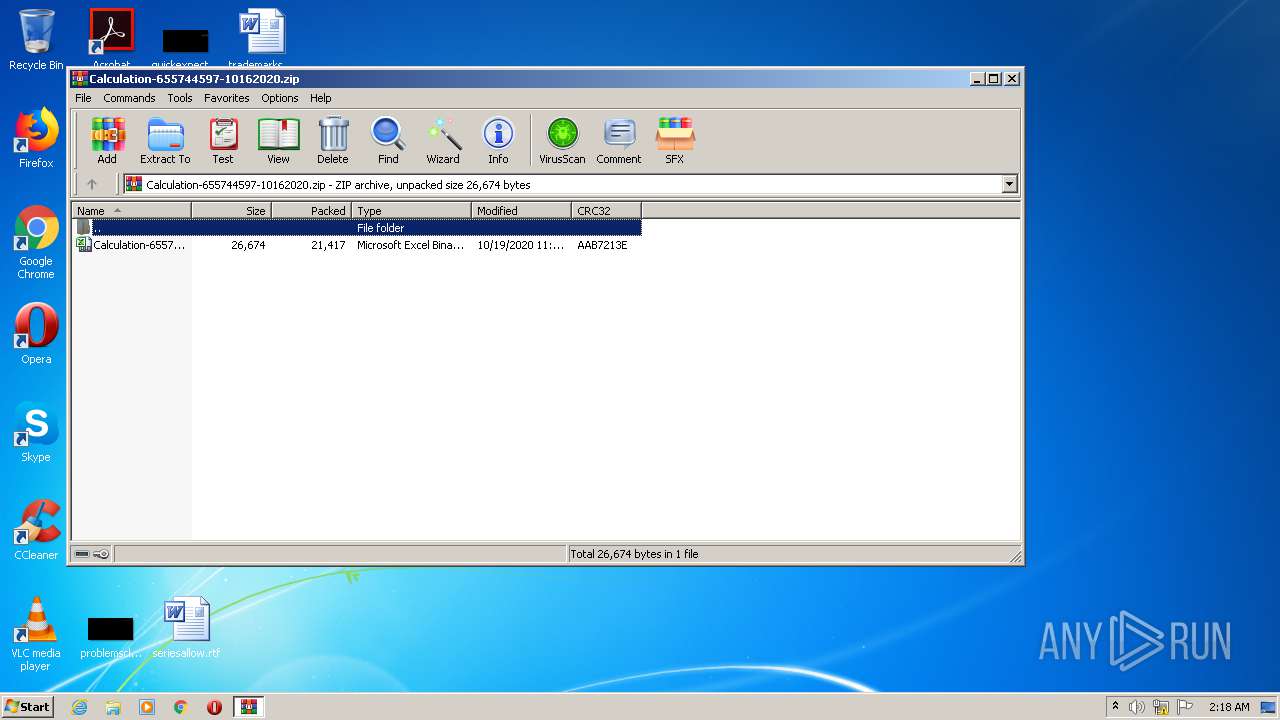
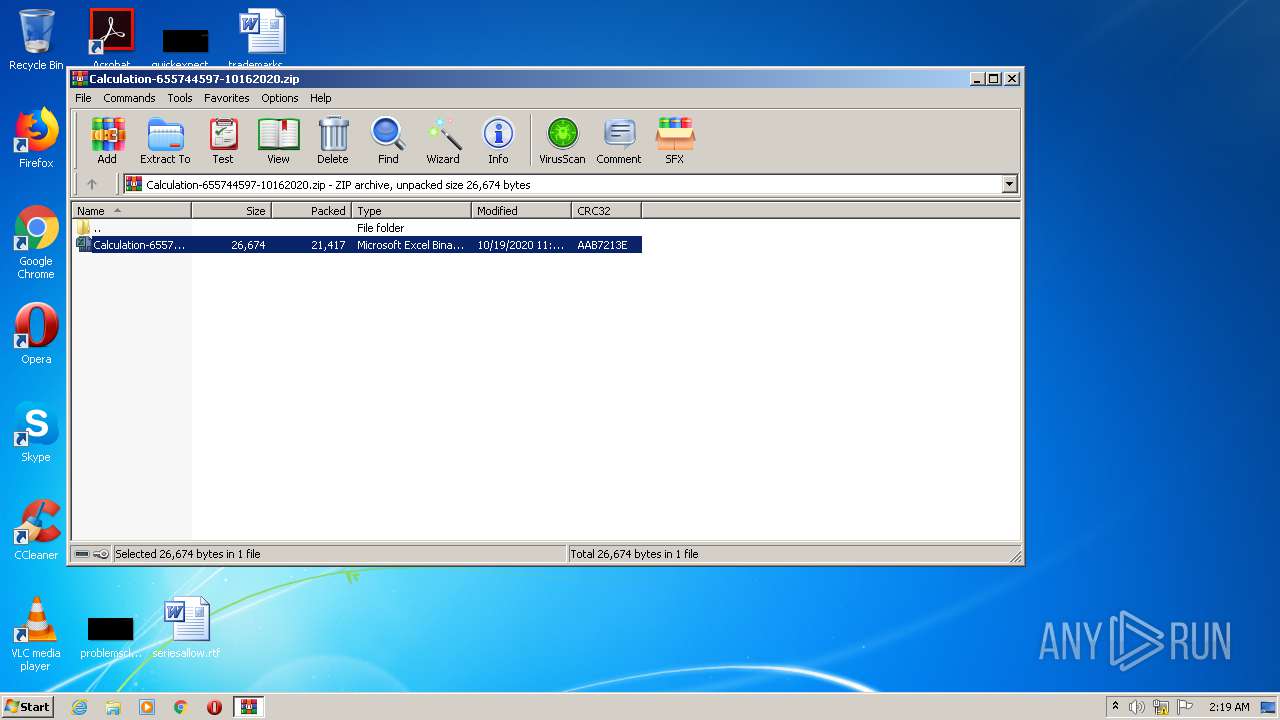
| File name: | Calculation-655744597-10162020.zip |
| Full analysis: | https://app.any.run/tasks/3372b48f-8ba9-432f-9677-56375c717c2f |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 01:17:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 57CECF419B1FCC148ABD4D3B6AF5B170 |
| SHA1: | FE2D1A12296C55047A861D193D9D52677B42E444 |
| SHA256: | B287D3DE0DAE4157DC66FA090A563C988FE6D8278461097C6605DAFB6C0A70CD |
| SSDEEP: | 384:oIgGkHXzg6Zr4VCNmoWOjLhHmd1sa+wyuqWLZ3kJgah9LKypIq:+jg6Zr4VFNkh3a+wNqWLtk2+JpF |
MALICIOUS
No malicious indicators.SUSPICIOUS
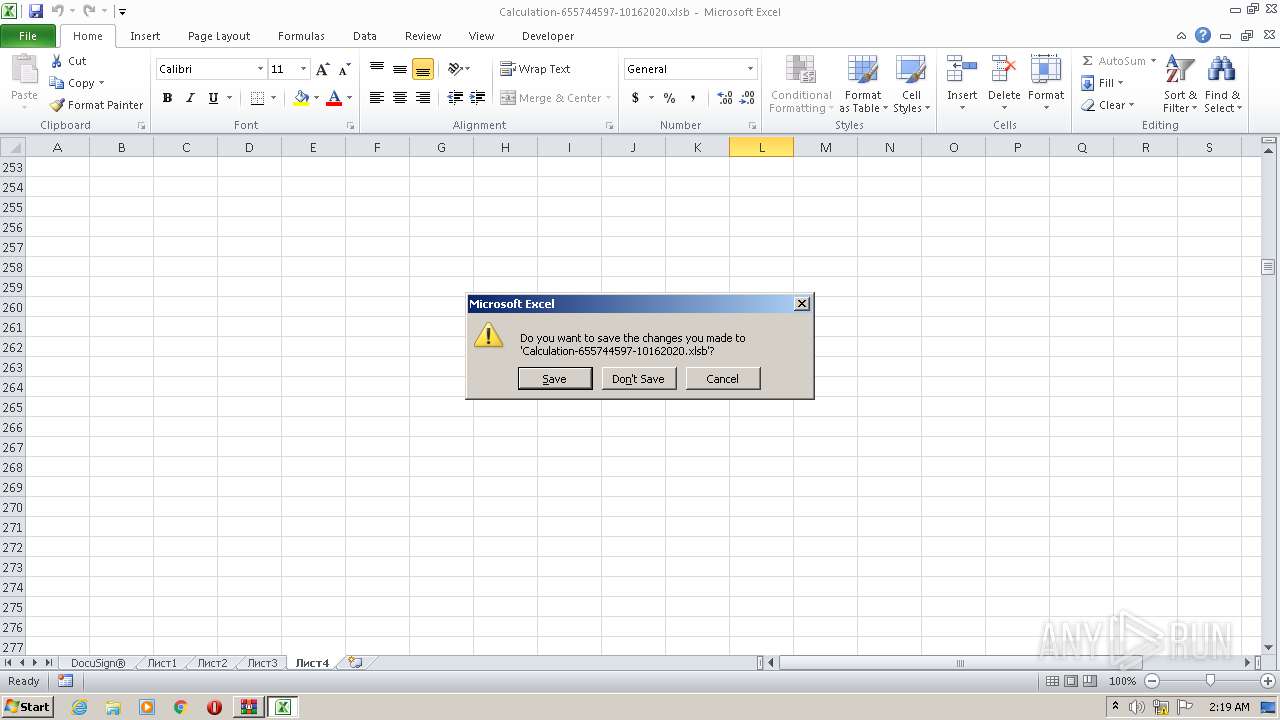
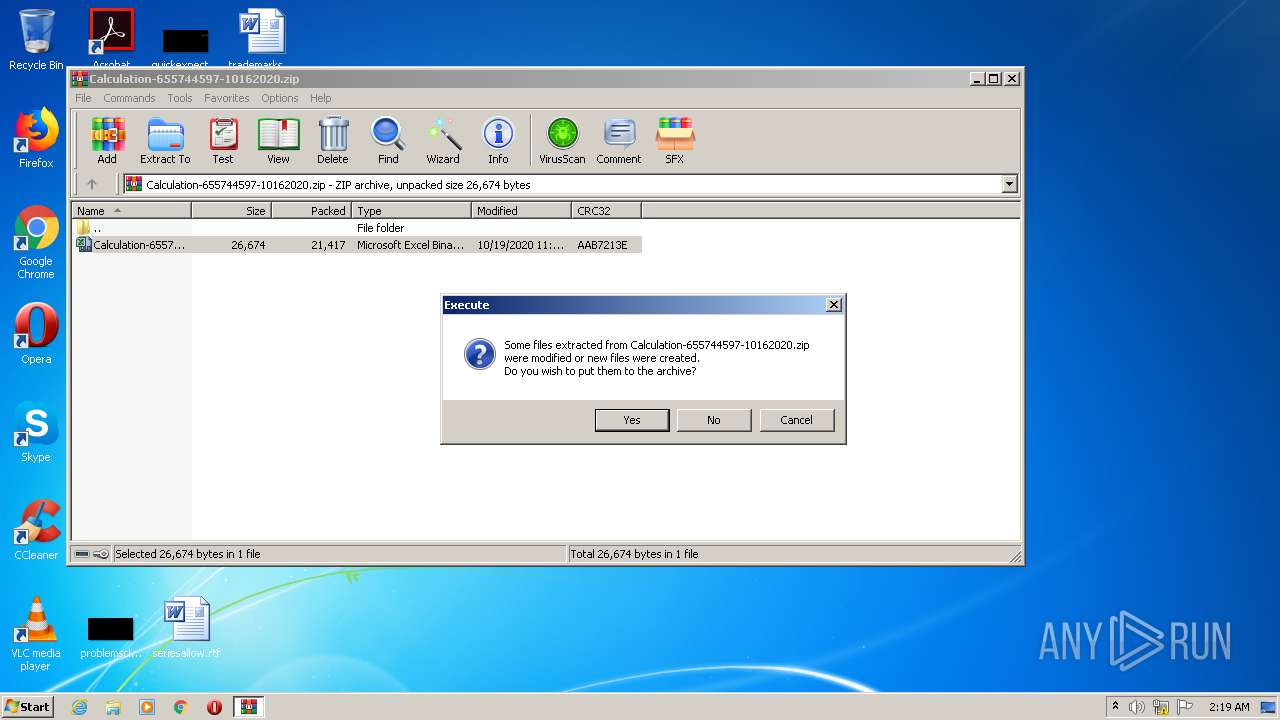
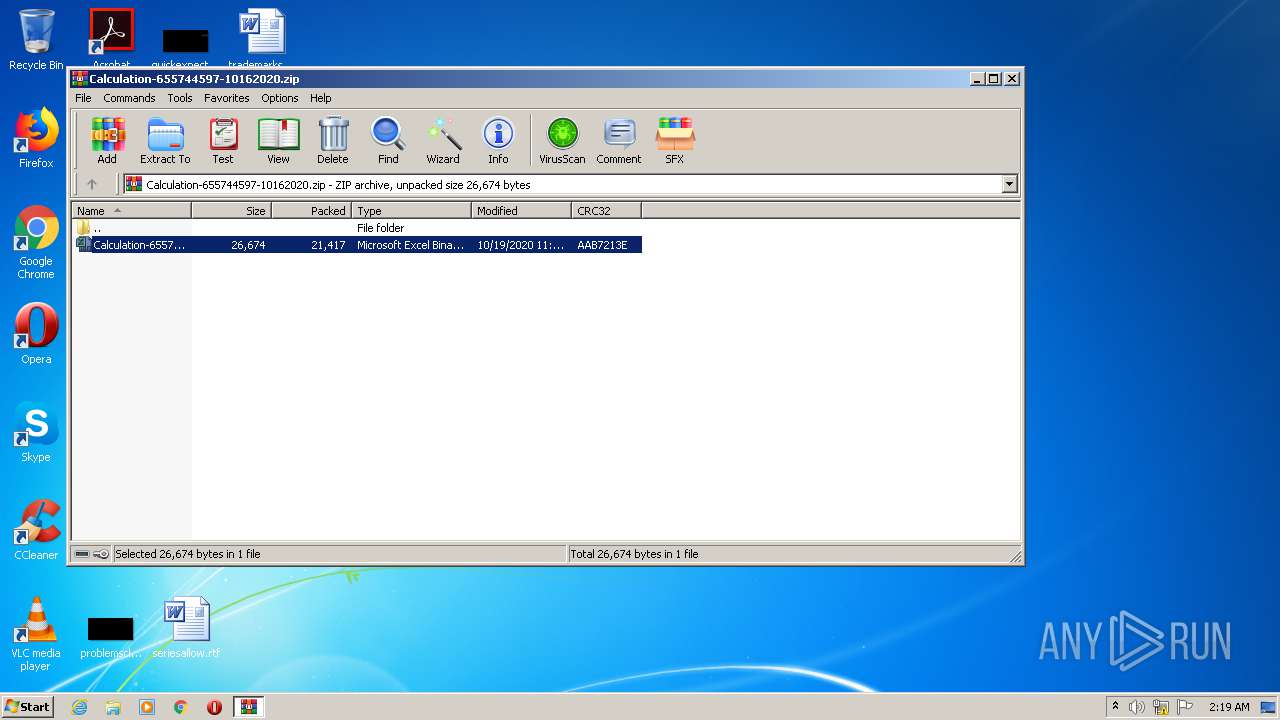
Starts Microsoft Office Application
- WinRAR.exe (PID: 2524)
INFO
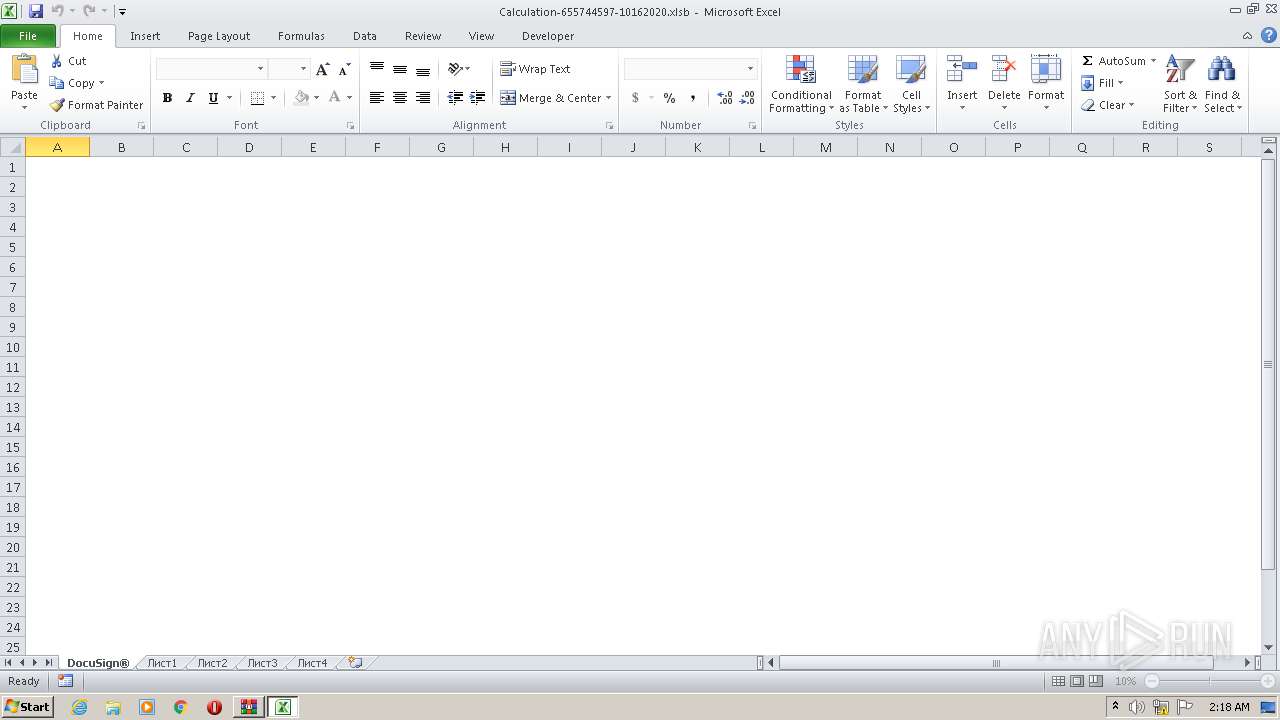
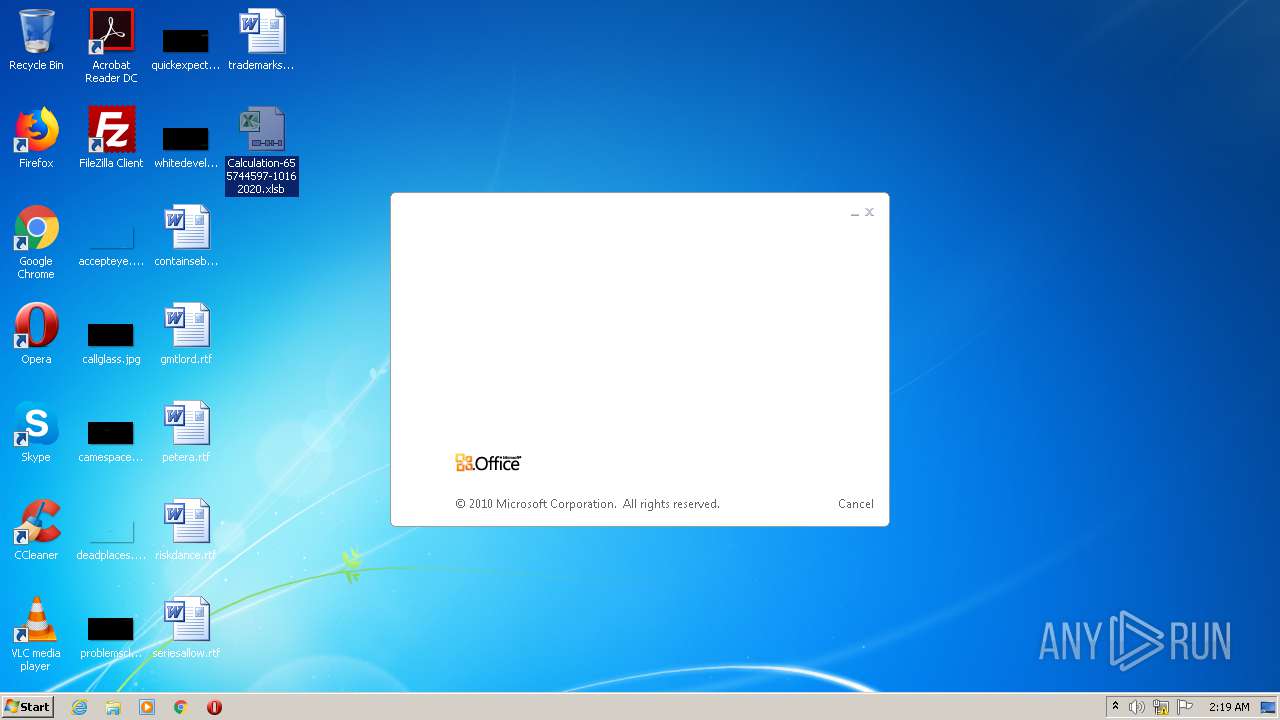
Manual execution by user
- EXCEL.EXE (PID: 2548)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2548)
- EXCEL.EXE (PID: 2472)
Creates files in the user directory
- EXCEL.EXE (PID: 2548)
Reads Internet Cache Settings
- EXCEL.EXE (PID: 2548)
- EXCEL.EXE (PID: 2472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:10:19 16:21:23 |
| ZipCRC: | 0xaab7213e |
| ZipCompressedSize: | 21417 |
| ZipUncompressedSize: | 26674 |
| ZipFileName: | Calculation-655744597-10162020.xlsb |
Total processes
42
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2472 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
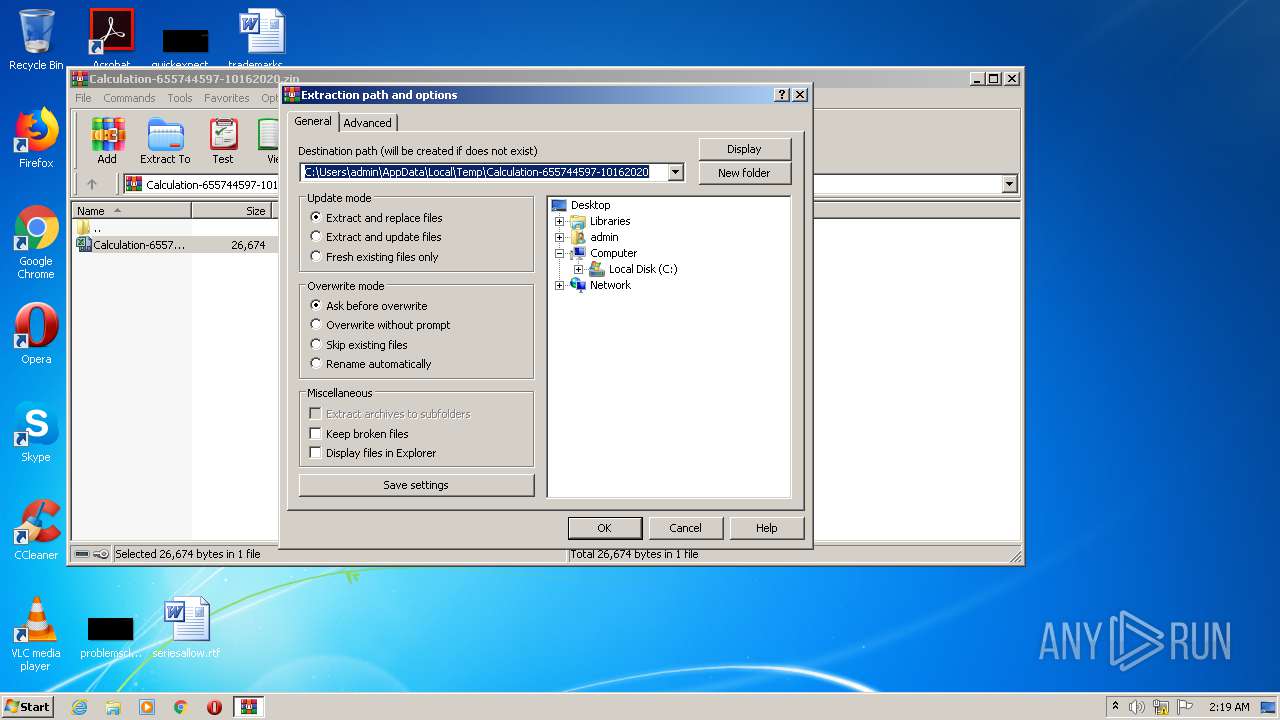
| 2524 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Calculation-655744597-10162020.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 753
Read events
1 611
Write events
115
Delete events
27
Modification events
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Calculation-655744597-10162020.zip | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2472) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | ln6 |
Value: 6C6E3600A8090000010000000000000000000000 | |||
| (PID) Process: | (2472) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR66DD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2472 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\80531E28.png | — | |
MD5:— | SHA256:— | |||
| 2472 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\94247809.png | — | |
MD5:— | SHA256:— | |||
| 2472 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C68EAE76.png | — | |
MD5:— | SHA256:— | |||
| 2472 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIa2524.2608\~$Calculation-655744597-10162020.xlsb | — | |
MD5:— | SHA256:— | |||
| 2548 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRE00F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2548 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2524 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2524.2608\Calculation-655744597-10162020.xlsb | document | |
MD5:— | SHA256:— | |||
| 2524 | WinRAR.exe | C:\Users\admin\Desktop\Calculation-655744597-10162020.xlsb | document | |
MD5:— | SHA256:— | |||
| 2548 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Calculation-655744597-10162020.xlsb.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2548 | EXCEL.EXE | GET | 200 | 192.185.91.48:80 | http://citycarmen.com/lvhyf/3415201.png | US | — | — | whitelisted |
2472 | EXCEL.EXE | GET | 200 | 192.185.91.48:80 | http://citycarmen.com/lvhyf/3415201.png | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.185.91.48:80 | citycarmen.com | CyrusOne LLC | US | malicious |
2472 | EXCEL.EXE | 192.185.91.48:80 | citycarmen.com | CyrusOne LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
citycarmen.com |
| whitelisted |