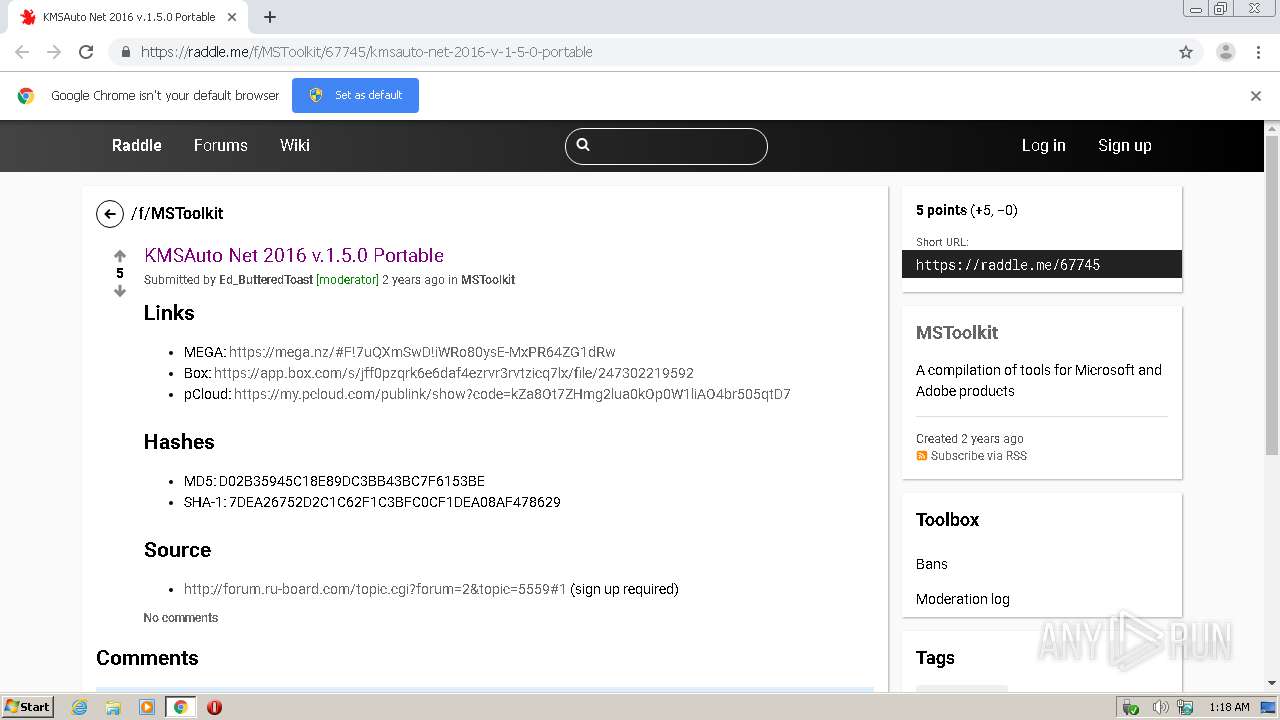
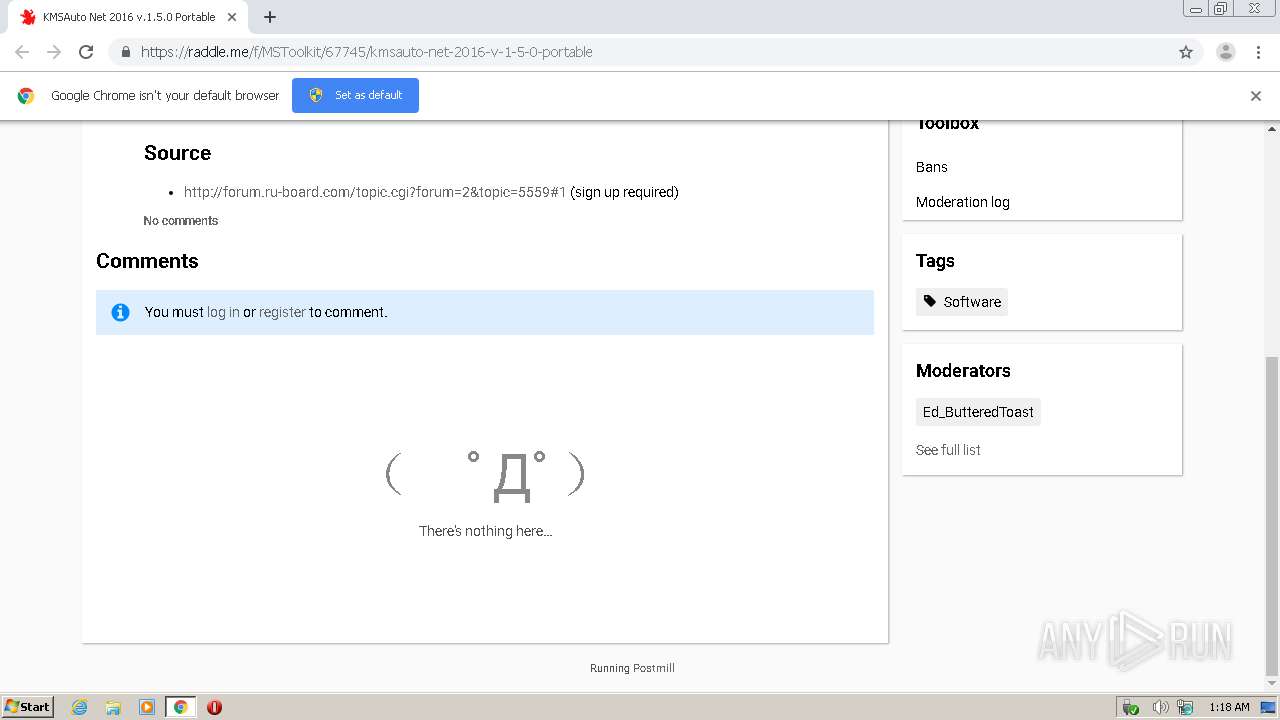
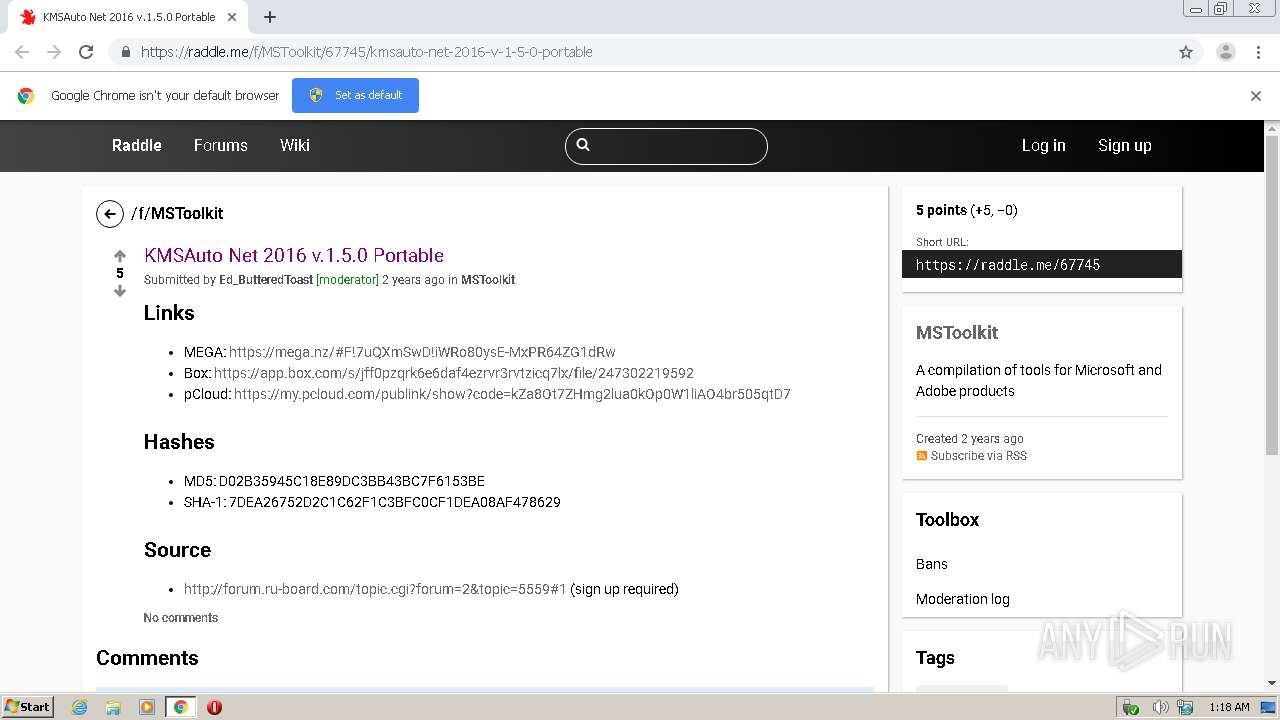
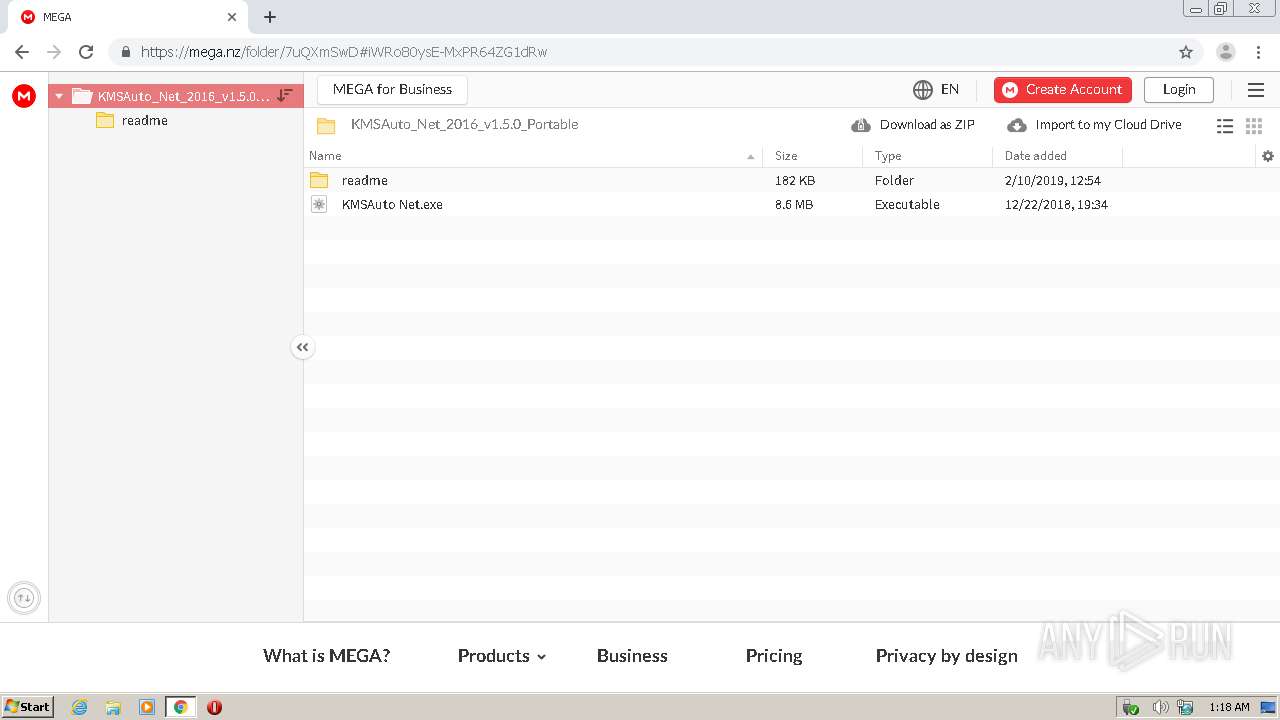
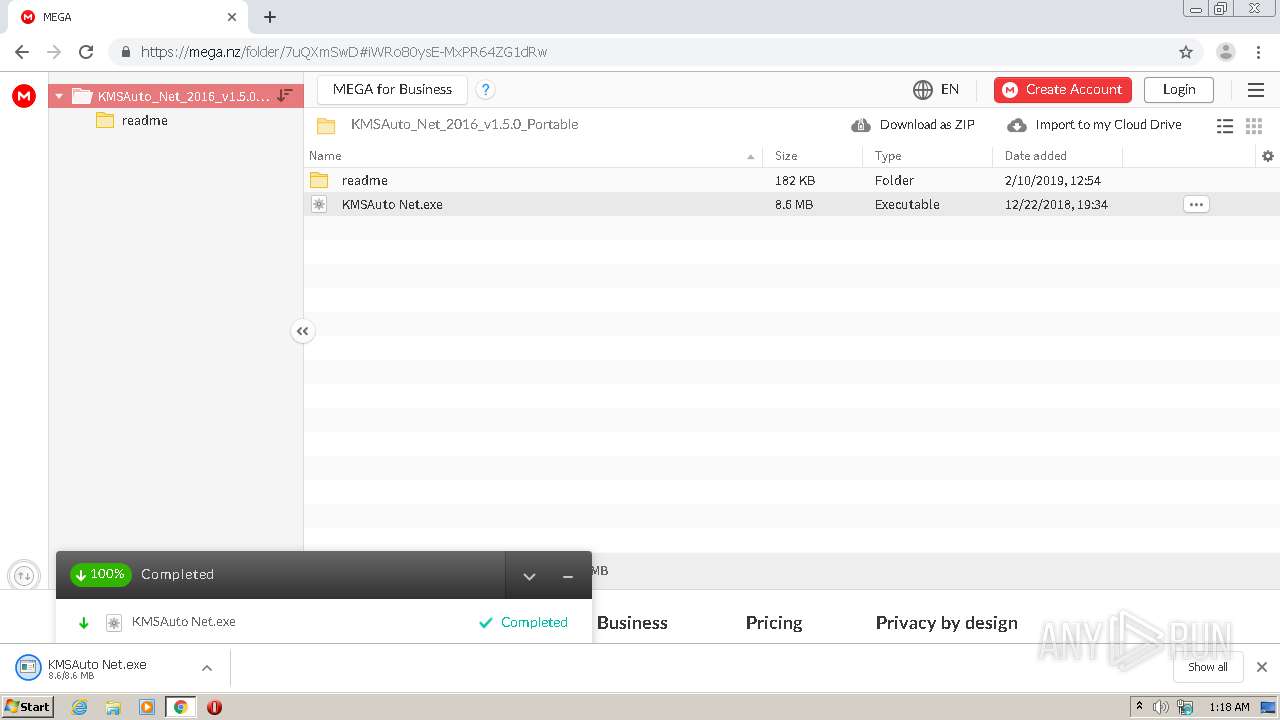
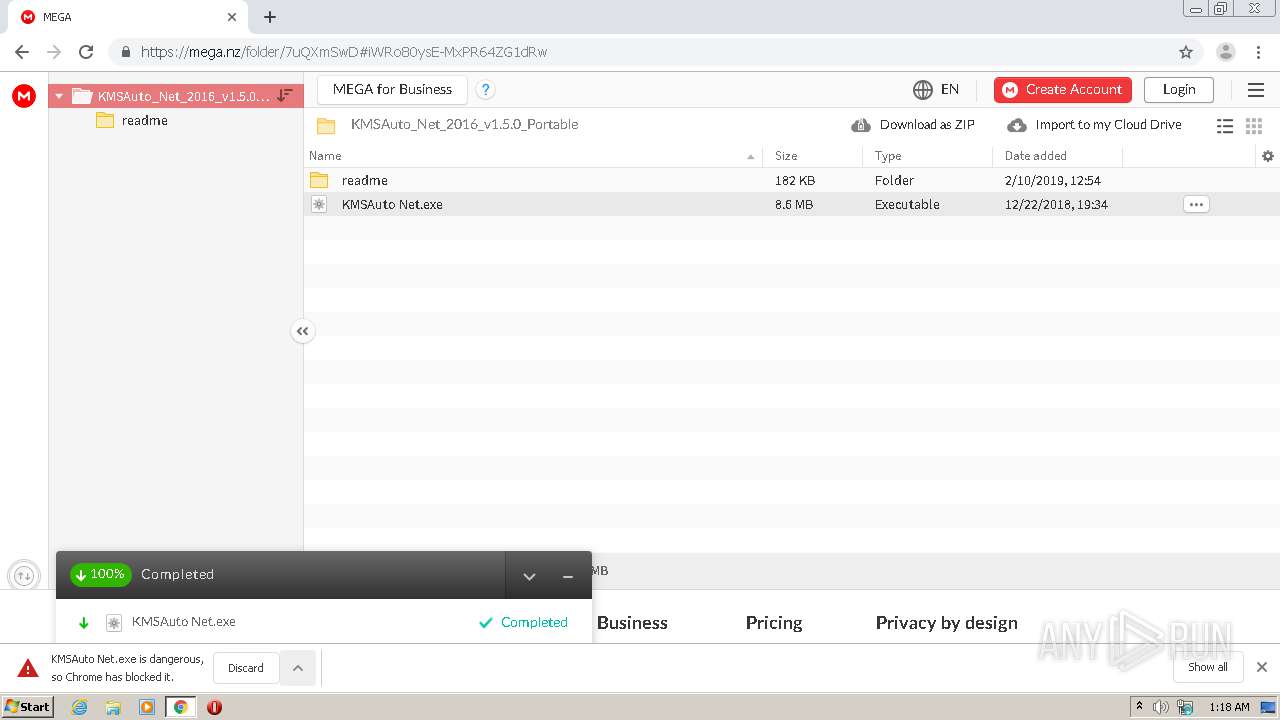
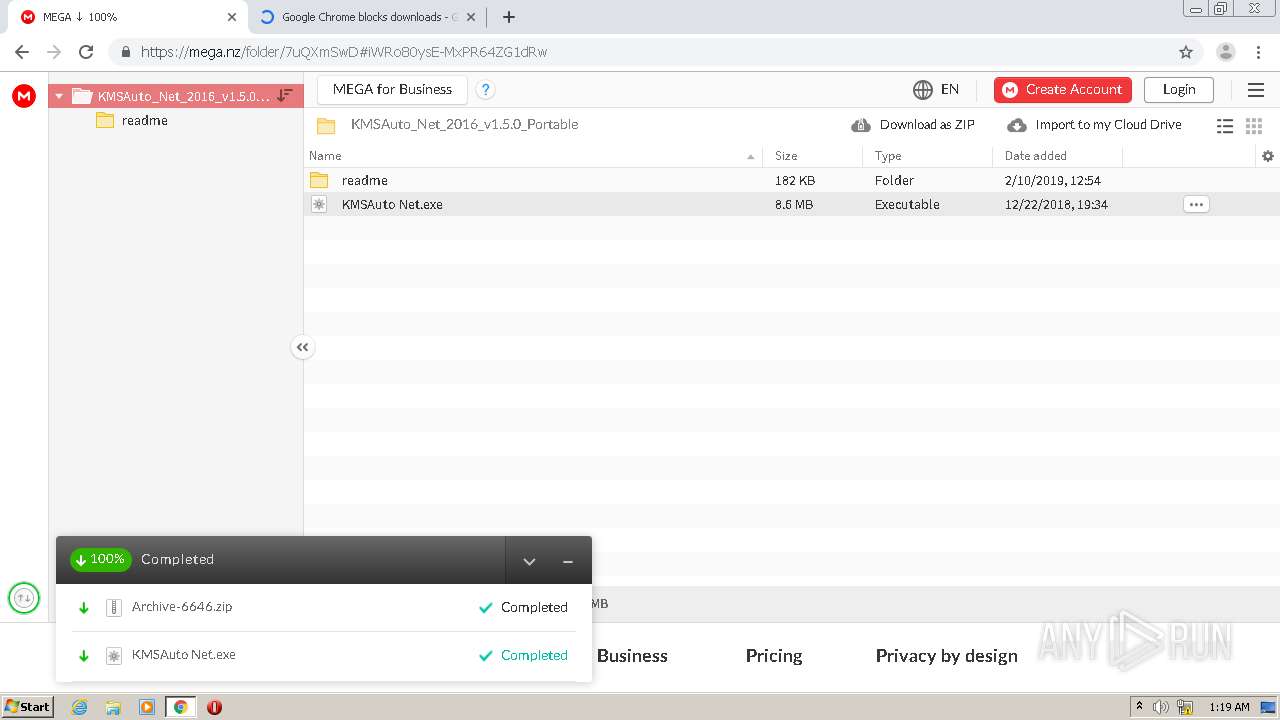
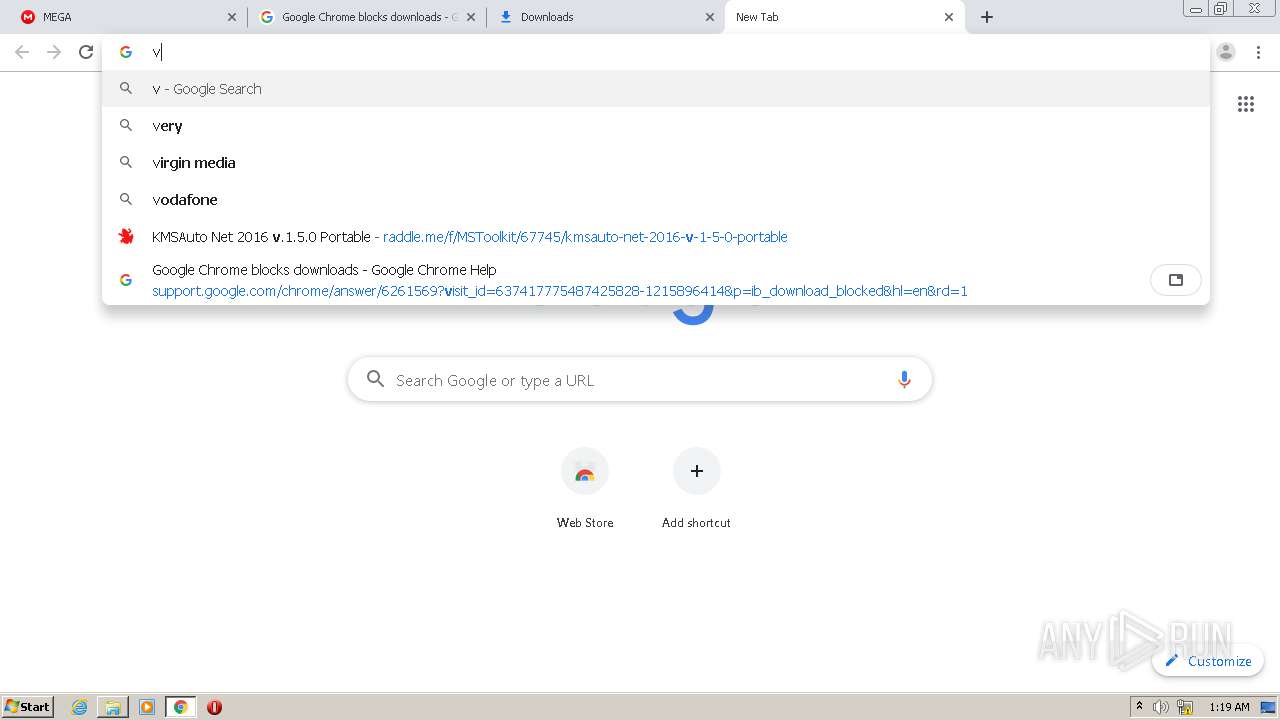
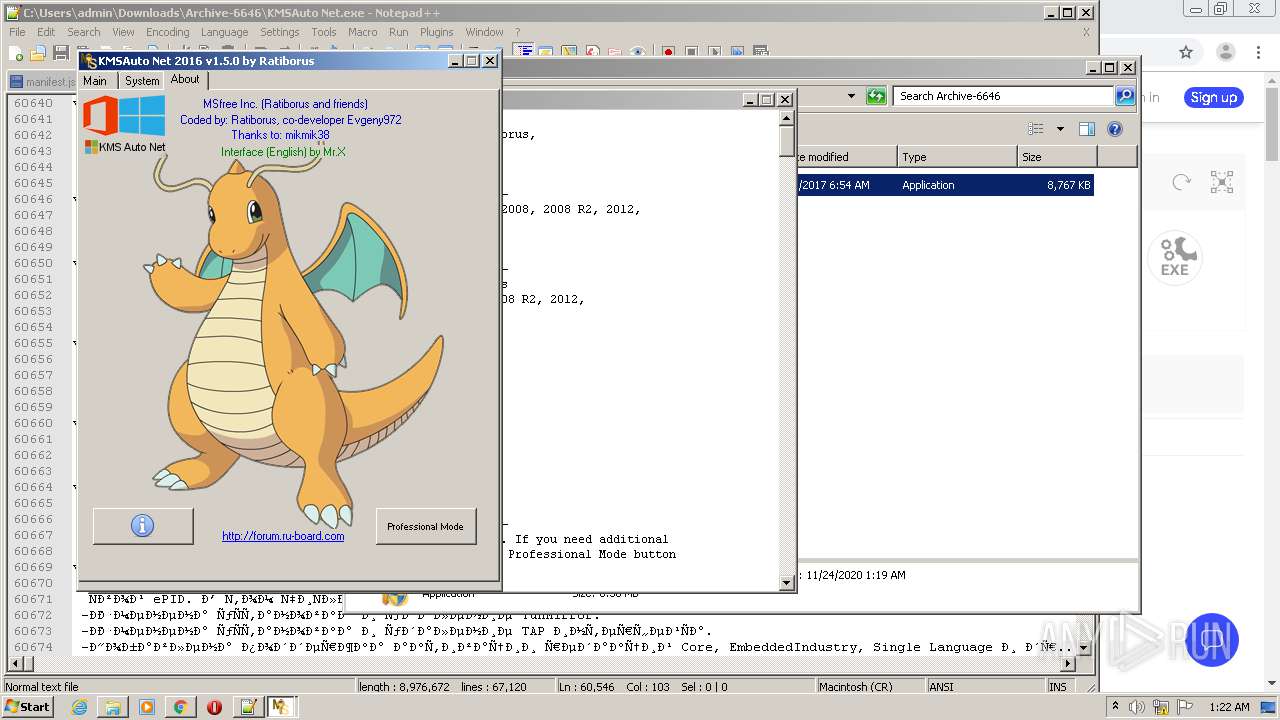
| URL: | https://raddle.me/f/MSToolkit/67745/kmsauto-net-2016-v-1-5-0-portable |
| Full analysis: | https://app.any.run/tasks/ba034d19-7042-4df5-abe7-2b758562ab9e |
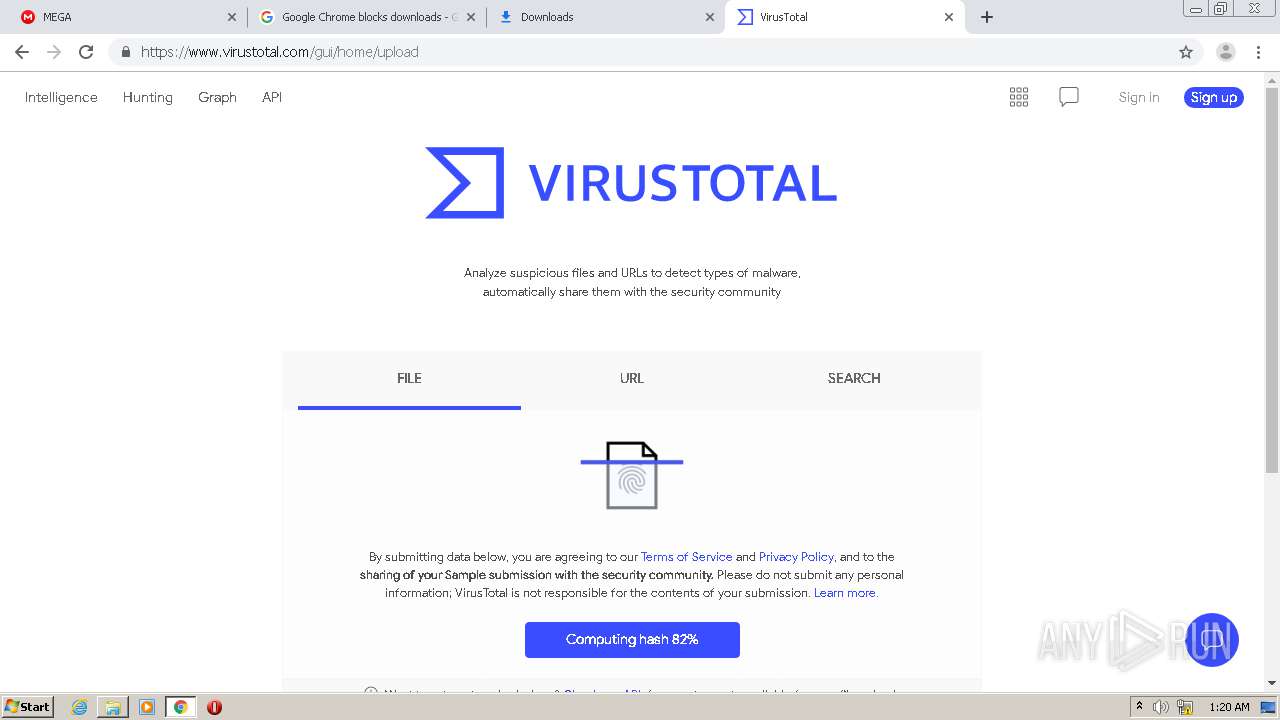
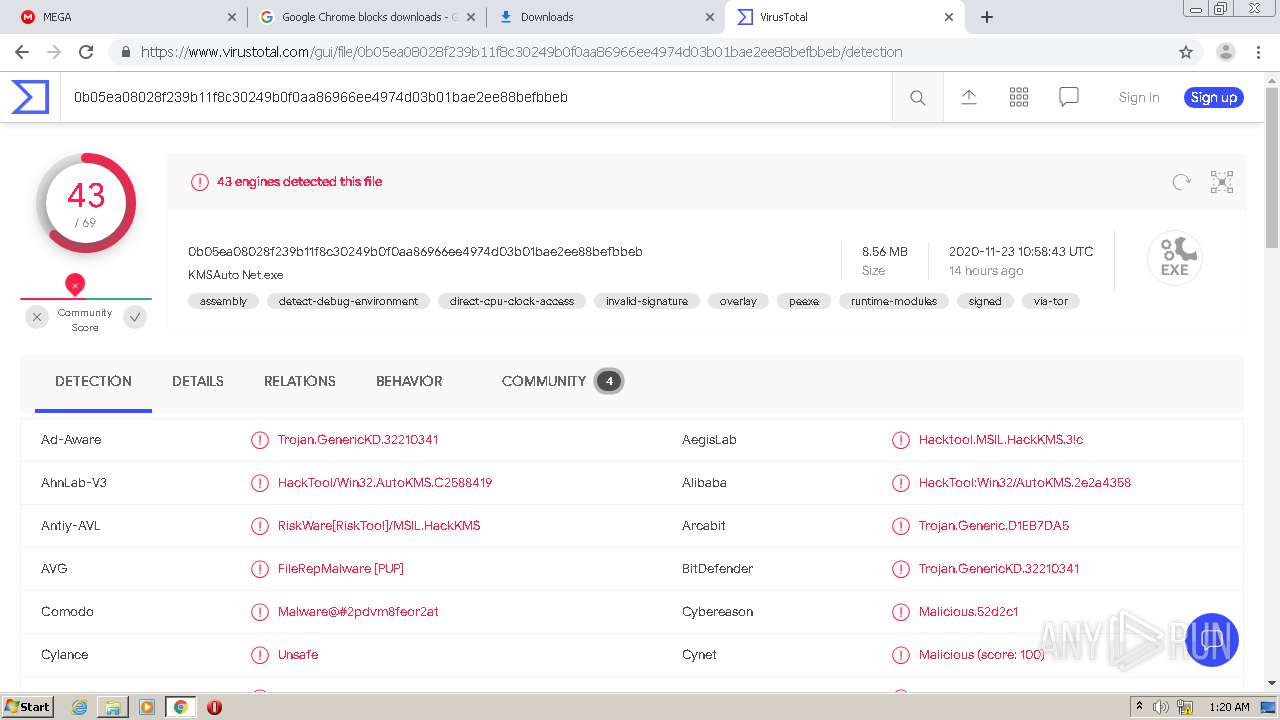
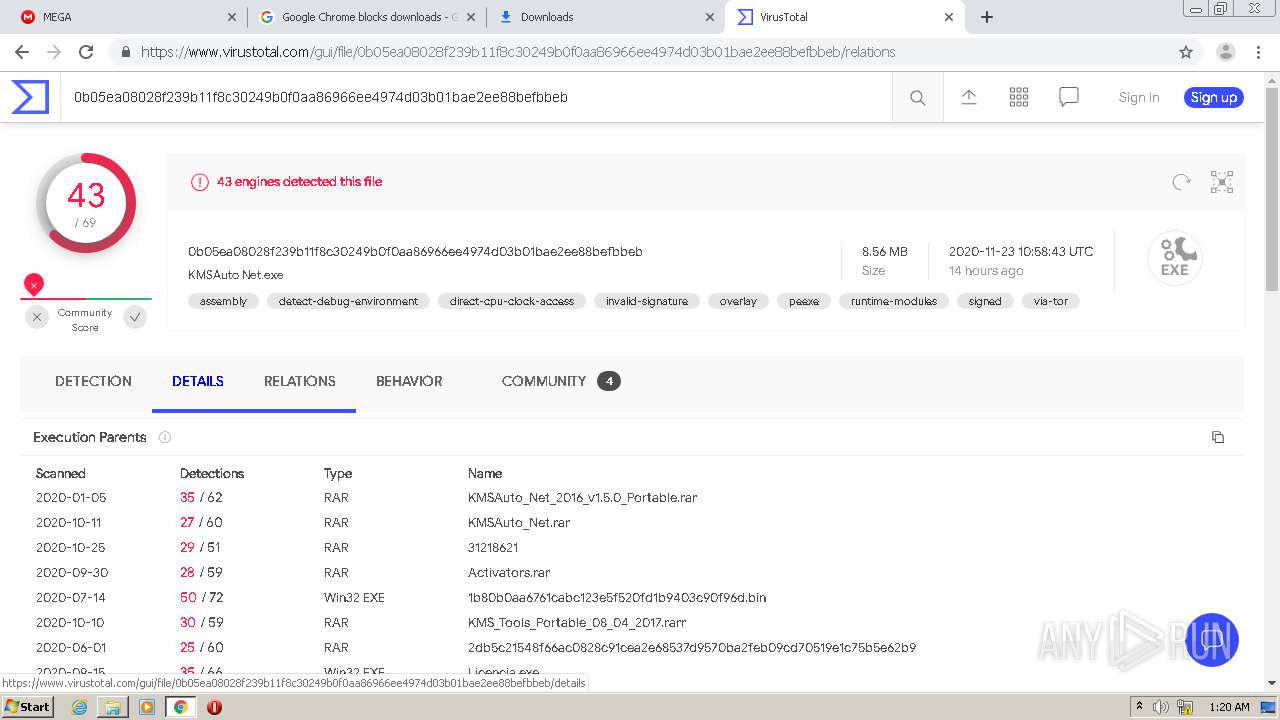
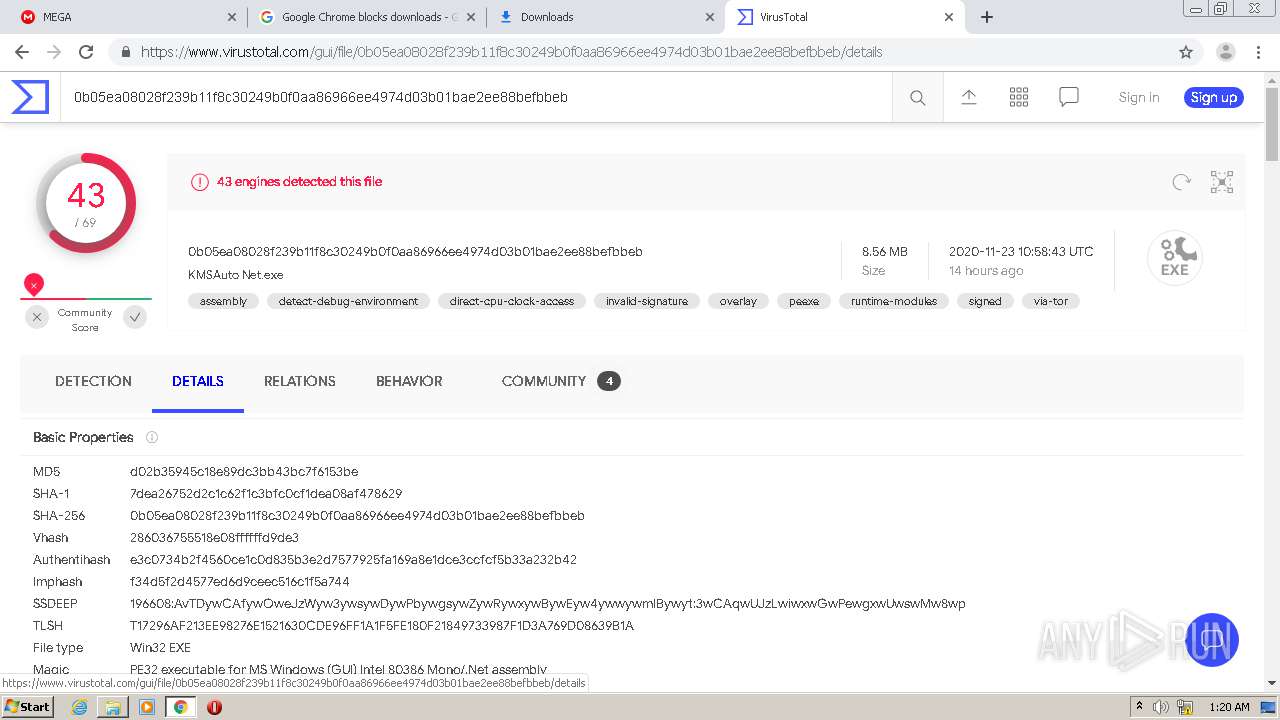
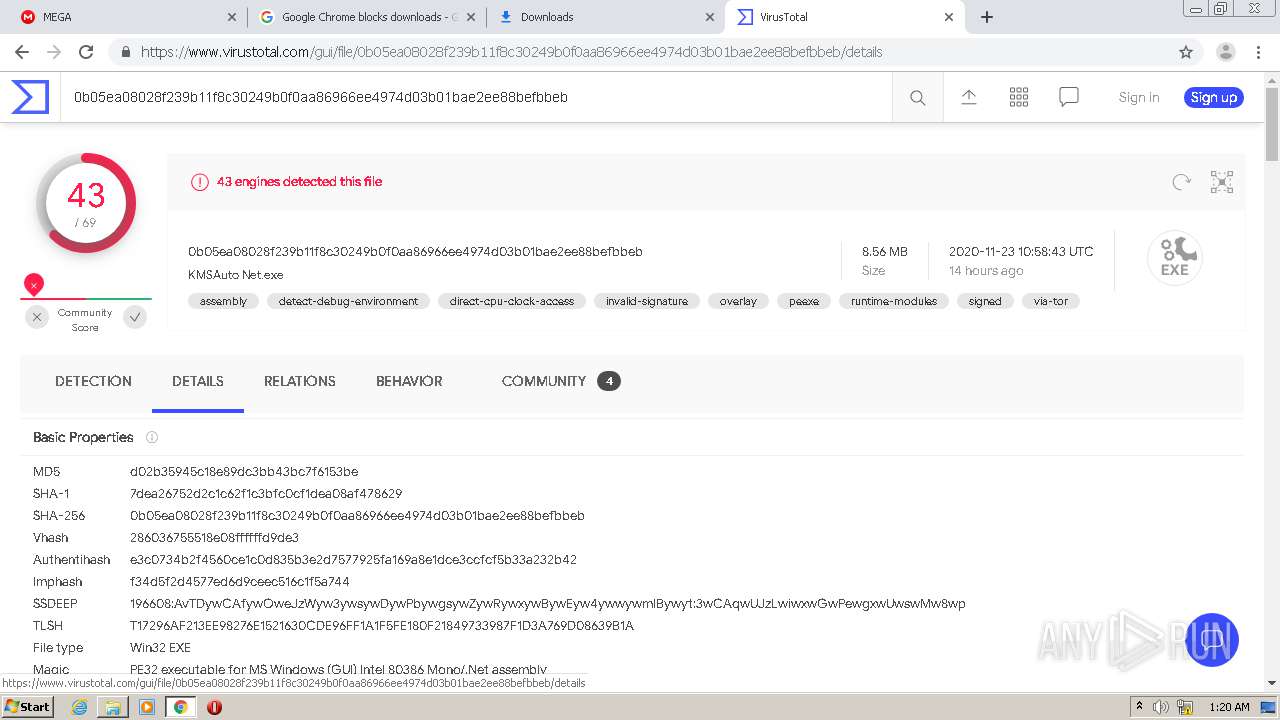
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2020, 01:18:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
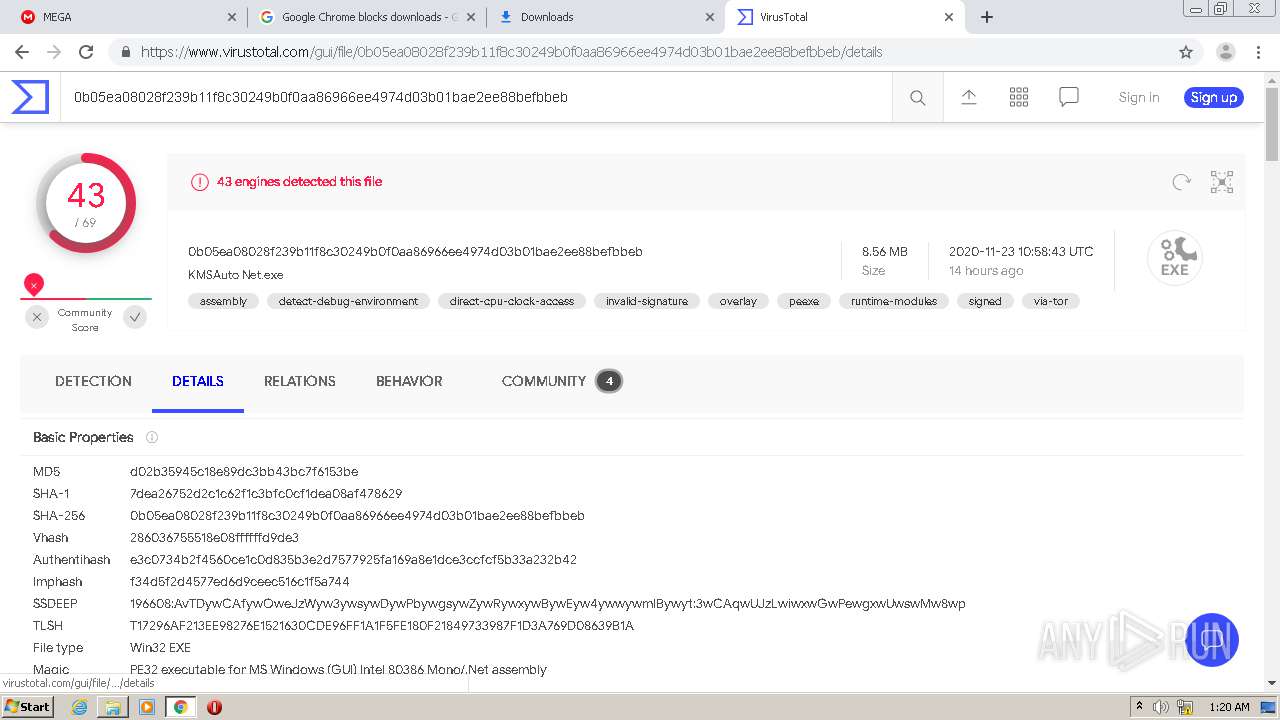
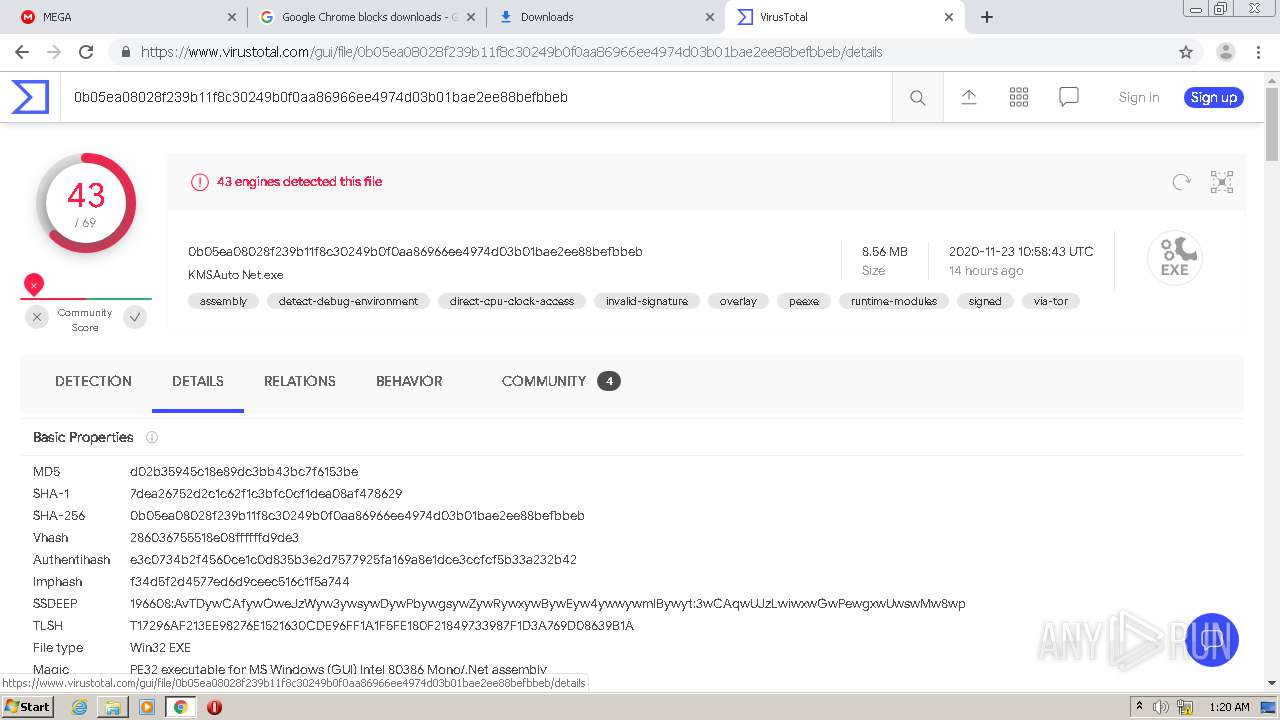
| MD5: | CF5F66FCFF082C19849BEDB129D5EDA1 |
| SHA1: | C4128763B8CA566FE42DD0A2F8661E920C972D68 |
| SHA256: | B29CB975B90F59130D21E2AA0DB41DF59BCE320805A2FE7646F52296E833B605 |
| SSDEEP: | 3:N8aOGMsnY9IlRX:2atfnYyll |
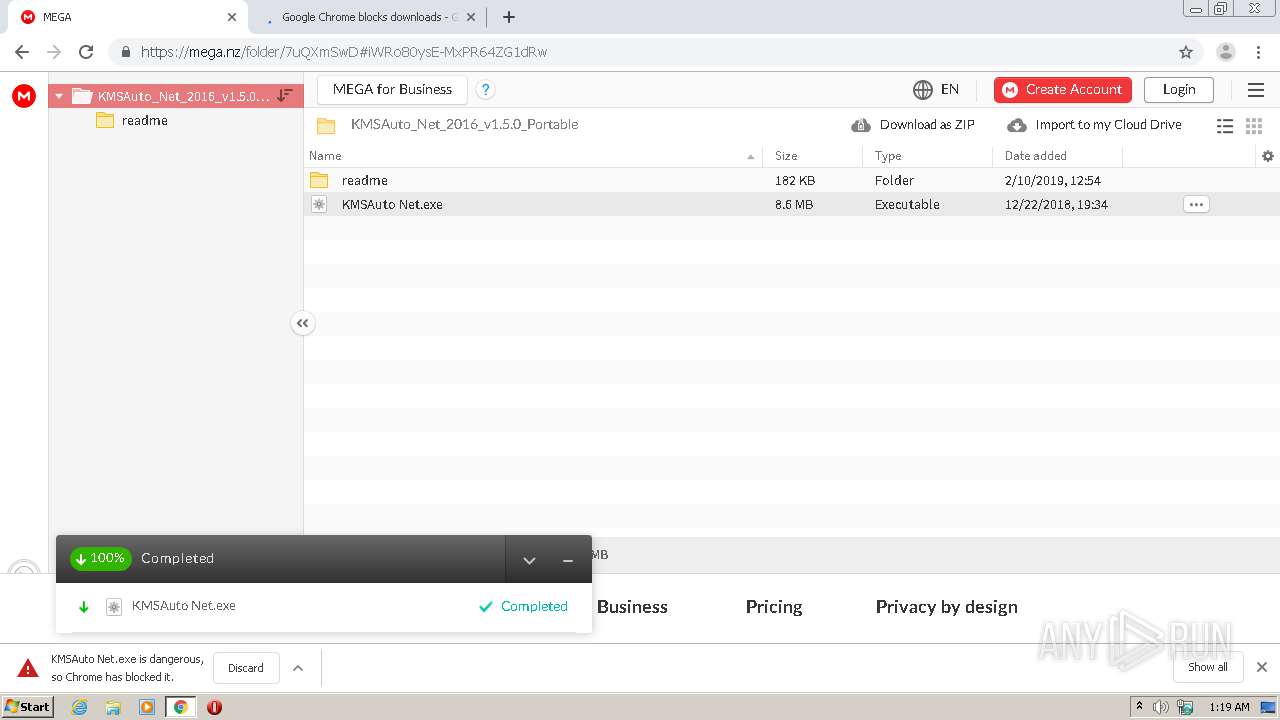
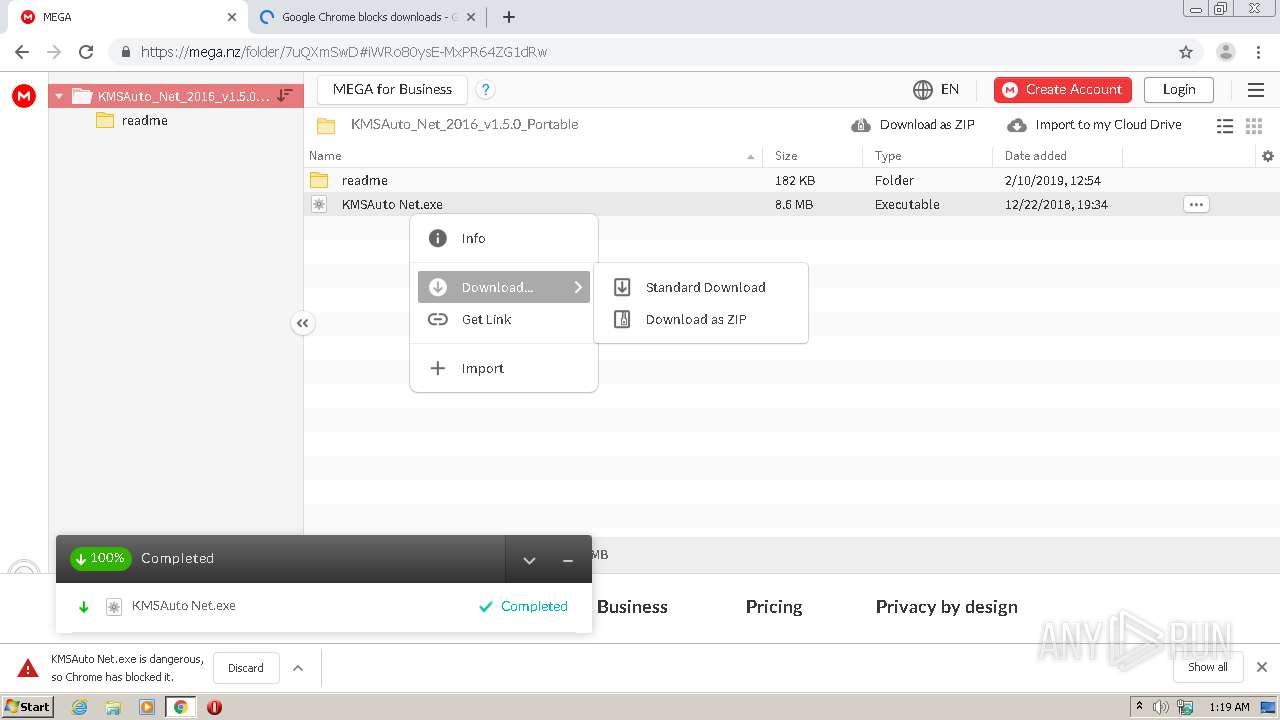
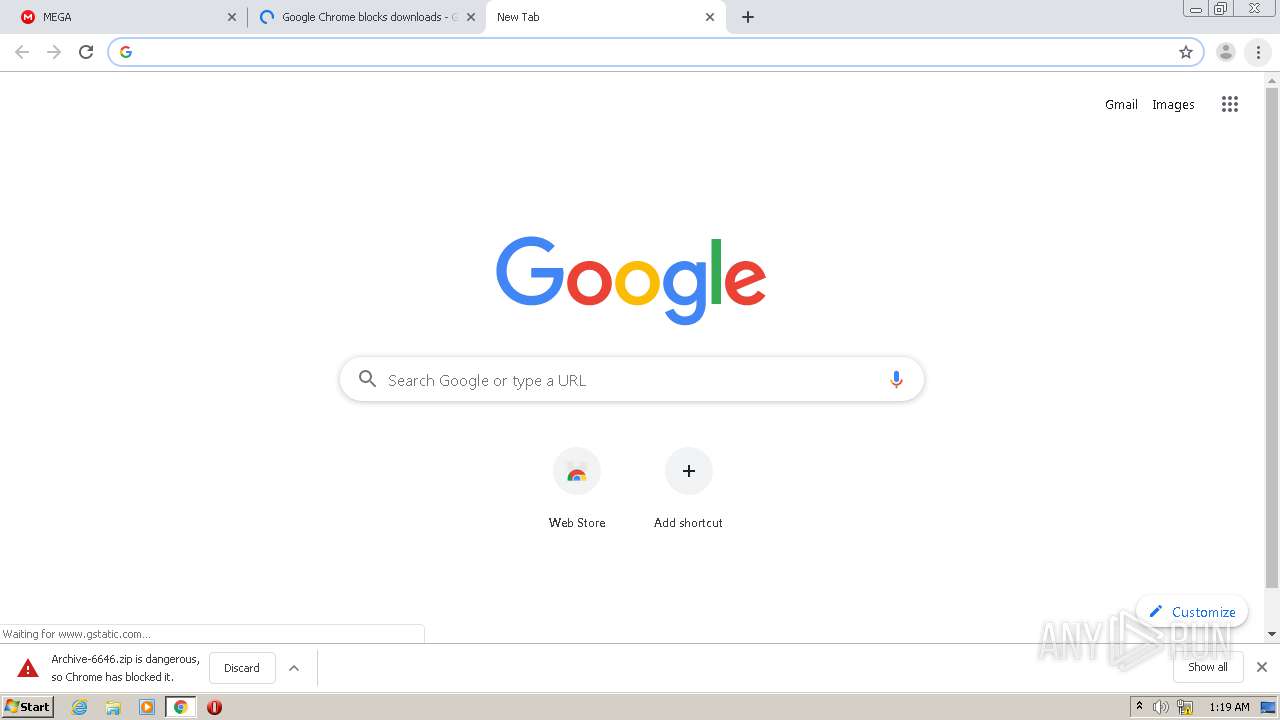
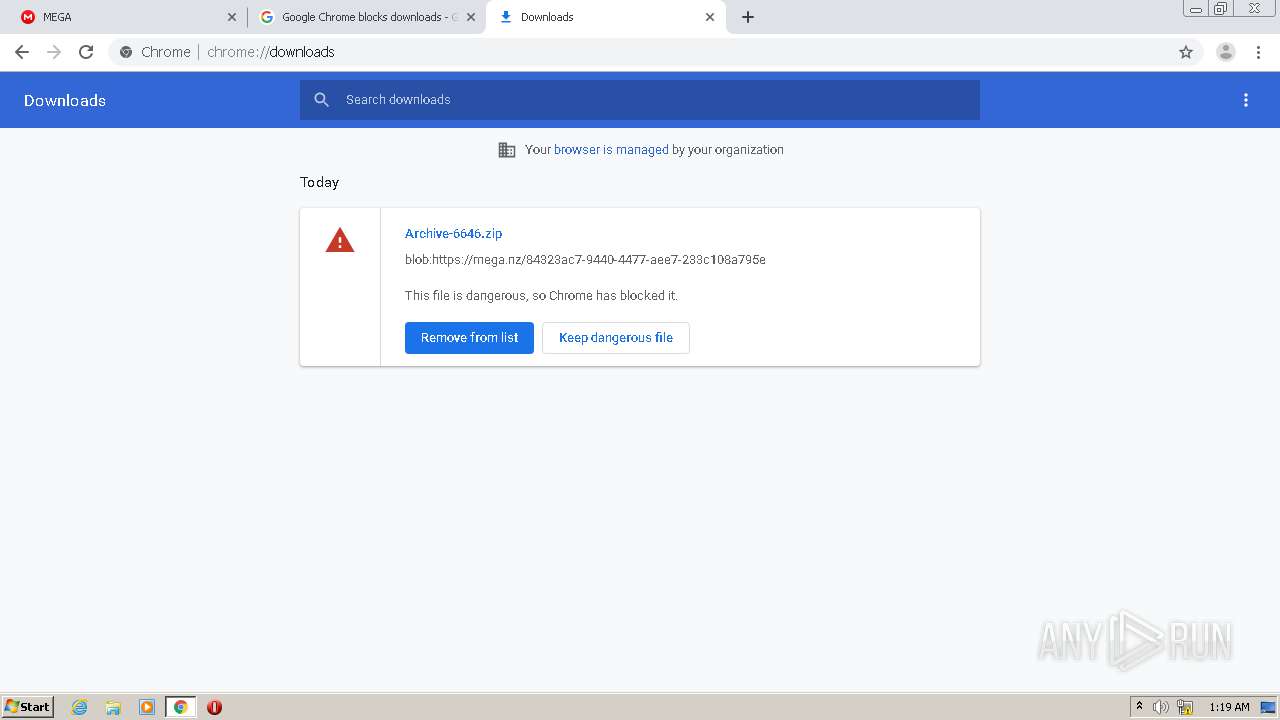
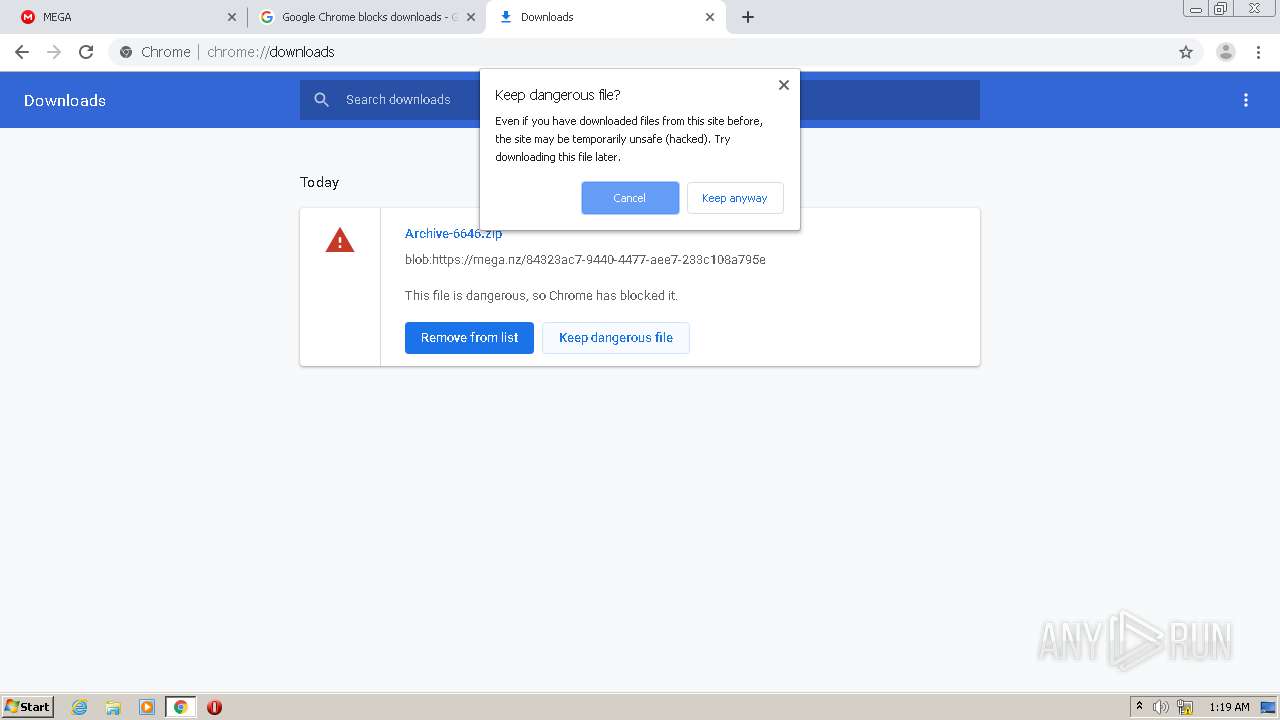
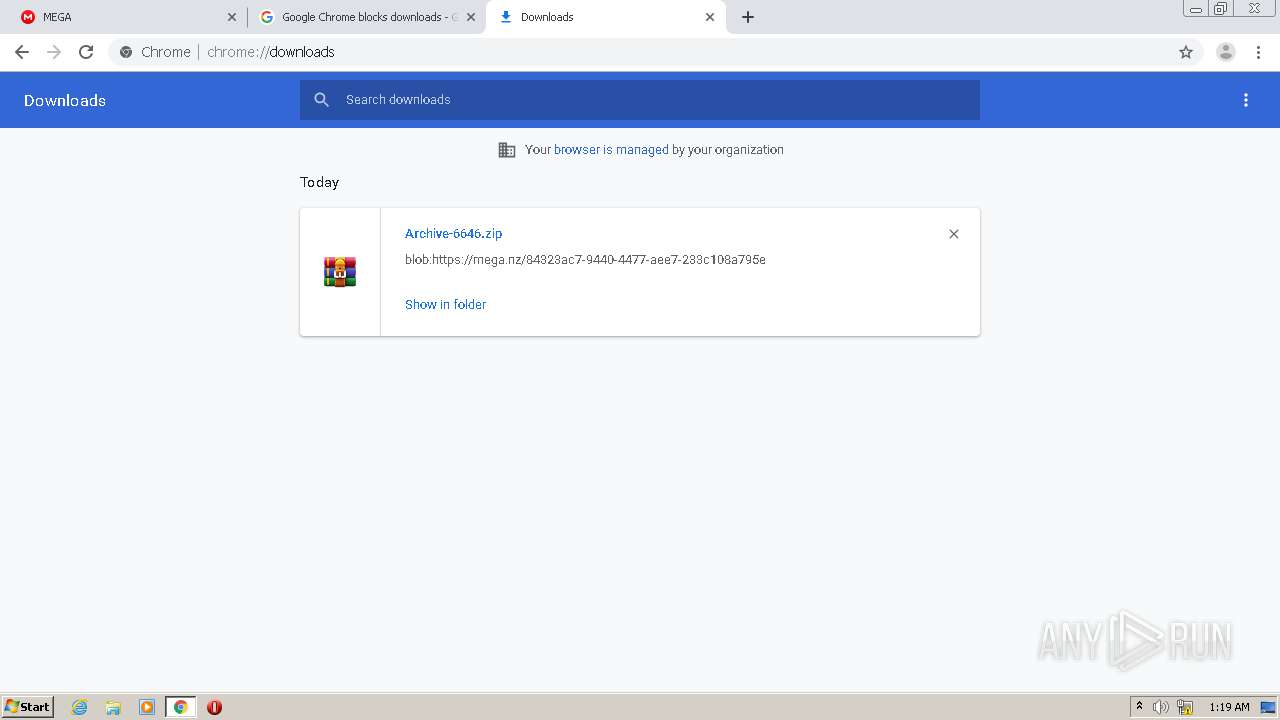
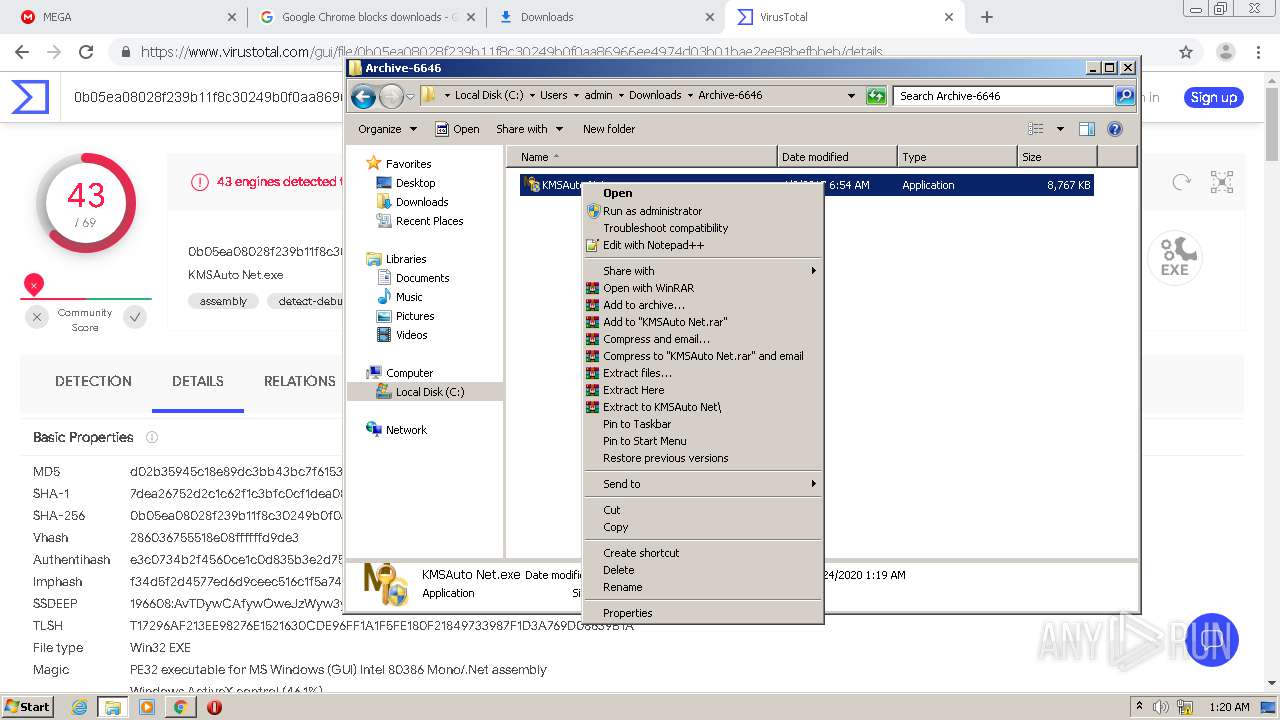
MALICIOUS
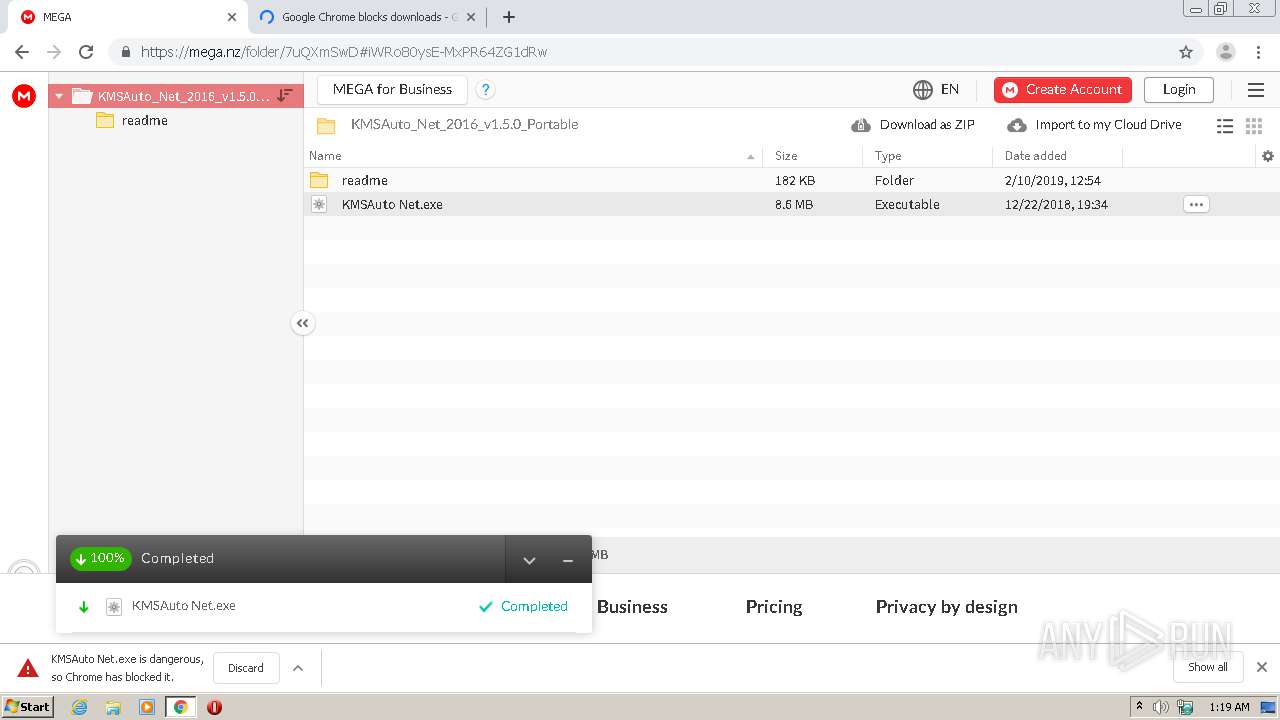
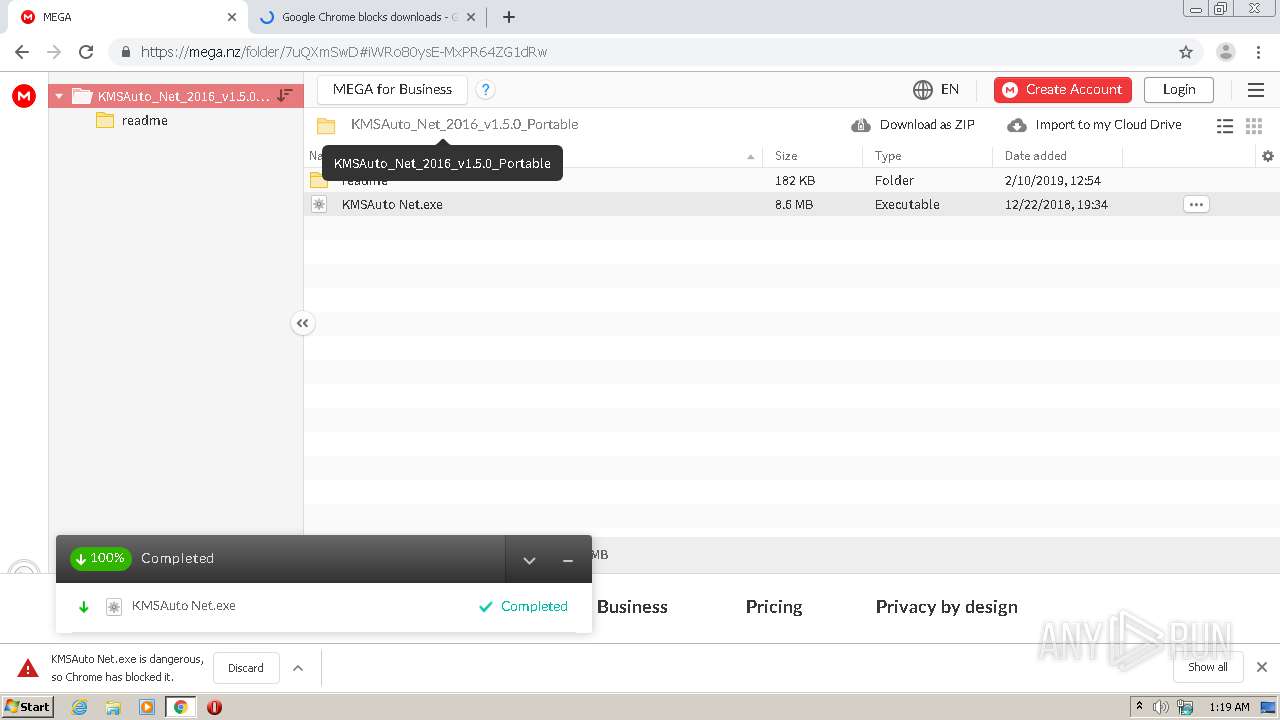
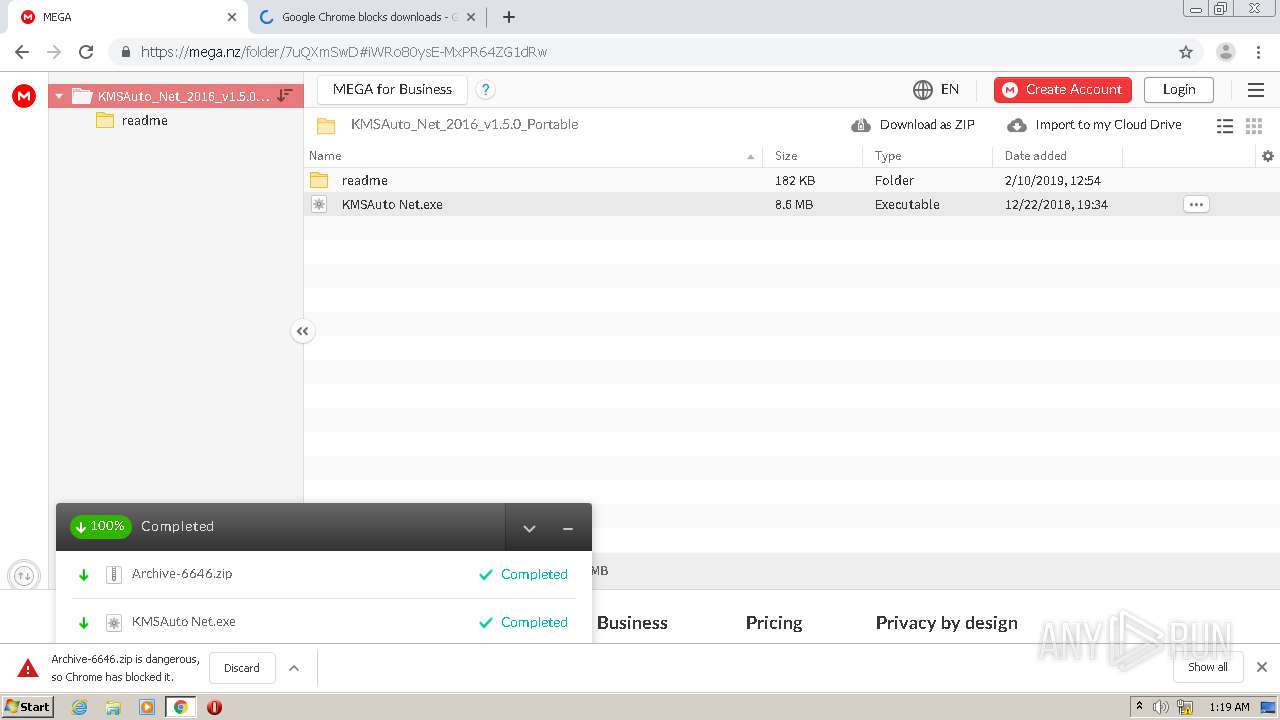
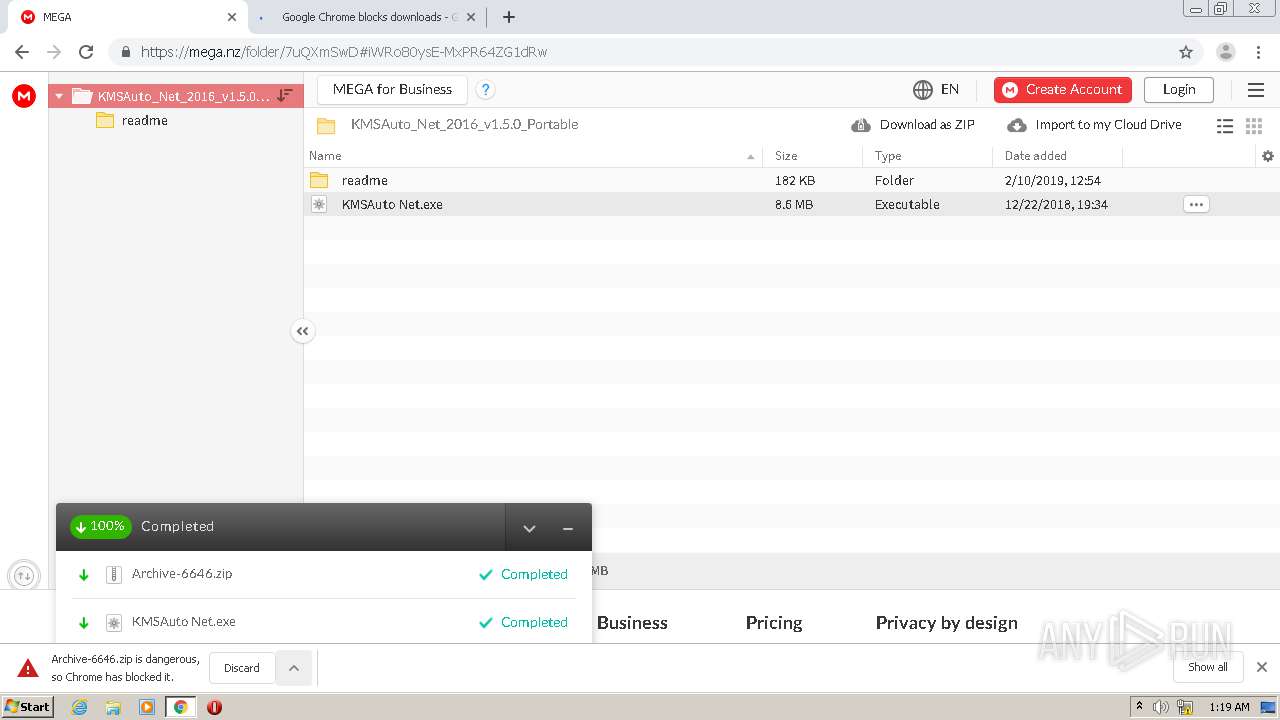
Drops executable file immediately after starts
- chrome.exe (PID: 3536)
- WinRAR.exe (PID: 3004)
Application was dropped or rewritten from another process
- KMSAuto Net.exe (PID: 876)
- KMSAuto Net.exe (PID: 2132)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3856)
- chrome.exe (PID: 3536)
- WinRAR.exe (PID: 3004)
Reads Microsoft Outlook installation path
- chrome.exe (PID: 3856)
Reads the computer name
- WinRAR.exe (PID: 3004)
- gup.exe (PID: 4060)
- notepad++.exe (PID: 3516)
- KMSAuto Net.exe (PID: 2132)
Checks supported languages
- WinRAR.exe (PID: 3004)
- notepad++.exe (PID: 3516)
- gup.exe (PID: 4060)
- KMSAuto Net.exe (PID: 2132)
- cmd.exe (PID: 3804)
- cmd.exe (PID: 3376)
- cmd.exe (PID: 3656)
- cmd.exe (PID: 2324)
Drops a file with a compile date too recent
- chrome.exe (PID: 3856)
Reads default file associations for system extensions
- chrome.exe (PID: 772)
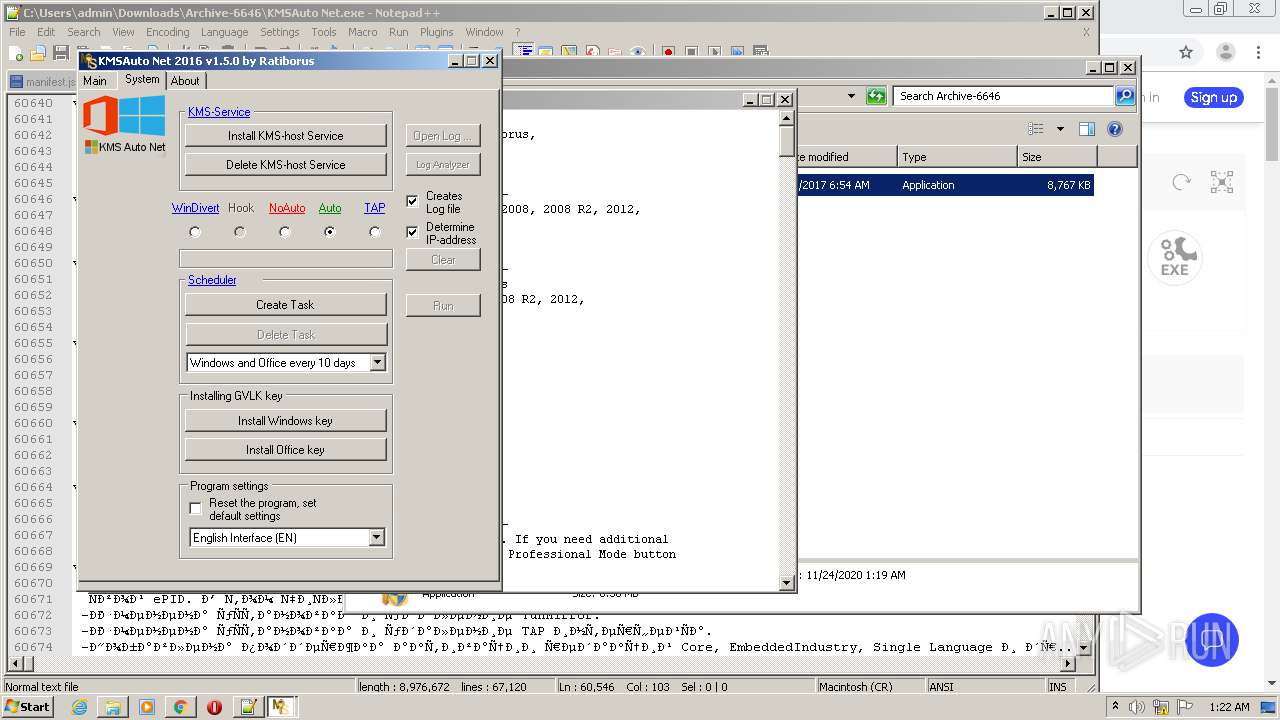
Starts CMD.EXE for self-deleting
- KMSAuto Net.exe (PID: 2132)
Starts CMD.EXE for commands execution
- KMSAuto Net.exe (PID: 2132)
Reads Environment values
- KMSAuto Net.exe (PID: 2132)
Reads internet explorer settings
- KMSAuto Net.exe (PID: 2132)
INFO
Reads the hosts file
- chrome.exe (PID: 3856)
- chrome.exe (PID: 2668)
Reads the computer name
- chrome.exe (PID: 2668)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 2324)
- chrome.exe (PID: 3176)
- chrome.exe (PID: 3824)
- chrome.exe (PID: 864)
- chrome.exe (PID: 2644)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 3900)
- chrome.exe (PID: 1792)
- chrome.exe (PID: 772)
- explorer.exe (PID: 3340)
Checks supported languages
- chrome.exe (PID: 2056)
- chrome.exe (PID: 3632)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 1836)
- chrome.exe (PID: 2916)
- chrome.exe (PID: 2976)
- chrome.exe (PID: 3536)
- chrome.exe (PID: 2516)
- chrome.exe (PID: 3388)
- chrome.exe (PID: 2404)
- chrome.exe (PID: 1828)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 3272)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 2936)
- chrome.exe (PID: 3816)
- chrome.exe (PID: 3308)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 3044)
- chrome.exe (PID: 1716)
- chrome.exe (PID: 772)
Reads settings of System Certificates
- chrome.exe (PID: 2668)
- chrome.exe (PID: 3856)
Checks Windows Trust Settings
- chrome.exe (PID: 3856)
Application launched itself
- chrome.exe (PID: 3856)
Reads the date of Windows installation
- chrome.exe (PID: 3928)
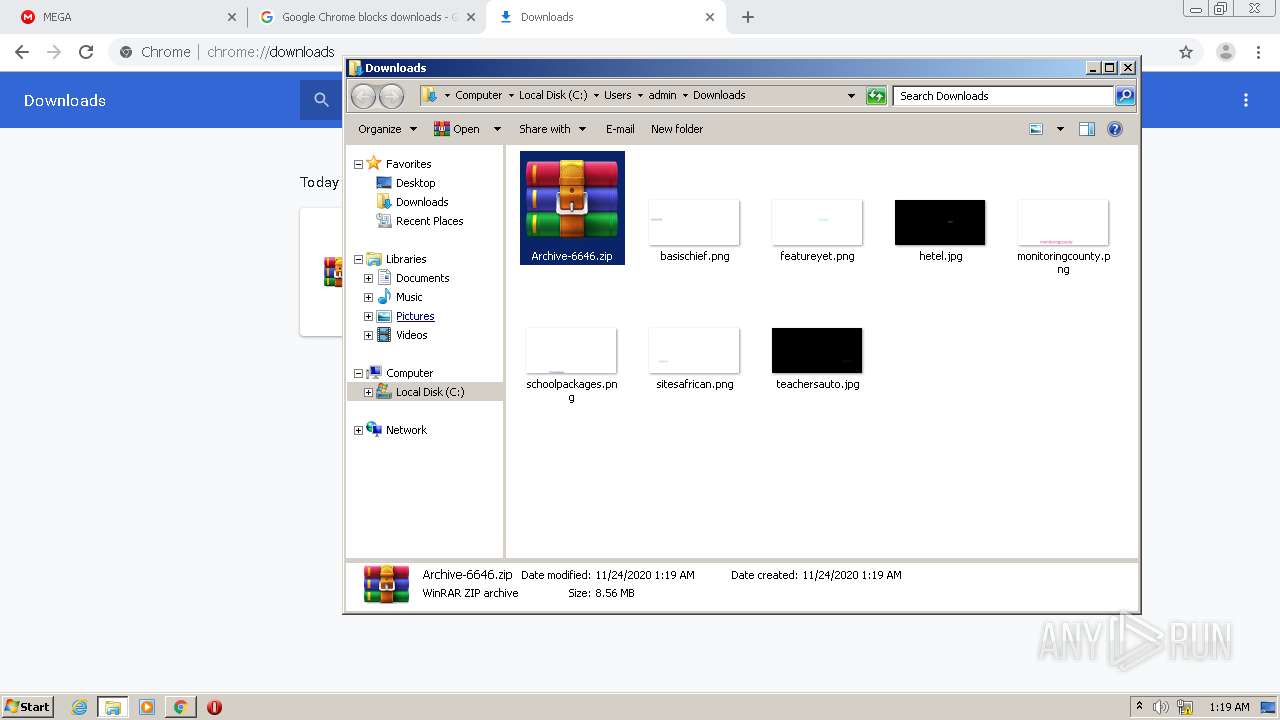
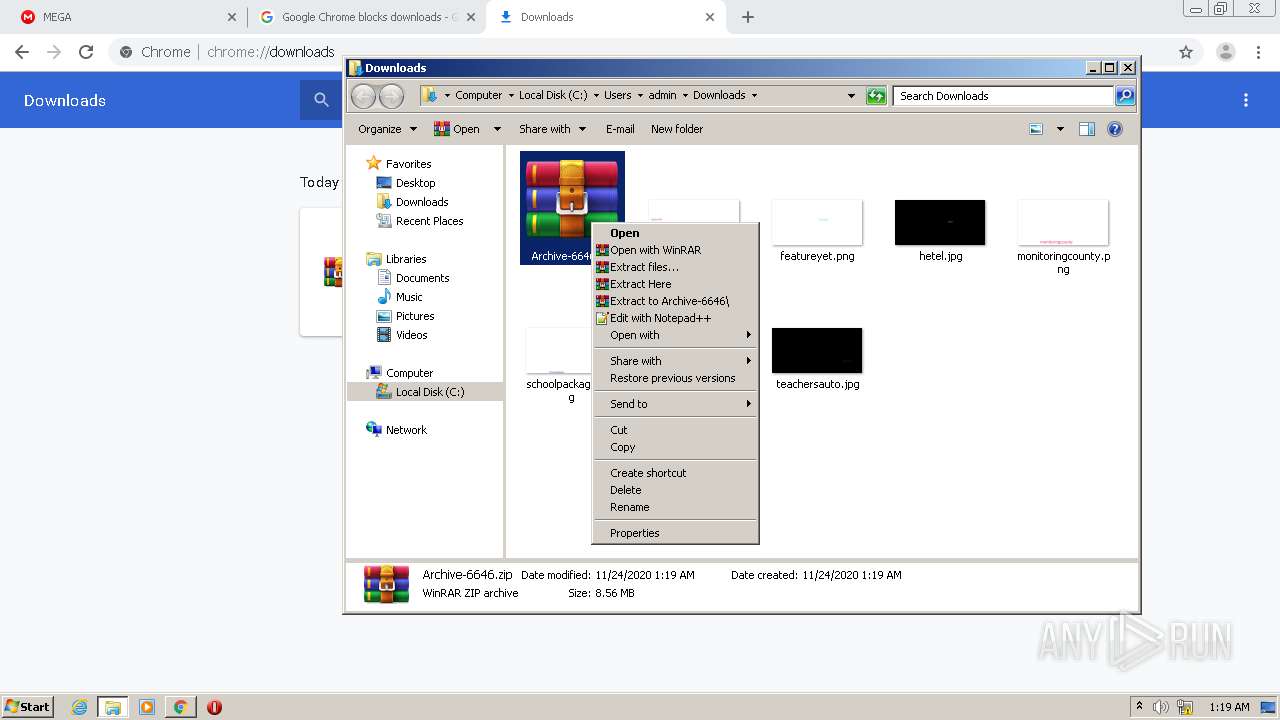
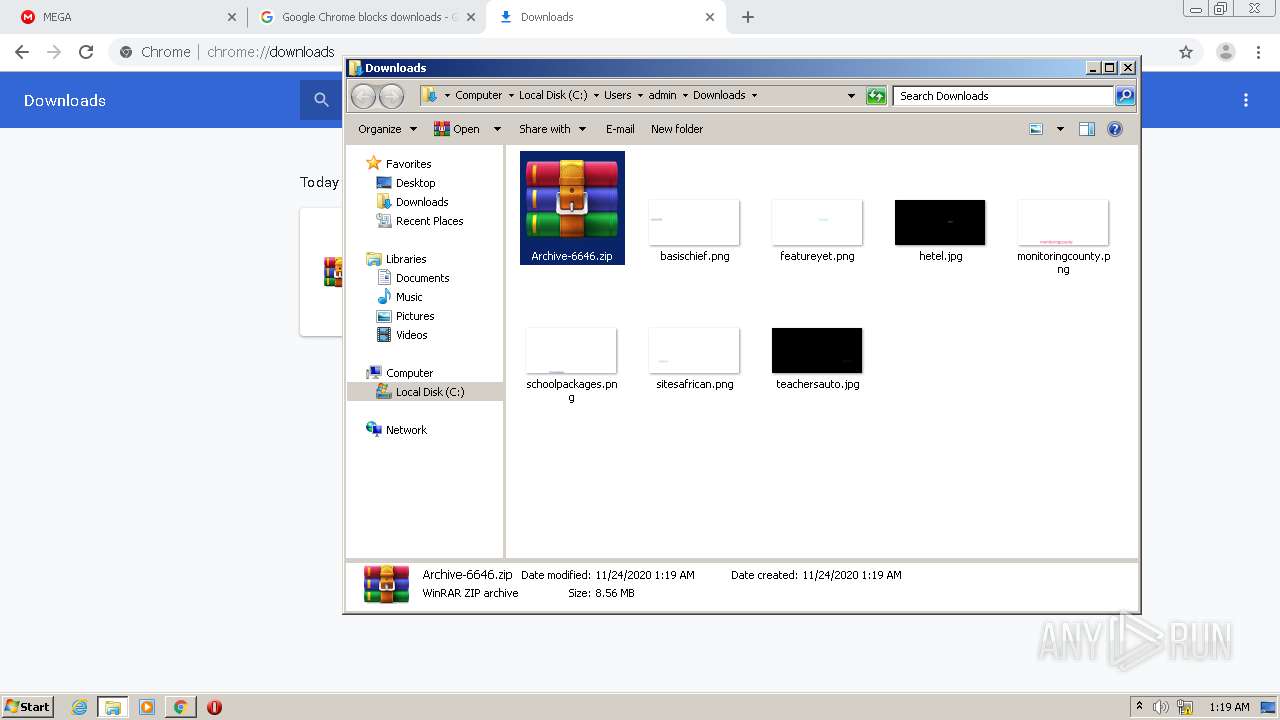
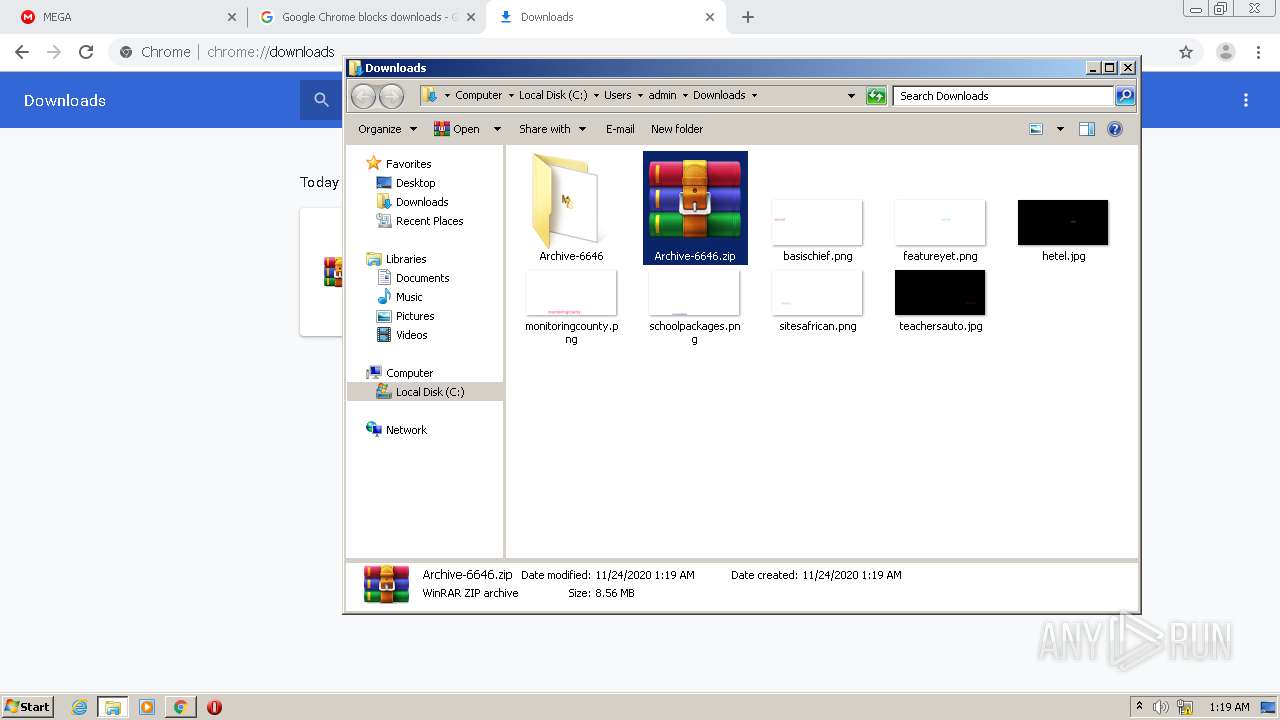
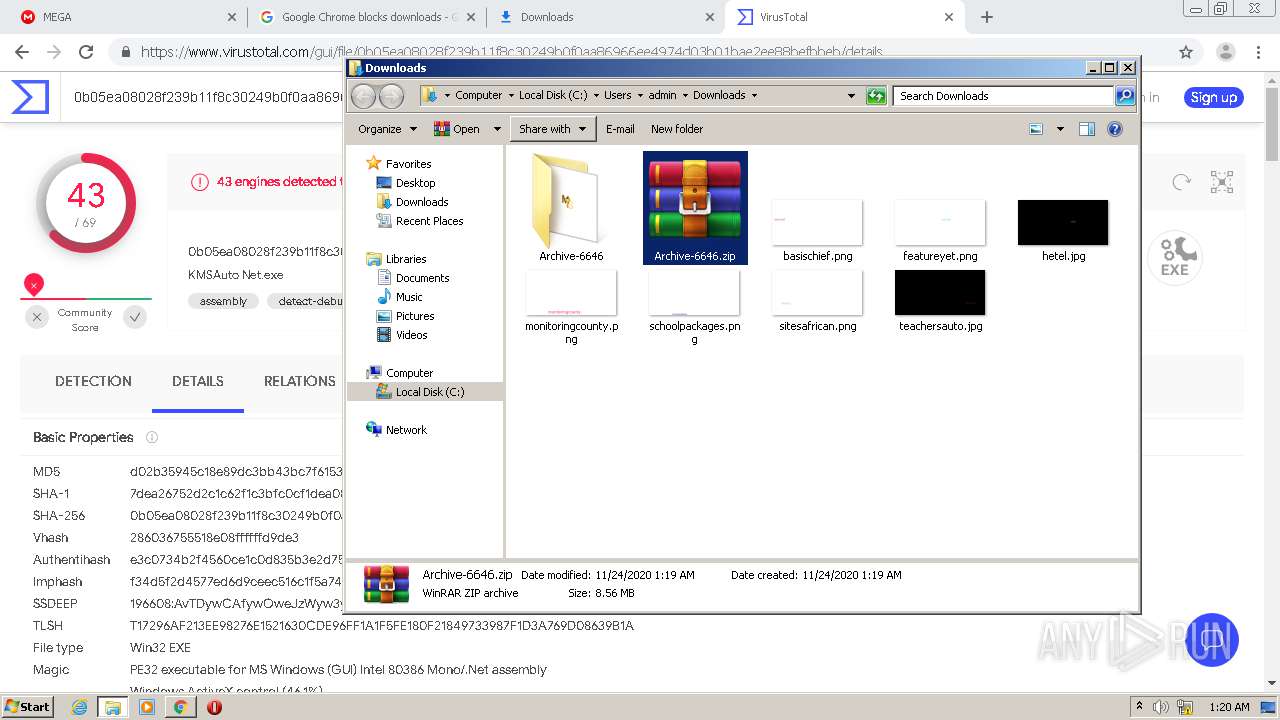
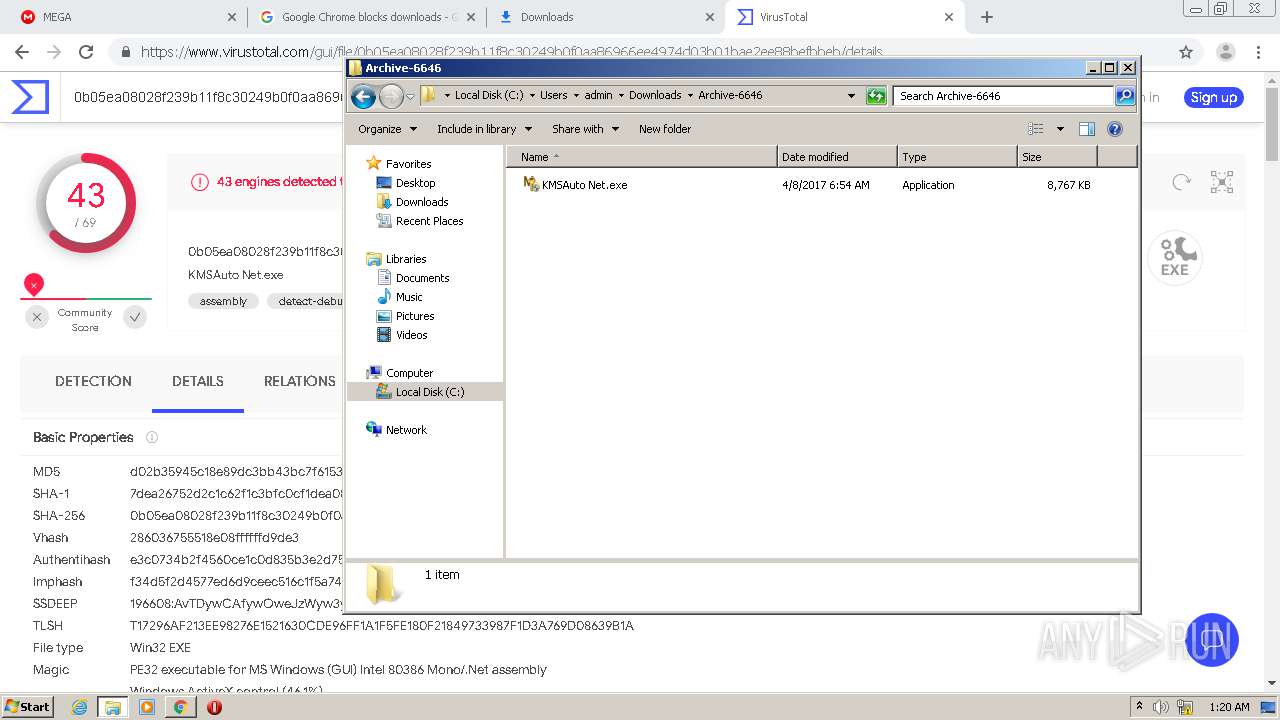
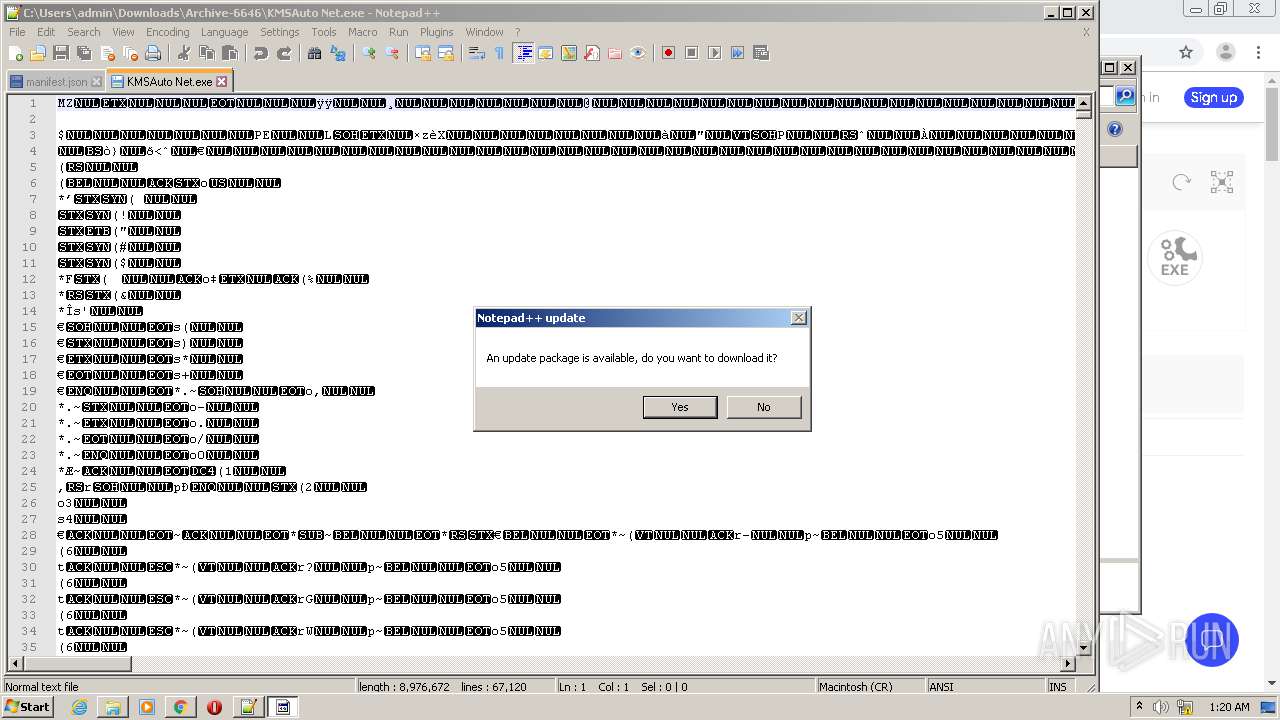
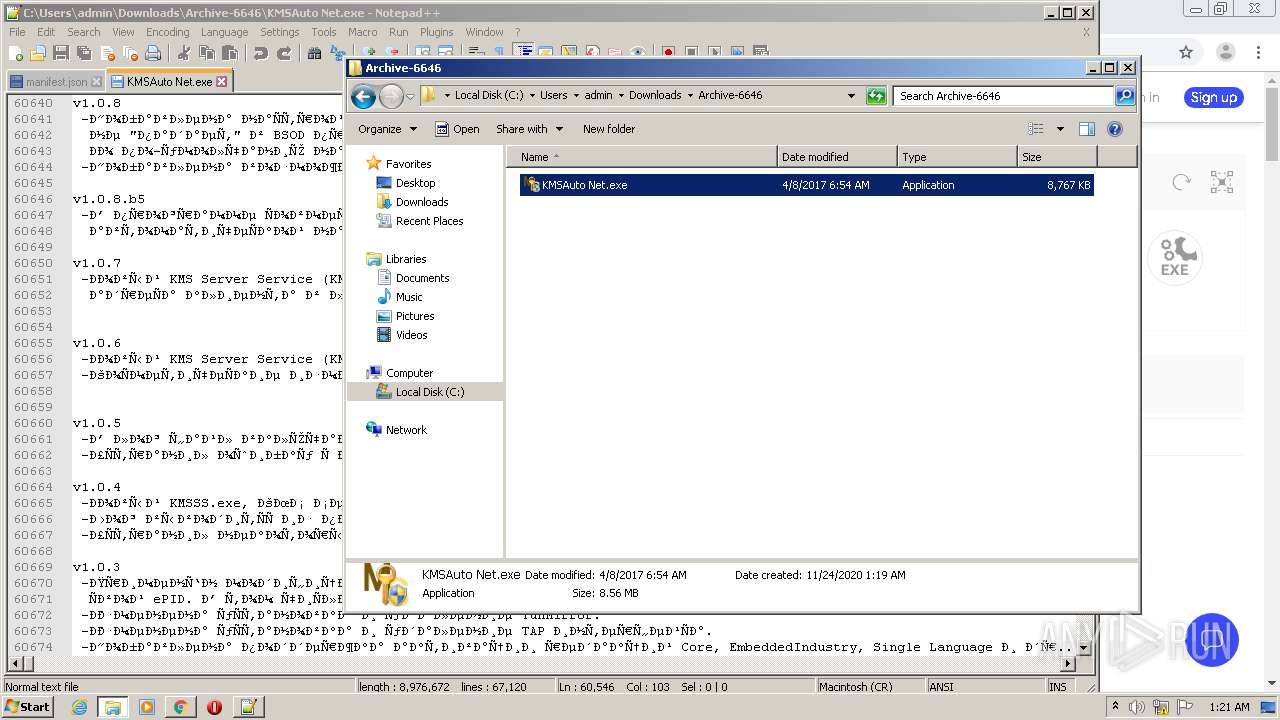
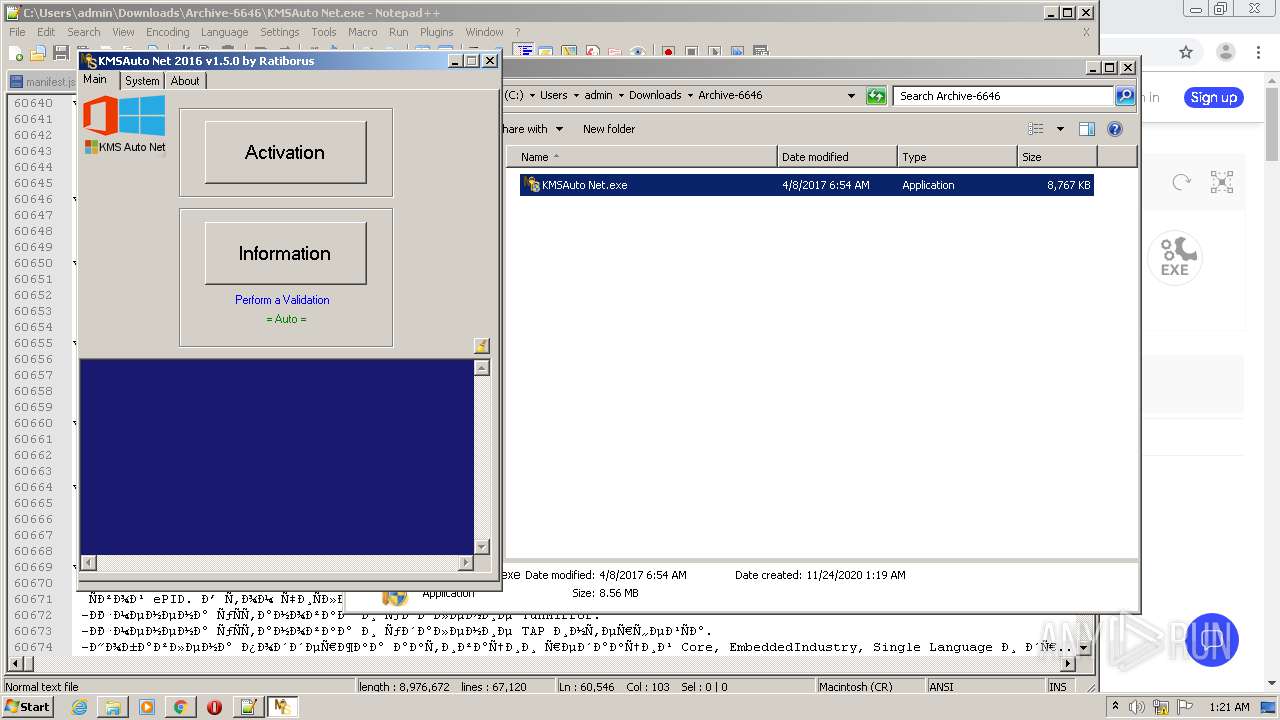
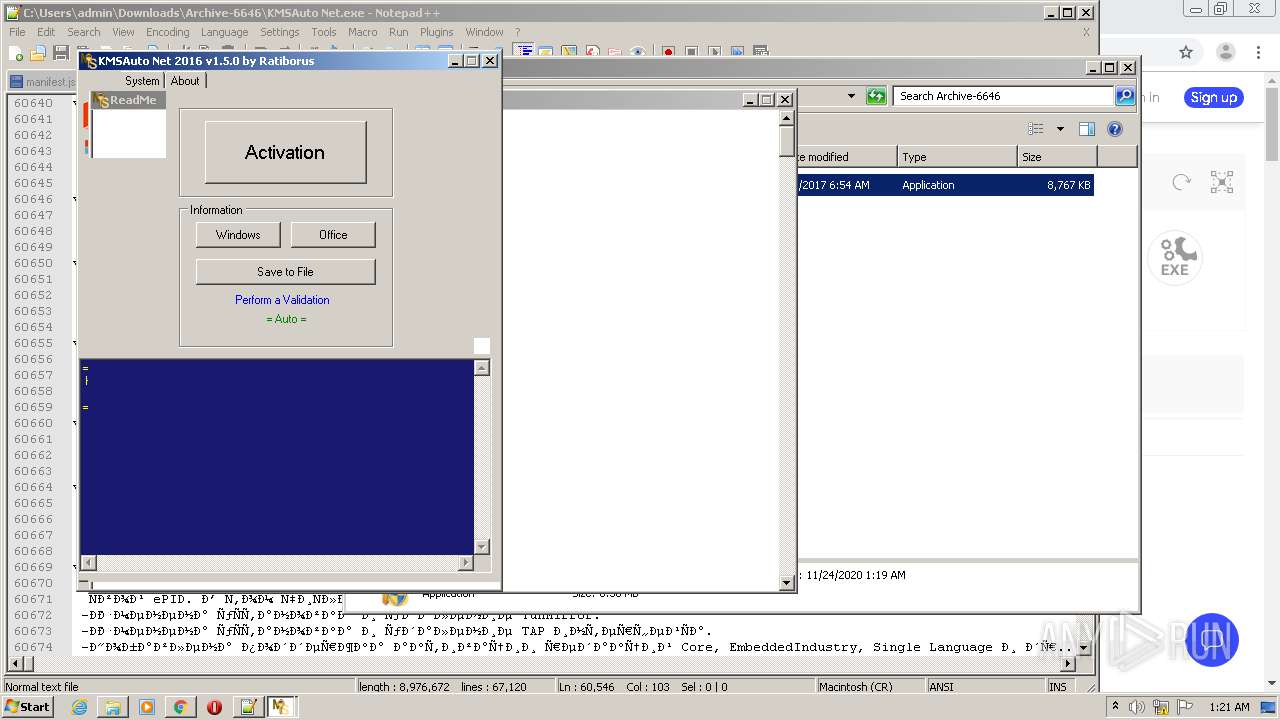
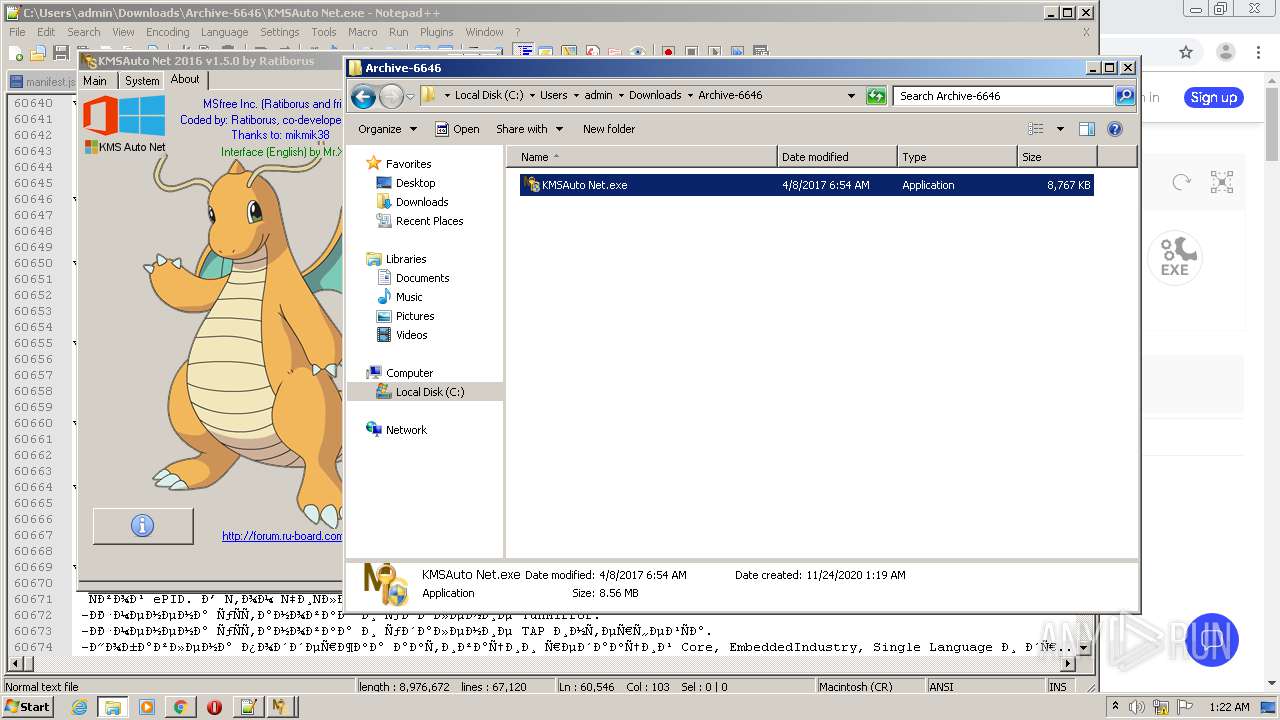
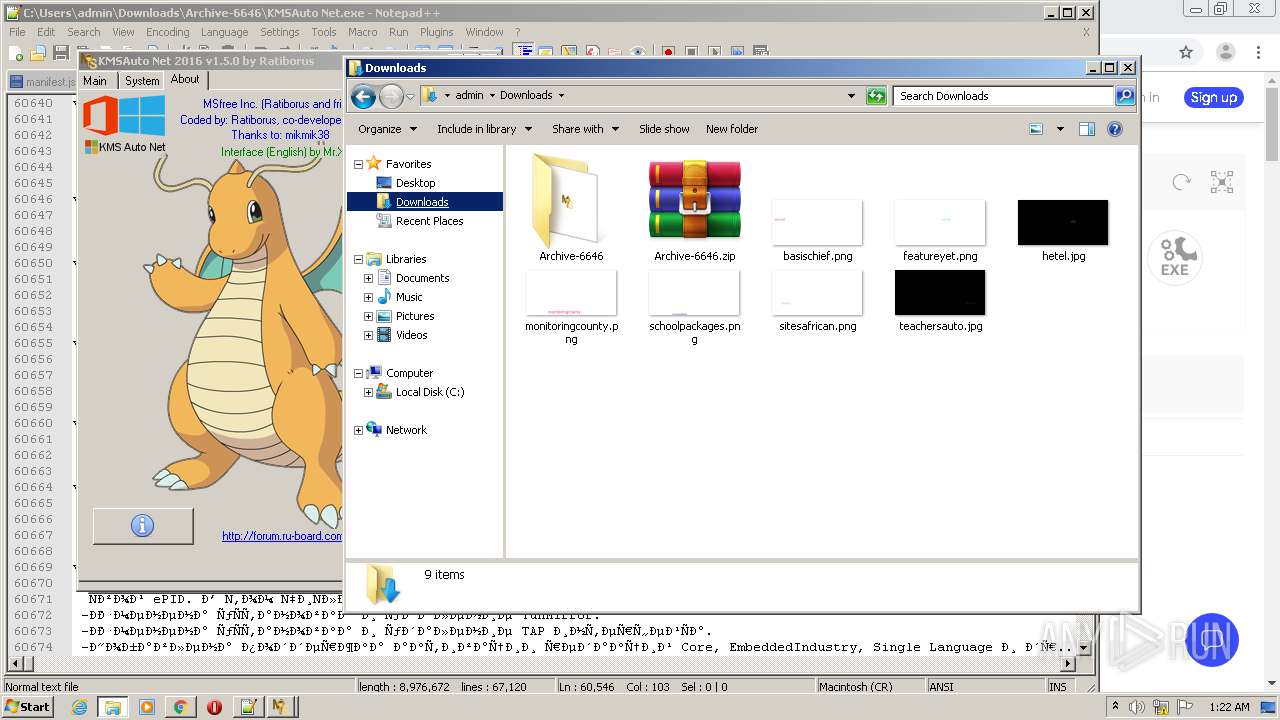
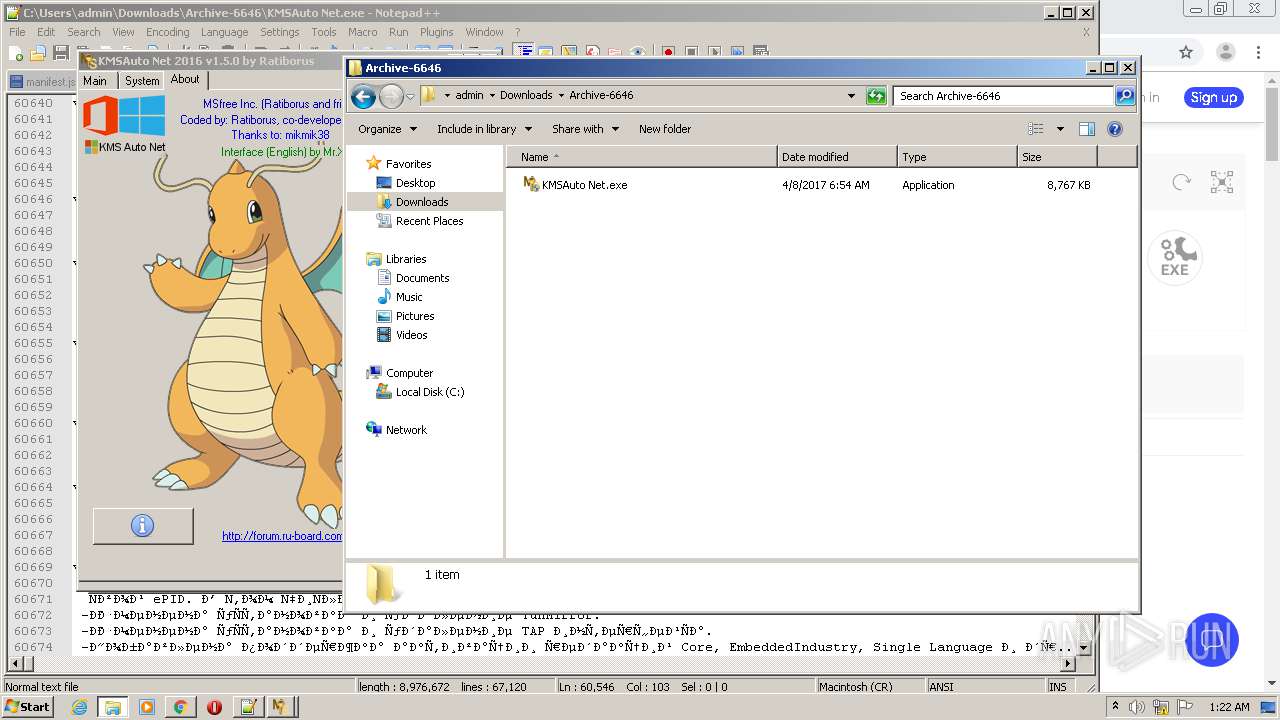
Manual execution by user
- WinRAR.exe (PID: 3004)
- notepad++.exe (PID: 3516)
- KMSAuto Net.exe (PID: 876)
- KMSAuto Net.exe (PID: 2132)
- explorer.exe (PID: 3340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
98
Monitored processes
46
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1088,7190833191316892724,9640826039353717243,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13994220338000838088 --mojo-platform-channel-handle=4860 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1088,7190833191316892724,9640826039353717243,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4654759702350503134 --mojo-platform-channel-handle=2704 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
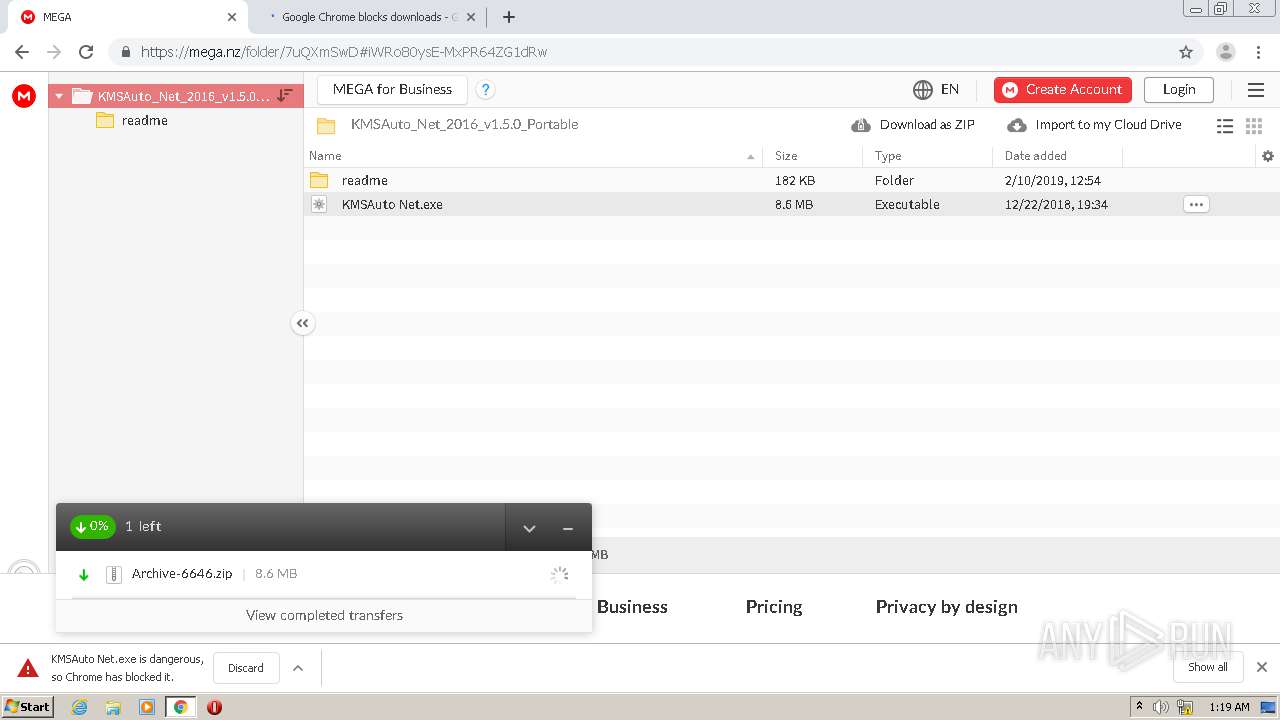
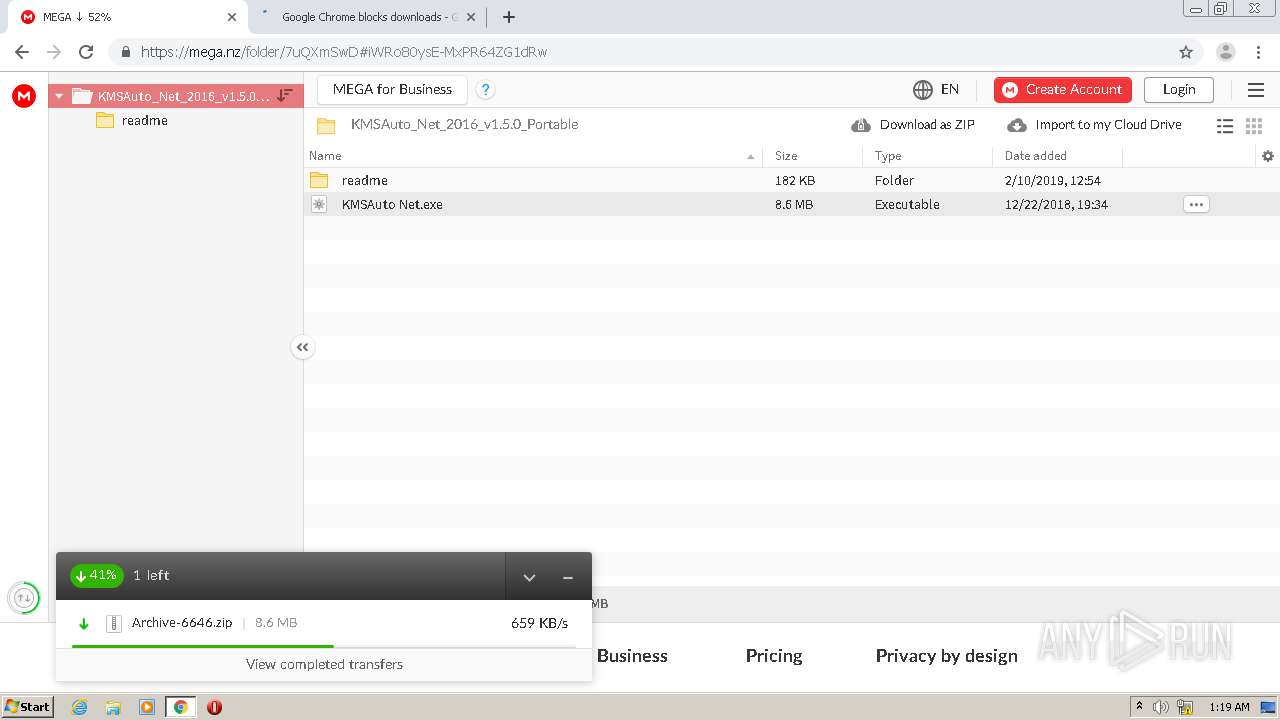
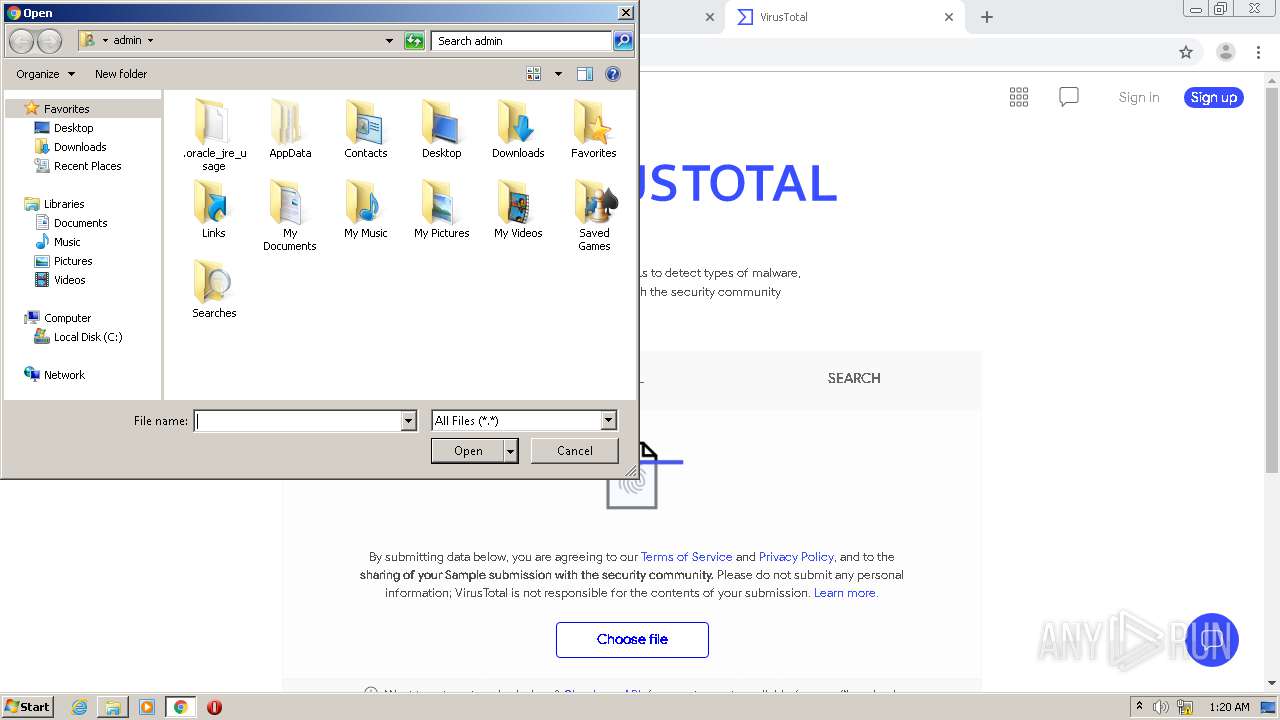
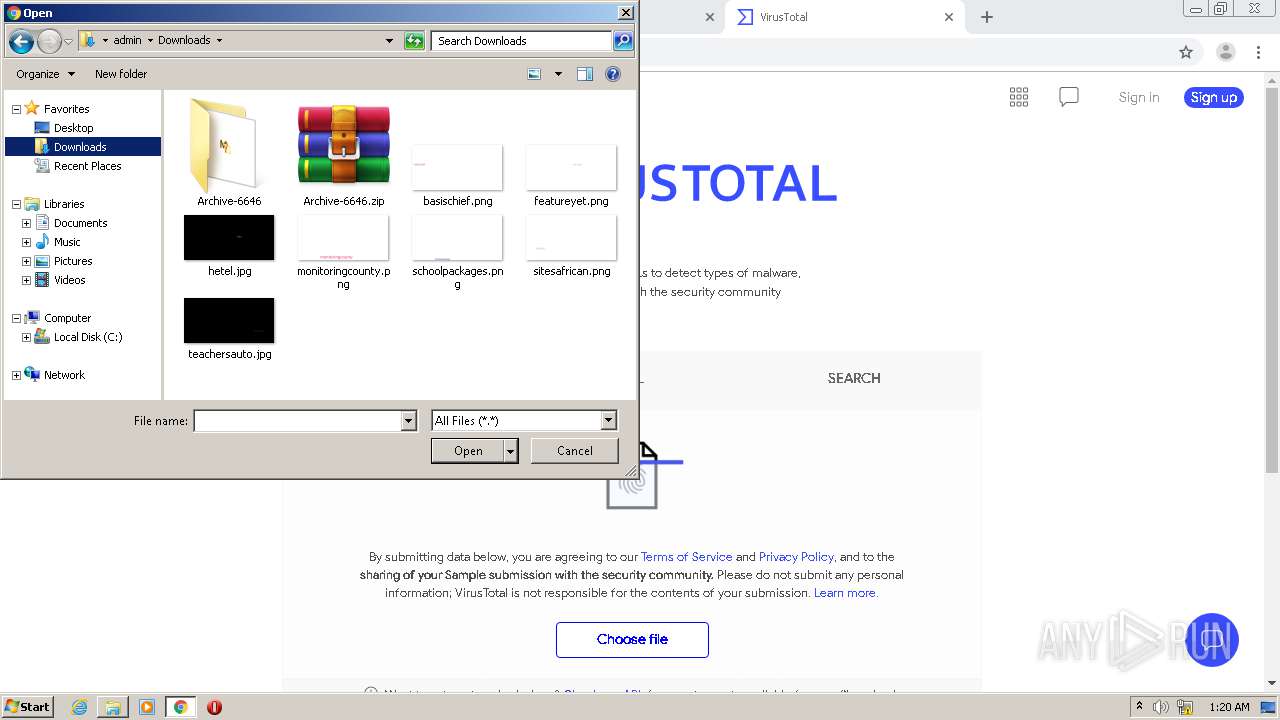
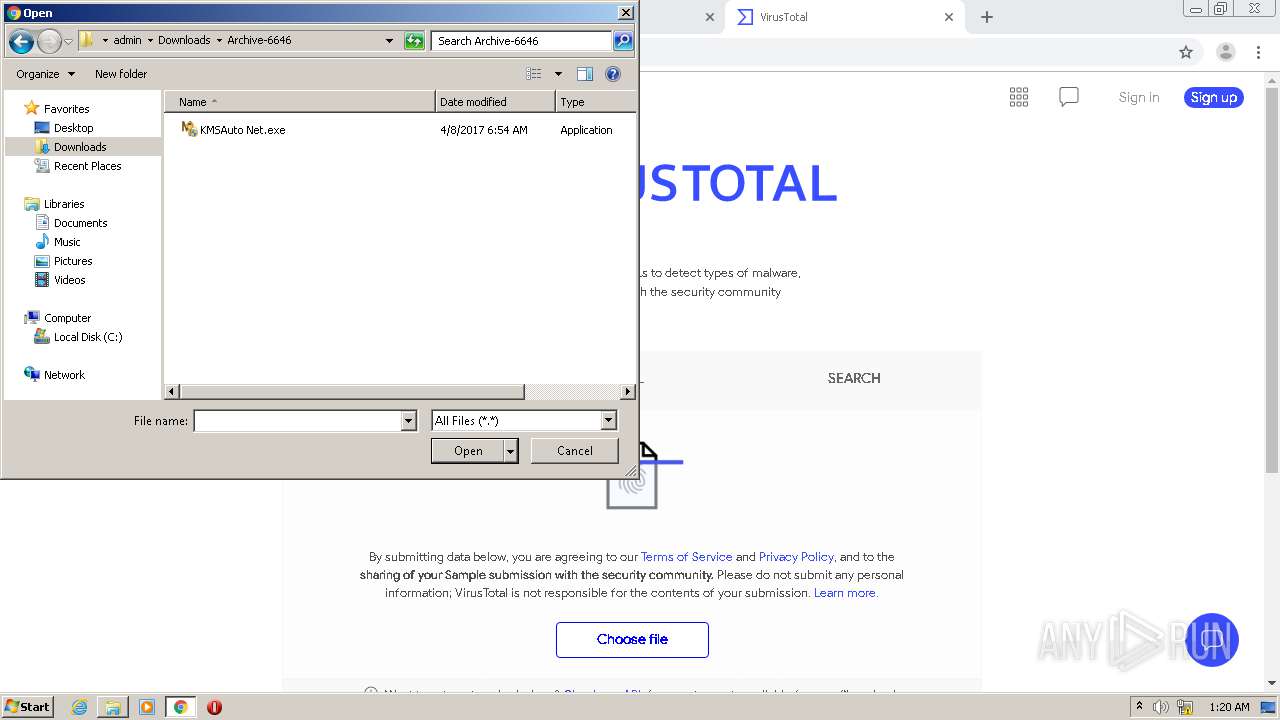
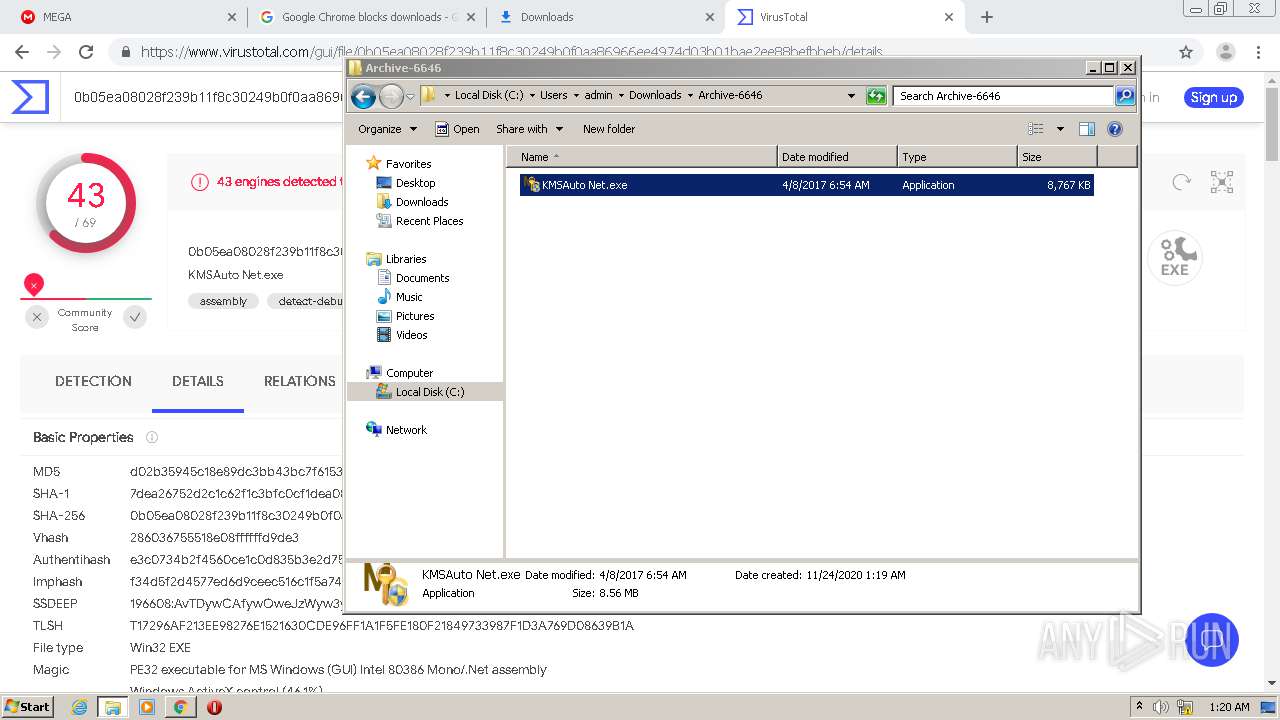
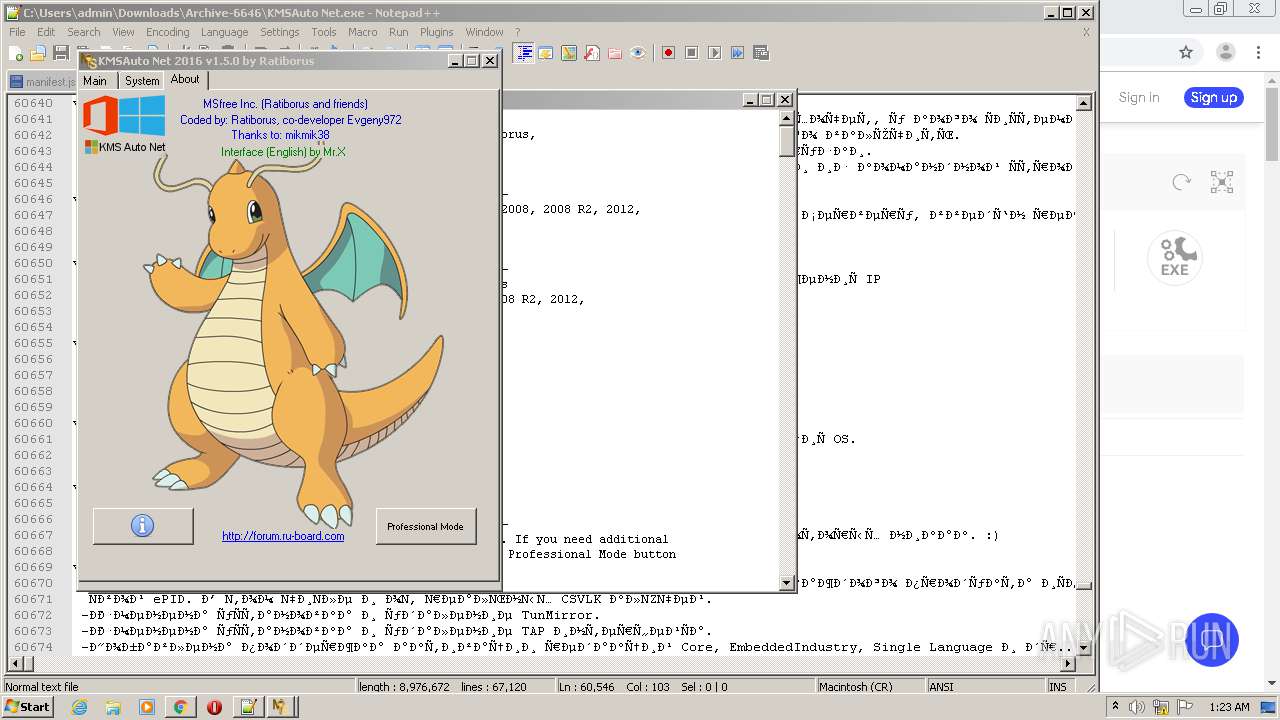
| 876 | "C:\Users\admin\Downloads\Archive-6646\KMSAuto Net.exe" | C:\Users\admin\Downloads\Archive-6646\KMSAuto Net.exe | — | Explorer.EXE | |||||||||||
User: admin Company: MSFree Inc. Integrity Level: MEDIUM Description: KMSAuto Net Exit code: 3221226540 Version: 1.5.0 Modules
| |||||||||||||||
| 1716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1088,7190833191316892724,9640826039353717243,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=684827163018250322 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1088,7190833191316892724,9640826039353717243,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=802190331569833600 --mojo-platform-channel-handle=4000 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1088,7190833191316892724,9640826039353717243,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10004249429690684197 --mojo-platform-channel-handle=4024 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1088,7190833191316892724,9640826039353717243,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18126517486018921087 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1088,7190833191316892724,9640826039353717243,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5363038809817862937 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2164 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2132 | "C:\Users\admin\Downloads\Archive-6646\KMSAuto Net.exe" | C:\Users\admin\Downloads\Archive-6646\KMSAuto Net.exe | Explorer.EXE | ||||||||||||
User: admin Company: MSFree Inc. Integrity Level: HIGH Description: KMSAuto Net Exit code: 3221225547 Version: 1.5.0 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3860 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
23 425
Read events
23 060
Write events
361
Delete events
4
Modification events
| (PID) Process: | (3856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
| (PID) Process: | (3856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3856) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
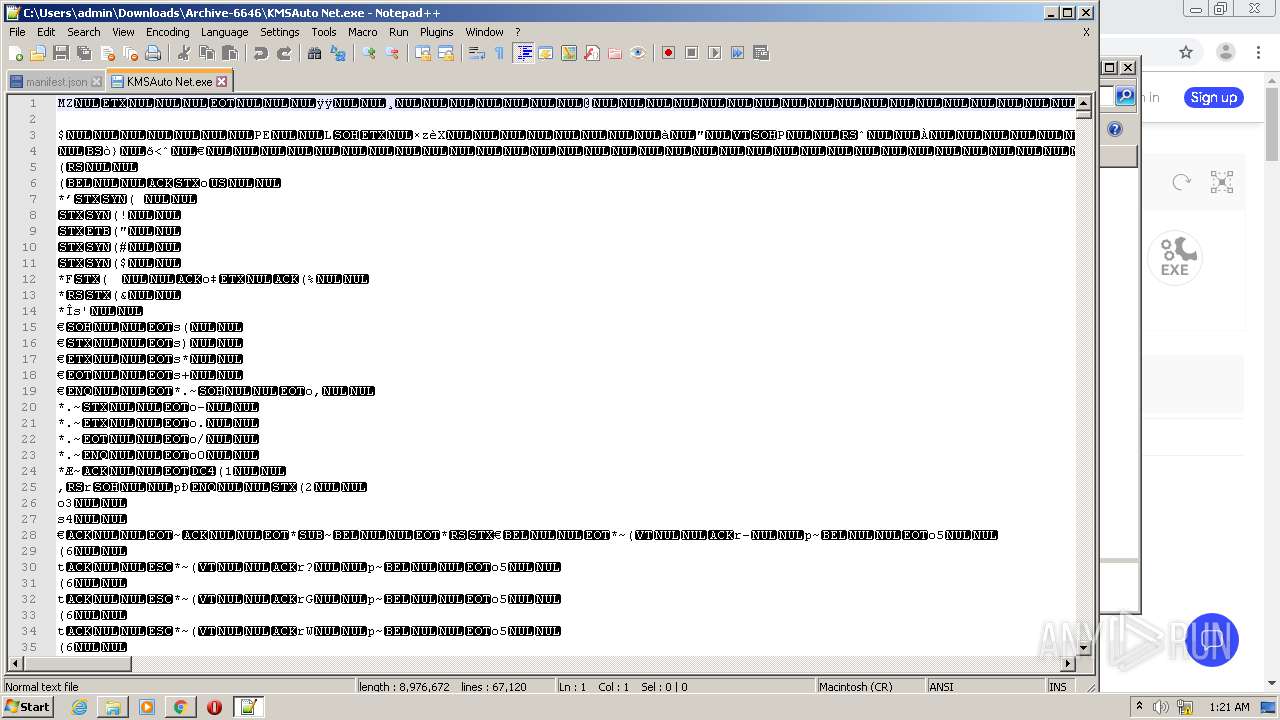
Executable files
3
Suspicious files
59
Text files
69
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG | text | |
MD5:— | SHA256:— | |||
| 3856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG | text | |
MD5:— | SHA256:— | |||
| 3856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Current Tabs | binary | |
MD5:— | SHA256:— | |||
| 3856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | text | |
MD5:— | SHA256:— | |||
| 3856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000054.dbtmp | text | |
MD5:— | SHA256:— | |||
| 3856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
71
DNS requests
34
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
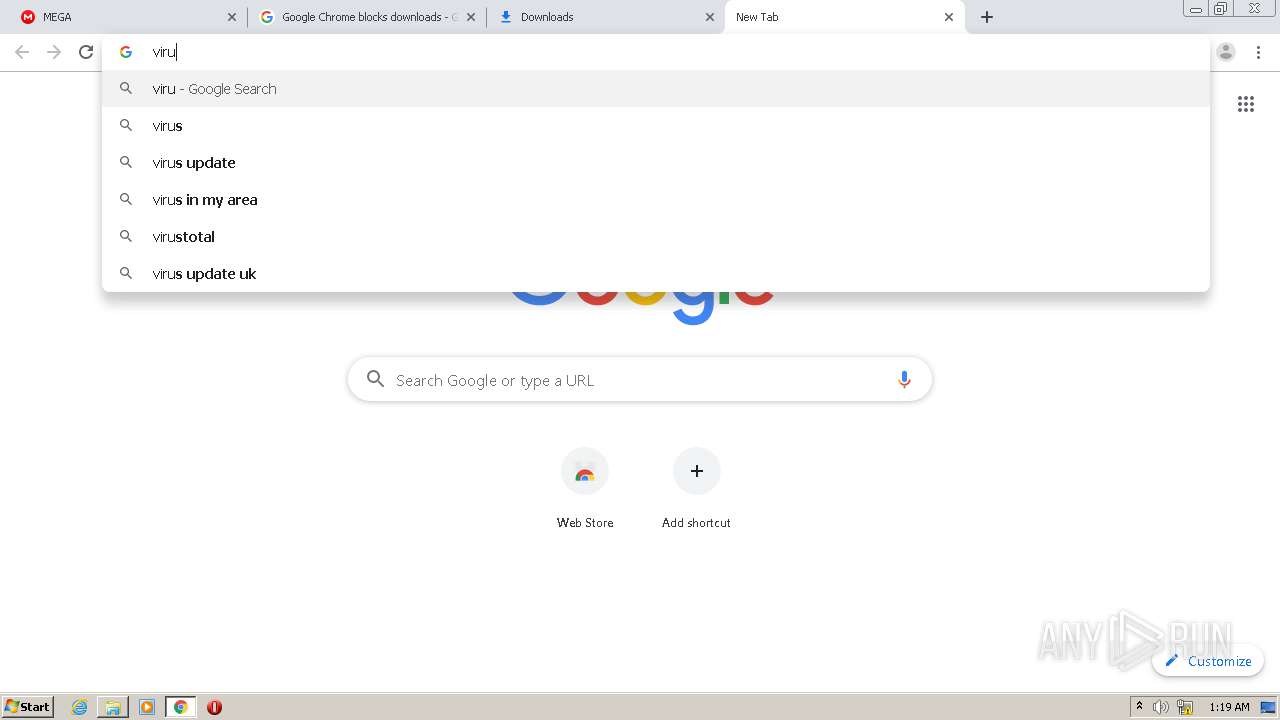
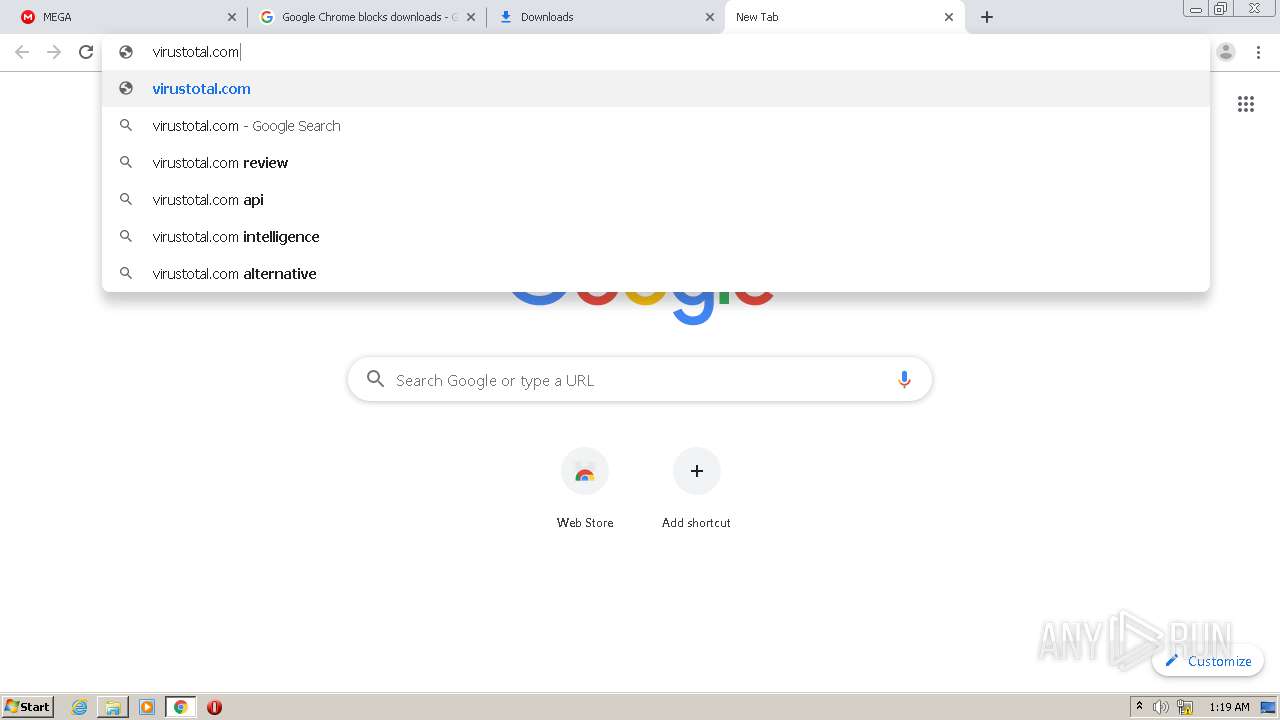
2668 | chrome.exe | GET | — | 94.156.128.52:80 | http://forum.ru-board.com/forall/ajax/ajax.css | BG | — | — | unknown |
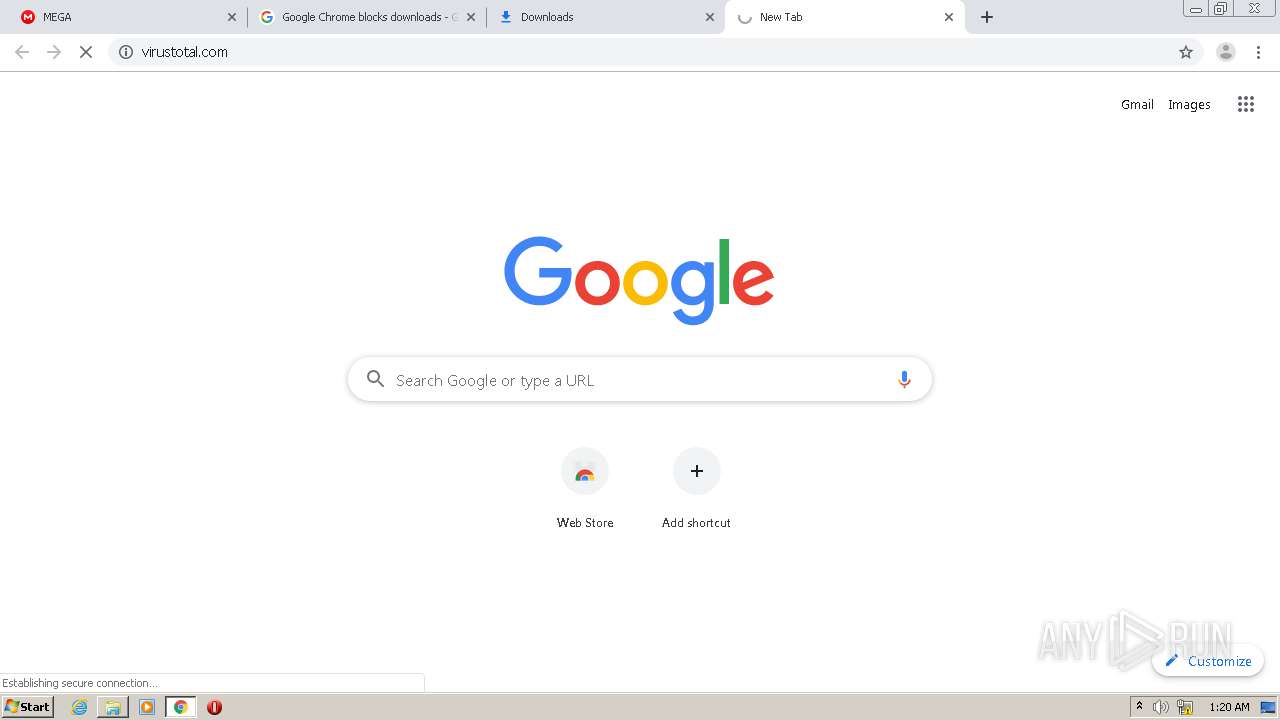
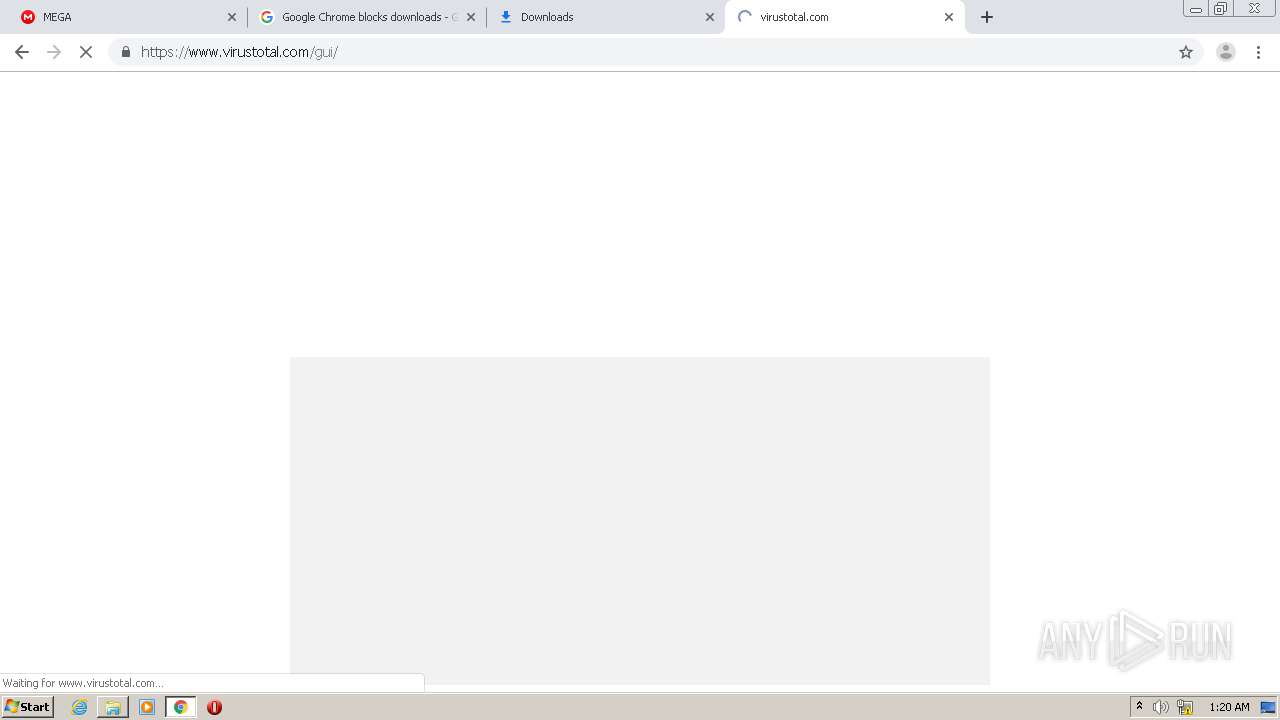
2668 | chrome.exe | GET | 302 | 216.239.38.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
2668 | chrome.exe | GET | — | 94.156.128.52:80 | http://forum.ru-board.com/board/board.css | BG | — | — | unknown |
2668 | chrome.exe | GET | 200 | 94.156.128.52:80 | http://forum.ru-board.com/topic.cgi?forum=2&topic=5559 | BG | html | 13.0 Kb | unknown |
484 | lsass.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2668 | chrome.exe | 216.58.212.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2668 | chrome.exe | 94.156.128.52:80 | forum.ru-board.com | BelCloud Hosting Corporation | BG | unknown |
2668 | chrome.exe | 172.217.16.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2668 | chrome.exe | 66.203.127.12:443 | mega.nz | RealNetworks, Inc. | US | unknown |
2668 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2668 | chrome.exe | 172.217.23.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
— | — | 89.44.169.132:443 | eu.static.mega.co.nz | Datacenter Luxembourg S.A. | LU | suspicious |
2668 | chrome.exe | 89.44.169.132:443 | eu.static.mega.co.nz | Datacenter Luxembourg S.A. | LU | suspicious |
2668 | chrome.exe | 178.62.216.192:443 | raddle.me | Digital Ocean, Inc. | NL | unknown |
— | — | 94.156.128.52:80 | forum.ru-board.com | BelCloud Hosting Corporation | BG | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
raddle.me |
| unknown |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
forum.ru-board.com |
| unknown |
mega.nz |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
g.api.mega.co.nz |
| shared |
gfs302n102.userstorage.mega.co.nz |
| unknown |