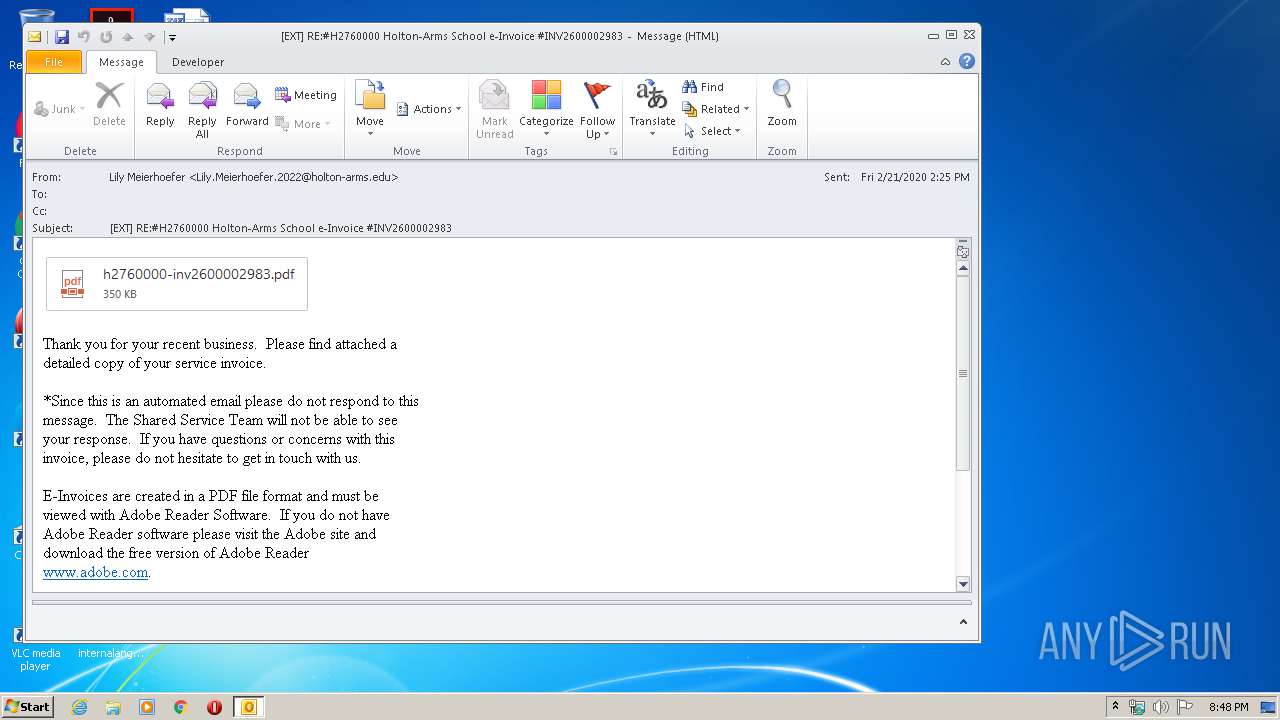
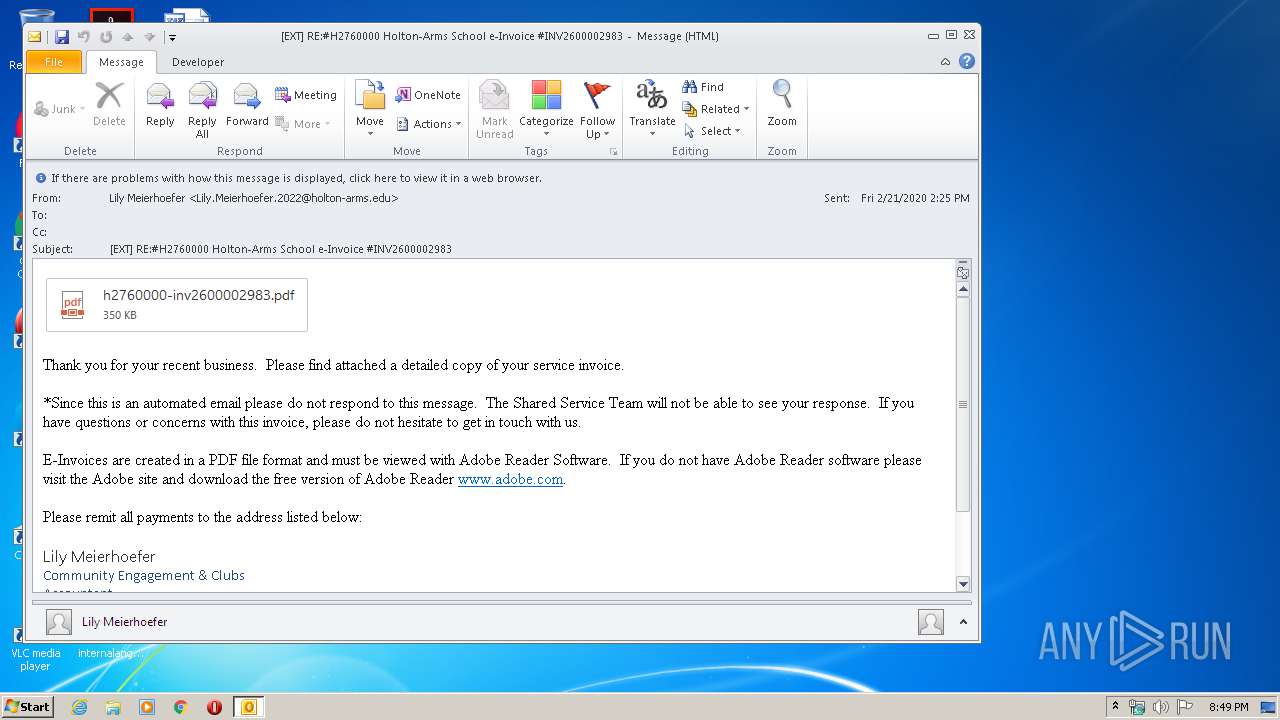
| File name: | EXT RE#H2760000 Holton-Arms School e-Invoice #INV2600002983.msg |
| Full analysis: | https://app.any.run/tasks/bb77b0a8-54e5-4806-b585-630e04043a0d |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 20:48:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 9436CB53490AAC621D9B631DA8556BEF |
| SHA1: | 3D4581B9CBC4E53E25B90109FCF057AD92639D71 |
| SHA256: | B2AA01C97A8BCEE6AB84E4000A4B7F9583DECD3A3A51810E38312120BFE55E57 |
| SSDEEP: | 3072:nygXbOcbX3yvYYhbqp7SXi/WAX3yBosKmKr2eTnoS92y:ygrDVtCdKKX |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 1720)
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 1720)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 1720)
Creates files in the user directory
- OUTLOOK.EXE (PID: 1720)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1720)
Reads Internet Cache Settings
- iexplore.exe (PID: 3900)
- iexplore.exe (PID: 2888)
Creates files in the user directory
- iexplore.exe (PID: 3900)
Changes internet zones settings
- iexplore.exe (PID: 2888)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3900)
Reads internet explorer settings
- iexplore.exe (PID: 3900)
Application launched itself
- iexplore.exe (PID: 2888)
Reads settings of System Certificates
- iexplore.exe (PID: 3900)
- iexplore.exe (PID: 2888)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2888)
Changes settings of System certificates
- iexplore.exe (PID: 2888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1720 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\EXT RE#H2760000 Holton-Arms School e-Invoice #INV2600002983.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2888 | "C:\Program Files\Internet Explorer\iexplore.exe" https://secure-web.cisco.com/1vmcoHk16L0k_3ZPwV1i8ynDCTZ781yU_eJgQLV6re1q9LXArD_r3XnCKtfs11n9InEkFkWKoBDSLWzm2xiT9bav9HG8zLUisMQO1V7IDoThnR-pvC3AKMFHJ9wd9RpkIyTjUzXrNnB36mf9DfN5TDVZyhqJy3CE-XSrQx7J59SXhFKOfyIPKkxJsSZqMN88Bo0AR0GRqf1km3pFgeDdnPJ8cPRWHE5QRKbdTPtpxQFjg0A1ucbp2q7RV9GkFzJ-eiWOVgG4WP107JNARzlgeG0xX7eOLgspEGLC9wiiQi8to9OwwdBahId7fmx76OqDJdNRYleudY5J8nAZ6q-EoB9njfUhh2HUsr8HwINyVyv_yNFTj2Uhy40zKtUew4kwjSO-7wYiZ5j0re6oJxQ43C59-flo5t6Njj7Su9NChAyuoq8mfwdb0GBzMSvyRkQEsLGCM-13xLwlq_925Xei5D72HnMQCOhJiO4STyBMswkngM3YmNjqaNalY6OtR0gA96Gq8wczdi8ScKzA4yhBLjw/https%3A%2F%2Fgustygulasgroup.us4.list-manage.com%2Ftrack%2Fclick%3Fu%3D8d104840f36293e4dfb89ed2a%26id%3D0dfac2ea5b%26e%3D288b976ac7 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3900 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2888 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
7 785
Read events
1 994
Write events
4 040
Delete events
1 751
Modification events
| (PID) Process: | (1720) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1720) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1720) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1720) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1720) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1720) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1720) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1720) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1720) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1720) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
12
Text files
33
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1720 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6B35.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2888 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab98ED.tmp | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar98EE.tmp | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\APIIAVB5.txt | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B0F2D31D2C32B49DCC8F7CC5C73F3C5D_2C8AAFA9D67255B0364928E0BF09B2FE | der | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\2EE749B7E1A15635422518BB5EBFD338_2BE9BBF30BBE030BE7B79471EABFE00A | der | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\2EE749B7E1A15635422518BB5EBFD338_2BE9BBF30BBE030BE7B79471EABFE00A | binary | |
MD5:— | SHA256:— | |||
| 1720 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6E1AA388.dat | image | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
24
DNS requests
16
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3900 | iexplore.exe | GET | 200 | 35.156.48.155:80 | http://ocsp.quovadisglobal.com/MFUwUzBRME8wTTAJBgUrDgMCGgUABBTyhcKR1A4XhQLFZRt5u%2BT8TDsYdQQUGoRivEhMMyUE1O7Q9gPEGUbRlGsCFHUXFneD0EN%2BtVbDV5RuRWO469Os | DE | der | 1.78 Kb | whitelisted |
3900 | iexplore.exe | GET | 200 | 35.156.48.155:80 | http://ocsp.quovadisglobal.com/MFUwUzBRME8wTTAJBgUrDgMCGgUABBRPT4HWWg2N6N2sdizmyiRTaupwfgQUmGq2LS6%2Fp6qf9vfWCa%2FVi1f5ircCFAJ6LdwhHmBeL%2BjGokwlqon6ciFk | DE | der | 1.80 Kb | whitelisted |
3900 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3900 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3900 | iexplore.exe | GET | 200 | 52.219.72.94:80 | http://crl.quovadisglobal.com/hydsslg2.crl | DE | der | 46.2 Kb | shared |
2888 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3900 | iexplore.exe | 208.90.58.178:443 | secure-web.cisco.com | Cisco Systems Ironport Division | US | suspicious |
2888 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3900 | iexplore.exe | 23.8.12.241:443 | gustygulasgroup.us4.list-manage.com | Akamai International B.V. | NL | unknown |
3900 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3900 | iexplore.exe | 35.156.48.155:80 | ocsp.quovadisglobal.com | Amazon.com, Inc. | DE | unknown |
3900 | iexplore.exe | 52.219.72.94:80 | crl.quovadisglobal.com | Amazon.com, Inc. | DE | unknown |
3900 | iexplore.exe | 62.109.0.180:443 | wpadvot.com | JSC ISPsystem | RU | suspicious |
2888 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1720 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
secure-web.cisco.com |
| whitelisted |
ocsp.quovadisglobal.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
gustygulasgroup.us4.list-manage.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
wpadvot.com |
| suspicious |
crl.quovadisglobal.com |
| shared |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3900 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3900 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |