| File name: | FW Error screen (326 KB).msg |
| Full analysis: | https://app.any.run/tasks/f6ce5ab3-7a3d-4bb3-962a-50151df8e820 |
| Verdict: | Malicious activity |
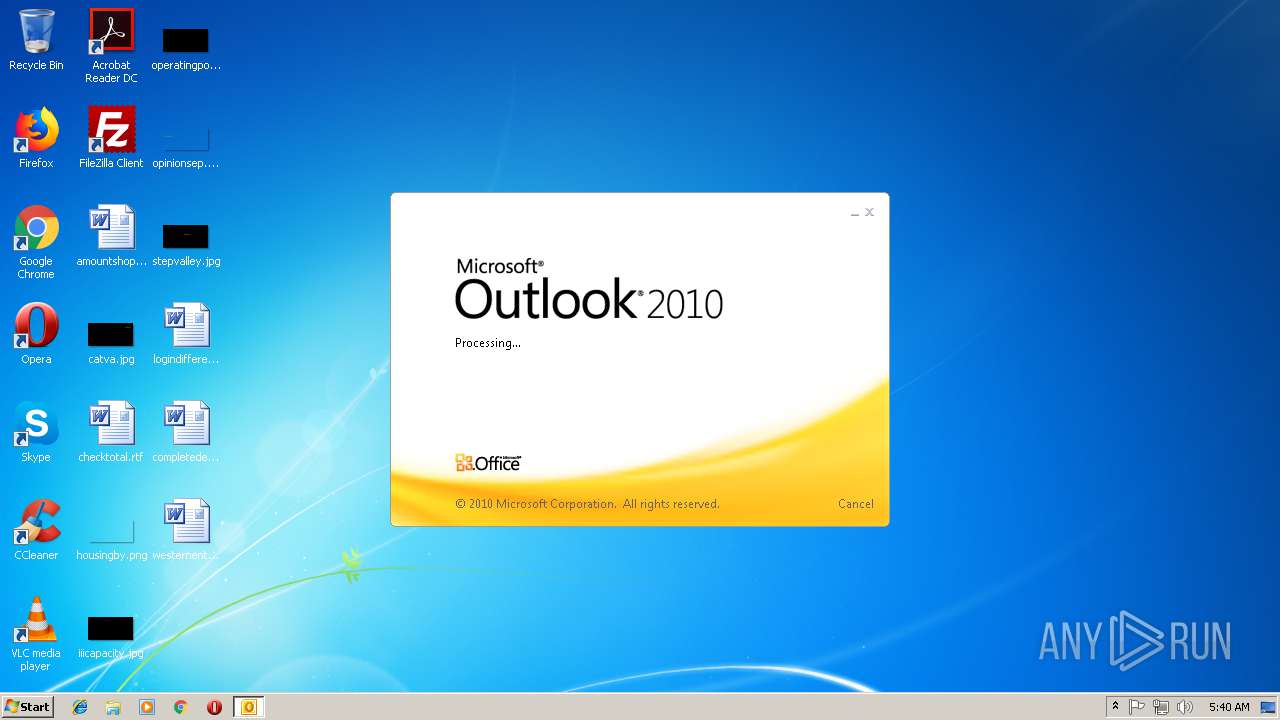
| Analysis date: | November 15, 2018, 05:40:01 |
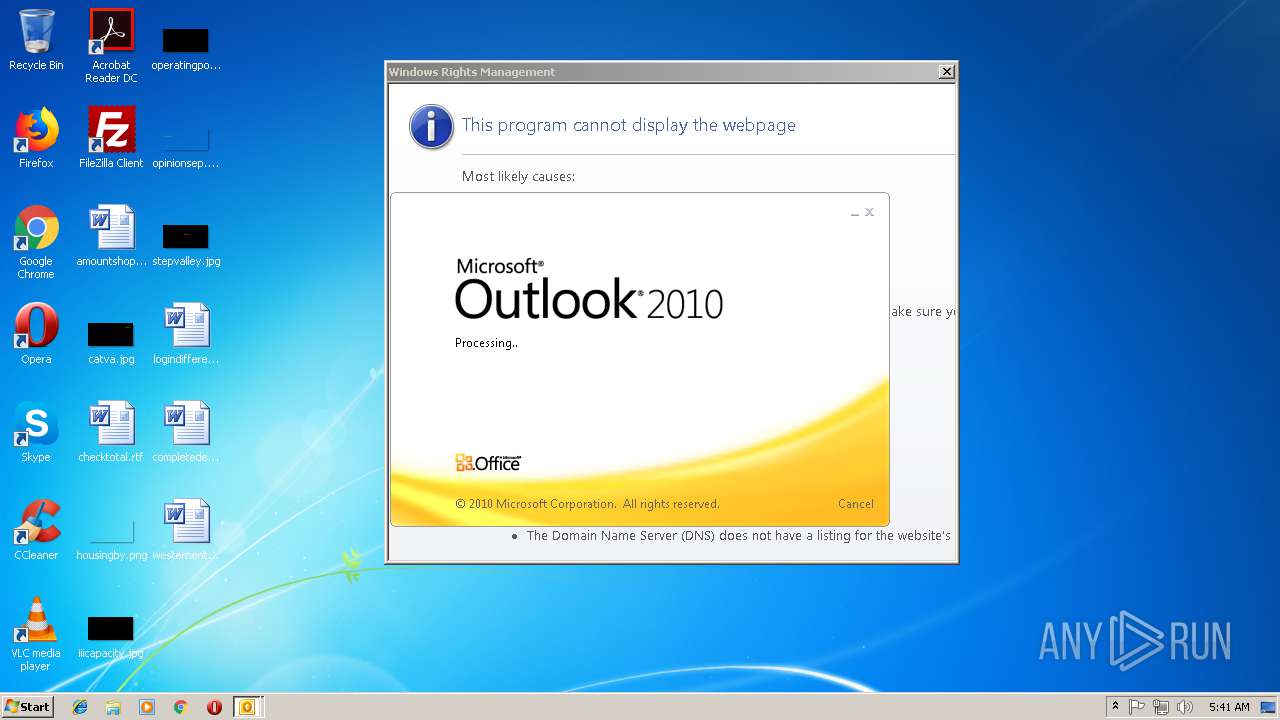
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | A8931167ED6F7008794F27657CF9E192 |
| SHA1: | 24E8AE5D05CA0443F2E1F0E5FCDEBA214BAE10B8 |
| SHA256: | B2EFA46D41637D9416E1CC19C2973EF0B12C9E133B68F46A246BE38431FB5D22 |
| SSDEEP: | 6144:1ORnbx5oPBDpujmxcVt7VHJQk13Dp4TRtNDAIiov2jahBmJZQf5Ax8hGFa+EICf:1AvkFujmxK7VpQmziTRtND5iov2jNZeo |
MALICIOUS
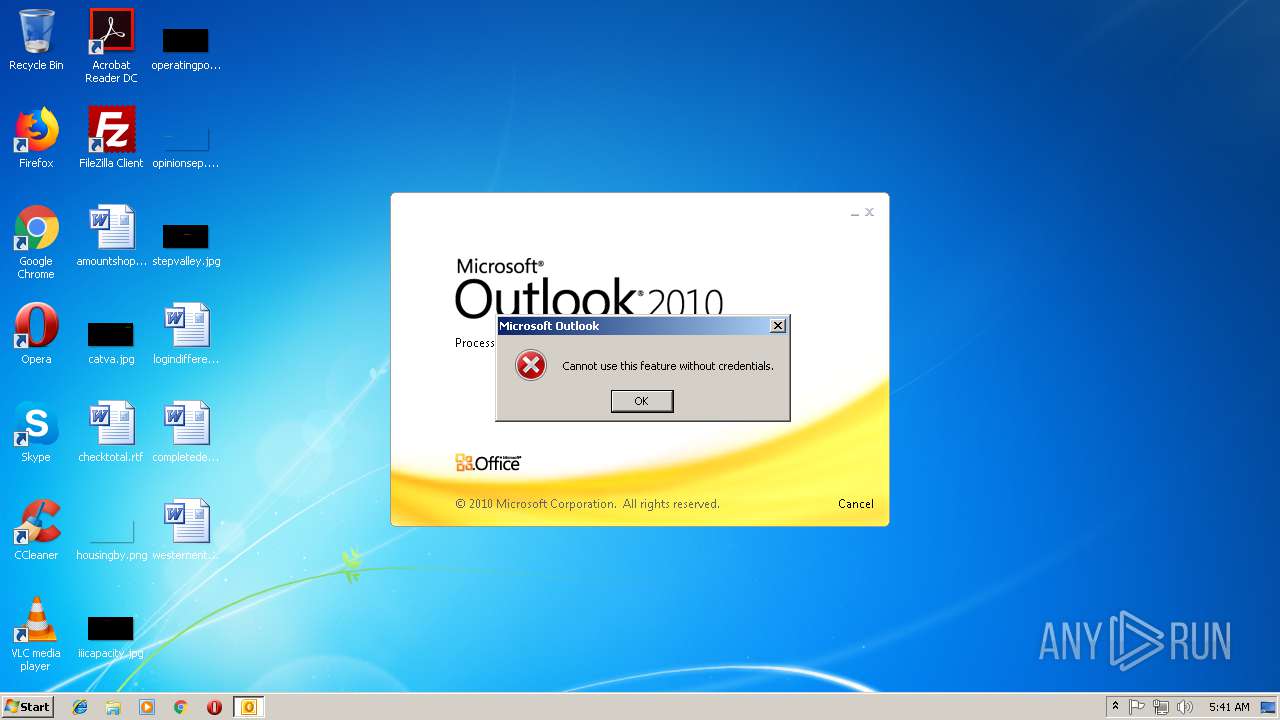
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3008)
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3008)
Reads internet explorer settings
- OUTLOOK.EXE (PID: 3008)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
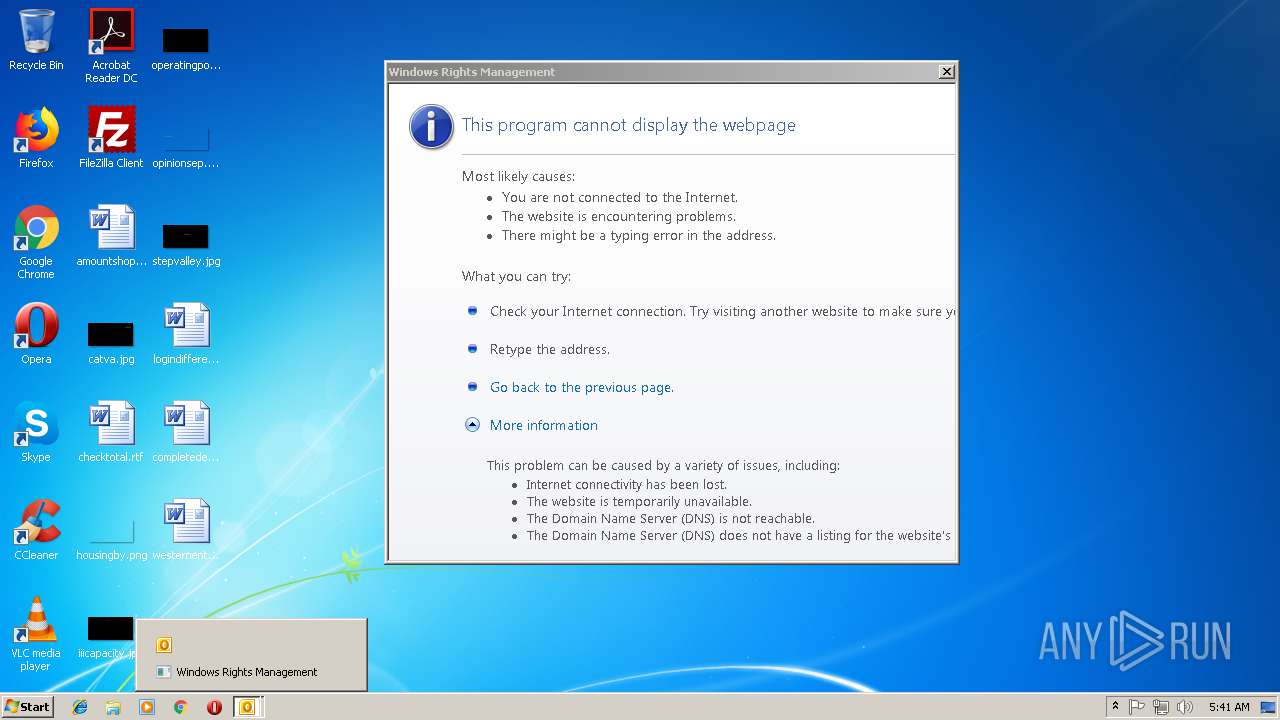
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
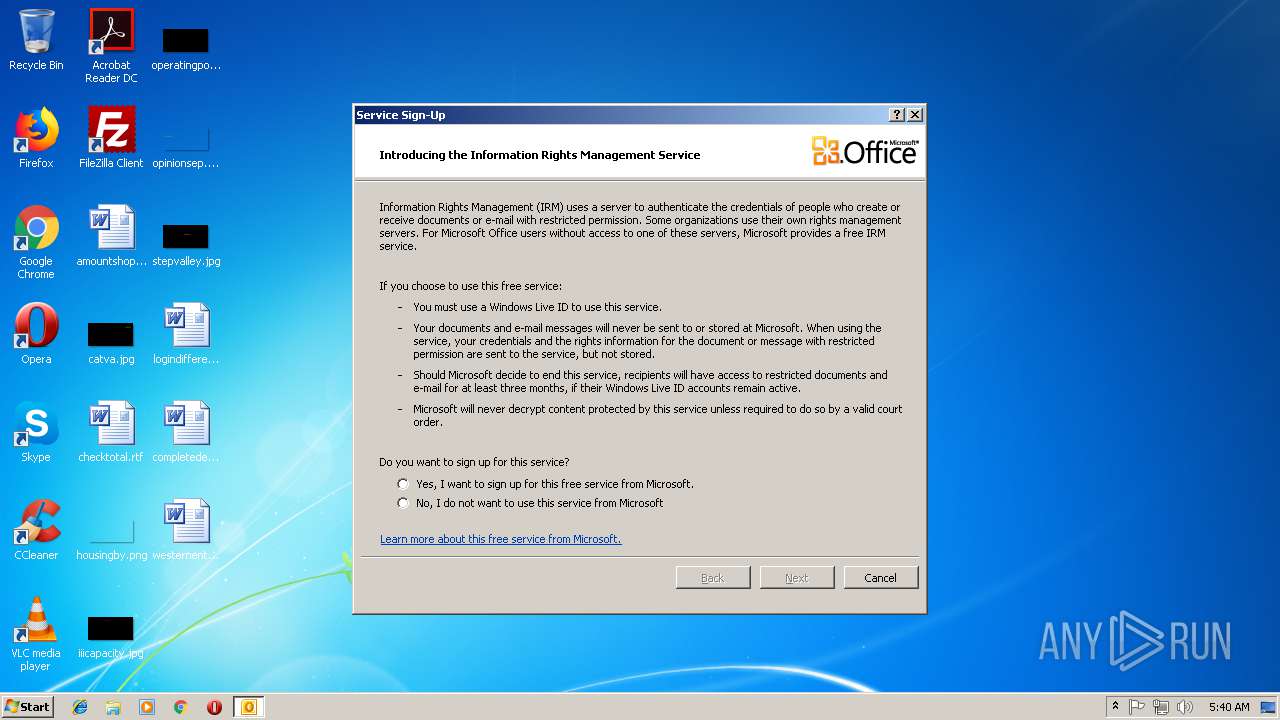
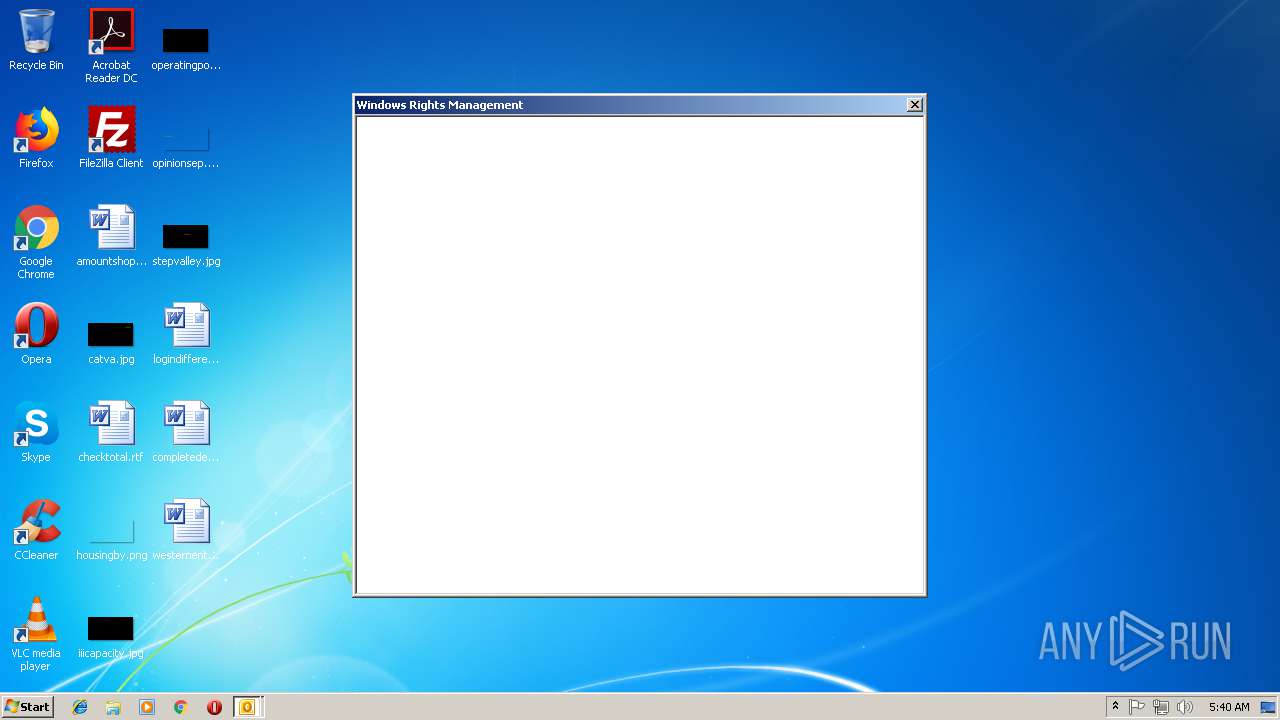
| 1992 | "C:\Windows\system32\rmactivate.exe" | C:\Windows\system32\rmactivate.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Rights Management Services Activation for Desktop Security Processor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3008 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\FW Error screen (326 KB).msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
589
Read events
521
Write events
65
Delete events
3
Modification events
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | /{l |
Value: 2F7B6C00C00B0000010000000000000000000000 | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: C00B0000B45A9AB3A57CD40100000000 | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219778560 | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1299120149 | |||
Executable files
0
Suspicious files
8
Text files
42
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3008 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9B9F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3008 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\ServiceLocator[1].asmx | — | |
MD5:— | SHA256:— | |||
| 1992 | rmactivate.exe | C:\Users\admin\AppData\Local\Temp\CabA803.tmp | — | |
MD5:— | SHA256:— | |||
| 1992 | rmactivate.exe | C:\Users\admin\AppData\Local\Temp\TarA804.tmp | — | |
MD5:— | SHA256:— | |||
| 3008 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\ErrorPageTemplate[1] | — | |
MD5:— | SHA256:— | |||
| 3008 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\errorPageStrings[1] | — | |
MD5:— | SHA256:— | |||
| 3008 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\SystemCertificates\My\Certificates\E02357FC7708441D4B0BE5F371F4B28961870F70 | binary | |
MD5:— | SHA256:— | |||
| 1992 | rmactivate.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B8CC409ACDBF2A2FE04C56F2875B1FD6 | binary | |
MD5:— | SHA256:— | |||
| 1992 | rmactivate.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F90F18257CBB4D84216AC1E1F3BB2C76 | der | |
MD5:— | SHA256:— | |||
| 1992 | rmactivate.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F90F18257CBB4D84216AC1E1F3BB2C76 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
17
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3008 | OUTLOOK.EXE | GET | 302 | 172.227.168.22:80 | http://go.microsoft.com/fwlink/?LinkId=5998&LANGID=1033 | US | — | — | whitelisted |
1992 | rmactivate.exe | GET | 200 | 104.107.216.163:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | NL | der | 781 b | whitelisted |
1992 | rmactivate.exe | GET | 200 | 104.107.216.163:80 | http://crl.microsoft.com/pki/crl/products/WinPCA.crl | NL | der | 530 b | whitelisted |
1992 | rmactivate.exe | GET | 200 | 104.107.216.163:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | NL | der | 550 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3008 | OUTLOOK.EXE | 13.107.6.181:443 | 6e7e26ce-8ca5-41b5-a6bd-d8192a7abe2e.rms.ap.aadrm.com | Microsoft Corporation | US | suspicious |
3008 | OUTLOOK.EXE | 172.227.168.22:80 | go.microsoft.com | Akamai International B.V. | US | whitelisted |
3008 | OUTLOOK.EXE | 65.55.61.29:443 | certification.drm.microsoft.com | Microsoft Corporation | US | whitelisted |
1992 | rmactivate.exe | 104.107.216.163:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
6e7e26ce-8ca5-41b5-a6bd-d8192a7abe2e.rms.ap.aadrm.com |
| suspicious |
crl.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
certification.drm.microsoft.com |
| whitelisted |