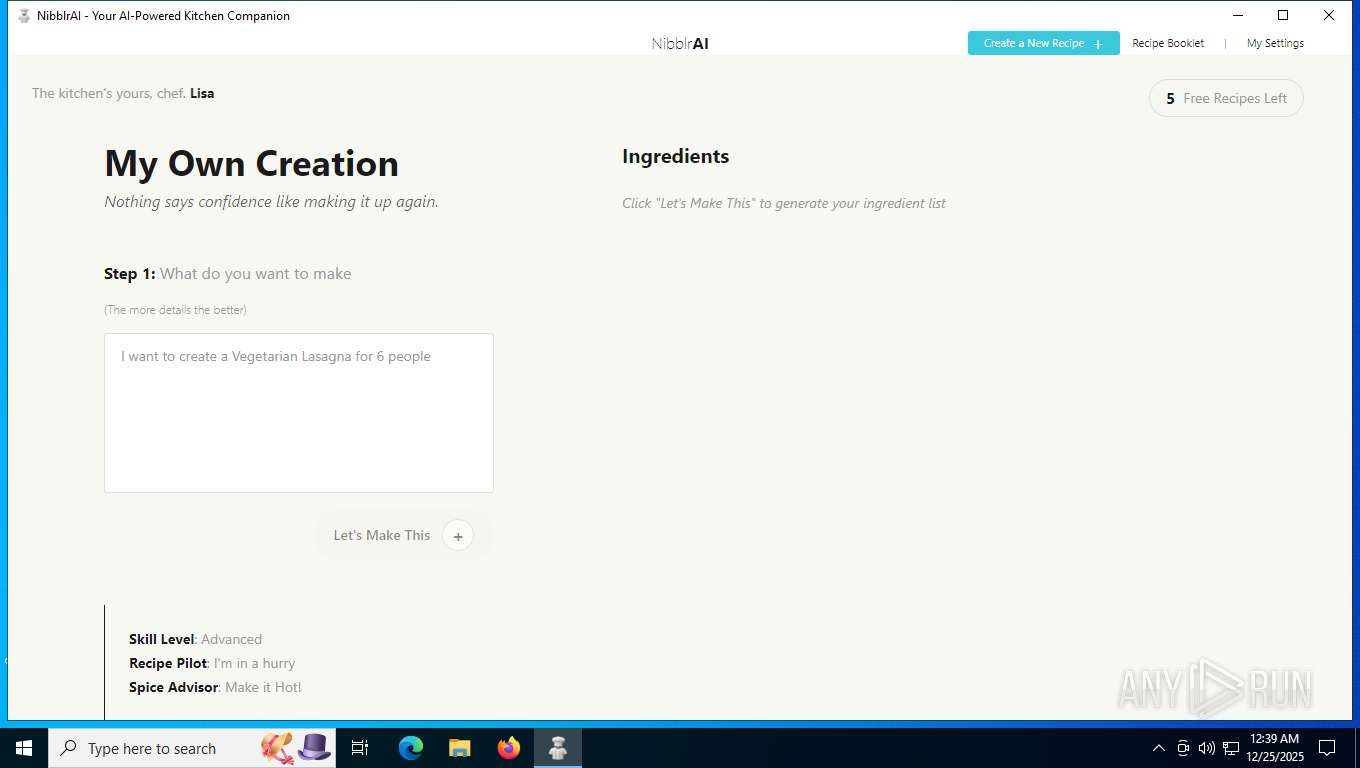
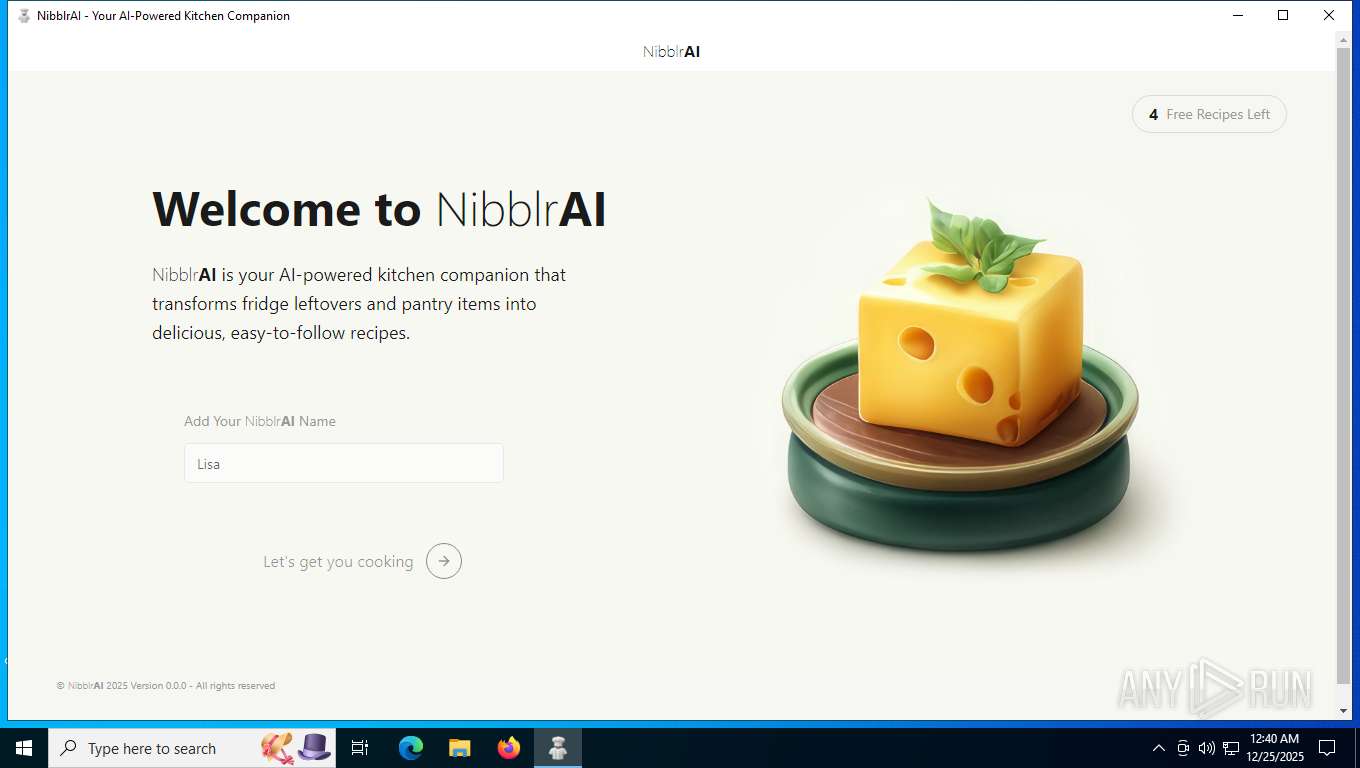
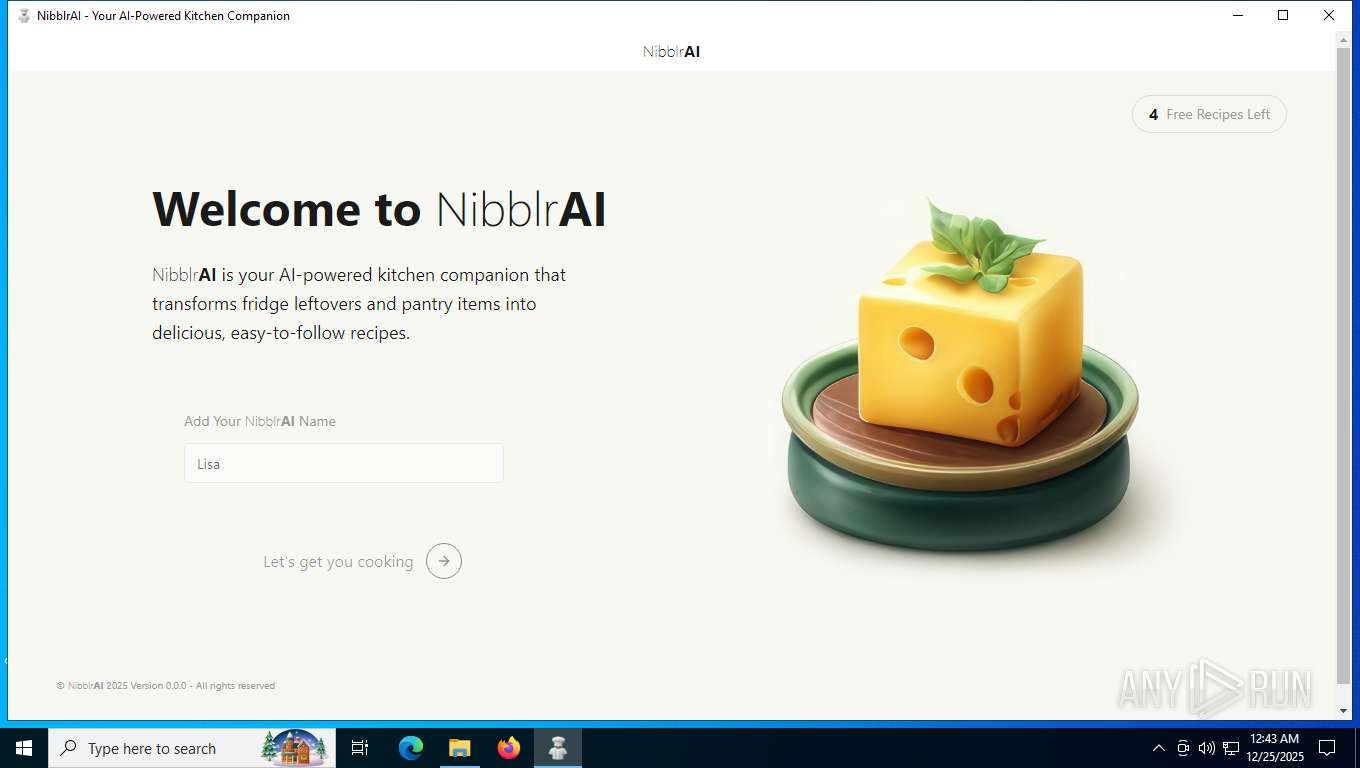
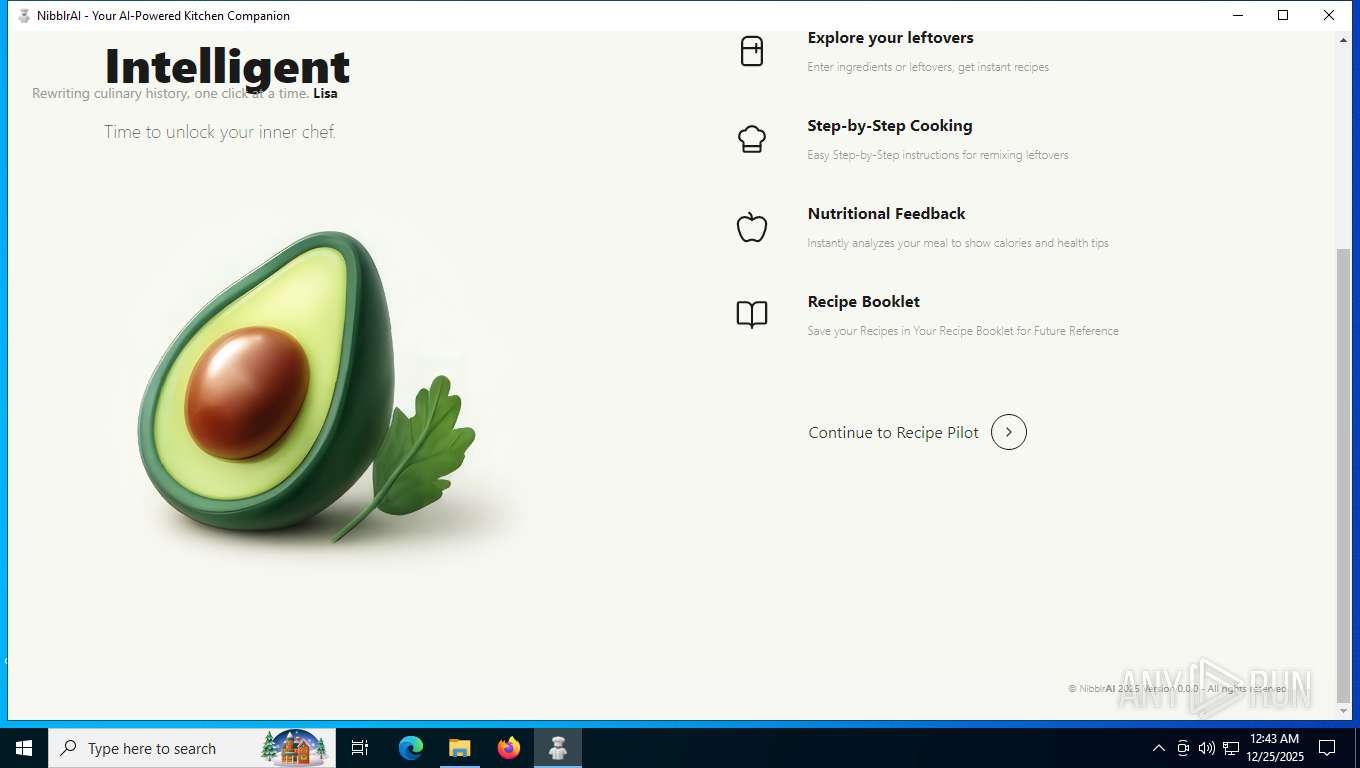
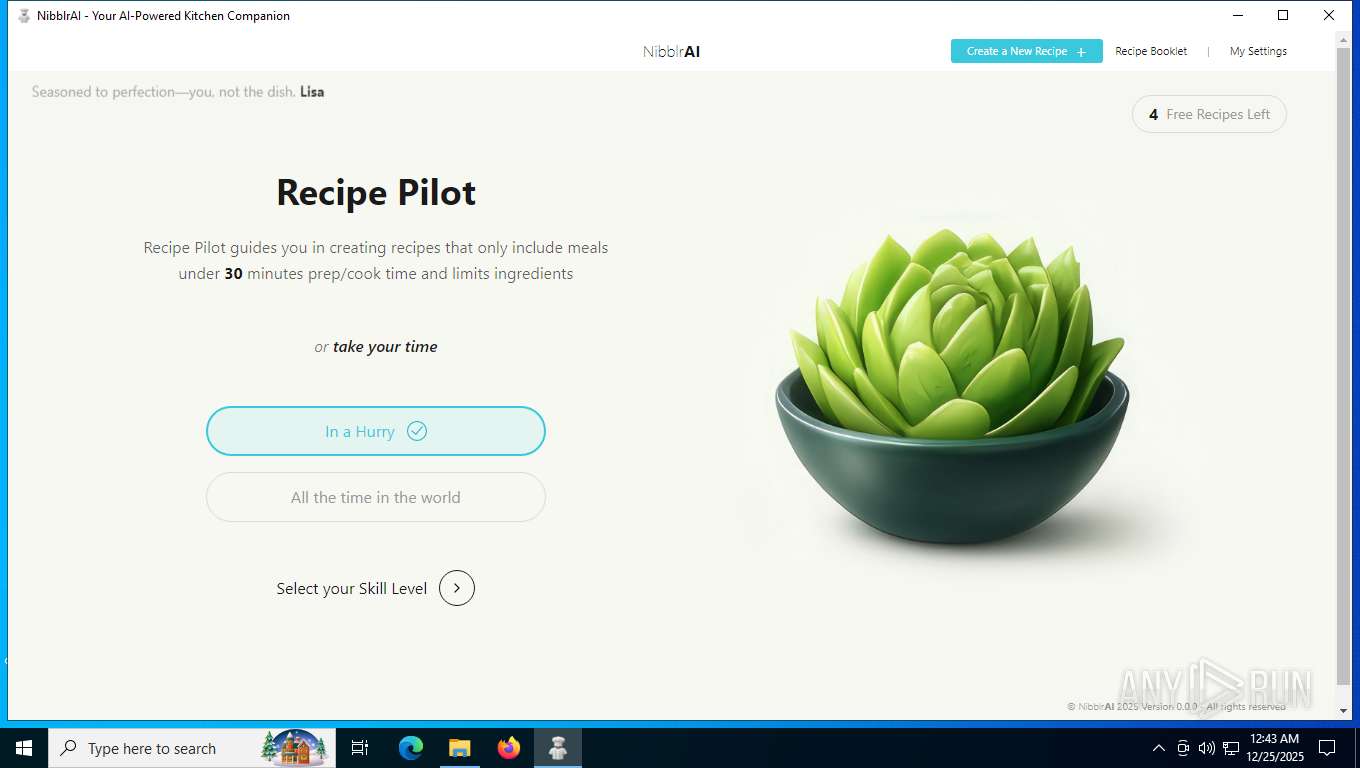
| URL: | nibblr-ai.com/NibblrAI.exe |
| Full analysis: | https://app.any.run/tasks/c3fe0c06-cbd6-4f1d-8917-787deab1f476 |
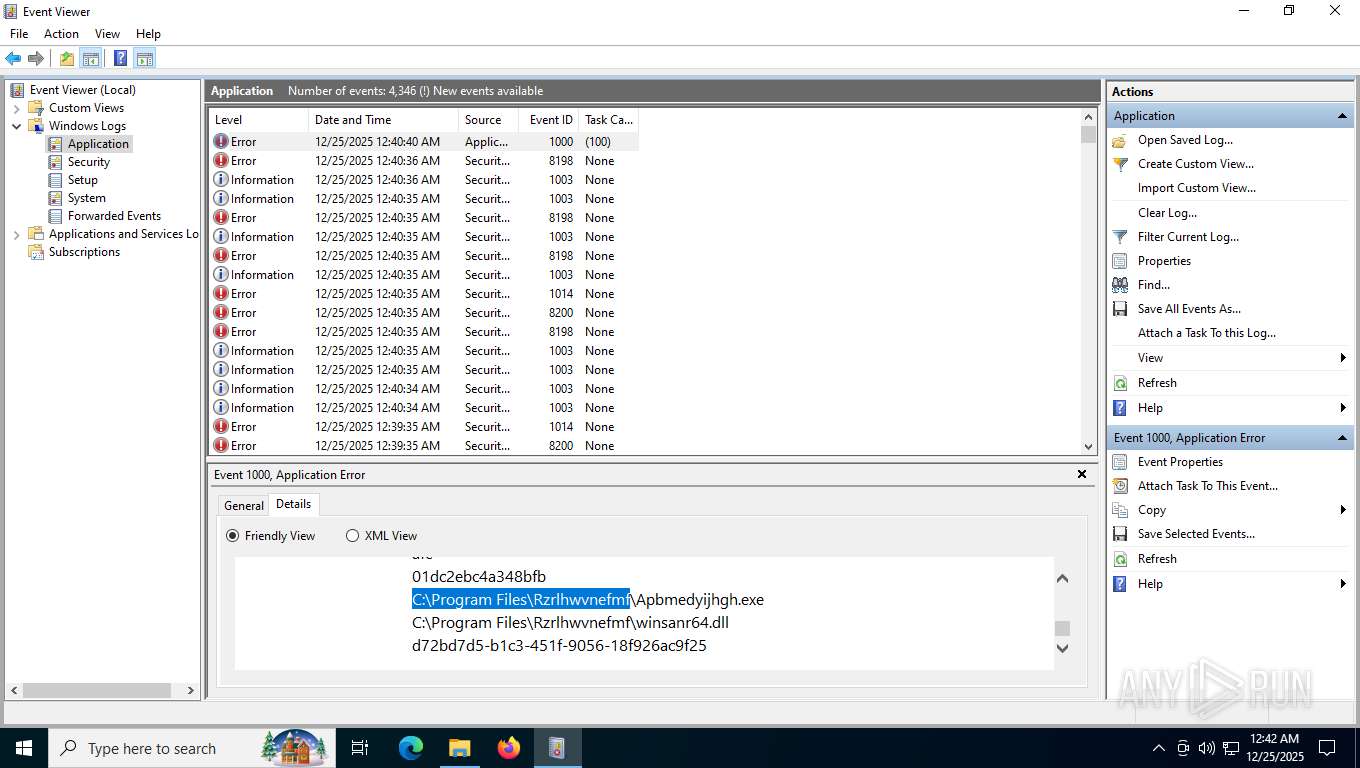
| Verdict: | Malicious activity |
| Analysis date: | December 25, 2025, 05:38:38 |
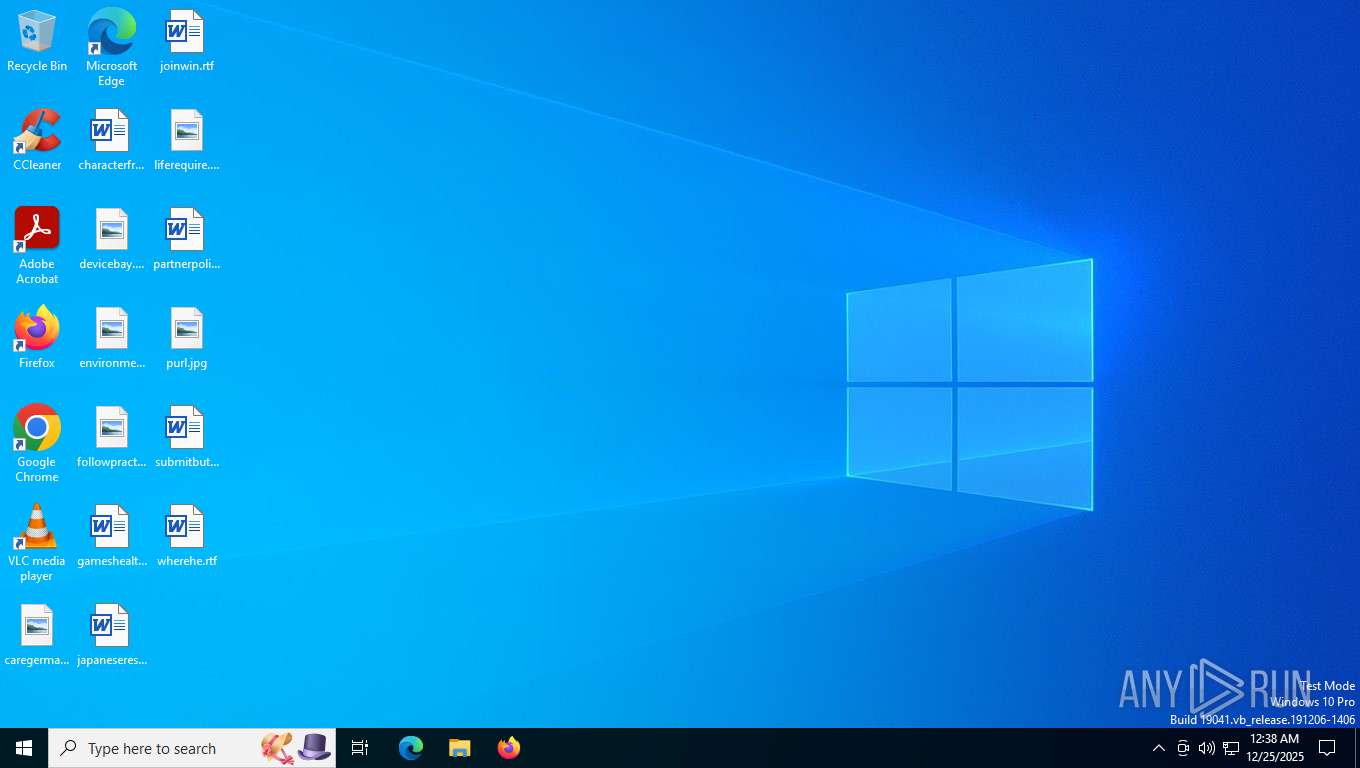
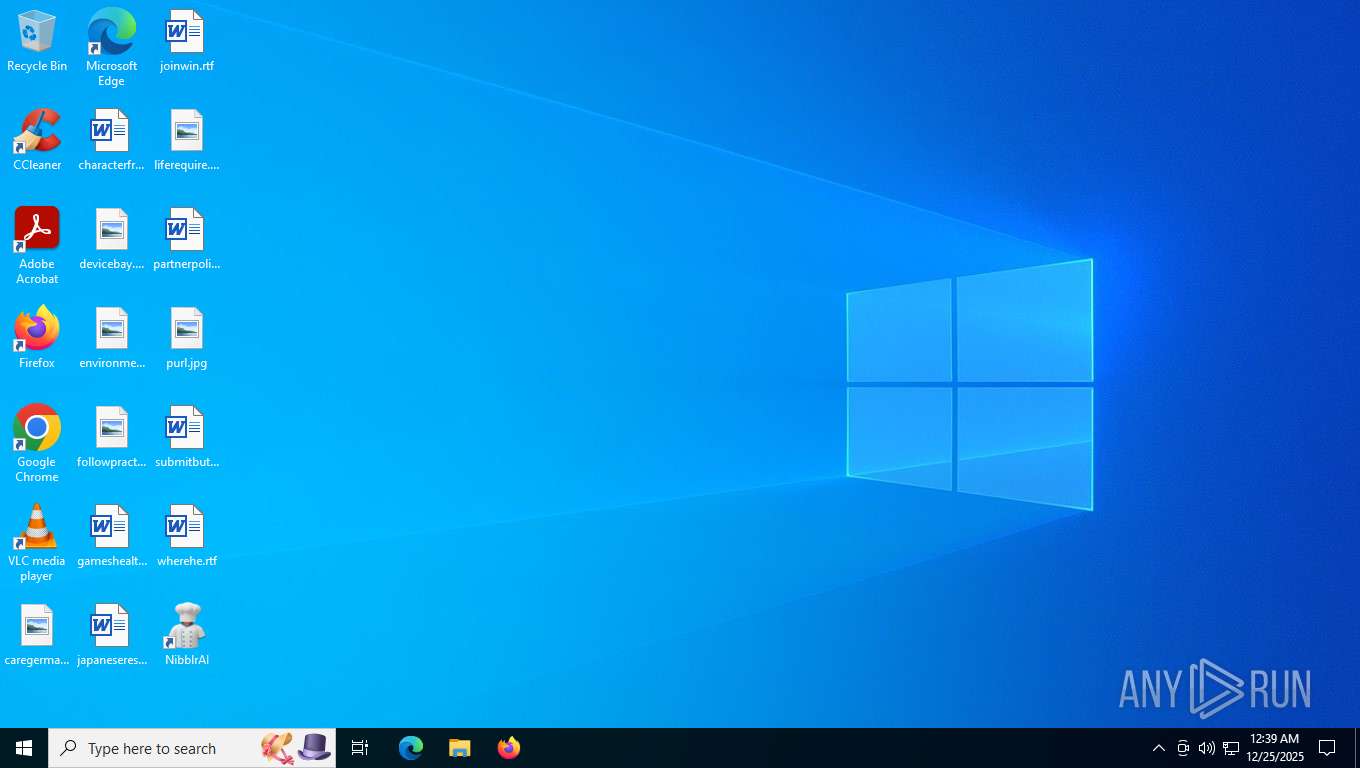
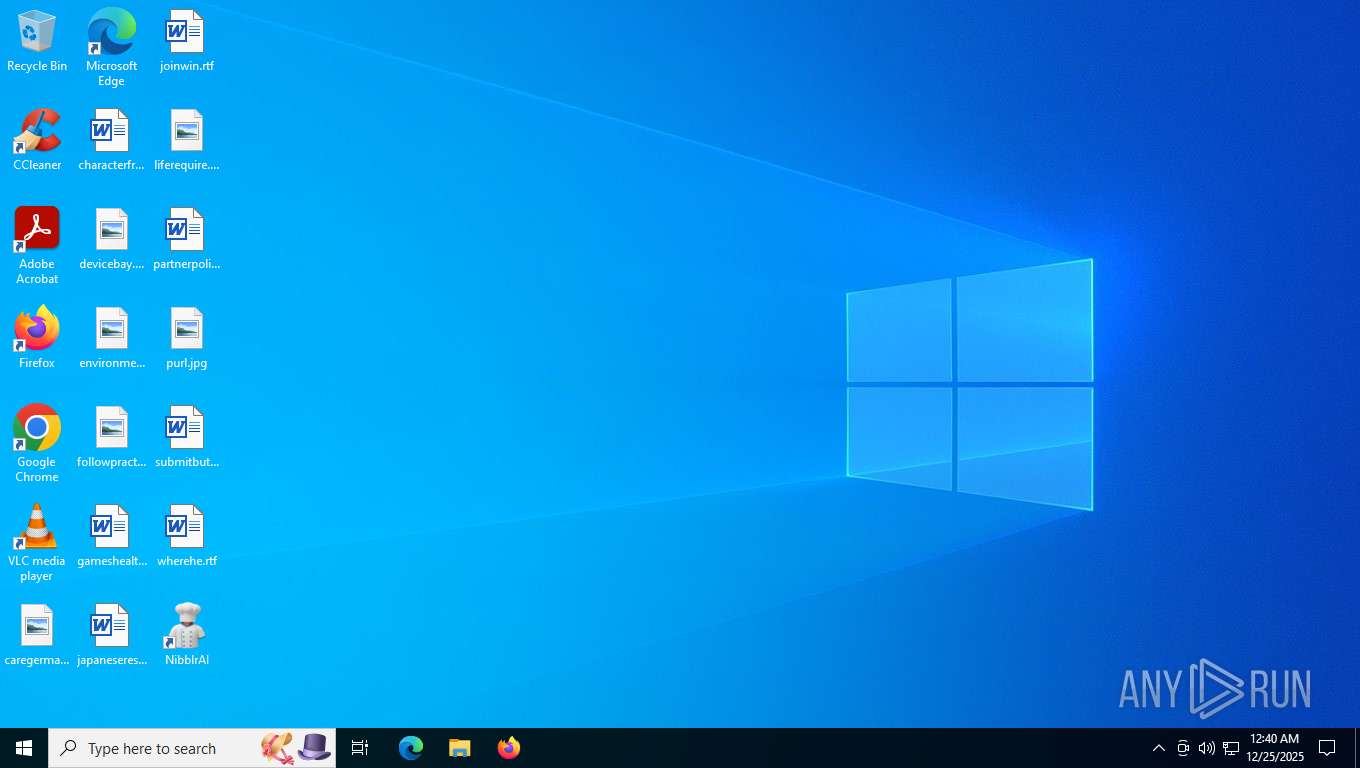
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 357DA8D33911822EA820A3B307646338 |
| SHA1: | DB9D0E7083B495DADF84FE6B2E79F624EF93F723 |
| SHA256: | B2FB4E7624BD18D3E1C216B76556D42D5550D1C3C043A8812BBE4FE36CC0125F |
| SSDEEP: | 3:c+NMJ:sJ |
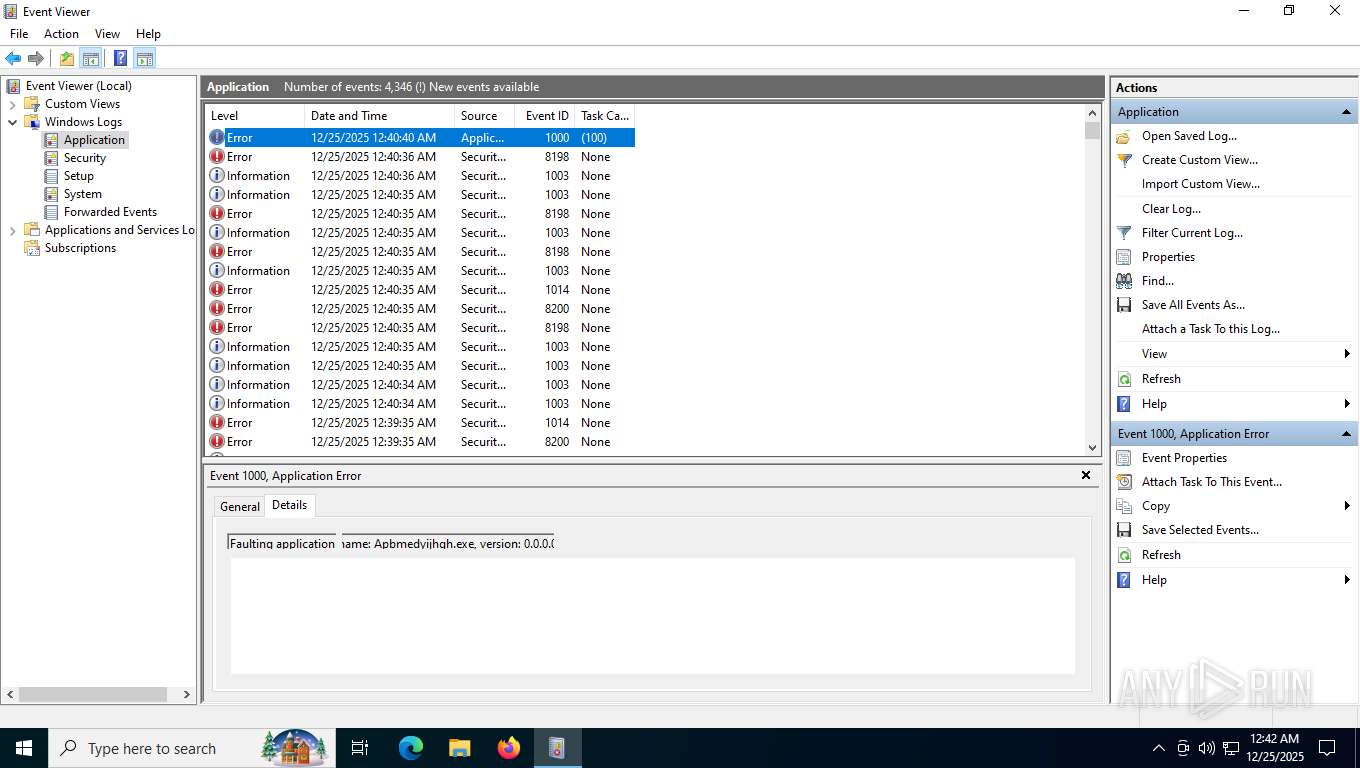
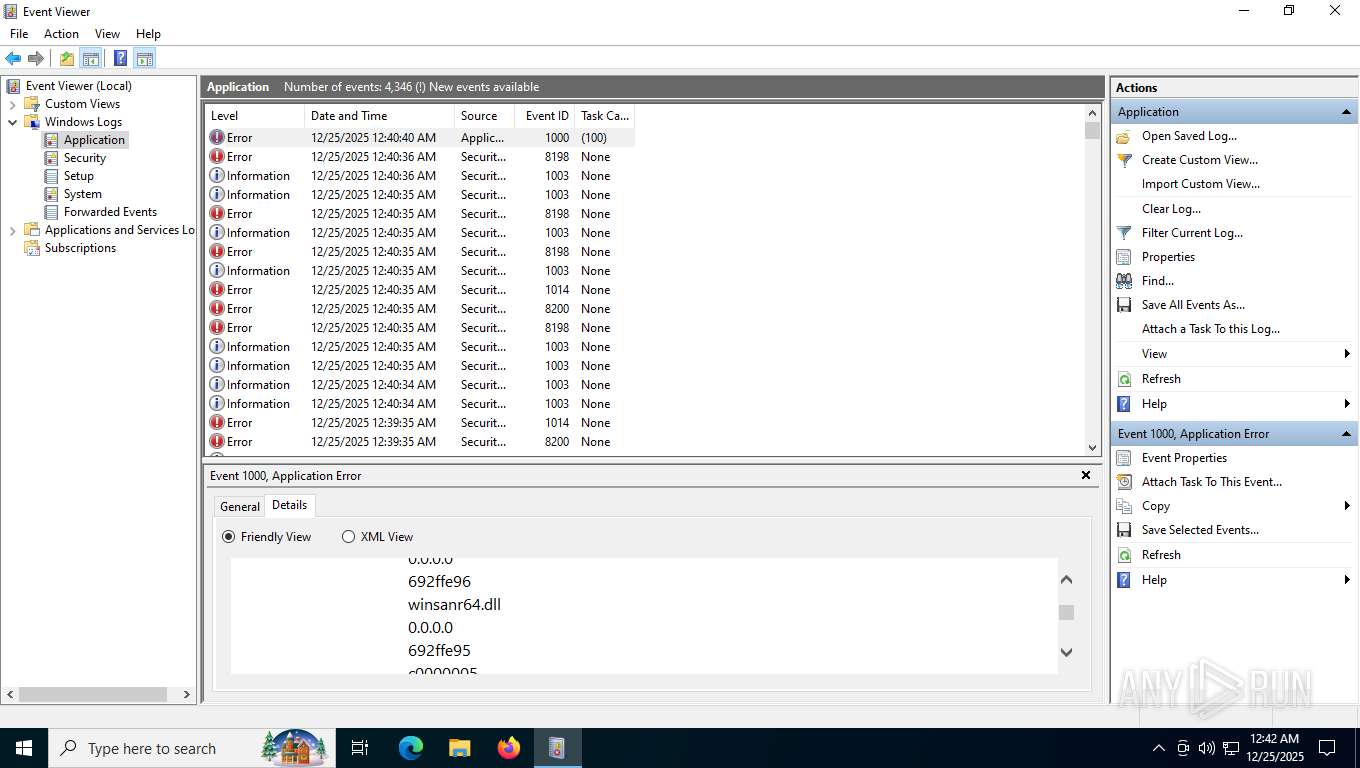
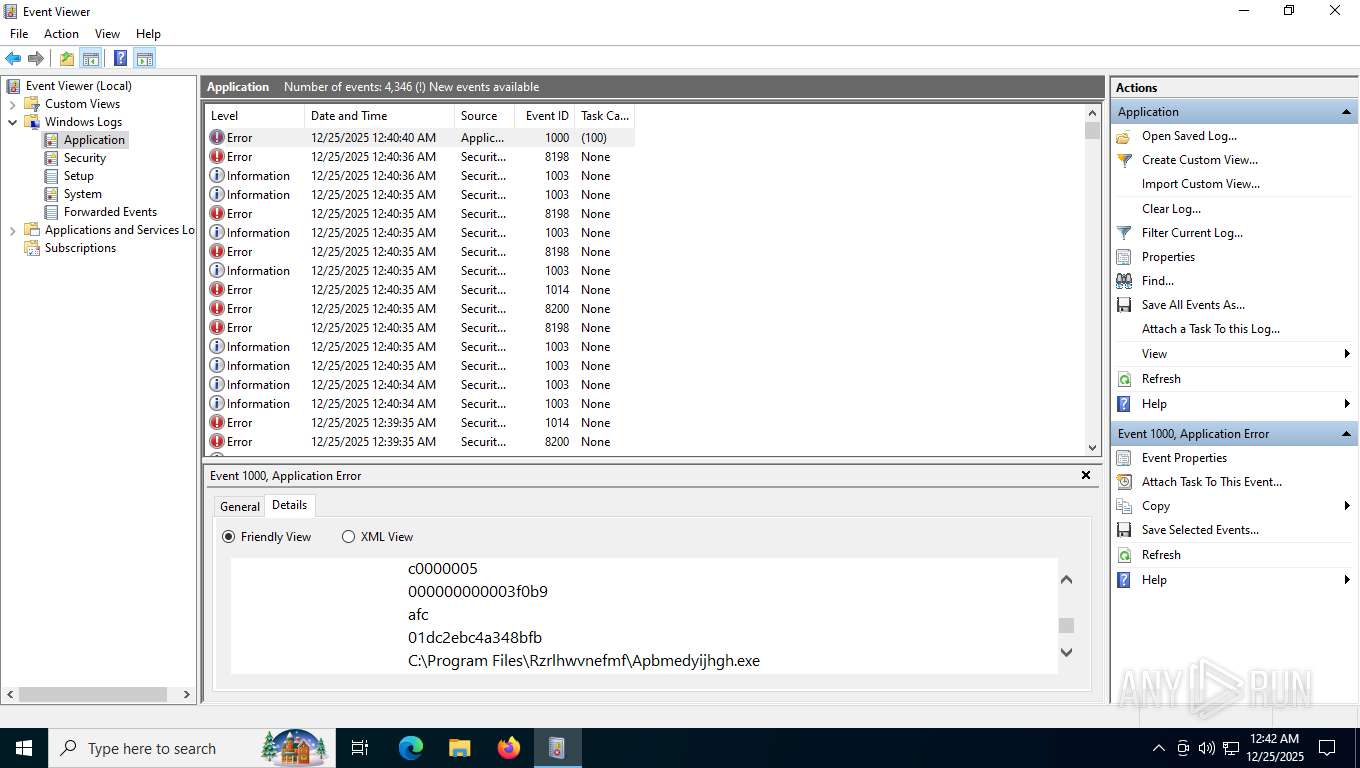
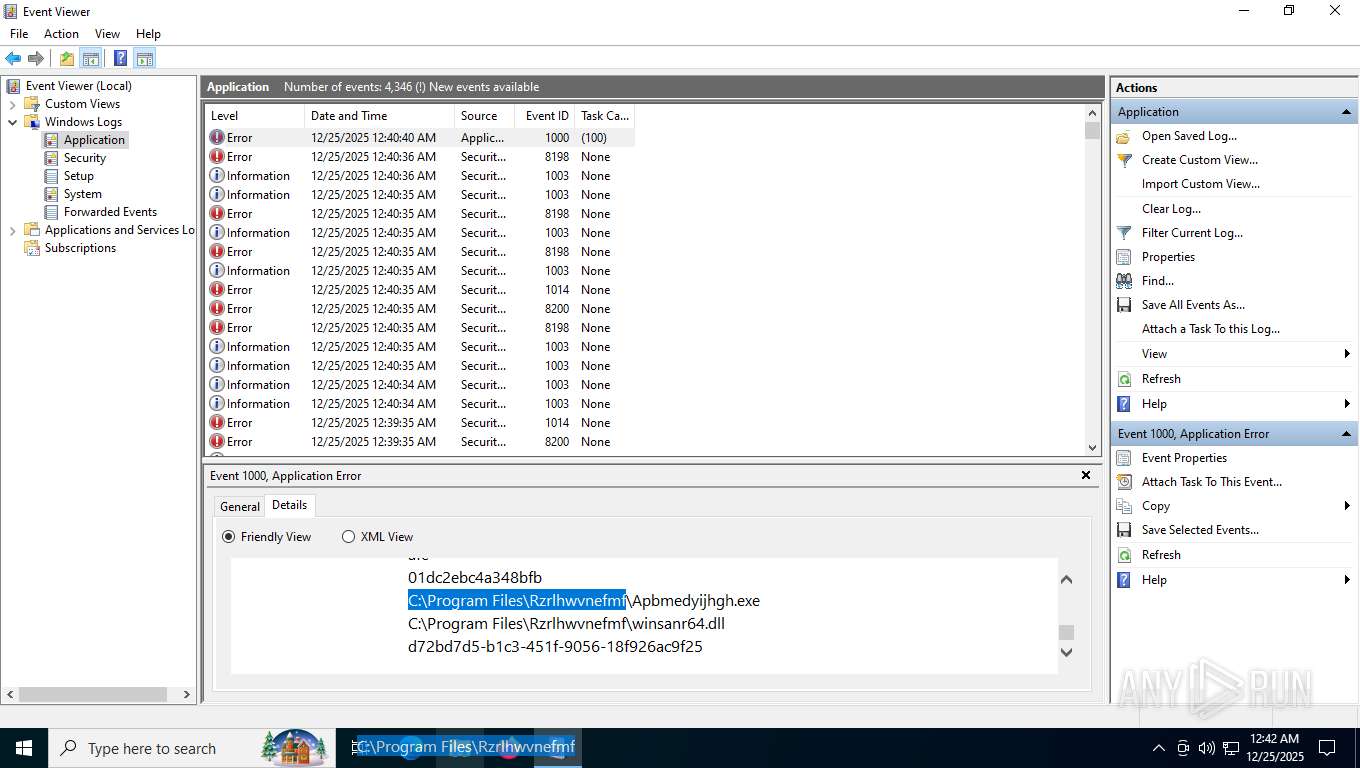
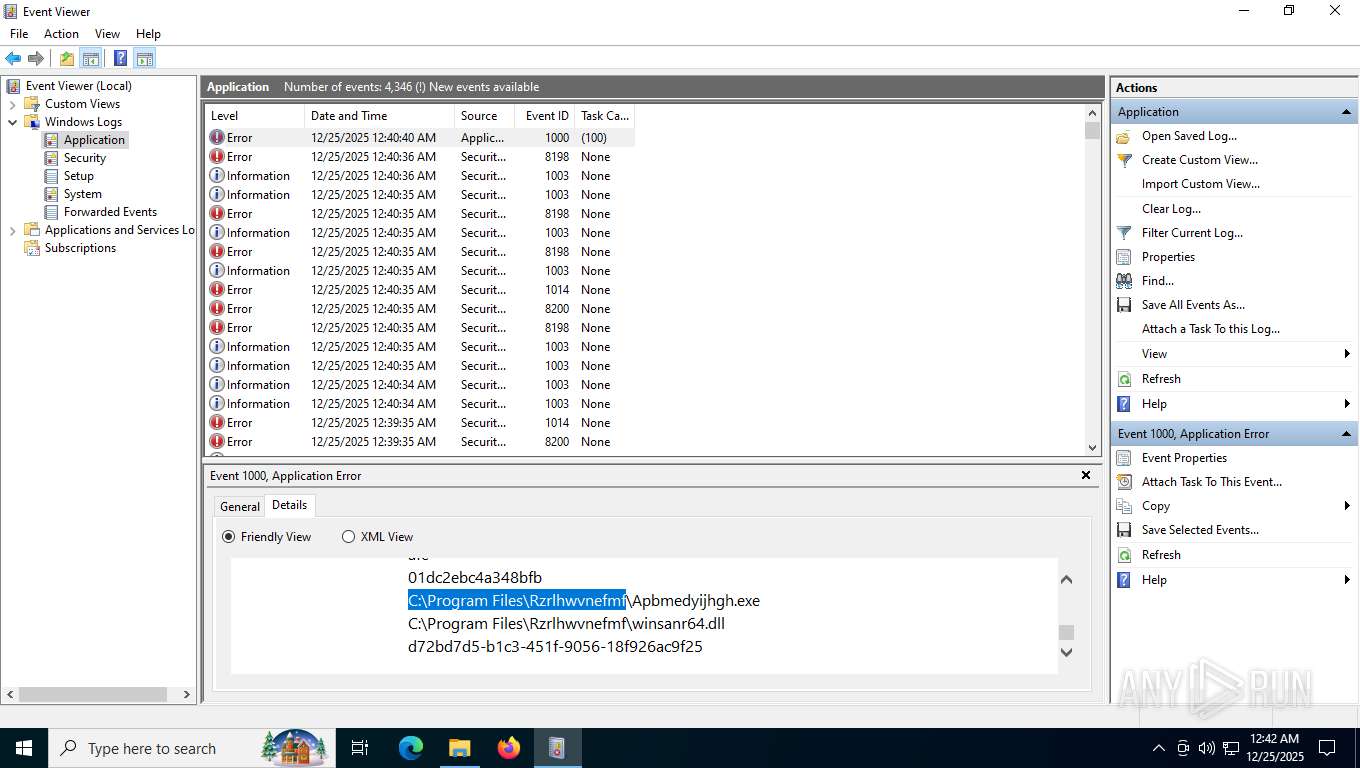
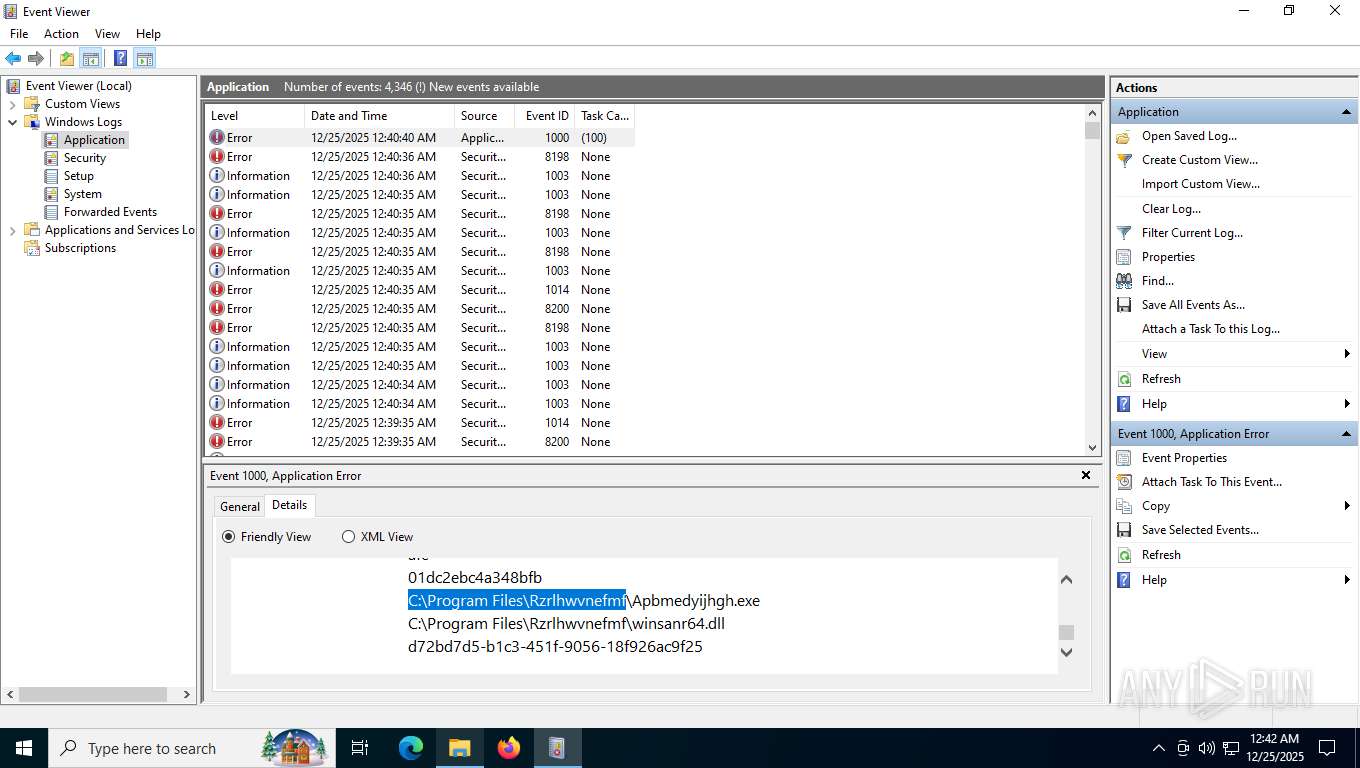
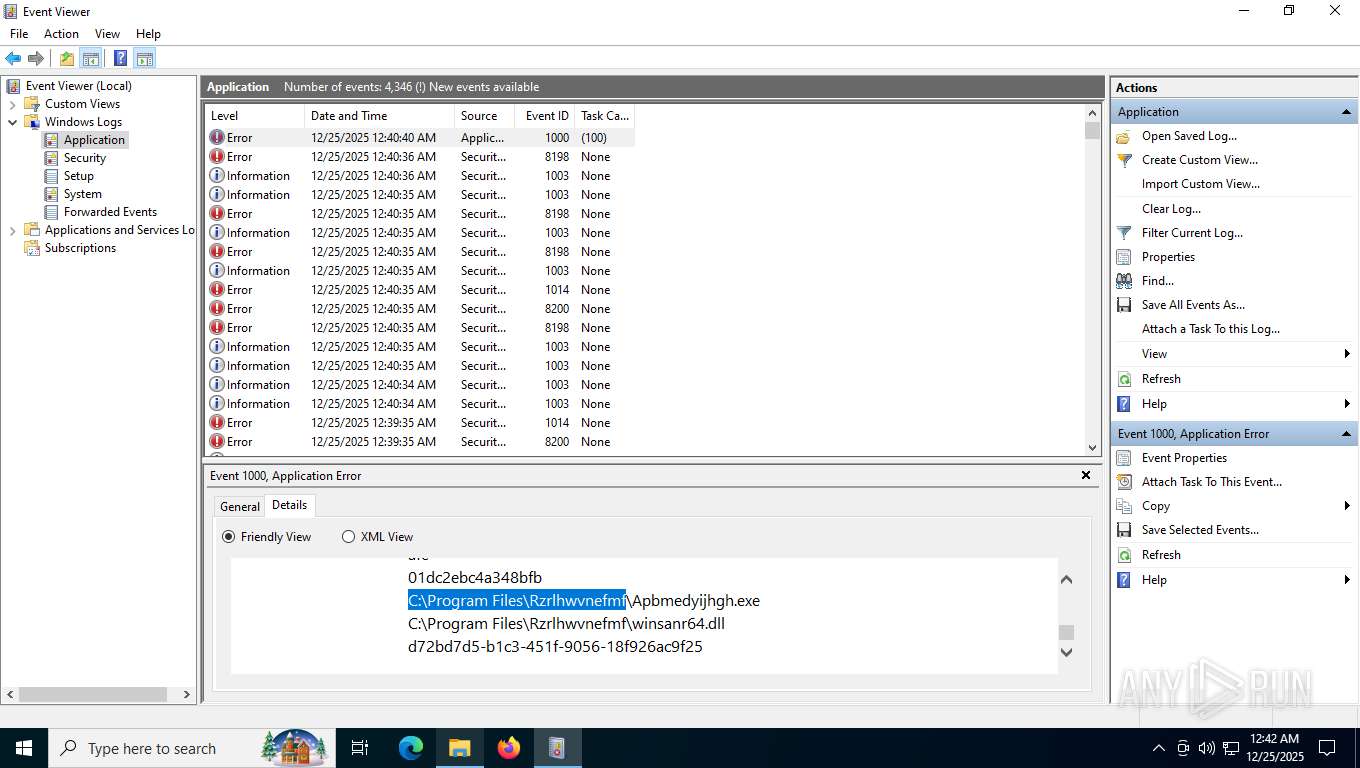
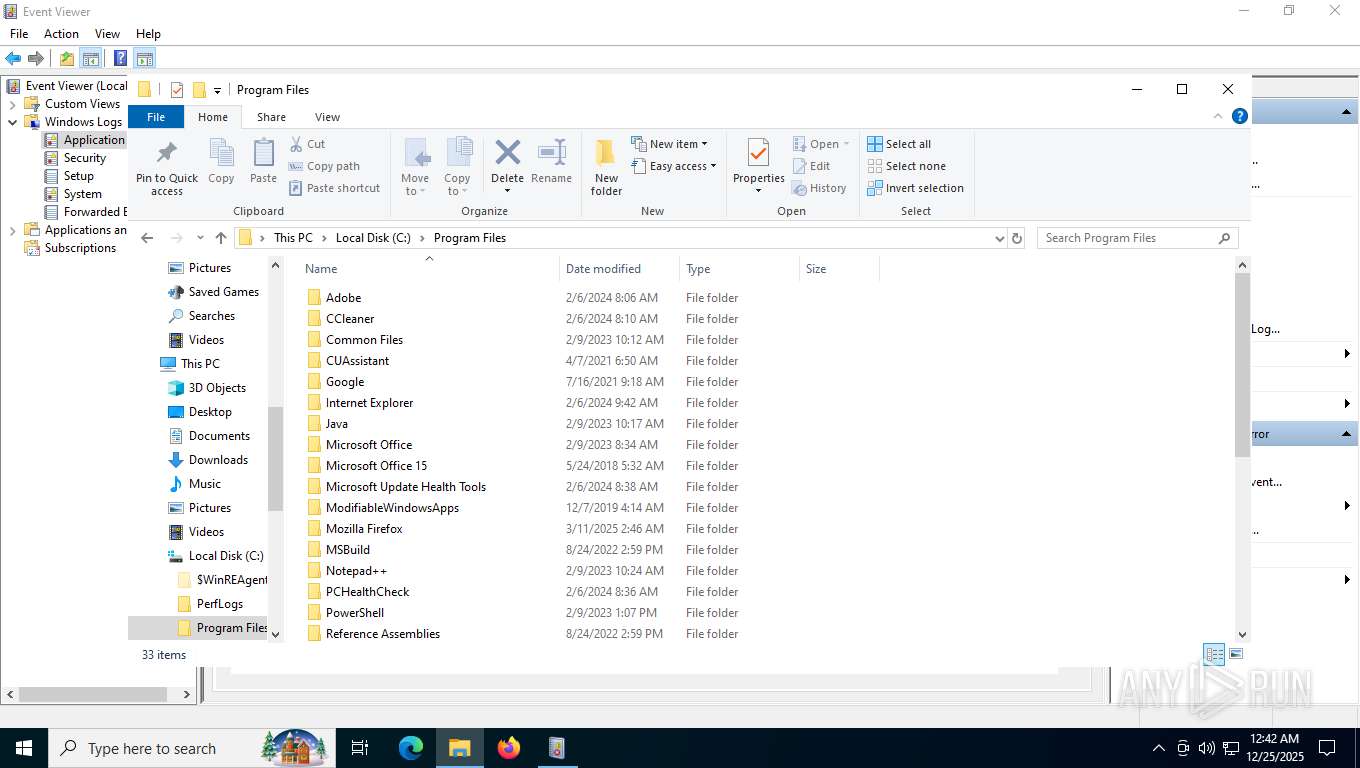
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Windows owner or organization settings
- nibblrai.tmp (PID: 8708)
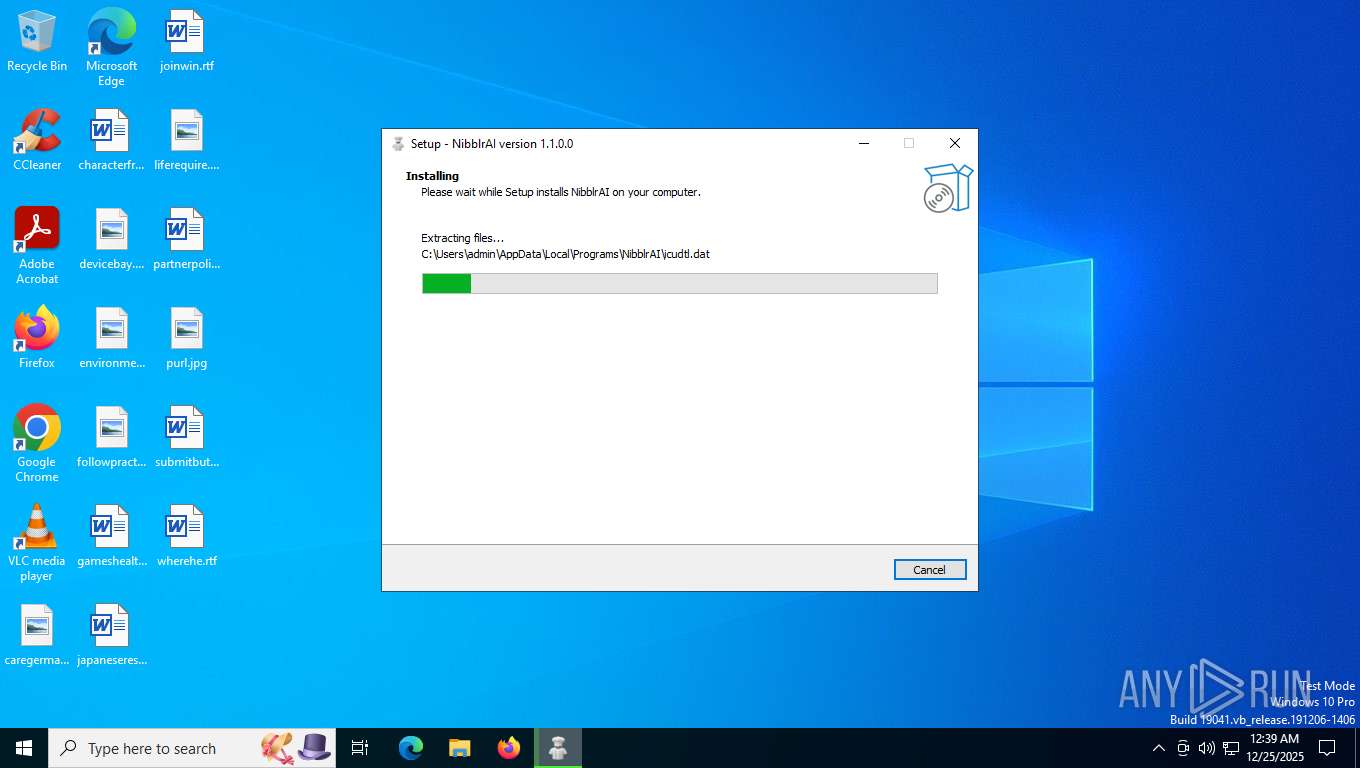
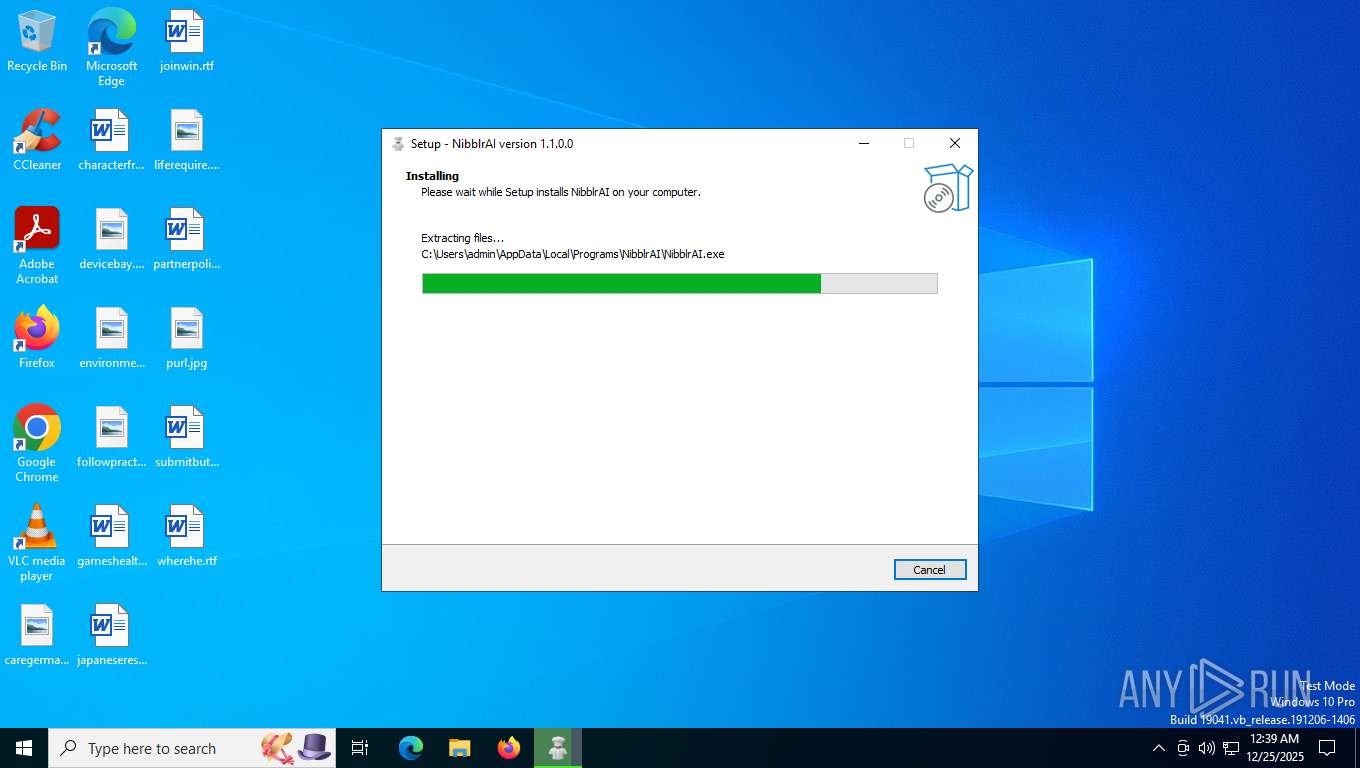
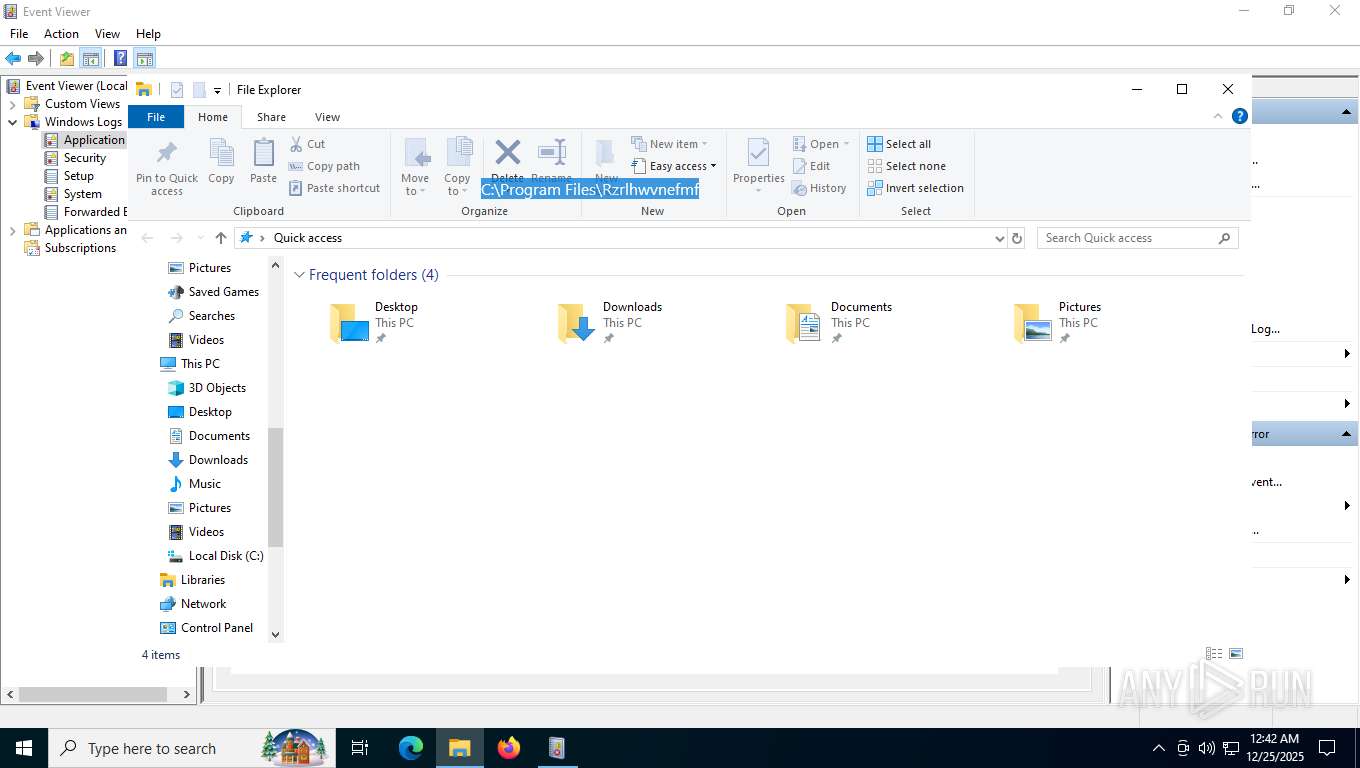
Executable content was dropped or overwritten
- nibblrai.exe (PID: 8688)
- nibblrai.tmp (PID: 8708)
Process drops legitimate windows executable
- nibblrai.tmp (PID: 8708)
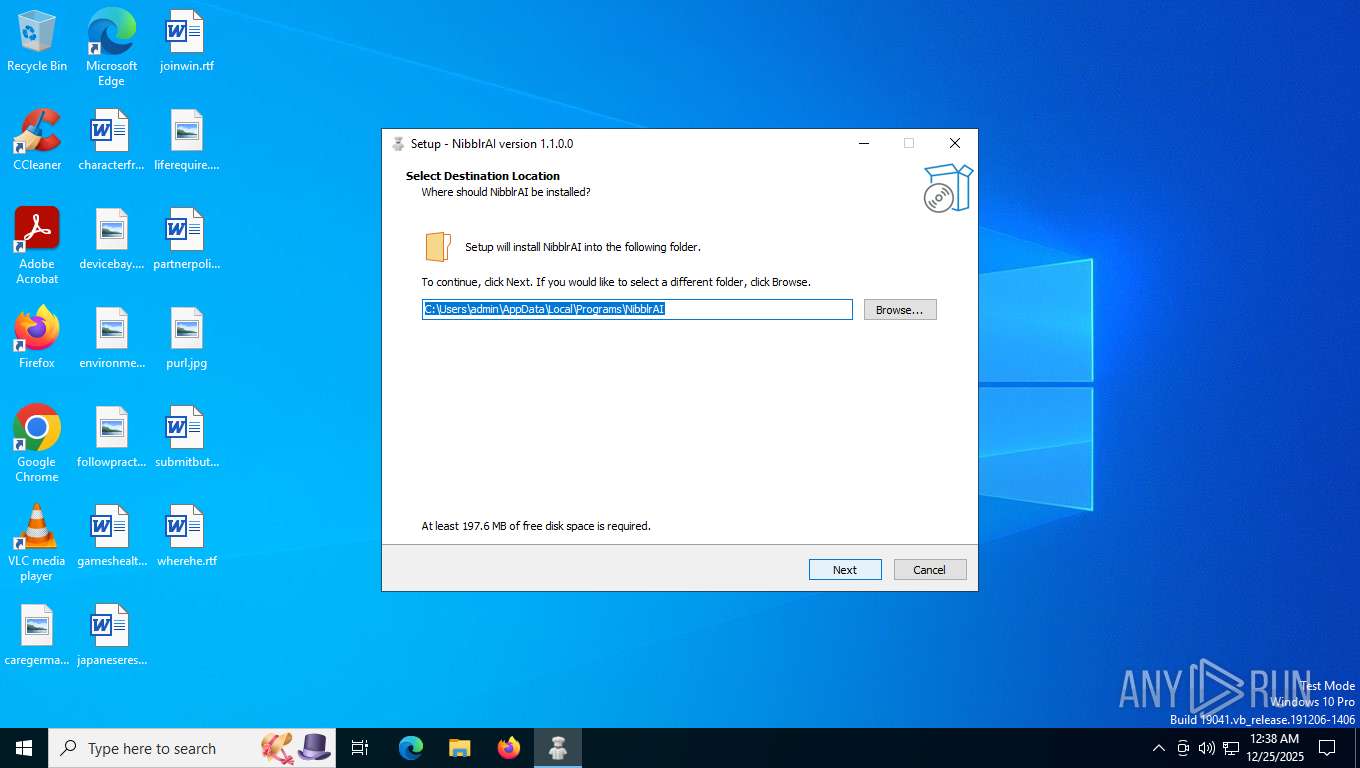
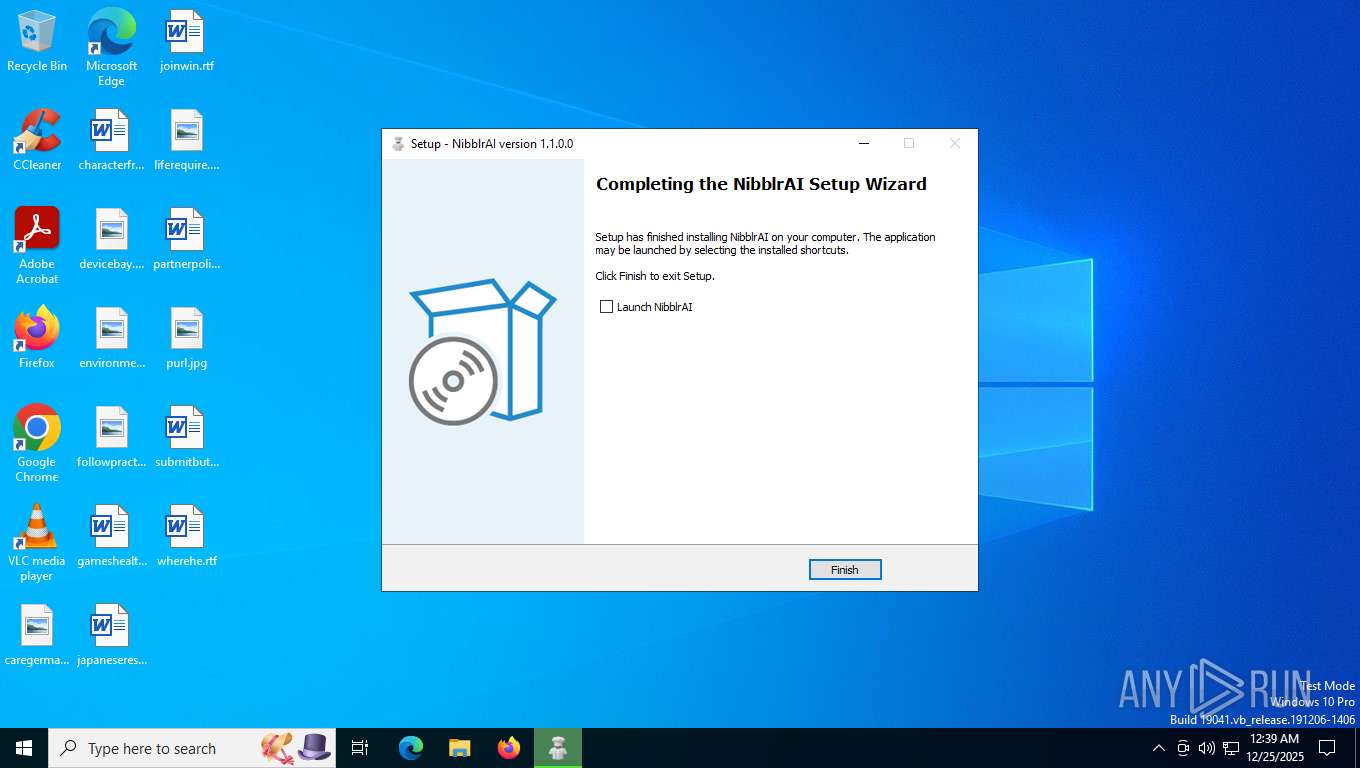
Application launched itself
- NibblrAI.exe (PID: 8356)
- NibblrAI.exe (PID: 7976)
- NibblrAI.exe (PID: 7240)
Found regular expressions for crypto-addresses (YARA)
- NibblrAI.exe (PID: 8548)
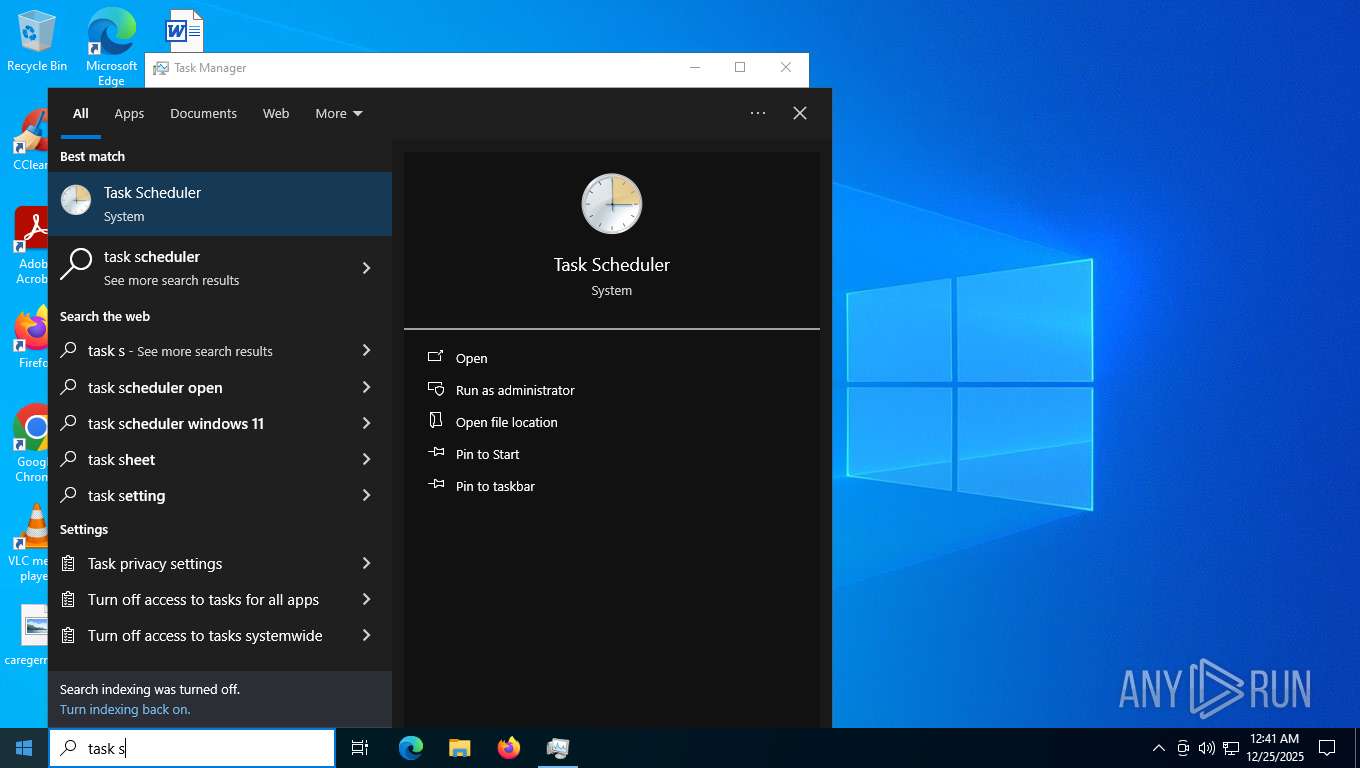
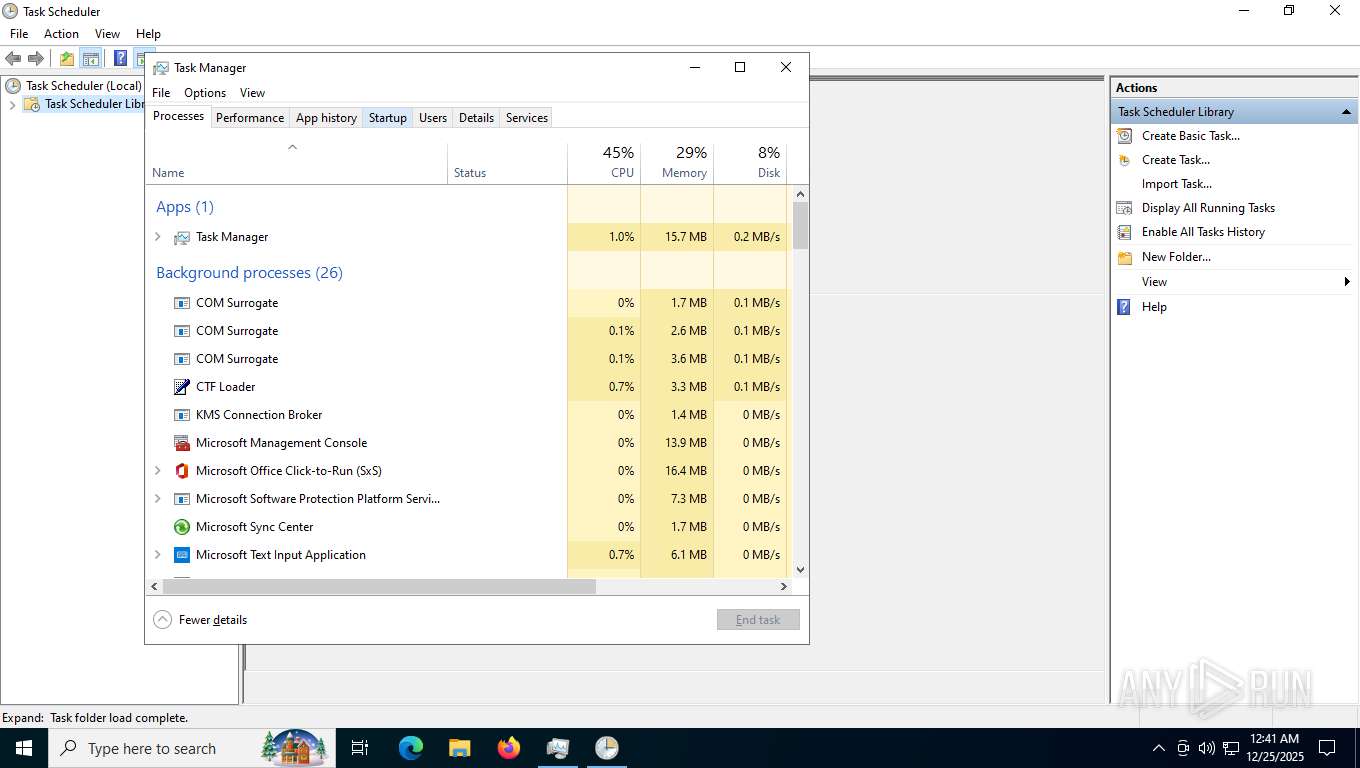
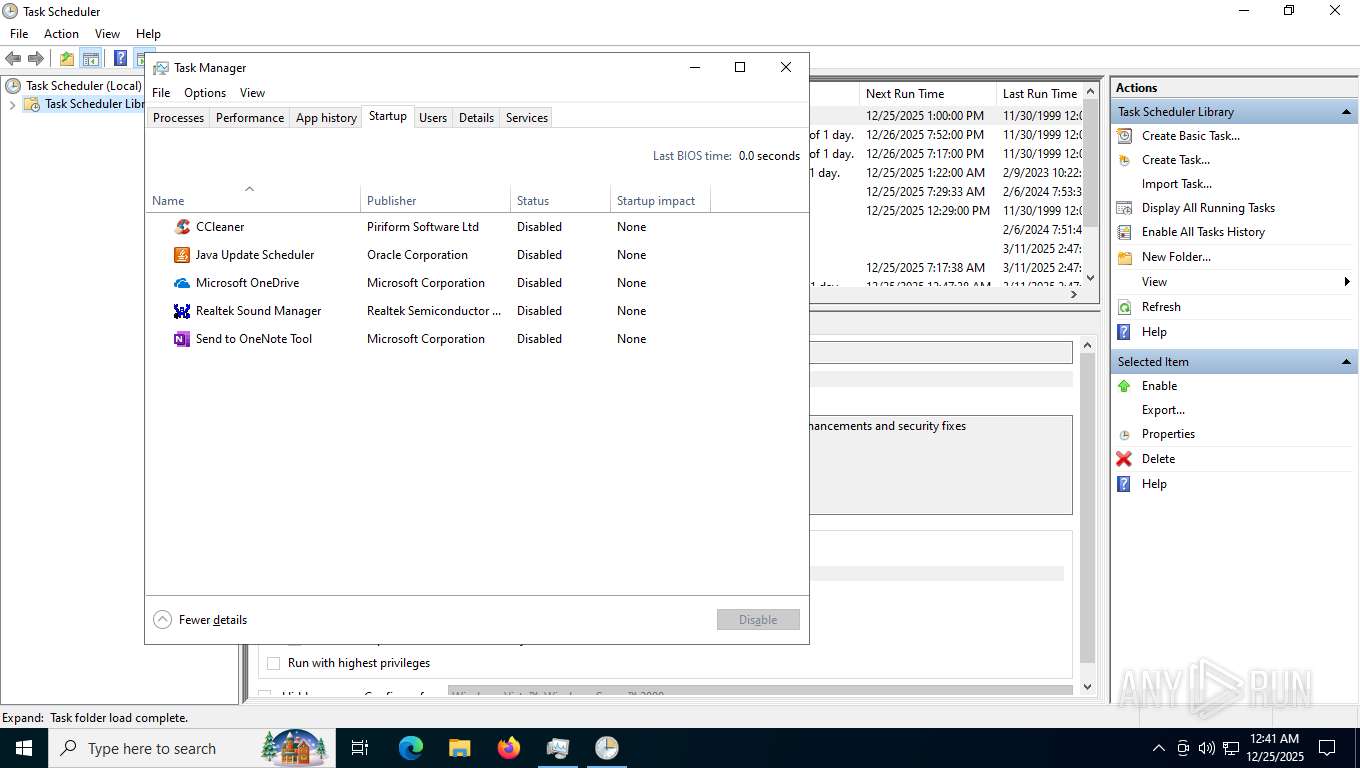
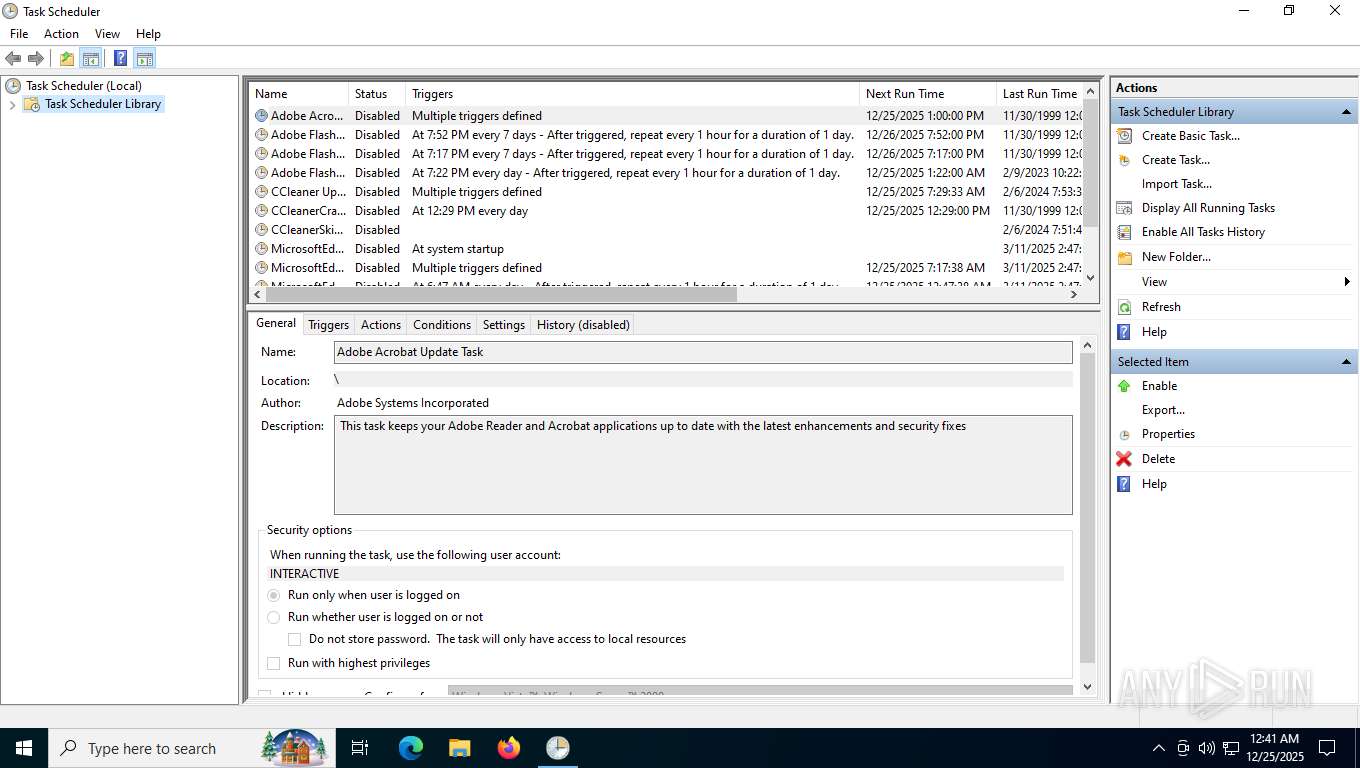
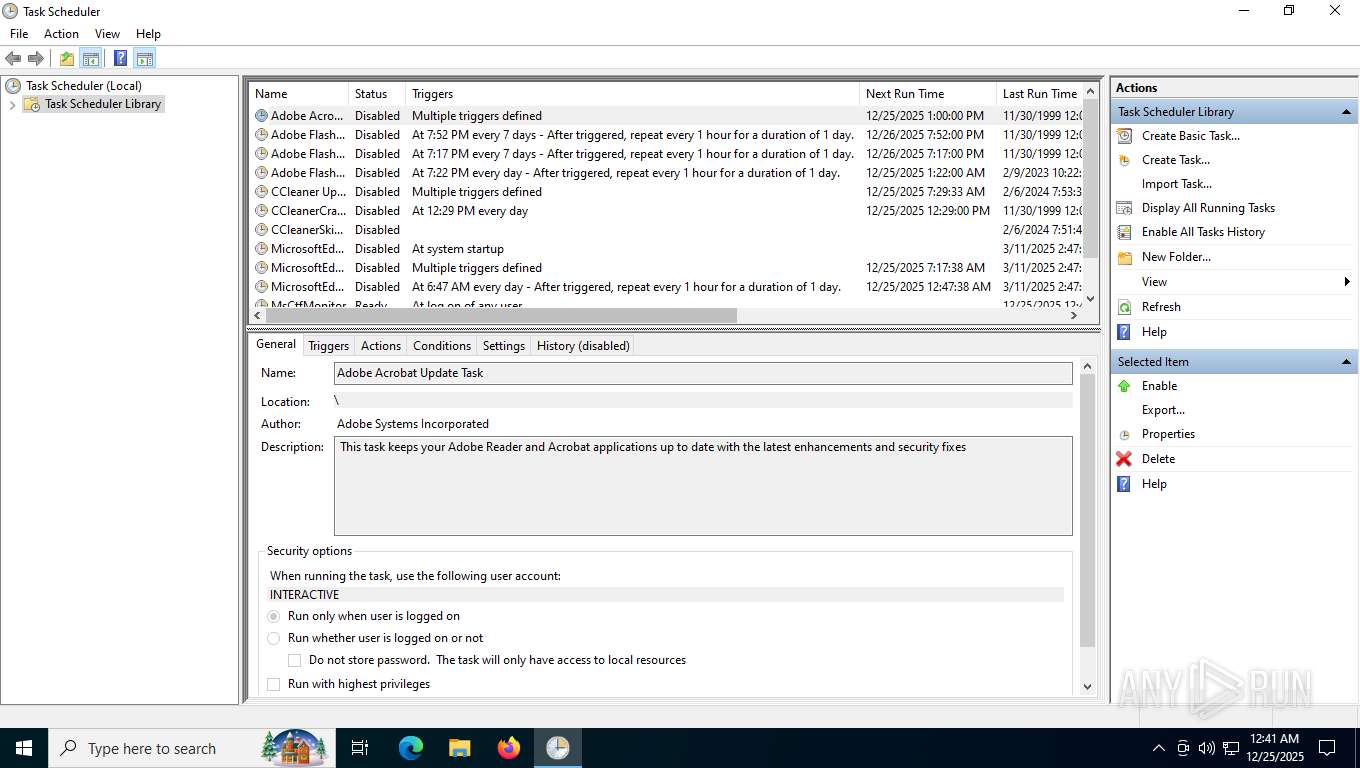
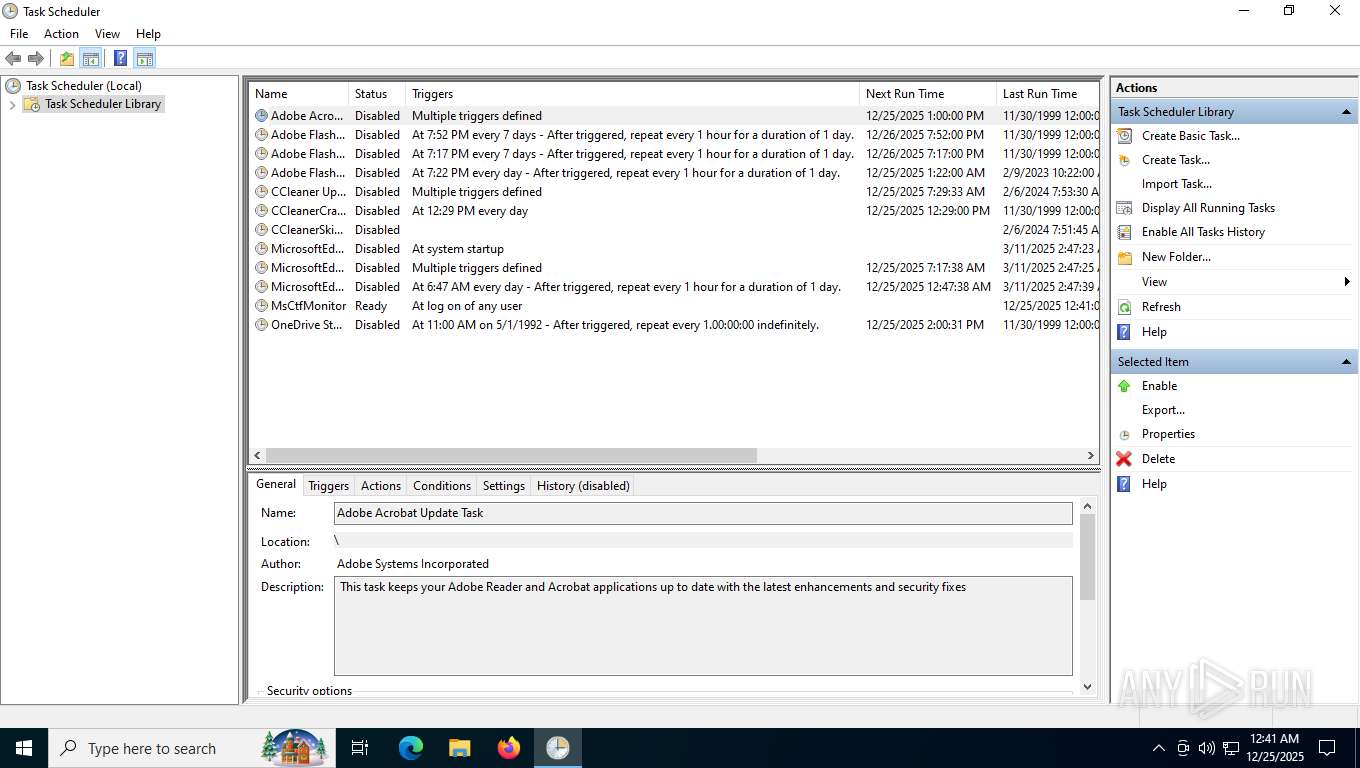
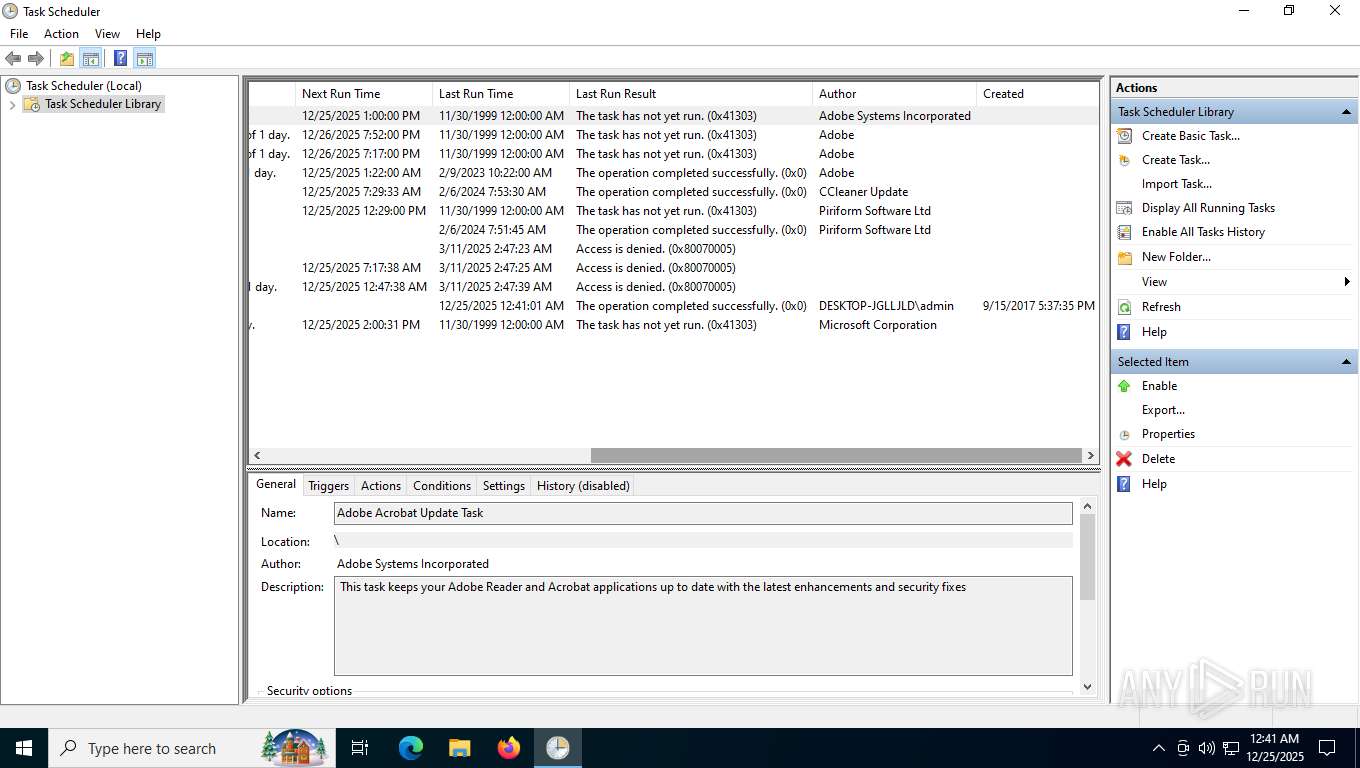
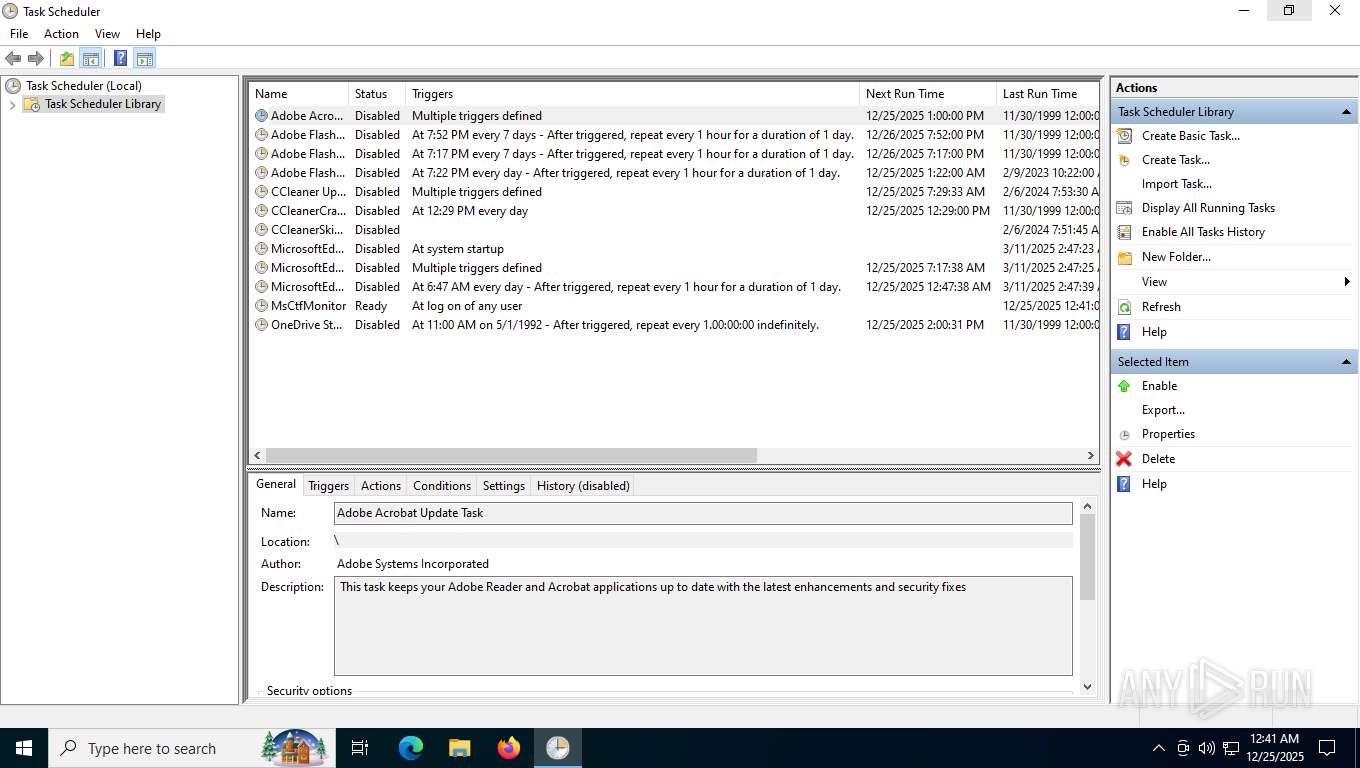
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4300)
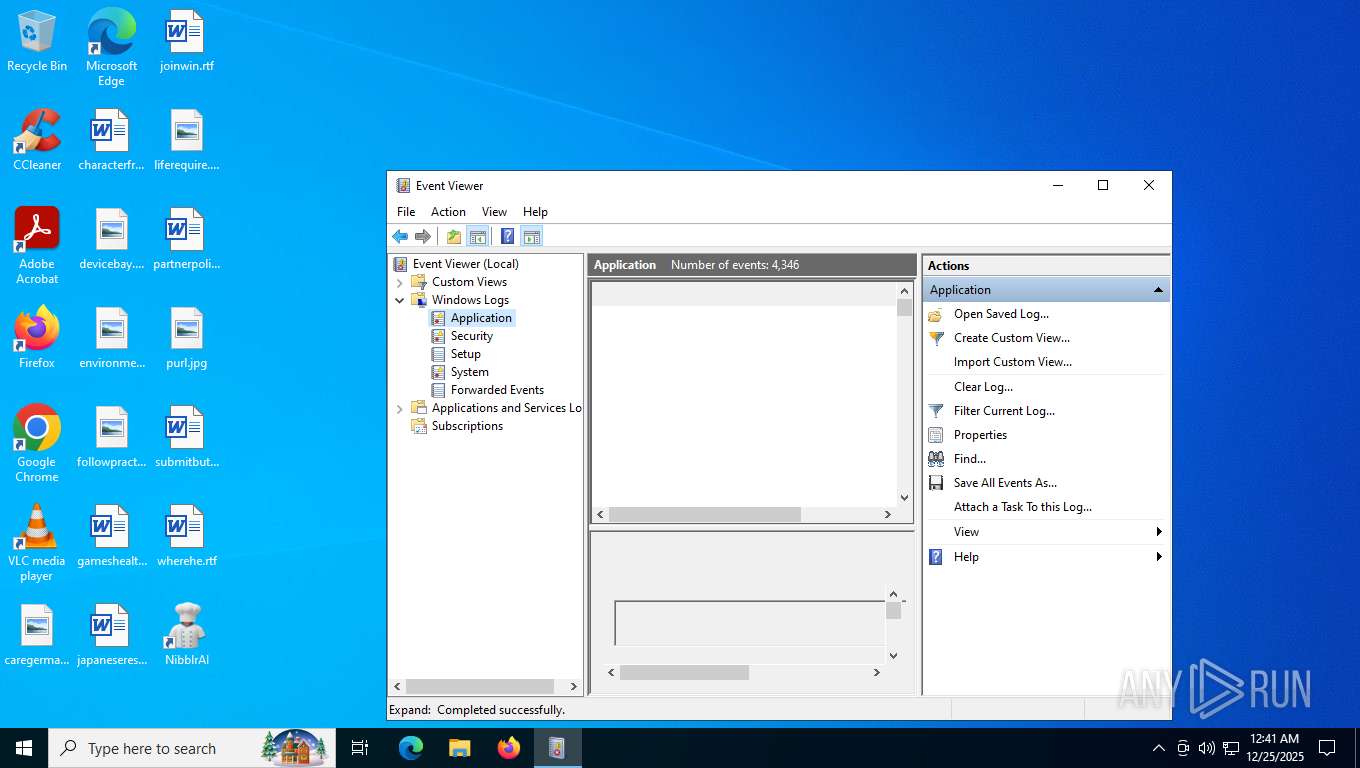
Reads Microsoft Outlook installation path
- mmc.exe (PID: 6748)
Reads Internet Explorer settings
- mmc.exe (PID: 6748)
There is functionality for taking screenshot (YARA)
- NibblrAI.exe (PID: 3568)
INFO
Checks supported languages
- identity_helper.exe (PID: 3380)
- nibblrai.exe (PID: 8688)
- nibblrai.tmp (PID: 8708)
- NibblrAI.exe (PID: 8356)
- NibblrAI.exe (PID: 3568)
- NibblrAI.exe (PID: 4632)
- NibblrAI.exe (PID: 8548)
- NibblrAI.exe (PID: 8072)
- NibblrAI.exe (PID: 7976)
- PLUGScheduler.exe (PID: 4300)
- NibblrAI.exe (PID: 8780)
- NibblrAI.exe (PID: 7740)
- NibblrAI.exe (PID: 7240)
- NibblrAI.exe (PID: 7360)
- NibblrAI.exe (PID: 7416)
- NibblrAI.exe (PID: 7384)
- TextInputHost.exe (PID: 3440)
Reads the computer name
- identity_helper.exe (PID: 3380)
- nibblrai.tmp (PID: 8708)
- NibblrAI.exe (PID: 3568)
- NibblrAI.exe (PID: 8356)
- NibblrAI.exe (PID: 4632)
- TextInputHost.exe (PID: 3440)
- NibblrAI.exe (PID: 7976)
- NibblrAI.exe (PID: 8072)
- PLUGScheduler.exe (PID: 4300)
- NibblrAI.exe (PID: 8780)
- NibblrAI.exe (PID: 7240)
- NibblrAI.exe (PID: 7384)
- NibblrAI.exe (PID: 7360)
Application launched itself
- msedge.exe (PID: 7612)
Create files in a temporary directory
- nibblrai.exe (PID: 8688)
- nibblrai.tmp (PID: 8708)
- NibblrAI.exe (PID: 8356)
- NibblrAI.exe (PID: 7976)
- mmc.exe (PID: 6748)
- NibblrAI.exe (PID: 7240)
Reads Environment values
- identity_helper.exe (PID: 3380)
- NibblrAI.exe (PID: 8356)
- NibblrAI.exe (PID: 8548)
- NibblrAI.exe (PID: 7976)
- NibblrAI.exe (PID: 7740)
- NibblrAI.exe (PID: 7240)
- NibblrAI.exe (PID: 7416)
Executable content was dropped or overwritten
- msedge.exe (PID: 7612)
Creates files or folders in the user directory
- nibblrai.tmp (PID: 8708)
- NibblrAI.exe (PID: 8356)
- NibblrAI.exe (PID: 4632)
- NibblrAI.exe (PID: 7976)
- mmc.exe (PID: 6748)
- NibblrAI.exe (PID: 7240)
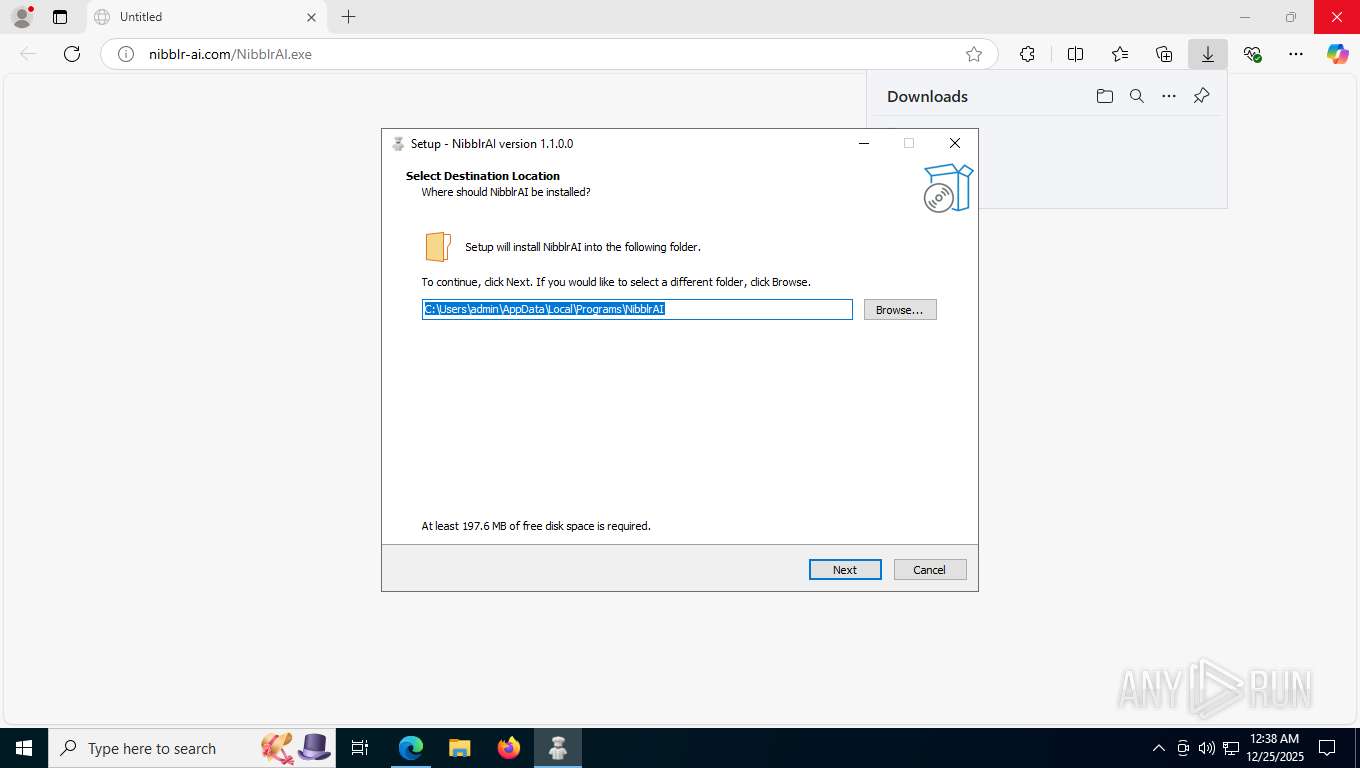
Detects InnoSetup installer (YARA)
- nibblrai.exe (PID: 8688)
- nibblrai.tmp (PID: 8708)
Compiled with Borland Delphi (YARA)
- nibblrai.exe (PID: 8688)
- nibblrai.tmp (PID: 8708)
The sample compiled with english language support
- nibblrai.tmp (PID: 8708)
Creates a software uninstall entry
- nibblrai.tmp (PID: 8708)
Reads product name
- NibblrAI.exe (PID: 8356)
- NibblrAI.exe (PID: 8548)
- NibblrAI.exe (PID: 7976)
- NibblrAI.exe (PID: 7740)
- NibblrAI.exe (PID: 7240)
- NibblrAI.exe (PID: 7416)
Reads the machine GUID from the registry
- NibblrAI.exe (PID: 8356)
- NibblrAI.exe (PID: 7976)
- NibblrAI.exe (PID: 7240)
Checks proxy server information
- NibblrAI.exe (PID: 8356)
- NibblrAI.exe (PID: 7976)
- slui.exe (PID: 2740)
- mmc.exe (PID: 6748)
- NibblrAI.exe (PID: 7240)
Process checks computer location settings
- NibblrAI.exe (PID: 8548)
- NibblrAI.exe (PID: 8356)
- NibblrAI.exe (PID: 7740)
- NibblrAI.exe (PID: 7976)
- NibblrAI.exe (PID: 7240)
- NibblrAI.exe (PID: 7416)
Node.js compiler has been detected
- NibblrAI.exe (PID: 8356)
- NibblrAI.exe (PID: 3568)
- NibblrAI.exe (PID: 4632)
- NibblrAI.exe (PID: 8548)
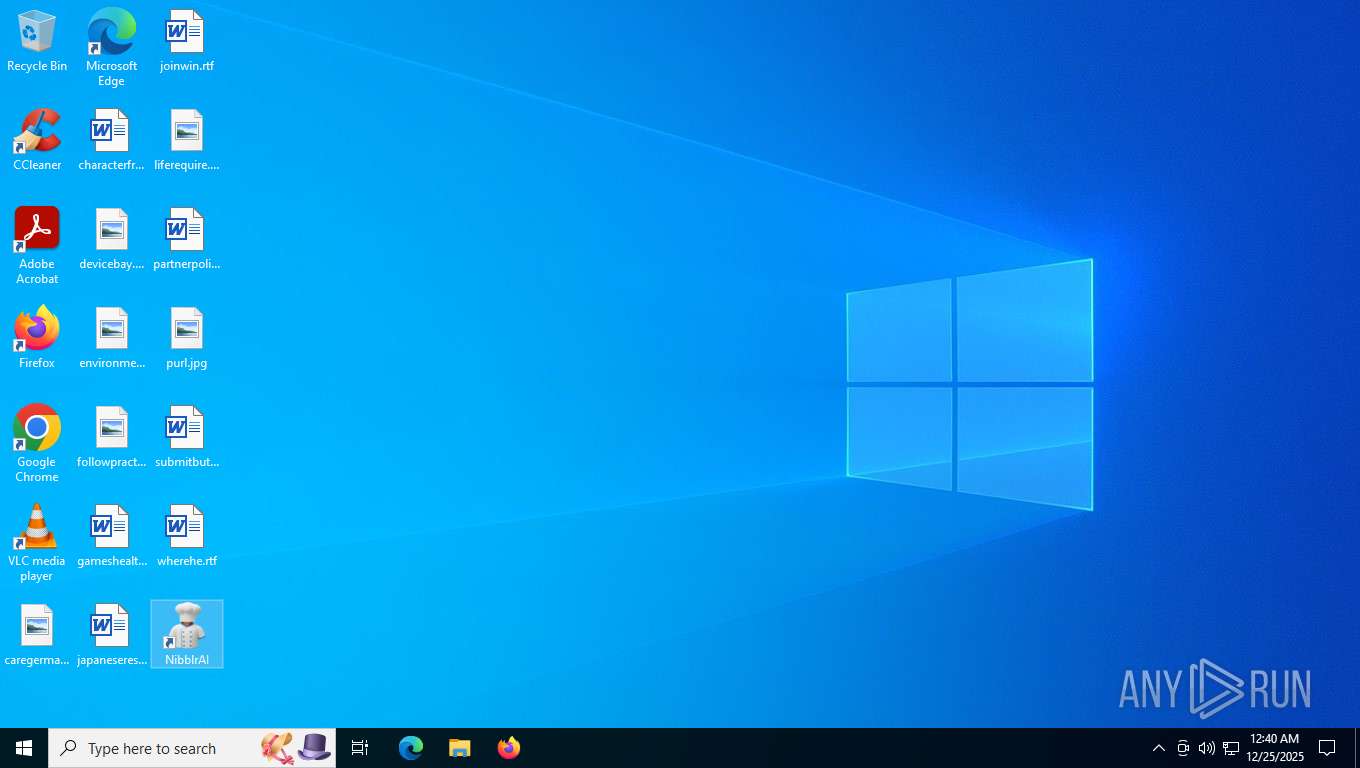
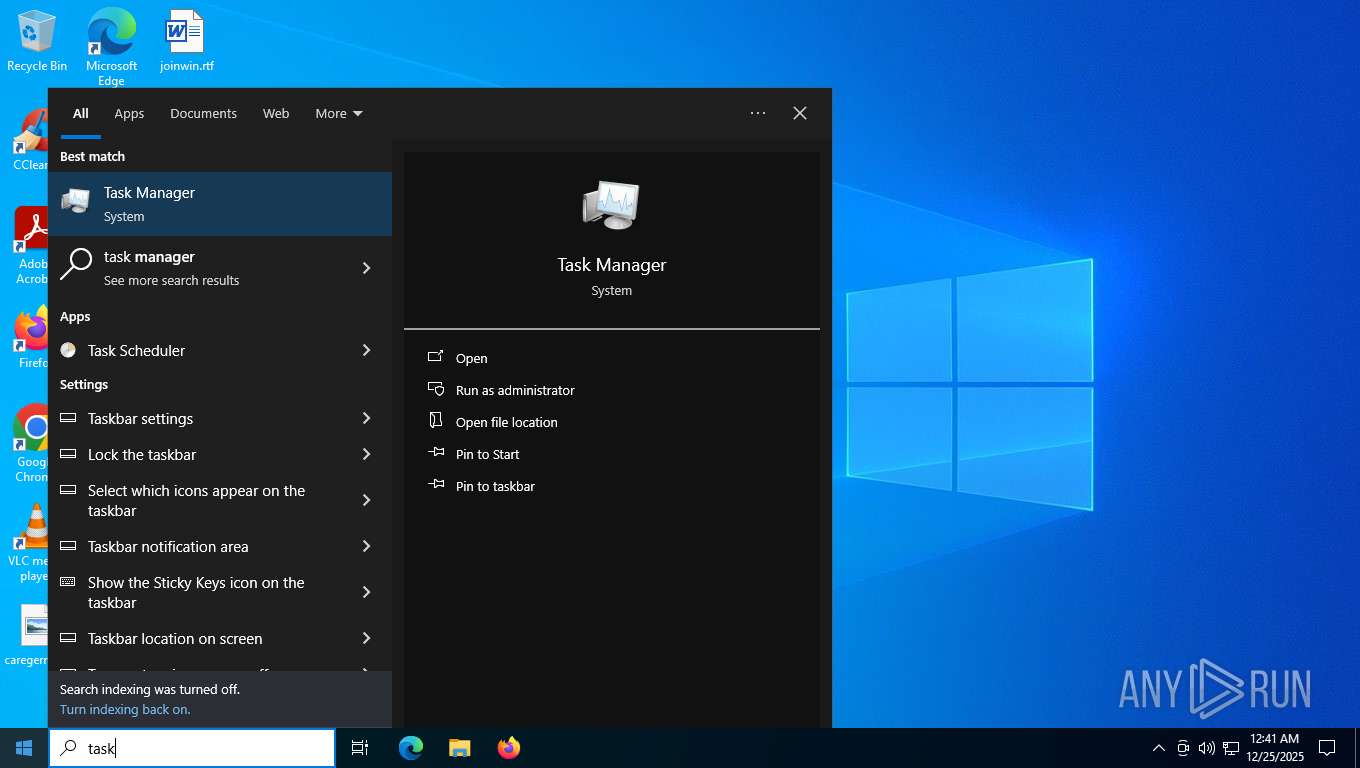
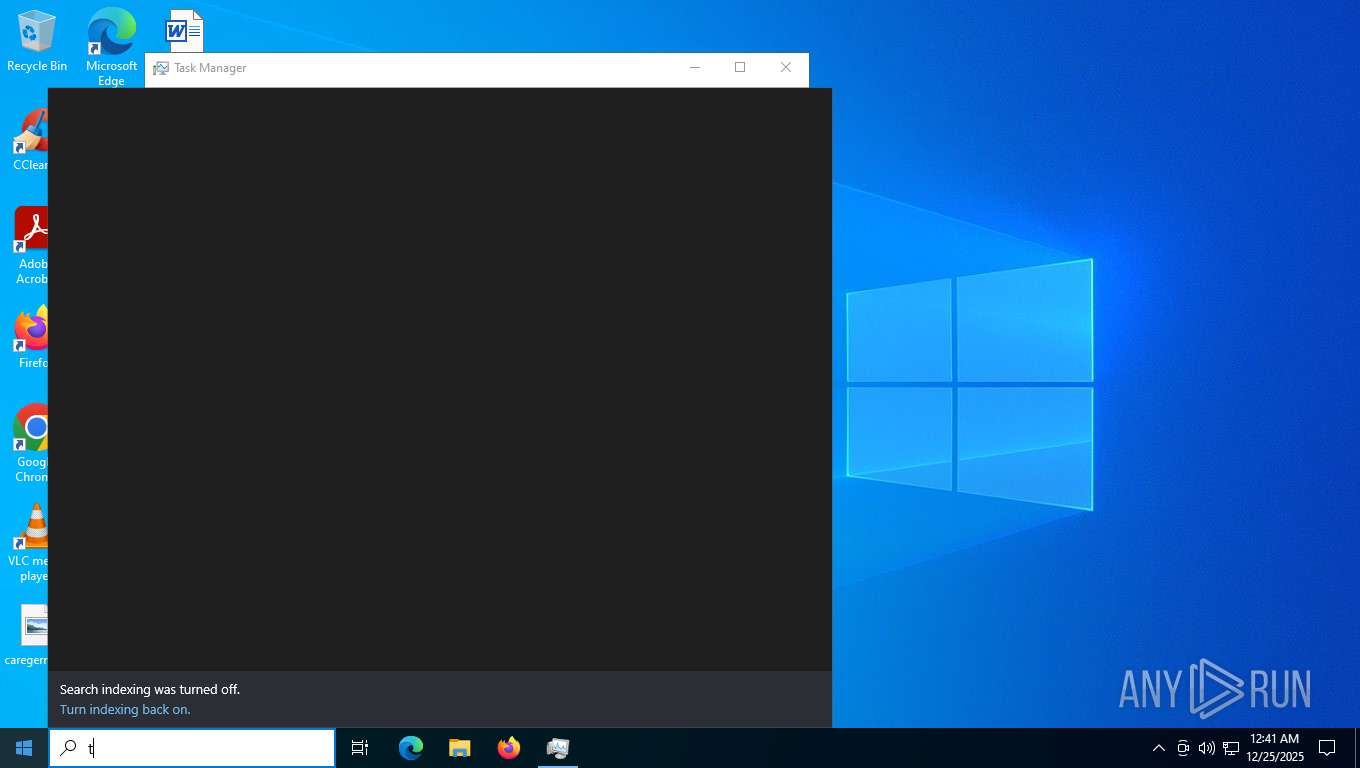
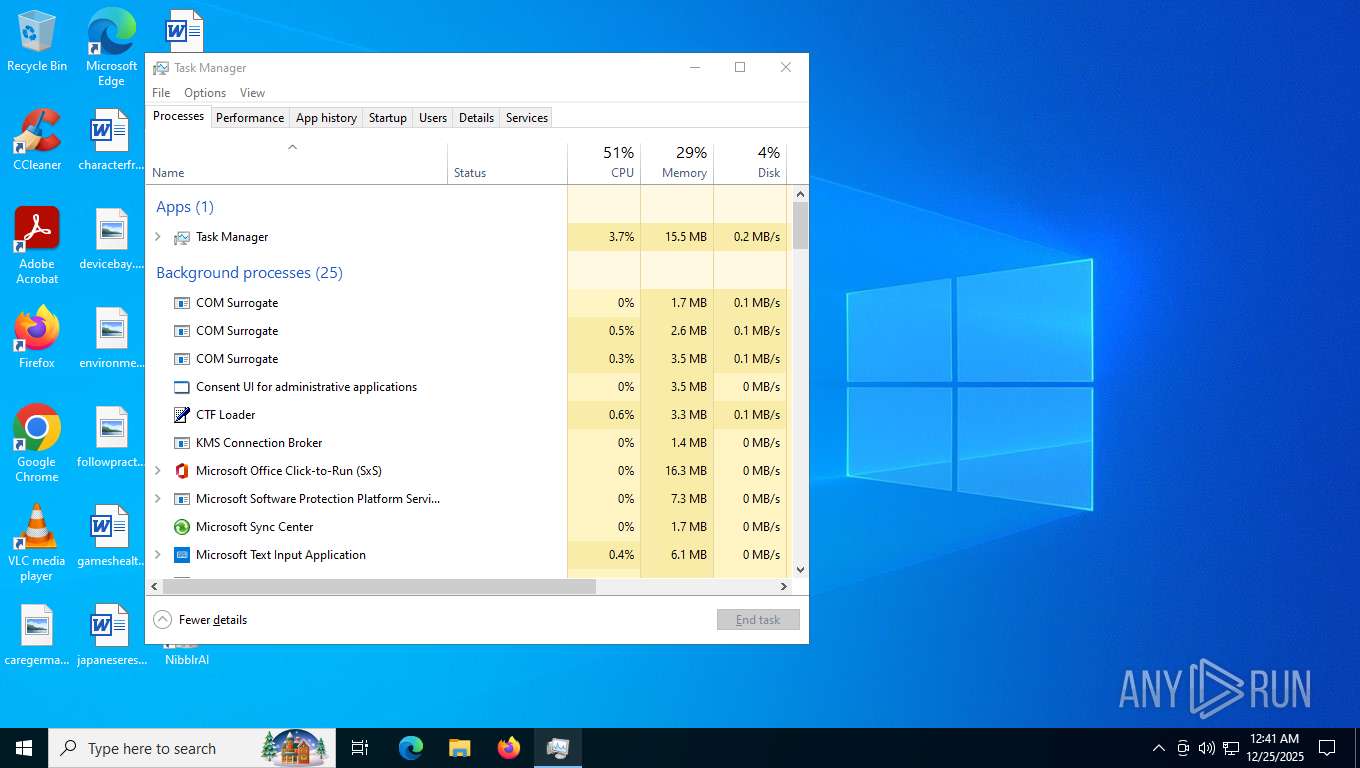
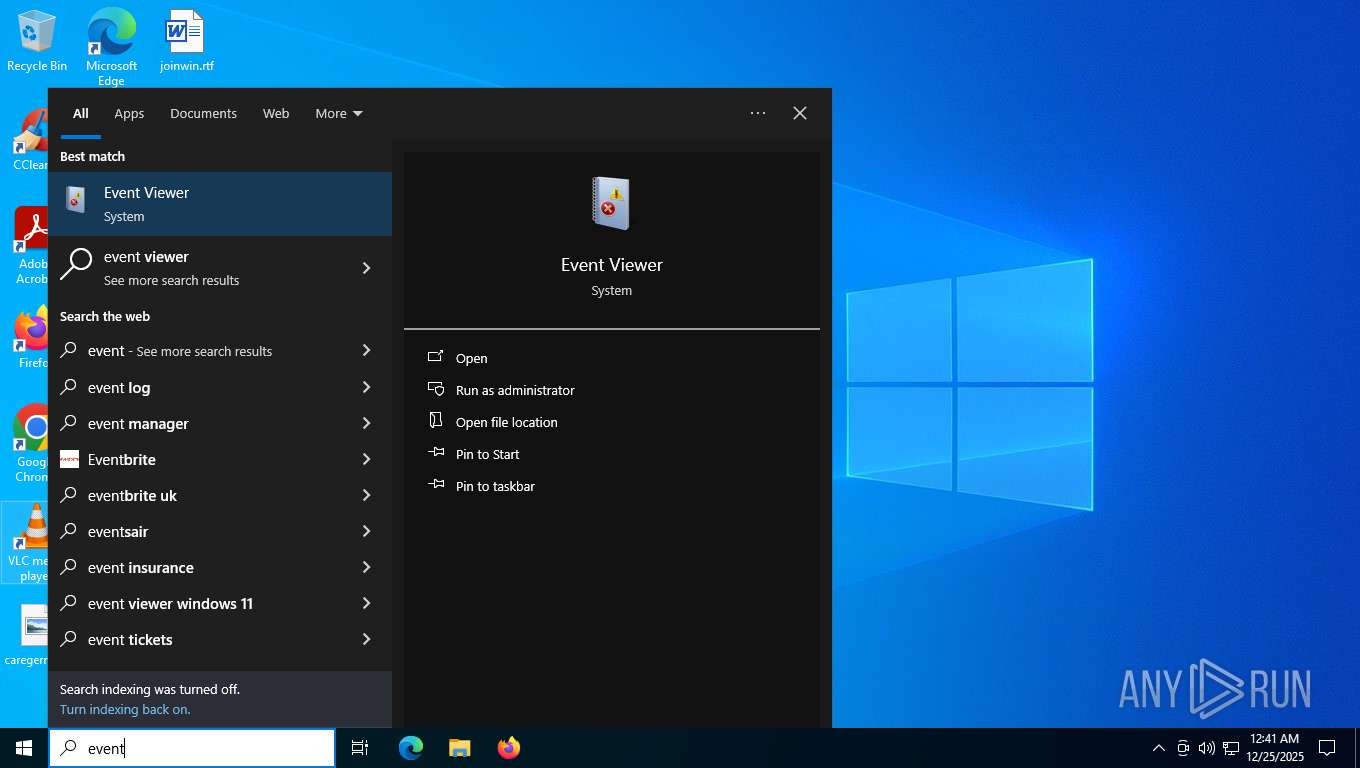
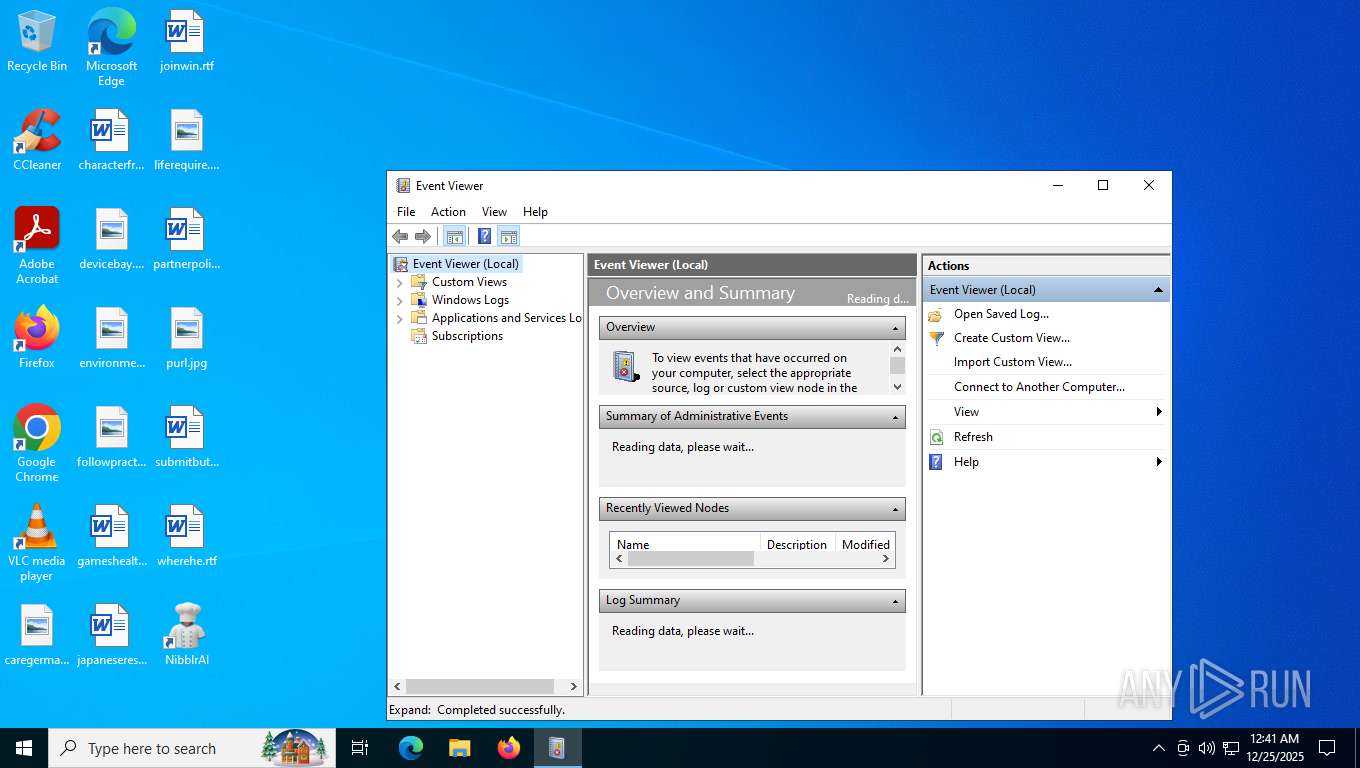
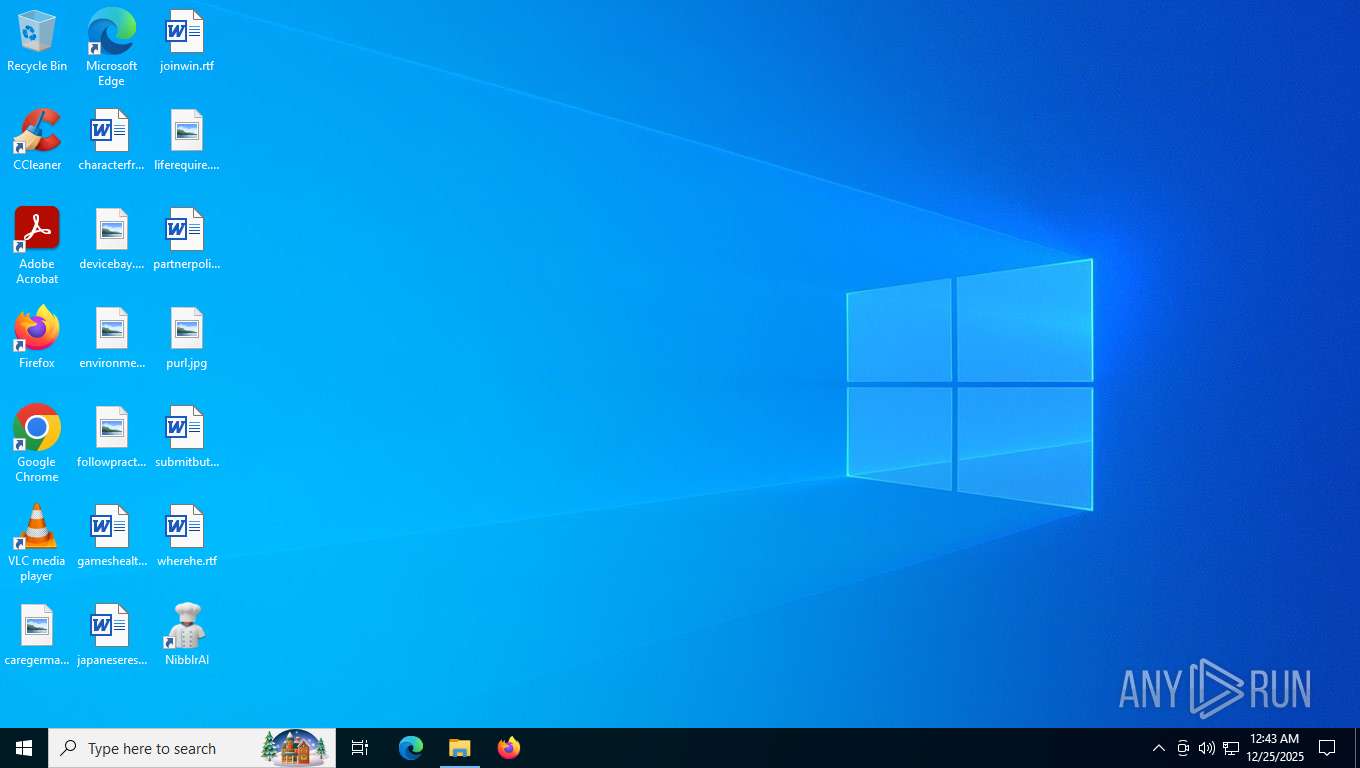
Manual execution by a user
- NibblrAI.exe (PID: 7976)
- Taskmgr.exe (PID: 6976)
- Taskmgr.exe (PID: 6888)
- mmc.exe (PID: 6748)
- NibblrAI.exe (PID: 7240)
- mmc.exe (PID: 6560)
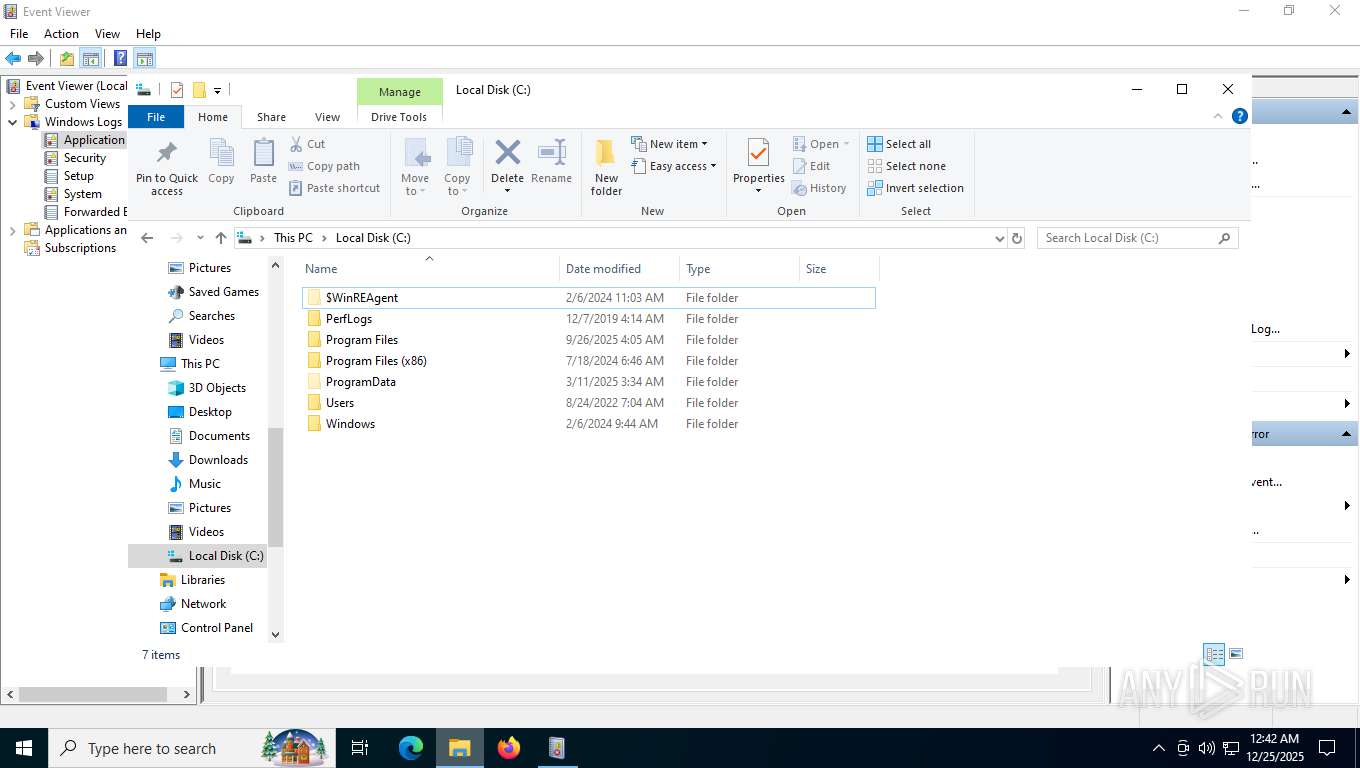
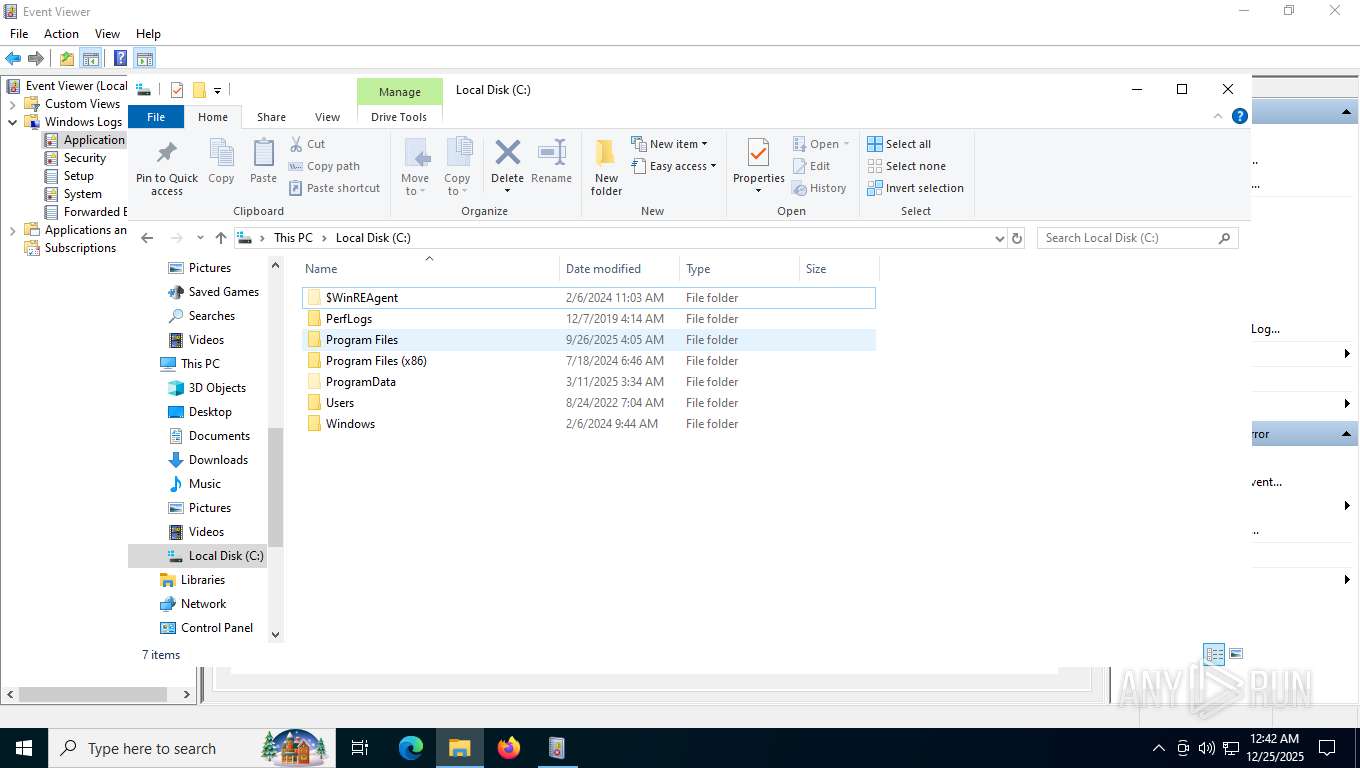
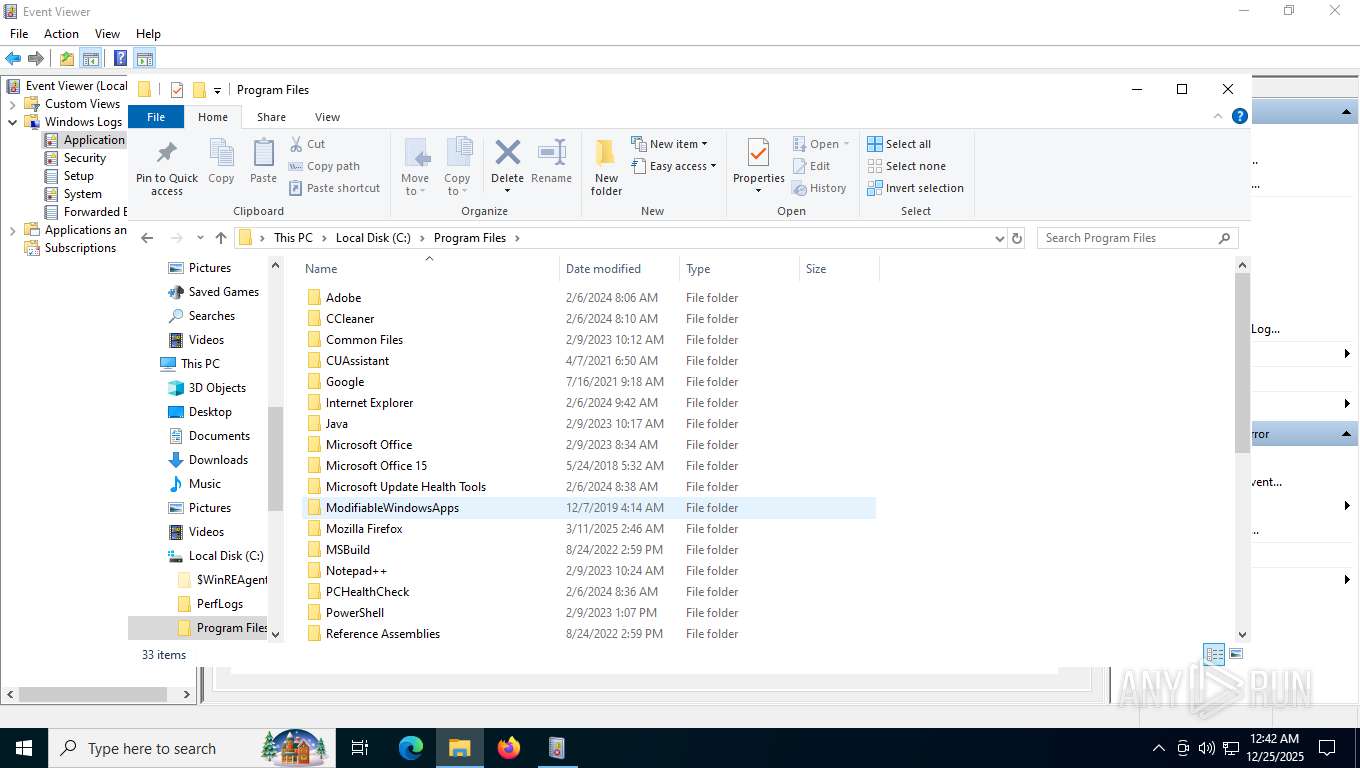
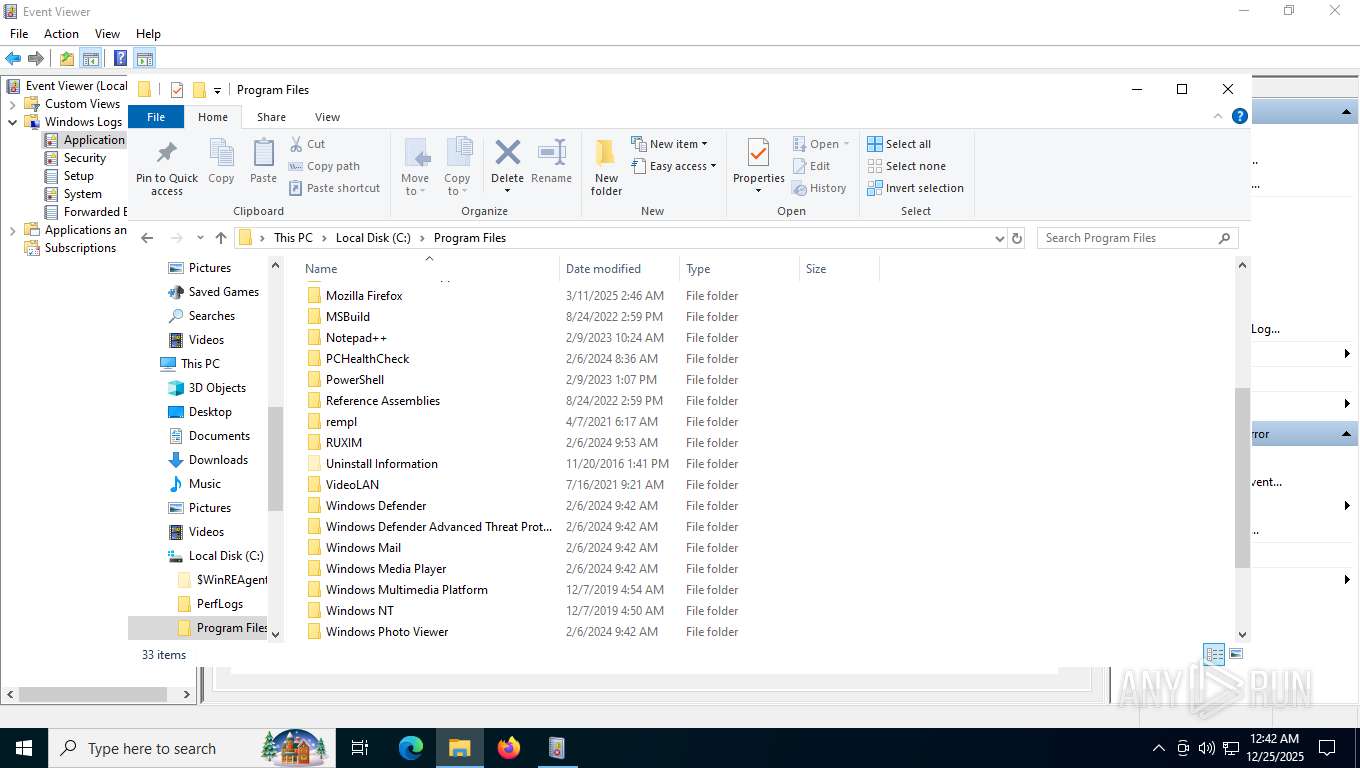
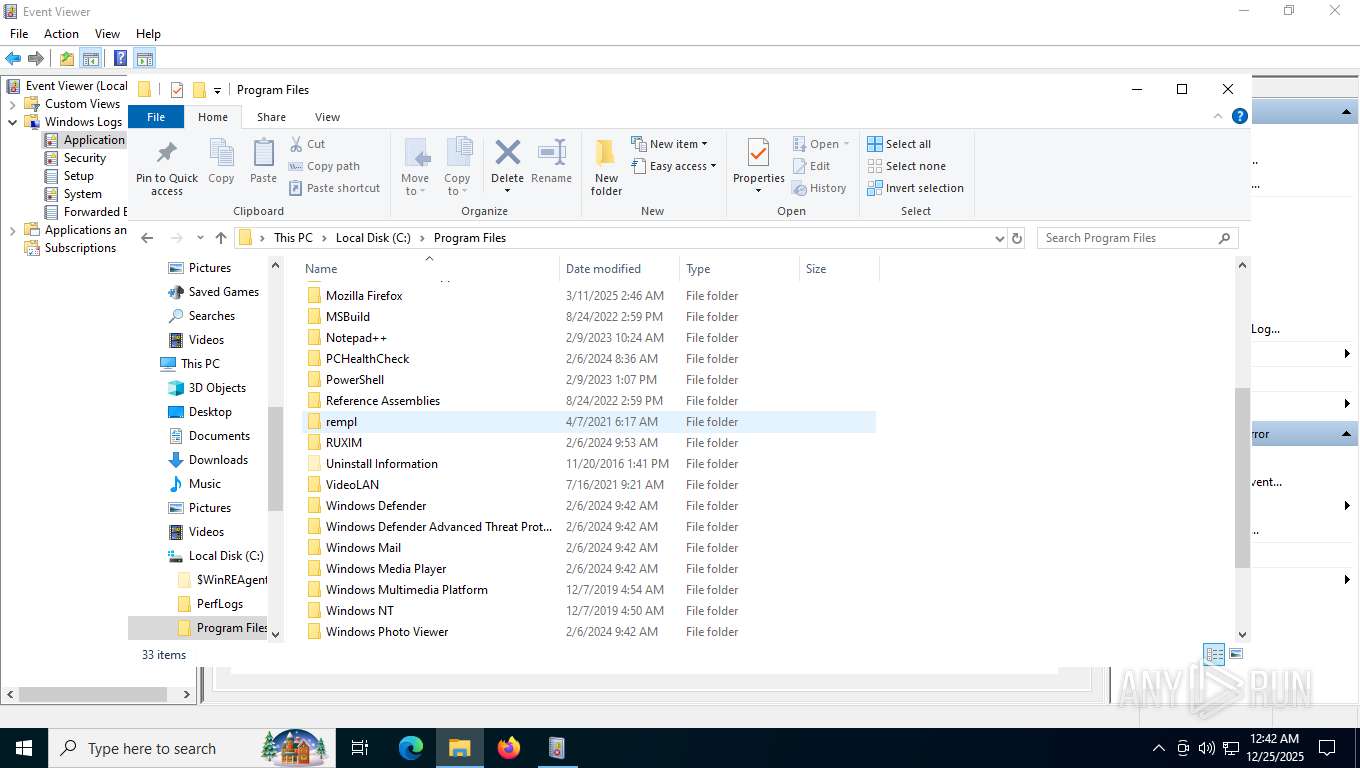
Creates files in the program directory
- PLUGScheduler.exe (PID: 4300)
- mmc.exe (PID: 6748)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 6976)
- mmc.exe (PID: 1380)
- mmc.exe (PID: 6748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
351
Monitored processes
44
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 792 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4256,i,15796020473969477308,4629657970465737210,262144 --variations-seed-version --mojo-platform-channel-handle=4300 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1380 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2368 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=12 --always-read-main-dll --field-trial-handle=5952,i,15796020473969477308,4629657970465737210,262144 --variations-seed-version --mojo-platform-channel-handle=6032 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2740 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3380 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5876,i,15796020473969477308,4629657970465737210,262144 --variations-seed-version --mojo-platform-channel-handle=5916 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3440 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 123.26505.0.0 Modules
| |||||||||||||||
| 3568 | "C:\Users\admin\AppData\Local\Programs\NibblrAI\NibblrAI.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\nibblrai-nativefier-69250a" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1604 --field-trial-handle=1704,i,17834946787406564181,11162276584118226432,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Local\Programs\NibblrAI\NibblrAI.exe | — | NibblrAI.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: LOW Description: NibblrAI Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 4136 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4300 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4308 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
Total events
21 212
Read events
21 108
Write events
47
Delete events
57
Modification events
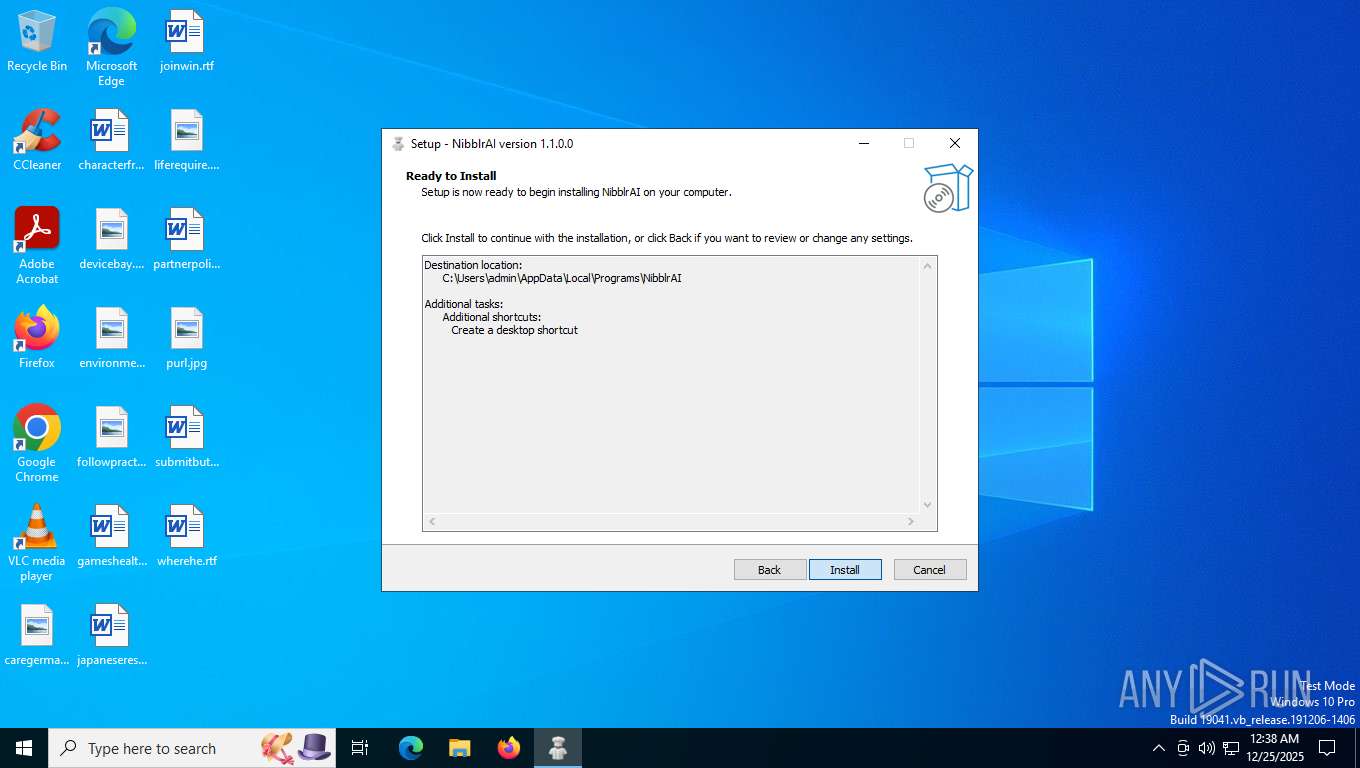
| (PID) Process: | (8708) nibblrai.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NibblrAI_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.4.3 | |||
| (PID) Process: | (8708) nibblrai.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NibblrAI_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Users\admin\AppData\Local\Programs\NibblrAI | |||
| (PID) Process: | (8708) nibblrai.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NibblrAI_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Programs\NibblrAI\ | |||
| (PID) Process: | (8708) nibblrai.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NibblrAI_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (8708) nibblrai.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NibblrAI_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (8708) nibblrai.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NibblrAI_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: desktopicon | |||
| (PID) Process: | (8708) nibblrai.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NibblrAI_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: | |||
| (PID) Process: | (8708) nibblrai.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NibblrAI_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: english | |||
| (PID) Process: | (8708) nibblrai.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NibblrAI_is1 |
| Operation: | write | Name: | DisplayName |
Value: NibblrAI version 1.1.0.0 | |||
| (PID) Process: | (8708) nibblrai.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NibblrAI_is1 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\Programs\NibblrAI\icon.ico | |||
Executable files
18
Suspicious files
249
Text files
311
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfe0e1.TMP | — | |
MD5:— | SHA256:— | |||
| 7612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfe0f1.TMP | — | |
MD5:— | SHA256:— | |||
| 7612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfe0f1.TMP | — | |
MD5:— | SHA256:— | |||
| 7612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfe0f1.TMP | — | |
MD5:— | SHA256:— | |||
| 7612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfe100.TMP | — | |
MD5:— | SHA256:— | |||
| 7612 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
219
TCP/UDP connections
102
DNS requests
72
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7932 | msedge.exe | GET | 200 | 3.171.214.111:443 | https://nibblr-ai.com/NibblrAI.exe | US | — | — | unknown |
7932 | msedge.exe | GET | 304 | 150.171.28.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
7932 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | US | text | 768 b | whitelisted |
7932 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | — | 25 b | whitelisted |
7932 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 311 b | whitelisted |
7932 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:dx08ys1NsdTskFZFqfbf-fctc0jlxZJyffqpaRcYqSw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
7932 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/extensionwebstorebase/v1/crx?os=win&arch=x64&os_arch=x86_64&nacl_arch=x86-64&prod=edgecrx&prodchannel=&prodversion=133.0.3065.92&lang=en-US&acceptformat=crx3,puff&x=id%3Djmjflgjpcpepeafmmgdpfkogkghcpiha%26v%3D1.2.1%26installedby%3Dother%26uc%26ping%3Dr%253D525%2526e%253D1 | US | xml | 413 b | whitelisted |
7932 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/entityextractiontemplates/api/v1/assets/find-assets?name=arbitration_priority_list&version=24.*.*&channel=stable&key=d414dd4f9db345fa8003e32adc81b362 | US | — | 271 b | whitelisted |
7932 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/entityextractiontemplates/api/v1/assets/find-assets?name=edge_hub_apps_manifest_gz&version=4.11.*&channel=stable&key=d414dd4f9db345fa8003e32adc81b362 | US | — | 266 b | whitelisted |
7932 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/entityextractiontemplates/api/v1/assets/find-assets?name=domains_config_gz&version=3.*.*&channel=stable&key=d414dd4f9db345fa8003e32adc81b362 | US | — | 267 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
1784 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1600 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7932 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7932 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7932 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7932 | msedge.exe | 3.171.214.111:80 | nibblr-ai.com | AMAZON-02 | US | whitelisted |
7932 | msedge.exe | 104.18.22.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
nibblr-ai.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |