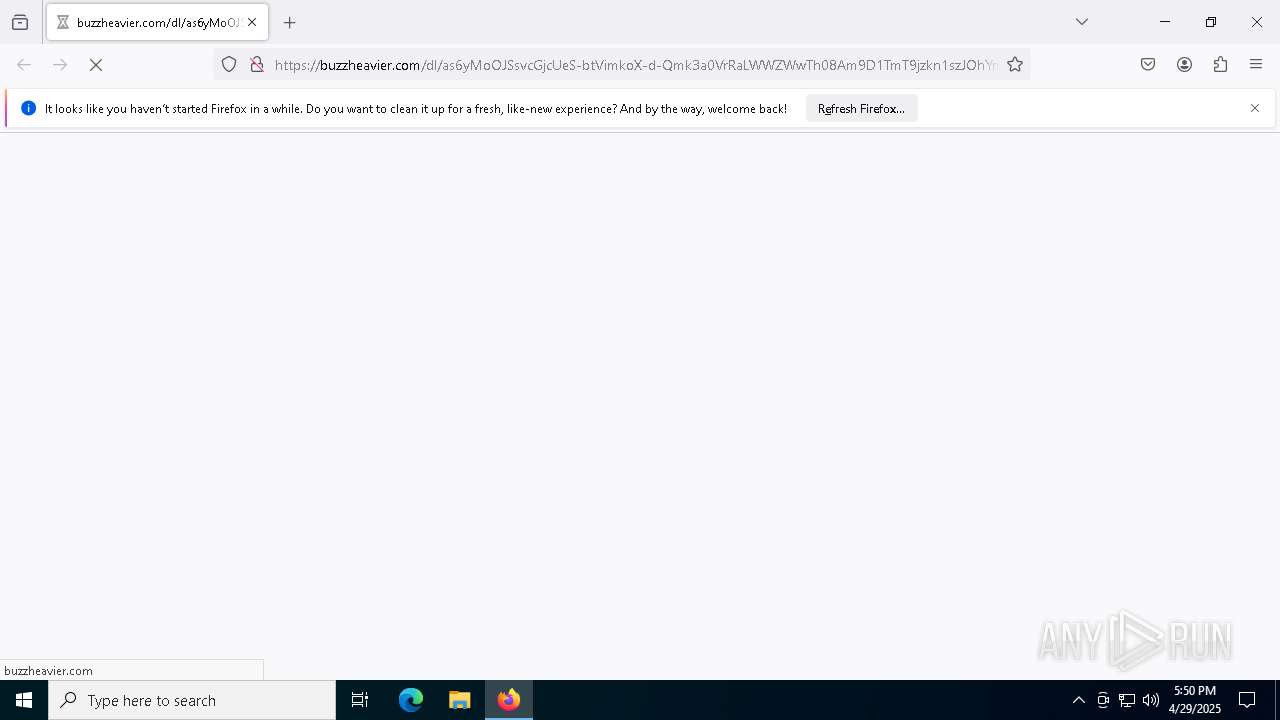
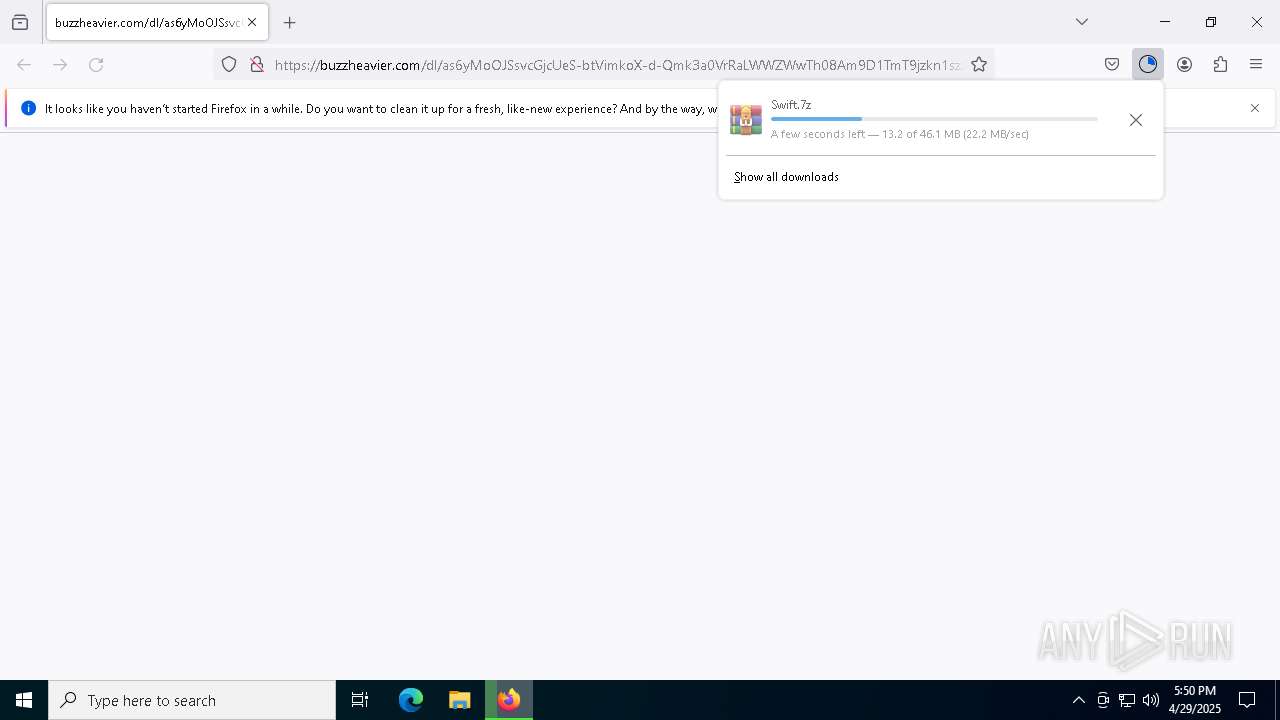
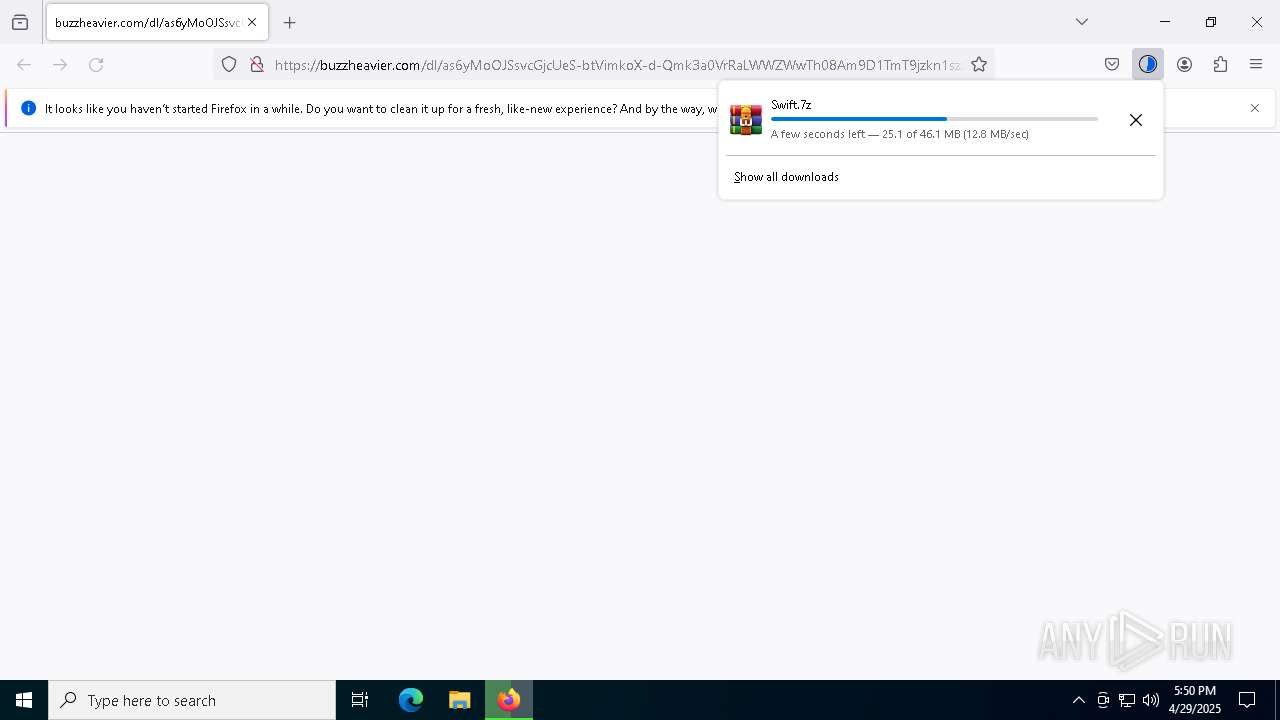
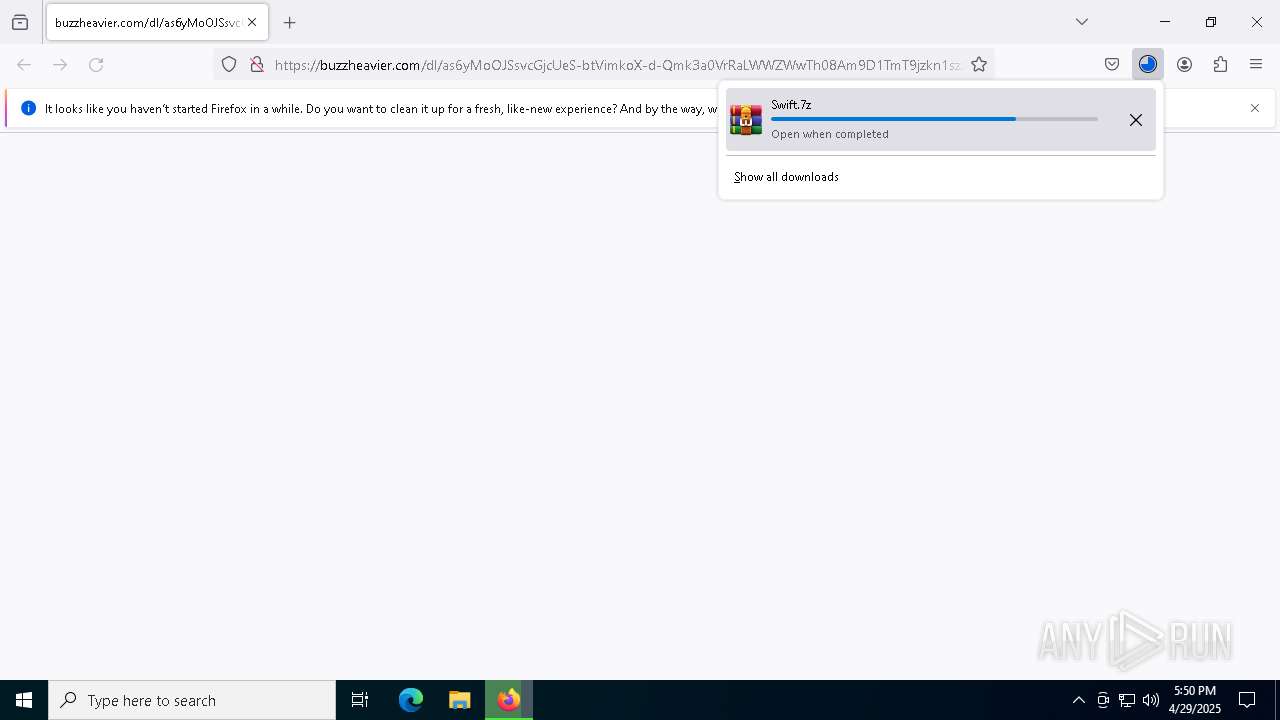
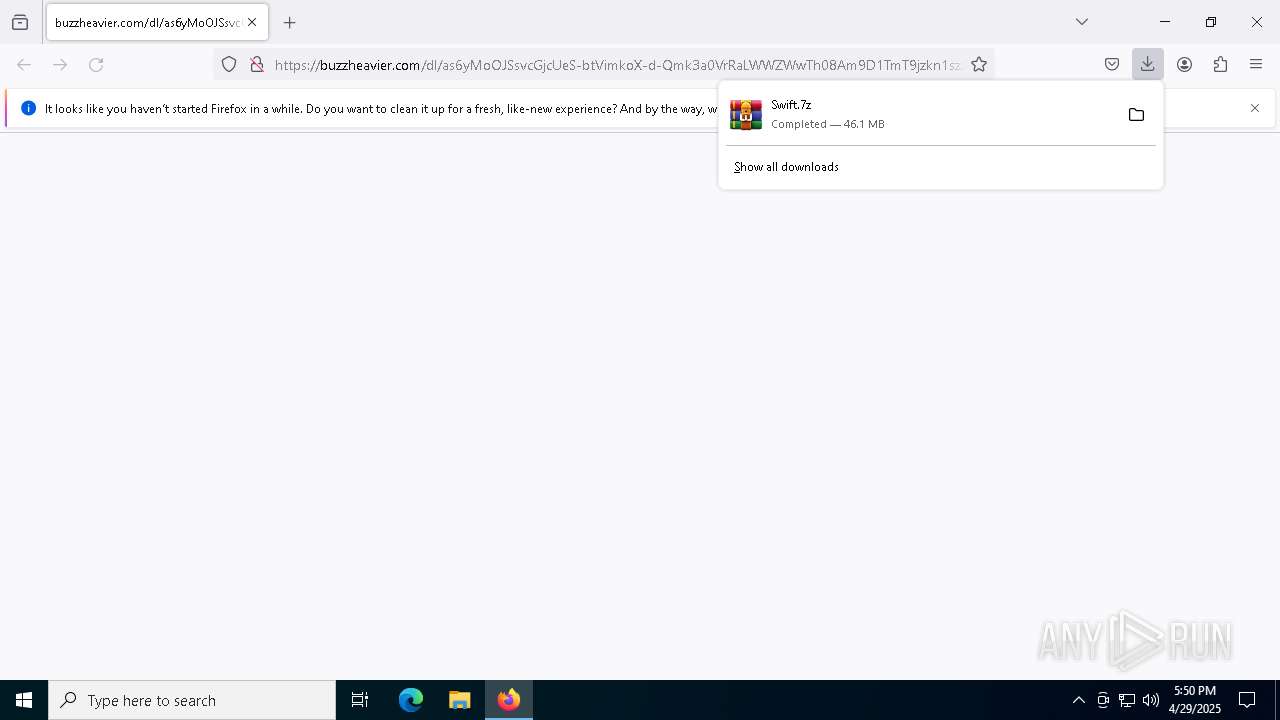
| URL: | https://buzzheavier.com/dl/as6yMoOJSsvcGjcUeS-btVimkoX-d-Qmk3a0VrRaLWWZWwTh08Am9D1TmT9jzkn1szJOhYmb1vaSk81iZRwYbsGUGYXsDx1iE19lNQ?v=1745948706-ftYooapGX8E3JXZBUFmZ%2F44vtXpED1PQoGXW6DxXYmI%3D |
| Full analysis: | https://app.any.run/tasks/18b6cd1c-0334-445c-be2b-d0ee5b5d1e3b |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 17:50:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | E07E1D98699E32FC2ADCC53E60B648BB |
| SHA1: | DA01024DB65478121B992B97A312C41A079B3BD2 |
| SHA256: | B28478AB5DFBFF95B6E77D7C829308DD45E30CA23A643D2B4B1703372C6FE3D9 |
| SSDEEP: | 3:N8XET7+Jg1fG/BG2QcUch4OgWKULOWM3qfrDT5SRJRATID8EAdTlojRQhgiGy3:2XETCC1fABAccOTDtfrDNSRe+8EAdBGY |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 5964)
- powershell.exe (PID: 5164)
- powershell.exe (PID: 5392)
SUSPICIOUS
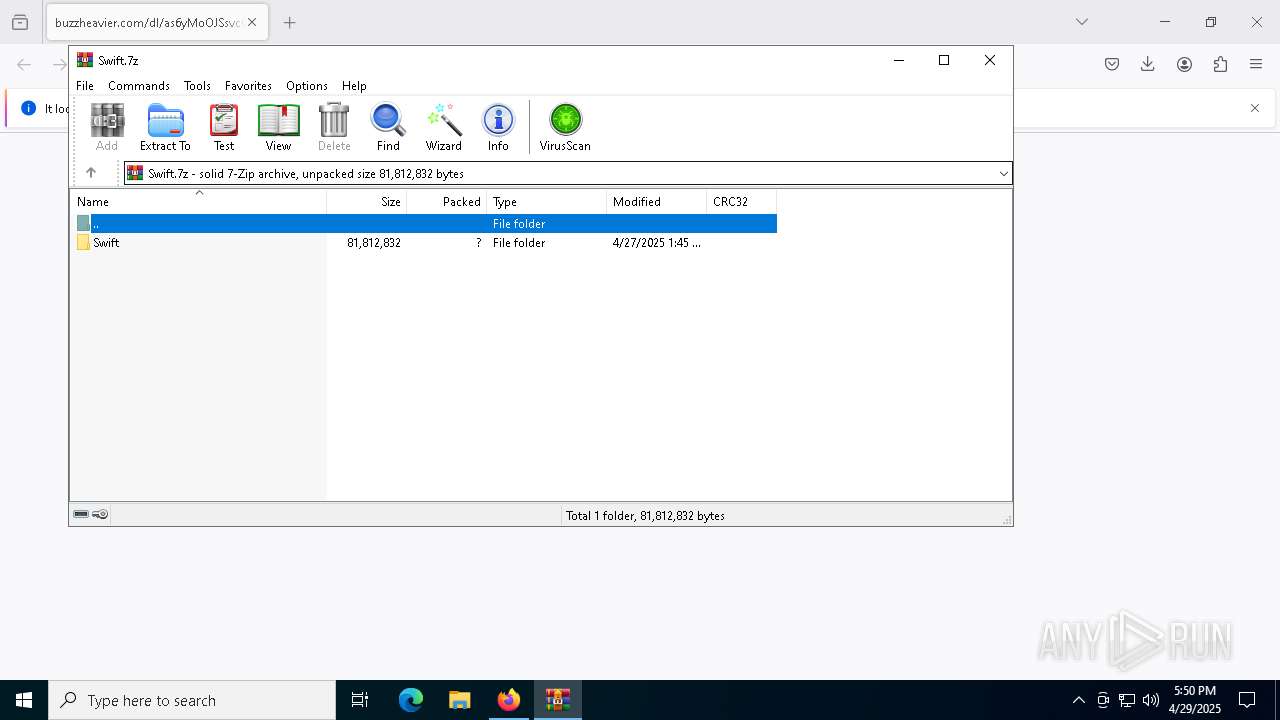
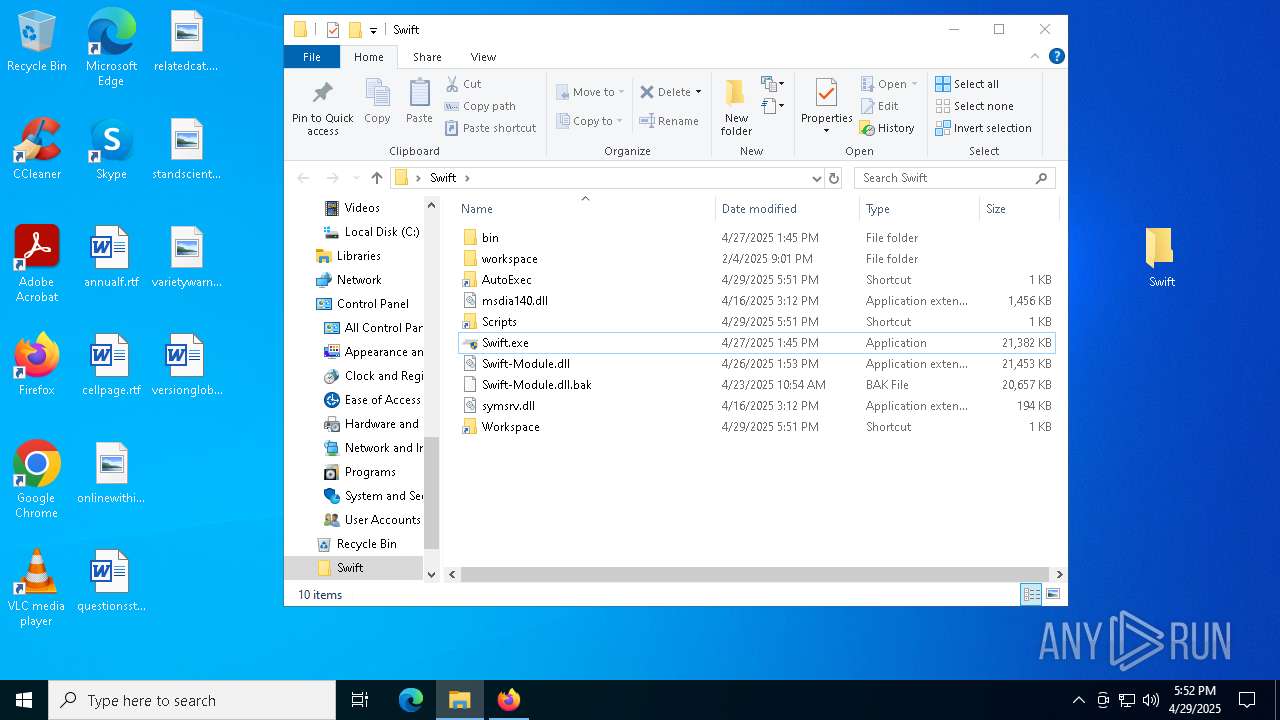
Process drops legitimate windows executable
- WinRAR.exe (PID: 8884)
Reads the BIOS version
- Swift.exe (PID: 2984)
Starts POWERSHELL.EXE for commands execution
- Swift.exe (PID: 2984)
The process bypasses the loading of PowerShell profile settings
- Swift.exe (PID: 2984)
The process hide an interactive prompt from the user
- Swift.exe (PID: 2984)
INFO
Application launched itself
- firefox.exe (PID: 2392)
- firefox.exe (PID: 6344)
The sample compiled with english language support
- WinRAR.exe (PID: 8884)
Process checks whether UAC notifications are on
- Swift.exe (PID: 2984)
Checks supported languages
- Swift.exe (PID: 2984)
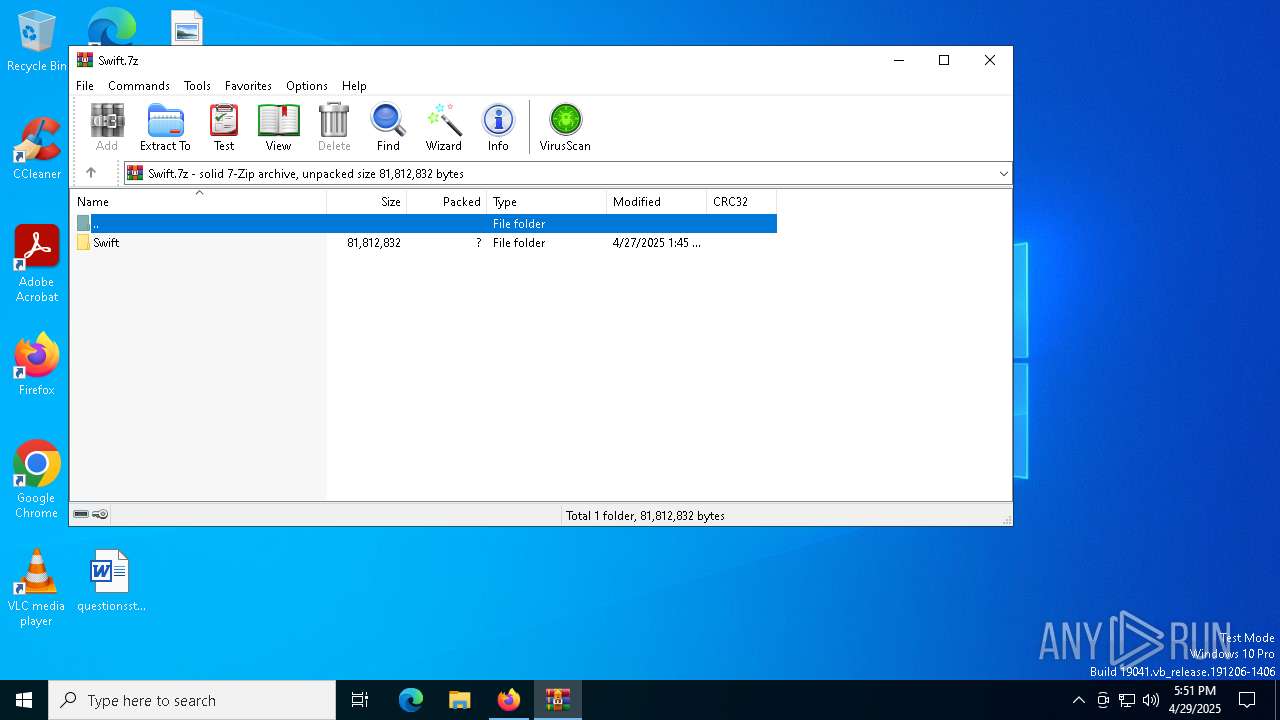
Manual execution by a user
- WinRAR.exe (PID: 8884)
- Swift.exe (PID: 8628)
- Swift.exe (PID: 2984)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8884)
Reads the computer name
- Swift.exe (PID: 2984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
161
Monitored processes
24
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1276 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5020 -childID 4 -isForBrowser -prefsHandle 5024 -prefMapHandle 5000 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1192 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {06d66ac3-4f71-46f2-a85b-a085fa8c4999} 2392 "\\.\pipe\gecko-crash-server-pipe.2392" 201848dcf50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://buzzheavier.com/dl/as6yMoOJSsvcGjcUeS-btVimkoX-d-Qmk3a0VrRaLWWZWwTh08Am9D1TmT9jzkn1szJOhYmb1vaSk81iZRwYbsGUGYXsDx1iE19lNQ?v=1745948706-ftYooapGX8E3JXZBUFmZ%2F44vtXpED1PQoGXW6DxXYmI%3D | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
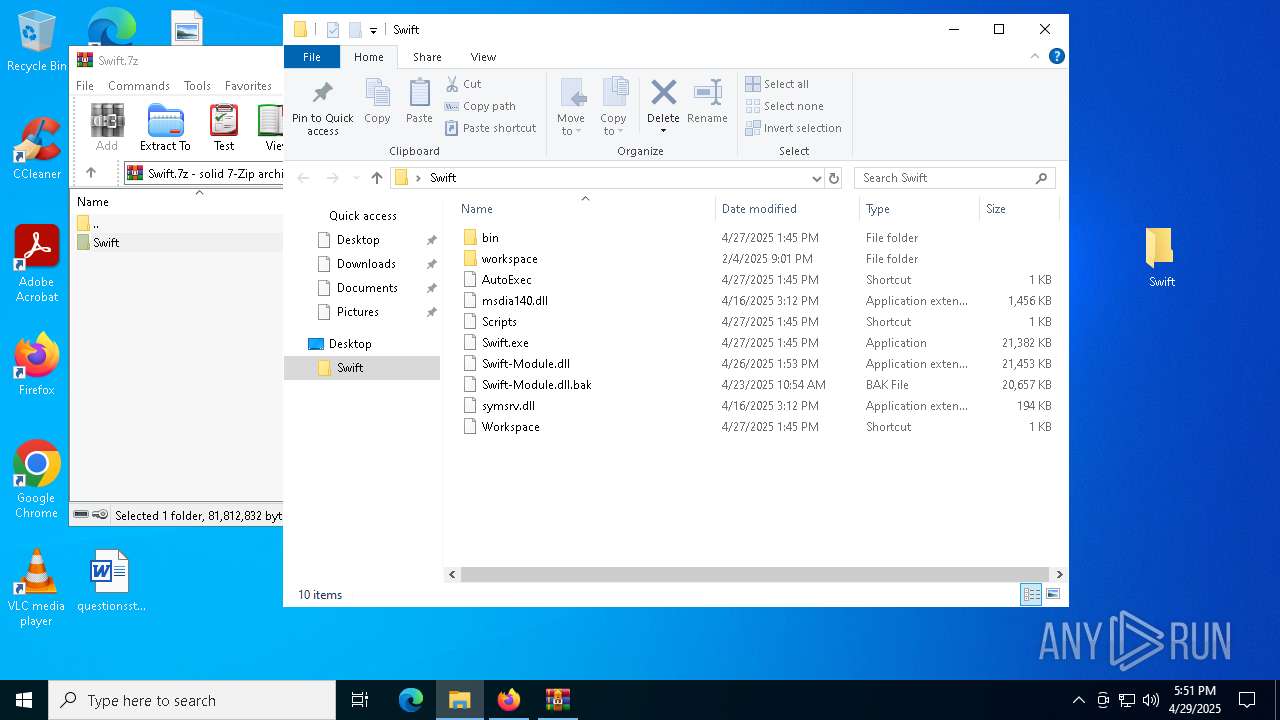
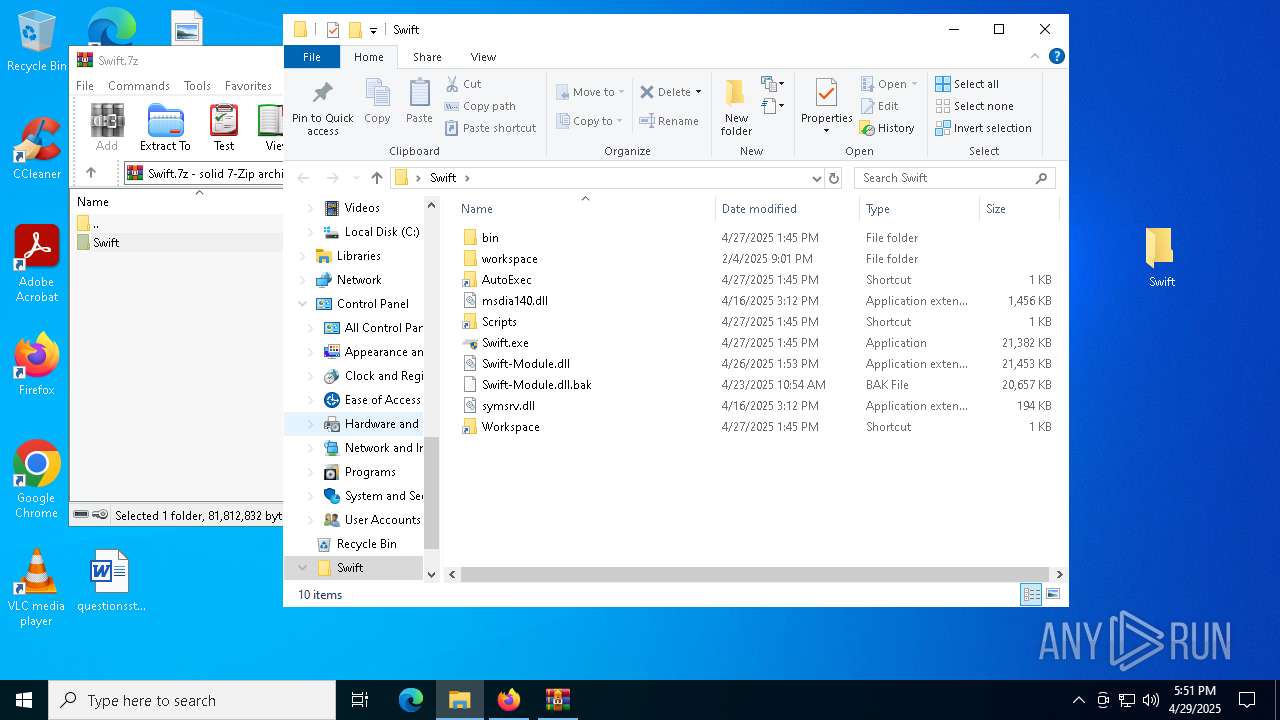
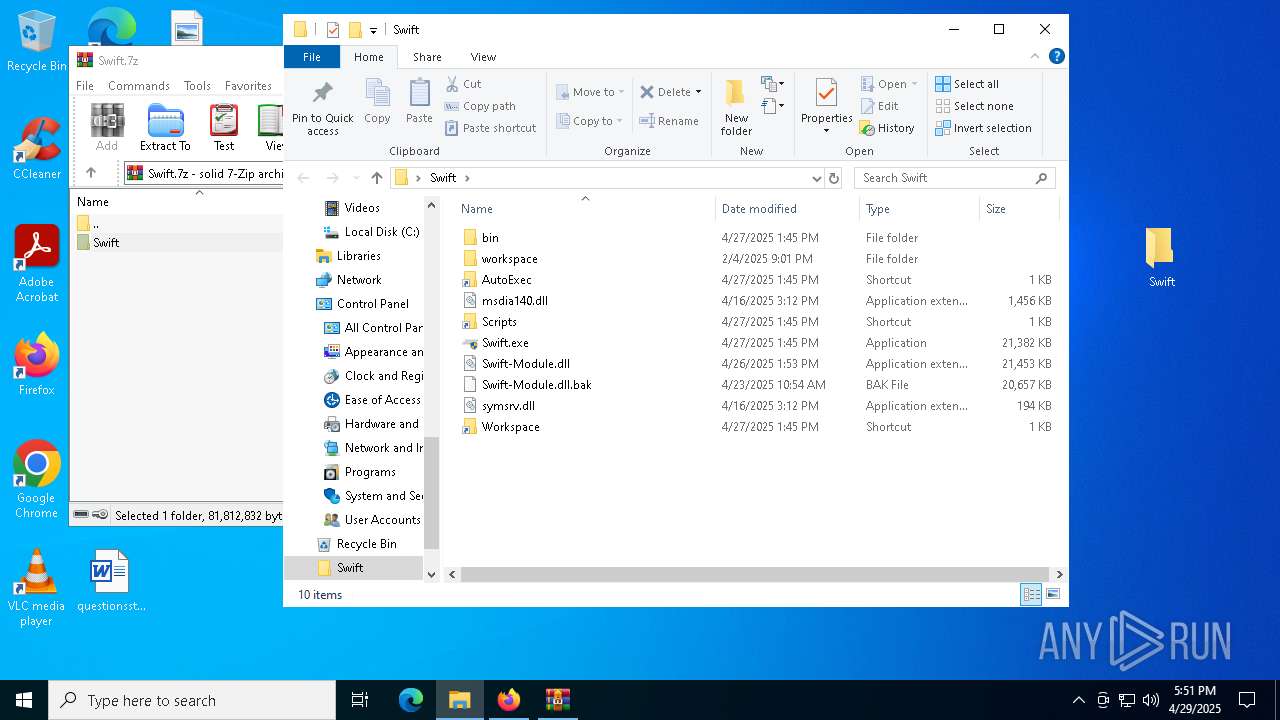
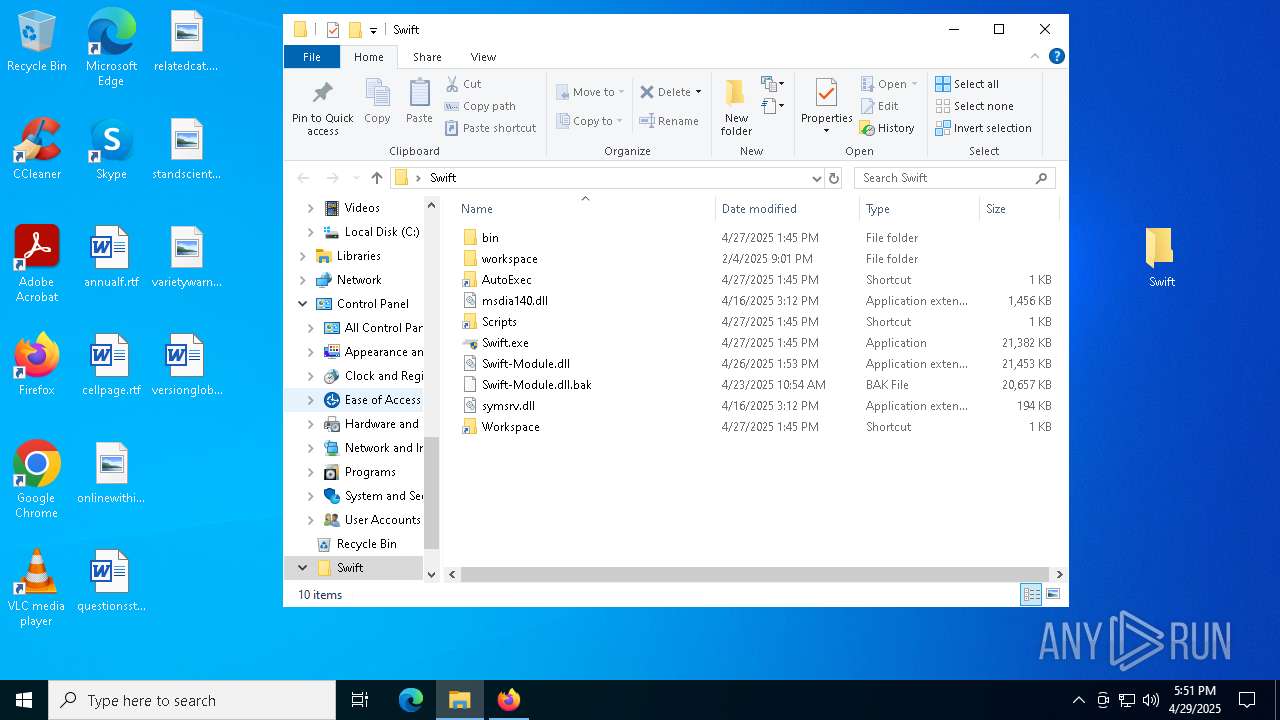
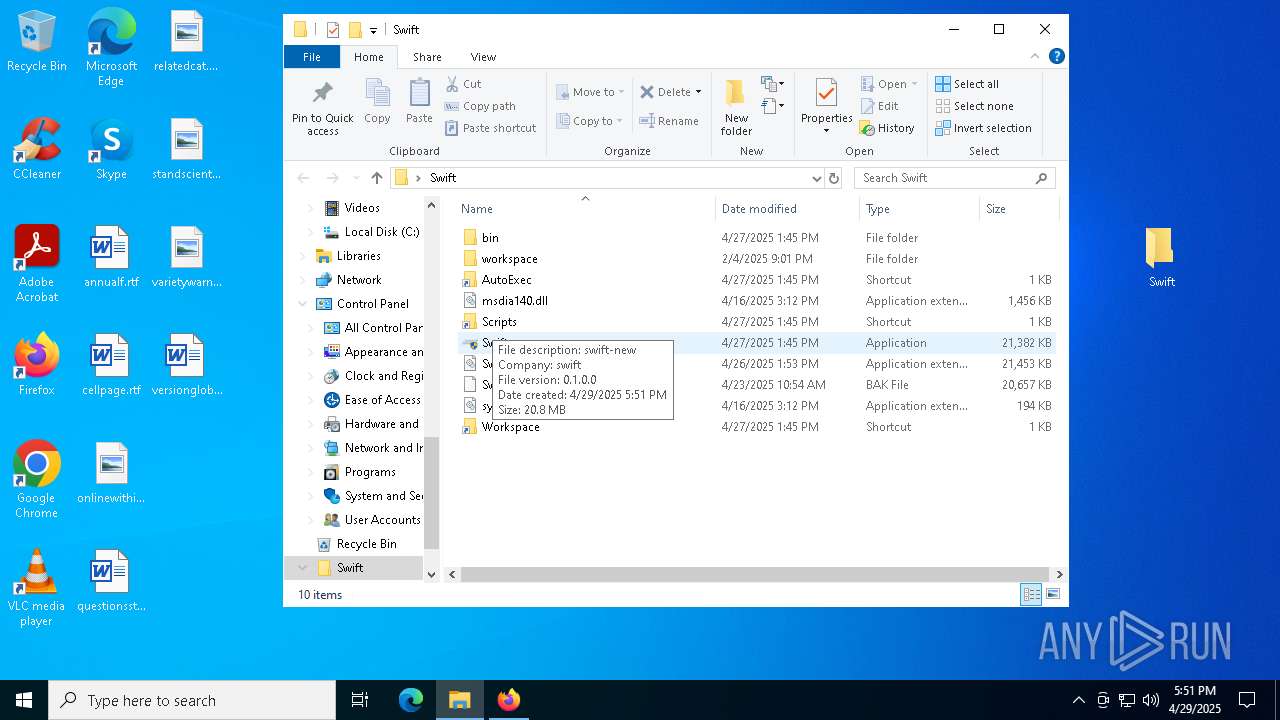
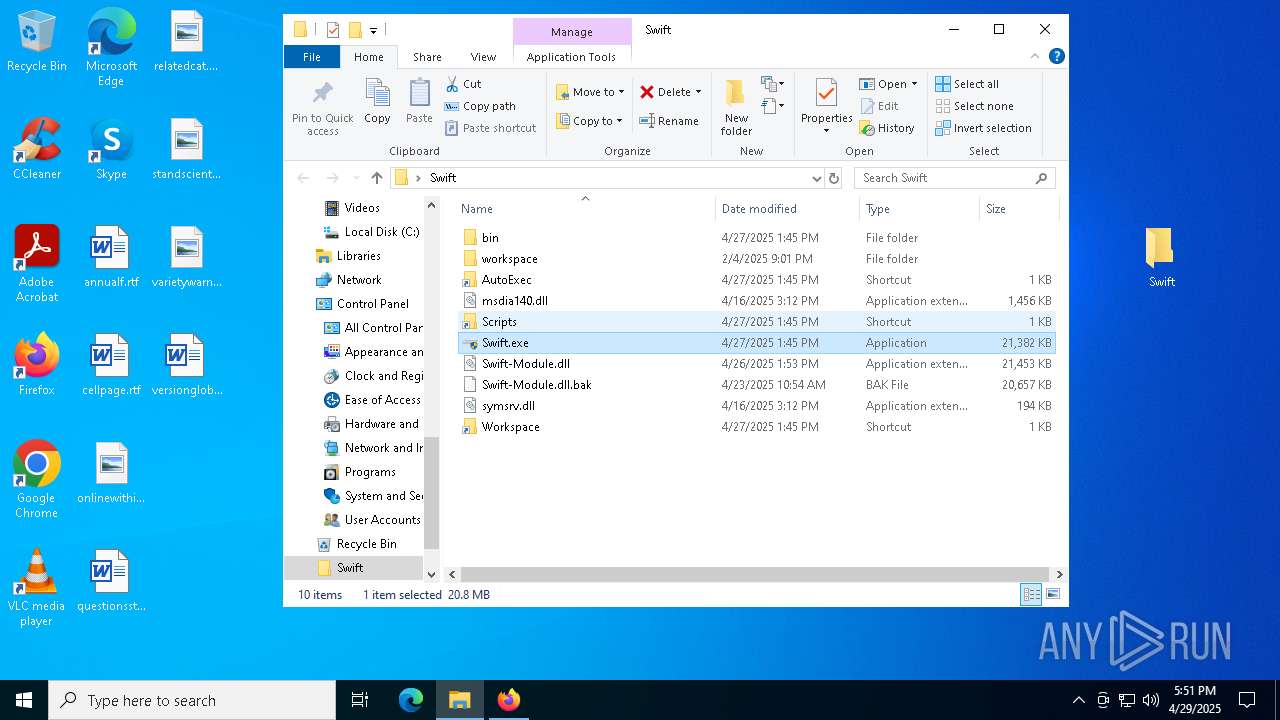
| 2984 | "C:\Users\admin\Desktop\Swift\Swift.exe" | C:\Users\admin\Desktop\Swift\Swift.exe | explorer.exe | ||||||||||||
User: admin Company: swift Integrity Level: HIGH Description: swift-new Version: 0.1.0 Modules
| |||||||||||||||
| 5056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
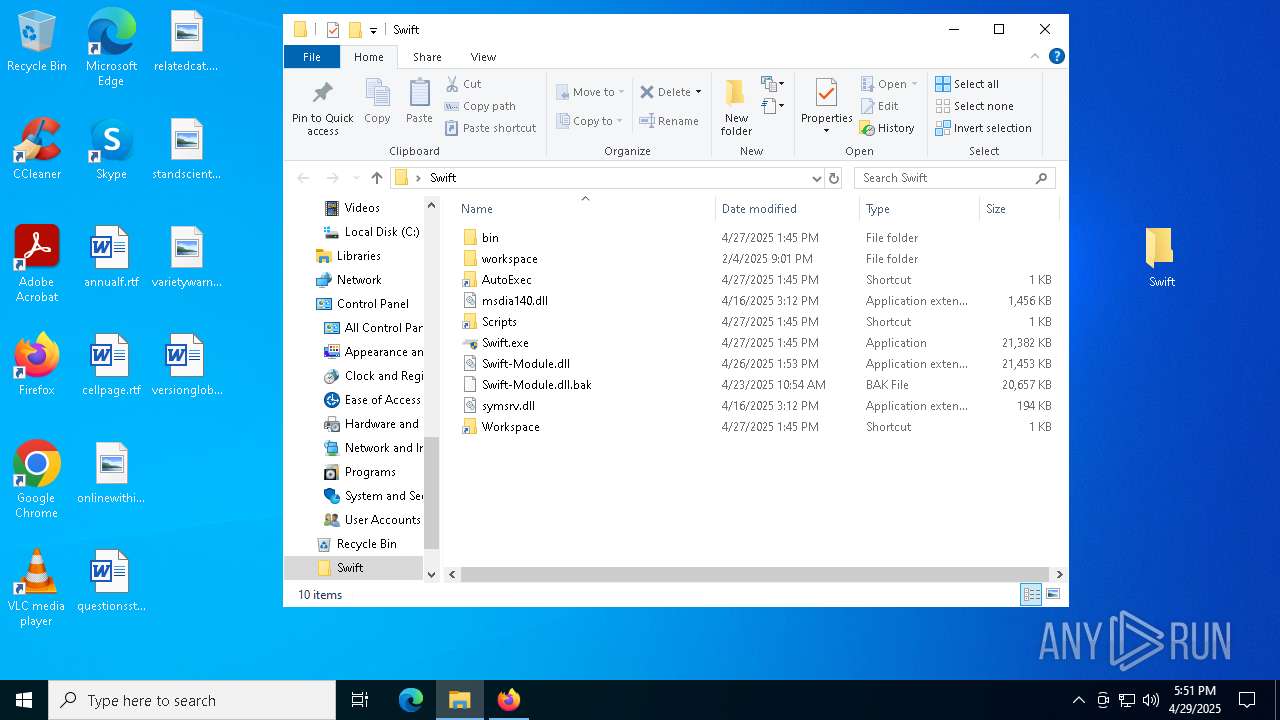
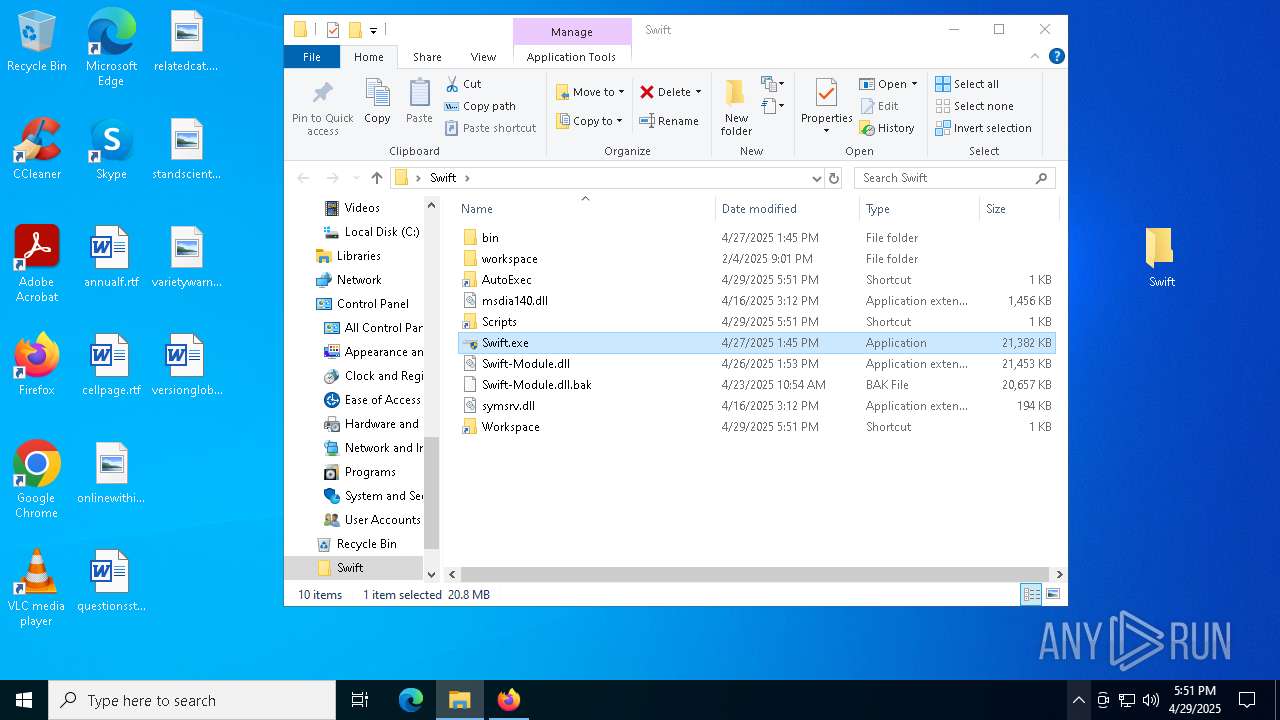
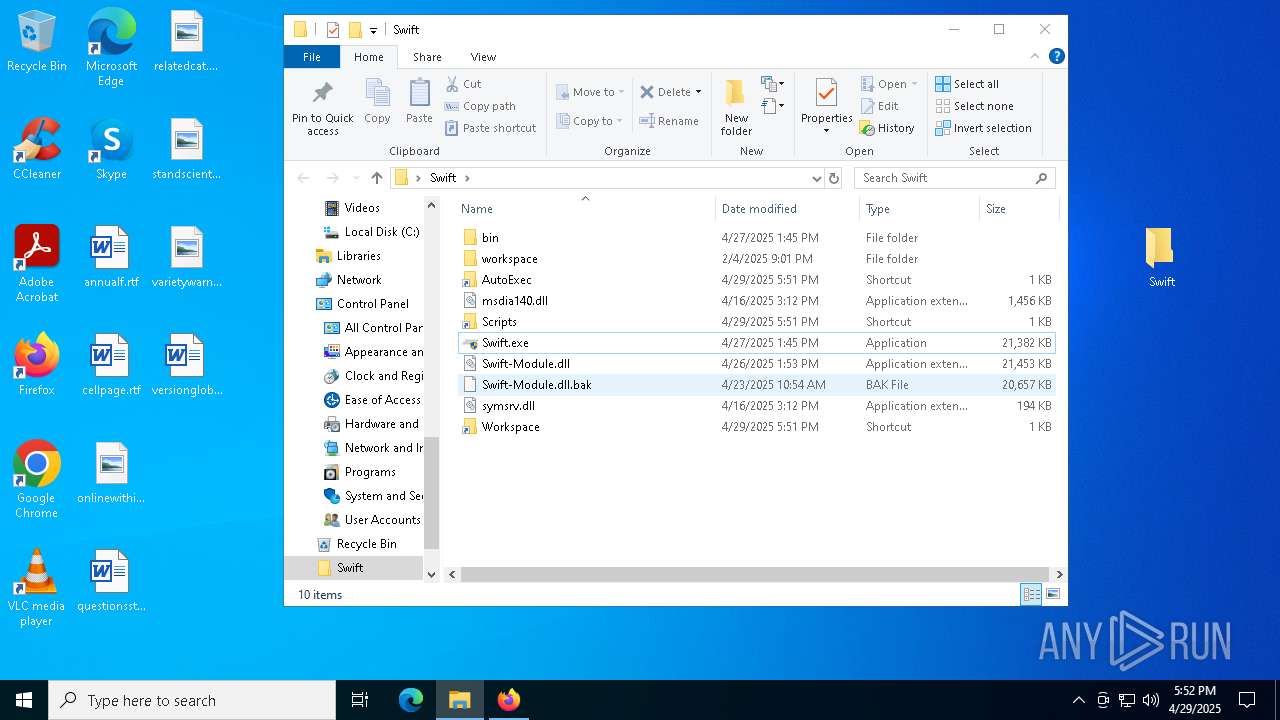
| 5164 | "powershell" -WindowStyle Hidden -NoProfile -NonInteractive -Command "$WshShell = New-Object -comObject WScript.Shell; $Shortcut = $WshShell.CreateShortcut('C:\Users\admin\Desktop\Swift\Workspace.lnk'); $Shortcut.TargetPath = 'C:\Users\admin\AppData\Roaming\Swift\Workspace'; $Shortcut.Save()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Swift.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5392 | "powershell" -WindowStyle Hidden -NoProfile -NonInteractive -Command "$WshShell = New-Object -comObject WScript.Shell; $Shortcut = $WshShell.CreateShortcut('C:\Users\admin\Desktop\Swift\AutoExec.lnk'); $Shortcut.TargetPath = 'C:\Users\admin\AppData\Roaming\Swift\AutoExec'; $Shortcut.Save()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Swift.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5964 | "powershell" -WindowStyle Hidden -NoProfile -NonInteractive -Command "$WshShell = New-Object -comObject WScript.Shell; $Shortcut = $WshShell.CreateShortcut('C:\Users\admin\Desktop\Swift\Scripts.lnk'); $Shortcut.TargetPath = 'C:\Users\admin\AppData\Roaming\Swift\Scripts'; $Shortcut.Save()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Swift.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6080 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6344 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://buzzheavier.com/dl/as6yMoOJSsvcGjcUeS-btVimkoX-d-Qmk3a0VrRaLWWZWwTh08Am9D1TmT9jzkn1szJOhYmb1vaSk81iZRwYbsGUGYXsDx1iE19lNQ?v=1745948706-ftYooapGX8E3JXZBUFmZ%2F44vtXpED1PQoGXW6DxXYmI%3D" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
Total events
29 867
Read events
29 845
Write events
22
Delete events
0
Modification events
| (PID) Process: | (2392) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 491C20EB00000000 | |||
| (PID) Process: | (2392) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 0 | |||
| (PID) Process: | (2392) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 1 | |||
| (PID) Process: | (2392) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
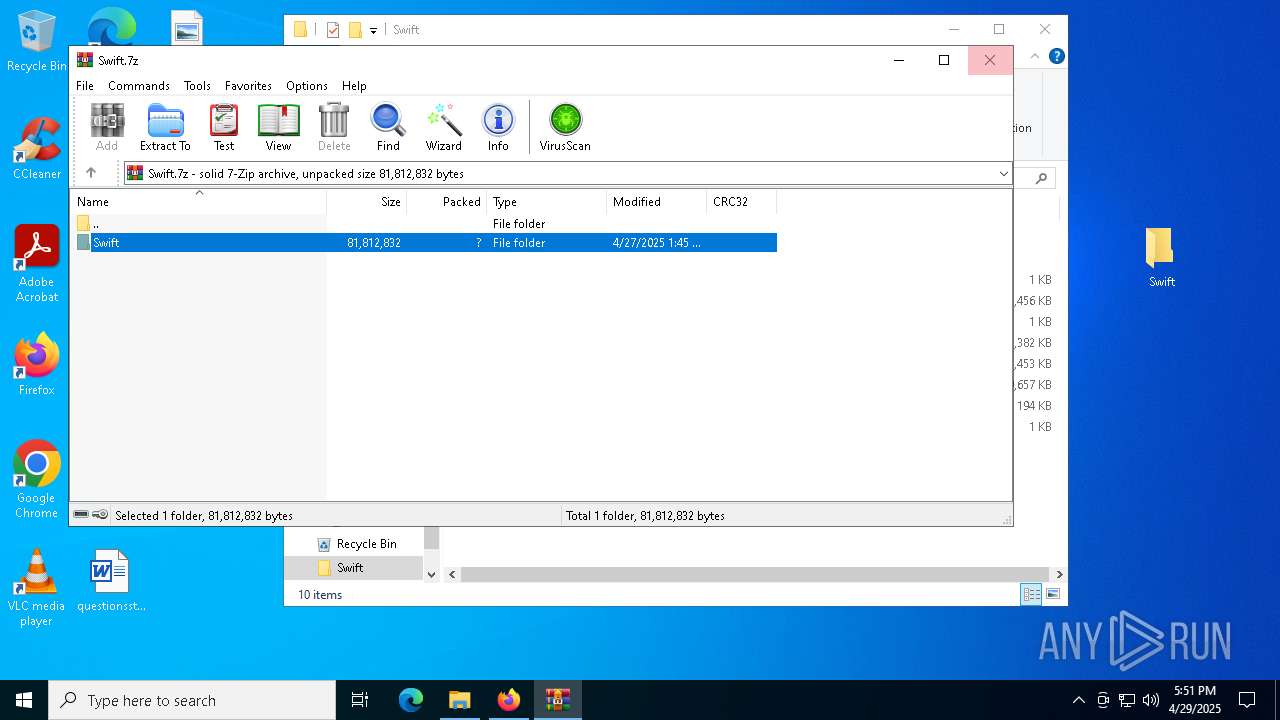
| (PID) Process: | (8884) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8884) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8884) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8884) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
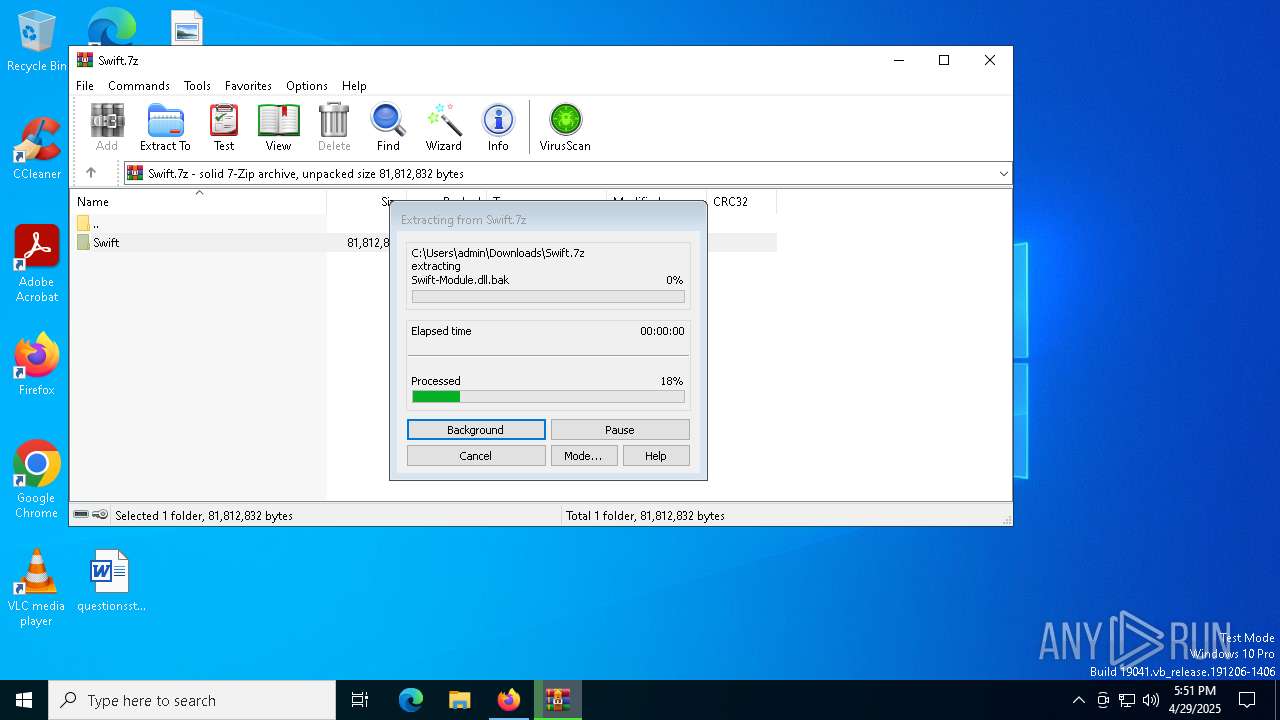
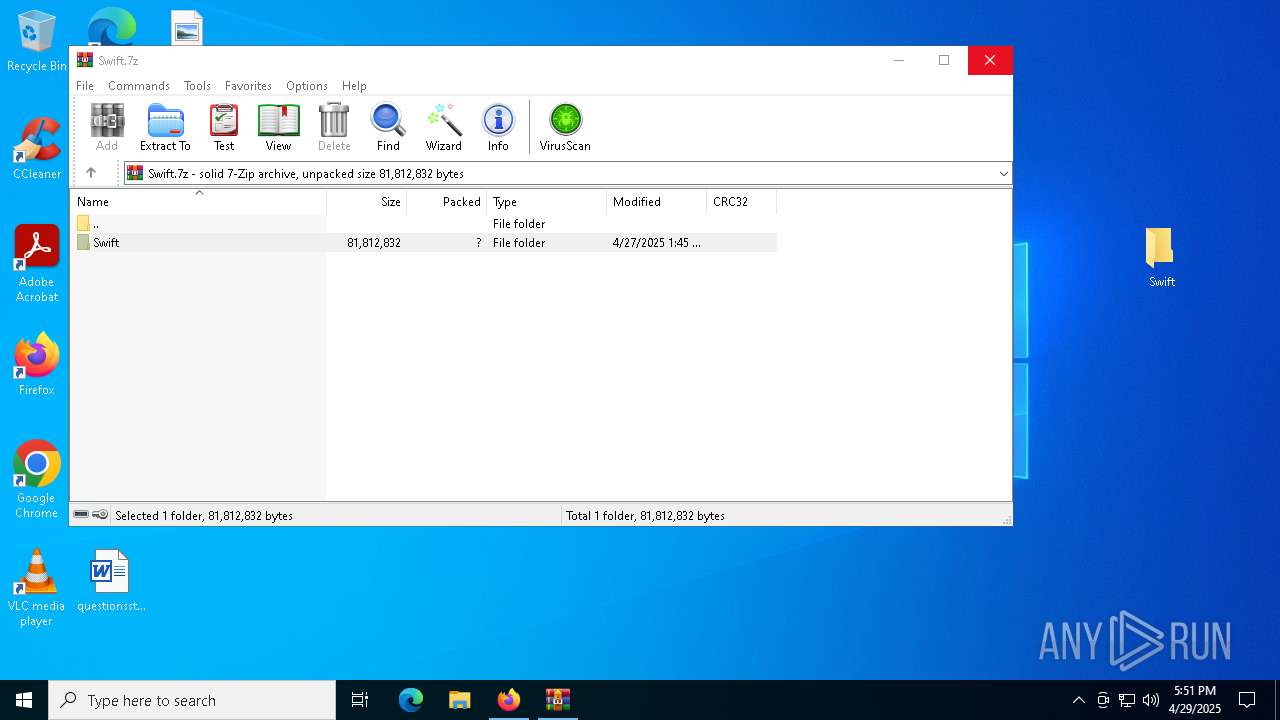
Value: C:\Users\admin\Downloads\Swift.7z | |||
| (PID) Process: | (8884) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8884) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
7
Suspicious files
174
Text files
32
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2392 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2392 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2392 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 2392 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2392 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2392 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 2392 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2392 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2392 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 2392 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
71
DNS requests
109
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2392 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
2392 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.33:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2392 | firefox.exe | POST | 200 | 184.24.77.44:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
2392 | firefox.exe | POST | 200 | 184.24.77.44:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
2392 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
2392 | firefox.exe | POST | 200 | 184.24.77.44:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
2392 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
2392 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1616 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.33:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2392 | firefox.exe | 104.18.3.146:443 | buzzheavier.com | CLOUDFLARENET | — | unknown |
2392 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
2392 | firefox.exe | 172.217.16.195:80 | o.pki.goog | GOOGLE | US | whitelisted |
2392 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
buzzheavier.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |