| download: | 4V_2e |
| Full analysis: | https://app.any.run/tasks/f5cf5268-13ab-4ce0-bf5e-21b7abdd83e1 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 23, 2019, 14:01:47 |
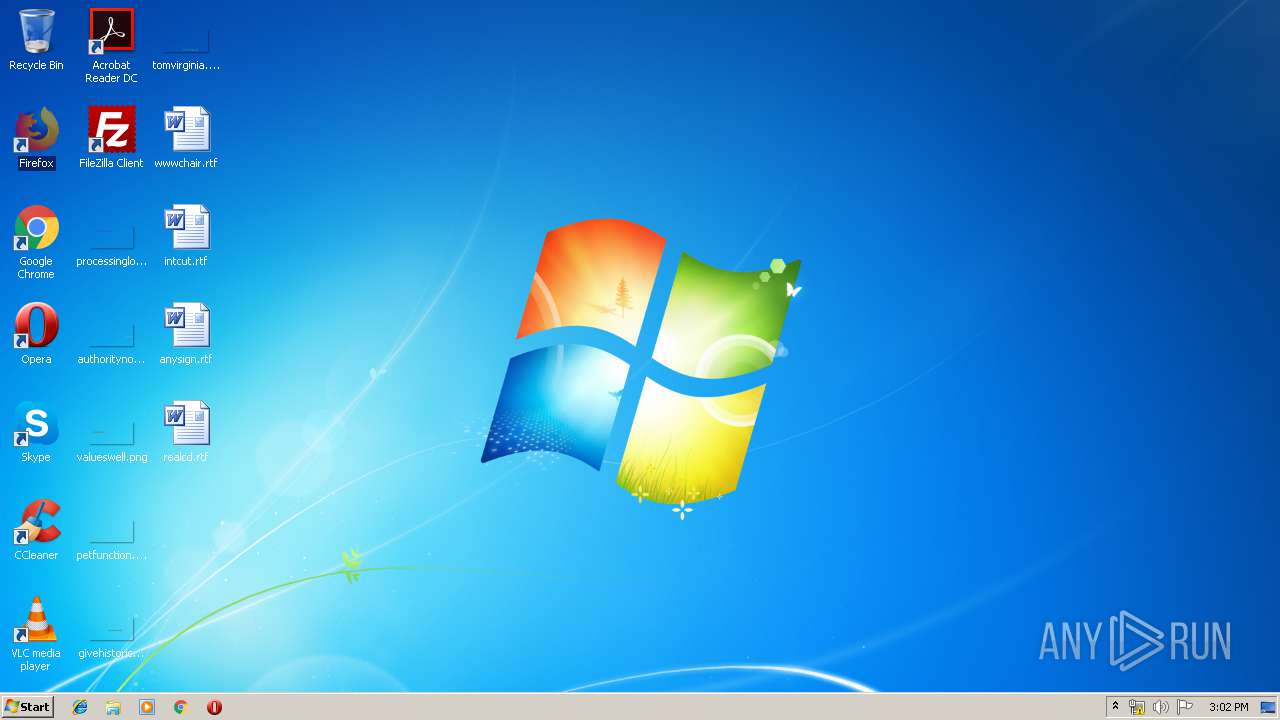
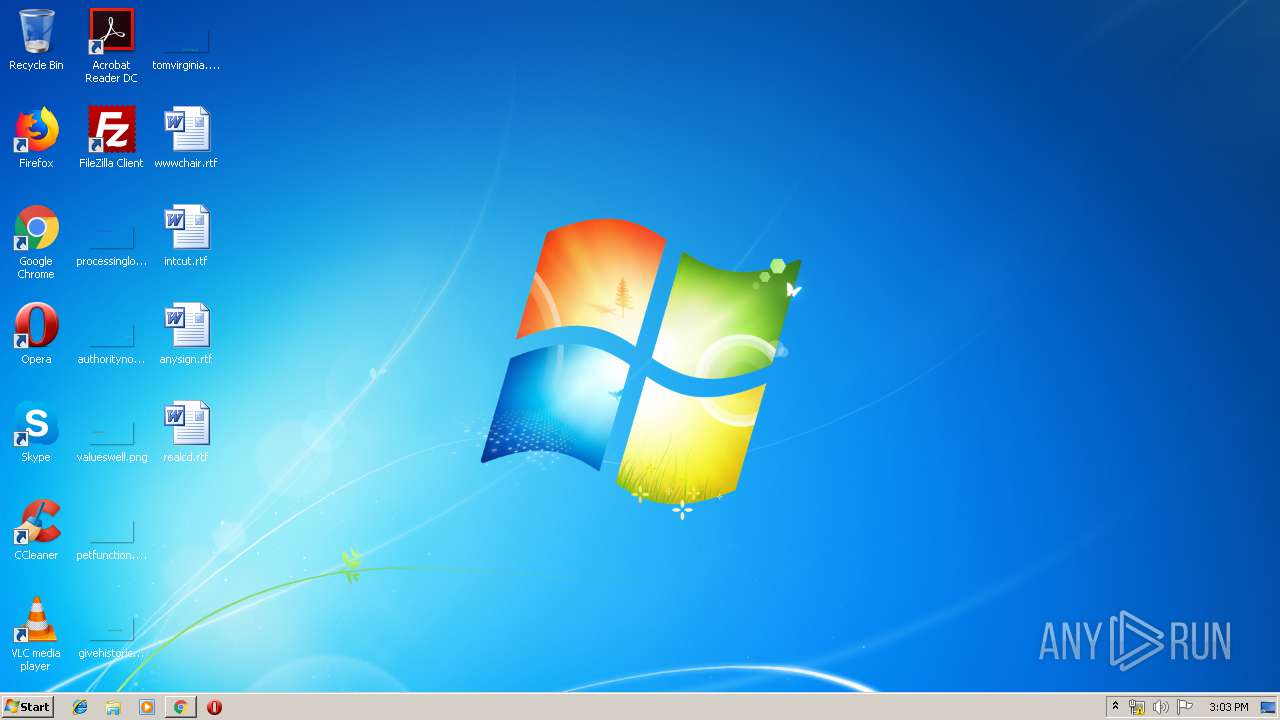
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0AD37153765933B373E0A55D54BB635A |
| SHA1: | 4B1505E788E1DA3587C40DF8D6C52B7C5307B2F0 |
| SHA256: | B2BCB7FE83FFB8606BA25C652C5DFA2B2CF0DC694AF39285546D44910B39F208 |
| SSDEEP: | 1536:tigHSpO94Ns7iBPD4VWJSobZLTzaIKzUAR4dGUArMf/NQKGVXlpRyN:MgHSpq4DBMVWJSotLKP7xMf1QKe |
MALICIOUS
Emotet process was detected
- soundser.exe (PID: 3628)
Changes the autorun value in the registry
- soundser.exe (PID: 996)
Connects to CnC server
- soundser.exe (PID: 996)
EMOTET was detected
- soundser.exe (PID: 996)
SUSPICIOUS
Starts itself from another location
- 4V_2e.exe (PID: 3284)
Connects to server without host name
- soundser.exe (PID: 996)
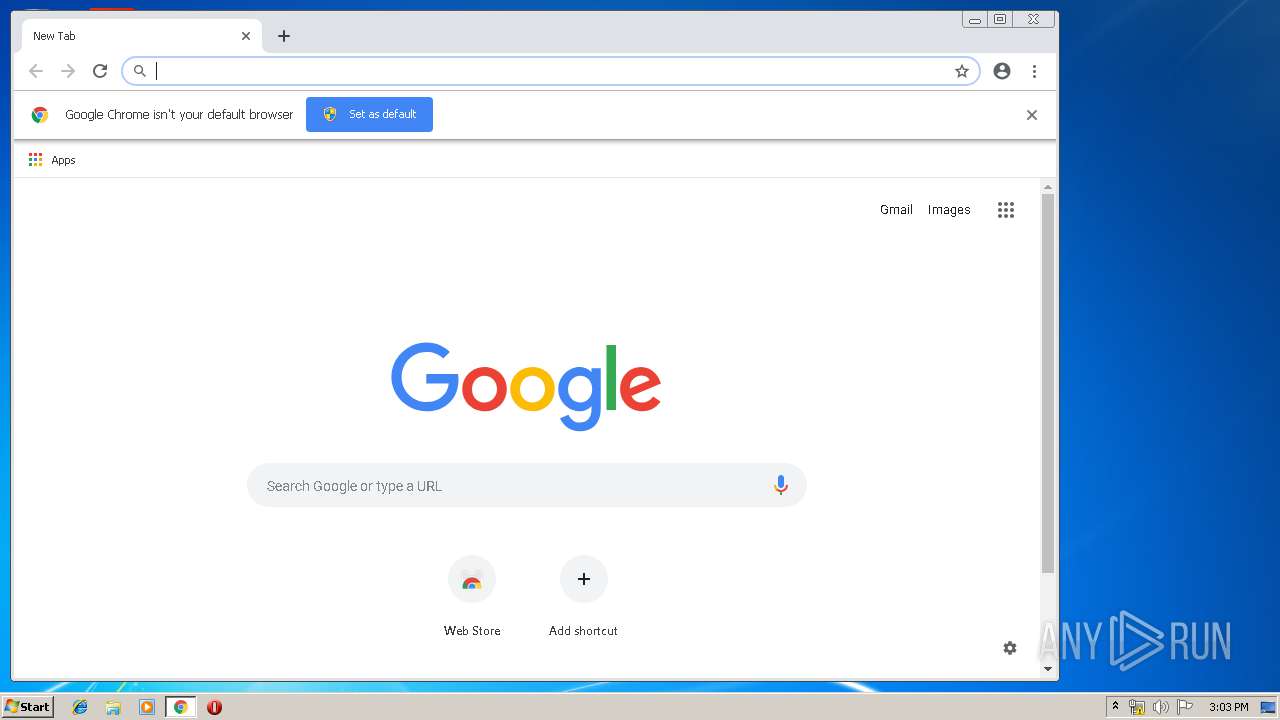
Modifies files in Chrome extension folder
- chrome.exe (PID: 2648)
Application launched itself
- 4V_2e.exe (PID: 2512)
Executable content was dropped or overwritten
- 4V_2e.exe (PID: 3284)
INFO
Application launched itself
- chrome.exe (PID: 2648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:04:09 00:07:12+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 13 |
| CodeSize: | 10240 |
| InitializedDataSize: | 68608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2608 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Apr-2014 22:07:12 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 2 |
| Time date stamp: | 08-Apr-2014 22:07:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00002750 | 0x00002800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.39743 |
.qwer | 0x00004000 | 0x00010B42 | 0x00010C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92061 |
Imports
advapi32.dll |
authz.dll |
certcli.dll |
kernel32.dll |
resutils.dll |
shell32.dll |
user32.dll |
wtsapi32.dll |
Total processes
52
Monitored processes
22
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,2580363239148065799,10114080540320418218,131072 --enable-features=PasswordImport --service-pipe-token=3327067884244075623 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3327067884244075623 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,2580363239148065799,10114080540320418218,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8053542095998908417 --mojo-platform-channel-handle=4312 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 996 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,2580363239148065799,10114080540320418218,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4994218346481065713 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4994218346481065713 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3772 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,2580363239148065799,10114080540320418218,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17108678860387104429 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17108678860387104429 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2616 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=952,2580363239148065799,10114080540320418218,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3479885919090967897 --mojo-platform-channel-handle=4572 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2920 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2512 | "C:\Users\admin\AppData\Local\Temp\4V_2e.exe" | C:\Users\admin\AppData\Local\Temp\4V_2e.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,2580363239148065799,10114080540320418218,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1135824463237960189 --mojo-platform-channel-handle=2672 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
624
Read events
518
Write events
101
Delete events
5
Modification events
| (PID) Process: | (996) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (996) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (996) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (996) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (996) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (996) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (996) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (996) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (996) soundser.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (996) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
57
Text files
143
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0dea1a06-60d1-4497-ba4f-8345f55c48eb.tmp | — | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
16
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
996 | soundser.exe | POST | — | 70.116.68.186:80 | http://70.116.68.186/enabled/teapot/ringin/ | US | — | — | malicious |
2648 | chrome.exe | GET | 200 | 194.9.25.78:80 | http://r3---sn-5uh5o-f5fs.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.219.109&mm=28&mn=sn-5uh5o-f5fs&ms=nvh&mt=1556027688&mv=u&pl=24&shardbypass=yes | PL | crx | 842 Kb | whitelisted |
996 | soundser.exe | POST | — | 68.229.130.39:80 | http://68.229.130.39/entries/enable/ringin/merge/ | US | — | — | malicious |
996 | soundser.exe | POST | 200 | 190.112.228.47:443 | http://190.112.228.47:443/iab/entries/ringin/merge/ | CW | binary | 132 b | malicious |
2648 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 508 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2648 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.78:80 | — | Google Inc. | US | whitelisted |
996 | soundser.exe | 68.229.130.39:80 | — | Cox Communications Inc. | US | malicious |
2648 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 216.58.208.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2648 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 216.58.206.14:443 | apis.google.com | Google Inc. | US | whitelisted |
996 | soundser.exe | 70.116.68.186:80 | — | Time Warner Cable Internet LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.pl |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
996 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
996 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
996 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
996 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
9 ETPRO signatures available at the full report