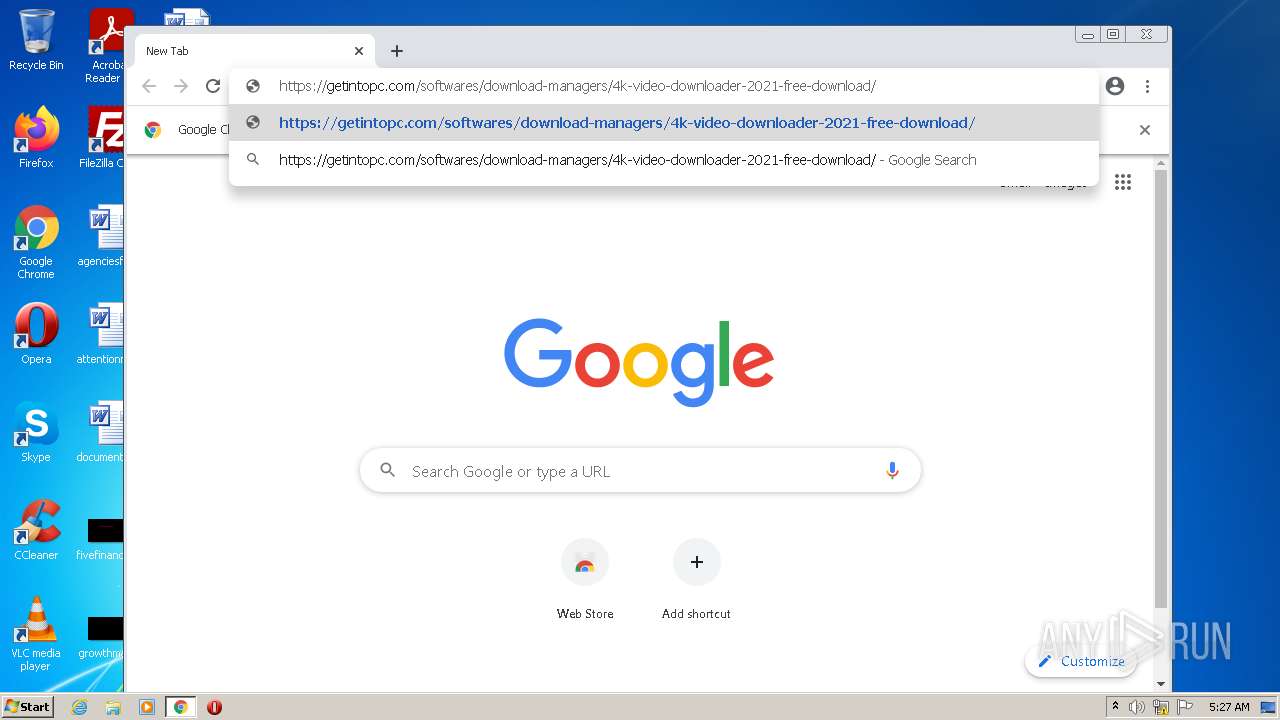
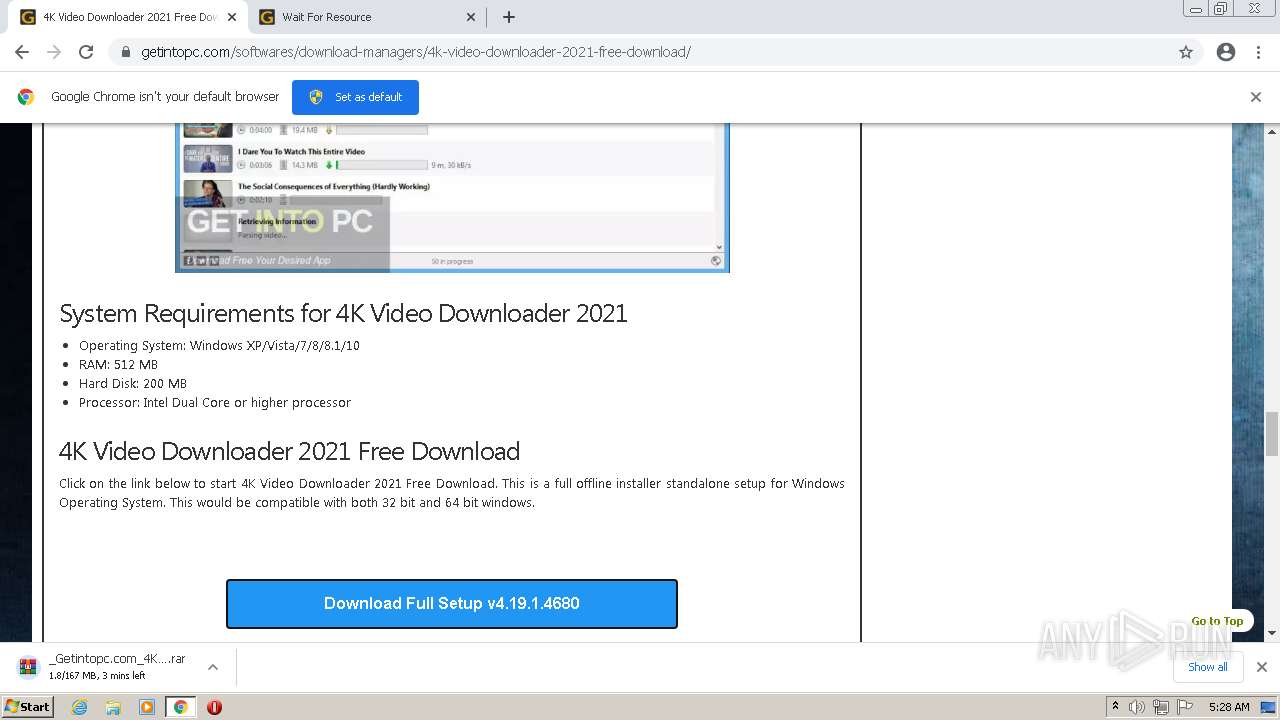
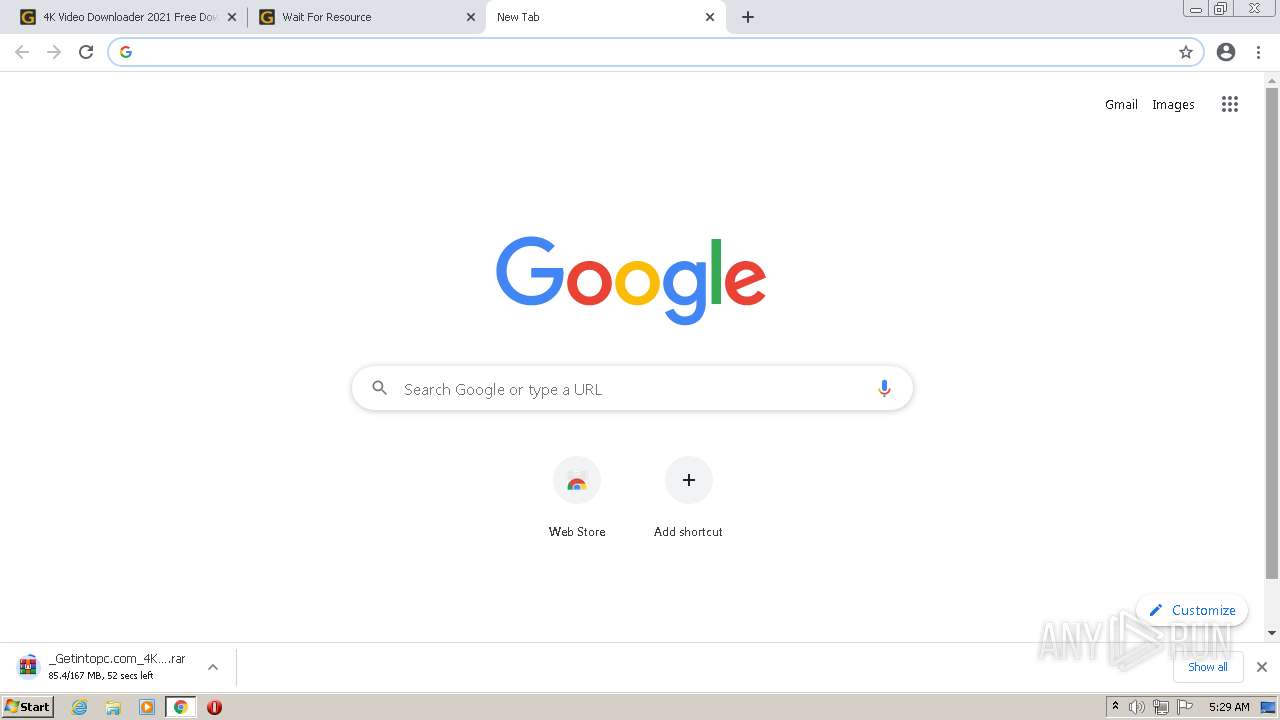
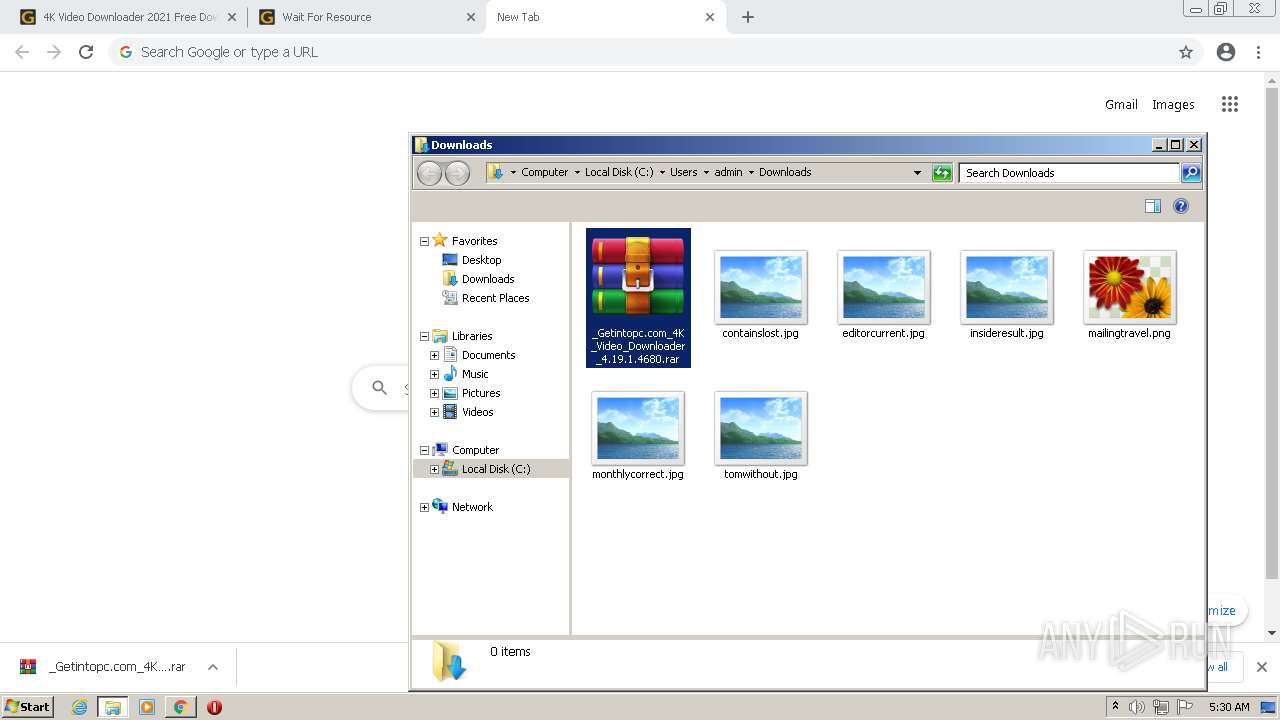
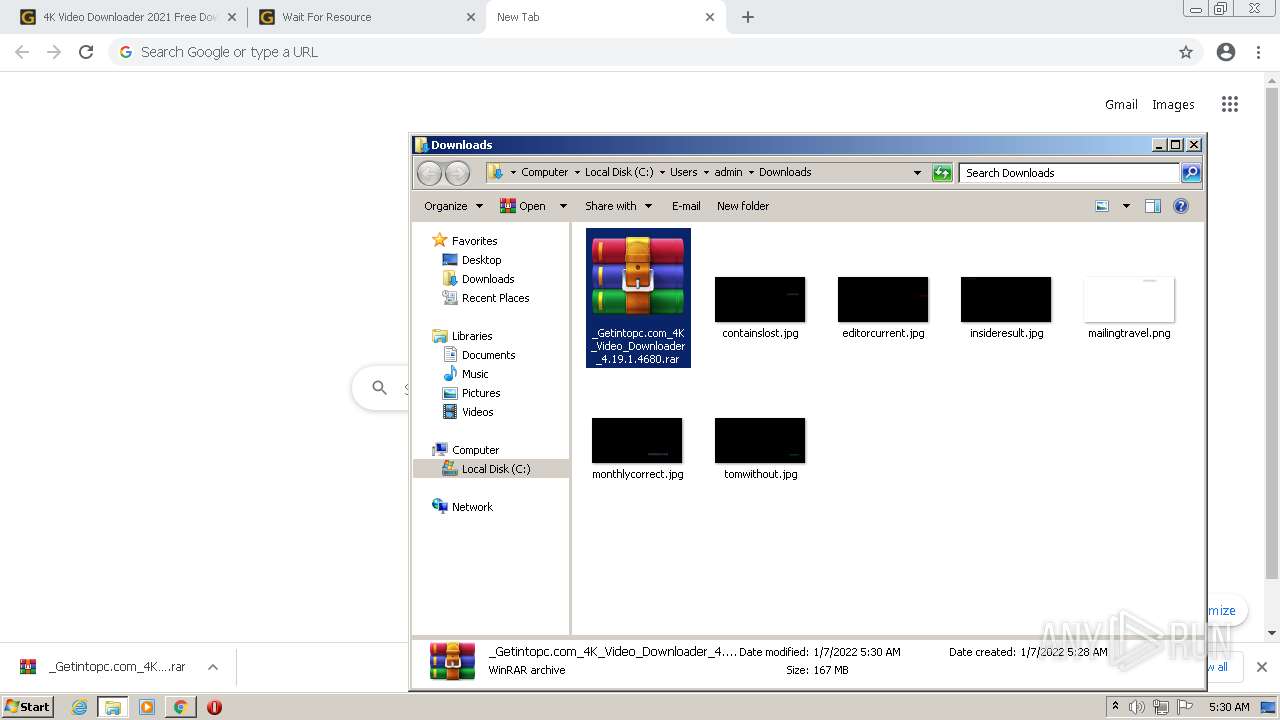
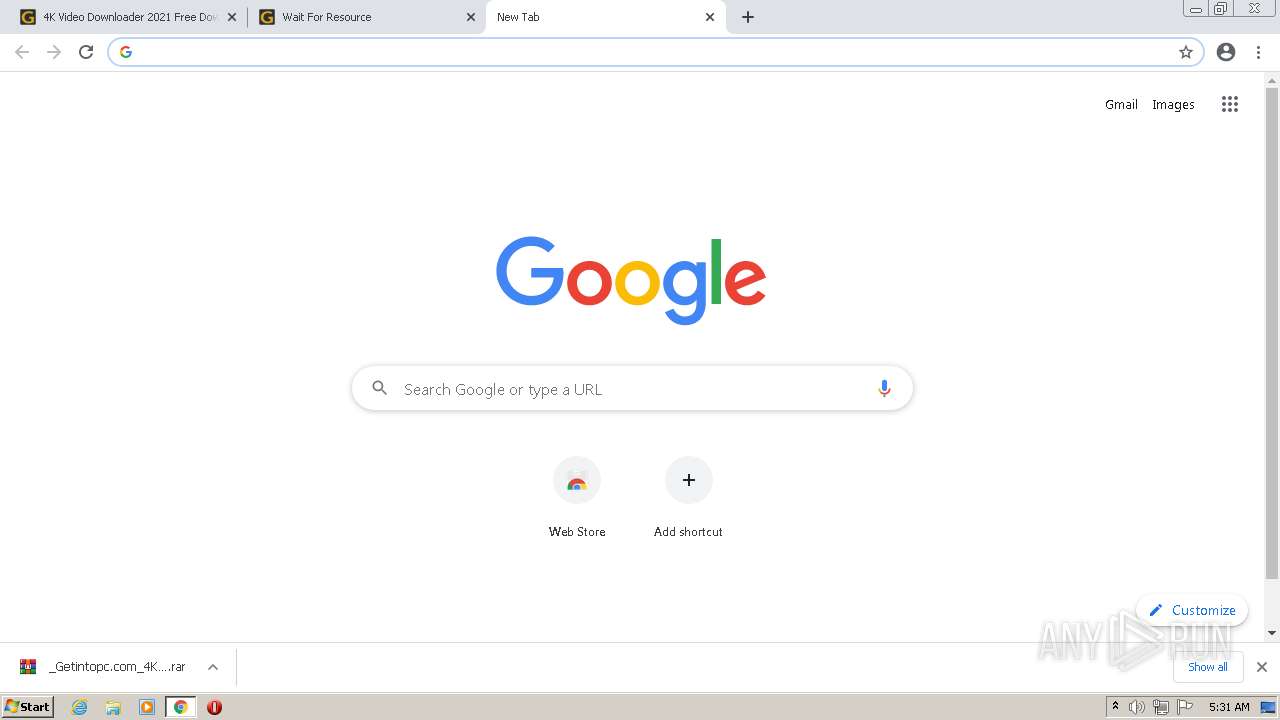
| URL: | https://getintopc.com/softwares/download-managers/4k-video-downloader-2021-free-download/ |
| Full analysis: | https://app.any.run/tasks/5415a765-cdd3-4e62-9e91-11c2e722ca82 |
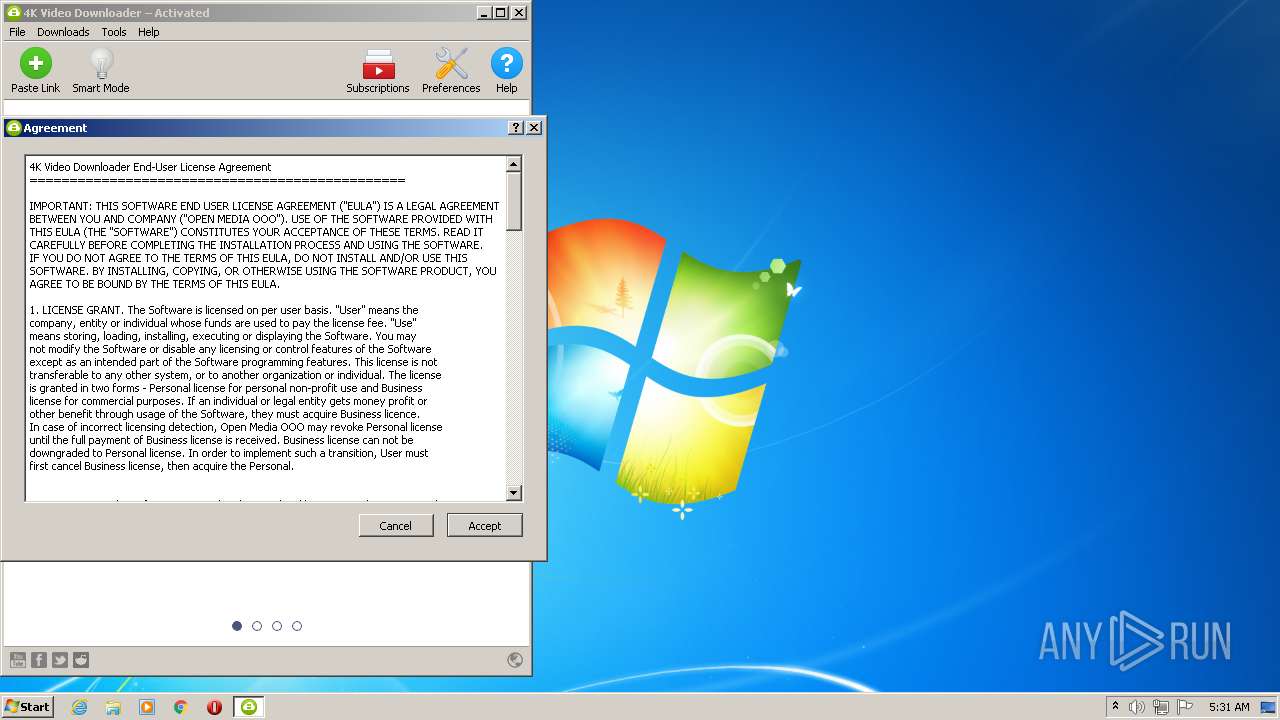
| Verdict: | Malicious activity |
| Analysis date: | January 07, 2022, 05:27:21 |
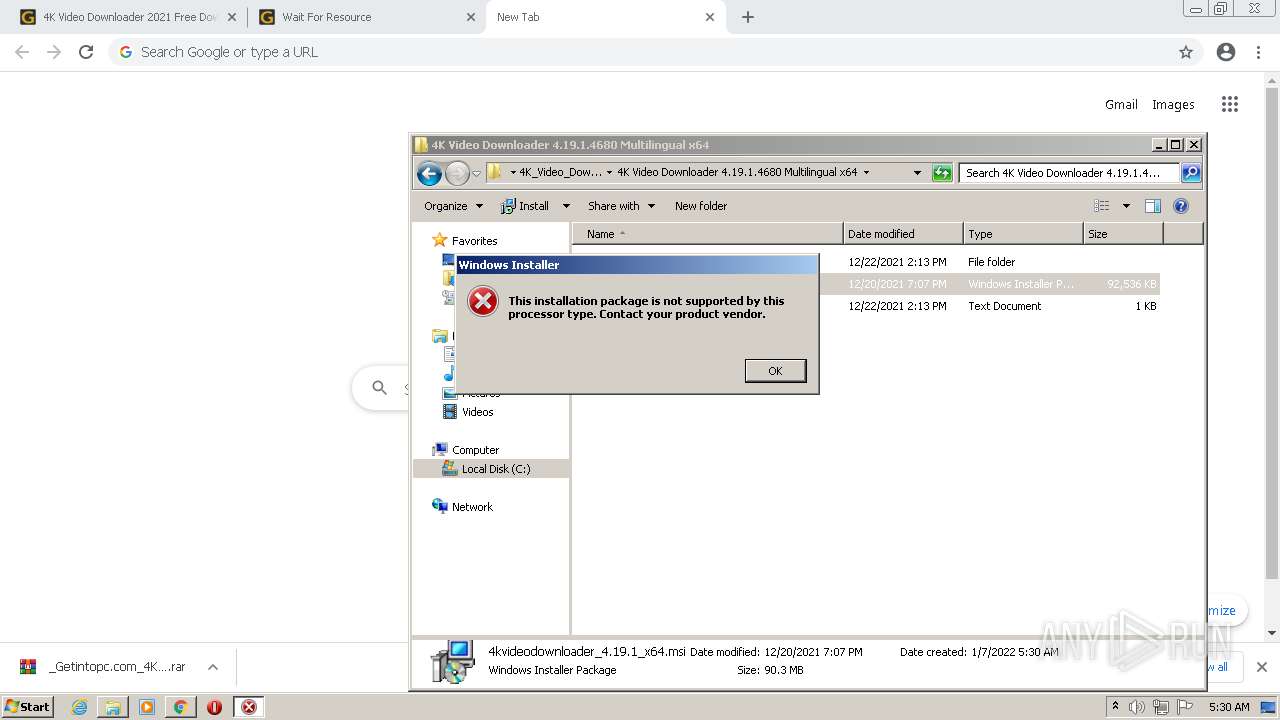
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7C3E32600B7E03B90ACDE3F856A39D3C |
| SHA1: | 17435DE362170843169B8F779B81FB717CDB7333 |
| SHA256: | B2F708CDF4EB5F9F2A970C60E209618237605B2E7831628F386C3579E11D66AD |
| SSDEEP: | 3:N8hILdIYM0IDXWiAqzuX1BFmn:2zxDX7Aq42 |
MALICIOUS
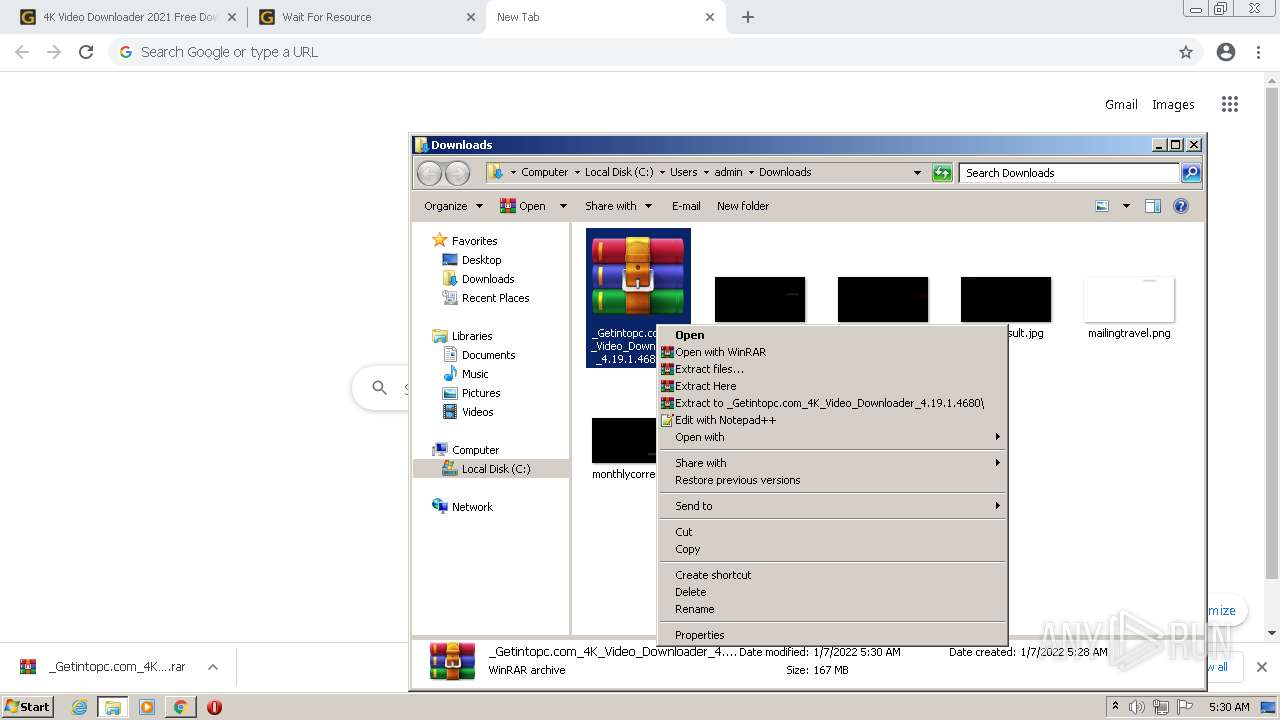
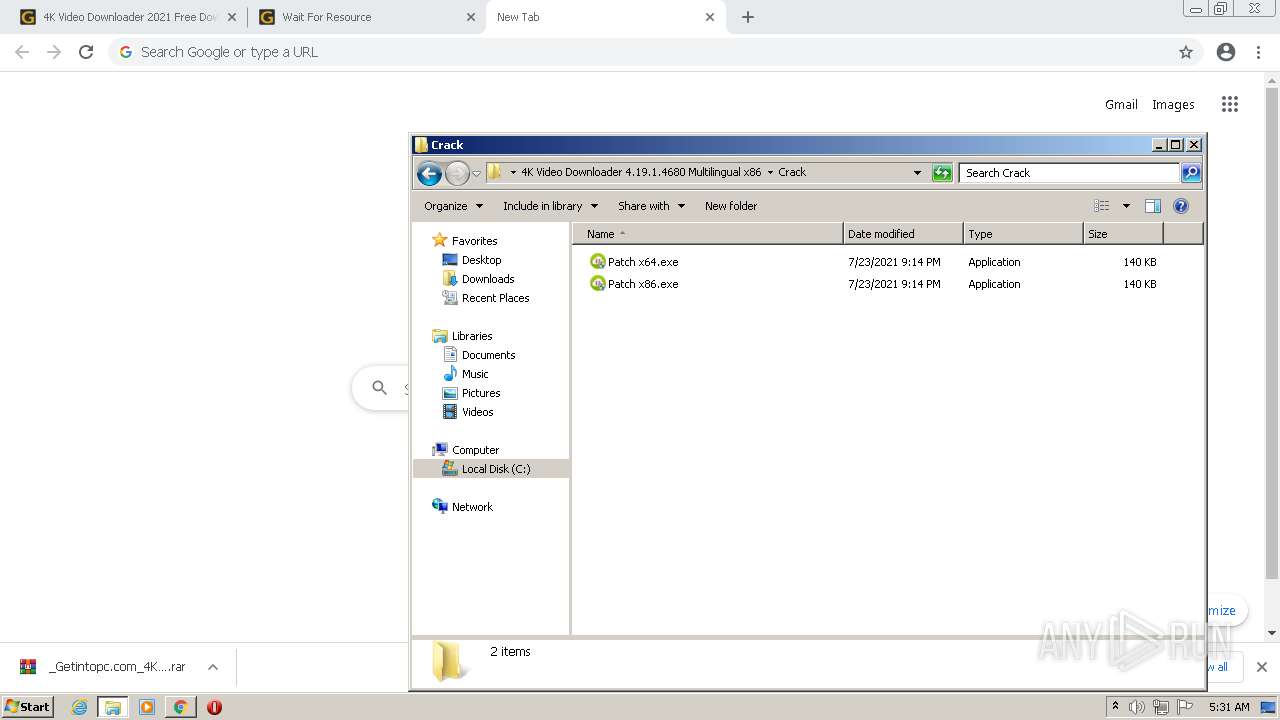
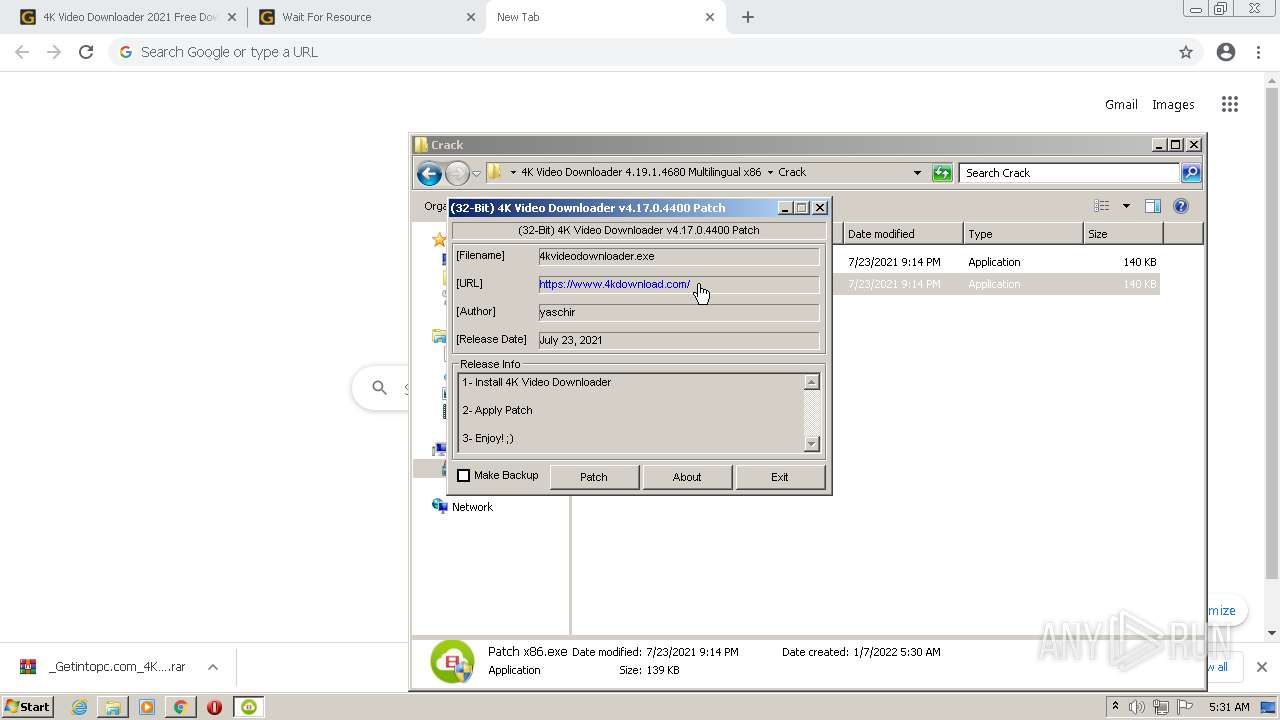
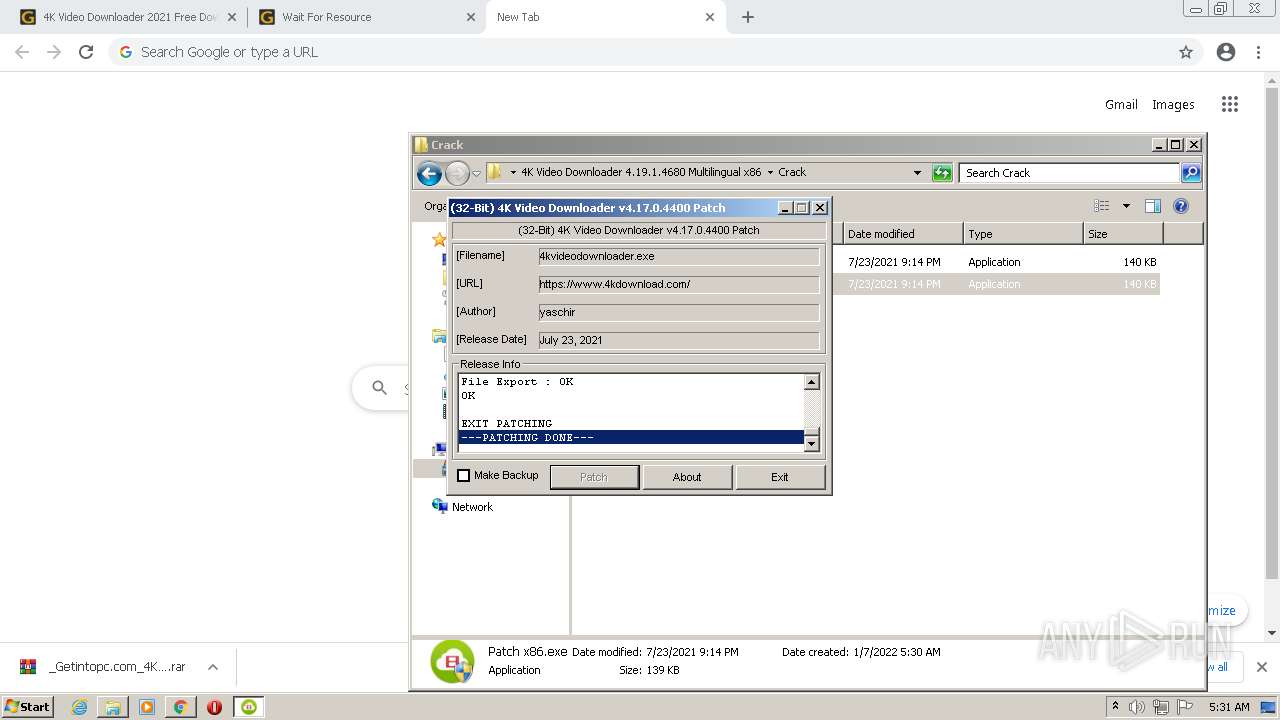
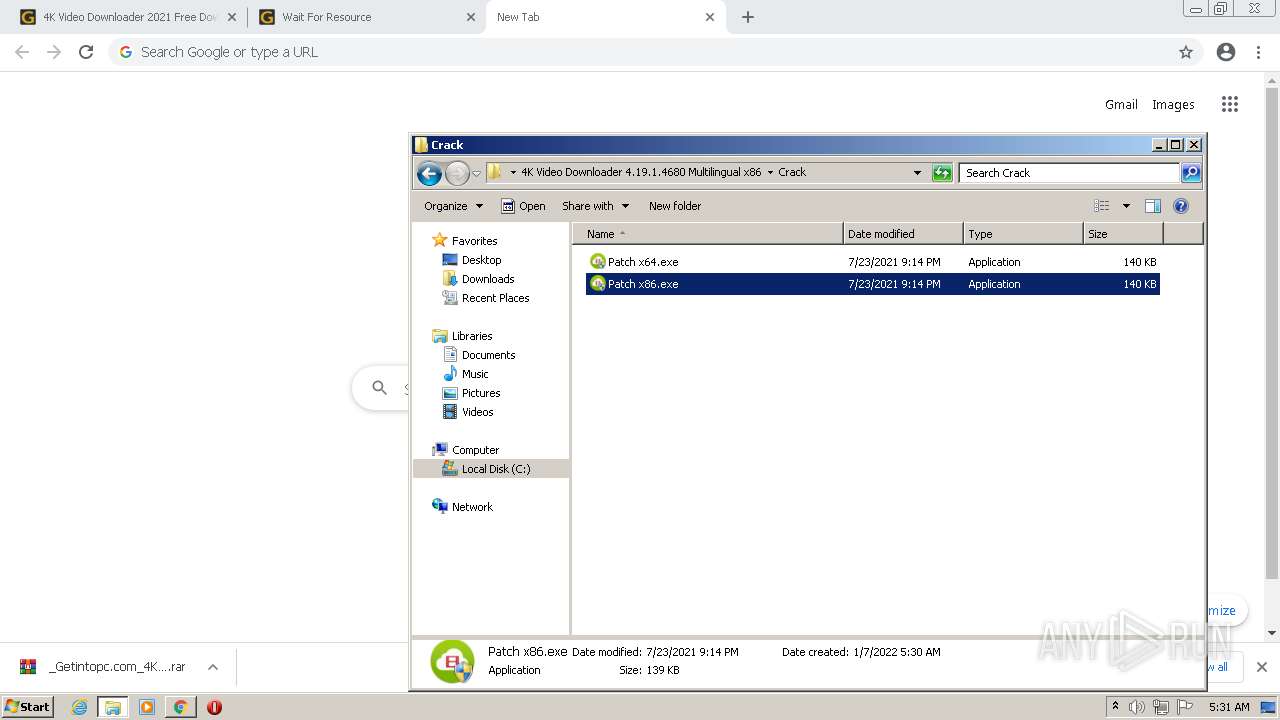
Drops executable file immediately after starts
- chrome.exe (PID: 3032)
- Patch x86.exe (PID: 628)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2176)
- MsiExec.exe (PID: 828)
- Patch x86.exe (PID: 628)
- 4kvideodownloader.exe (PID: 4076)
Application was dropped or rewritten from another process
- Patch x86.exe (PID: 628)
- Patch x86.exe (PID: 2968)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2584)
- iexplore.exe (PID: 1160)
Modifies files in Chrome extension folder
- chrome.exe (PID: 676)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 3032)
- msiexec.exe (PID: 2480)
- msiexec.exe (PID: 2564)
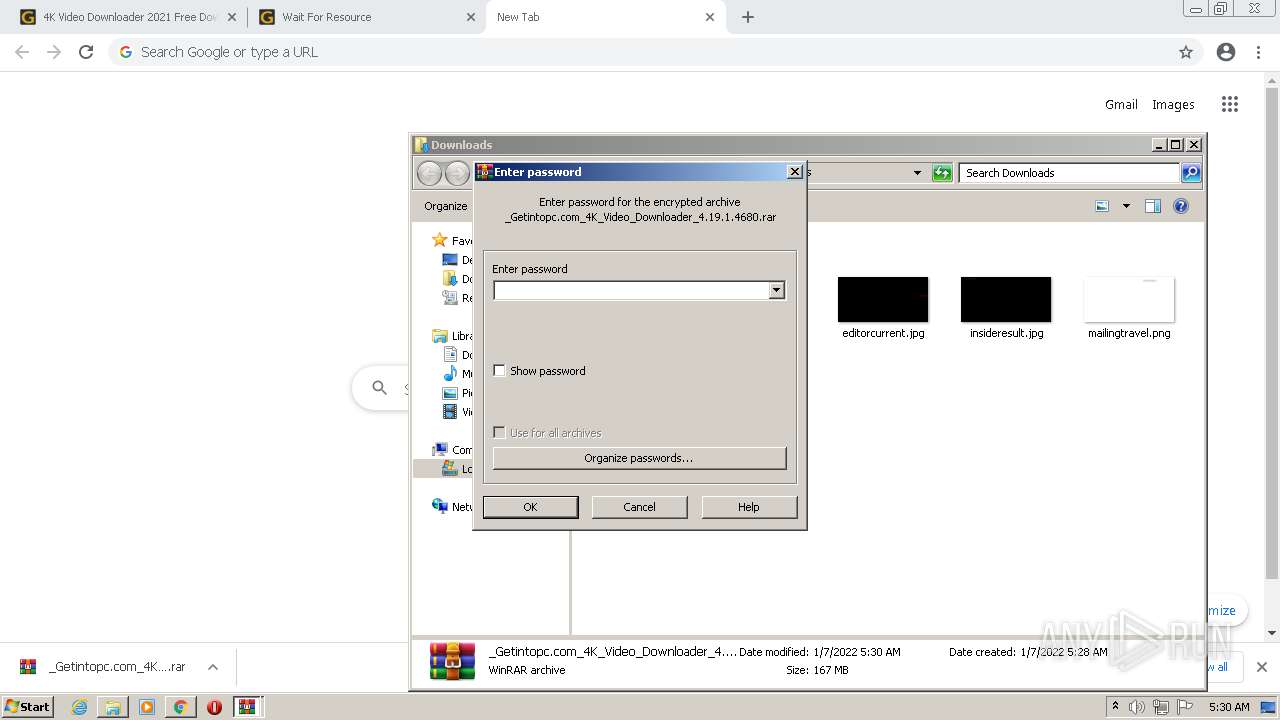
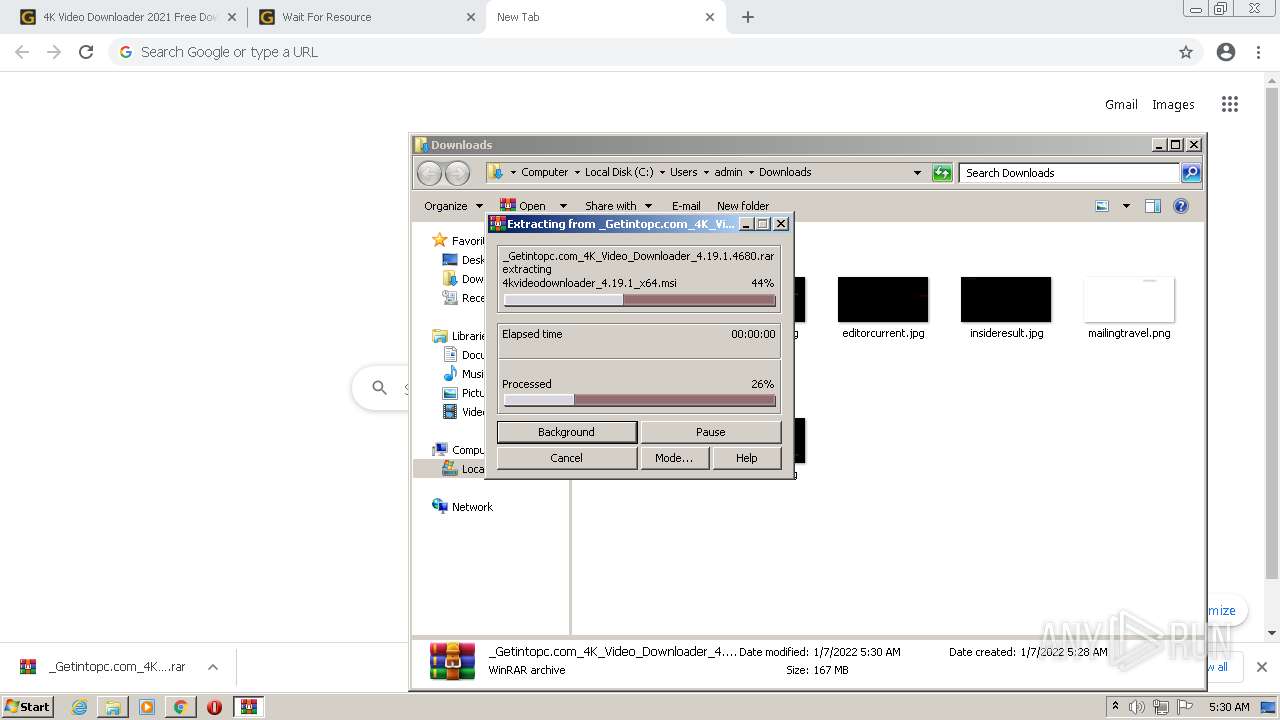
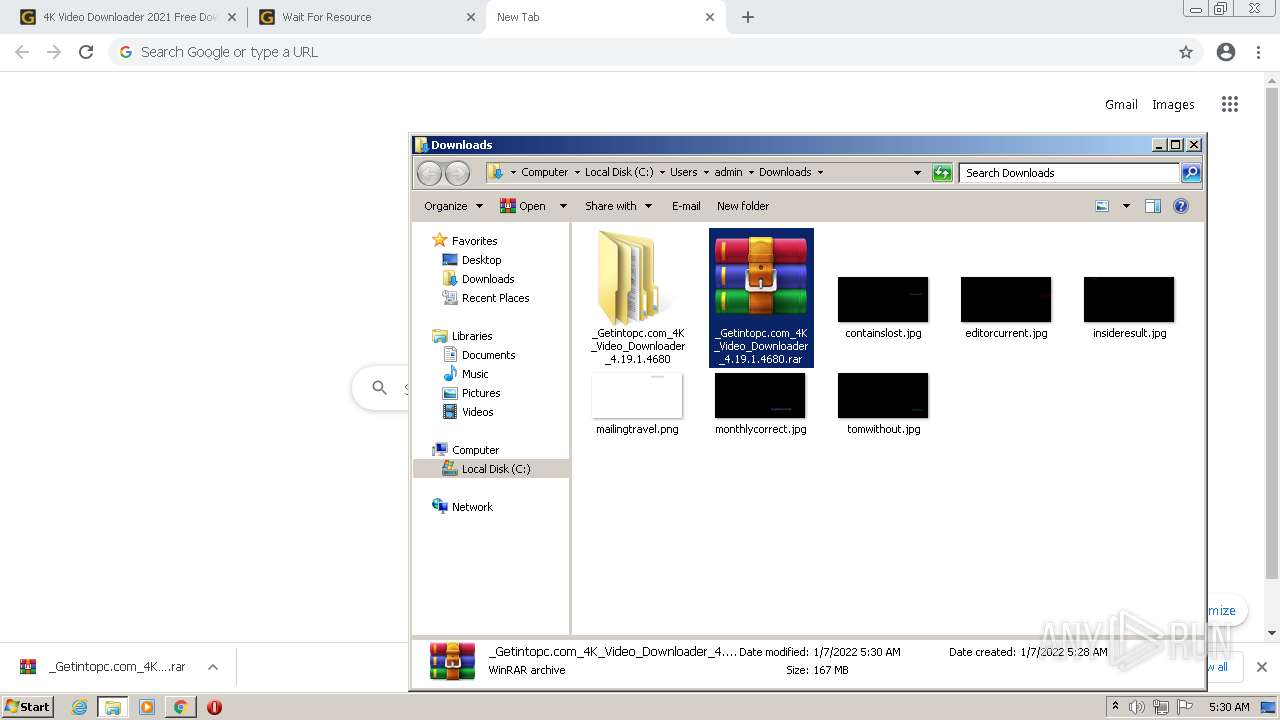
Executable content was dropped or overwritten
- chrome.exe (PID: 3032)
- WinRAR.exe (PID: 2204)
- msiexec.exe (PID: 2480)
- msiexec.exe (PID: 2564)
- Patch x86.exe (PID: 628)
Reads the computer name
- WinRAR.exe (PID: 2204)
- 4kvideodownloader.exe (PID: 4076)
Checks supported languages
- WinRAR.exe (PID: 2204)
- Patch x86.exe (PID: 628)
- cmd.exe (PID: 3764)
- 4kvideodownloader.exe (PID: 4076)
Executed as Windows Service
- msiexec.exe (PID: 2564)
- vssvc.exe (PID: 3068)
Reads Windows owner or organization settings
- msiexec.exe (PID: 2480)
- msiexec.exe (PID: 2564)
Reads the Windows organization settings
- msiexec.exe (PID: 2480)
- msiexec.exe (PID: 2564)
Application launched itself
- msiexec.exe (PID: 2564)
Reads Environment values
- vssvc.exe (PID: 3068)
Creates a directory in Program Files
- msiexec.exe (PID: 2564)
Creates a software uninstall entry
- msiexec.exe (PID: 2564)
Drops a file with a compile date too recent
- msiexec.exe (PID: 2564)
Starts CMD.EXE for commands execution
- Patch x86.exe (PID: 628)
Creates files in the program directory
- msiexec.exe (PID: 2564)
Searches for installed software
- msiexec.exe (PID: 2564)
Starts Internet Explorer
- 4kvideodownloader.exe (PID: 4076)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1368)
- iexplore.exe (PID: 2928)
Reads the computer name
- iexplore.exe (PID: 1368)
- chrome.exe (PID: 676)
- iexplore.exe (PID: 2584)
- chrome.exe (PID: 2632)
- chrome.exe (PID: 3156)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 2824)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 3420)
- chrome.exe (PID: 1588)
- chrome.exe (PID: 3892)
- chrome.exe (PID: 3936)
- chrome.exe (PID: 448)
- msiexec.exe (PID: 2072)
- msiexec.exe (PID: 2564)
- msiexec.exe (PID: 2480)
- MsiExec.exe (PID: 3868)
- vssvc.exe (PID: 3068)
- MsiExec.exe (PID: 828)
- MsiExec.exe (PID: 2176)
- iexplore.exe (PID: 2928)
- iexplore.exe (PID: 1160)
Application launched itself
- iexplore.exe (PID: 1368)
- chrome.exe (PID: 676)
- iexplore.exe (PID: 2928)
Checks Windows Trust Settings
- iexplore.exe (PID: 2584)
- iexplore.exe (PID: 1368)
- msiexec.exe (PID: 2072)
- msiexec.exe (PID: 2480)
- msiexec.exe (PID: 2564)
- iexplore.exe (PID: 1160)
- iexplore.exe (PID: 2928)
Checks supported languages
- iexplore.exe (PID: 1368)
- iexplore.exe (PID: 2584)
- chrome.exe (PID: 676)
- chrome.exe (PID: 1708)
- chrome.exe (PID: 2632)
- chrome.exe (PID: 3968)
- chrome.exe (PID: 2288)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 3156)
- chrome.exe (PID: 3496)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 1636)
- chrome.exe (PID: 3924)
- chrome.exe (PID: 1200)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 1144)
- chrome.exe (PID: 684)
- chrome.exe (PID: 2112)
- chrome.exe (PID: 3420)
- chrome.exe (PID: 1888)
- chrome.exe (PID: 576)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 448)
- chrome.exe (PID: 3764)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 1588)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 3032)
- chrome.exe (PID: 448)
- chrome.exe (PID: 4016)
- chrome.exe (PID: 3892)
- chrome.exe (PID: 3936)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 2824)
- chrome.exe (PID: 3680)
- msiexec.exe (PID: 2072)
- msiexec.exe (PID: 2564)
- msiexec.exe (PID: 2480)
- chrome.exe (PID: 2156)
- chrome.exe (PID: 1124)
- MsiExec.exe (PID: 3868)
- vssvc.exe (PID: 3068)
- MsiExec.exe (PID: 828)
- MsiExec.exe (PID: 2176)
- chrome.exe (PID: 1608)
- fltMC.exe (PID: 2392)
- chrome.exe (PID: 3828)
- chrome.exe (PID: 1728)
- iexplore.exe (PID: 2928)
- iexplore.exe (PID: 1160)
Reads internet explorer settings
- iexplore.exe (PID: 2584)
- iexplore.exe (PID: 1160)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1368)
- iexplore.exe (PID: 2928)
Changes settings of System certificates
- iexplore.exe (PID: 1368)
- iexplore.exe (PID: 2928)
Reads the date of Windows installation
- iexplore.exe (PID: 1368)
- chrome.exe (PID: 3420)
- iexplore.exe (PID: 2928)
Reads settings of System Certificates
- iexplore.exe (PID: 2584)
- iexplore.exe (PID: 1368)
- chrome.exe (PID: 3156)
- msiexec.exe (PID: 2480)
- msiexec.exe (PID: 2072)
- msiexec.exe (PID: 2564)
- iexplore.exe (PID: 1160)
- iexplore.exe (PID: 2928)
Creates files in the user directory
- iexplore.exe (PID: 2584)
- iexplore.exe (PID: 1160)
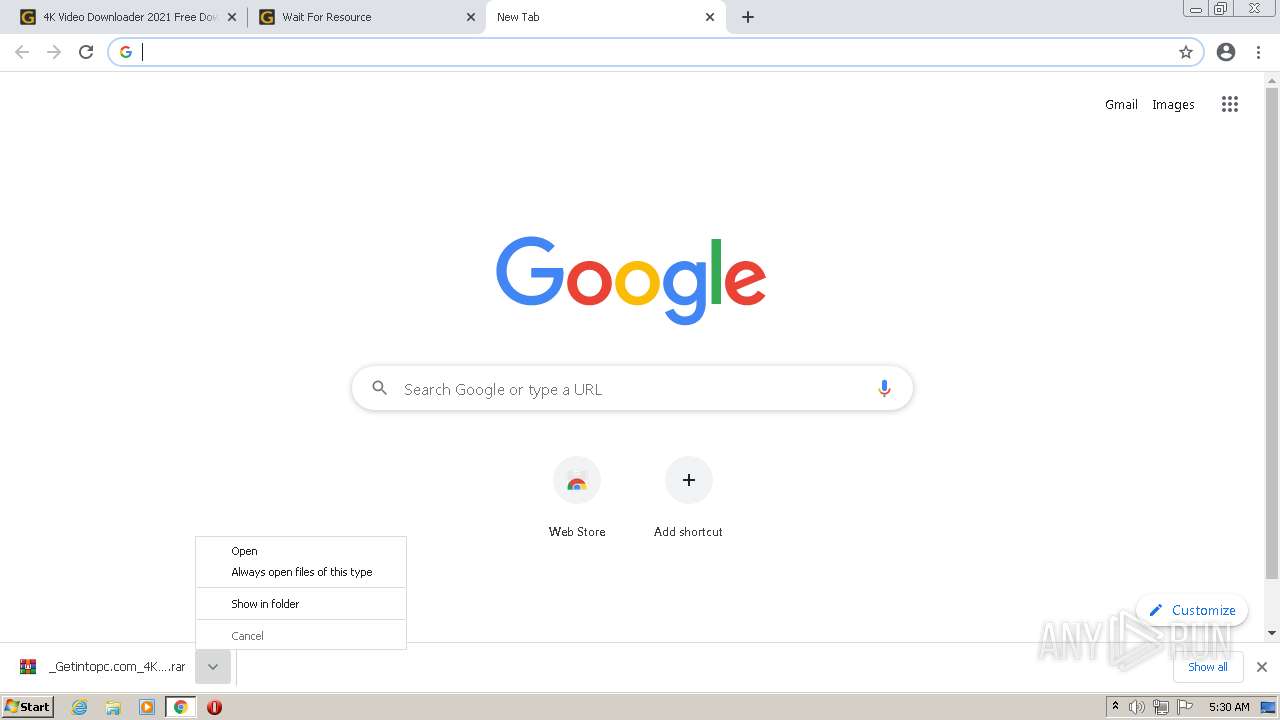
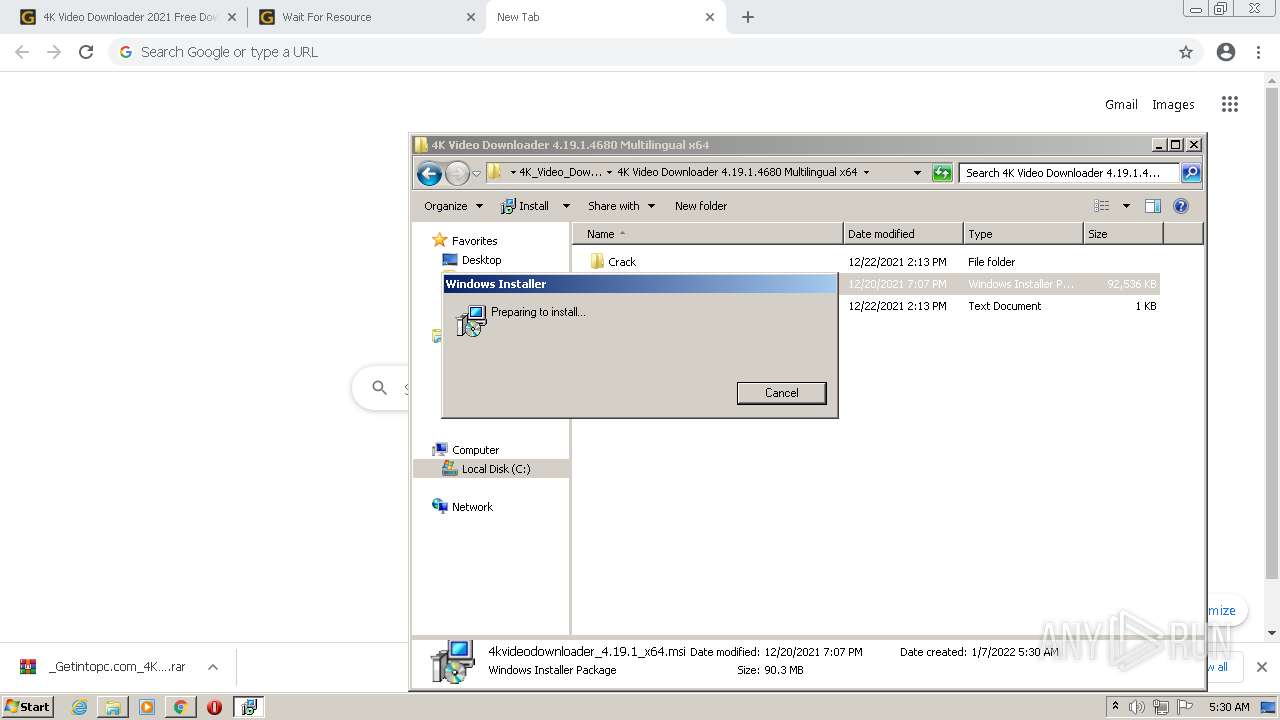
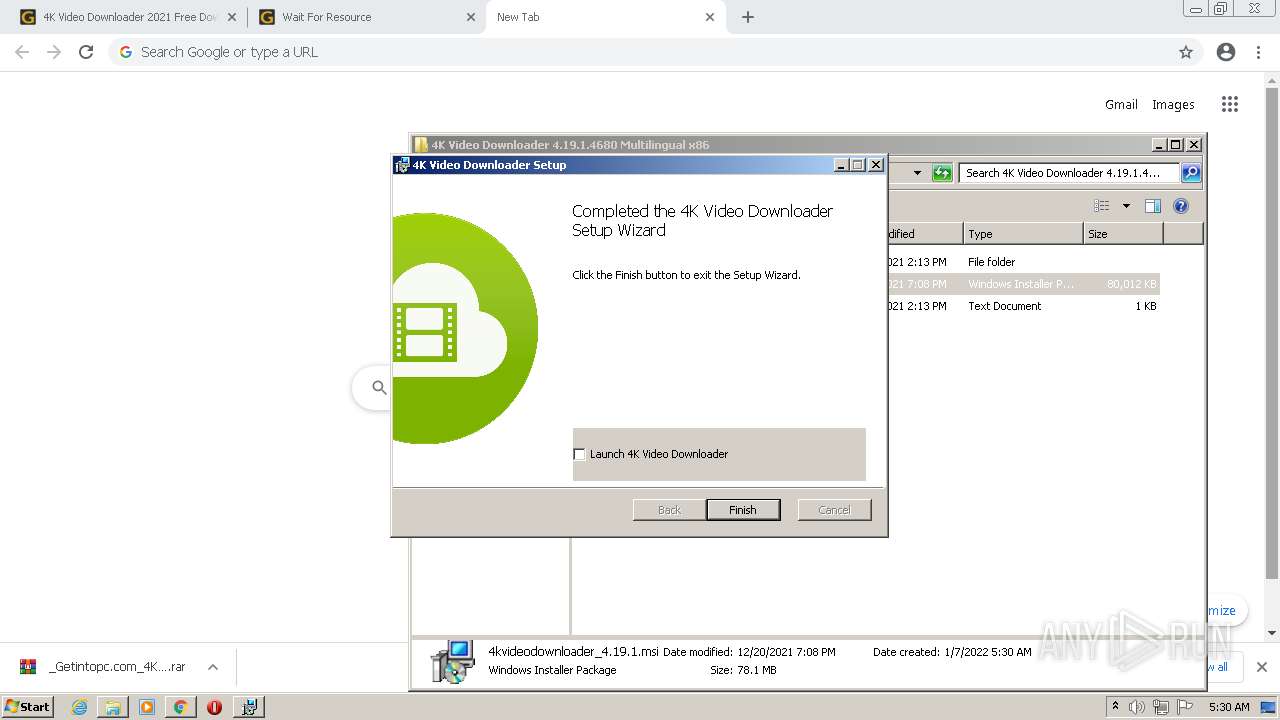
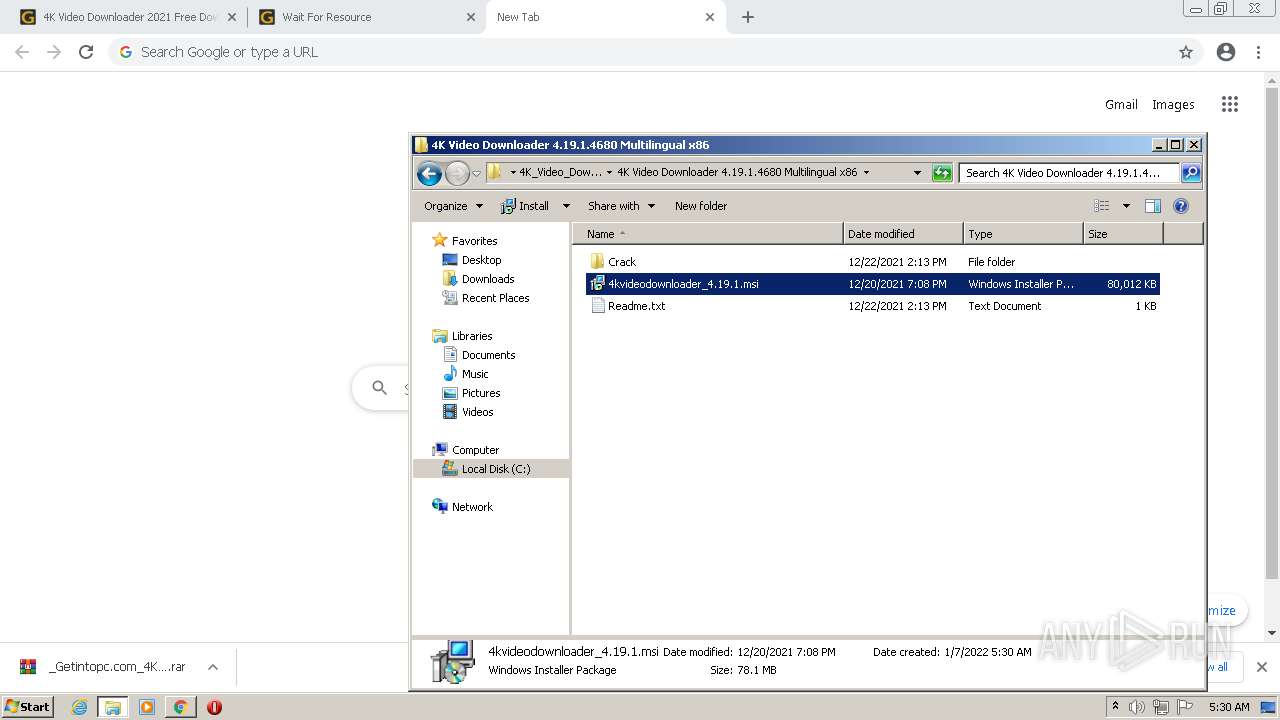
Manual execution by user
- chrome.exe (PID: 676)
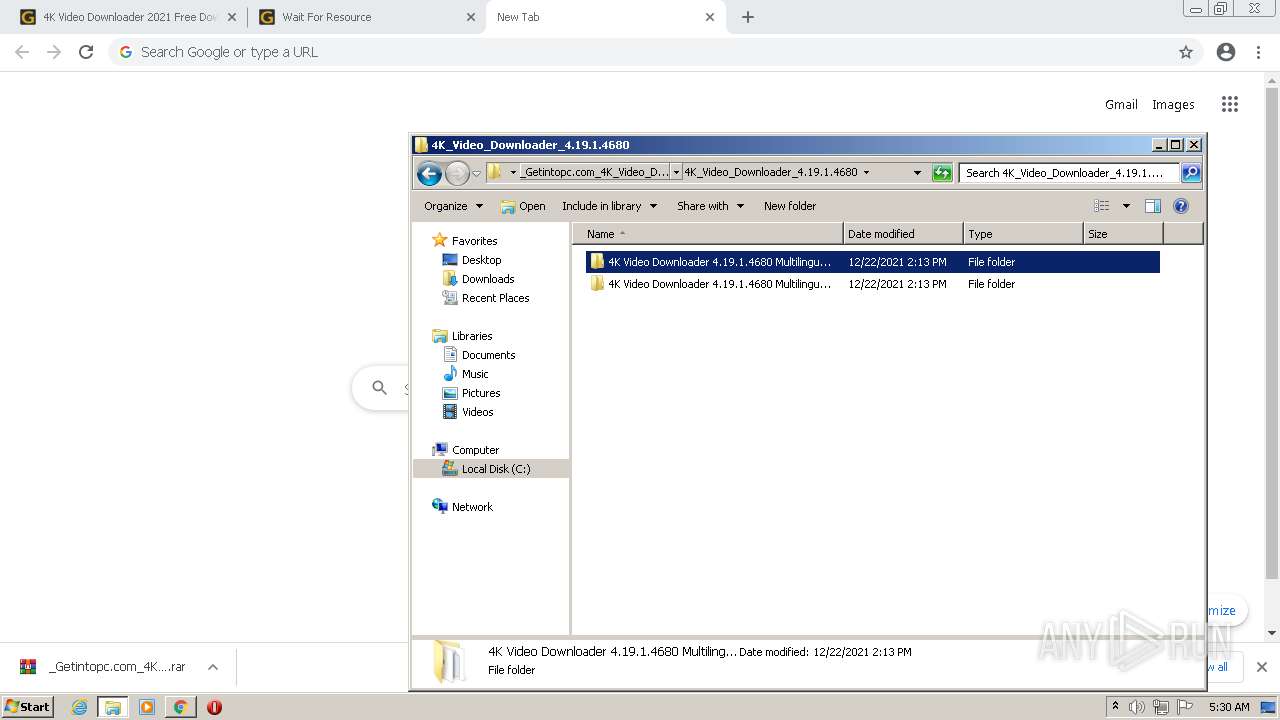
- WinRAR.exe (PID: 2204)
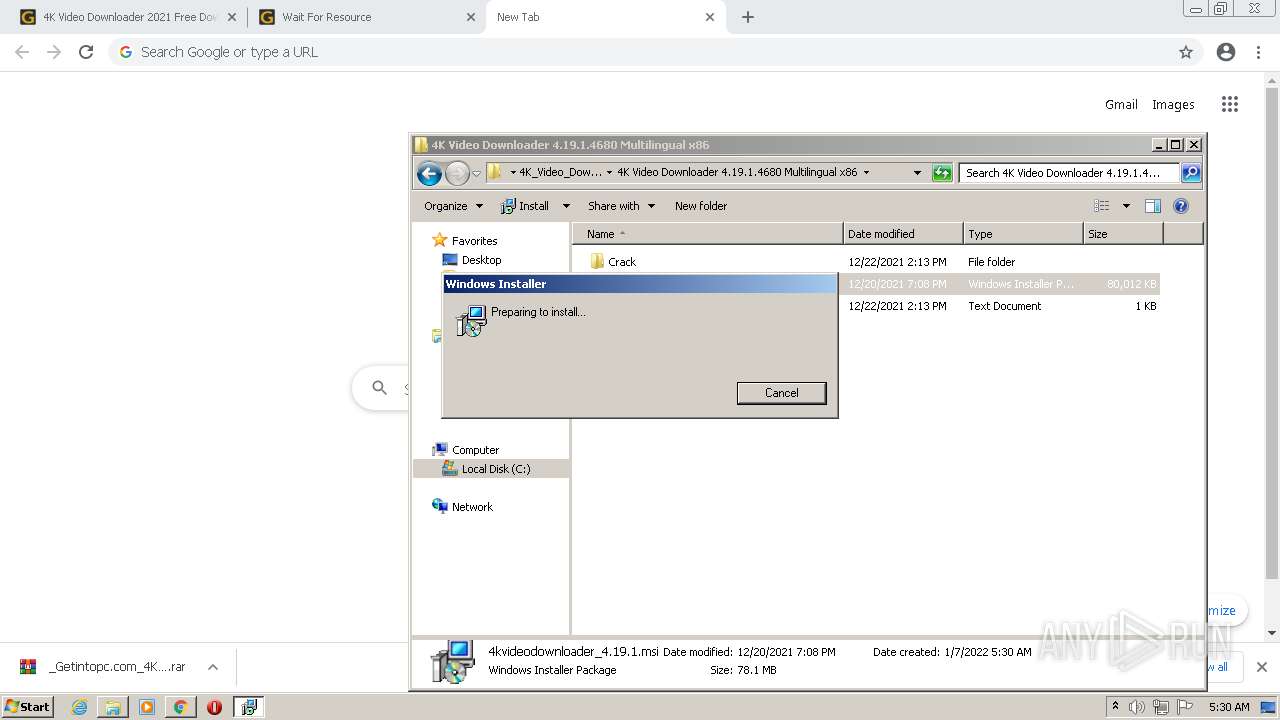
- msiexec.exe (PID: 2072)
- msiexec.exe (PID: 2480)
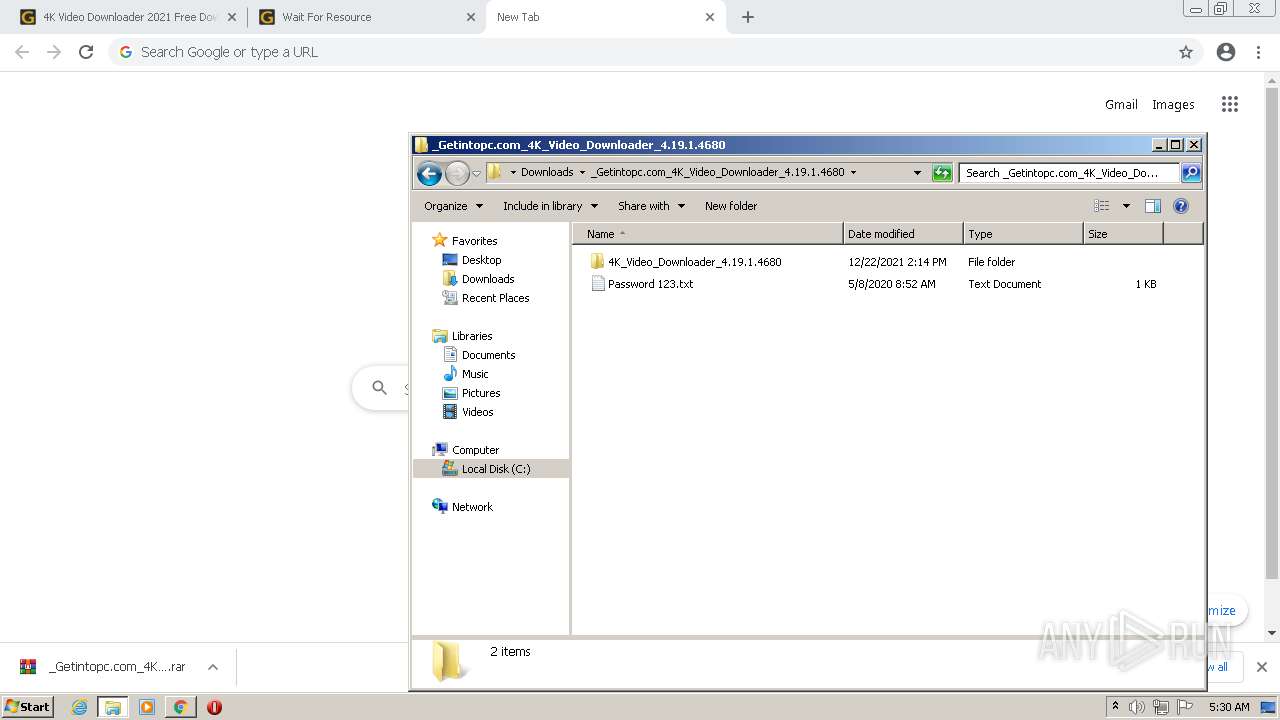
- Patch x86.exe (PID: 2968)
- Patch x86.exe (PID: 628)
- 4kvideodownloader.exe (PID: 4076)
Reads the hosts file
- chrome.exe (PID: 676)
- chrome.exe (PID: 3156)
- 4kvideodownloader.exe (PID: 4076)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
108
Monitored processes
56
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,15564232405127392245,4685873948388547793,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4028 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,15564232405127392245,4685873948388547793,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3596 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,15564232405127392245,4685873948388547793,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4116 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
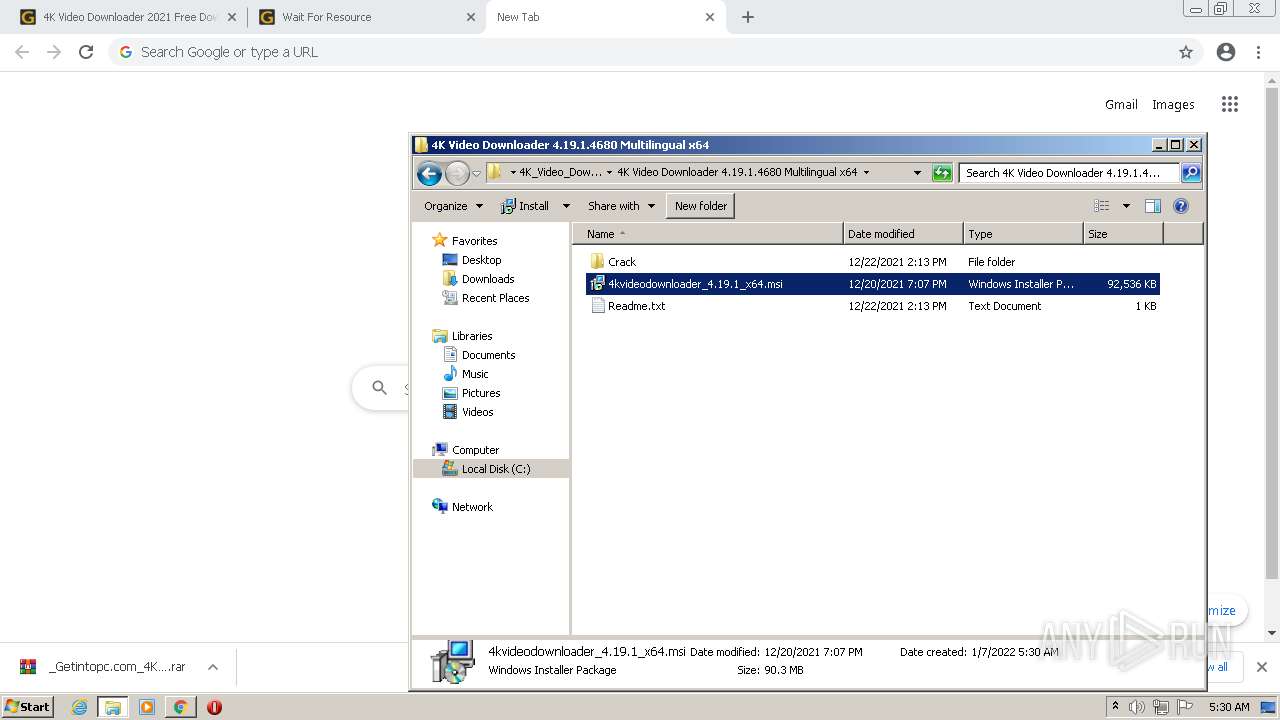
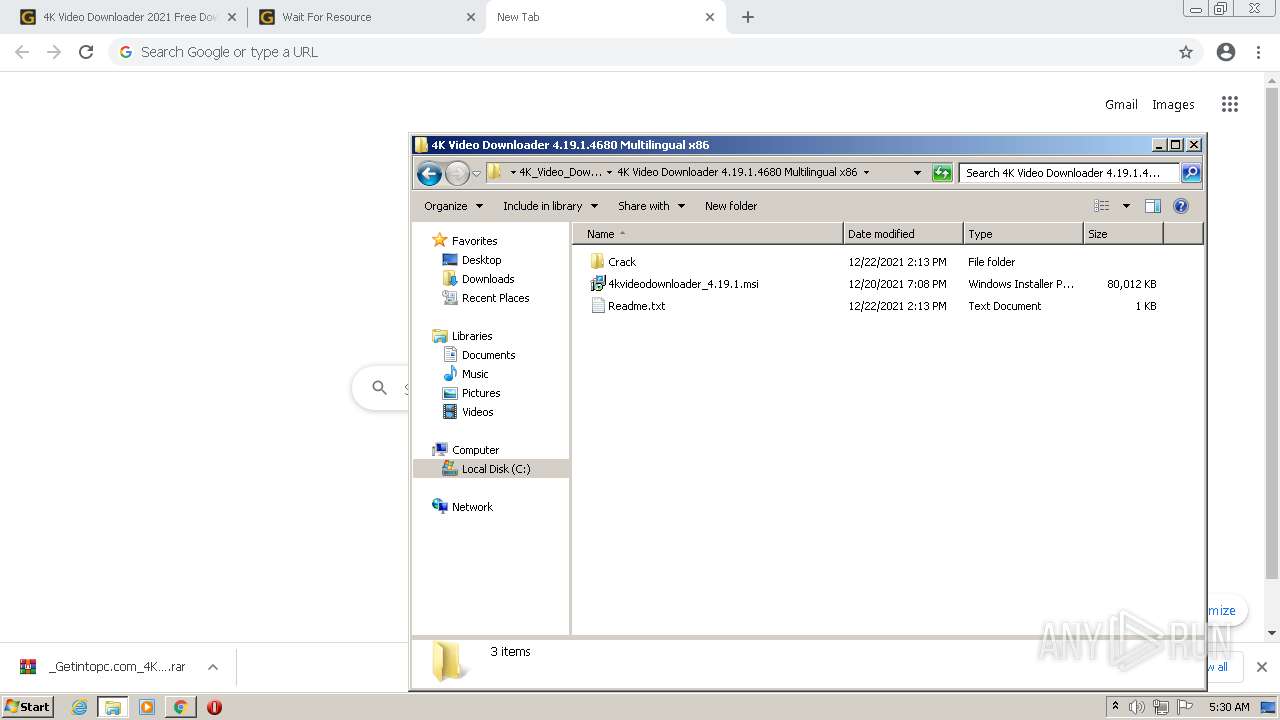
| 628 | "C:\Users\admin\Downloads\_Getintopc.com_4K_Video_Downloader_4.19.1.4680\4K_Video_Downloader_4.19.1.4680\4K Video Downloader 4.19.1.4680 Multilingual x86\Crack\Patch x86.exe" | C:\Users\admin\Downloads\_Getintopc.com_4K_Video_Downloader_4.19.1.4680\4K_Video_Downloader_4.19.1.4680\4K Video Downloader 4.19.1.4680 Multilingual x86\Crack\Patch x86.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,15564232405127392245,4685873948388547793,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3164 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 828 | C:\Windows\system32\MsiExec.exe -Embedding 8808EF865F1CA8DC1252A72274C296D4 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,15564232405127392245,4685873948388547793,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,15564232405127392245,4685873948388547793,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2928 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
56 022
Read events
54 843
Write events
1 151
Delete events
28
Modification events
| (PID) Process: | (1368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30933895 | |||
| (PID) Process: | (1368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30933895 | |||
| (PID) Process: | (1368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
65
Suspicious files
423
Text files
504
Unknown types
258
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 2584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 2584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\autoptimize_eacf97e003bce6ad39a4a1f8341cbc91[1].js | text | |
MD5:— | SHA256:— | |||
| 2584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:— | SHA256:— | |||
| 2584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 2584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\autoptimize_2a930e6b93951fdef02d83a253ba598b[1].css | text | |
MD5:— | SHA256:— | |||
| 2584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\4k-video-downloader-2021-free-download[1].htm | html | |
MD5:— | SHA256:— | |||
| 2584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 2584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
70
TCP/UDP connections
171
DNS requests
85
Threats
14 405
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3156 | chrome.exe | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | — | — | whitelisted |
2584 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2584 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2584 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2584 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2584 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD6vIn3vzMQlAoAAAABJf0y | US | der | 472 b | whitelisted |
2584 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2584 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDDxQmkH%2FlDagoAAAABJgJE | US | der | 472 b | whitelisted |
2584 | iexplore.exe | GET | 200 | 143.204.101.177:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2584 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEDW2QvuWQOeECgAAAAEl%2F%2BY%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2584 | iexplore.exe | 45.141.156.118:443 | getintopc.com | — | — | suspicious |
2584 | iexplore.exe | 104.18.31.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | unknown |
2584 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2584 | iexplore.exe | 104.18.30.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
2584 | iexplore.exe | 142.250.185.202:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2584 | iexplore.exe | 142.250.185.130:443 | pagead2.googlesyndication.com | Google Inc. | US | suspicious |
2584 | iexplore.exe | 69.16.175.10:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
2584 | iexplore.exe | 142.250.186.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2584 | iexplore.exe | 199.232.192.134:443 | getintopcofficial.disqus.com | — | US | suspicious |
2584 | iexplore.exe | 143.204.98.69:443 | c.disquscdn.com | — | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
getintopc.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
code.jquery.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3156 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
3156 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
3156 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED invalid ack |
3156 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM Packet with invalid ack |
3156 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED invalid ack |
3156 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM Packet with invalid ack |
3156 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |
3156 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED invalid ack |
3156 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM Packet with invalid ack |
3156 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |
Process | Message |
|---|---|
4kvideodownloader.exe | QEventLoop: Cannot be used without QApplication
|
4kvideodownloader.exe | QWindowsEGLStaticContext::create: Could not initialize EGL display: error 0x3001
|
4kvideodownloader.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
4kvideodownloader.exe | [4076:2492:20220107,053123.168:ERROR crashpad_client_win.cc:505] CreateProcess: Access is denied. (5)
|