| File name: | 2025-05-17_9260b18c14f2ebaac493ba15febe054c_amadey_black-basta_darkgate_elex_luca-stealer |
| Full analysis: | https://app.any.run/tasks/85f19795-2912-4494-a78f-313d68eeef30 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 07:53:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 9260B18C14F2EBAAC493BA15FEBE054C |
| SHA1: | 5348FECF6EC8F4327BD802320433189F708CB5C7 |
| SHA256: | B2ACBF6FF338819400941C339DBB393FCF7EB35F0CEDCEF22149A6F6204CED18 |
| SSDEEP: | 49152:hfQ1m473udDjeVmyN2HZAJKRIDZ2JiB9SoI+rkHReASNkwDDOkRdu4uWAxvZ:d+GyiZAJKRId2JiB9SoBr8RtSNkwDds4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
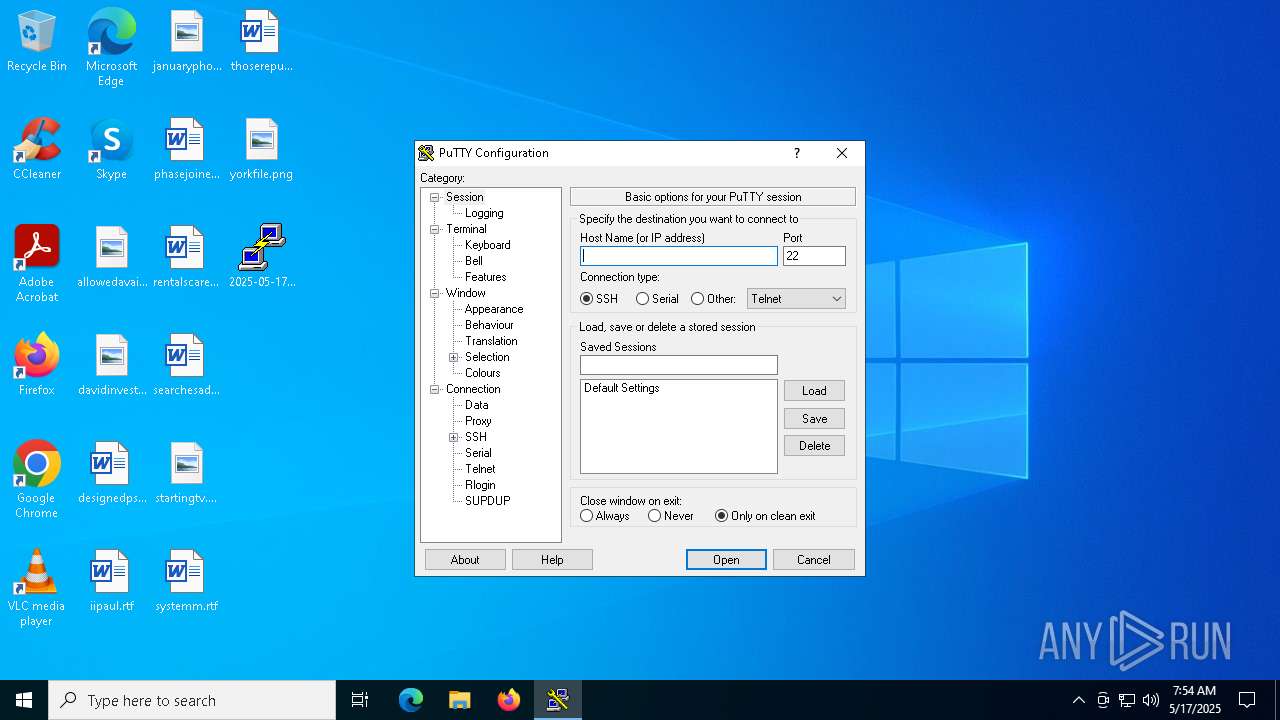
PUTTY has been detected
- 2025-05-17_9260b18c14f2ebaac493ba15febe054c_amadey_black-basta_darkgate_elex_luca-stealer.exe (PID: 6876)
Reads security settings of Internet Explorer
- 2025-05-17_9260b18c14f2ebaac493ba15febe054c_amadey_black-basta_darkgate_elex_luca-stealer.exe (PID: 6876)
Executes application which crashes
- 2025-05-17_9260b18c14f2ebaac493ba15febe054c_amadey_black-basta_darkgate_elex_luca-stealer.exe (PID: 6876)
INFO
Reads the computer name
- 2025-05-17_9260b18c14f2ebaac493ba15febe054c_amadey_black-basta_darkgate_elex_luca-stealer.exe (PID: 6876)
The sample compiled with english language support
- 2025-05-17_9260b18c14f2ebaac493ba15febe054c_amadey_black-basta_darkgate_elex_luca-stealer.exe (PID: 6876)
Checks proxy server information
- 2025-05-17_9260b18c14f2ebaac493ba15febe054c_amadey_black-basta_darkgate_elex_luca-stealer.exe (PID: 6876)
- slui.exe (PID: 2504)
Checks supported languages
- 2025-05-17_9260b18c14f2ebaac493ba15febe054c_amadey_black-basta_darkgate_elex_luca-stealer.exe (PID: 6876)
Reads the machine GUID from the registry
- 2025-05-17_9260b18c14f2ebaac493ba15febe054c_amadey_black-basta_darkgate_elex_luca-stealer.exe (PID: 6876)
Reads the software policy settings
- 2025-05-17_9260b18c14f2ebaac493ba15febe054c_amadey_black-basta_darkgate_elex_luca-stealer.exe (PID: 6876)
- slui.exe (PID: 2504)
Creates files or folders in the user directory
- WerFault.exe (PID: 2320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:02:01 11:27:15+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 820736 |
| InitializedDataSize: | 670208 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa1086 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.83.0.0 |
| ProductVersionNumber: | 0.83.0.0 |
| FileFlagsMask: | 0x000b |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| CompanyName: | Simon Tatham |
| ProductName: | PuTTY suite |
| FileDescription: | SSH, Telnet, Rlogin, and SUPDUP client |
| InternalName: | PuTTY |
| OriginalFileName: | PuTTY |
| FileVersion: | Release 0.83 (with embedded help) |
| ProductVersion: | Release 0.83 |
| LegalCopyright: | Copyright © 1997-2025 Simon Tatham. |
Total processes
124
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6876 -s 2248 | C:\Windows\SysWOW64\WerFault.exe | — | 2025-05-17_9260b18c14f2ebaac493ba15febe054c_amadey_black-basta_darkgate_elex_luca-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2504 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6876 | "C:\Users\admin\Desktop\2025-05-17_9260b18c14f2ebaac493ba15febe054c_amadey_black-basta_darkgate_elex_luca-stealer.exe" | C:\Users\admin\Desktop\2025-05-17_9260b18c14f2ebaac493ba15febe054c_amadey_black-basta_darkgate_elex_luca-stealer.exe | explorer.exe | ||||||||||||
User: admin Company: Simon Tatham Integrity Level: MEDIUM Description: SSH, Telnet, Rlogin, and SUPDUP client Exit code: 3221225622 Version: Release 0.83 (with embedded help) Modules
| |||||||||||||||
Total events
8 372
Read events
8 372
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2320 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_2025-05-17_9260b_87d875cf13a05bb45f9562967fcecff6c4e2455_99017b4f_58156b32-9f52-4e88-9845-2c4fde37359e\Report.wer | — | |
MD5:— | SHA256:— | |||
| 2320 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER1A7A.tmp.dmp | binary | |
MD5:D7FFE7464C39DFCE48BEEFEFCDBC1753 | SHA256:61FBC2FABF864EBC124295CBDFD4C11D92A31E58C7D98FAD789D37E673011CAE | |||
| 2320 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER1BF3.tmp.xml | xml | |
MD5:C227FCE1E404898F01470BCFE8E0D524 | SHA256:5230F847630A553D518E169038A48D758FC797260EC14691993B0A269DC3B87D | |||
| 2320 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER1BA4.tmp.WERInternalMetadata.xml | binary | |
MD5:E847A20FC39C3431A5BFE4BA0D59E2F7 | SHA256:8144221F051864EFFC99040B01CF699D316E55745268E36AD3B6257D94757444 | |||
| 2320 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\2025-05-17_9260b18c14f2ebaac493ba15febe054c_amadey_black-basta_darkgate_elex_luca-stealer.exe.6876.dmp | binary | |
MD5:D4F31A261C1AE3A1A9AEDD61578B0D16 | SHA256:99457400AF05BE0AA68B394D603DCA9F9C2604E4A819095B1F3E2340DB5BC0D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
20
DNS requests
4
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6876 | 2025-05-17_9260b18c14f2ebaac493ba15febe054c_amadey_black-basta_darkgate_elex_luca-stealer.exe | 187.0.2.4:443 | 7madh-qx2.ddns.net | Adylnet Telecom | BR | malicious |
4528 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2504 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
7madh-qx2.ddns.net |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
— | — | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS HTTP Request to a *.ddns .net Domain |