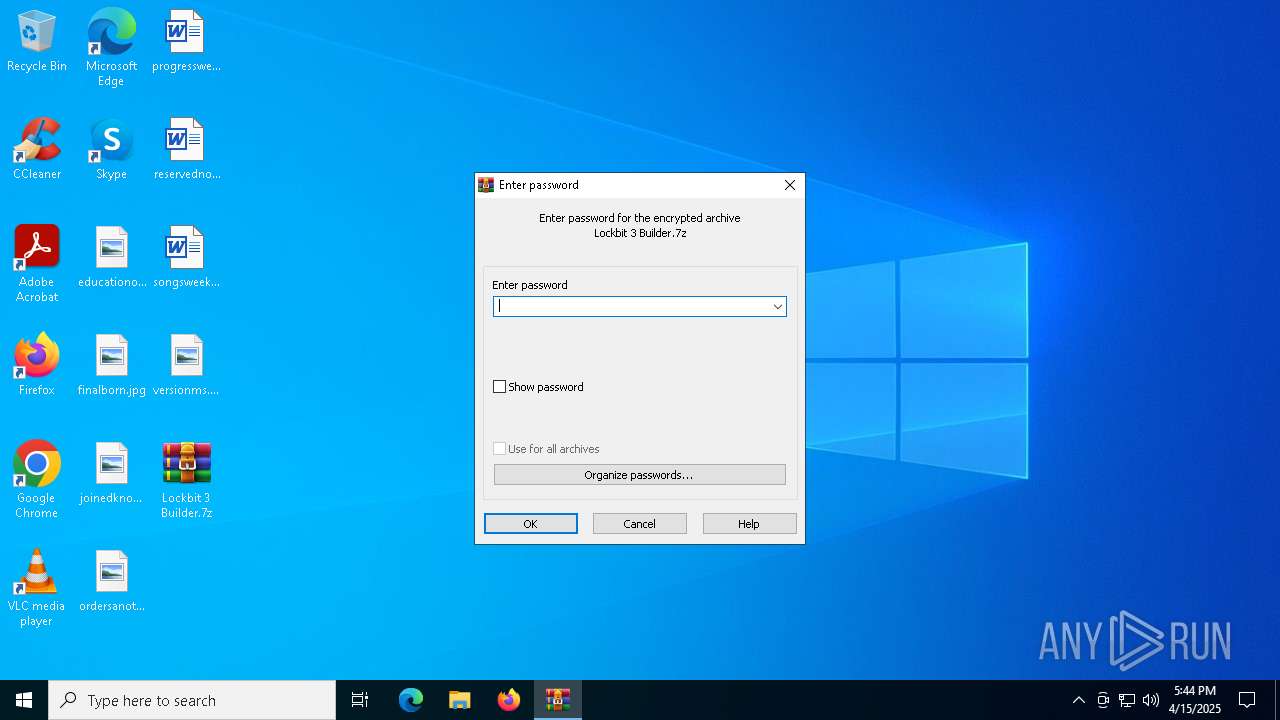
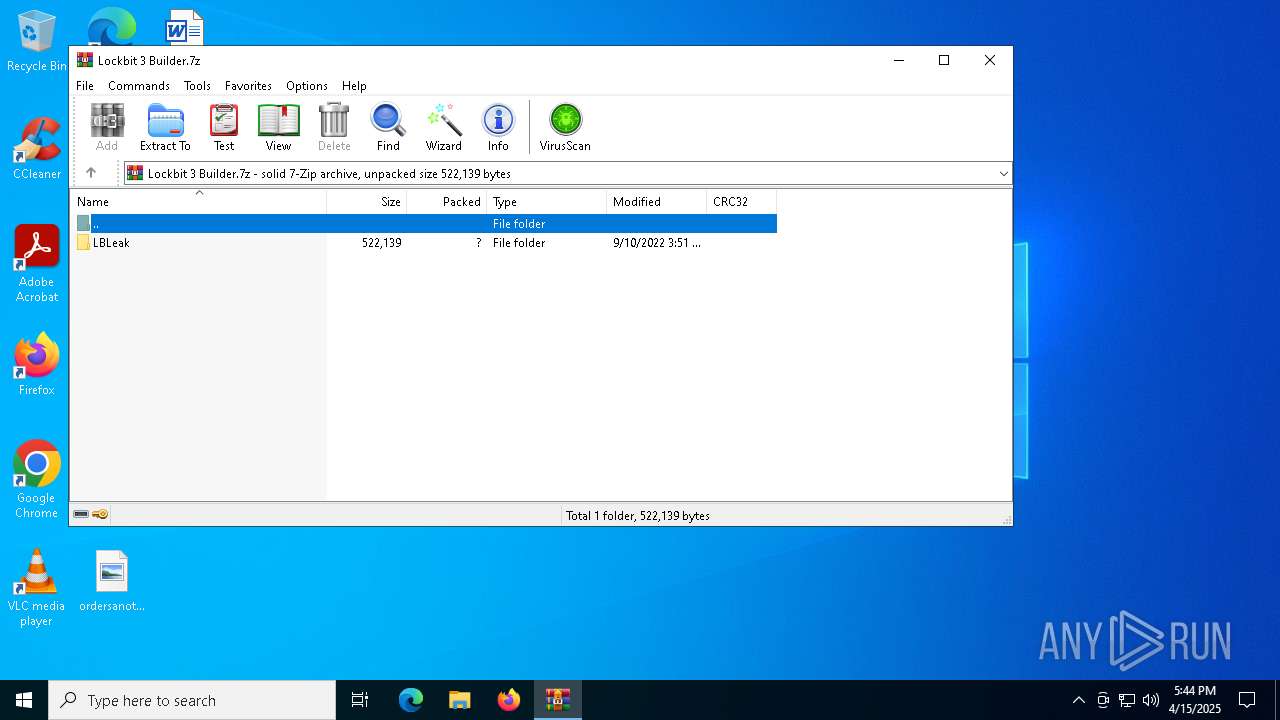
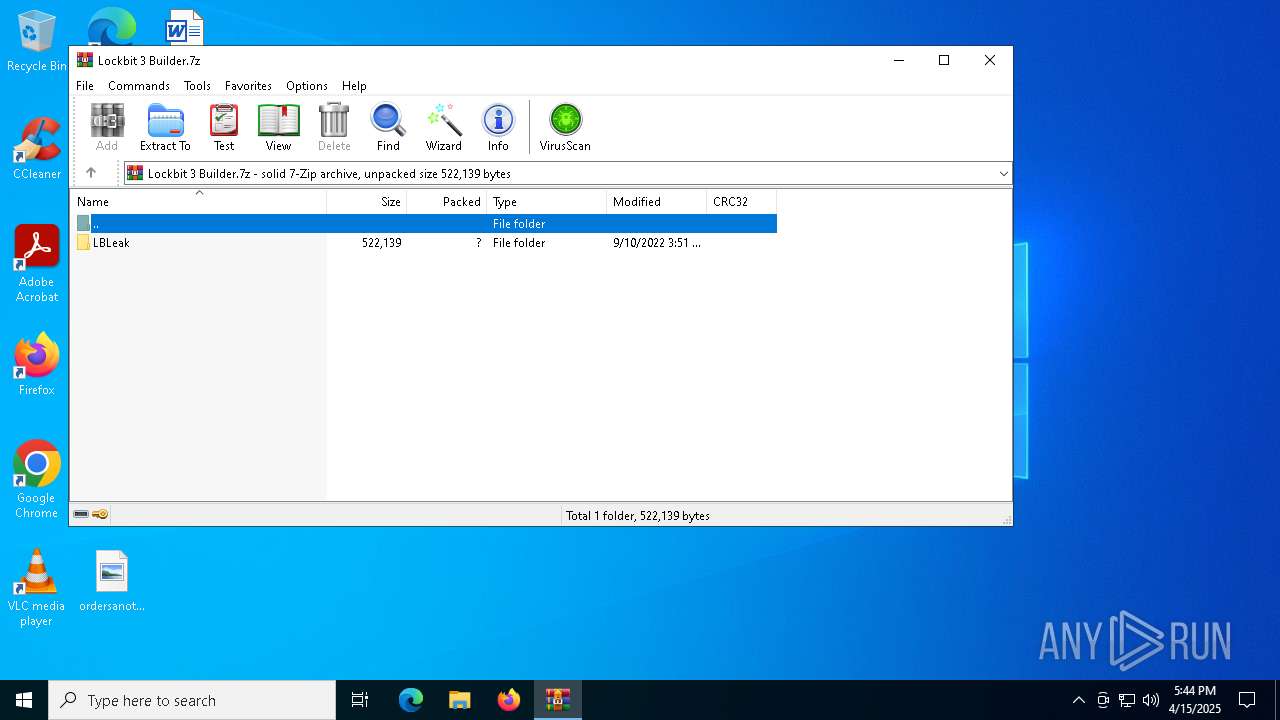
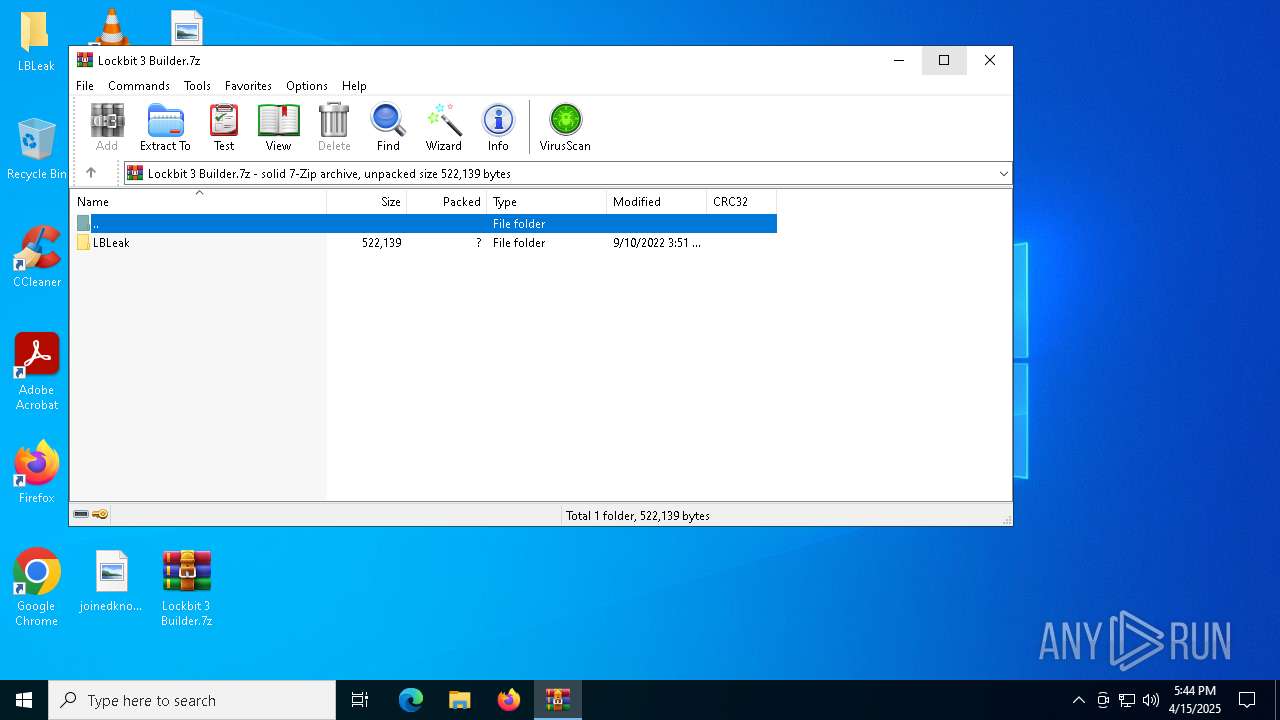
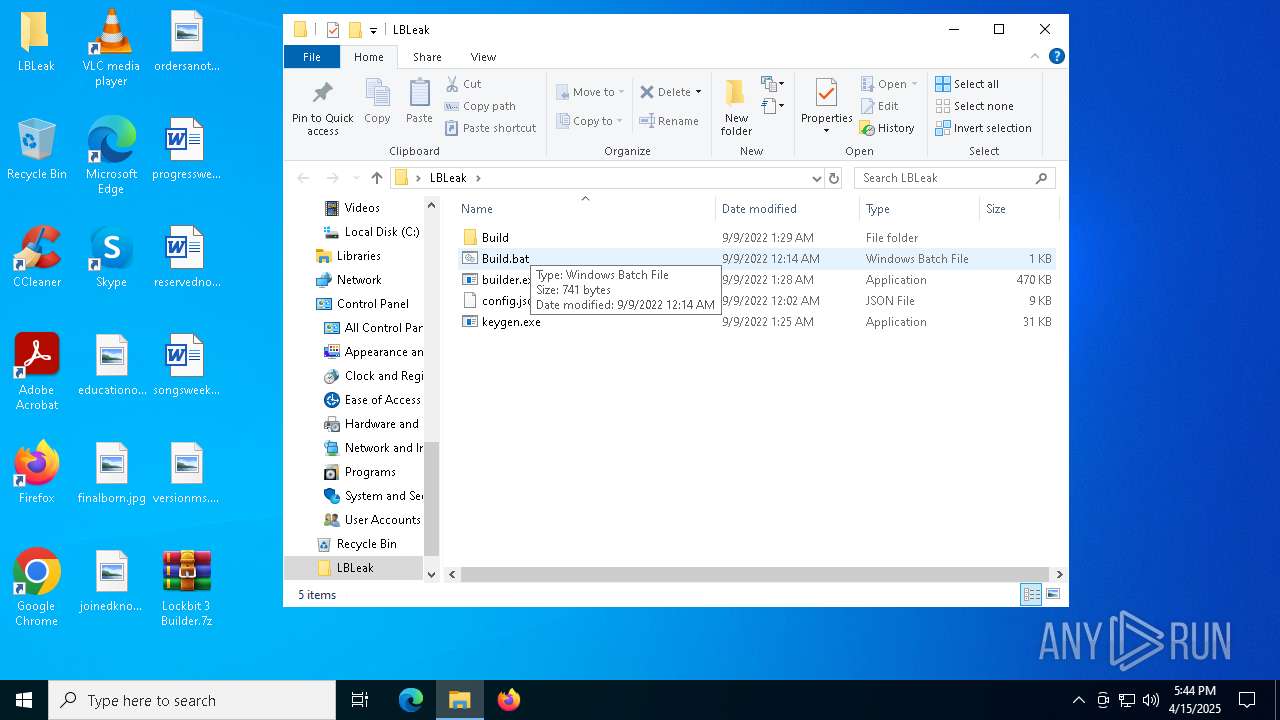
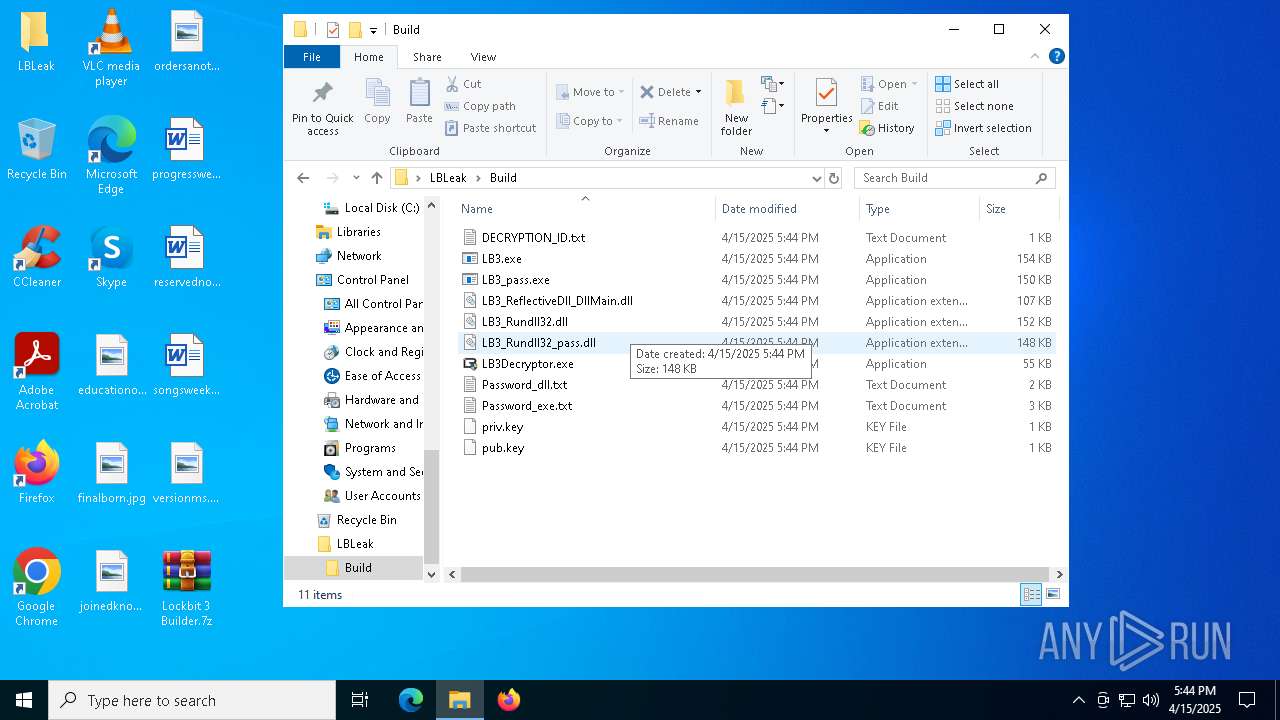
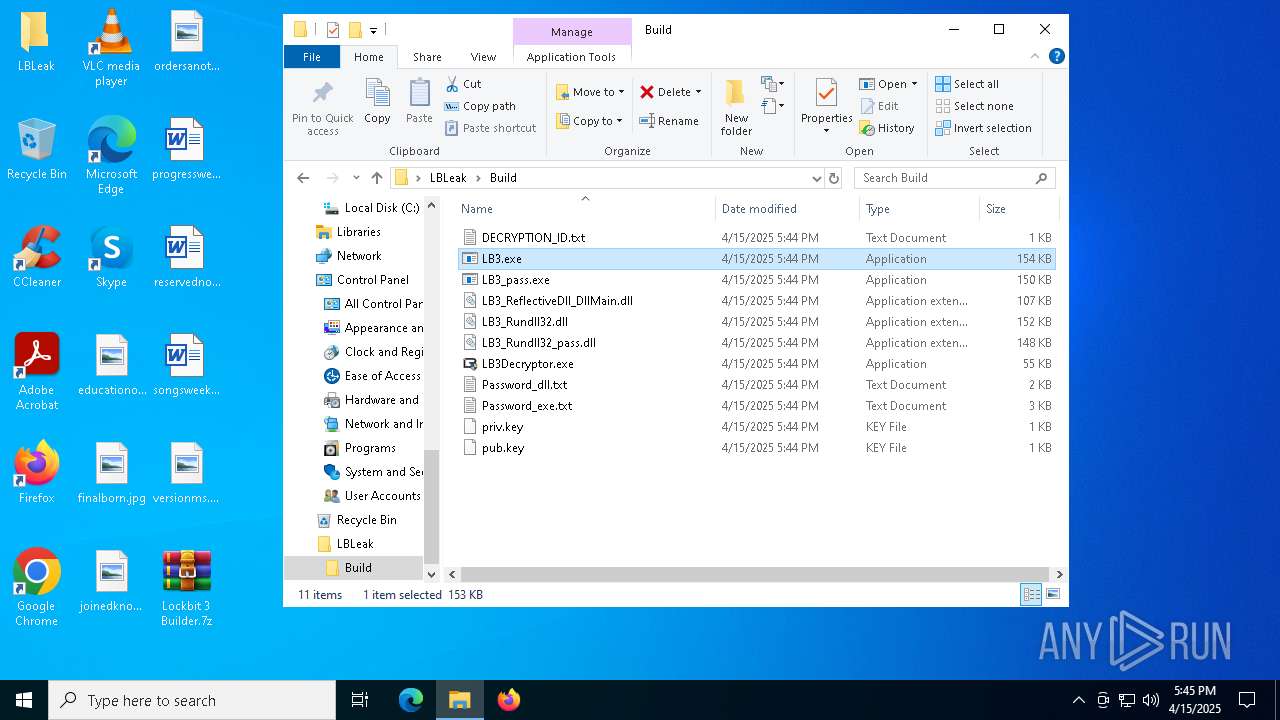
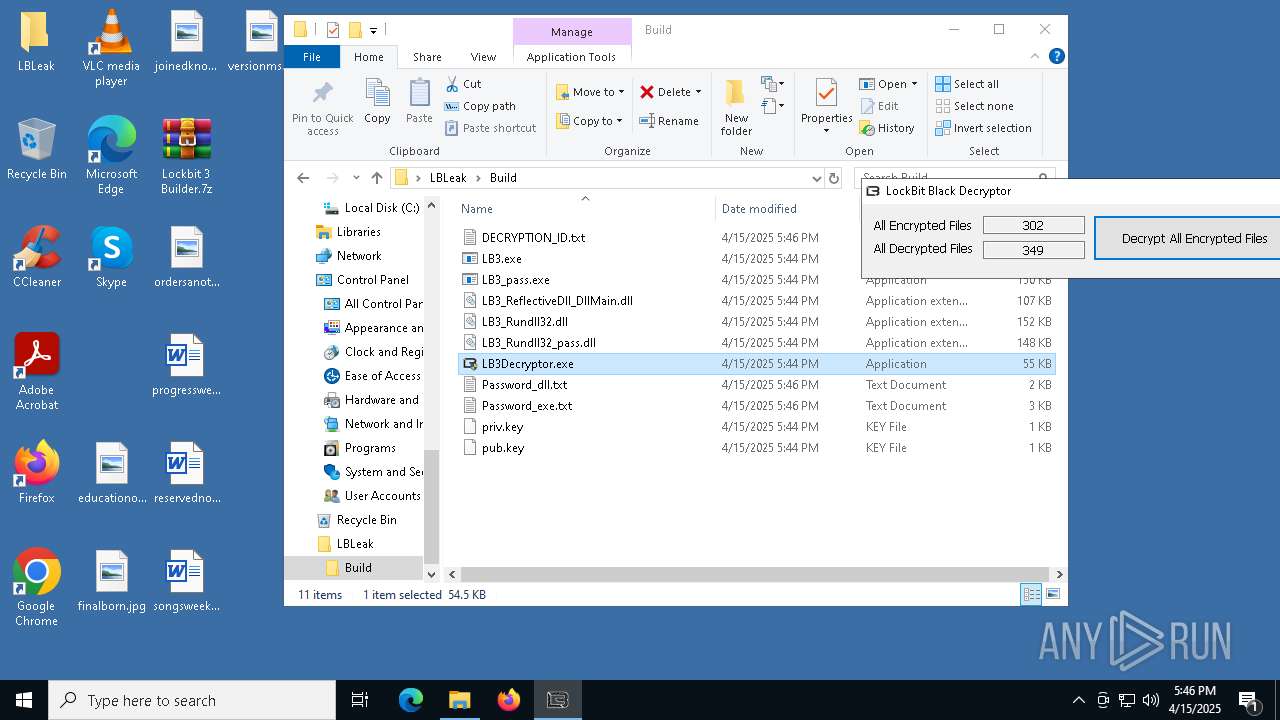
| File name: | Lockbit 3 Builder.7z |
| Full analysis: | https://app.any.run/tasks/c80717d7-f33d-41b3-b182-840b5896c0b2 |
| Verdict: | Malicious activity |
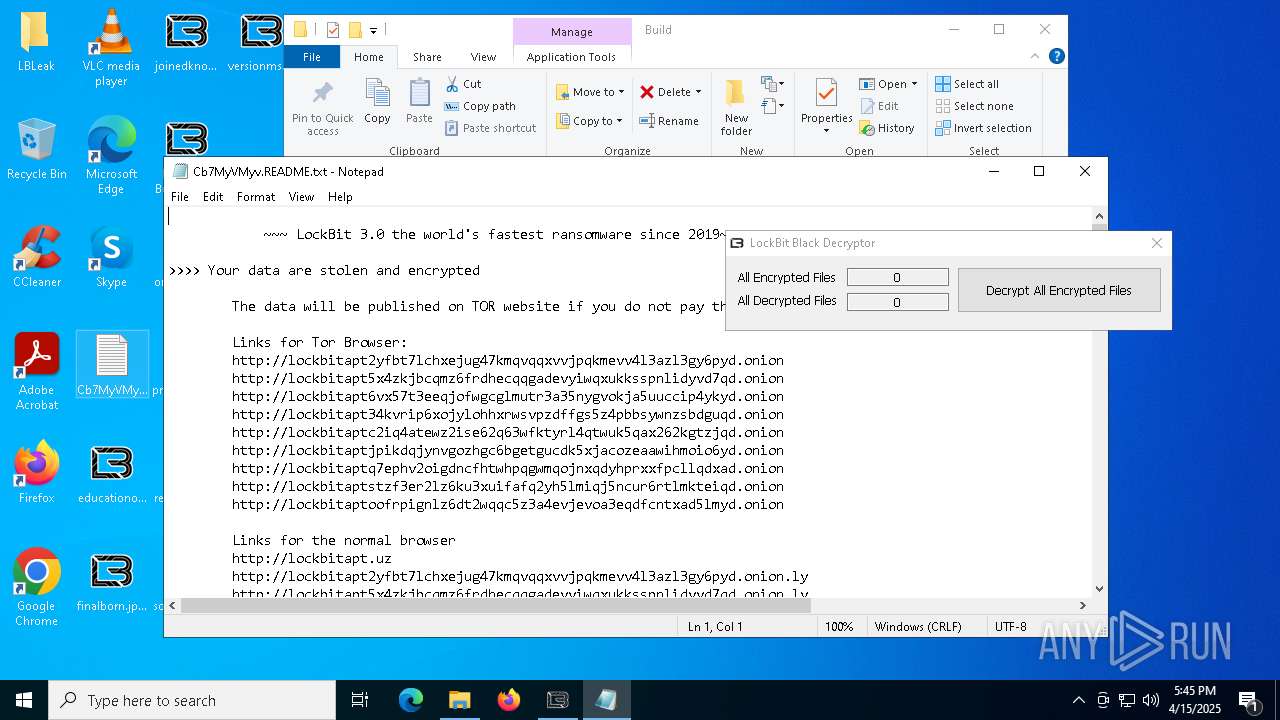
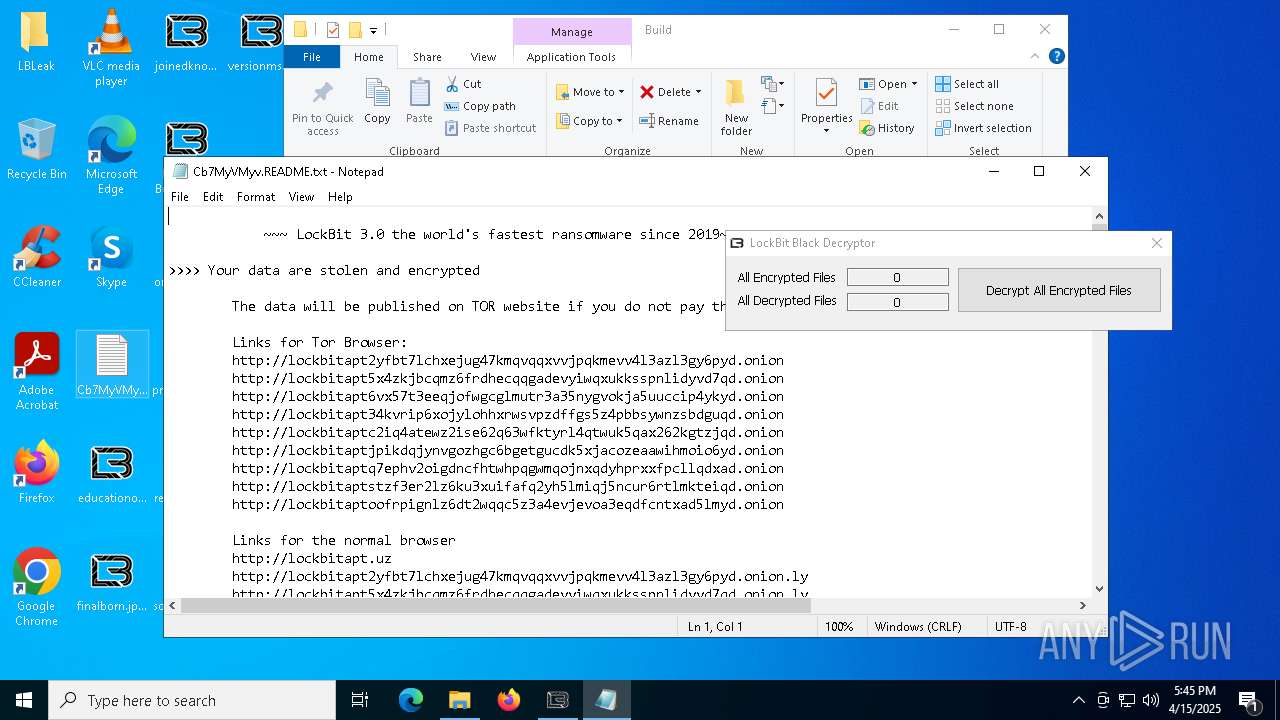
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | April 15, 2025, 17:44:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | C9C2F3805F0012628E9D62E8F75AF4DD |
| SHA1: | B6269B1FC8813B93C11EC6066DC33D9F99F2E431 |
| SHA256: | B2C3BEDA4B000A3D9AF0A457D6D942EC81696F3ED485F7CF723B18008A5F3D10 |
| SSDEEP: | 3072:pYWJsCuSlRODbWhyyZZsZ77n4s31uZzd2ppyMPOLOcrgCz:pbuSlicZyx4W1uLYpyMPOLjhz |
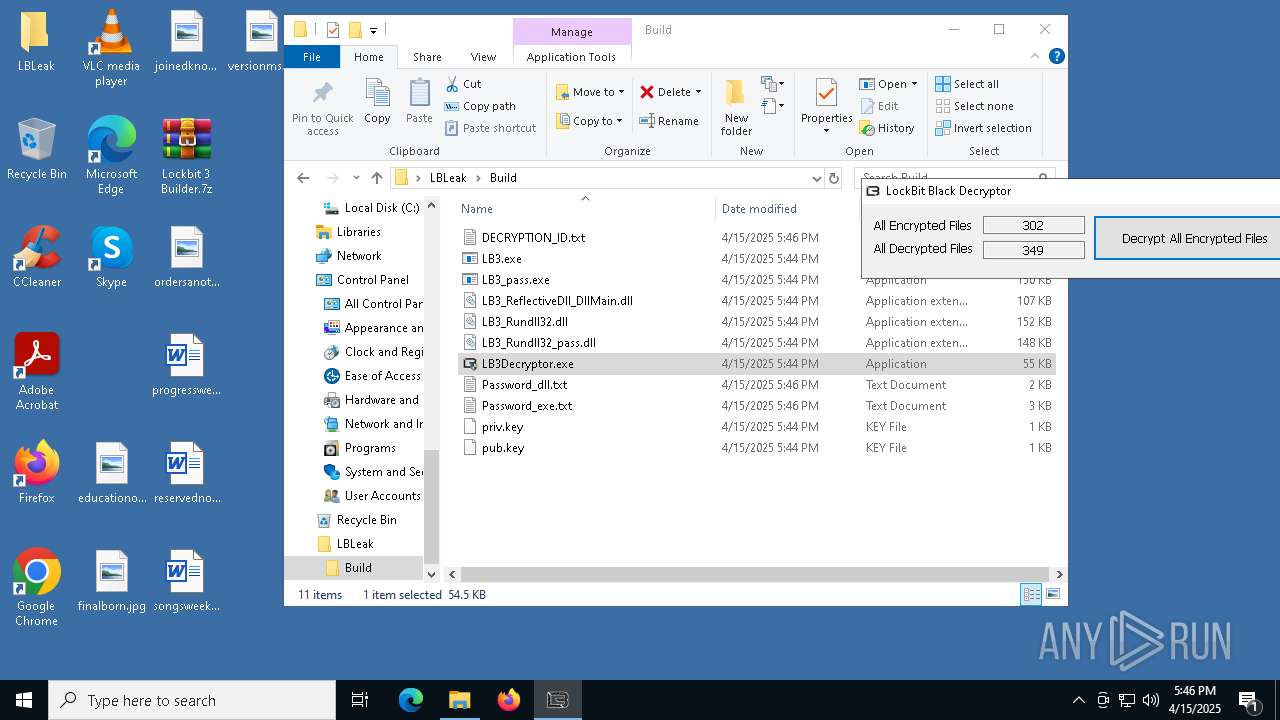
MALICIOUS
Known privilege escalation attack
- dllhost.exe (PID: 5968)
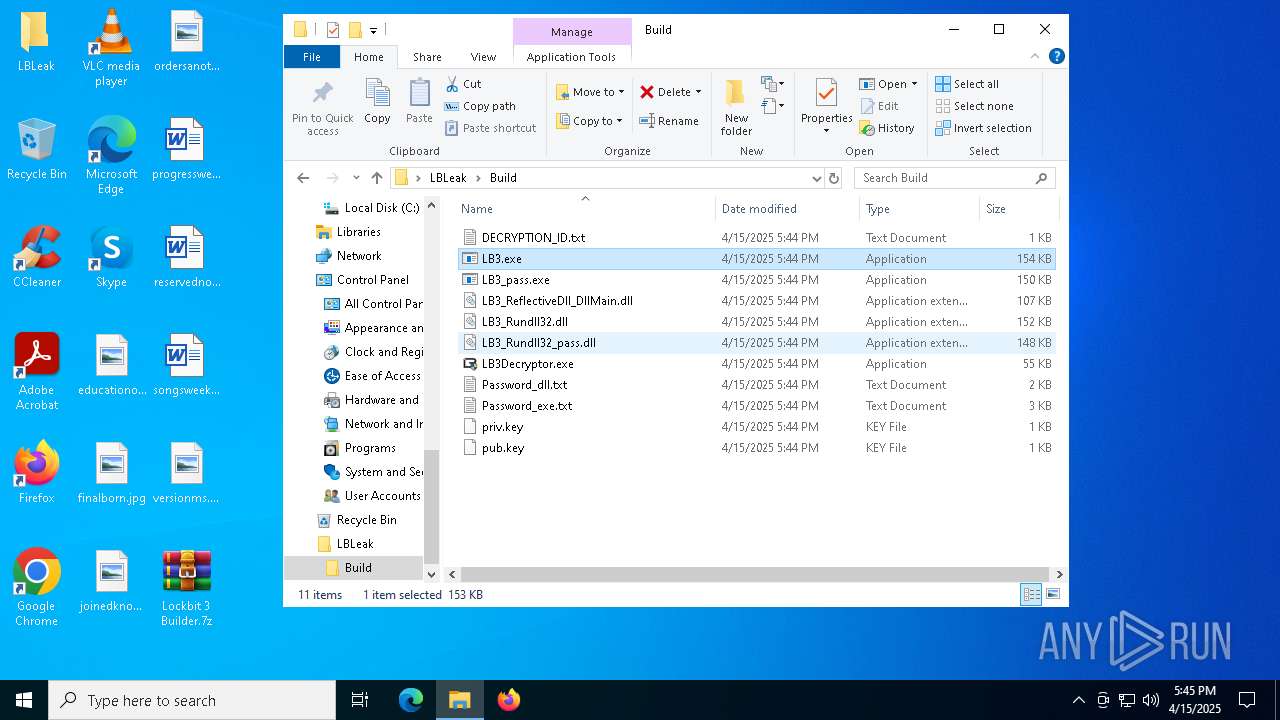
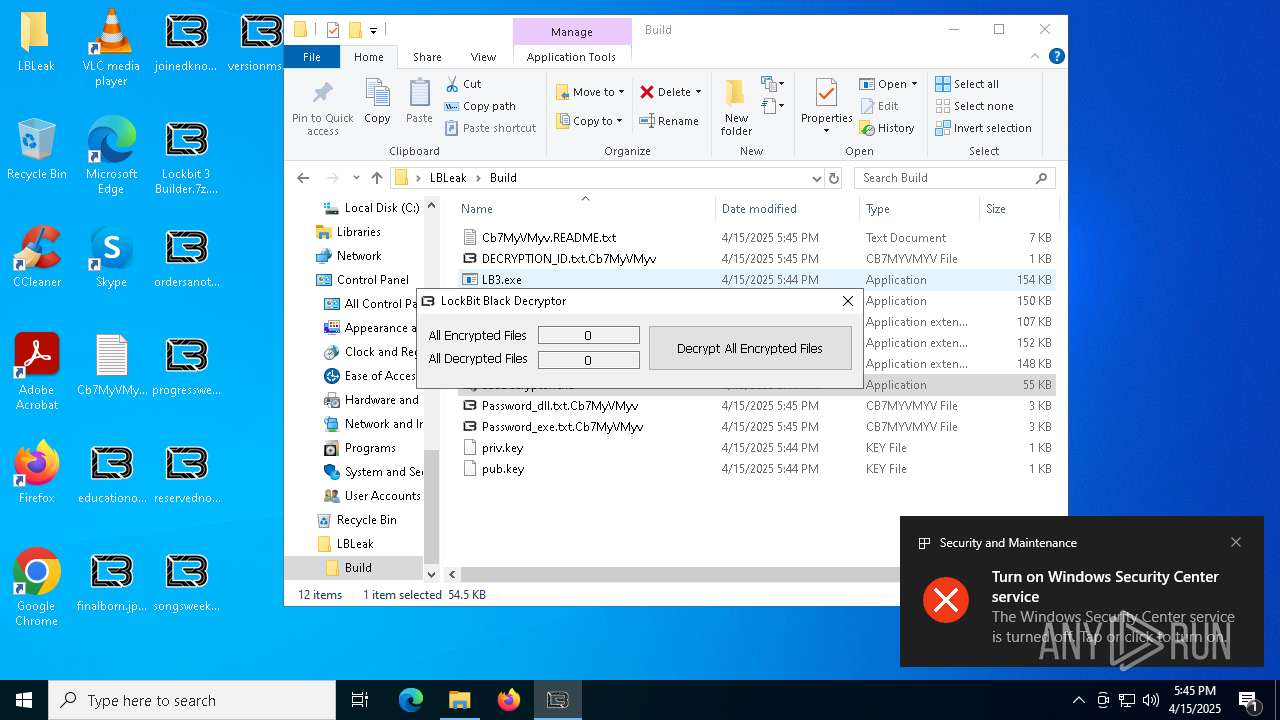
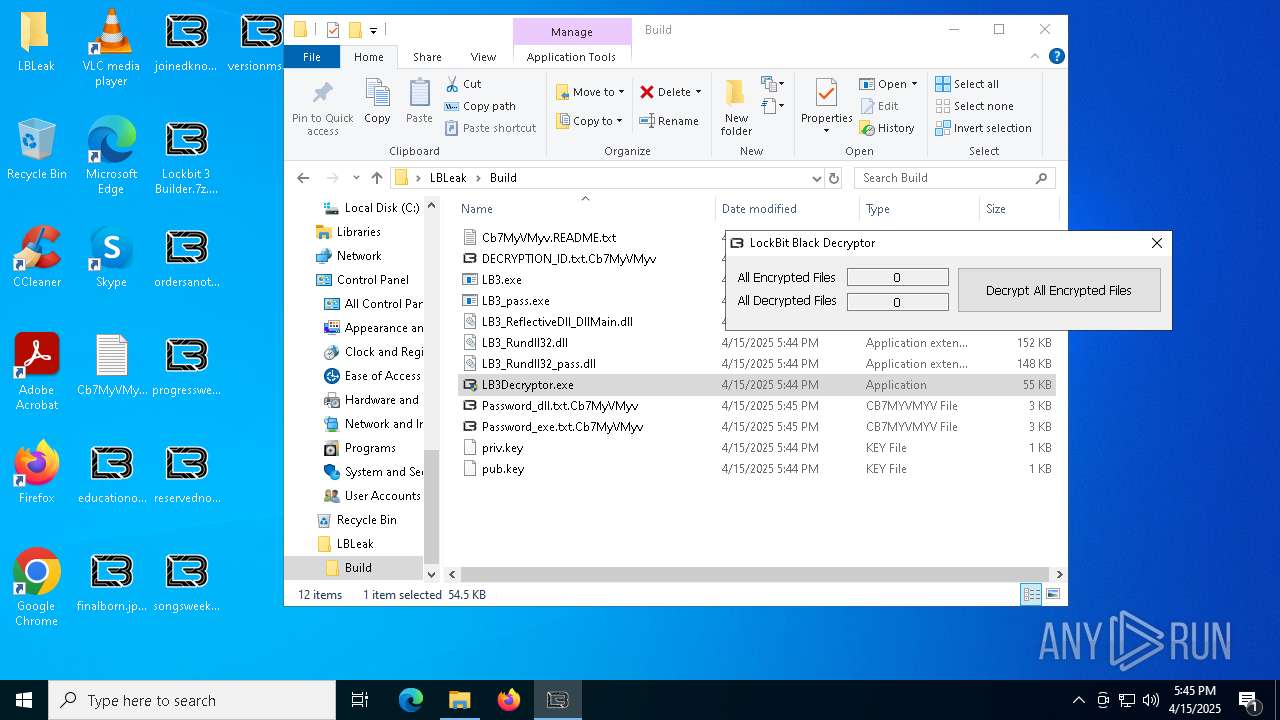
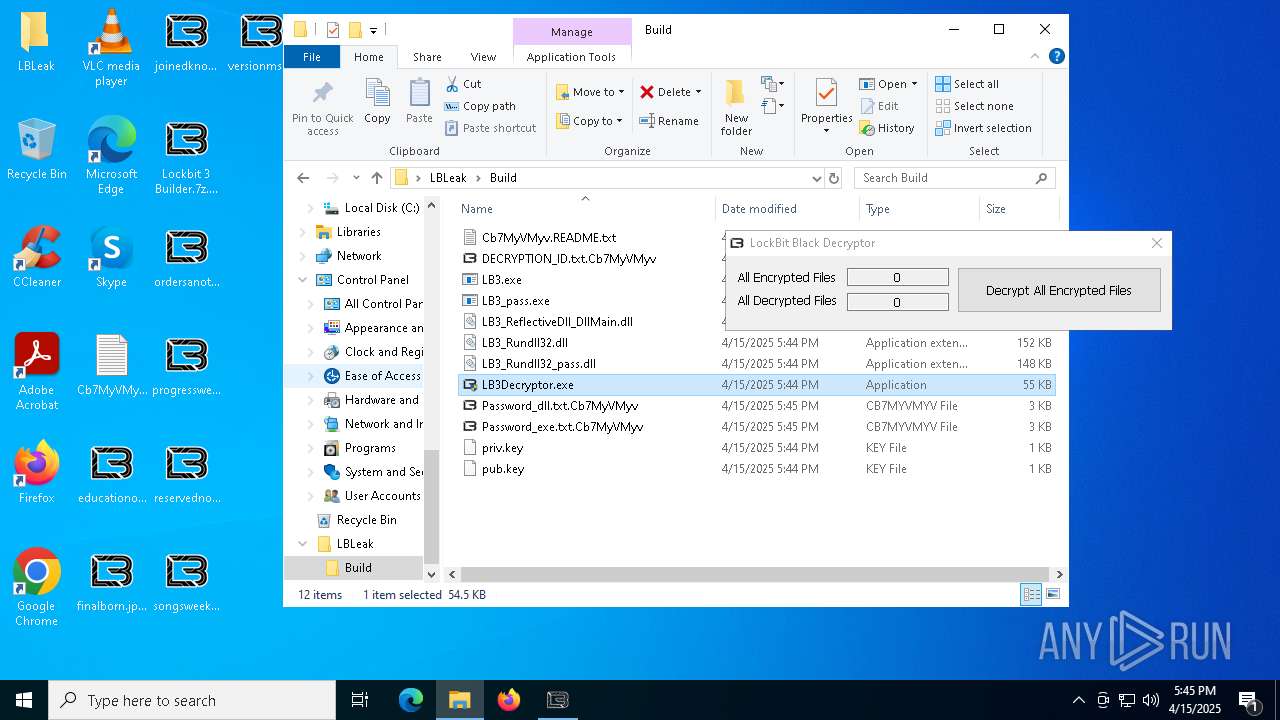
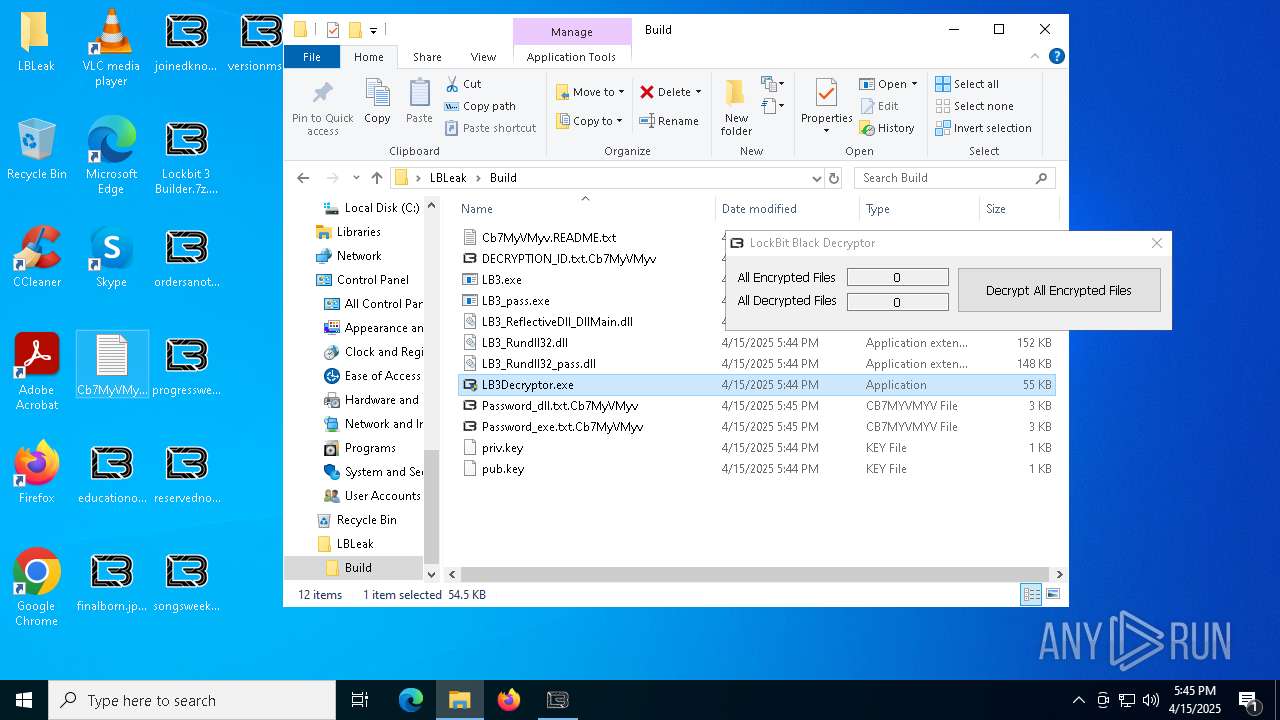
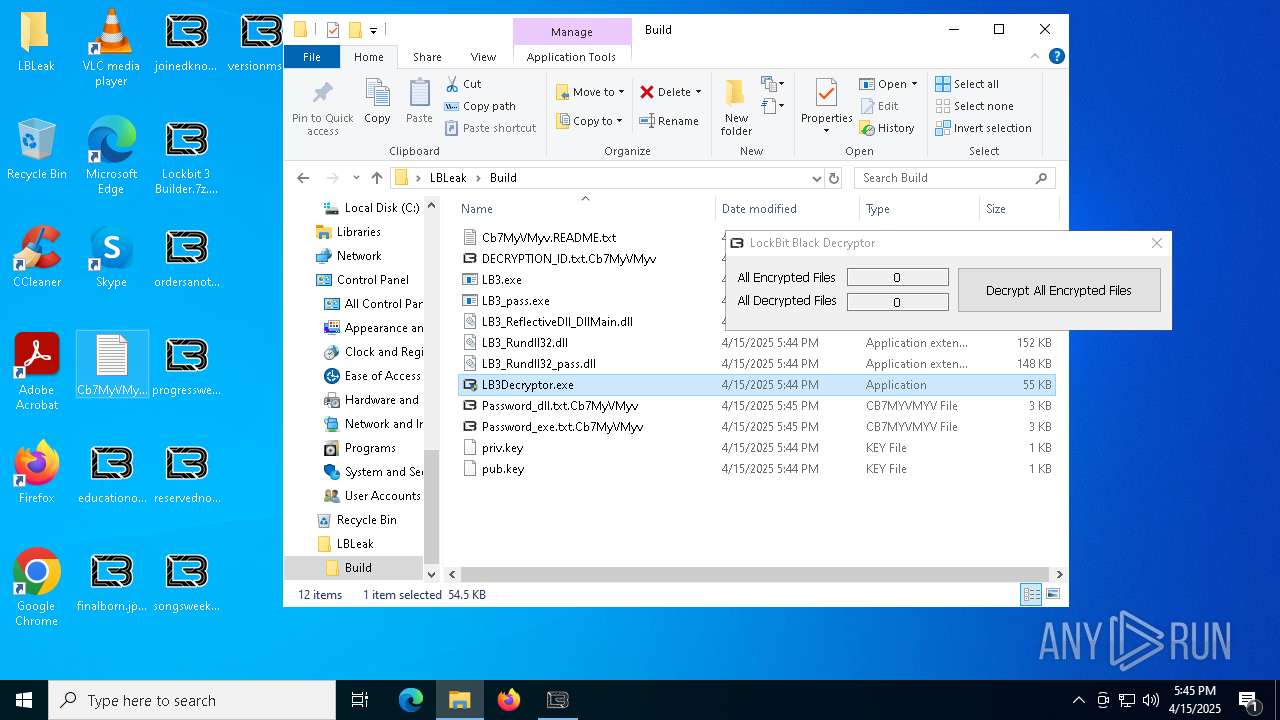
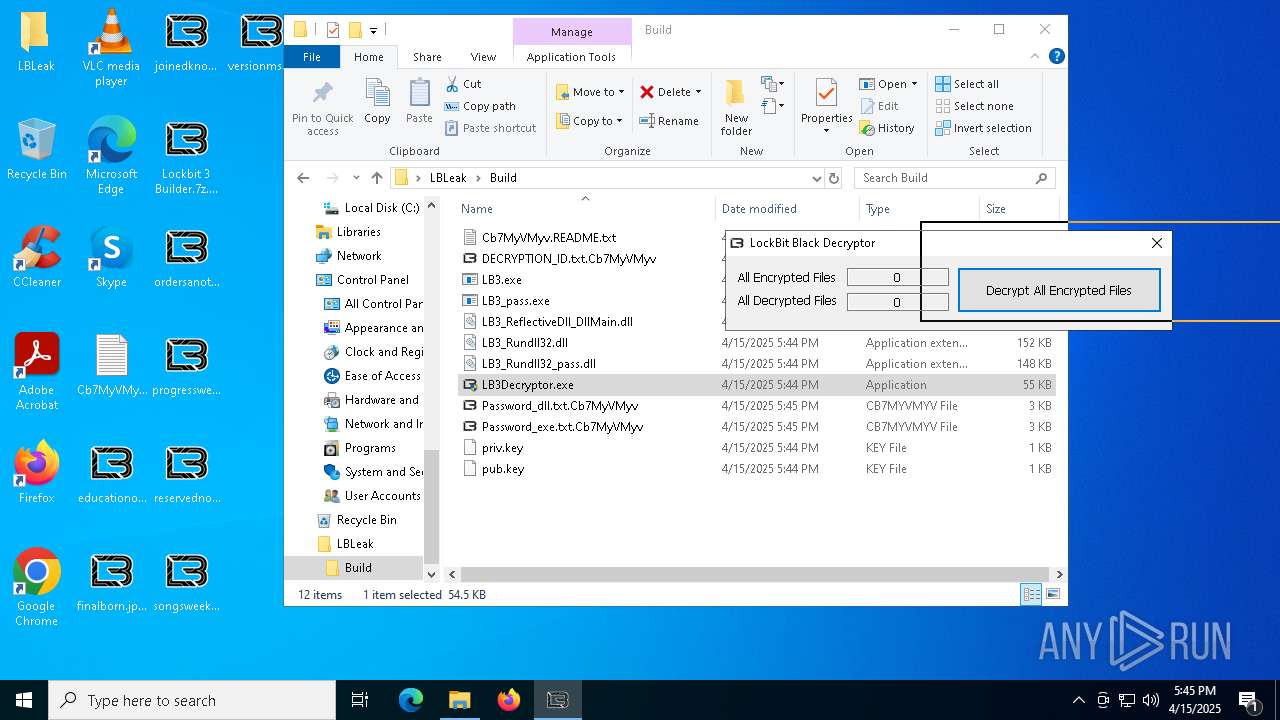
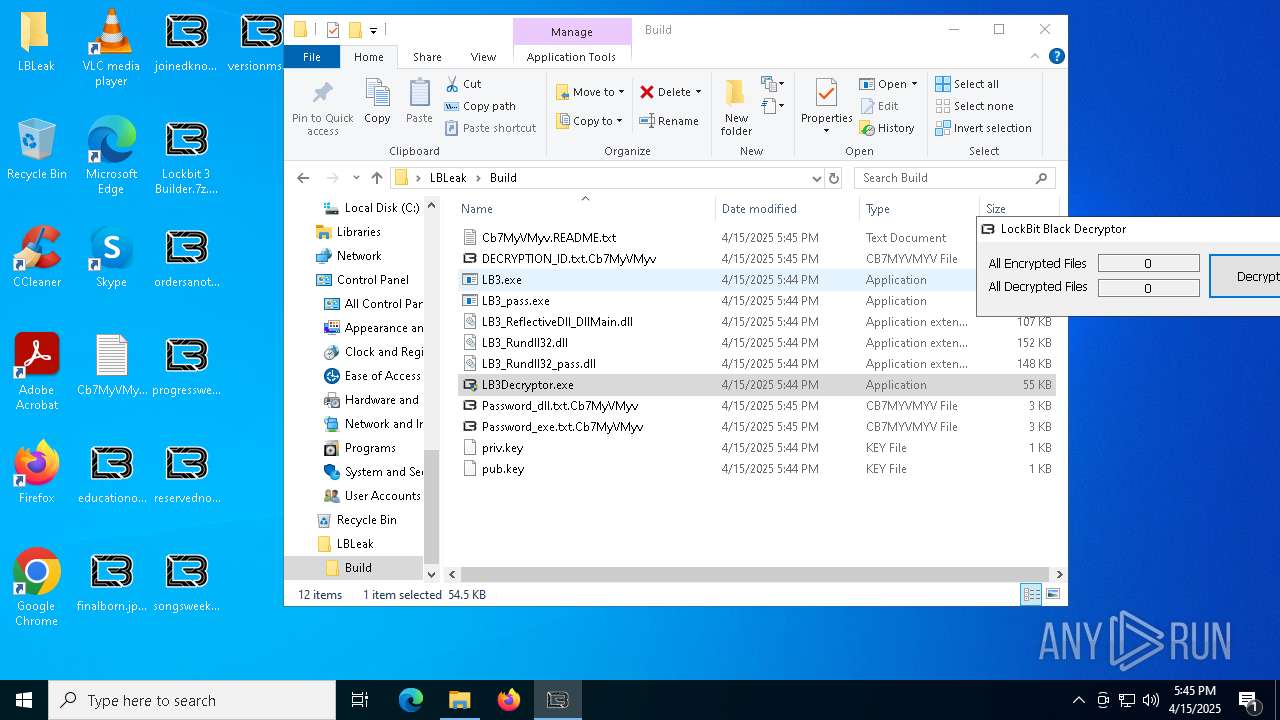
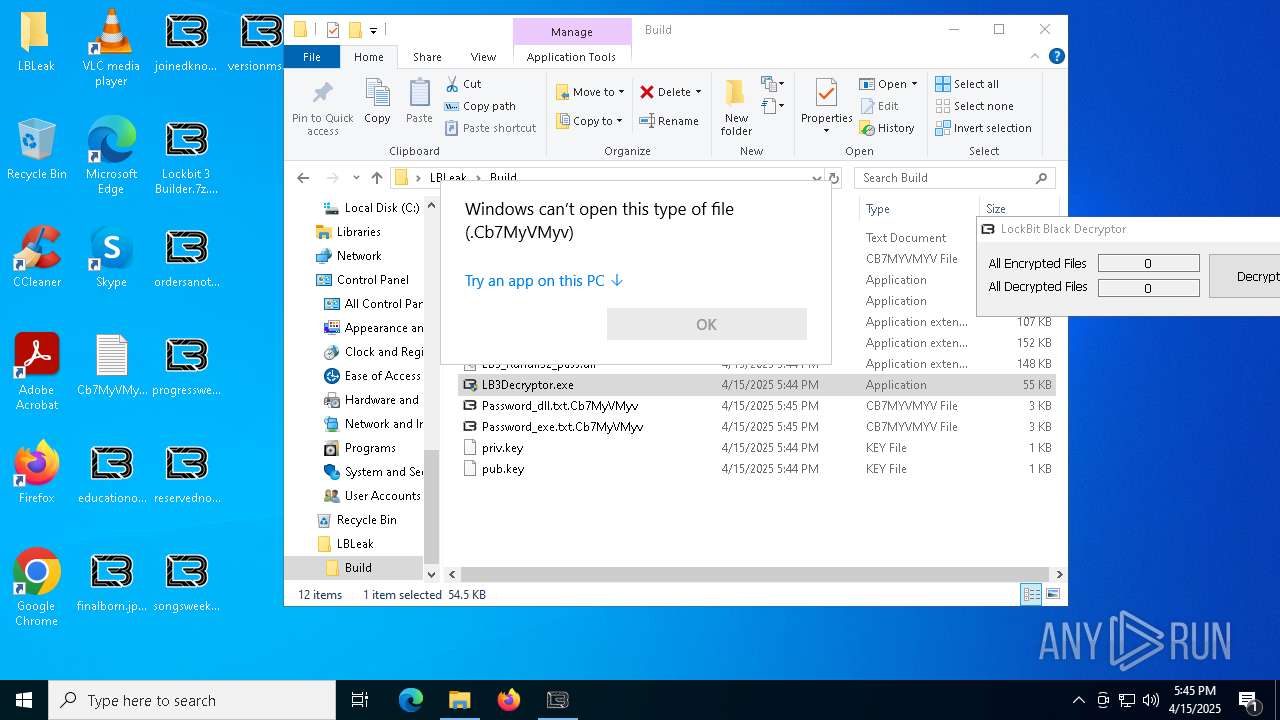
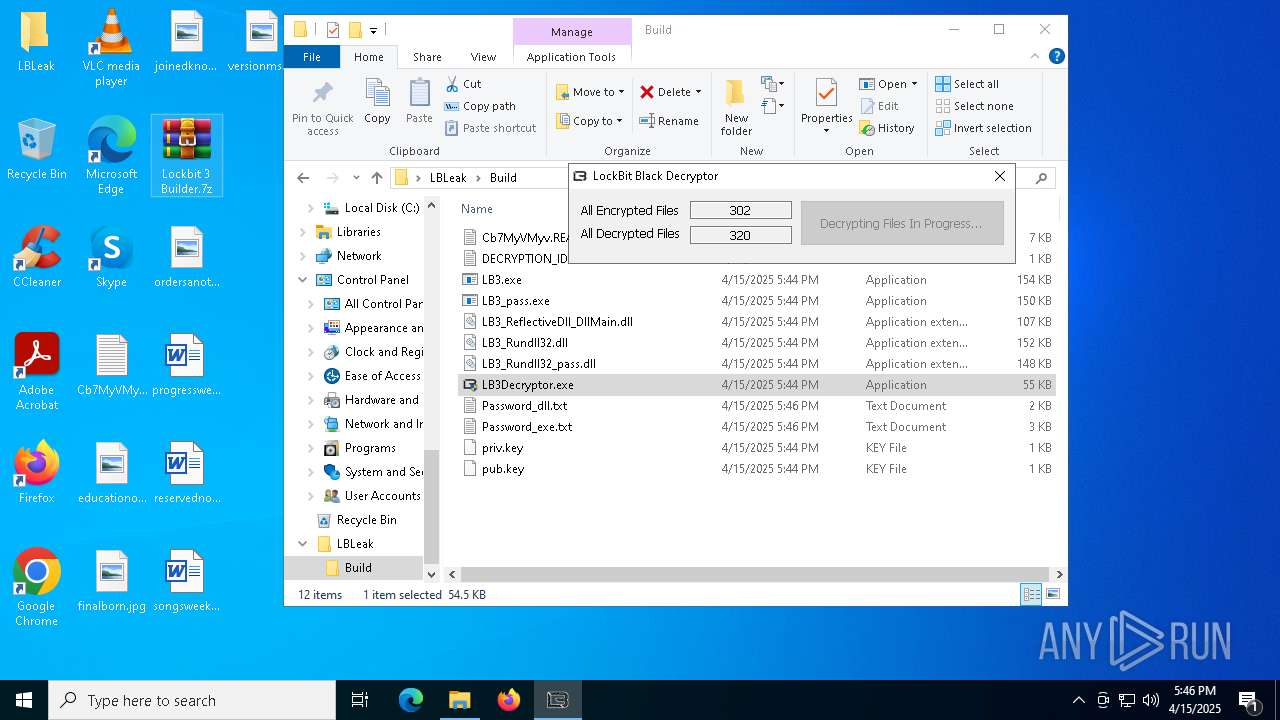
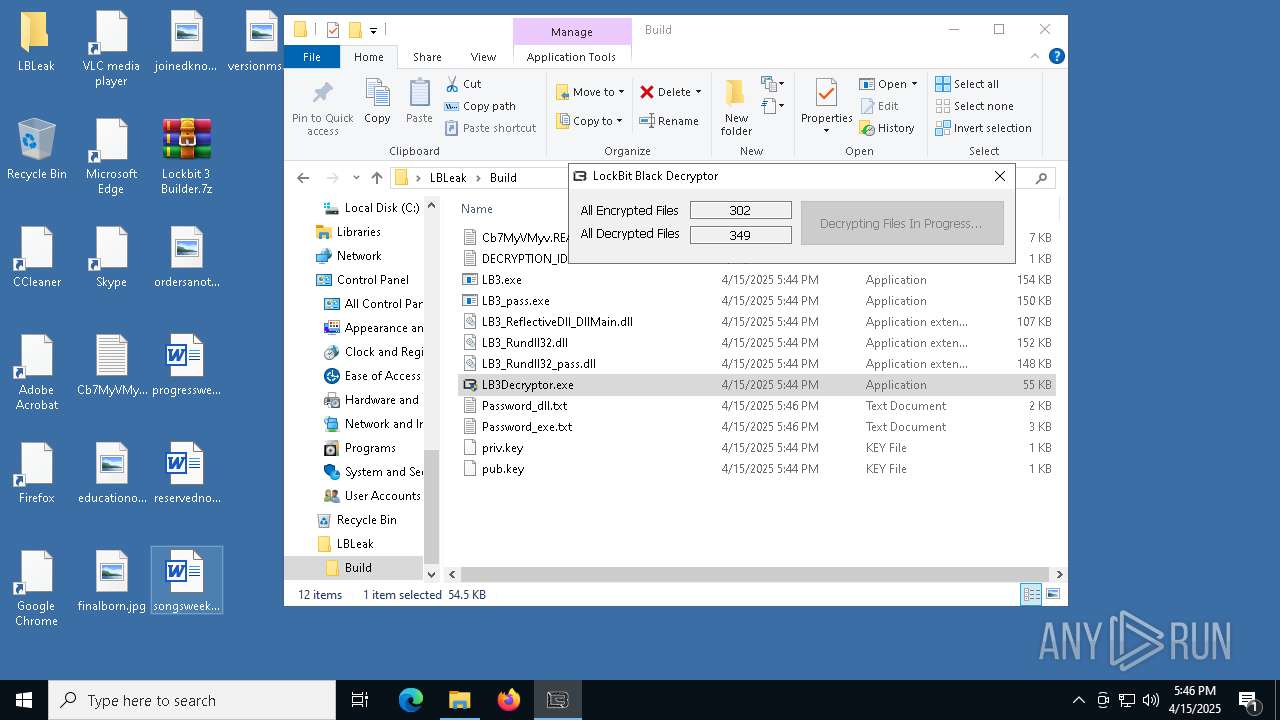
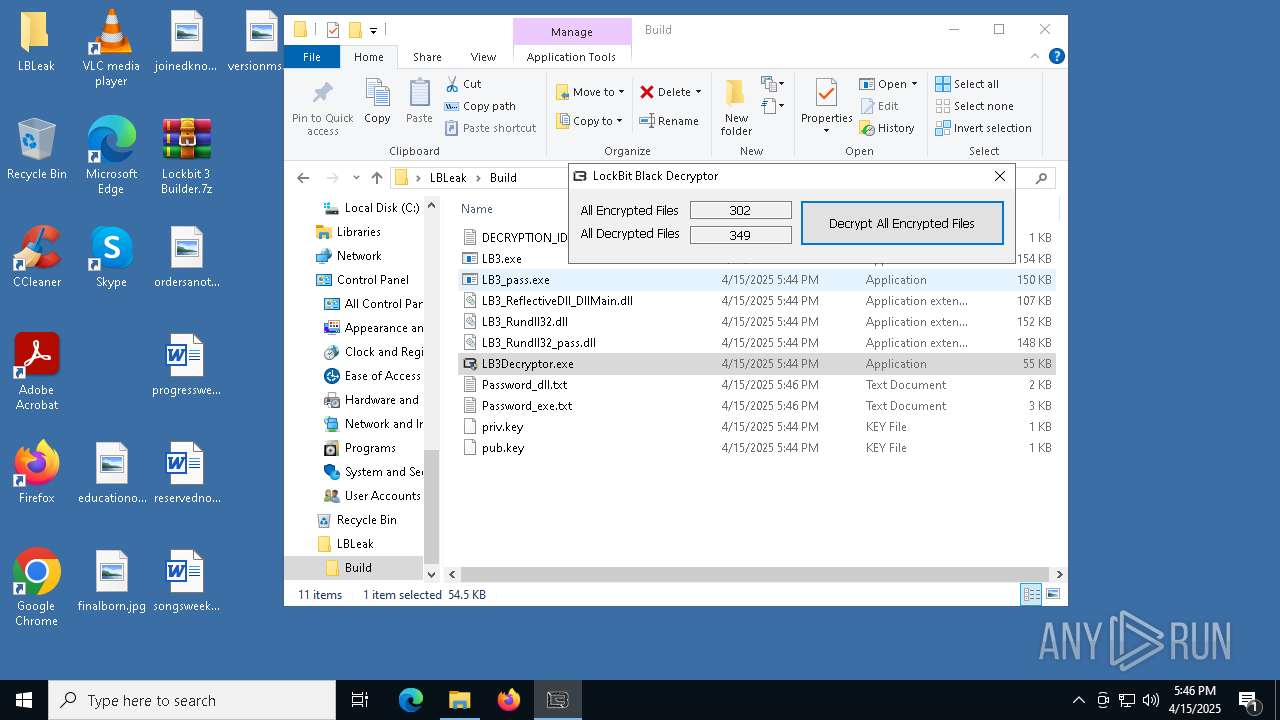
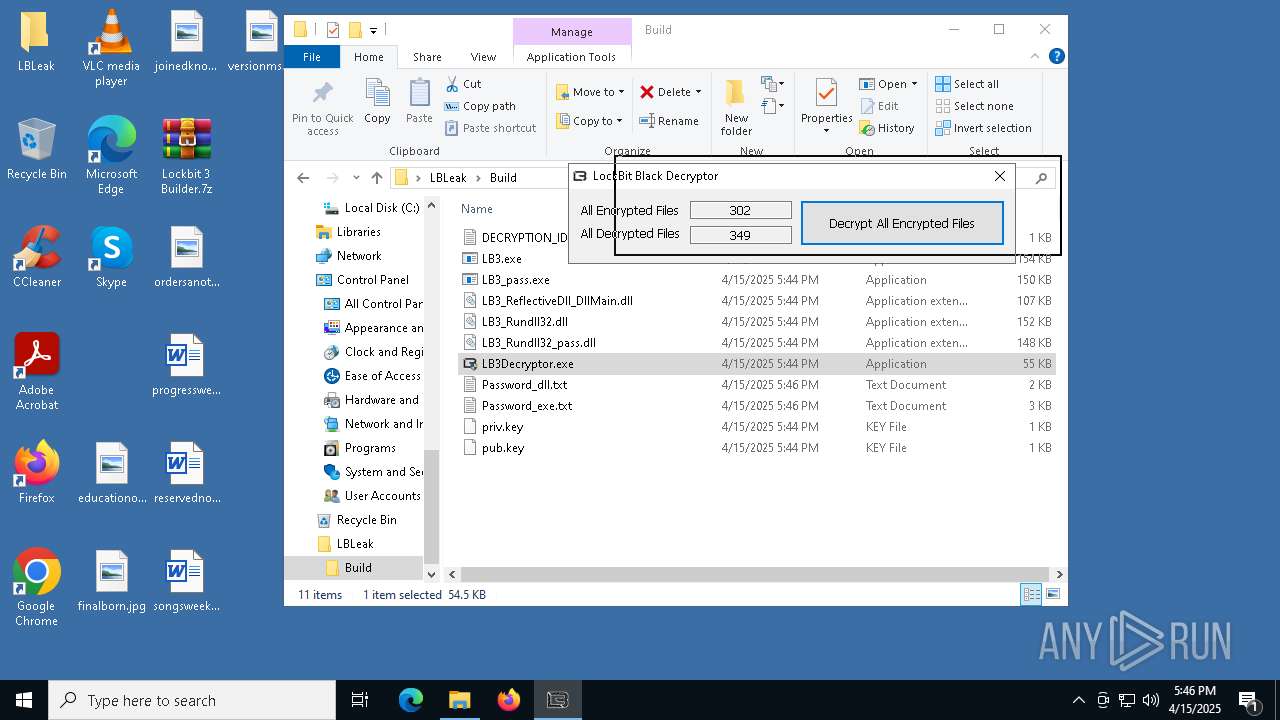
RANSOMWARE has been detected
- LB3.exe (PID: 7204)
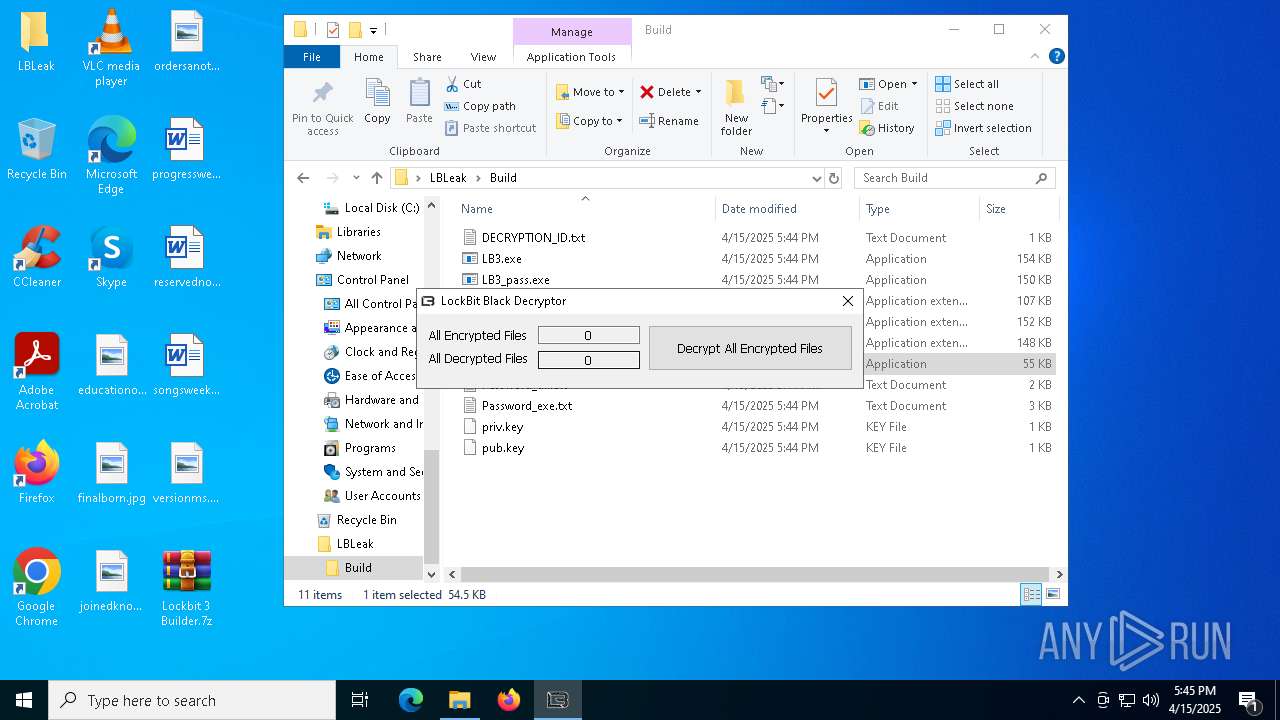
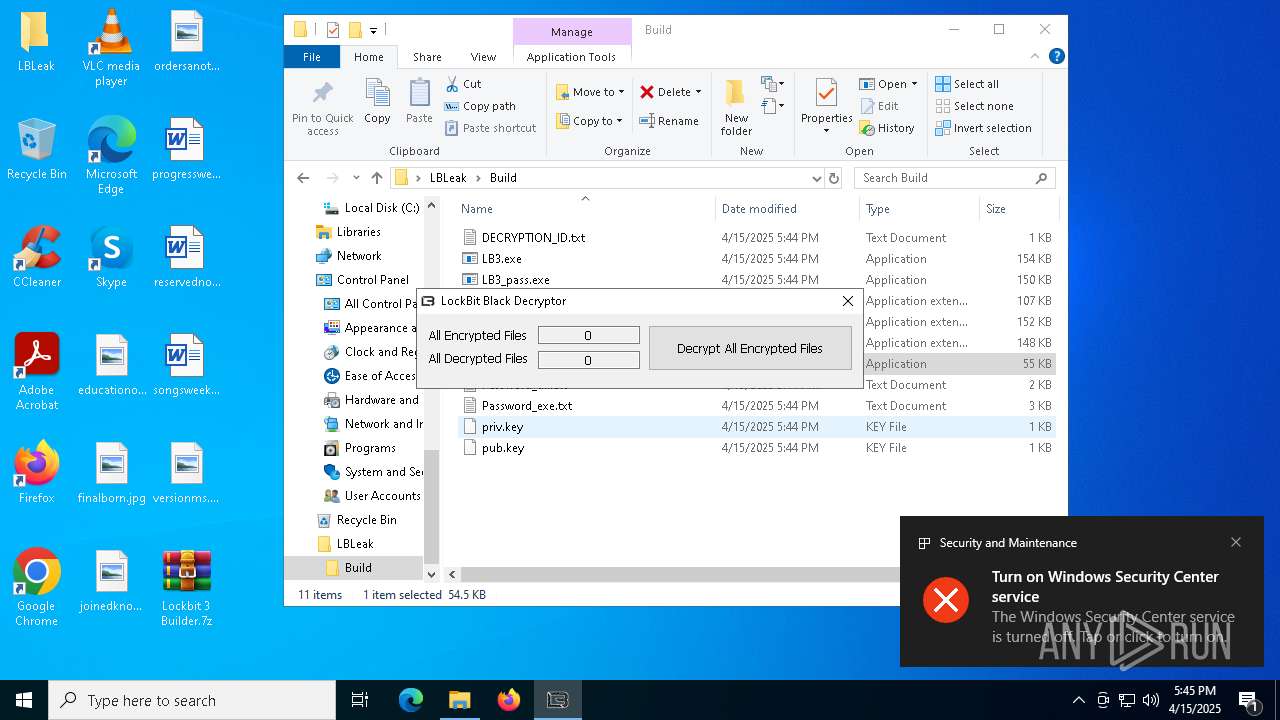
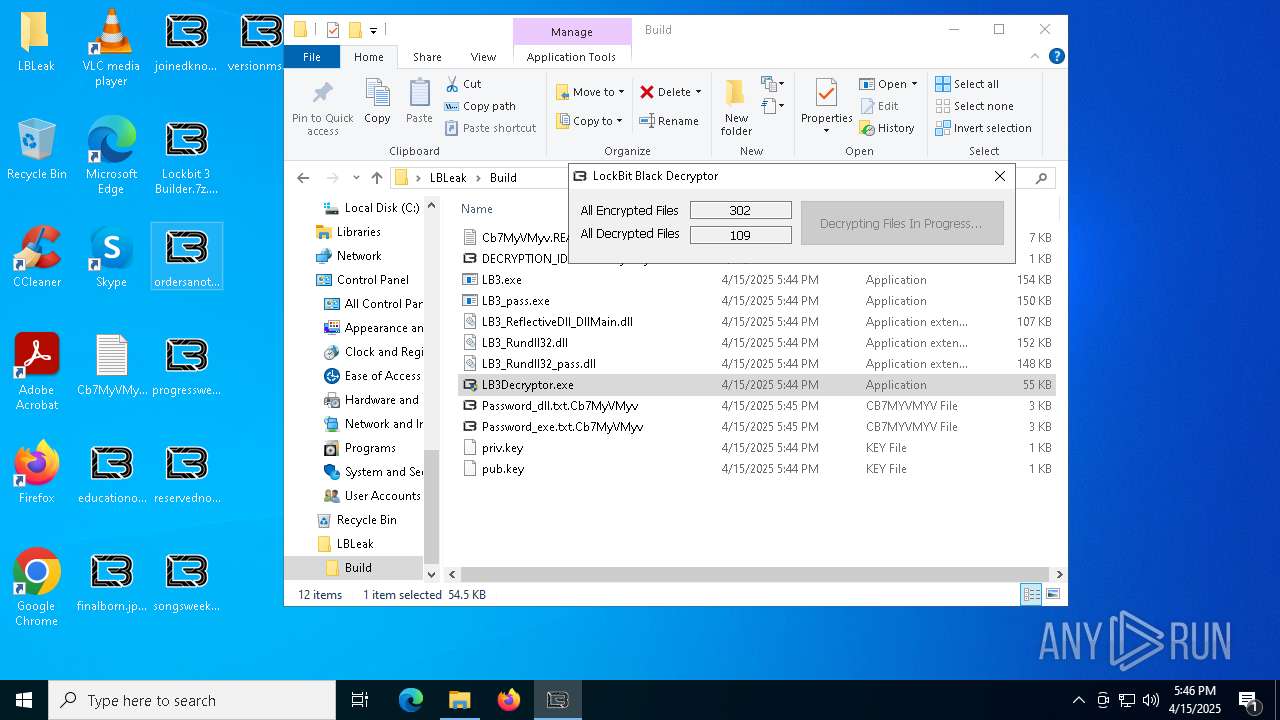
Actions looks like stealing of personal data
- LB3.exe (PID: 7204)
- LB3Decryptor.exe (PID: 5756)
Steals credentials from Web Browsers
- LB3.exe (PID: 7204)
- LB3Decryptor.exe (PID: 5756)
[YARA] LockBit is detected
- LB3.exe (PID: 7204)
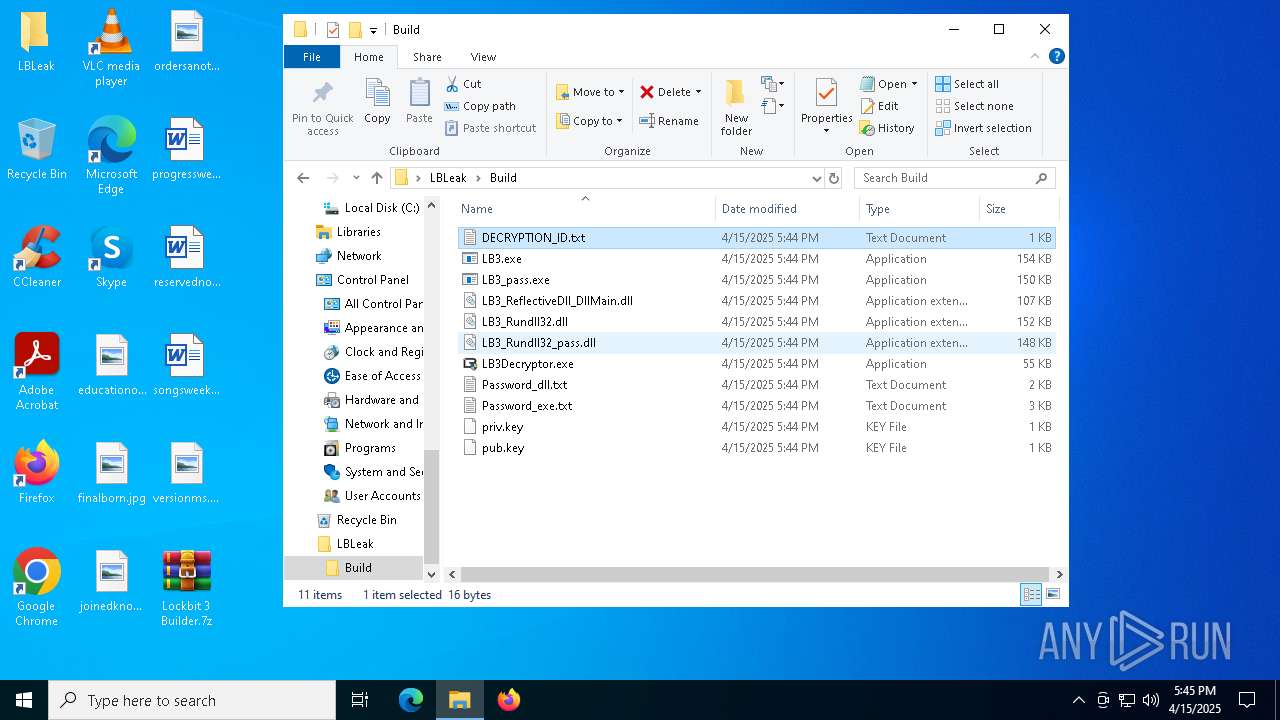
Renames files like ransomware
- LB3.exe (PID: 7204)
SUSPICIOUS
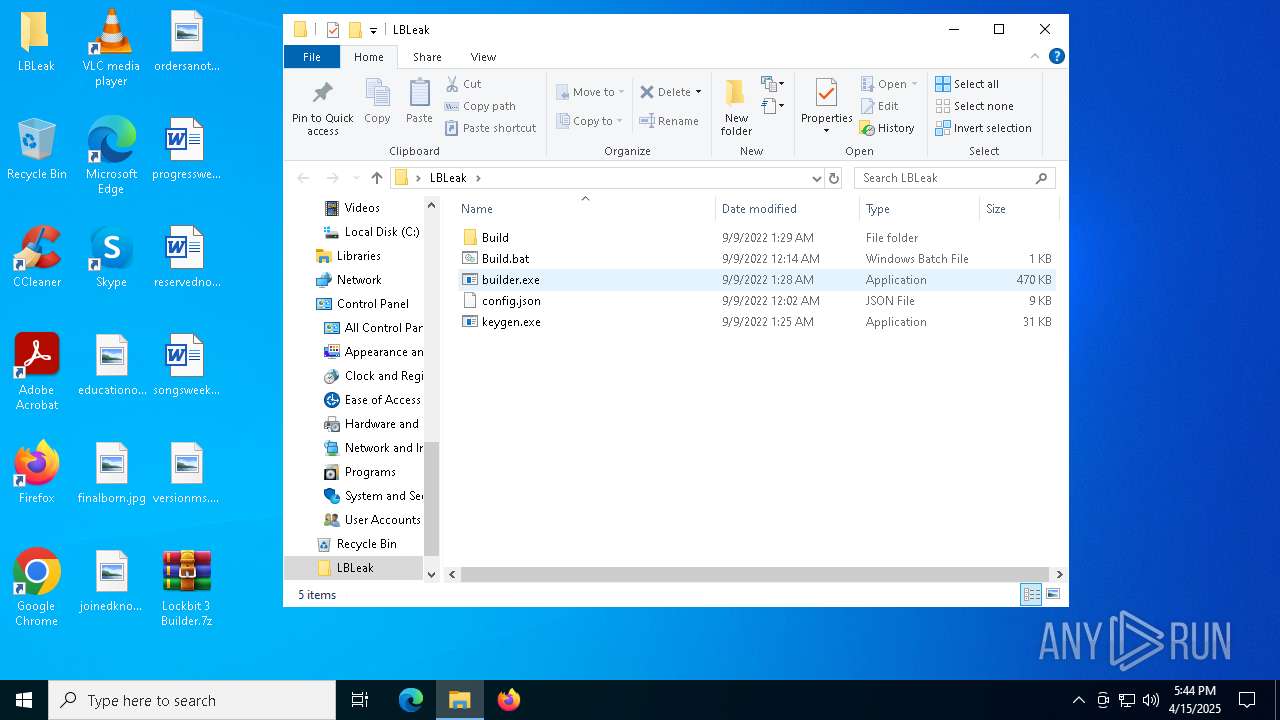
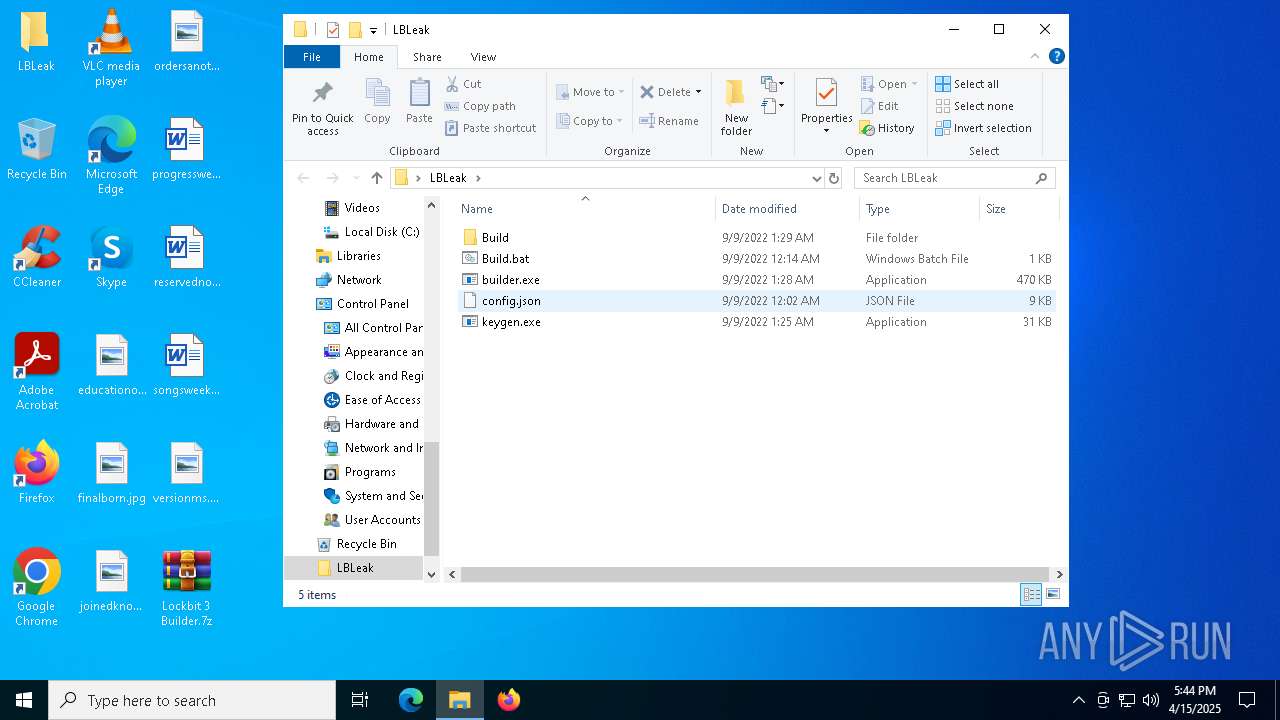
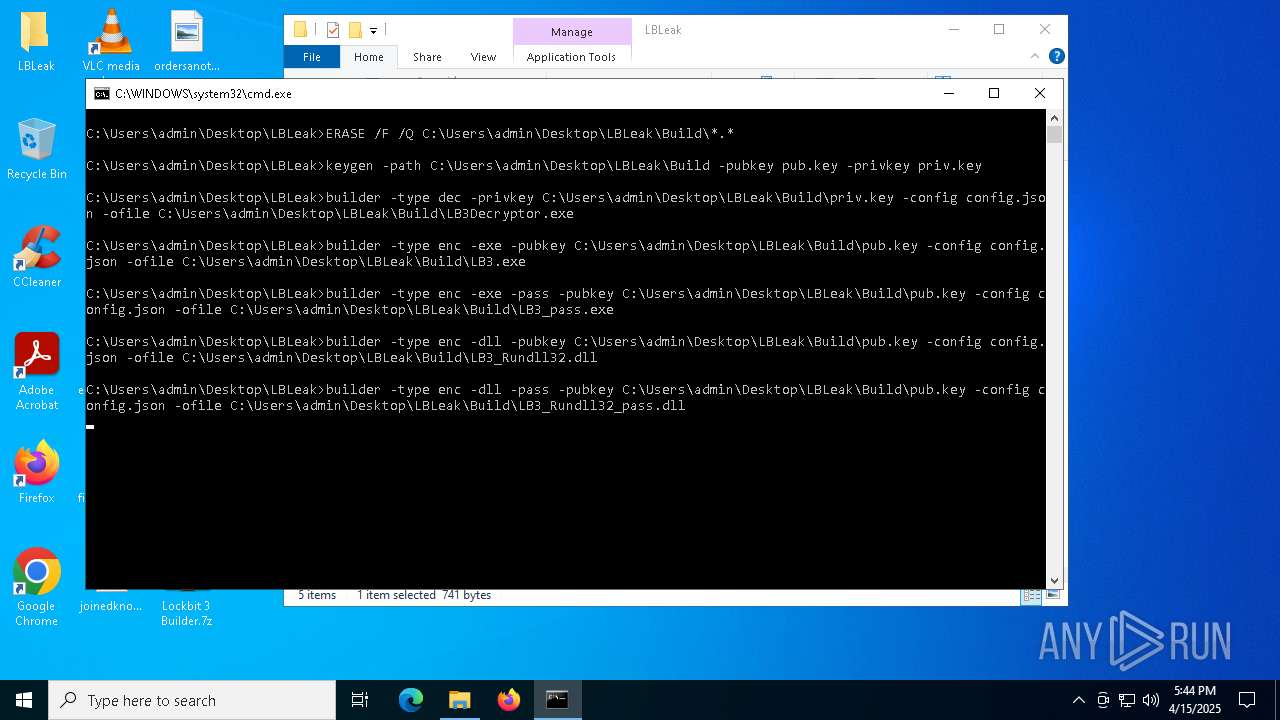
Executable content was dropped or overwritten
- builder.exe (PID: 7952)
- builder.exe (PID: 7928)
- builder.exe (PID: 7976)
- builder.exe (PID: 8000)
- builder.exe (PID: 8024)
- builder.exe (PID: 8048)
The process creates files with name similar to system file names
- builder.exe (PID: 8000)
Write to the desktop.ini file (may be used to cloak folders)
- LB3.exe (PID: 7204)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 2240)
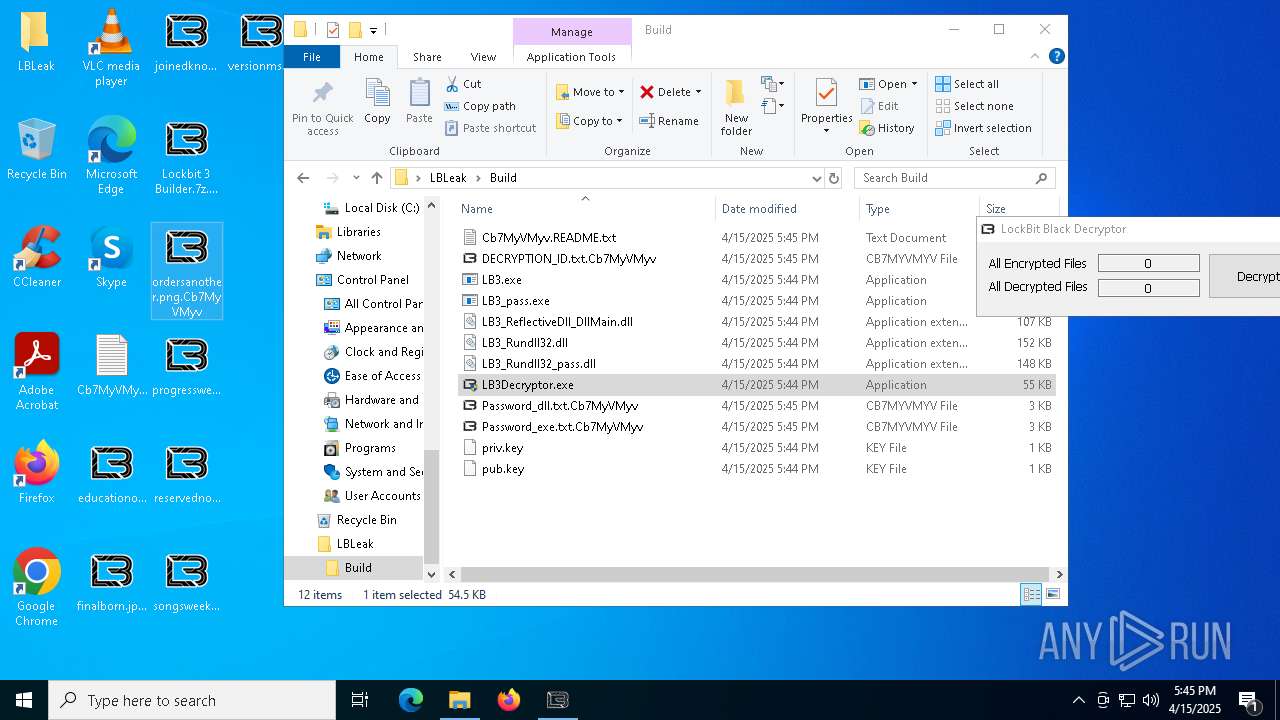
Changes the desktop background image
- LB3Decryptor.exe (PID: 5756)
INFO
Checks supported languages
- builder.exe (PID: 7928)
- builder.exe (PID: 7952)
- builder.exe (PID: 8000)
- builder.exe (PID: 7976)
- keygen.exe (PID: 7900)
- builder.exe (PID: 8024)
- builder.exe (PID: 8048)
- LB3.exe (PID: 7204)
- ShellExperienceHost.exe (PID: 2240)
- LB3Decryptor.exe (PID: 5756)
- SearchApp.exe (PID: 7932)
- LB3.exe (PID: 5608)
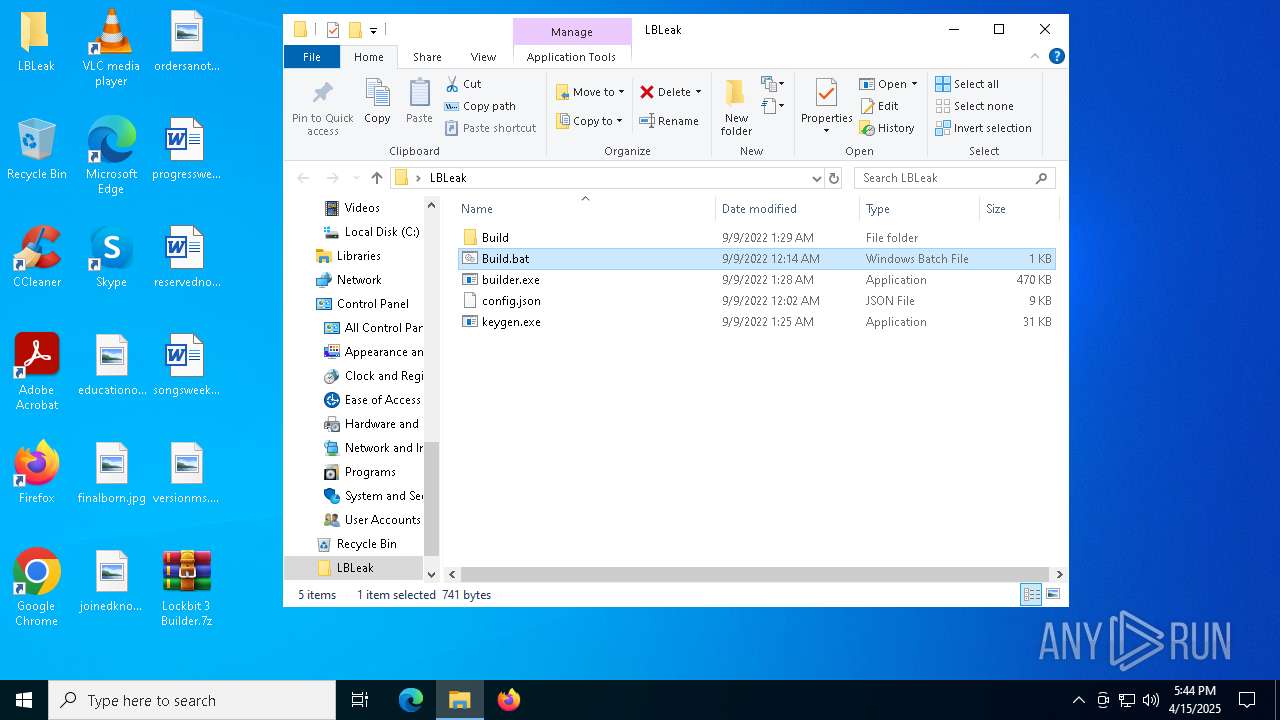
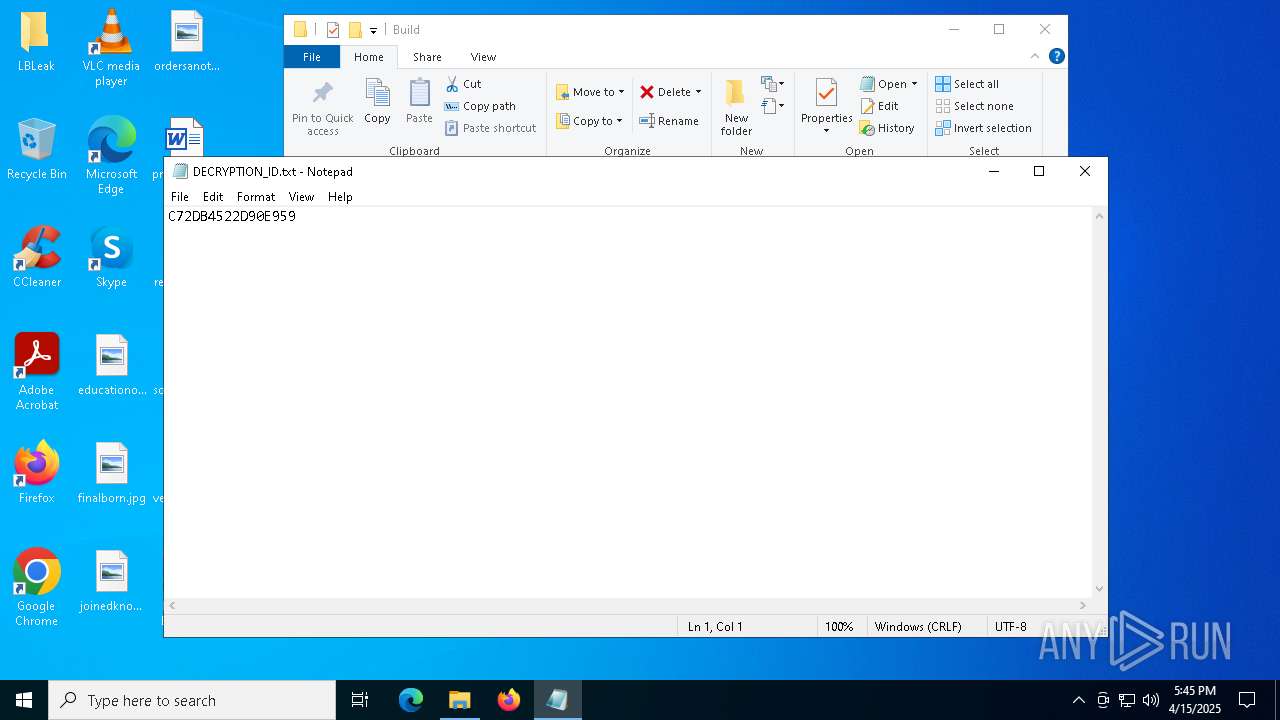
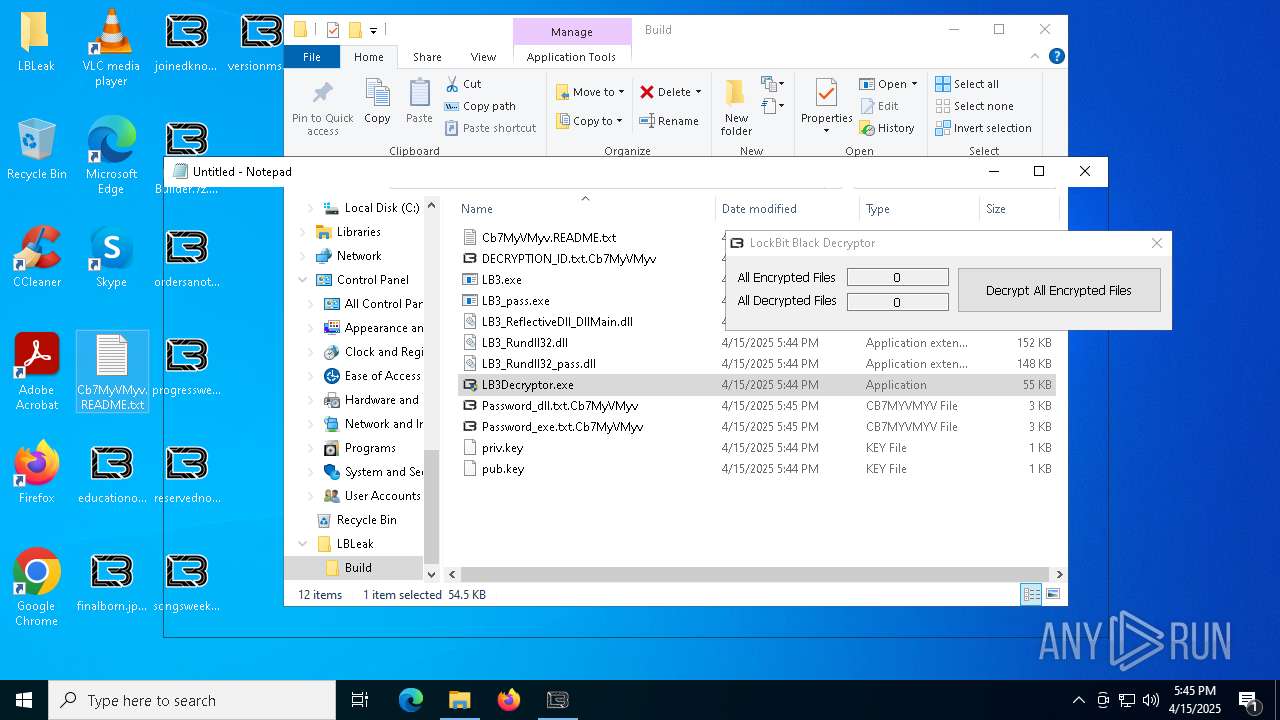
Manual execution by a user
- cmd.exe (PID: 7832)
- notepad.exe (PID: 1660)
- notepad.exe (PID: 1184)
- notepad.exe (PID: 6644)
- LB3Decryptor.exe (PID: 4652)
- LB3Decryptor.exe (PID: 5756)
- notepad.exe (PID: 7624)
- notepad.exe (PID: 7716)
- notepad.exe (PID: 4944)
- LB3.exe (PID: 5608)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2140)
Reads security settings of Internet Explorer
- notepad.exe (PID: 1660)
- notepad.exe (PID: 1184)
- notepad.exe (PID: 6644)
- dllhost.exe (PID: 5968)
- notepad.exe (PID: 7624)
- notepad.exe (PID: 7716)
- notepad.exe (PID: 4944)
Reads the software policy settings
- slui.exe (PID: 7260)
- SearchApp.exe (PID: 7932)
Reads the computer name
- LB3.exe (PID: 5608)
- LB3.exe (PID: 7204)
- ShellExperienceHost.exe (PID: 2240)
- LB3Decryptor.exe (PID: 5756)
- SearchApp.exe (PID: 7932)
Reads the machine GUID from the registry
- LB3.exe (PID: 5608)
- SearchApp.exe (PID: 7932)
Creates files in the program directory
- LB3.exe (PID: 7204)
Process checks computer location settings
- SearchApp.exe (PID: 7932)
Creates files or folders in the user directory
- LB3.exe (PID: 7204)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 7760)
Create files in a temporary directory
- LB3.exe (PID: 7204)
Reads Environment values
- SearchApp.exe (PID: 7932)
Checks proxy server information
- SearchApp.exe (PID: 7932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|
Total processes
159
Monitored processes
28
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
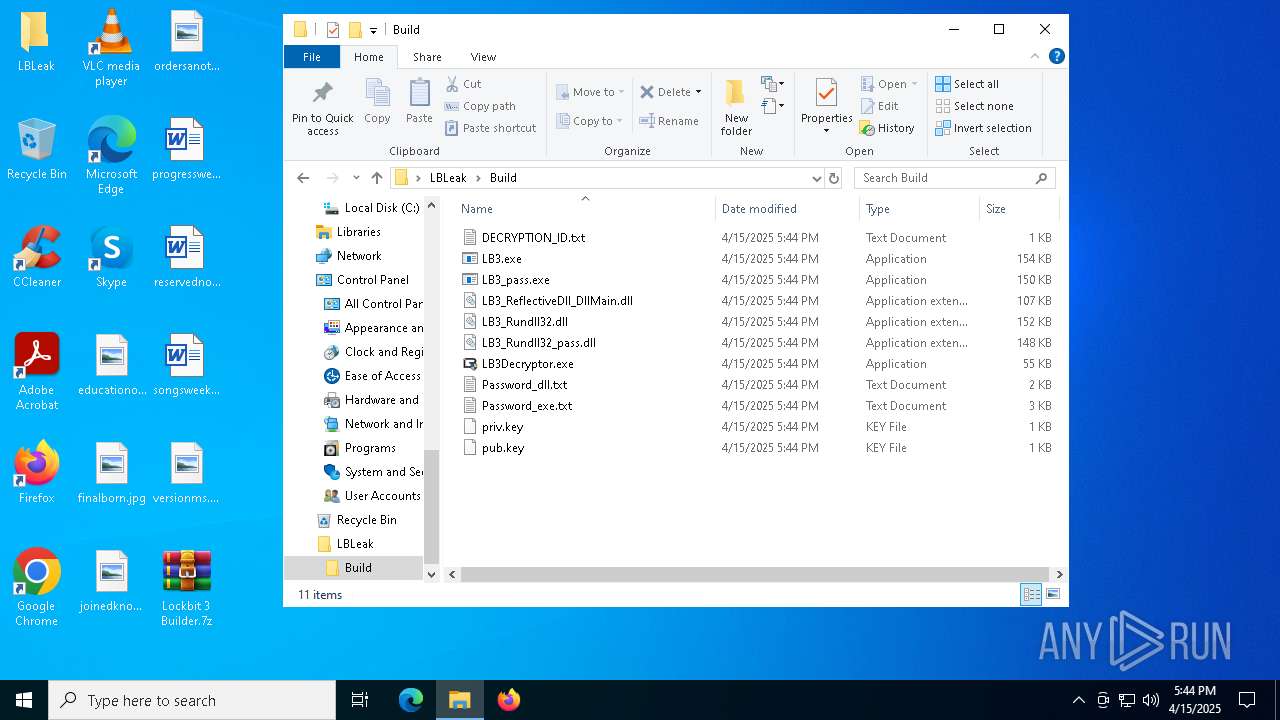
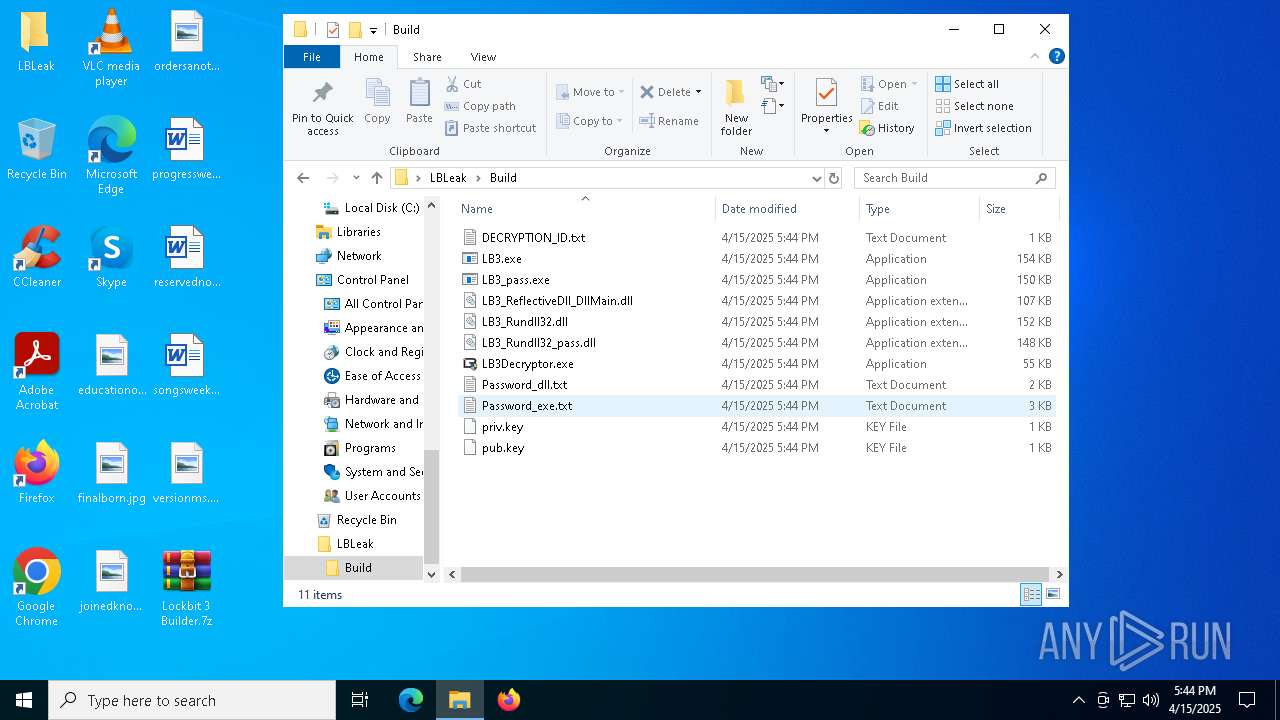
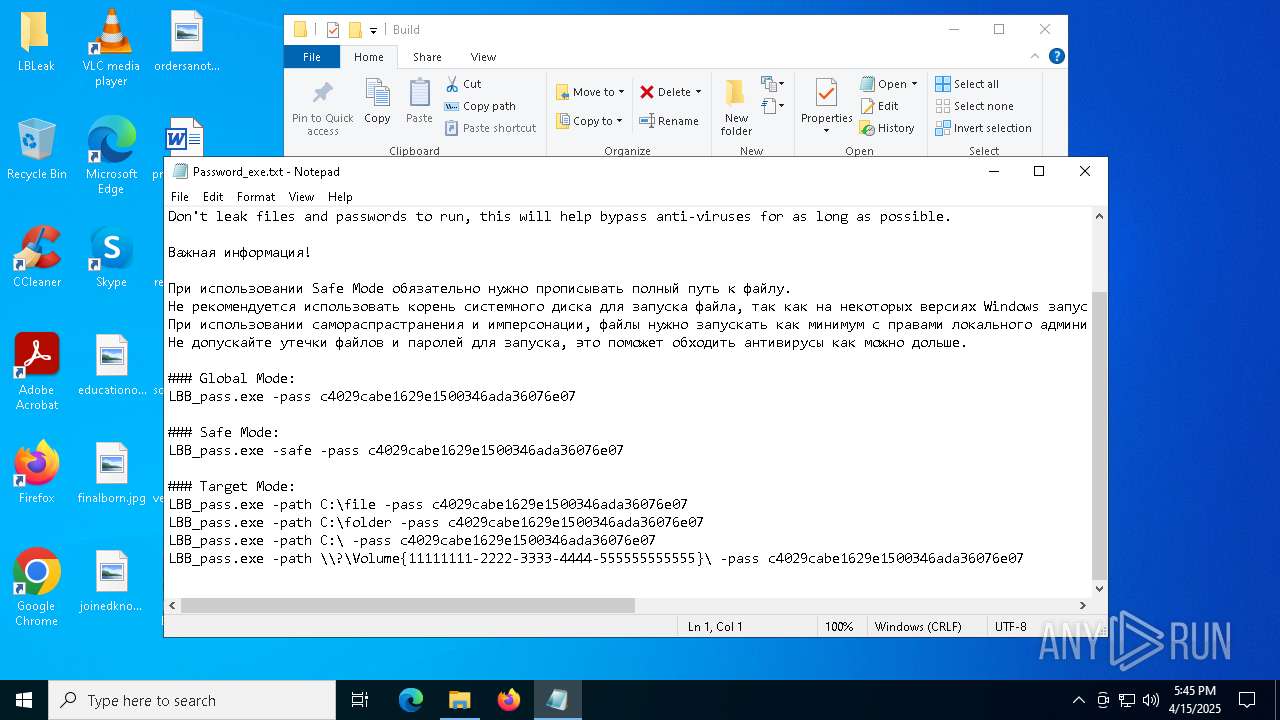
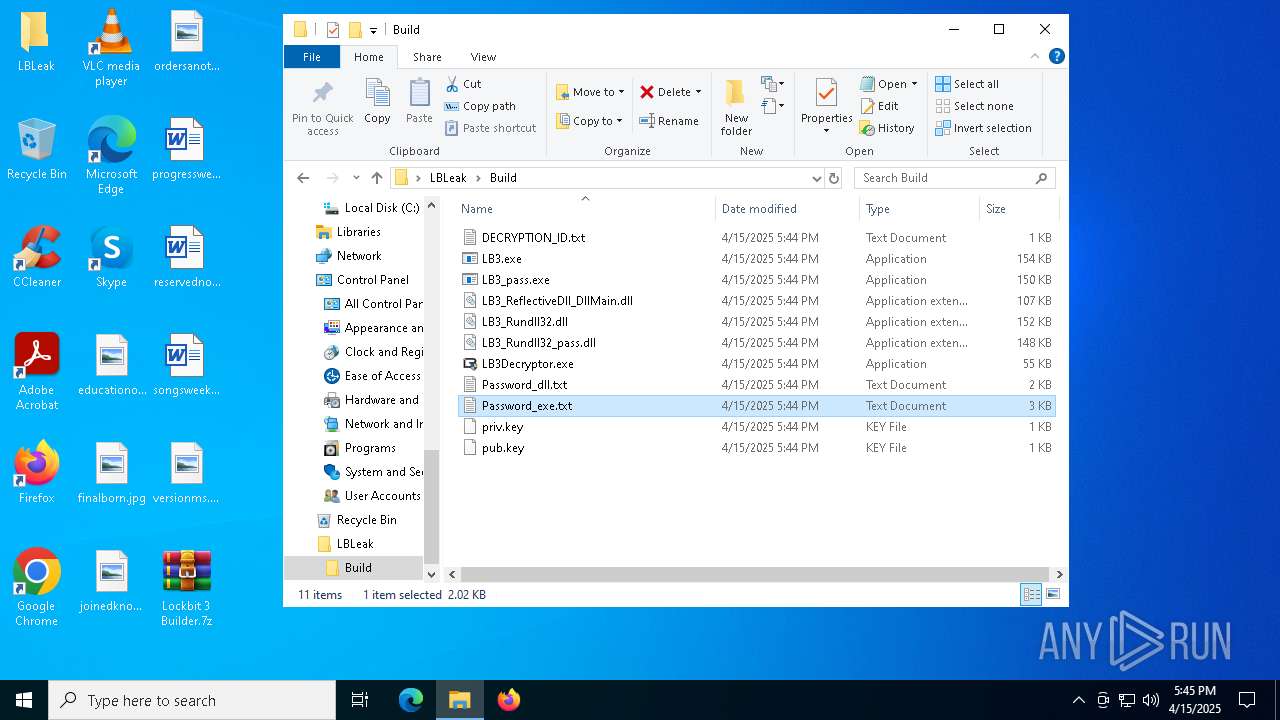
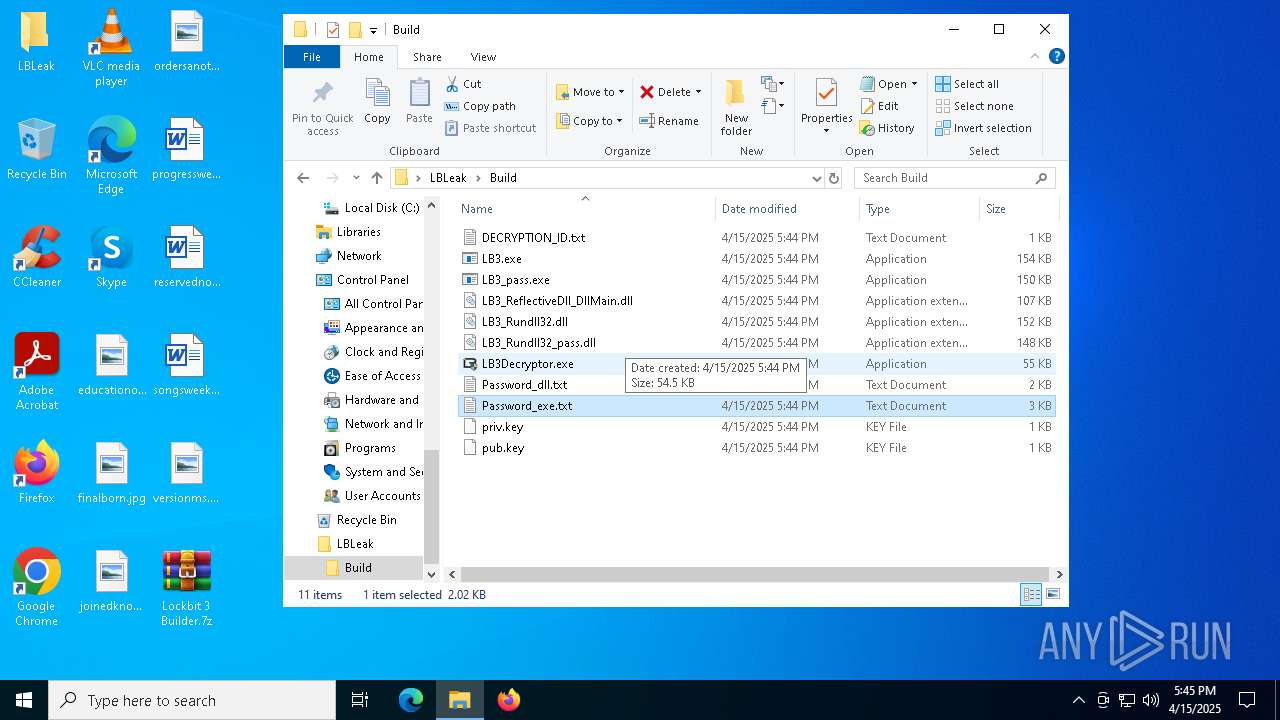
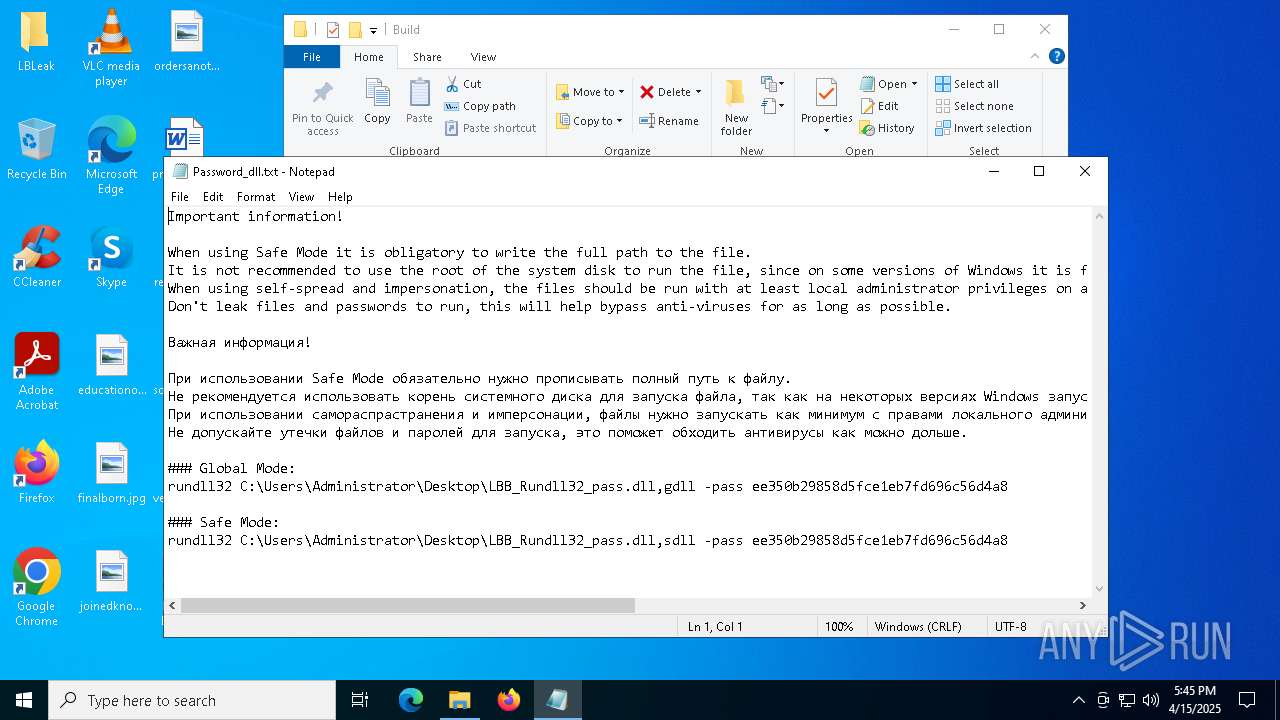
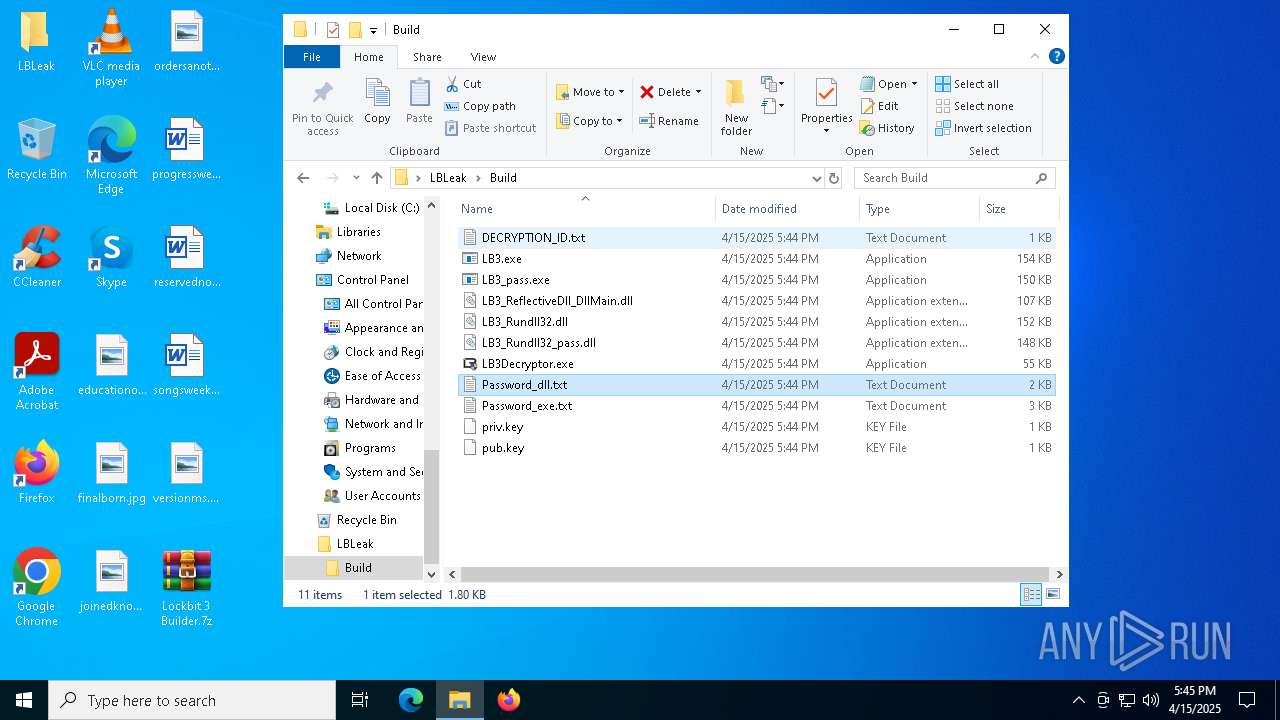
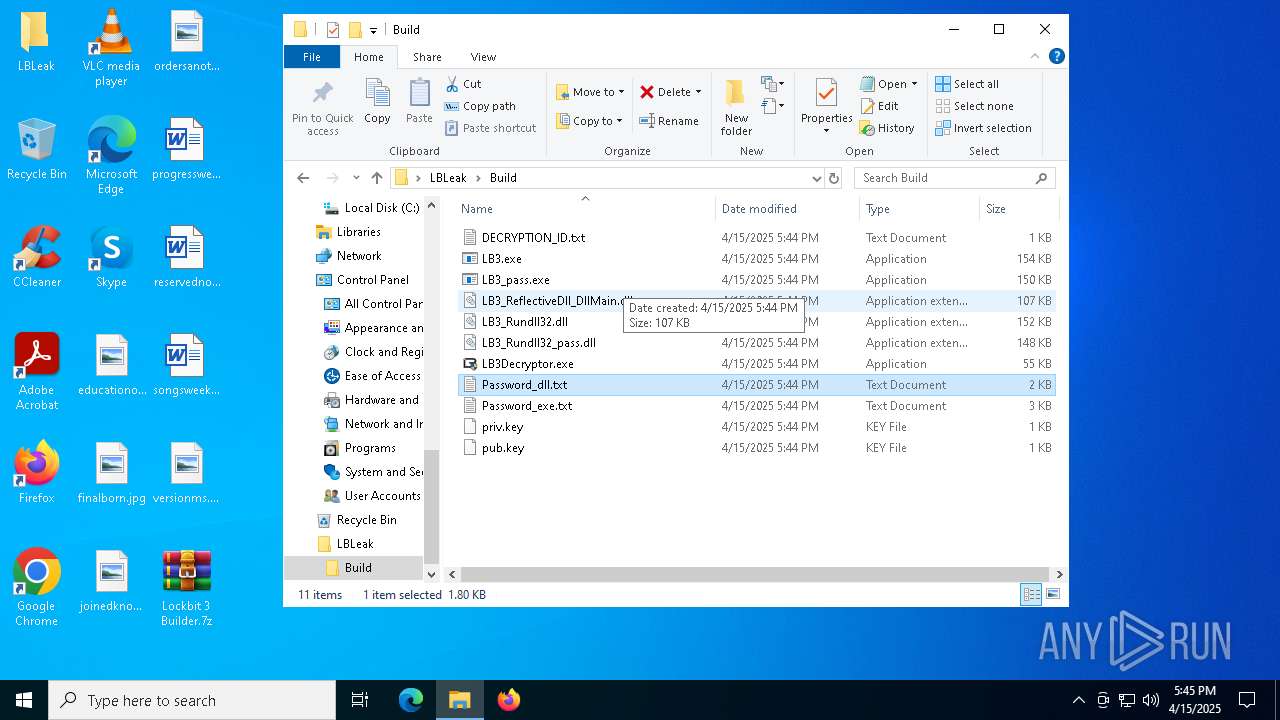
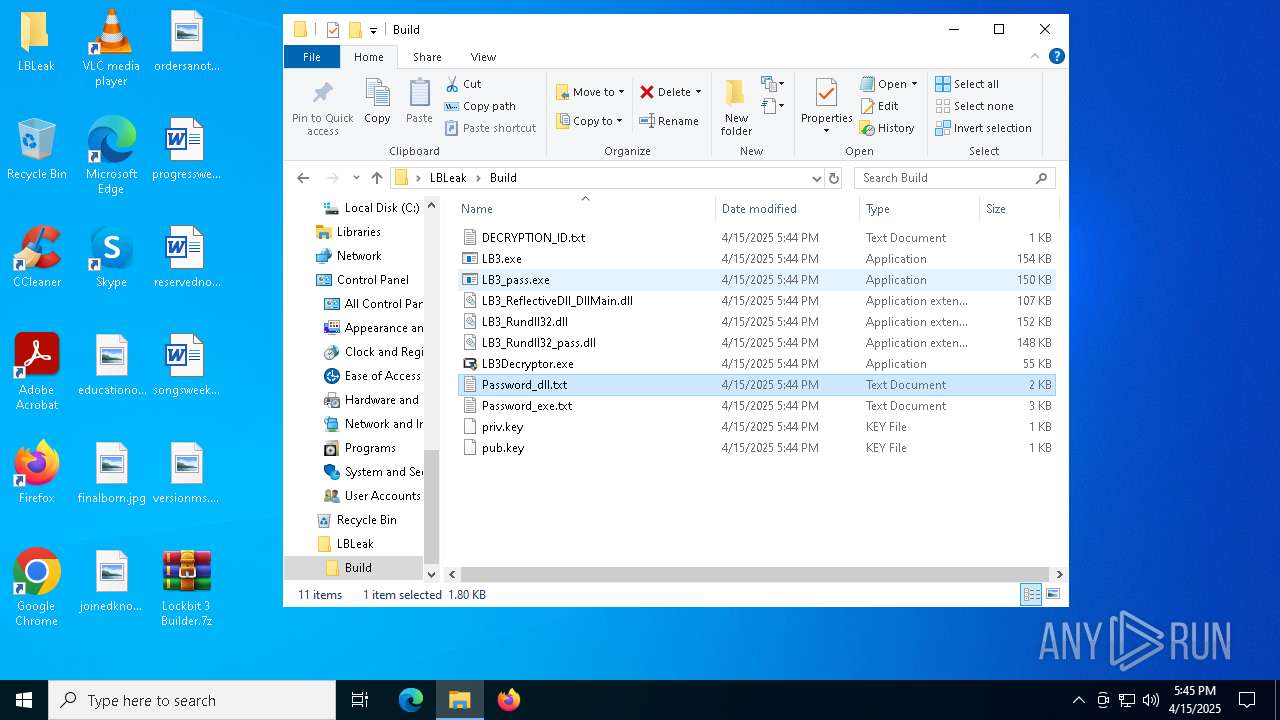
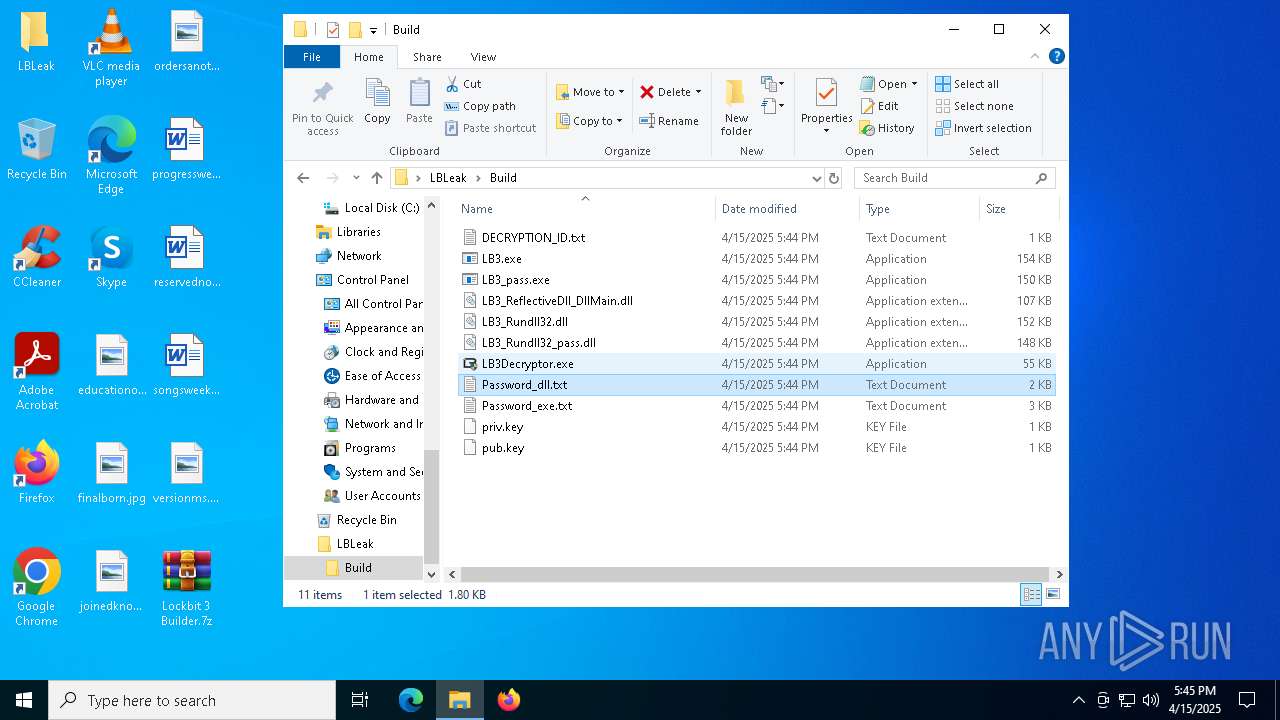
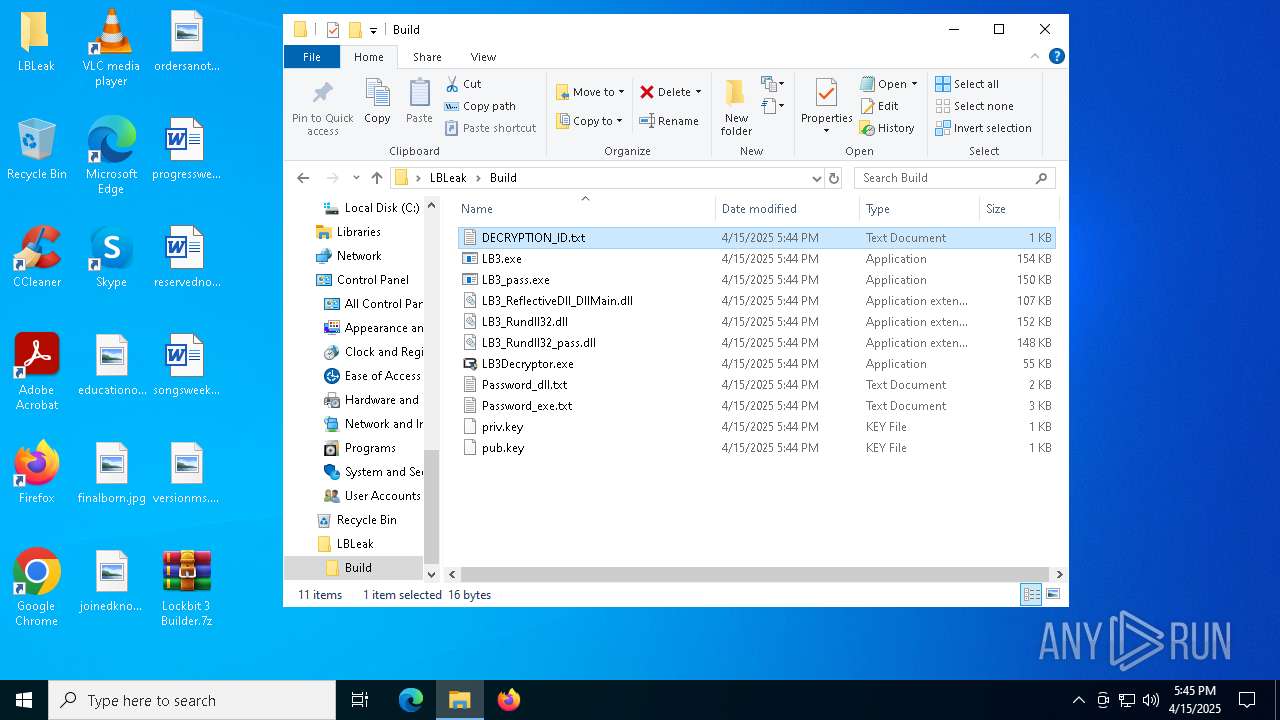
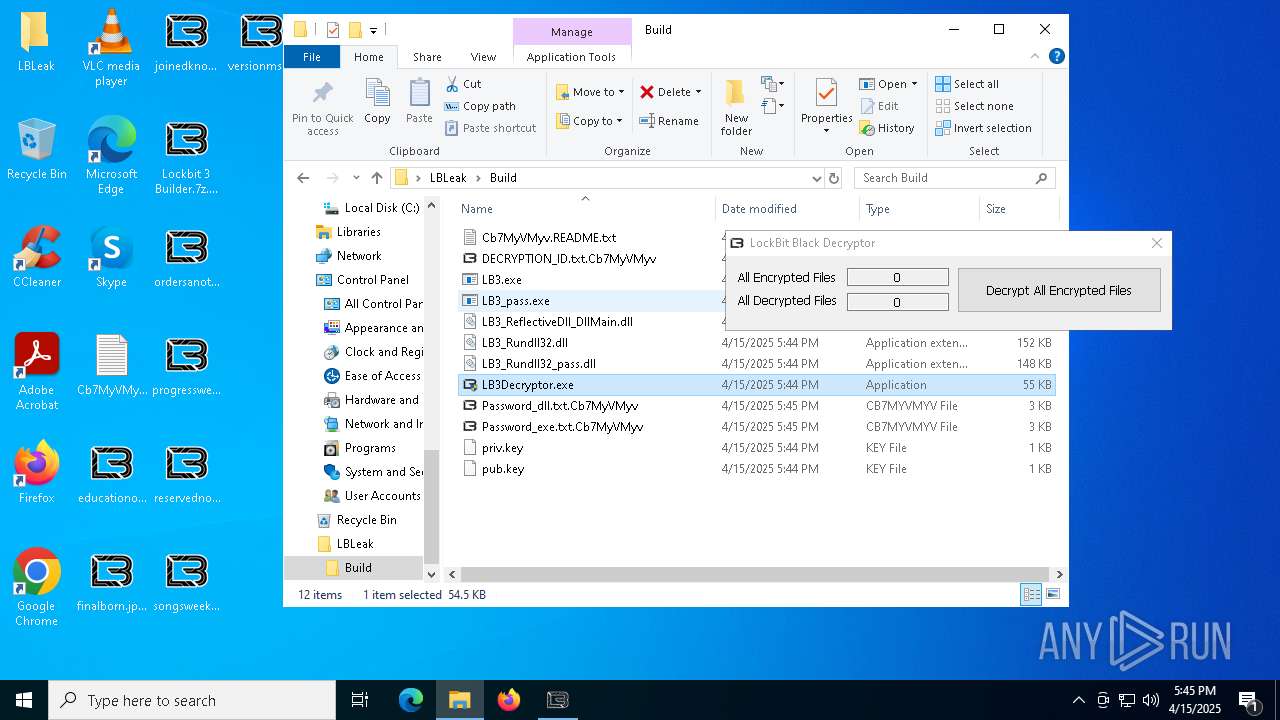
| 1184 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\LBLeak\Build\Password_dll.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
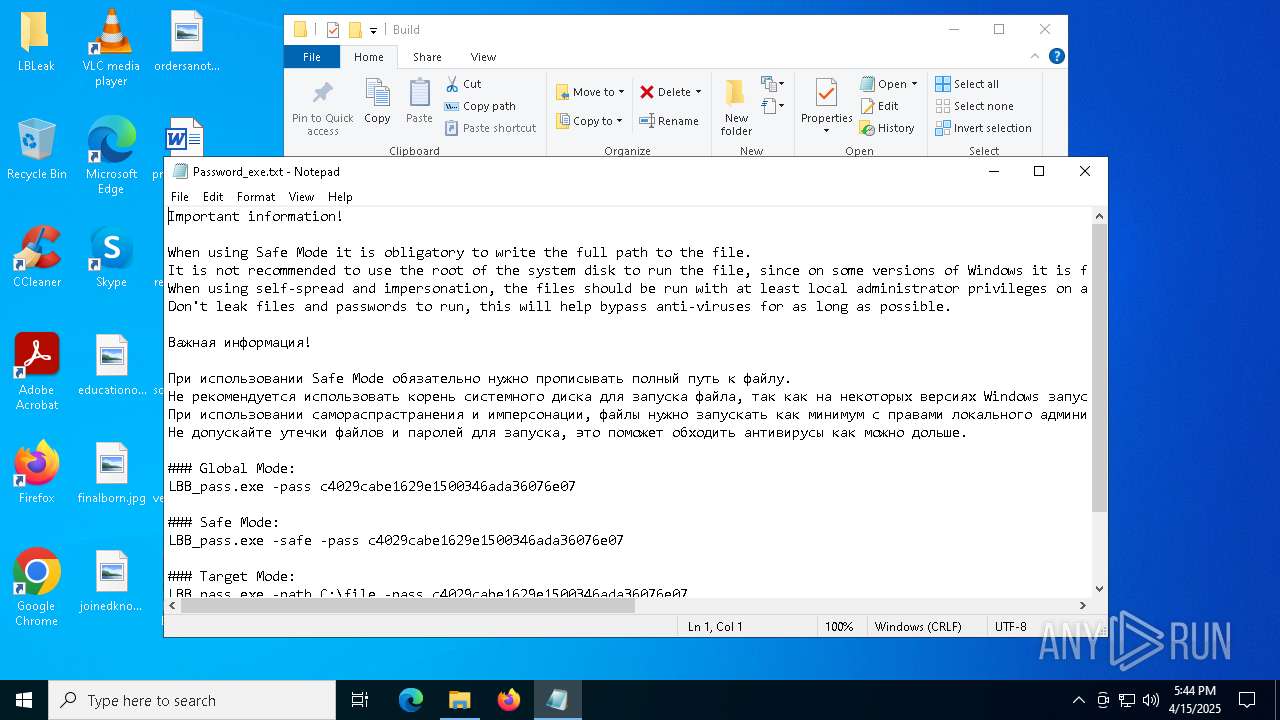
| 1660 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\LBLeak\Build\Password_exe.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
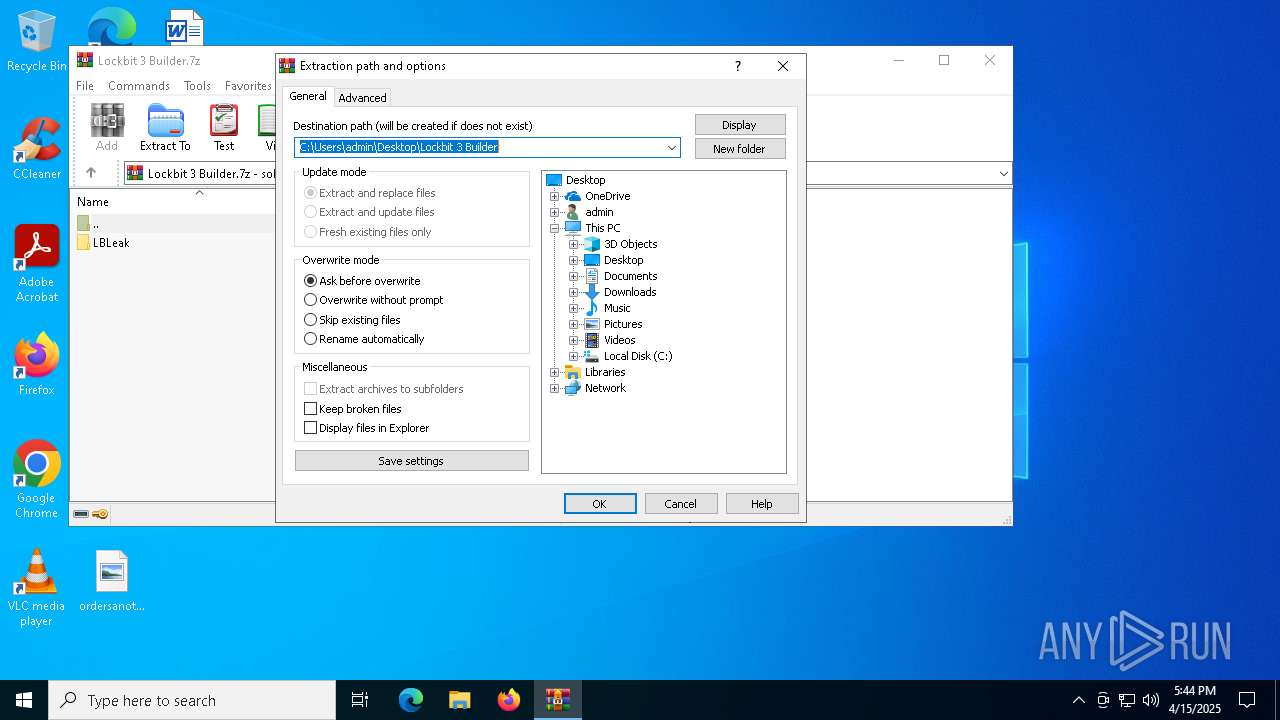
| 2140 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Lockbit 3 Builder.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2240 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
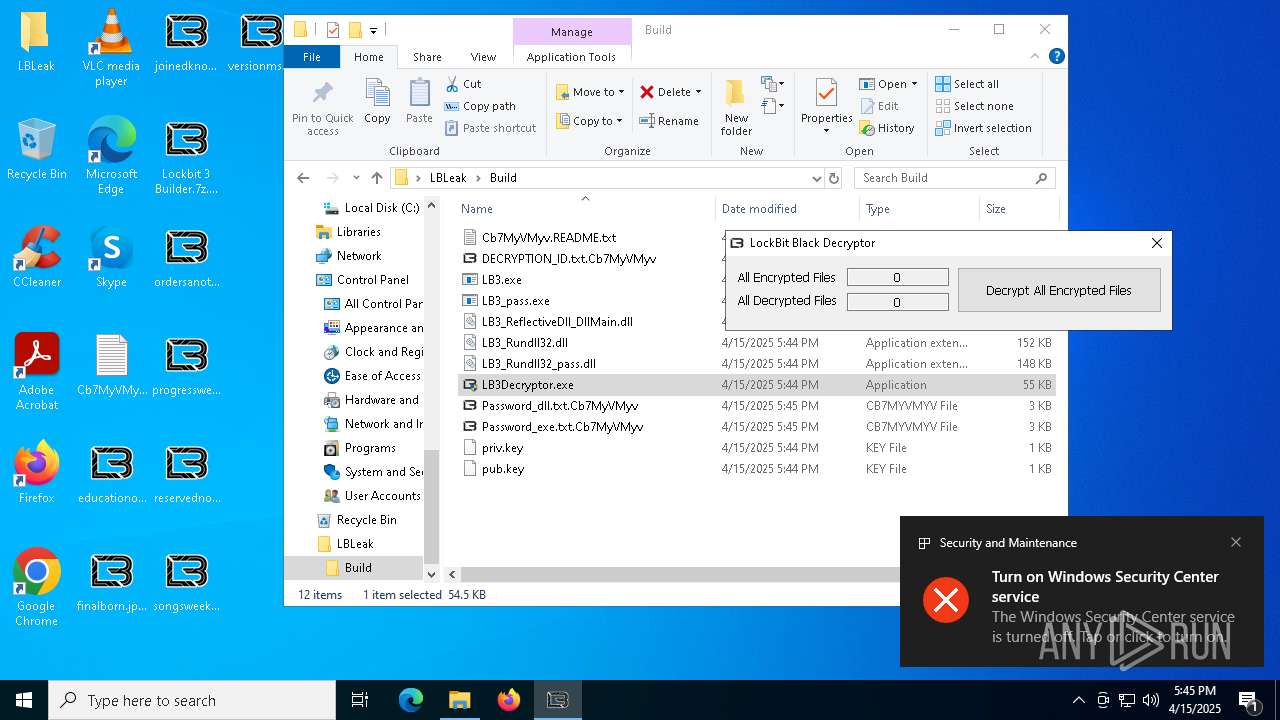
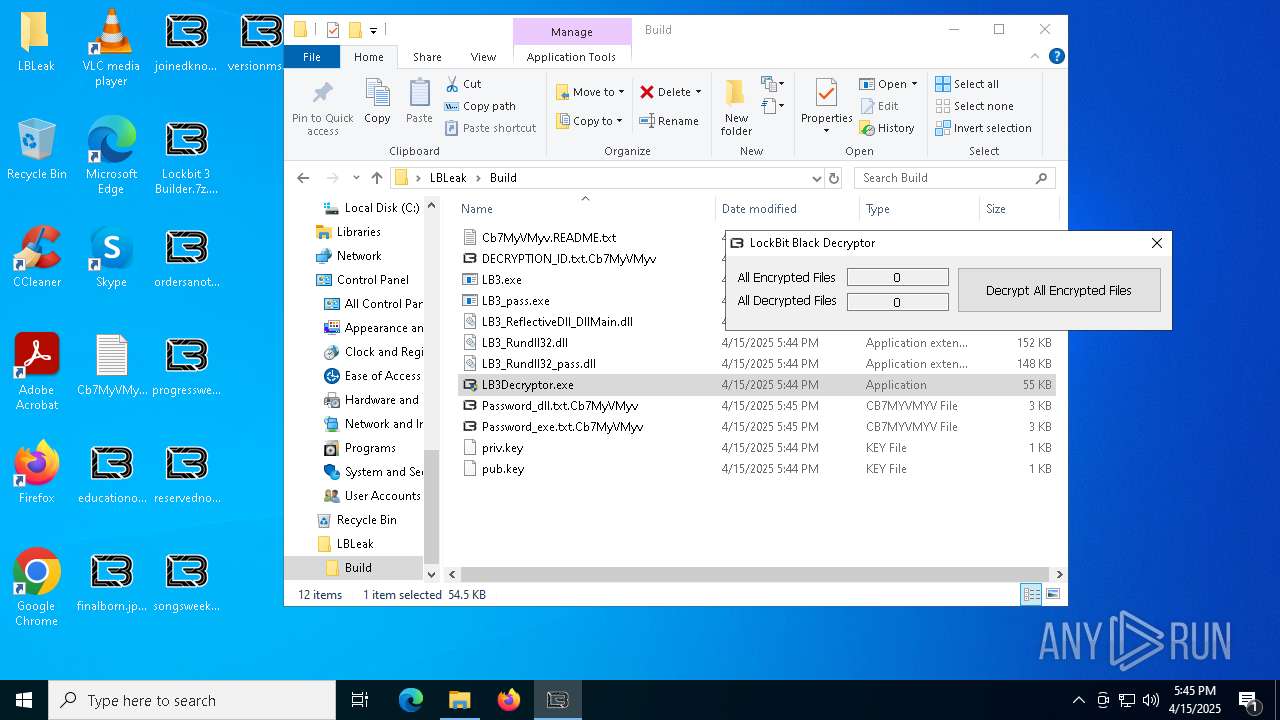
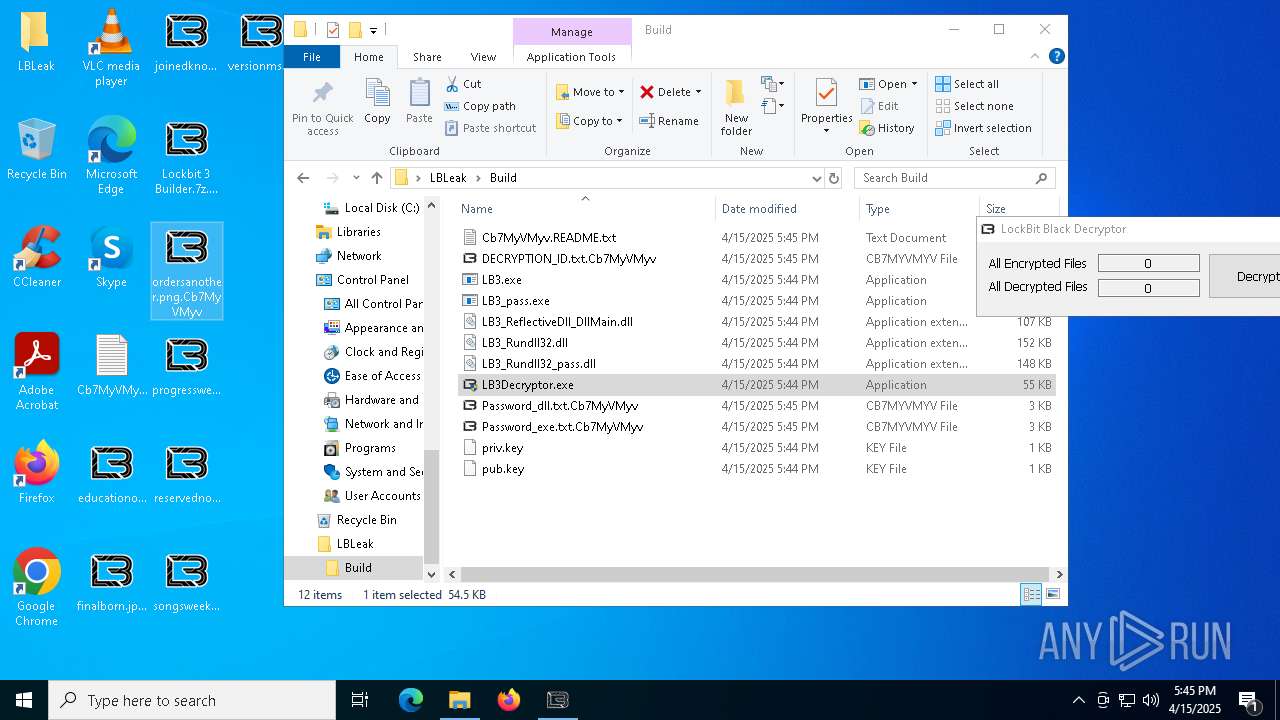
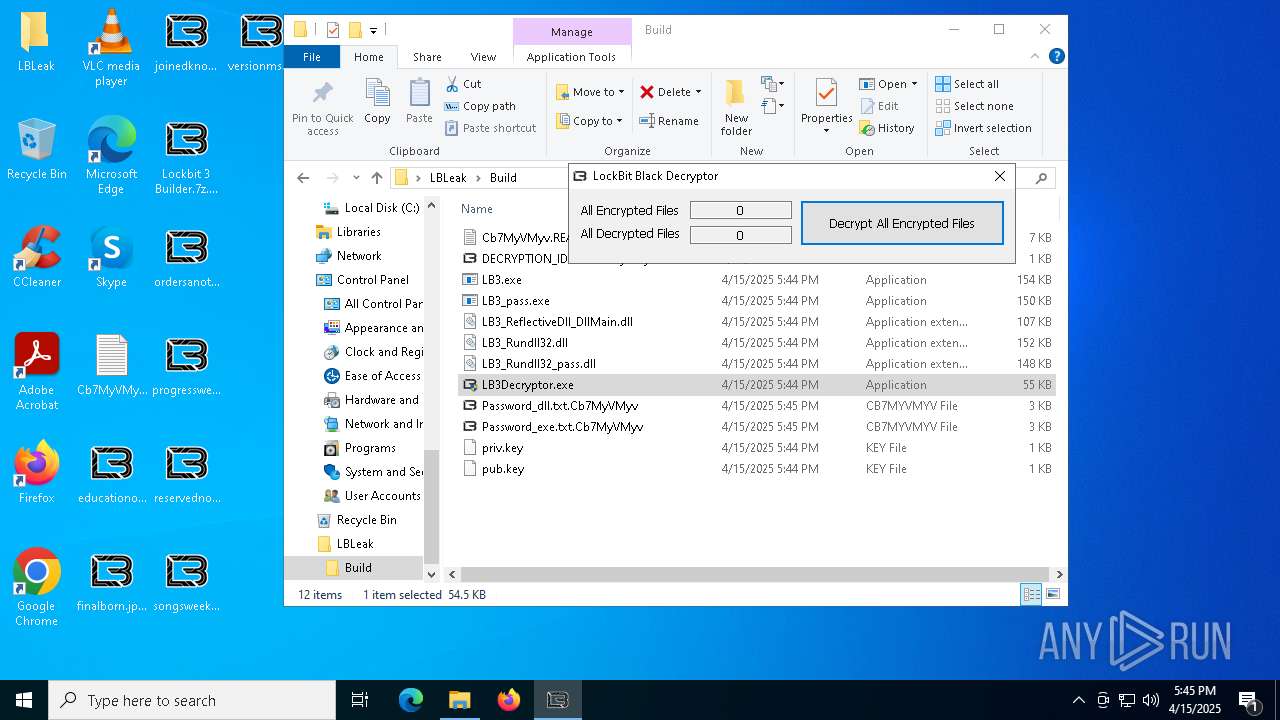
| 4652 | "C:\Users\admin\Desktop\LBLeak\Build\LB3Decryptor.exe" | C:\Users\admin\Desktop\LBLeak\Build\LB3Decryptor.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4944 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Cb7MyVMyv.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5376 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5608 | "C:\Users\admin\Desktop\LBLeak\Build\LB3.exe" | C:\Users\admin\Desktop\LBLeak\Build\LB3.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5756 | "C:\Users\admin\Desktop\LBLeak\Build\LB3Decryptor.exe" | C:\Users\admin\Desktop\LBLeak\Build\LB3Decryptor.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 5968 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 913
Read events
8 830
Write events
66
Delete events
17
Modification events
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Lockbit 3 Builder.7z | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2140) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
Executable files
21
Suspicious files
1 185
Text files
826
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | WinRAR.exe | C:\Users\admin\Desktop\LBLeak\Build.bat | text | |
MD5:4E46E28B2E61643F6AF70A8B19E5CB1F | SHA256:8E83A1727696CED618289F79674B97305D88BEEEABF46BD25FC77AC53C1AE339 | |||
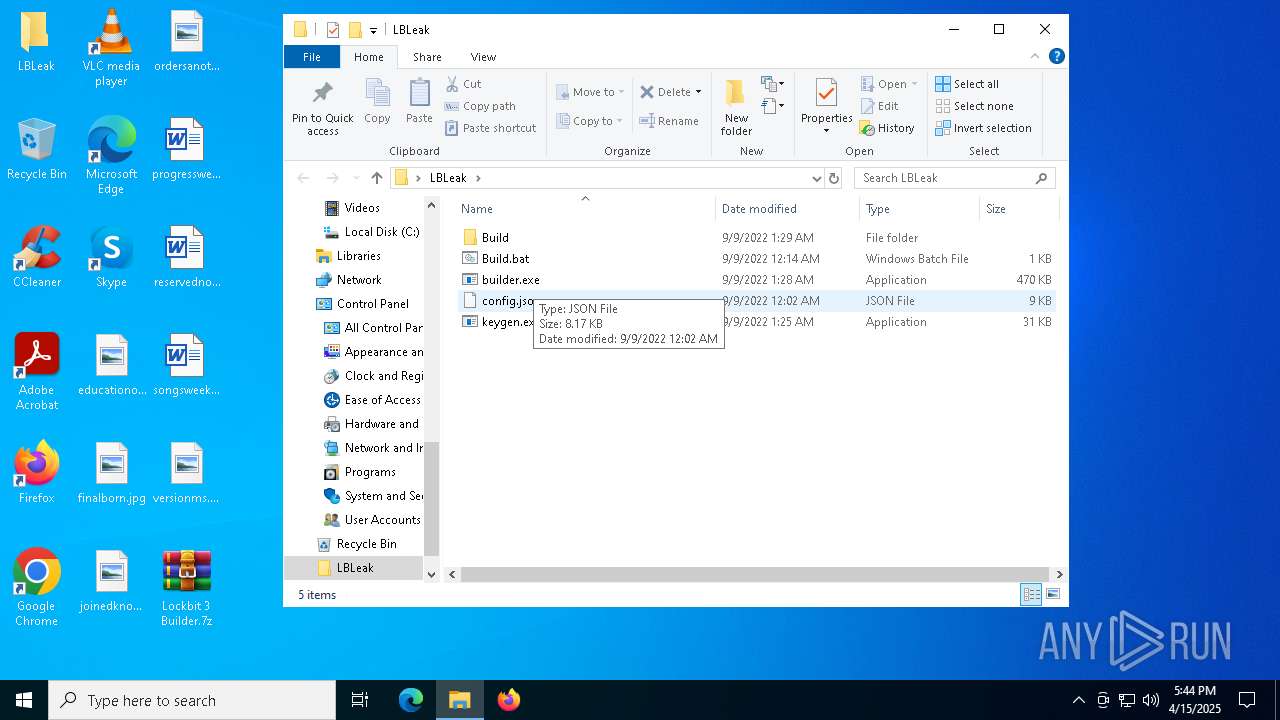
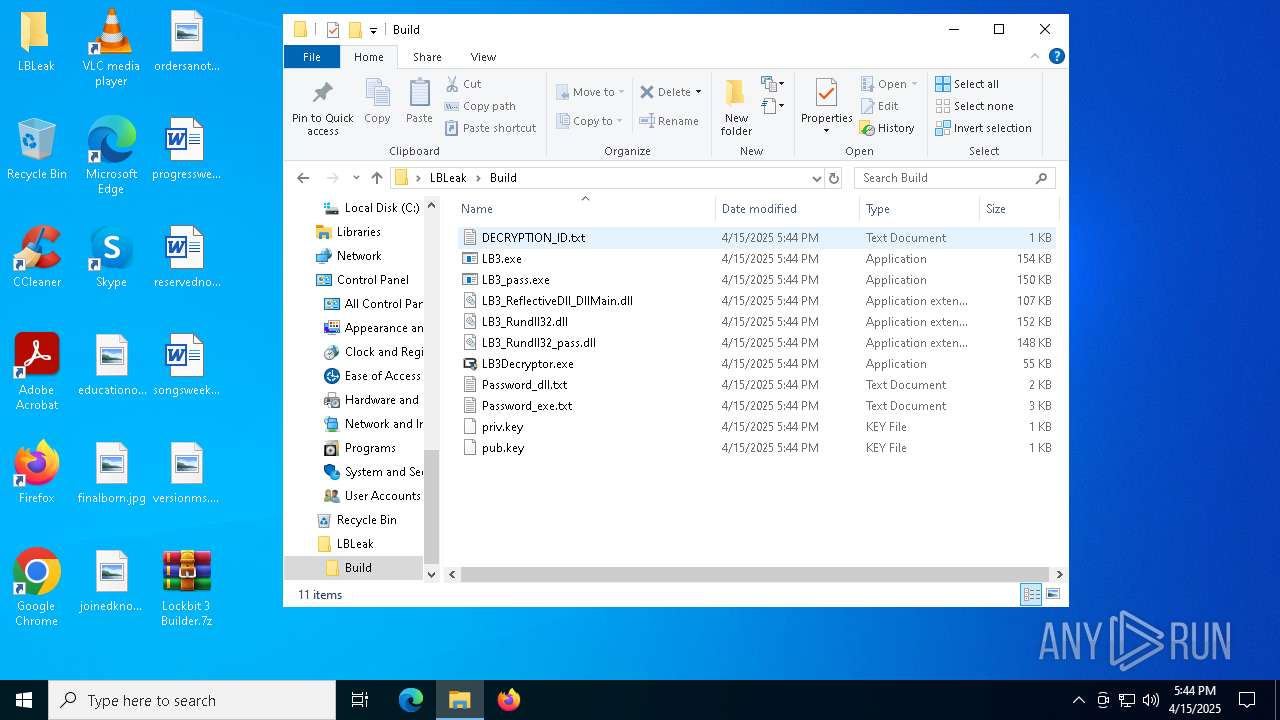
| 8024 | builder.exe | C:\Users\admin\Desktop\LBLeak\Build\Password_dll.txt | text | |
MD5:A5896F7601A261E8044EB26A9D9B5F39 | SHA256:98C71CD9B84434BC2244124D17C2E4155BEC791D31CA3F1BE42A1B1493719C1C | |||
| 7900 | keygen.exe | C:\Users\admin\Desktop\LBLeak\Build\priv.key | text | |
MD5:F7C0FDBEA29D43B9EA66DA4272AF7AC5 | SHA256:39CDEEB03E20EBF41DA1330D63B1279A6DA823AB7698B14616934E34E6410BD4 | |||
| 2140 | WinRAR.exe | C:\Users\admin\Desktop\LBLeak\builder.exe | executable | |
MD5:8C689DC9E82C9356B990D2B67B4943E1 | SHA256:E8E2DEB0A83AEBB1E2CC14846BC71715343372103F279D2D1622E383FB26D6EF | |||
| 7900 | keygen.exe | C:\Users\admin\Desktop\LBLeak\Build\pub.key | text | |
MD5:72A5CB4A959A902AABBBB57414C7D13A | SHA256:286D5D554DDDC78F365A41D09A95E3FC301AC1DC05E31AD3115E03DD82B0F78A | |||
| 2140 | WinRAR.exe | C:\Users\admin\Desktop\LBLeak\keygen.exe | executable | |
MD5:5E28C7C900E4DCE08366051C22F07F84 | SHA256:BB76F4D10EC2C1D24BE904D2EE078F34A6B5BD11F3B40F295E116FEA44824B89 | |||
| 7976 | builder.exe | C:\Users\admin\Desktop\LBLeak\Build\Password_exe.txt | text | |
MD5:2C04CB63FB00A6BF8852867B0CB0AB24 | SHA256:33CDCB8A386AA65A80A40C276A320C29534E3E18FE2FA1256DED6665349F1146 | |||
| 7928 | builder.exe | C:\Users\admin\Desktop\LBLeak\Build\LB3Decryptor.exe | executable | |
MD5:CB482777DACE01BD7F6D98D6F196C342 | SHA256:40ECA87B547E00CF9B6C1B97D10E4C98FE9B653E5EEE4DE0B46E2F501633EA3A | |||
| 7976 | builder.exe | C:\Users\admin\Desktop\LBLeak\Build\LB3_pass.exe | executable | |
MD5:29AFF0F29AD036AA18B5FE4E9ABF8B73 | SHA256:FF448525EF83641C21E694F1A0C2CCDF2E75F725AA97DD98E8BF5F921314F579 | |||
| 7204 | LB3.exe | C:\$Recycle.Bin\S-1-5-18\CCCCCCCCCCC | binary | |
MD5:71CA248BBB6BBC8F7234A6FDC8699380 | SHA256:1EE56D1A619166E2DB7D92E487526EAB52D6273B07E63AABE3F8CAFA42A94327 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
25
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.181:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8180 | SIHClient.exe | GET | 200 | 23.48.206.92:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.181:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7932 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8180 | SIHClient.exe | GET | 200 | 23.48.206.92:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.48.23.181:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.181:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |