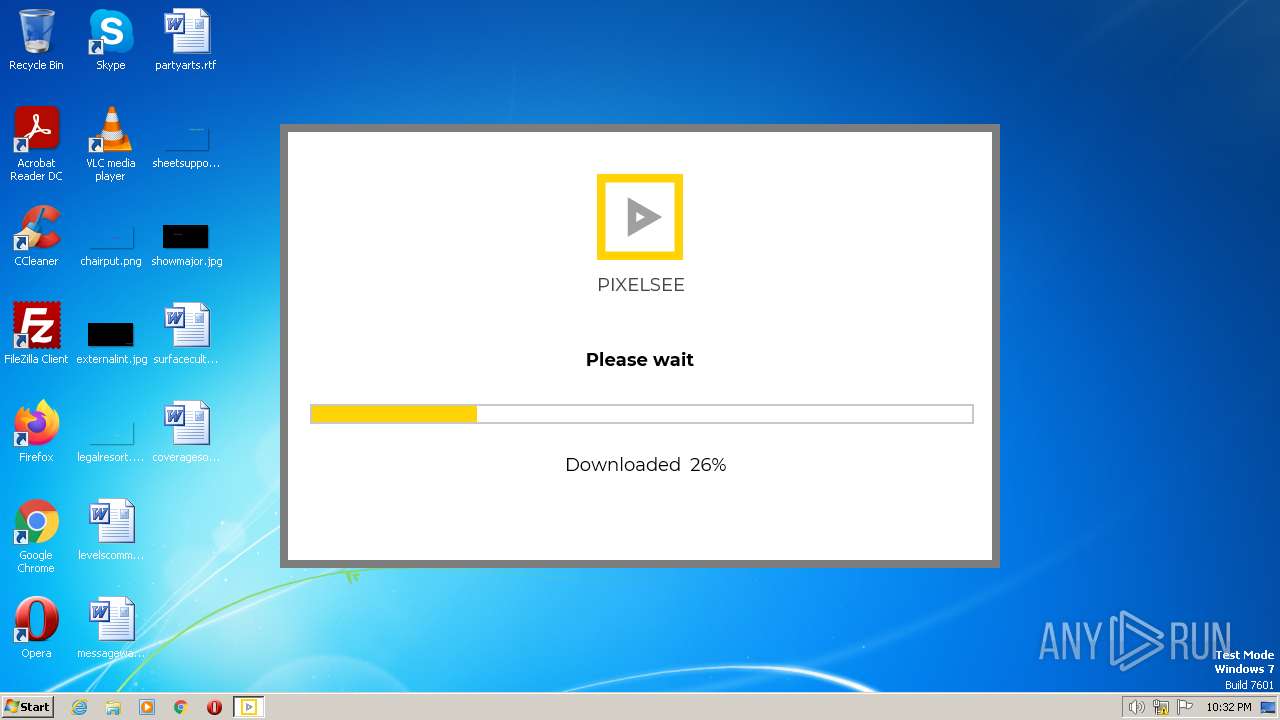
| download: | pixelsee_installer_p_2.exe |
| Full analysis: | https://app.any.run/tasks/dbaf628f-5810-4dba-a1fa-325591d3b65b |
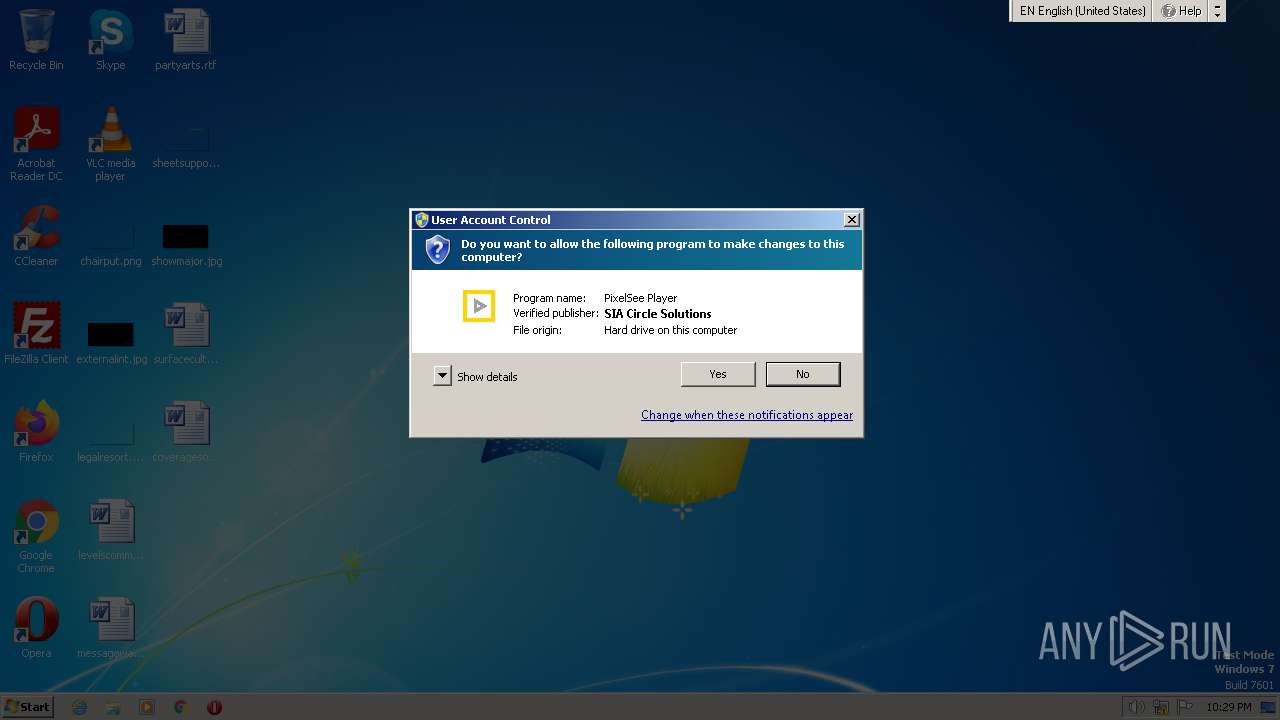
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2023, 21:28:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 60849A8FF219BE4BEC52709173984455 |
| SHA1: | 655F2A35EFE59837B287D9B02C0C723F09A73A8B |
| SHA256: | B2A96537B627CC5F7ED63B4B9491B9EA15B08C88DFDD5AEB7A00D903DD4D0176 |
| SSDEEP: | 49152:OYmOcTD7x4cPKESEzLU0Ava6yQdpM8nGWmIHa03okleDhojwVuaGfJb:eXx7Plvv1/QI8GWm03okl4E5 |
MALICIOUS
Actions looks like stealing of personal data
- pixelsee_installer_p_2.exe (PID: 3692)
The DLL Hijacking
- SearchProtocolHost.exe (PID: 1248)
SUSPICIOUS
Reads Microsoft Outlook installation path
- pixelsee_installer_p_2.exe (PID: 3692)
Reads Internet Explorer settings
- pixelsee_installer_p_2.exe (PID: 3692)
Reads the Internet Settings
- pixelsee_installer_p_2.exe (PID: 3692)
Executable content was dropped or overwritten
- pixelsee_installer_p_2.exe (PID: 3692)
INFO
Checks supported languages
- pixelsee_installer_p_2.exe (PID: 3692)
The process checks LSA protection
- pixelsee_installer_p_2.exe (PID: 3692)
- SearchProtocolHost.exe (PID: 1248)
Reads the computer name
- pixelsee_installer_p_2.exe (PID: 3692)
Checks proxy server information
- pixelsee_installer_p_2.exe (PID: 3692)
Create files in a temporary directory
- pixelsee_installer_p_2.exe (PID: 3692)
Reads the machine GUID from the registry
- pixelsee_installer_p_2.exe (PID: 3692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| ProductVersion: | 1 |
|---|---|
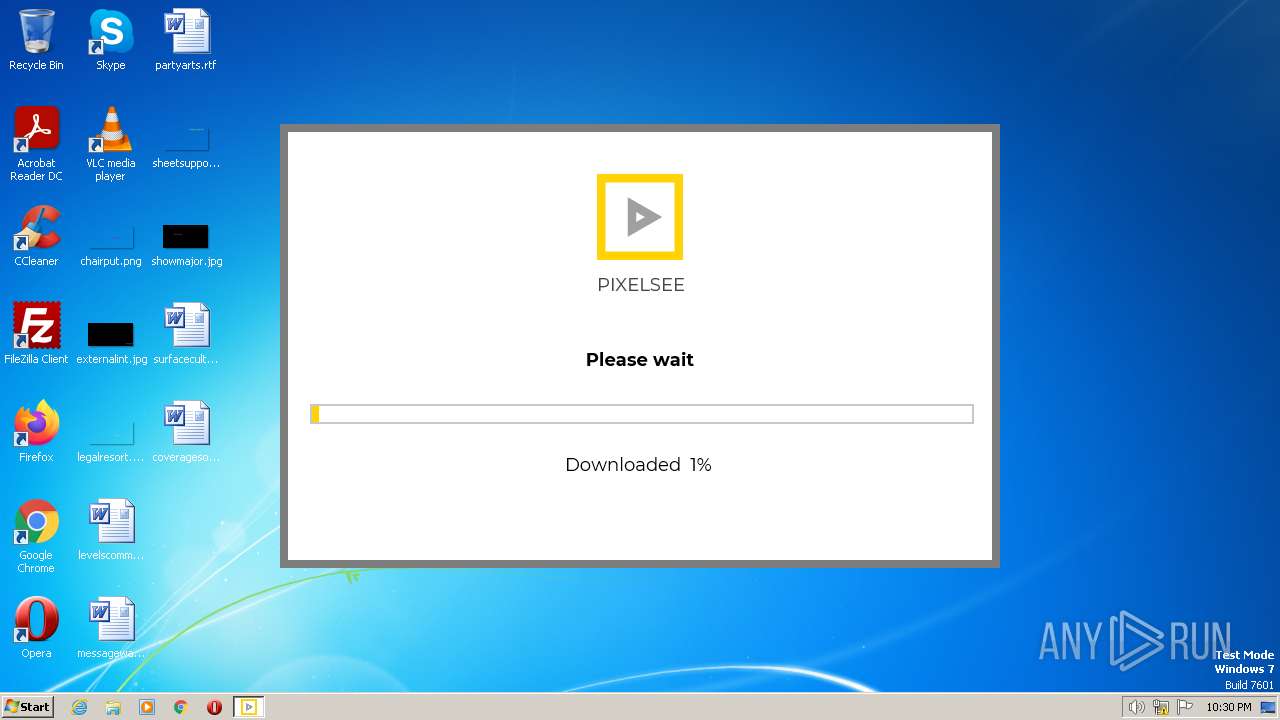
| ProductName: | PixelSee |
| PrivateBuild: | - |
| OriginalFileName: | pixelsee |
| LegalCopyright: | Copyright © 2022 PixelSee |
| InternalName: | pixelsee |
| FileVersion: | - |
| FileDescription: | PixelSee Player |
| CompanyName: | PixelSee |
| Comments: | PixelSee Player |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.1 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x18e9bc |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1651712 |
| CodeSize: | 1690112 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2022:05:26 15:17:56+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-May-2022 15:17:56 |
| Detected languages: |
|
| Comments: | PixelSee Player |
| CompanyName: | PixelSee |
| FileDescription: | PixelSee Player |
| FileVersion: | - |
| InternalName: | pixelsee |
| LegalCopyright: | Copyright © 2022 PixelSee |
| OriginalFilename: | pixelsee |
| PrivateBuild: | 0 |
| ProductName: | PixelSee |
| ProductVersion: | 1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 26-May-2022 15:17:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0019C804 | 0x0019CA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54925 |
.rdata | 0x0019E000 | 0x00076DD4 | 0x00076E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10406 |
.data | 0x00215000 | 0x0000F620 | 0x00009800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.06339 |
.rsrc | 0x00225000 | 0x000FAB7C | 0x000FAC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.90257 |
.reloc | 0x00320000 | 0x00018064 | 0x00018200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.19765 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22706 | 820 | Latin 1 / Western European | English - United States | RT_MANIFEST |
128 | 1.51664 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
129 | 1.67172 | 170 | Latin 1 / Western European | English - United States | UNKNOWN |
HTML | 7.99975 | 690787 | Latin 1 / Western European | Russian - Russia | ARCHIVE_7Z |
PRELOADER | 7.99824 | 103820 | Latin 1 / Western European | Russian - Russia | ARCHIVE_7Z |
CABUNDLE | 6.0253 | 227153 | Latin 1 / Western European | Russian - Russia | CRT |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCR90.dll |
OLEAUT32.dll |
OPENGL32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
43
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1248 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 2764 | "C:\Users\admin\Downloads\pixelsee_installer_p_2.exe" | C:\Users\admin\Downloads\pixelsee_installer_p_2.exe | — | explorer.exe | |||||||||||
User: admin Company: PixelSee Integrity Level: MEDIUM Description: PixelSee Player Exit code: 3221226540 Modules
| |||||||||||||||
| 3692 | "C:\Users\admin\Downloads\pixelsee_installer_p_2.exe" | C:\Users\admin\Downloads\pixelsee_installer_p_2.exe | explorer.exe | ||||||||||||
User: admin Company: PixelSee Integrity Level: HIGH Description: PixelSee Player Exit code: 0 Modules
| |||||||||||||||
Total events
1 714
Read events
1 699
Write events
15
Delete events
0
Modification events
| (PID) Process: | (3692) pixelsee_installer_p_2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3692) pixelsee_installer_p_2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3692) pixelsee_installer_p_2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3692) pixelsee_installer_p_2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3692) pixelsee_installer_p_2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3692) pixelsee_installer_p_2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1248) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
301
Suspicious files
122
Text files
117
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3692 | pixelsee_installer_p_2.exe | C:\Users\admin\AppData\Local\Temp\pixelsee-installer-tmp\Montserrat-Regular.eot | binary | |
MD5:2DD0A1DE870AF34D48D43B7CAD82B8D9 | SHA256:057BC6C47C47AACCDF31ADC48A6B401F6090A02C28E354099EFF80907DC2AF32 | |||
| 3692 | pixelsee_installer_p_2.exe | C:\Users\admin\AppData\Local\Temp\pixelsee-installer-tmp\bundles\bundle-opera.html | html | |
MD5:A0FD3EC1D58F5805C3ECBD3628B21815 | SHA256:0C94BD8D4EAB1C2B4CE4FC9A8BB3F8FD11524DC9F8C8B2FEBE5FBC132978B4DD | |||
| 3692 | pixelsee_installer_p_2.exe | C:\Users\admin\AppData\Local\Temp\pixelsee-installer-tmp\bundles\bundle-opera-friendly.html | html | |
MD5:0597FBE76E7C354C19D04F6D8F2CD1B9 | SHA256:B4D9AF00D896341A7DAAA53C41E4856FD52782B2F6261406919EAD9BCF5D0E73 | |||
| 3692 | pixelsee_installer_p_2.exe | C:\Users\admin\AppData\Local\Temp\pixelsee-installer-tmp\archive.7z | compressed | |
MD5:180178F6A9C890B59240ECE1AB766479 | SHA256:30D362C2644F6FB8AA916DD3B715E495DB618115880A6DA860182C7150BC588C | |||
| 3692 | pixelsee_installer_p_2.exe | C:\Users\admin\AppData\Local\Temp\pixelsee-installer-tmp\bundles\bundle-soax.html | html | |
MD5:DB6CA1C15991DA6DFB6D21179A33F786 | SHA256:B91114A2184430B1C0574336CACB253C52150830CE4591C5CA1FEE22895F745C | |||
| 3692 | pixelsee_installer_p_2.exe | C:\Users\admin\AppData\Local\Temp\pixelsee-installer-tmp\curl-ca-bundle.crt | text | |
MD5:BE2B0736EA029FFF398559FA7DF4E646 | SHA256:C05A79296D61E3B2A2EBAF5AF476839B976D69A5ACB6F581A667E60E681049A2 | |||
| 3692 | pixelsee_installer_p_2.exe | C:\Users\admin\AppData\Local\Temp\pixelsee-installer-tmp\bundles\bundle-luminati-wait.html | text | |
MD5:FEA427802F9F1505612945D97AAC9568 | SHA256:B550D0875D5DC5292C979981400782FAE63AACFC002CA03911FDC44A7C28E58A | |||
| 3692 | pixelsee_installer_p_2.exe | C:\Users\admin\AppData\Local\Temp\pixelsee-installer-tmp\main-icon-big.png | image | |
MD5:0E5FEA82CC4F4A8225532E5B2F45C6C8 | SHA256:81B5F50491579127D13E050847EF6D817265AB4B70D2796FB74021463B778BB9 | |||
| 3692 | pixelsee_installer_p_2.exe | C:\Users\admin\AppData\Local\Temp\pixelsee-installer-tmp\bundles\main.html | html | |
MD5:BFD7CD82084EC963A225BBAD55DB1053 | SHA256:087FCDAF55EC55FAEC74944BB6F0DFA012FE3A9F2F0FC32F70CA2080B372F13C | |||
| 3692 | pixelsee_installer_p_2.exe | C:\Users\admin\AppData\Local\Temp\pixelsee-installer-tmp\bundles\bundle-coc.html | html | |
MD5:9C040C5F4DB773934730C0471363B4A4 | SHA256:794AA2B7DCC14CF1A7017A9568AB47A81DA2F2D81CE6DE5BB777EDAE21AEF189 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
16
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1820 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3692 | pixelsee_installer_p_2.exe | 51.158.190.232:443 | pixelsee.app | Online S.a.s. | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pixelsee.app |
| suspicious |