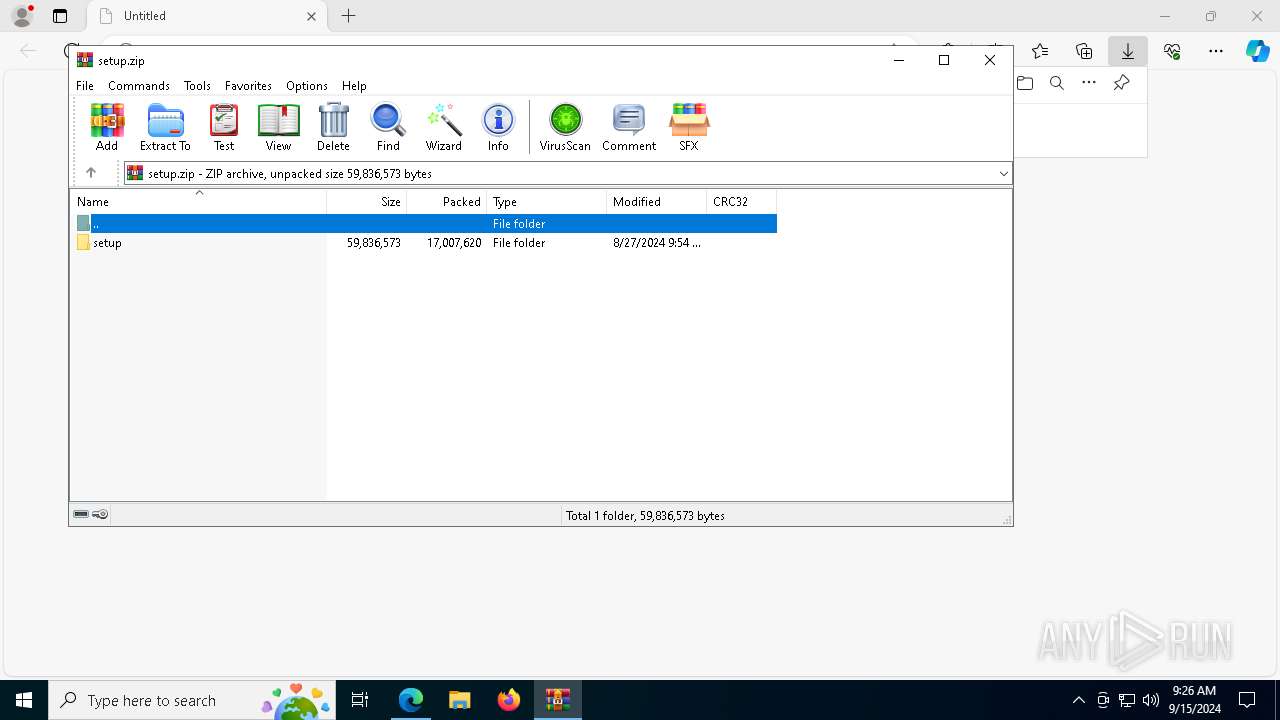
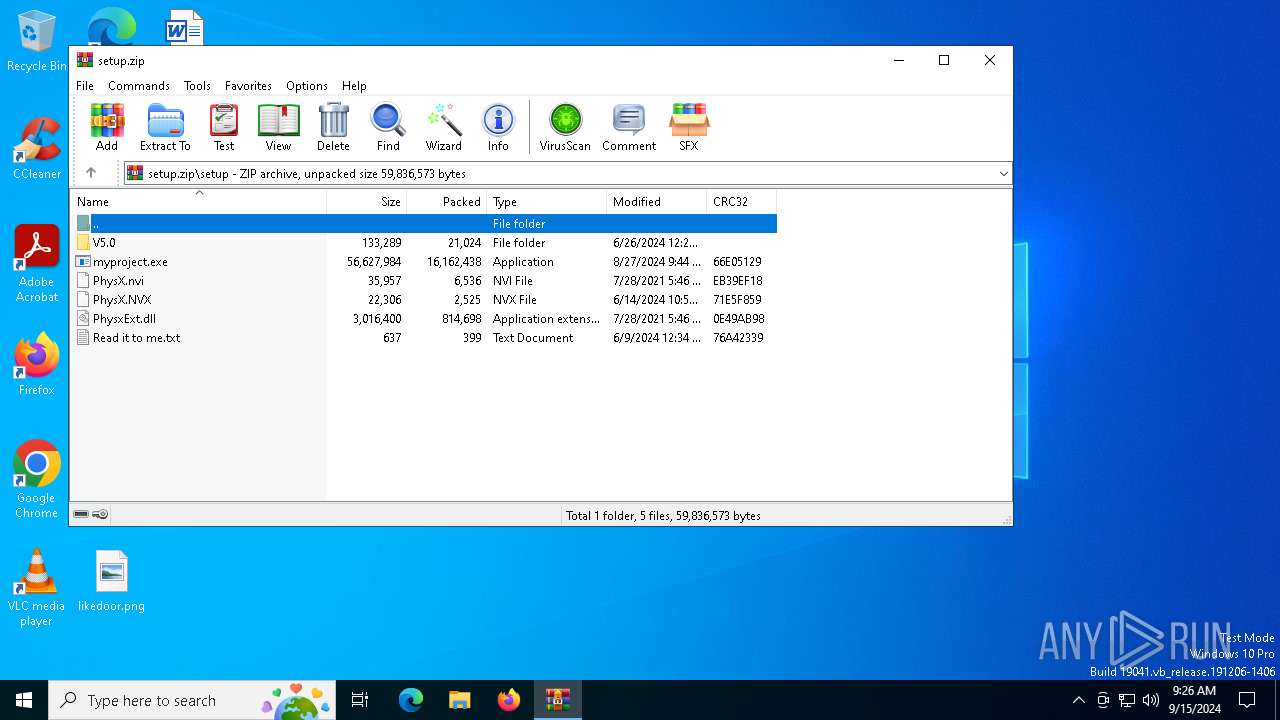
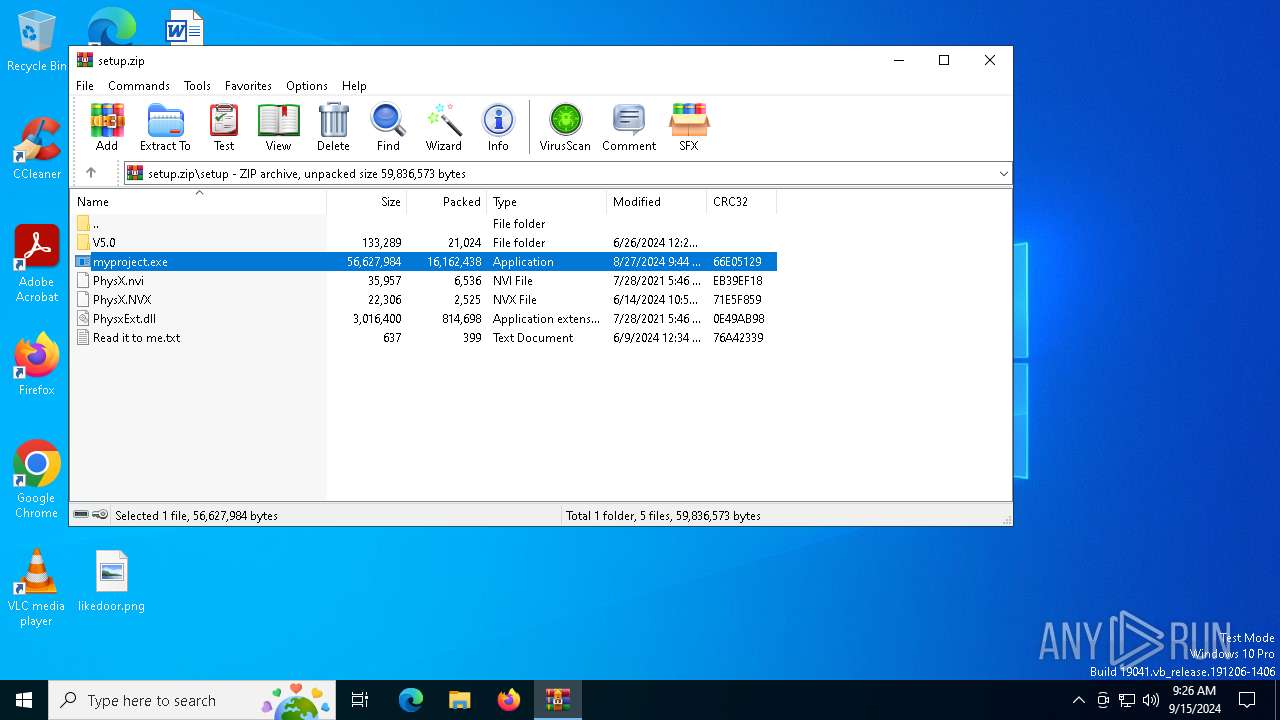
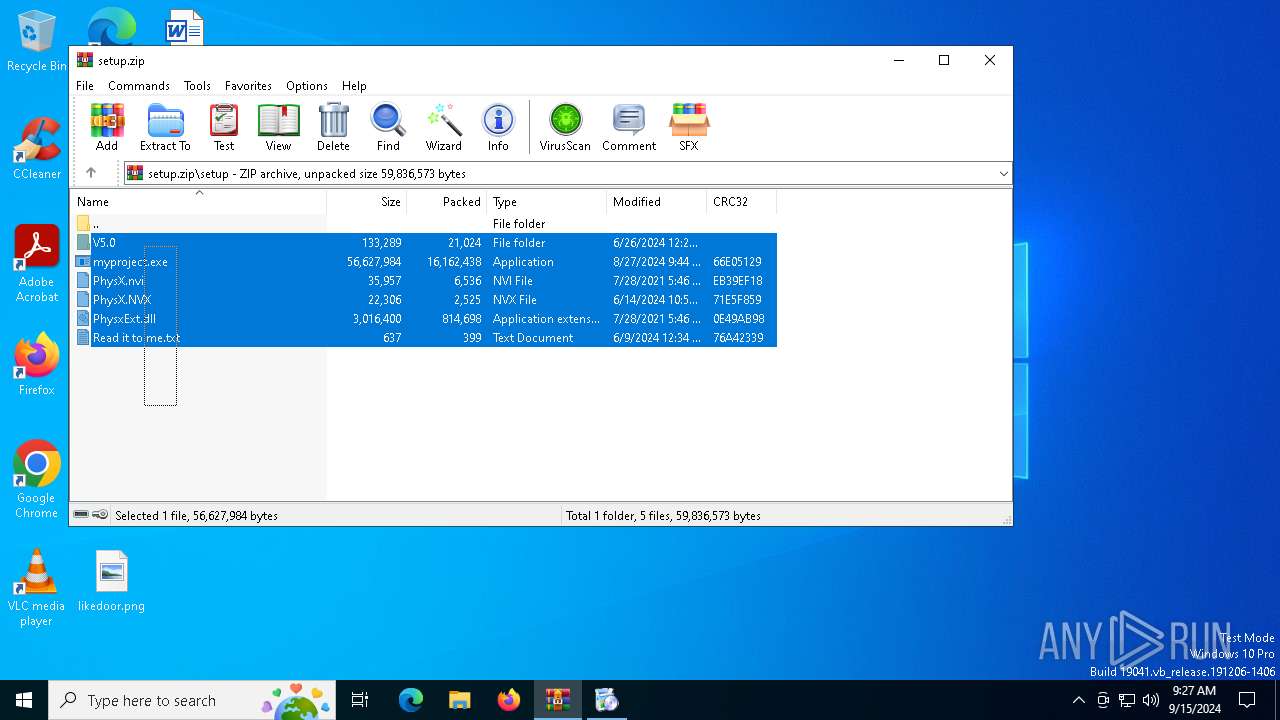
| URL: | https://github.com/PPJelly/Celery-executor/releases/download/Download/setup.zip |
| Full analysis: | https://app.any.run/tasks/3cf60516-a7fd-4f65-ba2c-ac97a7b0dd95 |
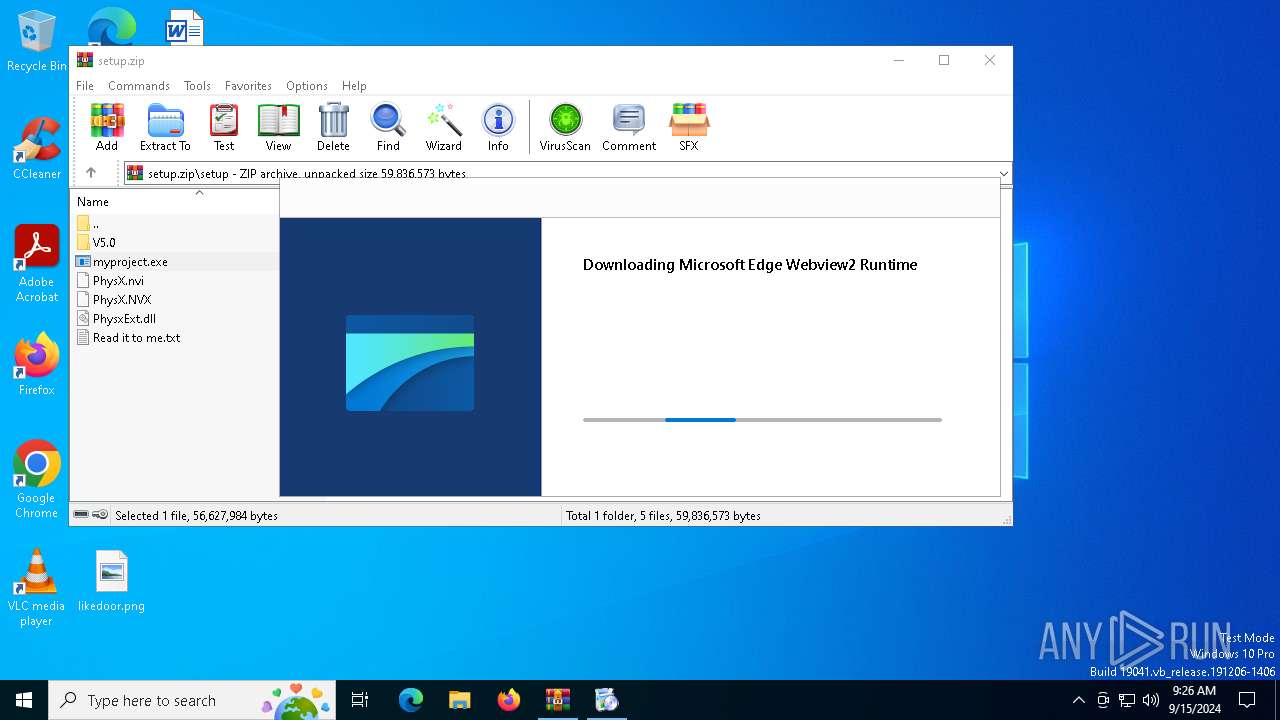
| Verdict: | Malicious activity |
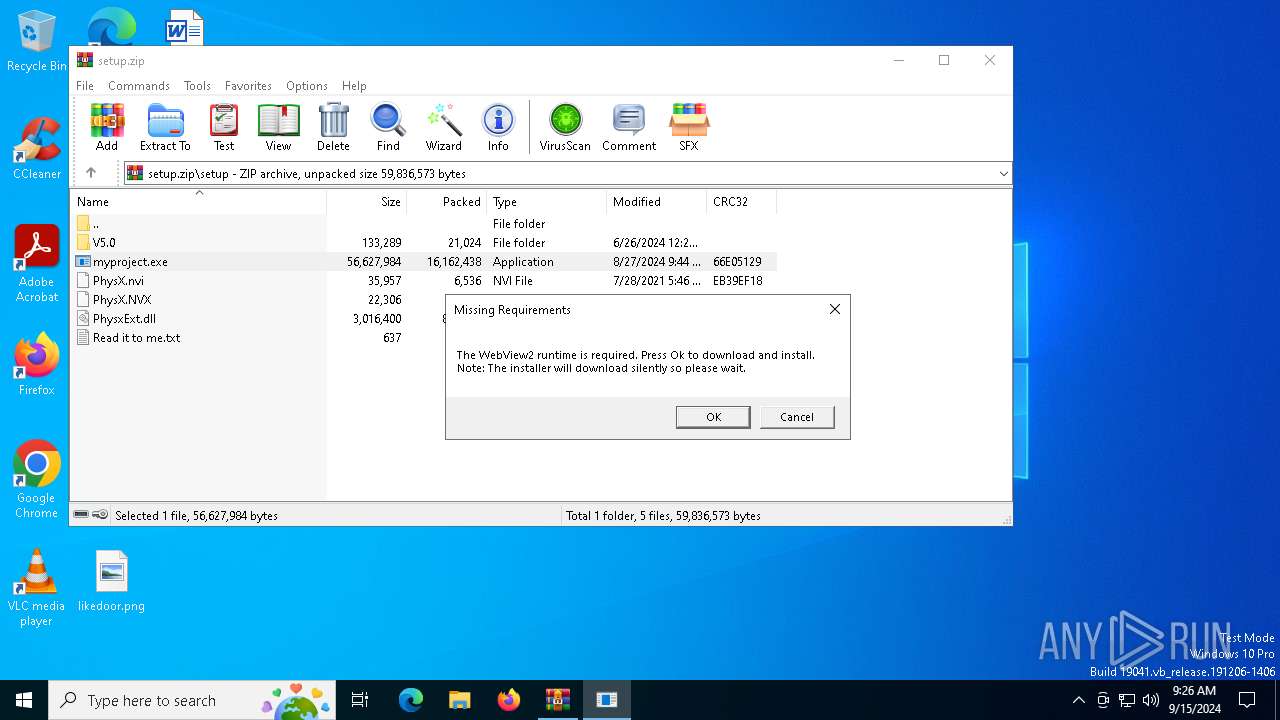
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | September 15, 2024, 09:26:18 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5F4C92197EFD420CD929C13D0DA2C531 |
| SHA1: | F8BD7390DD7449F006CE0659C1DF7299D952D8E9 |
| SHA256: | B2E0132BC827C01A1E85583B4B6D4D992162241790ADB24C8C038C6A30E936E6 |
| SSDEEP: | 3:N8tEdXoihXc/sRtE2kCcSLJf8xQhc:2uphXCsRtr9tUuc |
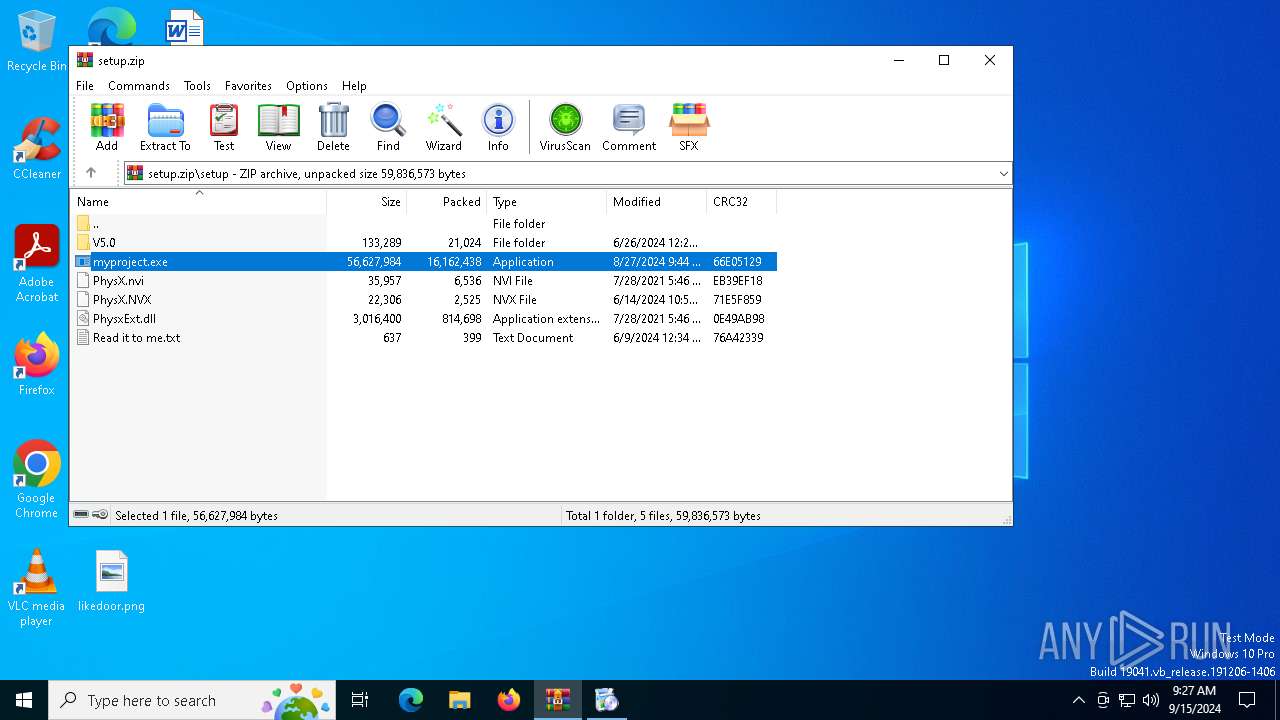
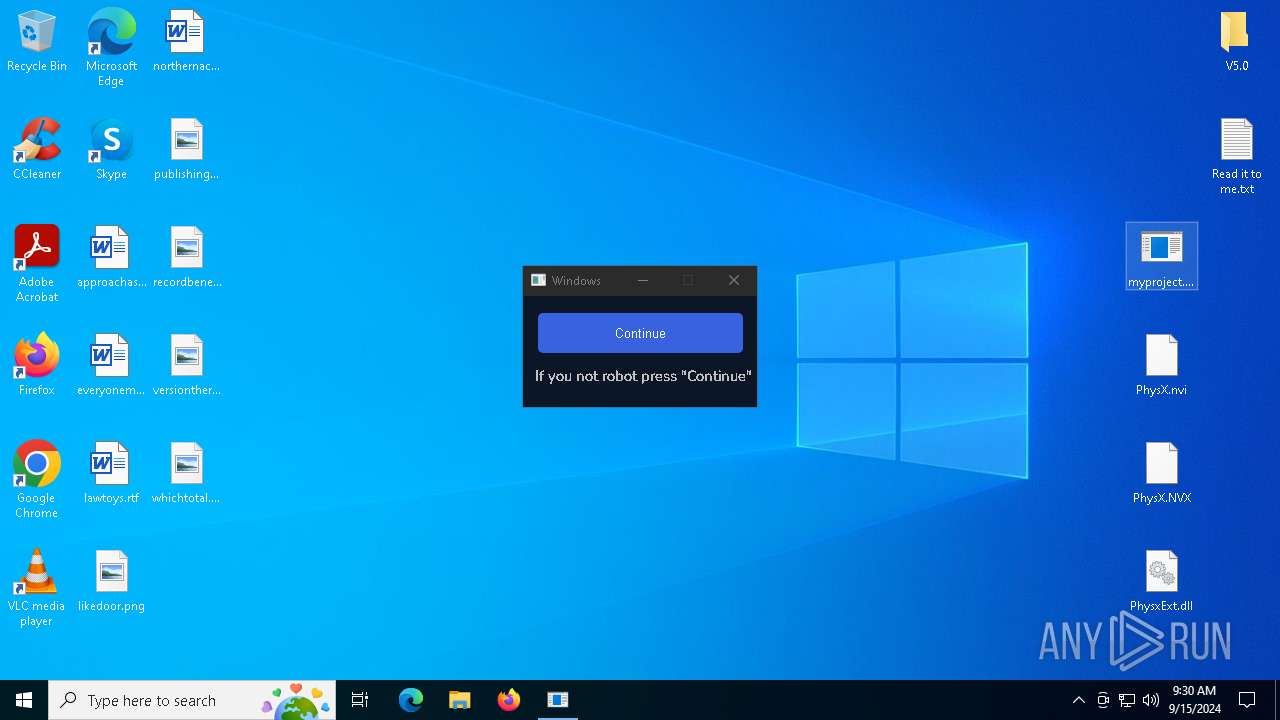
MALICIOUS
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 6728)
The DLL Hijacking
- msedgewebview2.exe (PID: 3896)
- msedgewebview2.exe (PID: 7600)
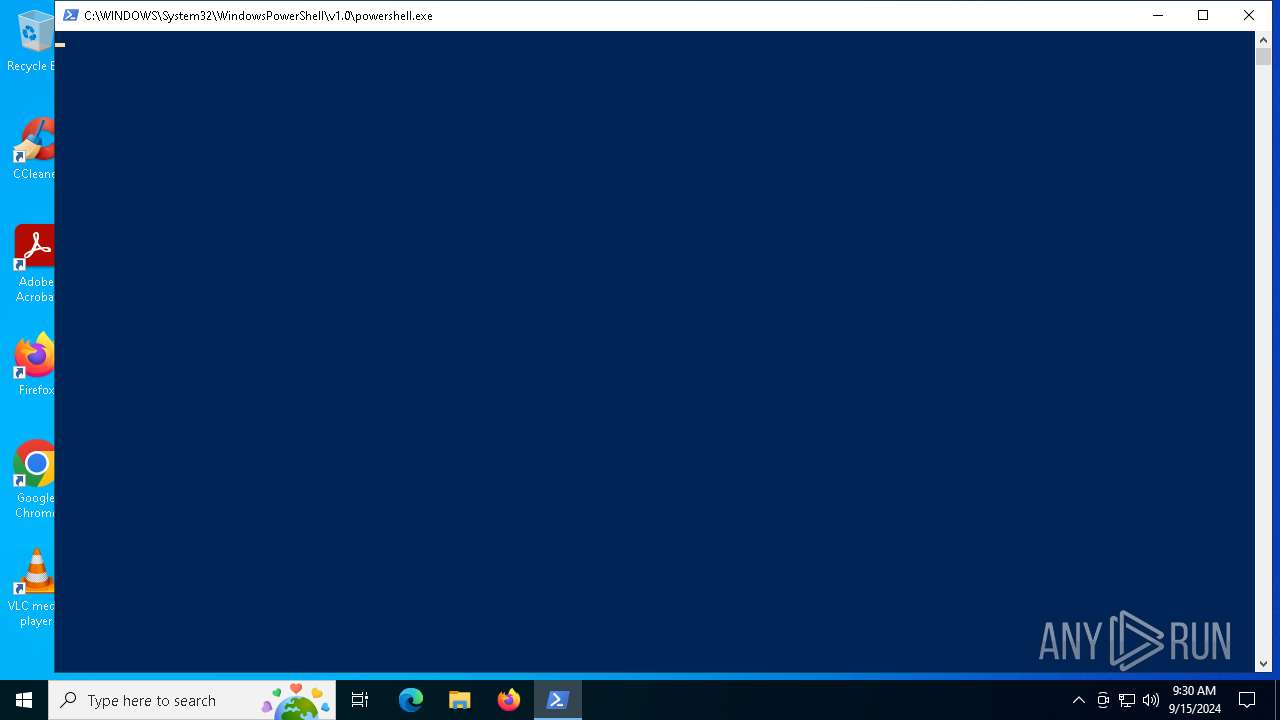
Run PowerShell with an invisible window
- powershell.exe (PID: 7568)
- powershell.exe (PID: 2112)
- powershell.exe (PID: 7256)
- powershell.exe (PID: 1932)
- powershell.exe (PID: 7608)
- powershell.exe (PID: 6868)
- powershell.exe (PID: 1492)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 7280)
Adds path to the Windows Defender exclusion list
- myproject.exe (PID: 4024)
- powershell.exe (PID: 7568)
- driver1.exe (PID: 2728)
Uses Task Scheduler to run other applications
- myproject.exe (PID: 4024)
RHADAMANTHYS has been detected (SURICATA)
- OpenWith.exe (PID: 5476)
- OOBE-Maintenance.exe (PID: 7184)
Actions looks like stealing of personal data
- OOBE-Maintenance.exe (PID: 7184)
Stealers network behavior
- OOBE-Maintenance.exe (PID: 7184)
RHADAMANTHYS has been detected (YARA)
- OOBE-Maintenance.exe (PID: 7184)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6912)
- MicrosoftEdgeUpdate.exe (PID: 6728)
- MicrosoftEdgeUpdate.exe (PID: 7296)
- msedgewebview2.exe (PID: 3244)
- myproject.exe (PID: 2524)
- msedgewebview2.exe (PID: 7152)
- myproject.exe (PID: 2584)
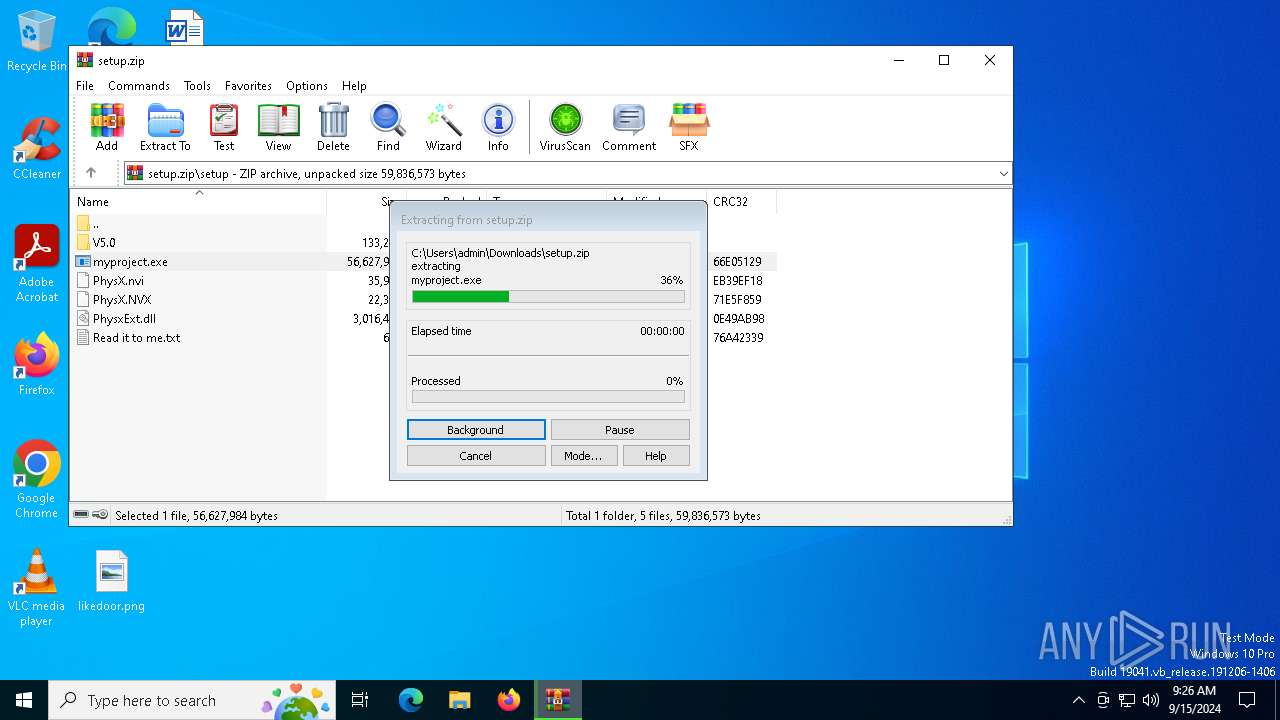
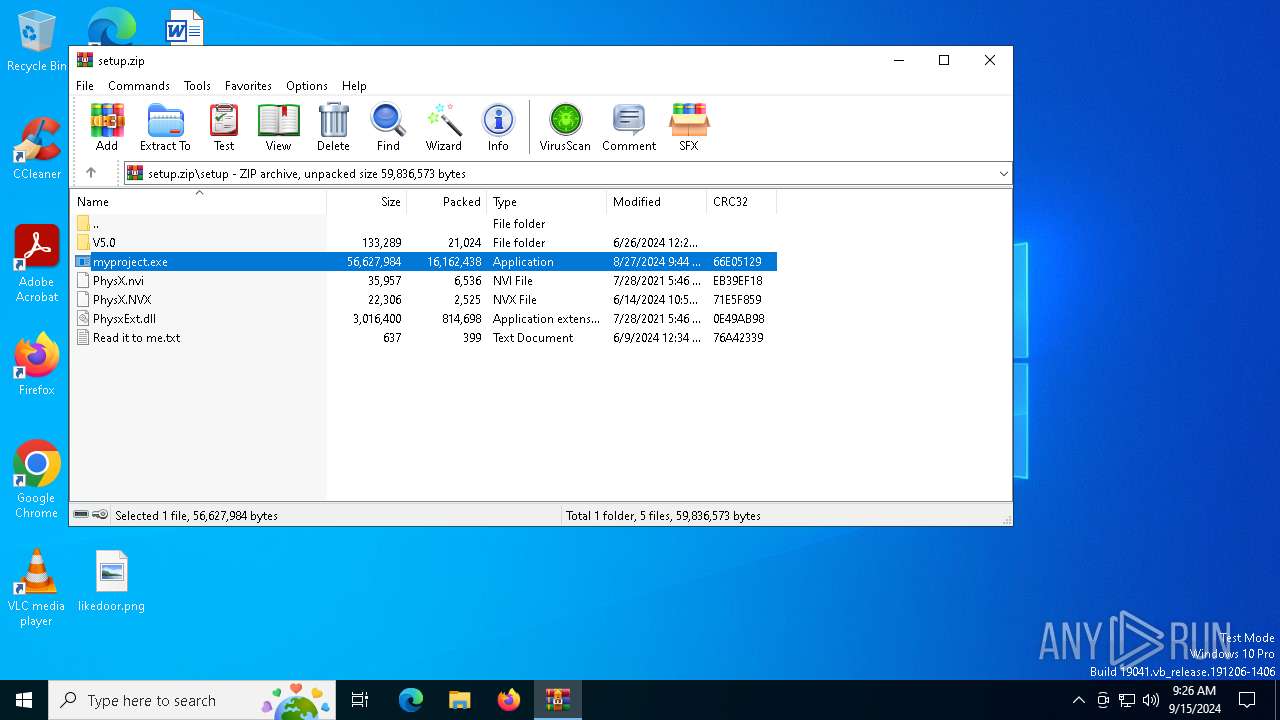
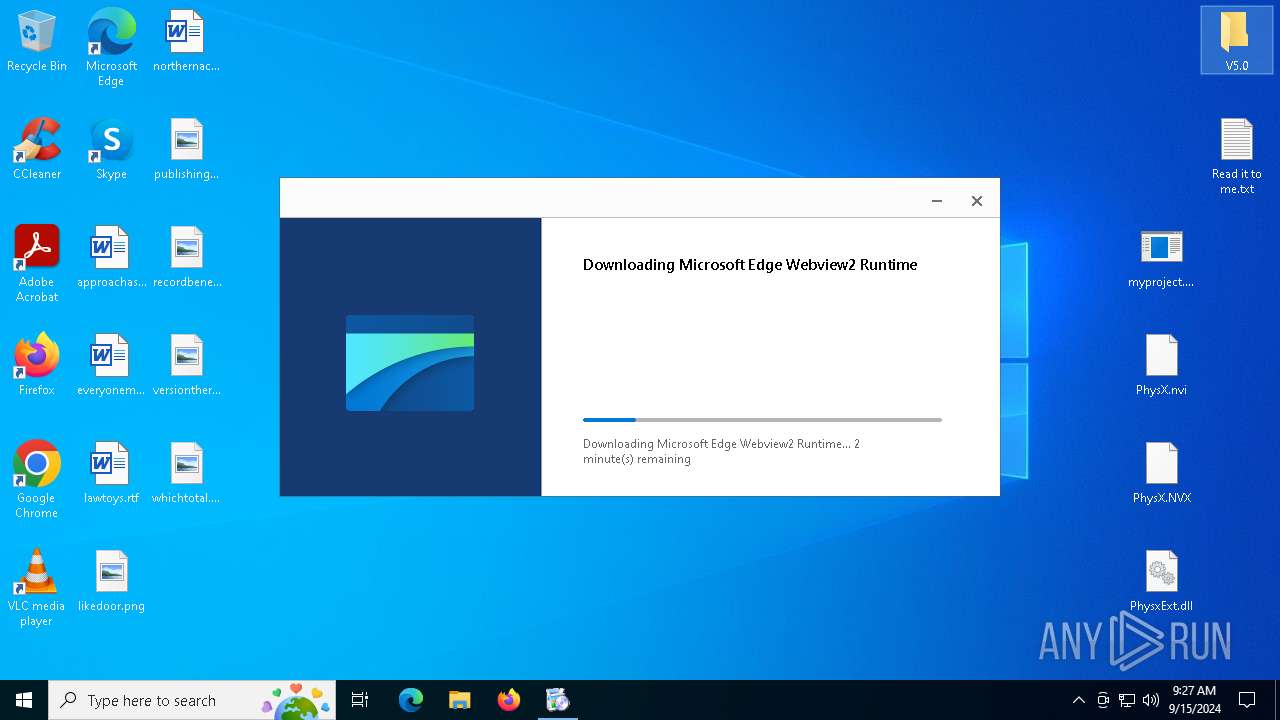
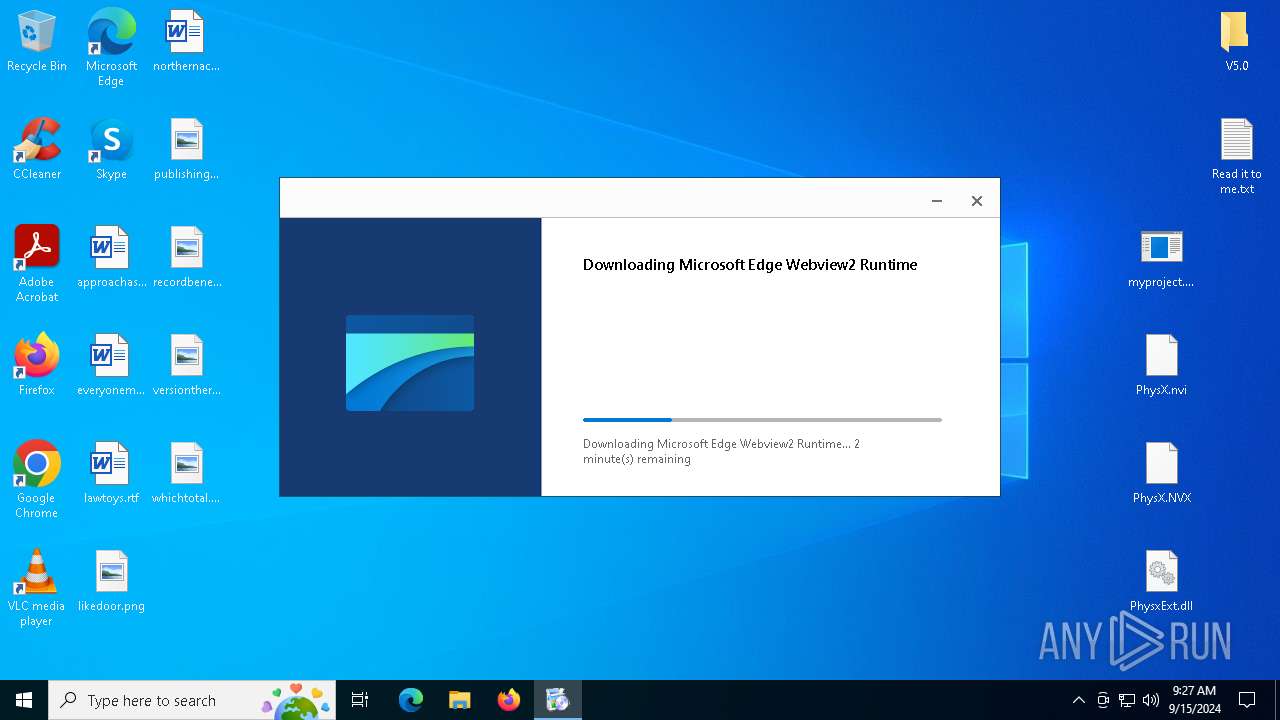
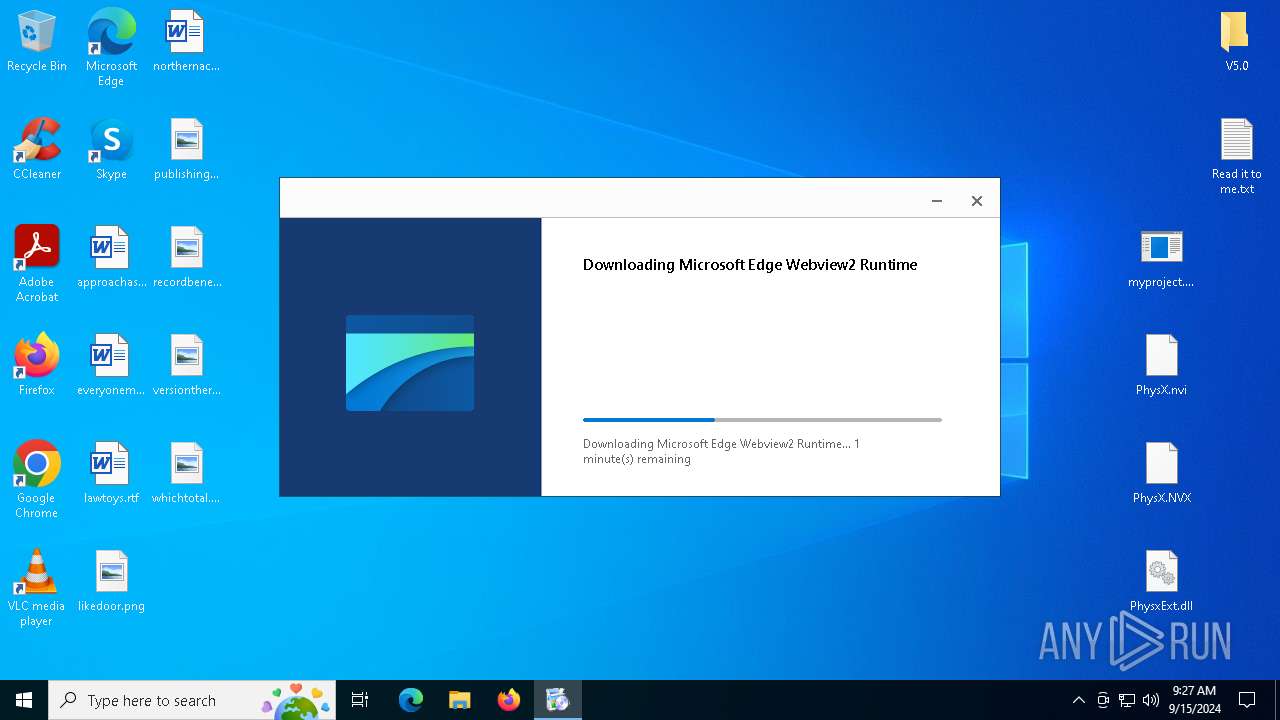
Executable content was dropped or overwritten
- myproject.exe (PID: 2524)
- MicrosoftEdgeWebview2Setup.exe (PID: 6928)
- MicrosoftEdgeUpdate.exe (PID: 6728)
- MicrosoftEdge_X64_128.0.2739.79.exe (PID: 4084)
- setup.exe (PID: 7788)
- myproject.exe (PID: 4024)
- msedgewebview2.exe (PID: 5548)
- driver1.exe (PID: 2728)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 6928)
- MicrosoftEdgeUpdate.exe (PID: 6728)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 6728)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1656)
- MicrosoftEdgeUpdate.exe (PID: 7464)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7408)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7180)
Potential Corporate Privacy Violation
- MicrosoftEdgeUpdate.exe (PID: 7296)
There is functionality for VM detection (VirtualBox)
- myproject.exe (PID: 2524)
- myproject.exe (PID: 4024)
There is functionality for VM detection (antiVM strings)
- myproject.exe (PID: 2524)
- myproject.exe (PID: 4024)
Found regular expressions for crypto-addresses (YARA)
- myproject.exe (PID: 2524)
- myproject.exe (PID: 4024)
There is functionality for VM detection (VMWare)
- myproject.exe (PID: 2524)
- myproject.exe (PID: 4024)
Checks Windows Trust Settings
- MicrosoftEdgeUpdate.exe (PID: 7296)
Application launched itself
- setup.exe (PID: 7788)
- MicrosoftEdgeUpdate.exe (PID: 7296)
- msedgewebview2.exe (PID: 3244)
- msedgewebview2.exe (PID: 7152)
- myproject.exe (PID: 2524)
- powershell.exe (PID: 7568)
- msedgewebview2.exe (PID: 6364)
- myproject.exe (PID: 2584)
- msedgewebview2.exe (PID: 5816)
Creates a software uninstall entry
- setup.exe (PID: 7788)
Searches for installed software
- setup.exe (PID: 7788)
- msedgewebview2.exe (PID: 7152)
- OOBE-Maintenance.exe (PID: 7184)
Reads the date of Windows installation
- myproject.exe (PID: 2524)
- myproject.exe (PID: 2584)
Starts POWERSHELL.EXE for commands execution
- myproject.exe (PID: 4024)
- powershell.exe (PID: 7568)
- driver1.exe (PID: 2728)
Script adds exclusion path to Windows Defender
- myproject.exe (PID: 4024)
- powershell.exe (PID: 7568)
- driver1.exe (PID: 2728)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 7568)
- powershell.exe (PID: 7256)
- OOBE-Maintenance.exe (PID: 7184)
Uses WMIC.EXE to obtain a list of video controllers
- myproject.exe (PID: 4024)
Read disk information to detect sandboxing environments
- myproject.exe (PID: 4024)
Get information on the list of running processes
- myproject.exe (PID: 4024)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 7212)
Uses WMIC.EXE to obtain Windows Installer data
- myproject.exe (PID: 4024)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 3896)
Connects to unusual port
- myproject.exe (PID: 4024)
- OpenWith.exe (PID: 5476)
- OOBE-Maintenance.exe (PID: 7184)
Adds/modifies Windows certificates
- myproject.exe (PID: 4024)
Contacting a server suspected of hosting an CnC
- OpenWith.exe (PID: 5476)
- OOBE-Maintenance.exe (PID: 7184)
Loads DLL from Mozilla Firefox
- OOBE-Maintenance.exe (PID: 7184)
The process checks if it is being run in the virtual environment
- OpenWith.exe (PID: 5476)
INFO
The process uses the downloaded file
- msedge.exe (PID: 1992)
- msedge.exe (PID: 6200)
- WinRAR.exe (PID: 6912)
- myproject.exe (PID: 2524)
- myproject.exe (PID: 2584)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6200)
Reads Environment values
- identity_helper.exe (PID: 7536)
- identity_helper.exe (PID: 1688)
- myproject.exe (PID: 2524)
- MicrosoftEdgeUpdate.exe (PID: 2492)
- identity_helper.exe (PID: 888)
- MicrosoftEdgeUpdate.exe (PID: 788)
- msedgewebview2.exe (PID: 3244)
- myproject.exe (PID: 4024)
- msedgewebview2.exe (PID: 7152)
- myproject.exe (PID: 2584)
- myproject.exe (PID: 7628)
Checks supported languages
- myproject.exe (PID: 2524)
- identity_helper.exe (PID: 1688)
- identity_helper.exe (PID: 7536)
- MicrosoftEdgeWebview2Setup.exe (PID: 6928)
- MicrosoftEdgeUpdate.exe (PID: 6728)
- MicrosoftEdgeUpdate.exe (PID: 7464)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7408)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1656)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7180)
- MicrosoftEdgeUpdate.exe (PID: 5220)
- MicrosoftEdgeUpdate.exe (PID: 2492)
- MicrosoftEdgeUpdate.exe (PID: 7296)
- identity_helper.exe (PID: 888)
- MicrosoftEdge_X64_128.0.2739.79.exe (PID: 4084)
- setup.exe (PID: 7788)
- setup.exe (PID: 7420)
- MicrosoftEdgeUpdate.exe (PID: 788)
- msedgewebview2.exe (PID: 3244)
- msedgewebview2.exe (PID: 3896)
- msedgewebview2.exe (PID: 7736)
- msedgewebview2.exe (PID: 7472)
- msedgewebview2.exe (PID: 1344)
- msedgewebview2.exe (PID: 2468)
- myproject.exe (PID: 4024)
- msedgewebview2.exe (PID: 7152)
- msedgewebview2.exe (PID: 208)
- msedgewebview2.exe (PID: 7600)
- msedgewebview2.exe (PID: 8028)
- msedgewebview2.exe (PID: 884)
- msedgewebview2.exe (PID: 7944)
- msedgewebview2.exe (PID: 4252)
- msedgewebview2.exe (PID: 7852)
- myproject.exe (PID: 2584)
- msedgewebview2.exe (PID: 6364)
- msedgewebview2.exe (PID: 4076)
- msedgewebview2.exe (PID: 7192)
- msedgewebview2.exe (PID: 7620)
- msedgewebview2.exe (PID: 2580)
- driver1.exe (PID: 2728)
- myproject.exe (PID: 7628)
- msedgewebview2.exe (PID: 5816)
- msedgewebview2.exe (PID: 7216)
- msedgewebview2.exe (PID: 5548)
- msedgewebview2.exe (PID: 3684)
- msedgewebview2.exe (PID: 6180)
- timbers.exe (PID: 6212)
- wmlaunch.exe (PID: 4392)
Reads the computer name
- identity_helper.exe (PID: 7536)
- identity_helper.exe (PID: 1688)
- myproject.exe (PID: 2524)
- MicrosoftEdgeUpdate.exe (PID: 6728)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1656)
- MicrosoftEdgeUpdate.exe (PID: 7464)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7408)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7180)
- MicrosoftEdgeUpdate.exe (PID: 2492)
- MicrosoftEdgeUpdate.exe (PID: 5220)
- MicrosoftEdgeUpdate.exe (PID: 7296)
- identity_helper.exe (PID: 888)
- MicrosoftEdge_X64_128.0.2739.79.exe (PID: 4084)
- setup.exe (PID: 7788)
- MicrosoftEdgeUpdate.exe (PID: 788)
- msedgewebview2.exe (PID: 3244)
- msedgewebview2.exe (PID: 3896)
- msedgewebview2.exe (PID: 7472)
- myproject.exe (PID: 4024)
- msedgewebview2.exe (PID: 7152)
- msedgewebview2.exe (PID: 8028)
- msedgewebview2.exe (PID: 7600)
- myproject.exe (PID: 2584)
- msedgewebview2.exe (PID: 6364)
- msedgewebview2.exe (PID: 5816)
- myproject.exe (PID: 7628)
- driver1.exe (PID: 2728)
- msedgewebview2.exe (PID: 3684)
Create files in a temporary directory
- myproject.exe (PID: 2524)
- MicrosoftEdgeWebview2Setup.exe (PID: 6928)
- MicrosoftEdgeUpdate.exe (PID: 6728)
- MicrosoftEdgeUpdate.exe (PID: 7296)
- msedgewebview2.exe (PID: 3244)
- msedgewebview2.exe (PID: 7152)
Reads the software policy settings
- myproject.exe (PID: 2524)
- MicrosoftEdgeUpdate.exe (PID: 2492)
- MicrosoftEdgeUpdate.exe (PID: 7296)
- HelpPane.exe (PID: 5712)
- MicrosoftEdgeUpdate.exe (PID: 788)
- myproject.exe (PID: 4024)
- driver1.exe (PID: 2728)
Application launched itself
- msedge.exe (PID: 6200)
- msedge.exe (PID: 7020)
- msedge.exe (PID: 3316)
Reads the machine GUID from the registry
- myproject.exe (PID: 2524)
- HelpPane.exe (PID: 5712)
- MicrosoftEdgeUpdate.exe (PID: 7296)
- msedgewebview2.exe (PID: 3244)
- msedgewebview2.exe (PID: 7152)
- myproject.exe (PID: 4024)
- driver1.exe (PID: 2728)
- msedgewebview2.exe (PID: 3684)
- wmlaunch.exe (PID: 4392)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6912)
- msedge.exe (PID: 7756)
Creates files or folders in the user directory
- MicrosoftEdgeUpdate.exe (PID: 6728)
- MicrosoftEdgeUpdate.exe (PID: 7296)
- MicrosoftEdge_X64_128.0.2739.79.exe (PID: 4084)
- setup.exe (PID: 7420)
- setup.exe (PID: 7788)
- msedgewebview2.exe (PID: 3244)
- msedgewebview2.exe (PID: 7736)
- msedgewebview2.exe (PID: 7472)
- msedgewebview2.exe (PID: 7152)
- msedgewebview2.exe (PID: 8028)
- msedgewebview2.exe (PID: 3684)
Checks proxy server information
- MicrosoftEdgeUpdate.exe (PID: 2492)
- MicrosoftEdgeUpdate.exe (PID: 7296)
- MicrosoftEdgeUpdate.exe (PID: 788)
- msedgewebview2.exe (PID: 3244)
- msedgewebview2.exe (PID: 7152)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 6728)
- setup.exe (PID: 7788)
- msedgewebview2.exe (PID: 3244)
- msedgewebview2.exe (PID: 2468)
- myproject.exe (PID: 2524)
- msedgewebview2.exe (PID: 7152)
- msedgewebview2.exe (PID: 884)
- msedgewebview2.exe (PID: 7192)
- myproject.exe (PID: 2584)
- msedgewebview2.exe (PID: 2580)
Reads security settings of Internet Explorer
- HelpPane.exe (PID: 5712)
- notepad.exe (PID: 5796)
- WMIC.exe (PID: 7212)
- WMIC.exe (PID: 3896)
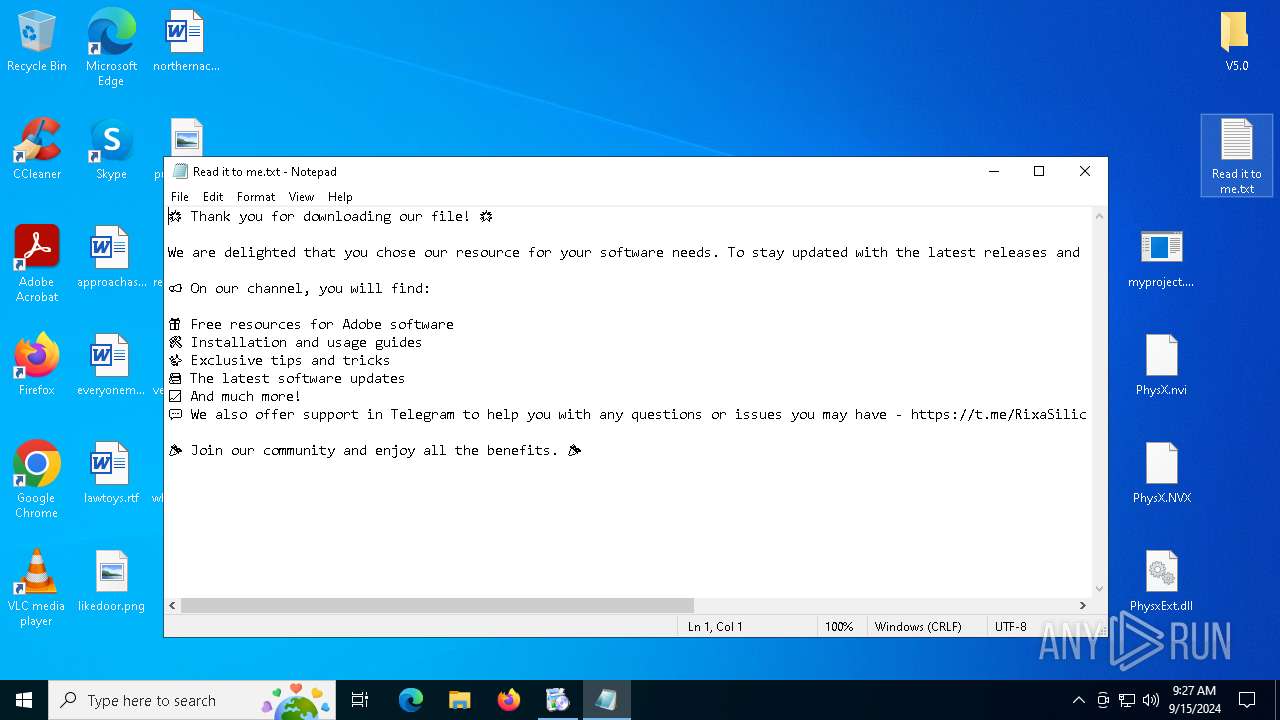
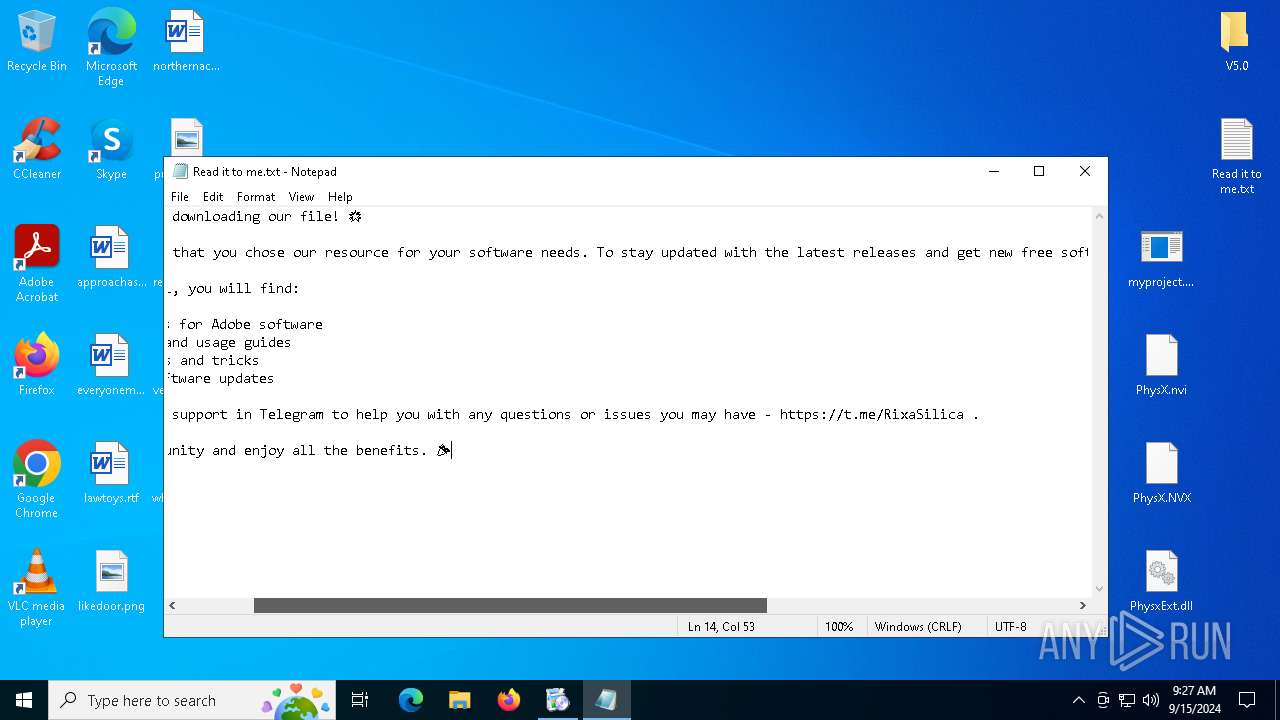
Manual execution by a user
- notepad.exe (PID: 5796)
- myproject.exe (PID: 2584)
Sends debugging messages
- msedgewebview2.exe (PID: 3244)
- msedgewebview2.exe (PID: 7152)
- msedgewebview2.exe (PID: 6364)
- msedgewebview2.exe (PID: 4076)
- msedgewebview2.exe (PID: 5816)
- msedgewebview2.exe (PID: 7620)
- OOBE-Maintenance.exe (PID: 7184)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7568)
- powershell.exe (PID: 2112)
- powershell.exe (PID: 1932)
- powershell.exe (PID: 7608)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7280)
- powershell.exe (PID: 1492)
- powershell.exe (PID: 7256)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 6868)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7568)
- powershell.exe (PID: 2112)
- powershell.exe (PID: 1932)
- powershell.exe (PID: 7608)
- powershell.exe (PID: 7256)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7280)
- powershell.exe (PID: 1492)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 6868)
Creates files in the program directory
- myproject.exe (PID: 4024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
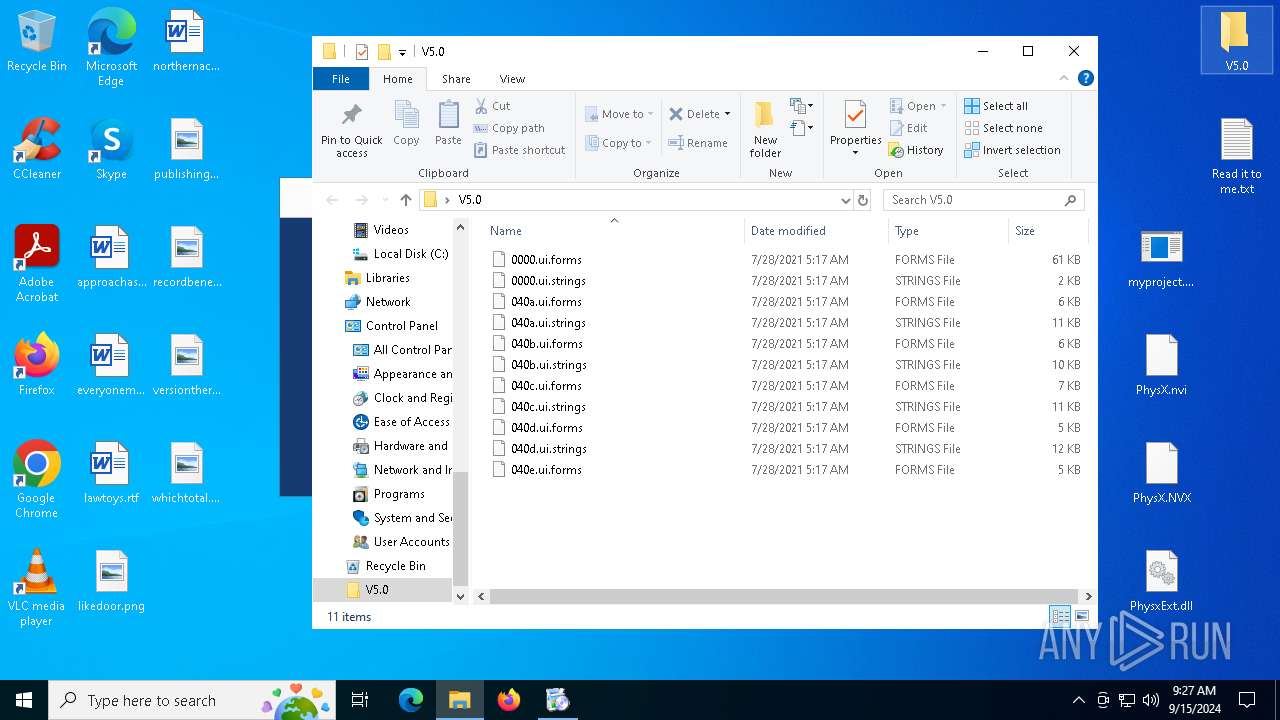
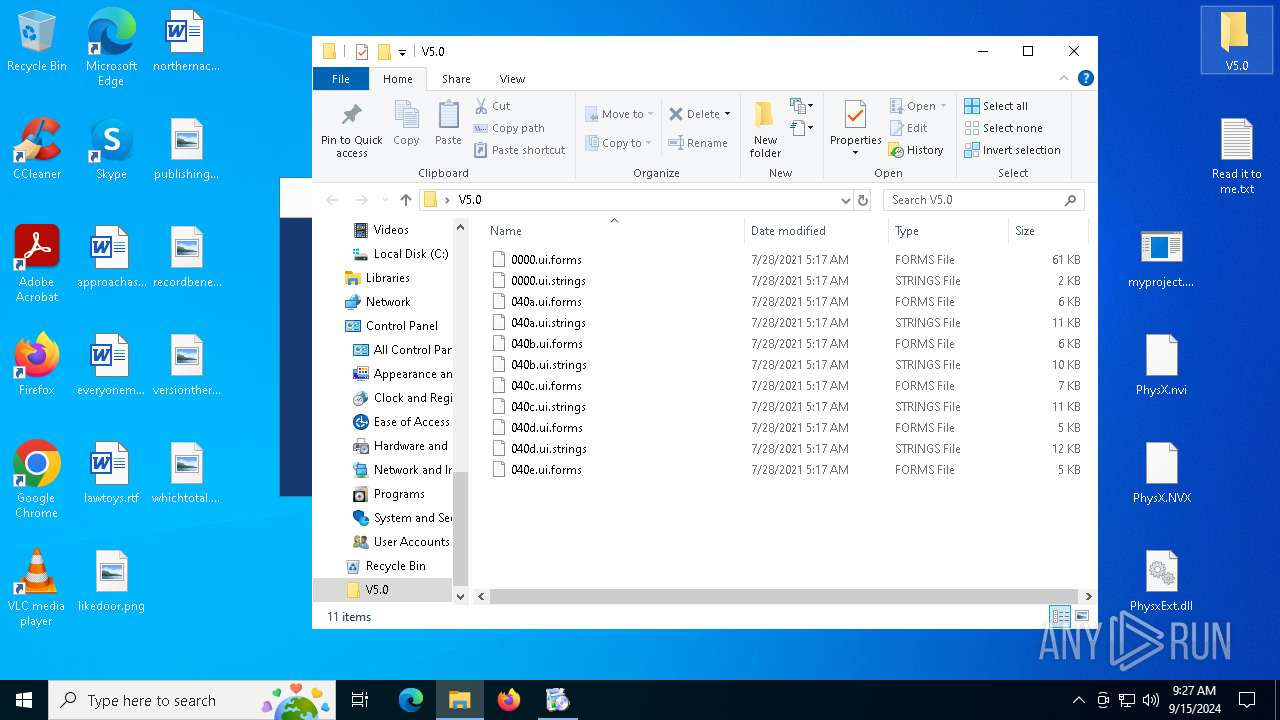
Total processes
312
Monitored processes
171
Malicious processes
18
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\128.0.2739.79\msedgewebview2.exe --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Roaming\myproject.exe\EBWebView /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Roaming\myproject.exe\EBWebView\Crashpad --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=128.0.6613.138 --annotation=exe=C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\128.0.2739.79\msedgewebview2.exe --annotation=plat=Win64 "--annotation=prod=Edge WebView2" --annotation=ver=128.0.2739.79 --initial-client-data=0x188,0x18c,0x190,0x164,0x198,0x7fffcf589fd8,0x7fffcf589fe4,0x7fffcf589ff0 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\128.0.2739.79\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Version: 128.0.2739.79 Modules
| |||||||||||||||
| 488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2404 --field-trial-handle=2412,i,10406713970711405413,5625844851670257807,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 788 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /ping PD94bWwgdmVyc2lvbj0iMS4wIiBlbmNvZGluZz0iVVRGLTgiPz48cmVxdWVzdCBwcm90b2NvbD0iMy4wIiB1cGRhdGVyPSJPbWFoYSIgdXBkYXRlcnZlcnNpb249IjEuMy4xOTUuMTkiIHNoZWxsX3ZlcnNpb249IjEuMy4xOTUuMTkiIGlzbWFjaGluZT0iMCIgc2Vzc2lvbmlkPSJ7MTNEQzYyMTAtODYwQy00MDgyLUEwQ0QtNEVBQUJEQkMwRTY1fSIgdXNlcmlkPSJ7MkQ5N0M2MzYtOTc3Ni00NjYzLTk4MTktMjFBQjEzMzk2MTE2fSIgaW5zdGFsbHNvdXJjZT0idGFnZ2VkbWkiIHJlcXVlc3RpZD0iezIwMjdBRjQ3LTI3RjYtNEFBMC04NzIxLUU0NTREQzA0OTI4M30iIGRlZHVwPSJjciIgZG9tYWluam9pbmVkPSIwIj48aHcgbG9naWNhbF9jcHVzPSI0IiBwaHlzbWVtb3J5PSI0IiBkaXNrX3R5cGU9IjIiIHNzZT0iMSIgc3NlMj0iMSIgc3NlMz0iMSIgc3NzZTM9IjEiIHNzZTQxPSIxIiBzc2U0Mj0iMSIgYXZ4PSIxIi8-PG9zIHBsYXRmb3JtPSJ3aW4iIHZlcnNpb249IjEwLjAuMTkwNDUuNDA0NiIgc3A9IiIgYXJjaD0ieDY0IiBwcm9kdWN0X3R5cGU9IjQ4IiBpc193aXA9IjAiIGlzX2luX2xvY2tkb3duX21vZGU9IjAiLz48b2VtIHByb2R1Y3RfbWFudWZhY3R1cmVyPSJERUxMIiBwcm9kdWN0X25hbWU9IkRFTEwiLz48ZXhwIGV0YWc9IiZxdW90O3I0NTJ0MStrMlRncS9IWHpqdkZOQlJob3BCV1I5c2JqWHhxZVVESDl1WDA9JnF1b3Q7Ii8-PGFwcCBhcHBpZD0ie0YzMDE3MjI2LUZFMkEtNDI5NS04QkRGLTAwQzNBOUE3RTRDNX0iIHZlcnNpb249IiIgbmV4dHZlcnNpb249IjEyOC4wLjI3MzkuNzkiIGxhbmc9ImVuIiBicmFuZD0iIiBjbGllbnQ9IiIgZXhwZXJpbWVudHM9ImNvbnNlbnQ9ZmFsc2UiIGluc3RhbGxhZ2U9Ii0xIiBpbnN0YWxsZGF0ZT0iLTEiPjx1cGRhdGVjaGVjay8-PGV2ZW50IGV2ZW50dHlwZT0iOSIgZXZlbnRyZXN1bHQ9IjEiIGVycm9yY29kZT0iMCIgZXh0cmFjb2RlMT0iMCIgc3lzdGVtX3VwdGltZV90aWNrcz0iMTI0OTk4NjYyMDMiIGRvbmVfYmVmb3JlX29vYmVfY29tcGxldGU9IjAiLz48ZXZlbnQgZXZlbnR0eXBlPSI1IiBldmVudHJlc3VsdD0iMSIgZXJyb3Jjb2RlPSIwIiBleHRyYWNvZGUxPSIwIiBzeXN0ZW1fdXB0aW1lX3RpY2tzPSIxMjUwMDAyMjQzMCIgZG9uZV9iZWZvcmVfb29iZV9jb21wbGV0ZT0iMCIvPjxldmVudCBldmVudHR5cGU9IjEiIGV2ZW50cmVzdWx0PSIxIiBlcnJvcmNvZGU9IjAiIGV4dHJhY29kZTE9IjAiIHN5c3RlbV91cHRpbWVfdGlja3M9IjEzNTAwMDM2MTU1IiBzb3VyY2VfdXJsX2luZGV4PSIwIiBkb25lX2JlZm9yZV9vb2JlX2NvbXBsZXRlPSIwIiBkb3dubG9hZGVyPSJ3aW5odHRwIiB1cmw9Imh0dHA6Ly9tc2VkZ2UuZi50bHUuZGwuZGVsaXZlcnkubXAubWljcm9zb2Z0LmNvbS9maWxlc3RyZWFtaW5nc2VydmljZS9maWxlcy8zYzBkZTJiZi02NWJmLTQ5ZDUtYWNiMS0zNzliYTgyMTVjNjA_UDE9MTcyNjk5NzIxMiZhbXA7UDI9NDA0JmFtcDtQMz0yJmFtcDtQND1OMVRZQzdCZmxleiUyYlo3c0lCdUJ1SnRWcTI2cXRaVUU5NDhHT3FrQkZrZkFXOEZjQ3oyZnVITVVSS2NxZWZlNmEzV3RmdSUyZldGSHMlMmJxa3htalBocUZvUSUzZCUzZCIgc2VydmVyX2lwX2hpbnQ9IjIzLjQ4LjIzLjciIGNkbl9jaWQ9IjIiIGNkbl9jY2M9IkRFIiBjZG5fbXNlZGdlX3JlZj0iIiBjZG5fYXp1cmVfcmVmX29yaWdpbl9zaGllbGQ9IiIgY2RuX2NhY2hlPSIiIGNkbl9wM3A9IiIgZG93bmxvYWRlZD0iMTczOTA5NTg0IiB0b3RhbD0iMTczOTA5NTg0IiBkb3dubG9hZF90aW1lX21zPSI5NjE4OSIvPjxldmVudCBldmVudHR5cGU9IjEiIGV2ZW50cmVzdWx0PSIxIiBlcnJvcmNvZGU9IjAiIGV4dHJhY29kZTE9IjAiIHN5c3RlbV91cHRpbWVfdGlja3M9IjEzNTAwMzQ5MjUxIiBzb3VyY2VfdXJsX2luZGV4PSIwIiBkb25lX2JlZm9yZV9vb2JlX2NvbXBsZXRlPSIwIi8-PGV2ZW50IGV2ZW50dHlwZT0iNiIgZXZlbnRyZXN1bHQ9IjEiIGVycm9yY29kZT0iMCIgZXh0cmFjb2RlMT0iMCIgc3lzdGVtX3VwdGltZV90aWNrcz0iMTM1MjA1MDYwOTIiIGRvbmVfYmVmb3JlX29vYmVfY29tcGxldGU9IjAiLz48ZXZlbnQgZXZlbnR0eXBlPSIyIiBldmVudHJlc3VsdD0iMSIgZXJyb3Jjb2RlPSIwIiBleHRyYWNvZGUxPSIxOTY2MDkiIHN5c3RlbV91cHRpbWVfdGlja3M9IjEzNzQ5NjcyNjg0IiBzb3VyY2VfdXJsX2luZGV4PSIwIiBkb25lX2JlZm9yZV9vb2JlX2NvbXBsZXRlPSIwIiB1cGRhdGVfY2hlY2tfdGltZV9tcz0iNzM1IiBkb3dubG9hZF90aW1lX21zPSIxMDAwMTciIGRvd25sb2FkZWQ9IjE3MzkwOTU4NCIgdG90YWw9IjE3MzkwOTU4NCIgcGFja2FnZV9jYWNoZV9yZXN1bHQ9IjAiIGluc3RhbGxfdGltZV9tcz0iMjI5MDEiLz48L2FwcD48L3JlcXVlc3Q- | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.195.19 Modules
| |||||||||||||||
| 884 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\128.0.2739.79\msedgewebview2.exe" --type=renderer --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Roaming\myproject.exe\EBWebView" --webview-exe-name=myproject.exe --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=1 --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --js-flags="--harmony-weak-refs-with-cleanup-some --expose-gc --ms-user-locale=" --field-trial-handle=3488,i,15068019151408855788,4671672986563844915,262144 --enable-features=MojoIpcz --disable-features=msSmartScreenProtection --variations-seed-version --mojo-platform-channel-handle=3500 /prefetch:1 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\128.0.2739.79\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Version: 128.0.2739.79 Modules
| |||||||||||||||
| 888 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3416 --field-trial-handle=2332,i,6936114891680205489,3336606786544204122,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1124 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=4052 --field-trial-handle=2332,i,6936114891680205489,3336606786544204122,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1344 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\128.0.2739.79\msedgewebview2.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Roaming\myproject.exe\EBWebView" --webview-exe-name=myproject.exe --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=1 --field-trial-handle=2396,i,11183153064928938885,6983776179019801365,262144 --enable-features=MojoIpcz --disable-features=msSmartScreenProtection --variations-seed-version --mojo-platform-channel-handle=2412 /prefetch:8 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\128.0.2739.79\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Exit code: 0 Version: 128.0.2739.79 Modules
| |||||||||||||||
| 1480 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2600 --field-trial-handle=2412,i,10406713970711405413,5625844851670257807,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1492 | powershell -WindowStyle Hidden -Command "Add-MpPreference -ExclusionPath 'C:\ProgramData'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | driver1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
97 626
Read events
93 820
Write events
3 734
Delete events
72
Modification events
| (PID) Process: | (6200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6200) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DB706555BB802F00 | |||
| (PID) Process: | (6200) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 34EE6D55BB802F00 | |||
| (PID) Process: | (6200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393830 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {81A89EC1-93A4-49F4-8F64-70DF1363FEE4} | |||
| (PID) Process: | (6200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393830 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {31BF4069-5CE8-4052-9619-6B12699477C0} | |||
| (PID) Process: | (6200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (6200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
220
Suspicious files
642
Text files
325
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF12aaa0.TMP | — | |
MD5:— | SHA256:— | |||
| 6200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF12aaa0.TMP | — | |
MD5:— | SHA256:— | |||
| 6200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF12aacf.TMP | — | |
MD5:— | SHA256:— | |||
| 6200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF12aacf.TMP | — | |
MD5:— | SHA256:— | |||
| 6200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF12aacf.TMP | — | |
MD5:— | SHA256:— | |||
| 6200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
102
DNS requests
101
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2248 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6112 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6236 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6236 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7296 | MicrosoftEdgeUpdate.exe | GET | 200 | 23.48.23.7:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3c0de2bf-65bf-49d5-acb1-379ba8215c60?P1=1726997212&P2=404&P3=2&P4=N1TYC7Bflez%2bZ7sIBuBuJtVq26qtZUE948GOqkBFkfAW8FcCz2fuHMURKcqefe6a3Wtfu%2fWFHs%2bqkxmjPhqFoQ%3d%3d | unknown | — | — | whitelisted |
6660 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726534721&P2=404&P3=2&P4=lm1pSOrU%2fgpki%2filTgbvgFZYNZB%2b8Qi4SL4ydDIdyhrDA0j7Y%2fvJUpdg7YdD4KRDRFlo%2fHMsaGl%2bjbdb56OZlw%3d%3d | unknown | — | — | whitelisted |
6660 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726534721&P2=404&P3=2&P4=lm1pSOrU%2fgpki%2filTgbvgFZYNZB%2b8Qi4SL4ydDIdyhrDA0j7Y%2fvJUpdg7YdD4KRDRFlo%2fHMsaGl%2bjbdb56OZlw%3d%3d | unknown | — | — | whitelisted |
6660 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726534721&P2=404&P3=2&P4=lm1pSOrU%2fgpki%2filTgbvgFZYNZB%2b8Qi4SL4ydDIdyhrDA0j7Y%2fvJUpdg7YdD4KRDRFlo%2fHMsaGl%2bjbdb56OZlw%3d%3d | unknown | — | — | whitelisted |
6660 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726534721&P2=404&P3=2&P4=lm1pSOrU%2fgpki%2filTgbvgFZYNZB%2b8Qi4SL4ydDIdyhrDA0j7Y%2fvJUpdg7YdD4KRDRFlo%2fHMsaGl%2bjbdb56OZlw%3d%3d | unknown | — | — | whitelisted |
6660 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726534721&P2=404&P3=2&P4=lm1pSOrU%2fgpki%2filTgbvgFZYNZB%2b8Qi4SL4ydDIdyhrDA0j7Y%2fvJUpdg7YdD4KRDRFlo%2fHMsaGl%2bjbdb56OZlw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7084 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2248 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1480 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6200 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1480 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | shared |
1480 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1480 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1480 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| shared |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
objects.githubusercontent.com |
| shared |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7296 | MicrosoftEdgeUpdate.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
4024 | myproject.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
4024 | myproject.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 23 |
4024 | myproject.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
4024 | myproject.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host RAR Request |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7184 | OOBE-Maintenance.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
7184 | OOBE-Maintenance.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
5 ETPRO signatures available at the full report
Process | Message |
|---|---|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Roaming directory exists )
|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Roaming\myproject.exe\EBWebView directory exists )
|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Roaming\myproject.exe\EBWebView directory exists )
|
msedgewebview2.exe | [0915/093014.096:ERROR:exception_handler_server.cc(529)] ConnectNamedPipe: The pipe is being closed. (0xE8)
|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Roaming\myproject.exe\EBWebView directory exists )
|
msedgewebview2.exe | [0915/093014.922:ERROR:exception_handler_server.cc(529)] ConnectNamedPipe: The pipe is being closed. (0xE8)
|
OOBE-Maintenance.exe | [thresholding] image = 000001D3C0AF5D80 , (0 , 863) (0 , 432)
|
OOBE-Maintenance.exe | [thresholding] image = 000001D3C0AF5D80 , (0 , 783) (0 , 392)
|