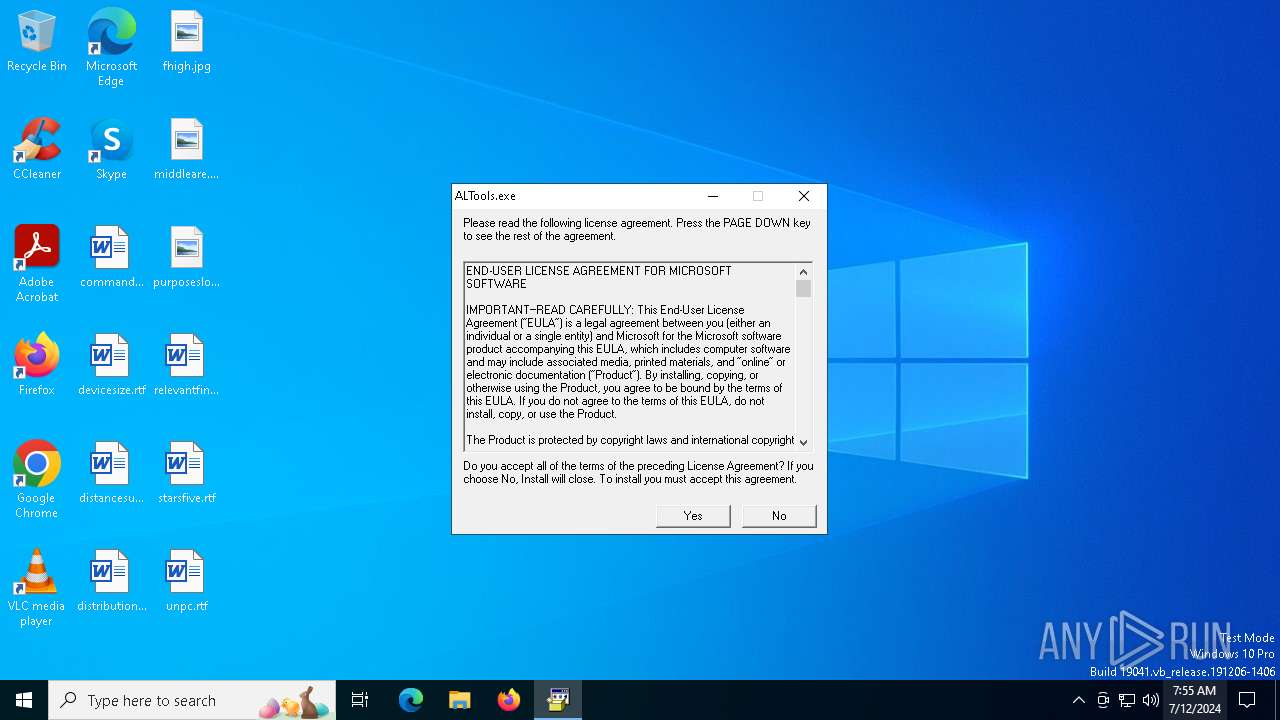
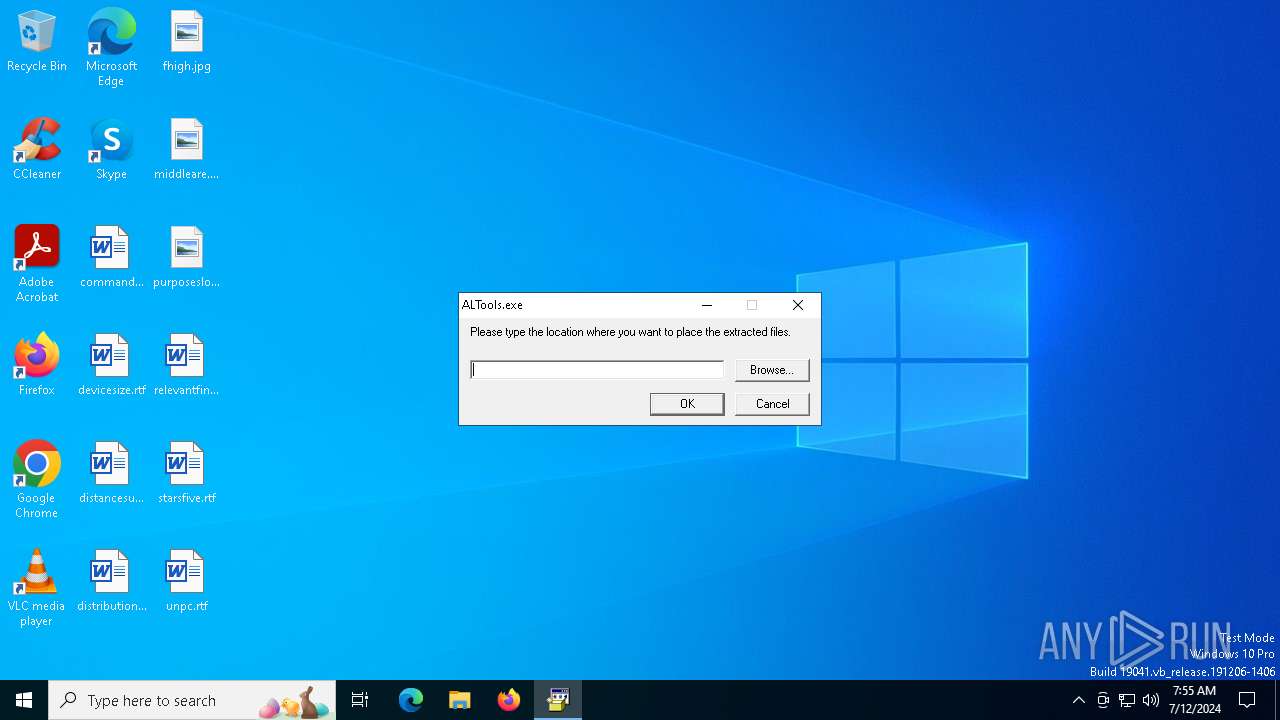
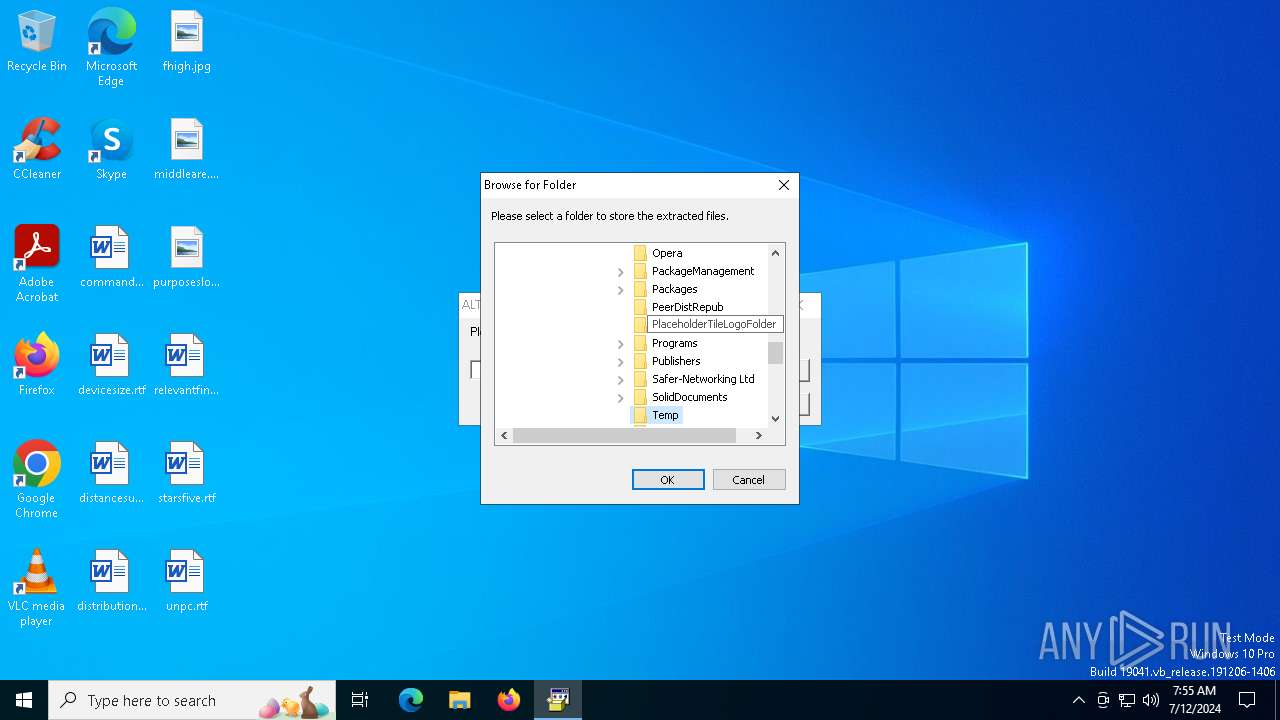
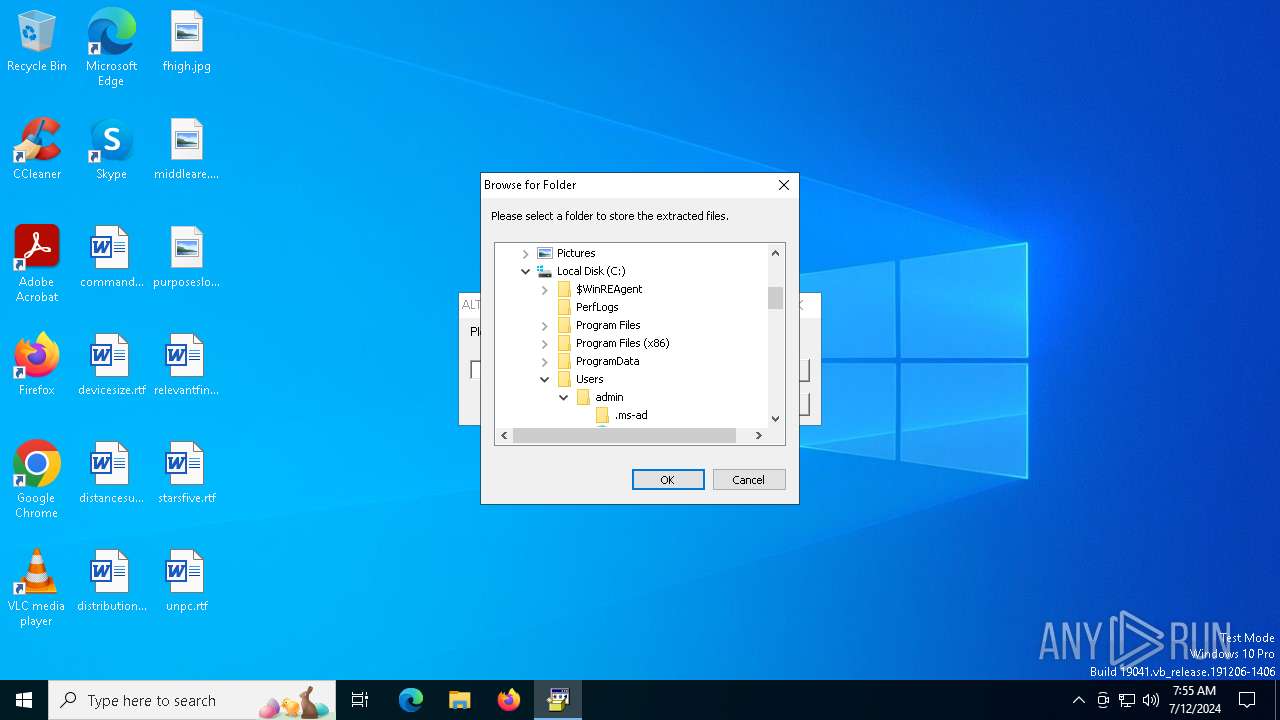
| File name: | ALTools.exe |
| Full analysis: | https://app.any.run/tasks/a9836aeb-9df6-4387-8091-addc89fdda8c |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2024, 07:54:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, MS CAB-Installer self-extracting archive |
| MD5: | 8758B8FAB32B20113E8B4C7F93F1D359 |
| SHA1: | 3A3B0D7FC1F166C496C8072C17EBAAFE1F382D1F |
| SHA256: | B2B439713B9B50F447E07DDBE7A3462F7BC129E8E1E1B49C4352A7C396912381 |
| SSDEEP: | 24576:YxfiB4wpRsztiAKrc8IarzGjofj41vpqy9BsgbHJOemcb2MAAqm75+u5nIZTBBOD:YxfiB4wpRszti9rc8IarzGcfj41vpqyp |
MALICIOUS
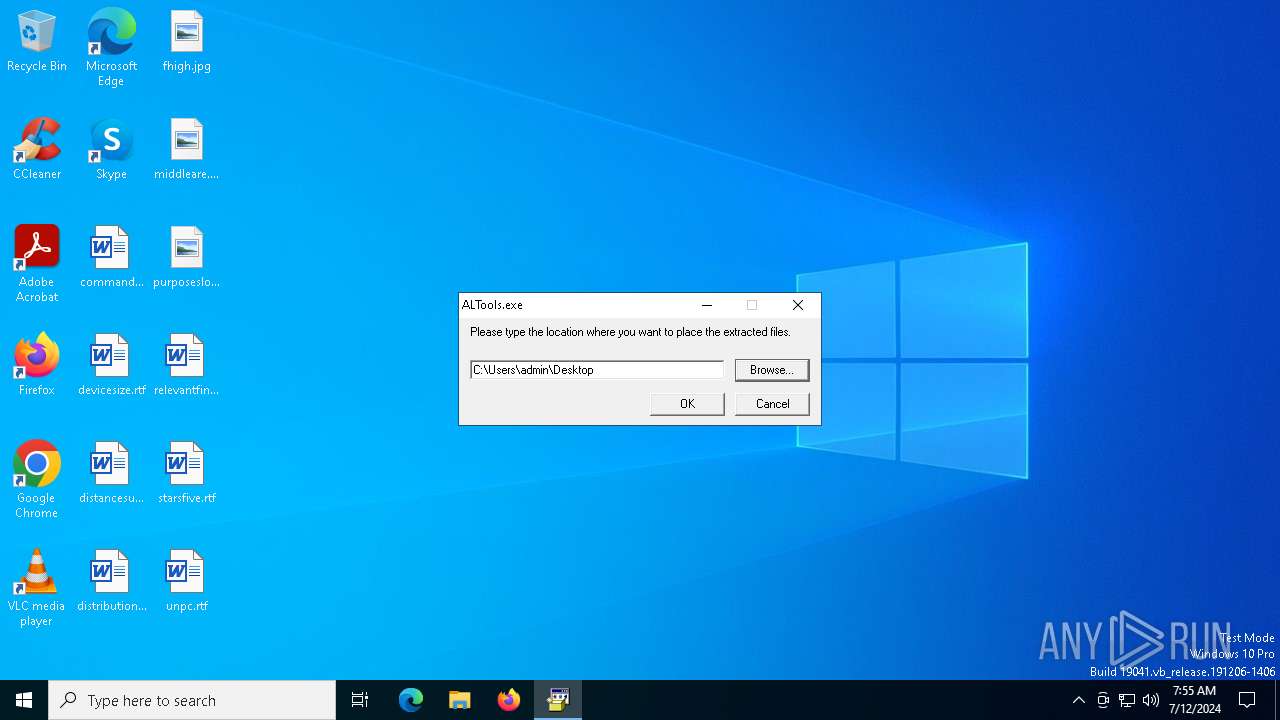
Drops the executable file immediately after the start
- ALTools.exe (PID: 5604)
SUSPICIOUS
Reads security settings of Internet Explorer
- ALTools.exe (PID: 5604)
Creates file in the systems drive root
- ALTools.exe (PID: 5604)
Starts a Microsoft application from unusual location
- ALTools.exe (PID: 5604)
Process drops legitimate windows executable
- ALTools.exe (PID: 5604)
Executable content was dropped or overwritten
- ALTools.exe (PID: 5604)
INFO
Reads the computer name
- ALTools.exe (PID: 5604)
- LockoutStatus.exe (PID: 6608)
Checks supported languages
- LockoutStatus.exe (PID: 6608)
- aloinfo.exe (PID: 6648)
- ALTools.exe (PID: 5604)
- aloinfo.exe (PID: 6724)
Manual execution by a user
- LockoutStatus.exe (PID: 6608)
- aloinfo.exe (PID: 6648)
- aloinfo.exe (PID: 6724)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 6500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (80.4) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (8.2) |
| .exe | | | Win64 Executable (generic) (7.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.7) |
| .exe | | | Win32 Executable (generic) (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2002:08:29 08:25:42+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 7 |
| CodeSize: | 34816 |
| InitializedDataSize: | 826880 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5ae4 |
| OSVersion: | 5.1 |
| ImageVersion: | 5.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.2800.1106 |
| ProductVersionNumber: | 6.0.2800.1106 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 6.00.2800.1106 (xpsp1.020828-1920) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.00.2800.1106 |
Total processes
148
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5604 | "C:\Users\admin\AppData\Local\Temp\ALTools.exe" | C:\Users\admin\AppData\Local\Temp\ALTools.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 6.00.2800.1106 (xpsp1.020828-1920) Modules
| |||||||||||||||
| 6268 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6300 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6500 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
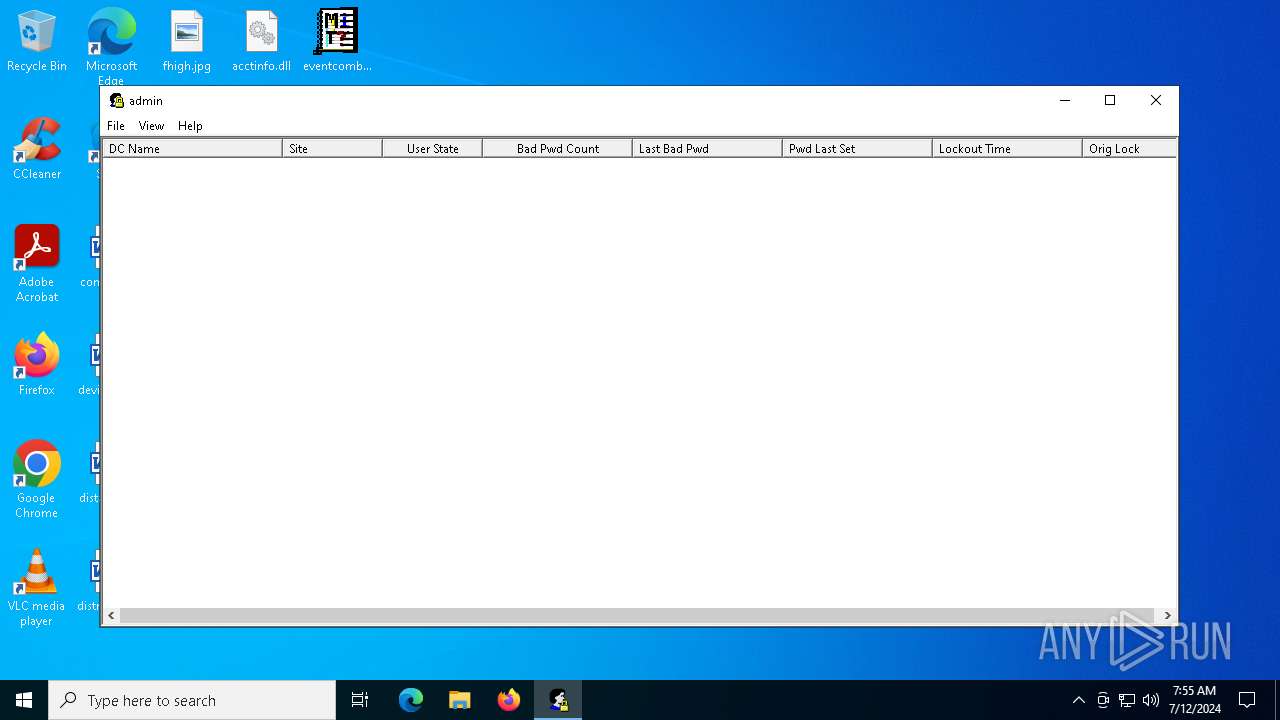
| 6608 | "C:\Users\admin\Desktop\LockoutStatus.exe" | C:\Users\admin\Desktop\LockoutStatus.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Account Lockout Status Exit code: 0 Version: 1, 0, 0, 50 Modules
| |||||||||||||||
| 6648 | "C:\Users\admin\Desktop\aloinfo.exe" | C:\Users\admin\Desktop\aloinfo.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 6656 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | aloinfo.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6724 | "C:\Users\admin\Desktop\aloinfo.exe" | C:\Users\admin\Desktop\aloinfo.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 6732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | aloinfo.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 009
Read events
5 983
Write events
26
Delete events
0
Modification events
| (PID) Process: | (5604) ALTools.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\Program Files (x86)\Common Files\system\wab32res.dll,-10100 |
Value: Contacts | |||
| (PID) Process: | (5604) ALTools.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5604) ALTools.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5604) ALTools.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5604) ALTools.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
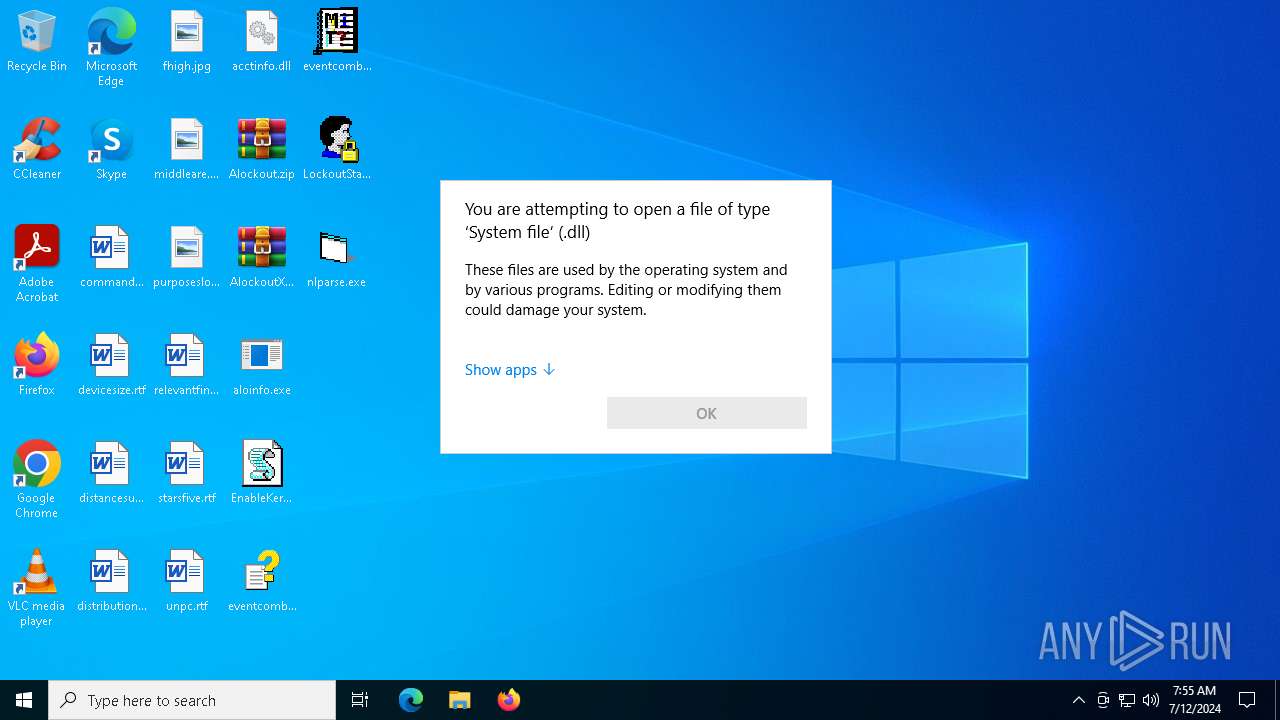
| (PID) Process: | (6500) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.dll\OpenWithProgids |
| Operation: | write | Name: | dllfile |
Value: | |||
| (PID) Process: | (6500) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\Office16\oregres.dll,-205 |
Value: Word | |||
| (PID) Process: | (6500) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @wmploc.dll,-102 |
Value: Windows Media Player | |||
| (PID) Process: | (6608) LockoutStatus.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\LockoutStatus |
| Operation: | write | Name: | TargetDomain |
Value: | |||
| (PID) Process: | (6608) LockoutStatus.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\LockoutStatus |
| Operation: | write | Name: | TargetName |
Value: admin | |||
Executable files
5
Suspicious files
2
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5604 | ALTools.exe | C:\Users\admin\Desktop\Alockout.zip | compressed | |
MD5:BAD044EC32EDC76D13C2B39B959031D9 | SHA256:3A0F1373725F70DFC10418A6521399DA30AB41E902F1BA5A8581B7FEBE5C0BB6 | |||
| 5604 | ALTools.exe | C:\Users\admin\Desktop\aloinfo.exe | executable | |
MD5:BAE3B4DE715013DF2C739EFF3FE6010A | SHA256:47ED995E3239B8E11A0FAF6205559368CBA851CCC7F738266F7EAF5E5DF5AB20 | |||
| 5604 | ALTools.exe | C:\Users\admin\Desktop\eventcombmt.chm | chm | |
MD5:869A7E37406A6B6AC1E690900D608074 | SHA256:F362668304F2B48861E1A5A455092D2A27BCF430F44065A97C80DAAE948C22F3 | |||
| 5604 | ALTools.exe | C:\Users\admin\Desktop\AlockoutXP.zip | compressed | |
MD5:BAC01C1CCA45DBDACD79FBB8DE73C5F7 | SHA256:46F891945AC7B6775499910DDD4B36121B590579D527E0ABF4064BAC84E613AE | |||
| 5604 | ALTools.exe | C:\Users\admin\Desktop\nlparse.exe | executable | |
MD5:FC8F026039FC95BFA2F8D02371C7D537 | SHA256:7C347D64FD583BB71B95CC3E2CC61B488C097A28327EED98597107BEC396E802 | |||
| 5604 | ALTools.exe | C:\Users\admin\Desktop\EnableKerbLog.vbs | text | |
MD5:20ACAAA72F7ECEC8551A93E053870B61 | SHA256:4C2267E10D542A2880954BA816D4DB839C32512698FE28C1B31E89C332A0F504 | |||
| 5604 | ALTools.exe | C:\Users\admin\Desktop\acctinfo.dll | executable | |
MD5:204AA9B5259A3BE495A1A0545EBC3CDF | SHA256:7C9C9E525B5156DAC288F7228584F190A3D1A3ADE58F382A2598012894156F7A | |||
| 5604 | ALTools.exe | C:\Users\admin\Desktop\eventcombMT.exe | executable | |
MD5:B8532EBC109723C7DD0D9857FAD9E9B5 | SHA256:4ABE75B1A2DCE146EDBD3685259F91DD441C041D7277DEC541352751A1D75B90 | |||
| 5604 | ALTools.exe | C:\Users\admin\Desktop\LockoutStatus.exe | executable | |
MD5:449E3183E893EEDCBB72F5C935C31DD0 | SHA256:8A7C3CEE167CFBBF5452A1091F13CDAD3BC412017FCE77C94B7CE1CA309EBA3A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
56
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
900 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
900 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2456 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2008 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4092 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6352 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6352 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1280 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1968 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4656 | SearchApp.exe | 104.126.37.161:443 | www.bing.com | Akamai International B.V. | DE | unknown |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
900 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
900 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
900 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
LockoutStatus.exe | [6608:6612] InitRegistryValues: Leaving with 0x0 |
LockoutStatus.exe | [6608:6612] InitInstance() cmdLine: "C:\Users\admin\Desktop\LockoutStatus.exe" |
LockoutStatus.exe | [6608:6612] InitRegistryValues: On Enter |
LockoutStatus.exe | [6608:6612] InitRegistryValues: Found Current User: admin |
LockoutStatus.exe | [6608:6612] GetDefaultDomainName: On Enter |
LockoutStatus.exe | [6608:6612] GetDefaultDomainName: Leaving with 0x54b |
LockoutStatus.exe | [6608:6612] InitRegistryValues: Could not retrive domain name from system. |
LockoutStatus.exe | [6608:6612] SetRegistryValues() entered. |
LockoutStatus.exe | [6608:6612] SetRegistryValues() Saving TARGETDOMAIN (0x0) |
LockoutStatus.exe | [6608:6612] SetRegistryValues() Saving TARGETNAME (0x0) |