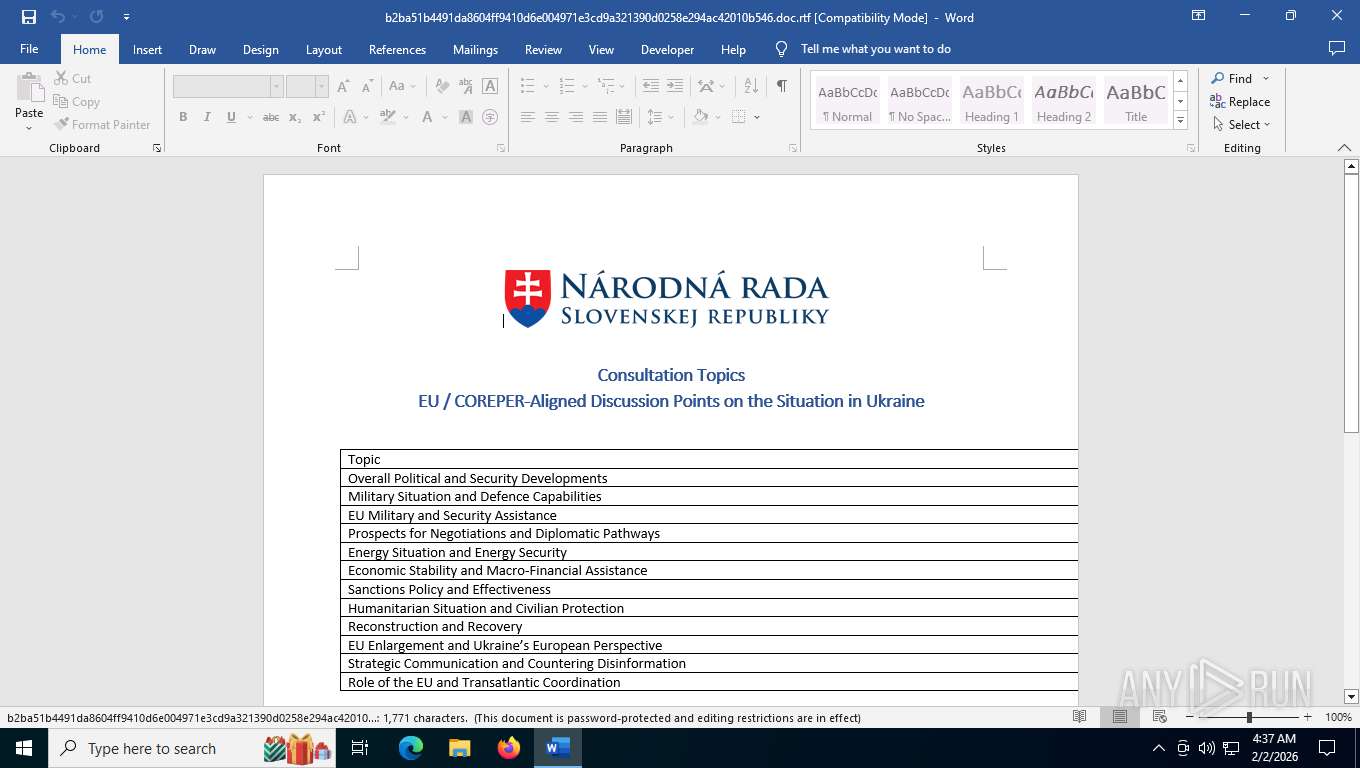
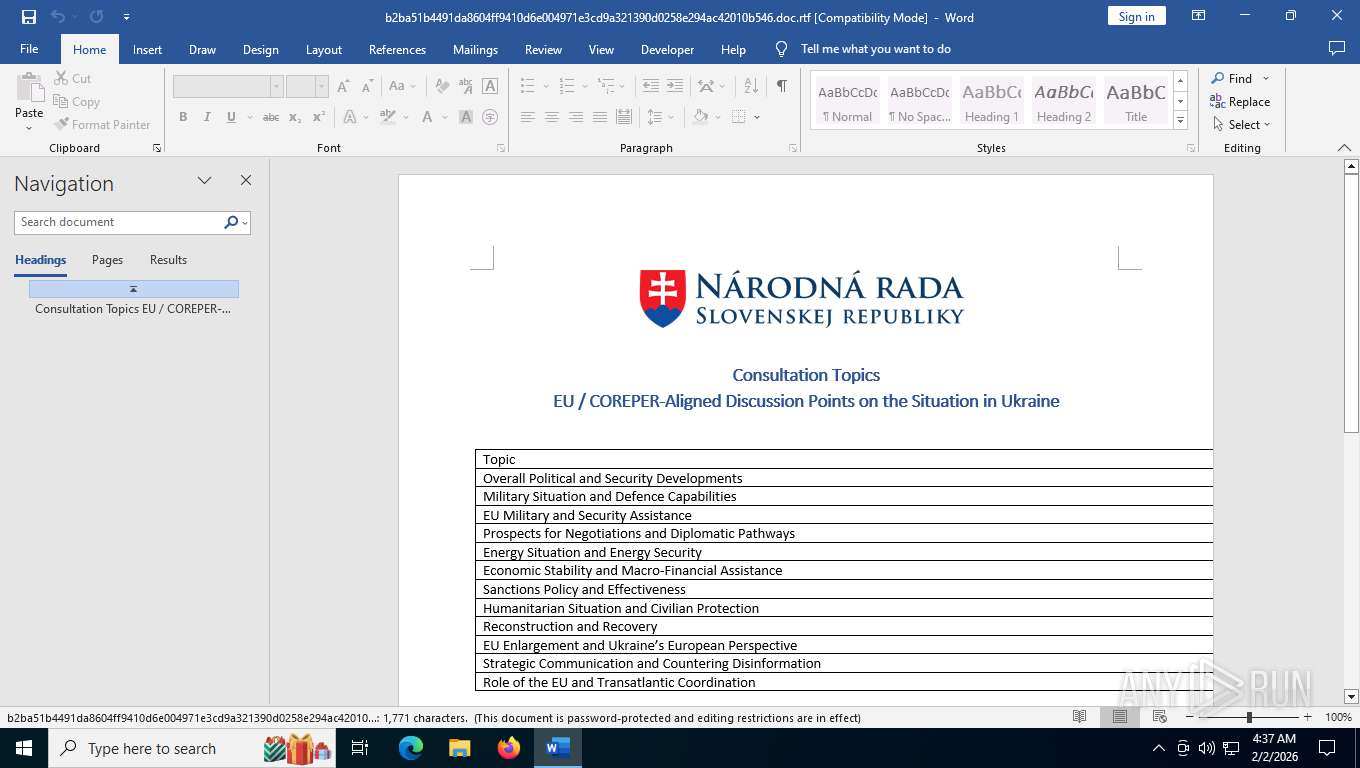
| File name: | b2ba51b4491da8604ff9410d6e004971e3cd9a321390d0258e294ac42010b546.doc |
| Full analysis: | https://app.any.run/tasks/4c60bb56-3316-4404-a383-db100f0fa8e2 |
| Verdict: | Malicious activity |
| Analysis date: | February 02, 2026, 09:37:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, ANSI, code page 1252, default middle east language ID 1025 |
| MD5: | 95E59536455A089CED64F5AF2539A449 |
| SHA1: | 4592E6173A643699DC526778AA0A30330D16FE08 |
| SHA256: | B2BA51B4491DA8604FF9410D6E004971E3CD9A321390D0258E294AC42010B546 |
| SSDEEP: | 6144:fm1rI2QHBJLHY1cMNkei0evKSgWH8940PYM30+FzW4CUCkXdwUo05bM7I:fC2L41cMHeK/l27I |
MALICIOUS
WebDav connection (SURICATA)
- WINWORD.EXE (PID: 4128)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 8640)
Abuses WebDav for code execution
- svchost.exe (PID: 8640)
Potential Corporate Privacy Violation
- WINWORD.EXE (PID: 4128)
INFO
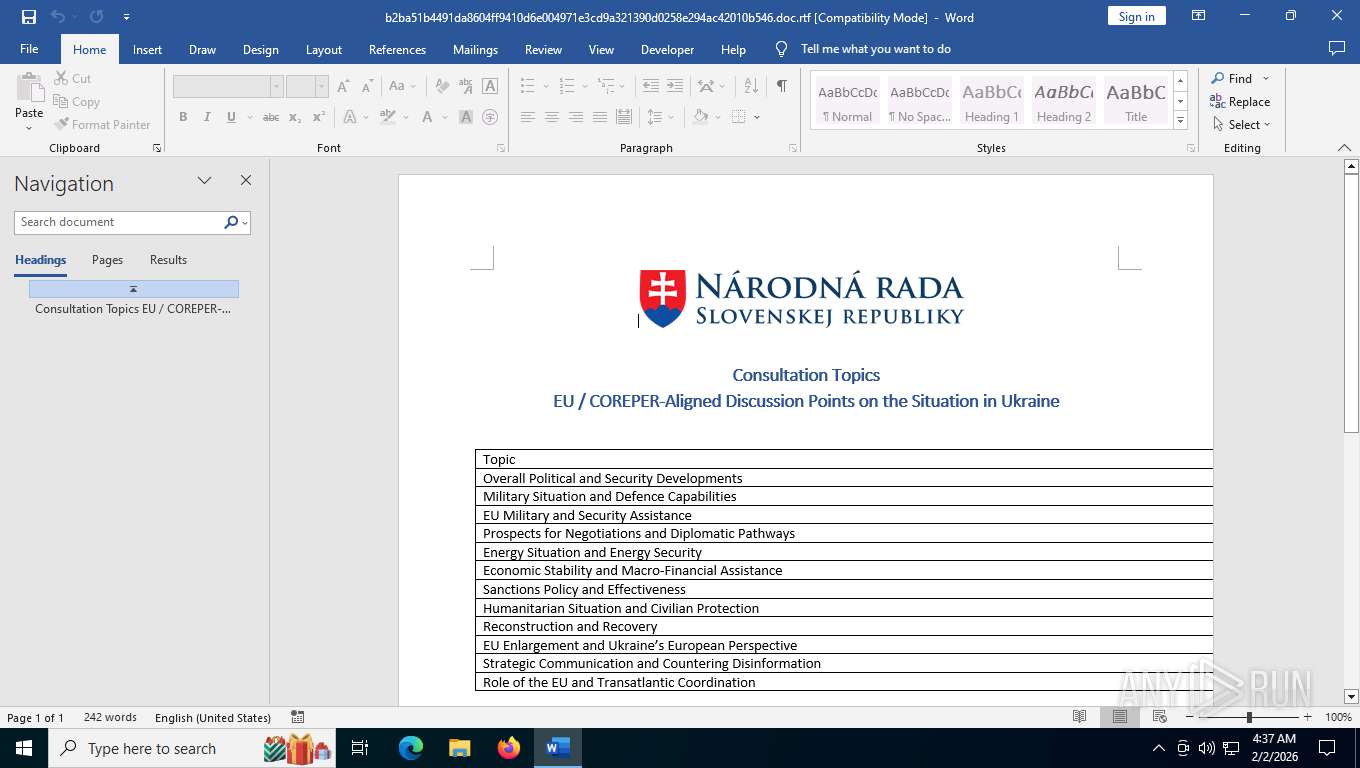
An automatically generated document
- WINWORD.EXE (PID: 4128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
| Author: | Administrator |
|---|---|
| LastModifiedBy: | Administrator |
| CreateDate: | 2026:01:27 07:43:00 |
| ModifyDate: | 2026:01:27 07:43:00 |
| RevisionNumber: | 2 |
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | 300 |
| Characters: | 1711 |
| CharactersWithSpaces: | 2007 |
| InternalVersionNumber: | 31 |
Total processes
159
Monitored processes
4
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4128 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n C:\Users\admin\AppData\Local\Temp\b2ba51b4491da8604ff9410d6e004971e3cd9a321390d0258e294ac42010b546.doc.rtf /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 4756 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "25740BCD-DE14-4435-A67A-B4AAE9F96FD8" "B55BE6CE-E11C-4ACB-9F8A-11A439BED480" "4128" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 8640 | C:\WINDOWS\system32\svchost.exe -k LocalService -p -s WebClient | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8672 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 535
Read events
15 203
Write events
309
Delete events
23
Modification events
| (PID) Process: | (4128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\WINWORD\4128 |
| Operation: | write | Name: | 0 |
Value: 0B0E10CD69071D997FA940A4649B93C0FD7F232300469E8BDAD7F884A5EE016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511A020D2120B770069006E0077006F00720064002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (4128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (4128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (4128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (4128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (4128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (4128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (4128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (4128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
| (PID) Process: | (4128) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ru-ru |
Value: 2 | |||
Executable files
34
Suspicious files
126
Text files
20
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4128 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:92A8CC37DF3070AC6CD9DBD619409B56 | SHA256:220C7BB12DCD8453502E75749922CC50700E040CCF6022B10C4C5CB675FAA463 | |||
| 4128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:45D5BB9769B7E43BDEC14B72FD7C6335 | SHA256:C86F75D920D3F98FB88BAFE1D408B805AD0608864FC37D9001A5CFB515B1CE9C | |||
| 4128 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\WindowsUpdateDiagnostic.xml.LNK | binary | |
MD5:643A52F1CDDD2BBFA473B1F6DF201B0A | SHA256:B40B947D90ED0ED33879EA5ECBFAA9063A13BA263E860A0FC02A48C401F81BE4 | |||
| 4128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\51963639.wmf | binary | |
MD5:B5AFE00FF6D785307B8BBA2DDEE7F252 | SHA256:B7E16FCF3DB4EF95606B73CEEC8DD155930818B80C827E1155207BC07D1F7748 | |||
| 4128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 4128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\535B5F85-CCC7-4534-A6BA-1939F2B04EF9 | xml | |
MD5:69865E31A15A8CE9F87D33390AC6B9ED | SHA256:9178AB251327A21E91B46B4A36168462ABAFC9E11616AFB4268CF05C7BC7D25C | |||
| 4128 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:19D36C9C242655D0B8BF52574DCD2C58 | SHA256:FC5DD8083C5FDE2D120C57FDFF5A3561402ECFFE66913B7B9992D14605DAE0E5 | |||
| 4128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ba51b4491da8604ff9410d6e004971e3cd9a321390d0258e294ac42010b546.doc.rtf | binary | |
MD5:0CA618AB7399B8747EB0BB03E96C6149 | SHA256:1A53208D326F68D3412C2FEC553CB97C405F839867195BBDDEE37C18ABF57439 | |||
| 4128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:ACAC7A3E8D27B4B4F1C2F512BC9BD894 | SHA256:54B5ECCB0DE29552C5BA2C4BE3BF5C6F194544A8EEC3DFF8D5FC1344229C997E | |||
| 4128 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:6BF0A328609C79416AE5203BC62B719A | SHA256:7485263CF3893E8769E655ABEB8042CE91600A6F6C495C64E1B091CF0262AB3D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
149
TCP/UDP connections
82
DNS requests
32
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4128 | WINWORD.EXE | GET | 200 | 52.109.32.97:443 | https://officeclient.microsoft.com/config16/?lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3 | US | xml | 128 Kb | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
4128 | WINWORD.EXE | GET | 200 | 2.16.168.119:443 | https://omex.cdn.office.net/addinclassifier/officesharedentities | NL | text | 128 Kb | whitelisted |
4128 | WINWORD.EXE | OPTIONS | 308 | 159.253.120.2:80 | http://freefoodaid.com/ | MD | html | 234 b | unknown |
8640 | svchost.exe | OPTIONS | 308 | 159.253.120.2:80 | http://freefoodaid.com/ | MD | html | 234 b | unknown |
4128 | WINWORD.EXE | OPTIONS | 403 | 159.253.120.2:443 | https://freefoodaid.com/ | MD | html | 199 b | unknown |
8640 | svchost.exe | OPTIONS | 403 | 159.253.120.2:443 | https://freefoodaid.com/ | MD | html | 199 b | unknown |
6768 | MoUsoCoreWorker.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
8640 | svchost.exe | OPTIONS | 403 | 159.253.120.2:443 | https://freefoodaid.com/ | MD | html | 199 b | unknown |
7004 | svchost.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7004 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5524 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.20.142.136:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4128 | WINWORD.EXE | 52.109.32.97:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4128 | WINWORD.EXE | 52.123.129.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
roaming.svc.cloud.microsoft |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4128 | WINWORD.EXE | Potential Corporate Privacy Violation | POLICY [ANY.RUN] WebDav activity has been detected |
4128 | WINWORD.EXE | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 28 |
4128 | WINWORD.EXE | Potential Corporate Privacy Violation | POLICY [ANY.RUN] WebDav activity has been detected |
7004 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|