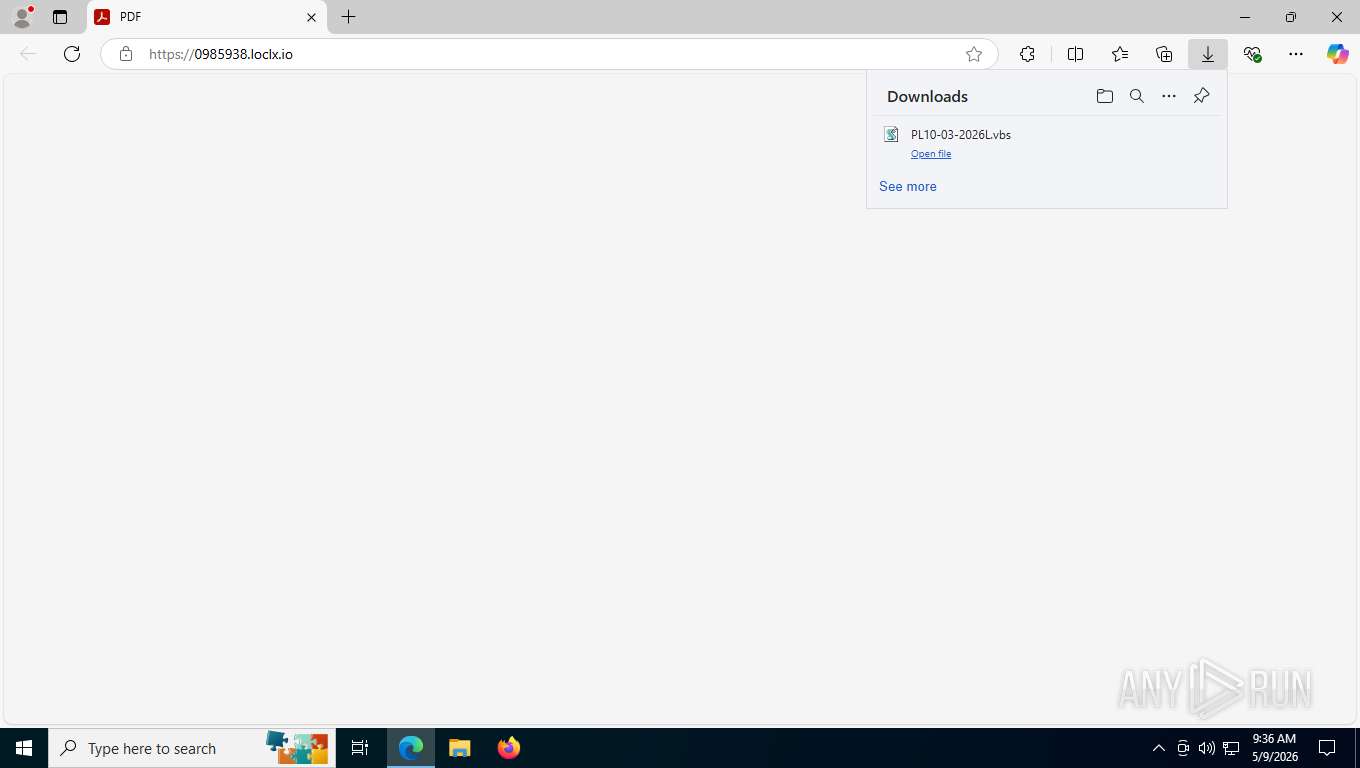
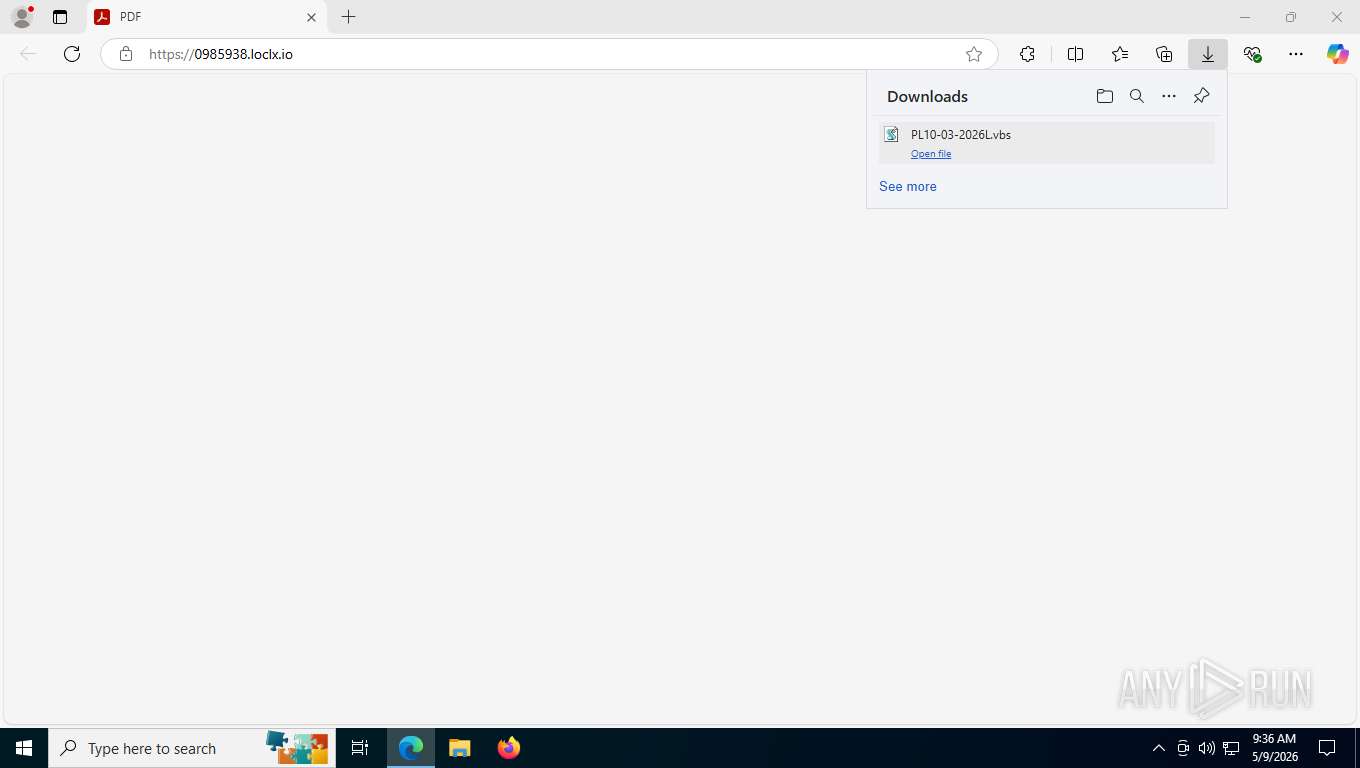
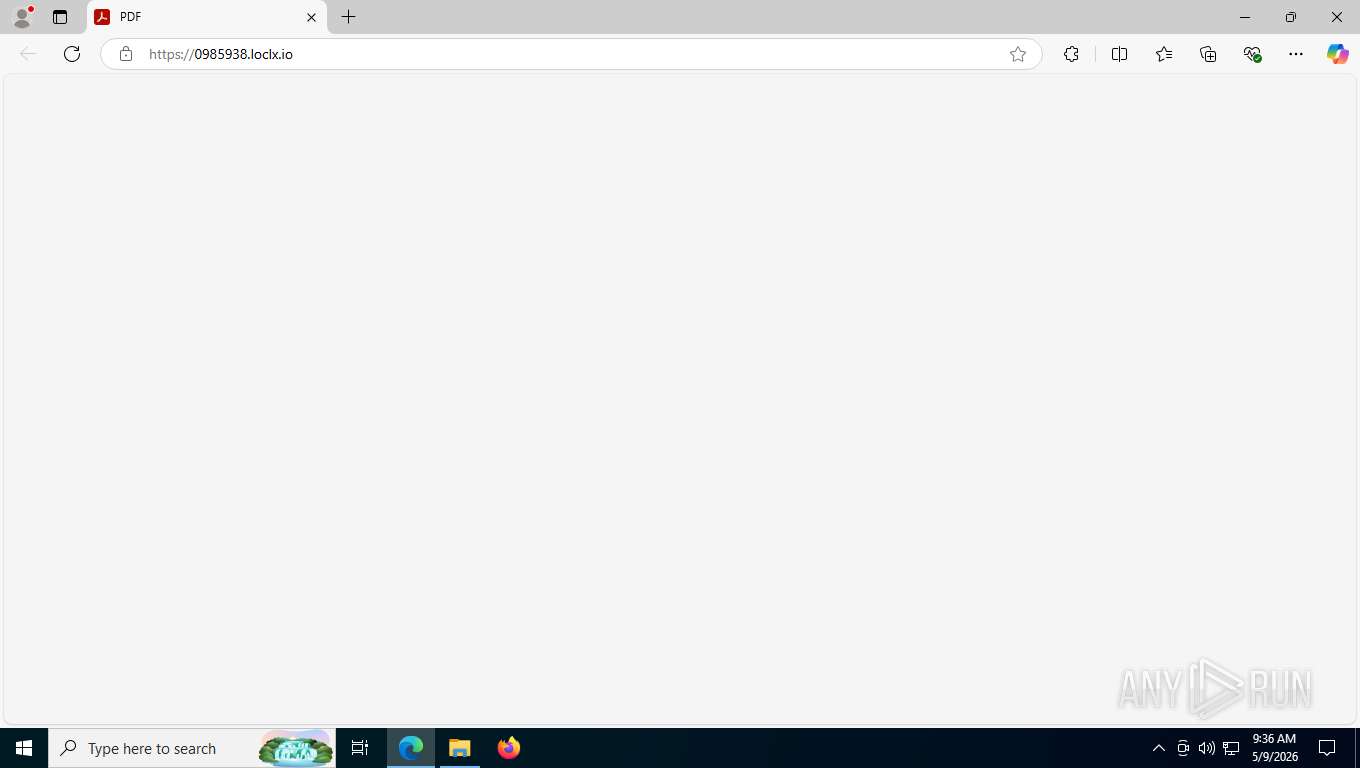
| URL: | https://0985938.loclx.io/ |
| Full analysis: | https://app.any.run/tasks/774c14a0-28f0-49e8-b620-9be10ac1cd97 |
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2026, 13:36:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A569C0EC26C174F90D97D98C60967BD5 |
| SHA1: | 979BAF0BAB6CADD7B0097DCCA4114FAAE5092E47 |
| SHA256: | B28420DEFB9F1172D37E5351049CC70607CF7E8E7674E6376BF7A1C988ADBA50 |
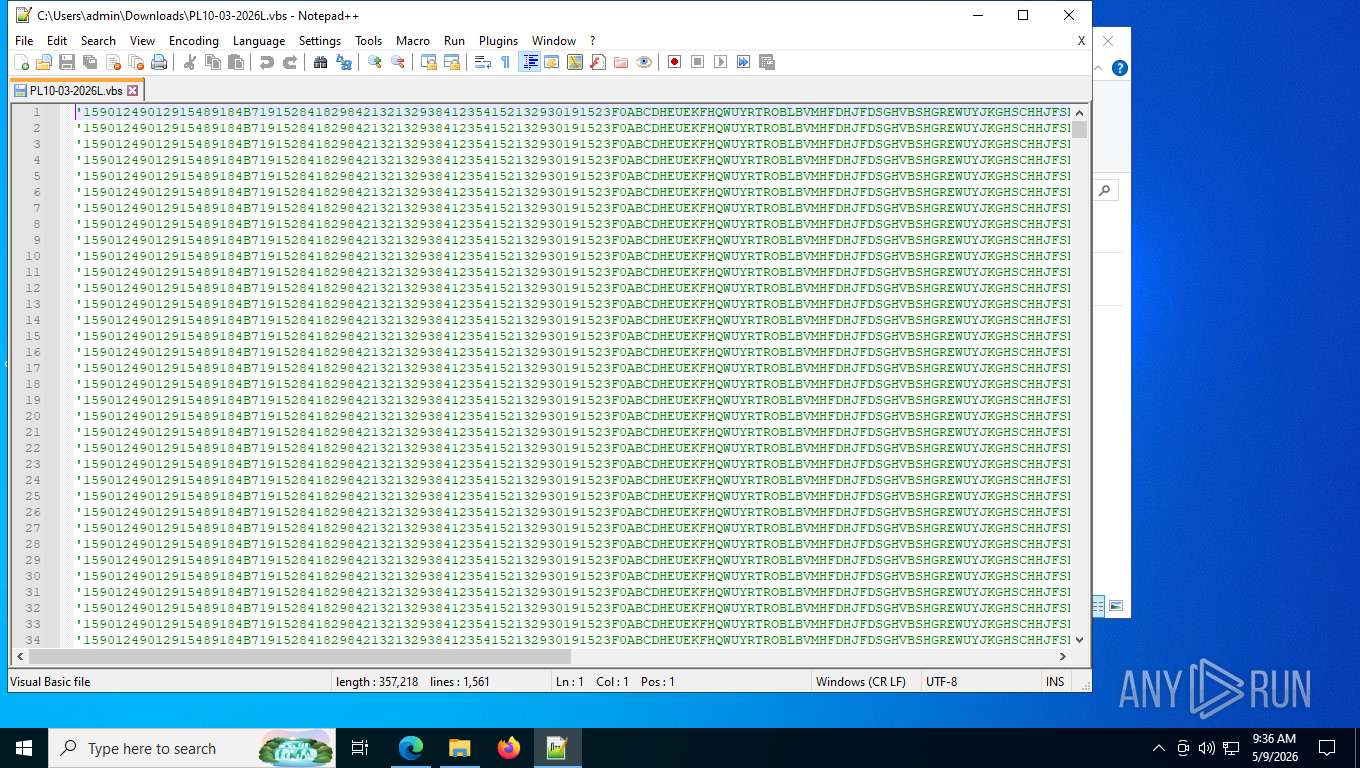
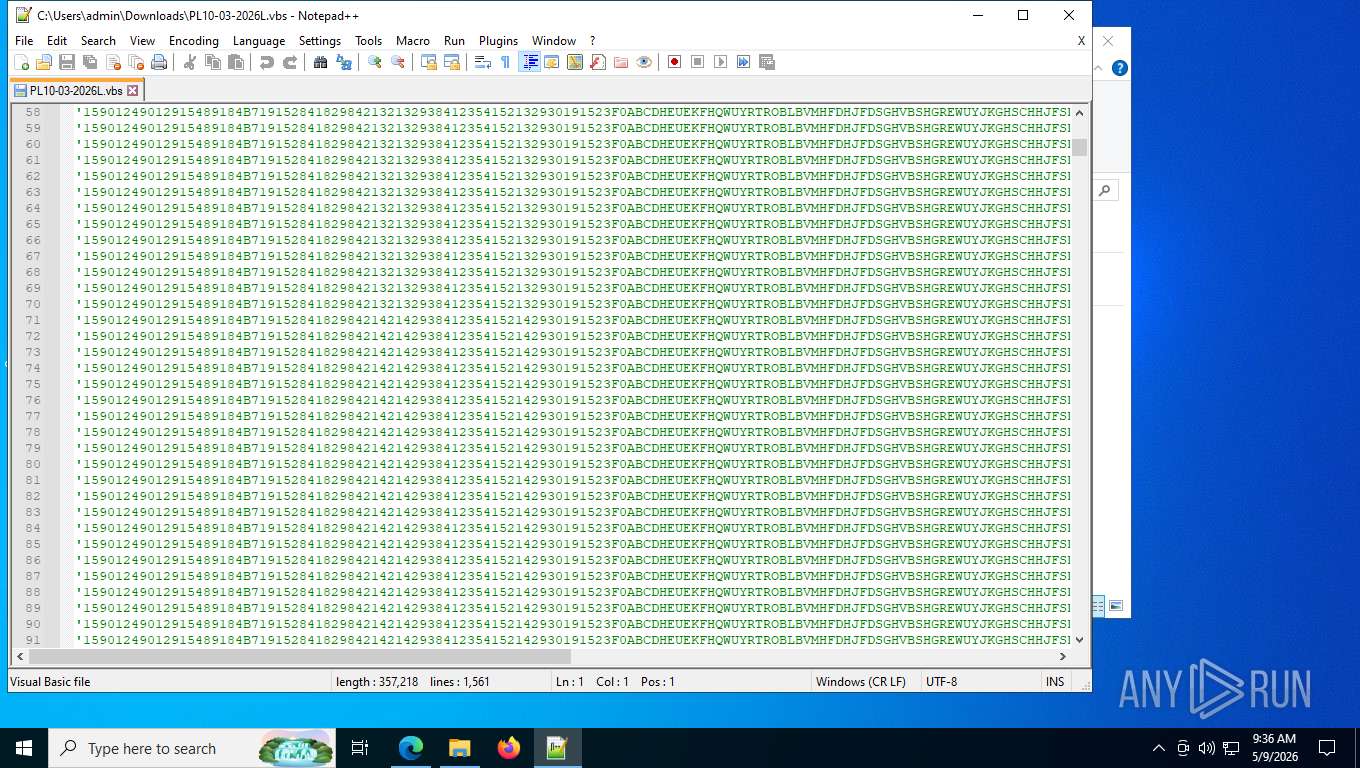
| SSDEEP: | 3:N8GAEMKn:2fzK |
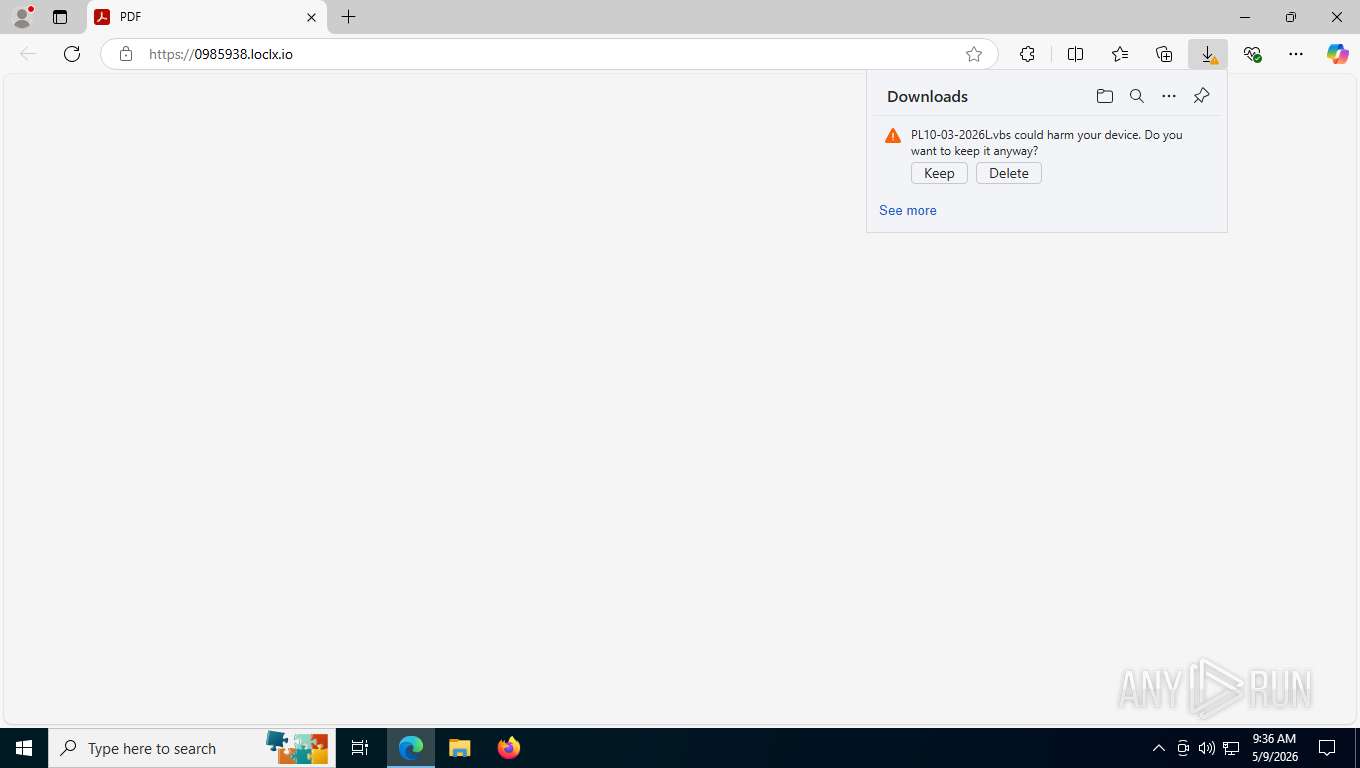
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 8868)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 8868)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 8868)
Creates a new folder (SCRIPT)
- wscript.exe (PID: 8868)
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 8868)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 8868)
Changes the autorun value in the registry
- reg.exe (PID: 5160)
- reg.exe (PID: 6844)
SUSPICIOUS
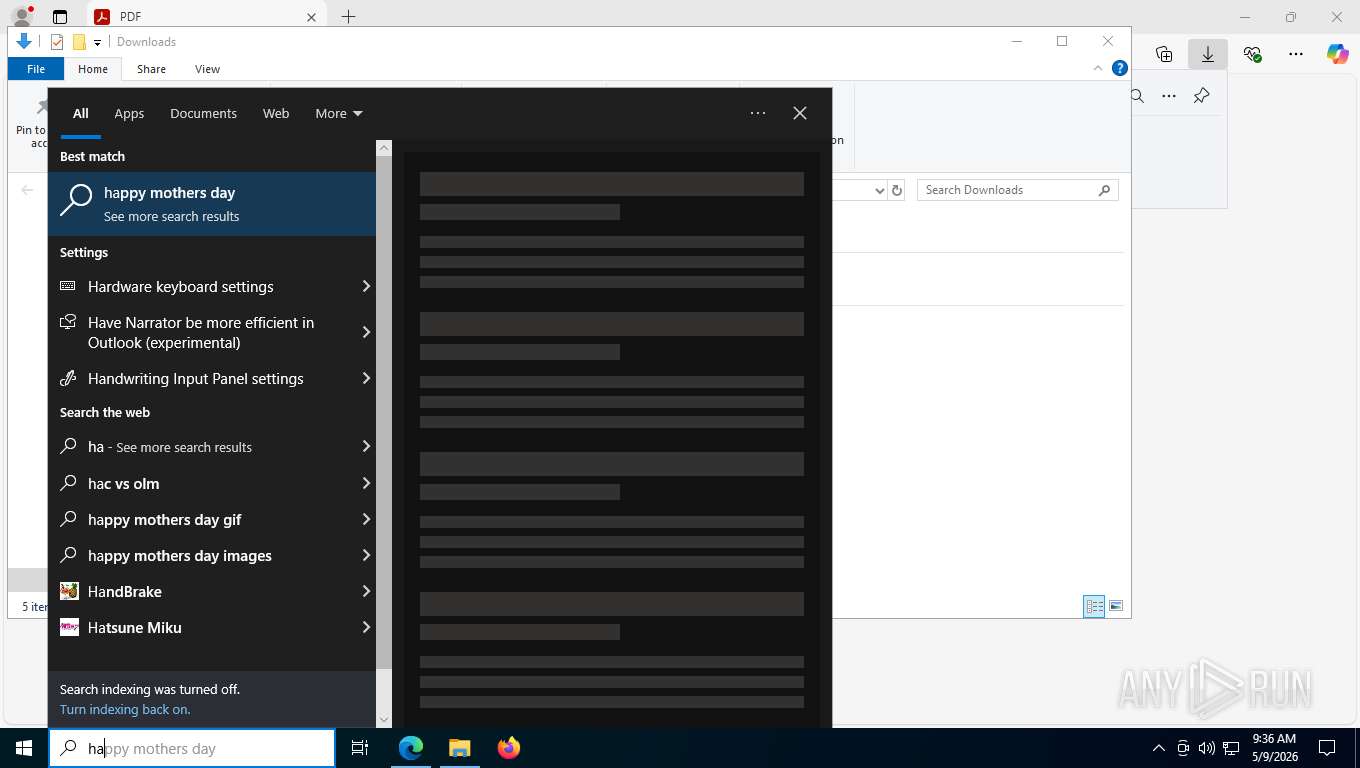
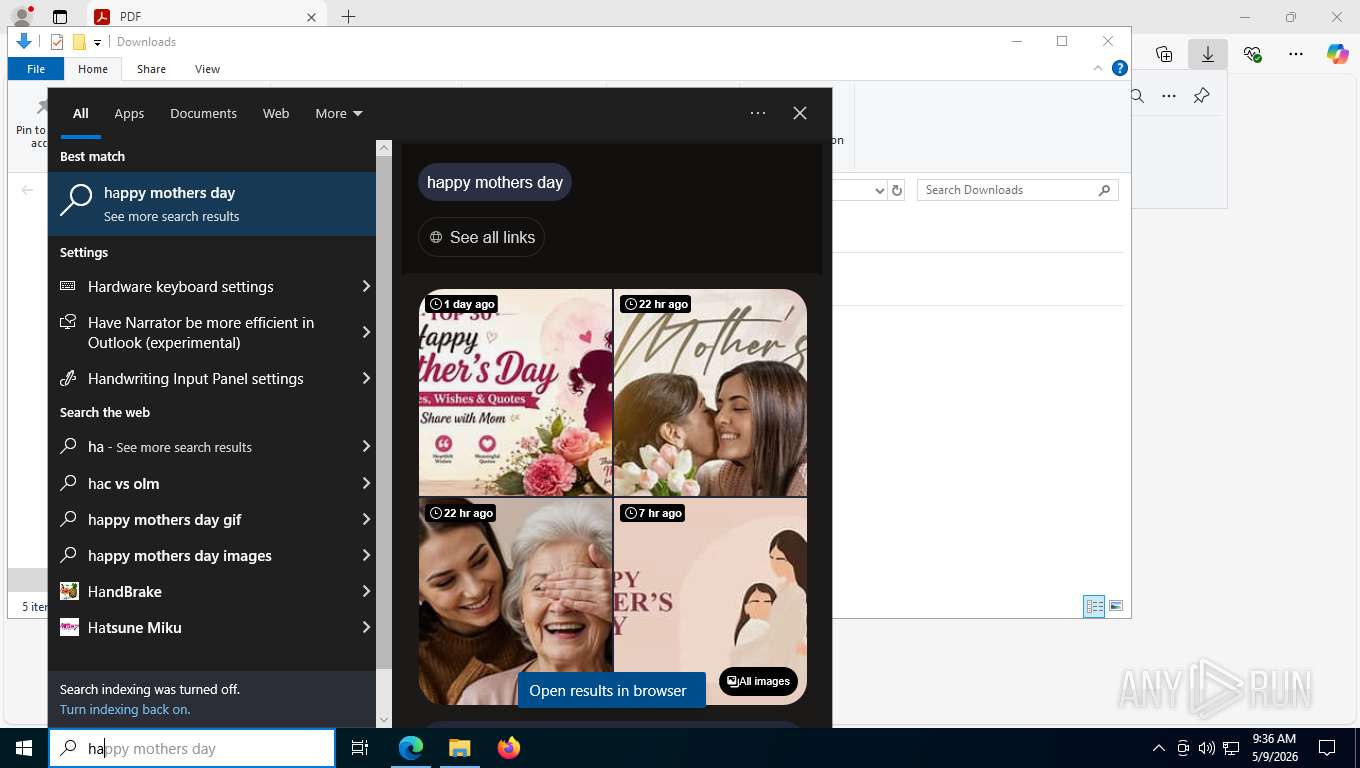
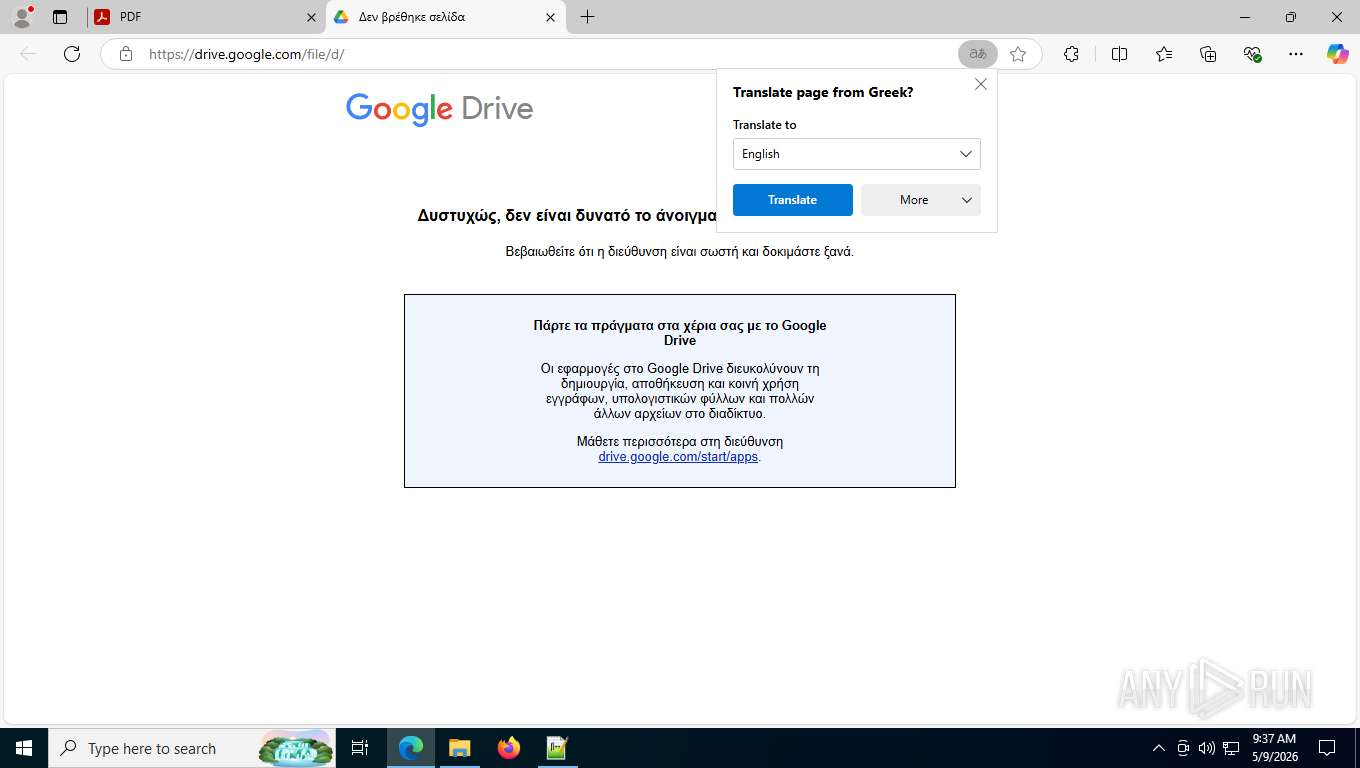
Potential Corporate Privacy Violation
- msedge.exe (PID: 4324)
The process executes VB scripts
- wscript.exe (PID: 8868)
- wscript.exe (PID: 9132)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 8868)
- wscript.exe (PID: 9132)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8868)
- wscript.exe (PID: 9132)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 8868)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 8868)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 8868)
Creates a Folder object (SCRIPT)
- wscript.exe (PID: 8868)
Executable content was dropped or overwritten
- wscript.exe (PID: 8868)
The process drops C-runtime libraries
- wscript.exe (PID: 8868)
Executing commands from ".cmd" file
- wscript.exe (PID: 8868)
- wscript.exe (PID: 9132)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 5484)
- java.exe (PID: 3008)
- cmd.exe (PID: 5568)
- reg.exe (PID: 5160)
- cmd.exe (PID: 7504)
- java.exe (PID: 7992)
- cmd.exe (PID: 7672)
- reg.exe (PID: 6844)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 5484)
- cmd.exe (PID: 5568)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7672)
Uses REG/REGEDIT.EXE to modify or delete registry entries
- cmd.exe (PID: 5568)
- cmd.exe (PID: 7672)
Starts CMD.EXE with AutoRun commands disabled
- cmd.exe (PID: 5568)
- cmd.exe (PID: 7672)
Checks system UUID (probably for evasion)
- java.exe (PID: 3008)
- java.exe (PID: 7992)
Uses WMIC.EXE to obtain Windows Installer data
- java.exe (PID: 3008)
- java.exe (PID: 7992)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 6448)
- WMIC.exe (PID: 8060)
INFO
Application launched itself
- msedge.exe (PID: 5196)
- msedge.exe (PID: 8924)
- msedge.exe (PID: 7408)
Checks supported languages
- identity_helper.exe (PID: 2368)
- identity_helper.exe (PID: 7952)
- java.exe (PID: 3008)
- java.exe (PID: 7992)
- identity_helper.exe (PID: 2332)
Reads the computer name
- identity_helper.exe (PID: 2368)
- java.exe (PID: 3008)
- identity_helper.exe (PID: 7952)
- identity_helper.exe (PID: 2332)
- java.exe (PID: 7992)
Reads Environment values
- identity_helper.exe (PID: 2368)
- identity_helper.exe (PID: 7952)
- identity_helper.exe (PID: 2332)
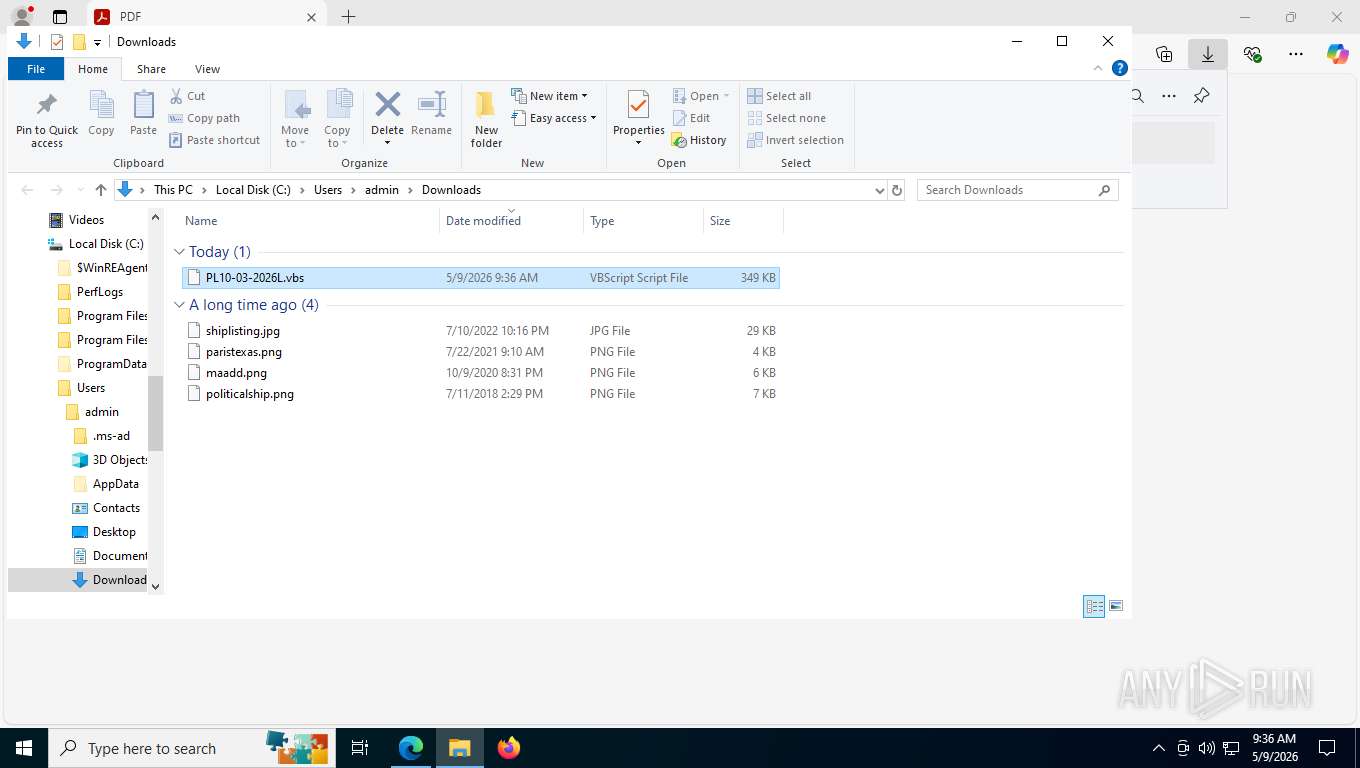
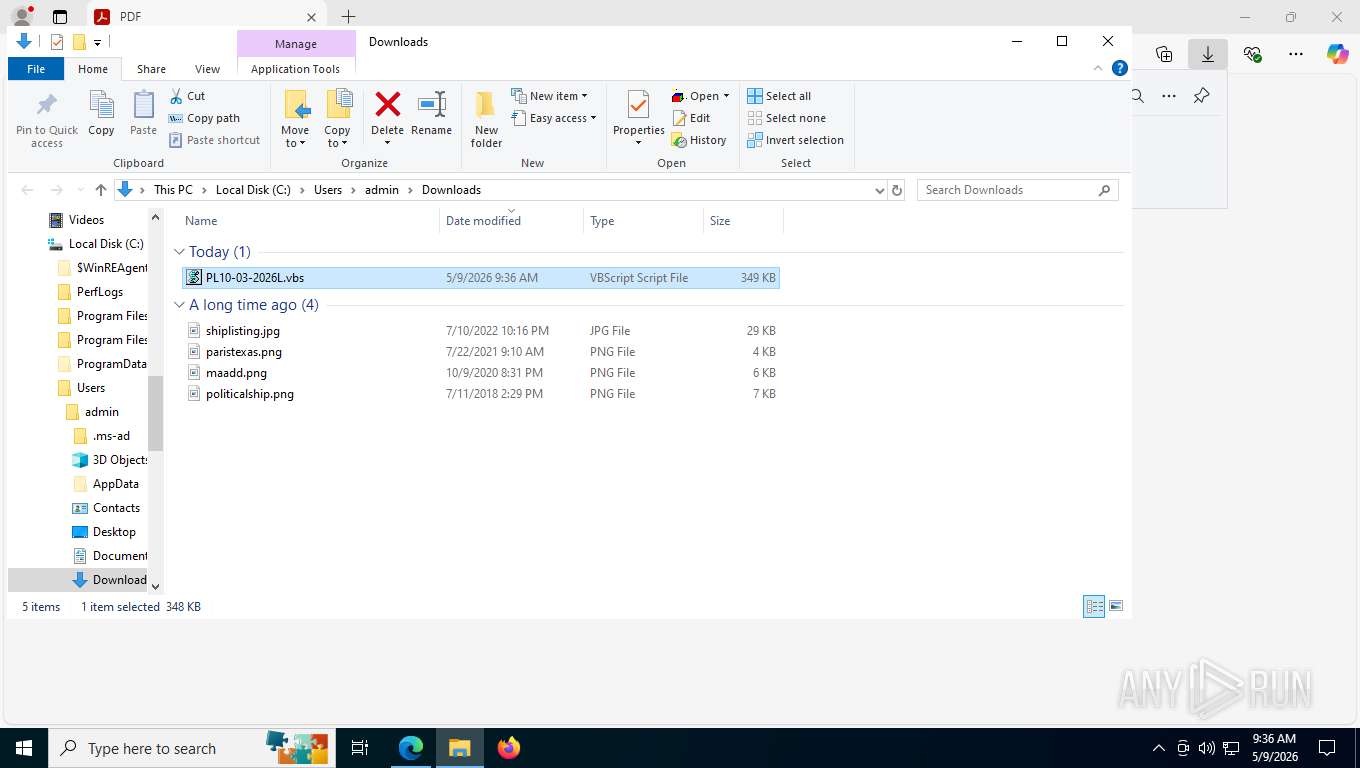
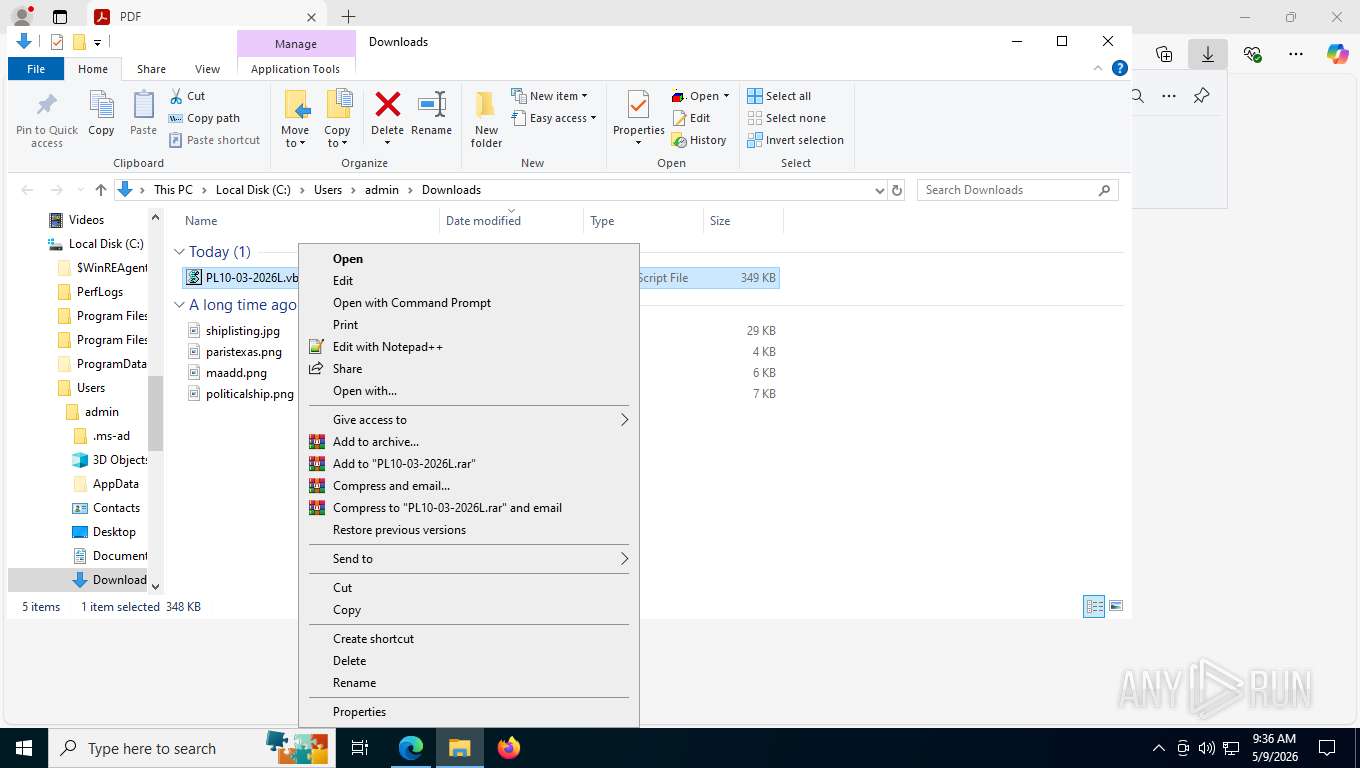
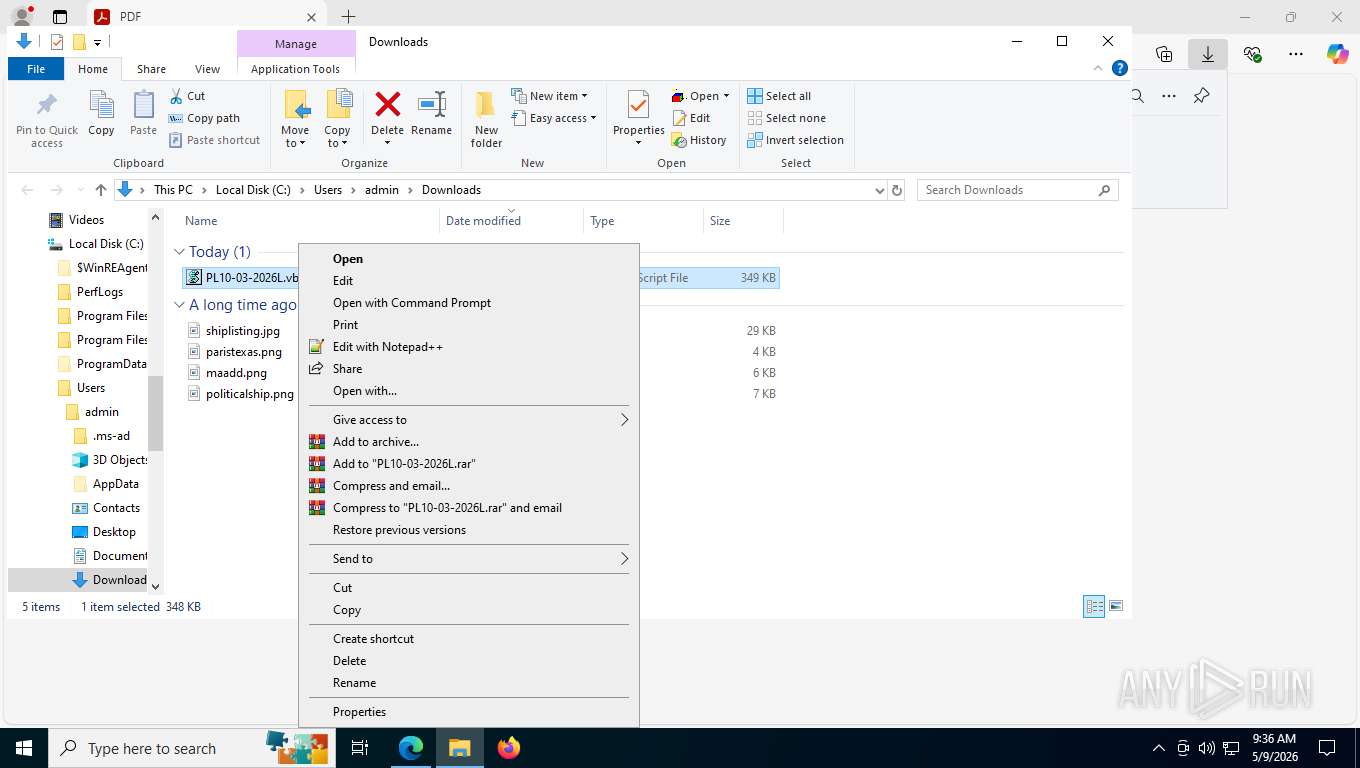
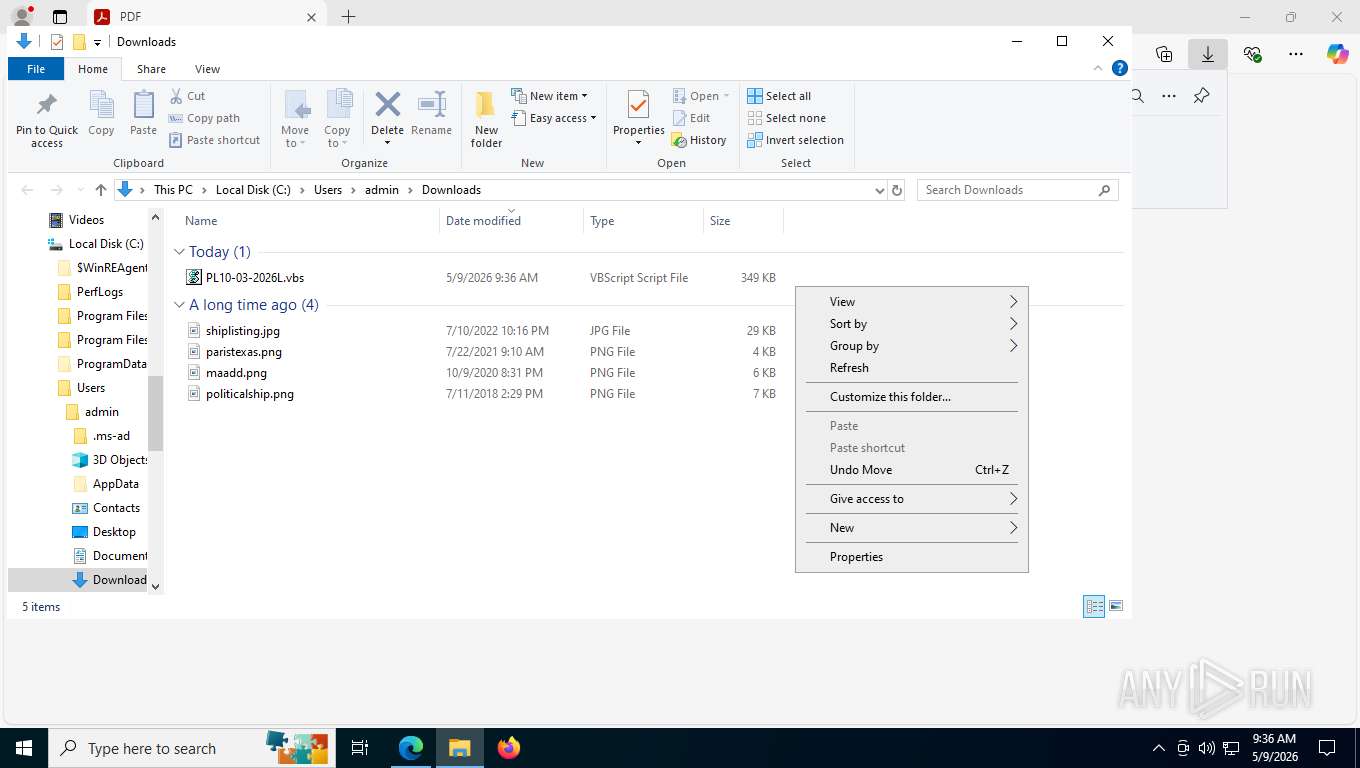
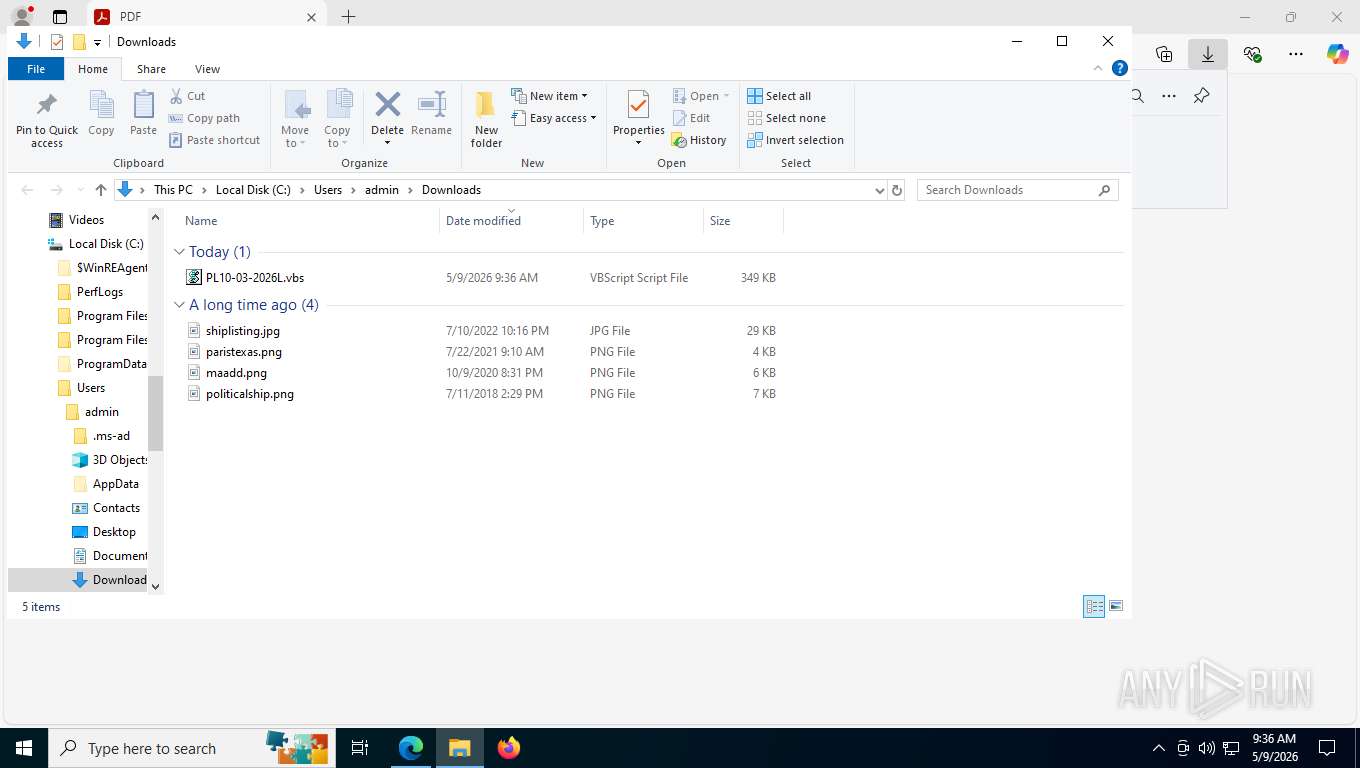
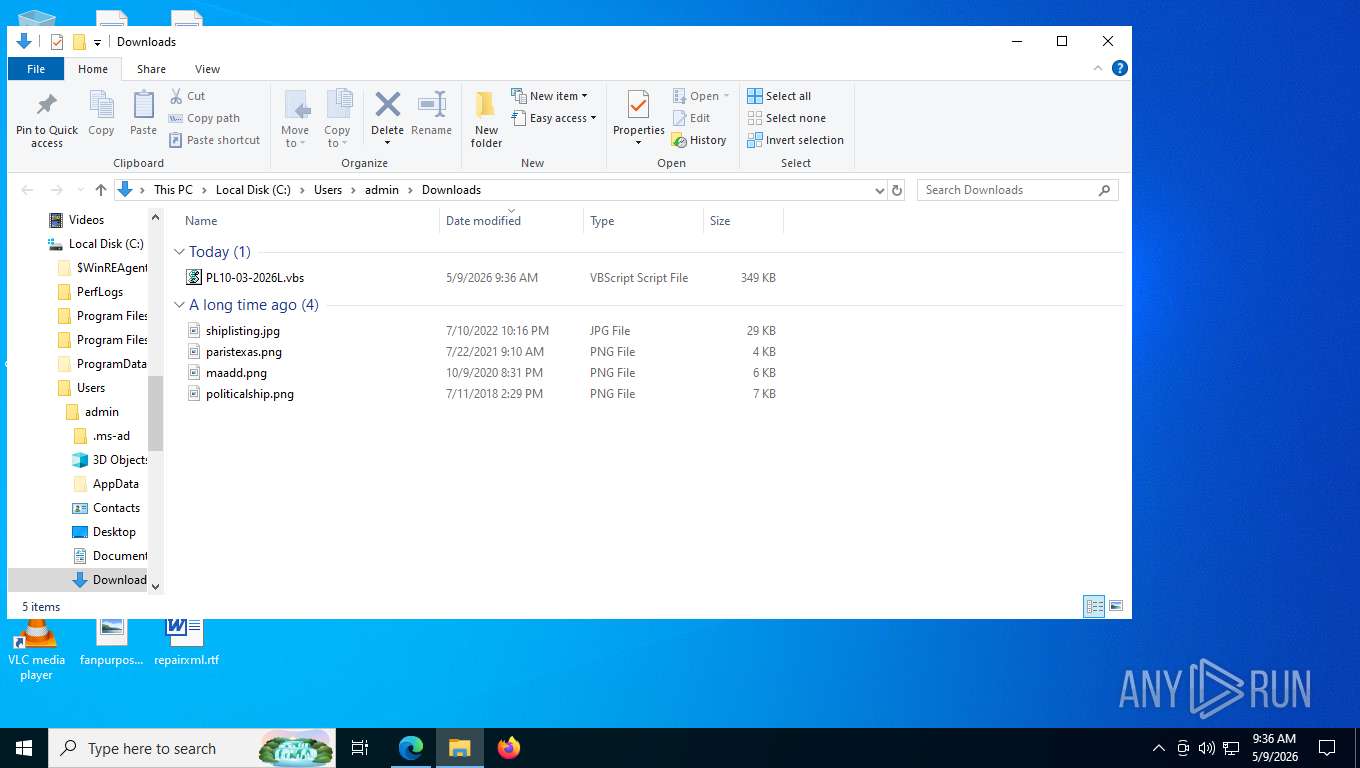
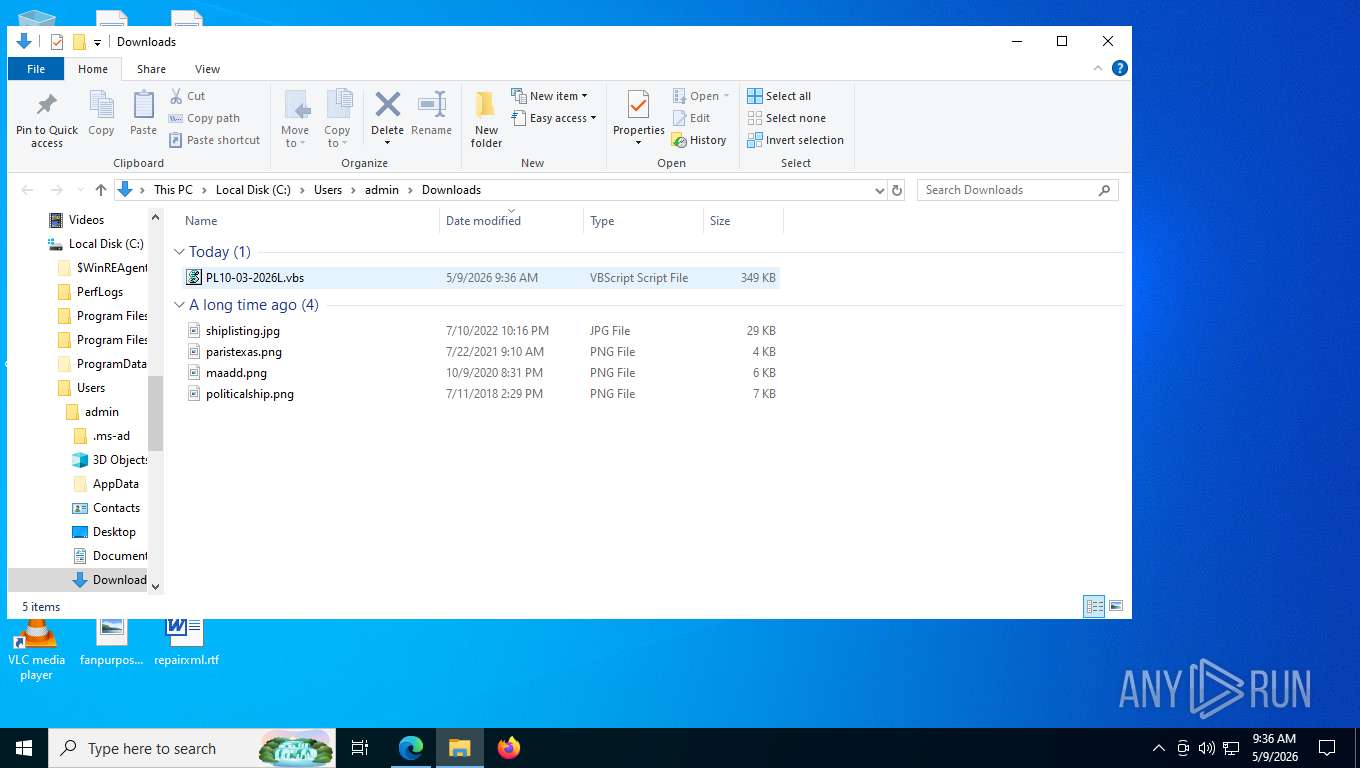
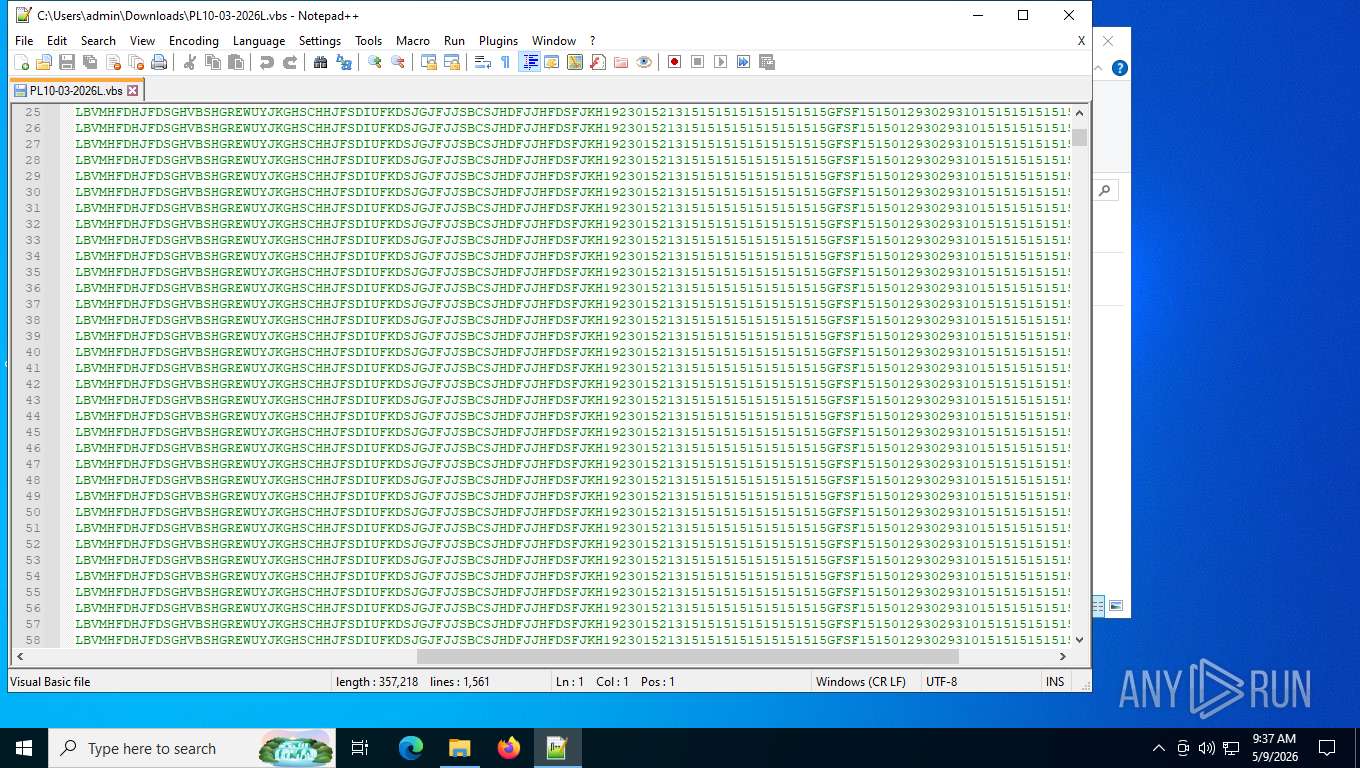
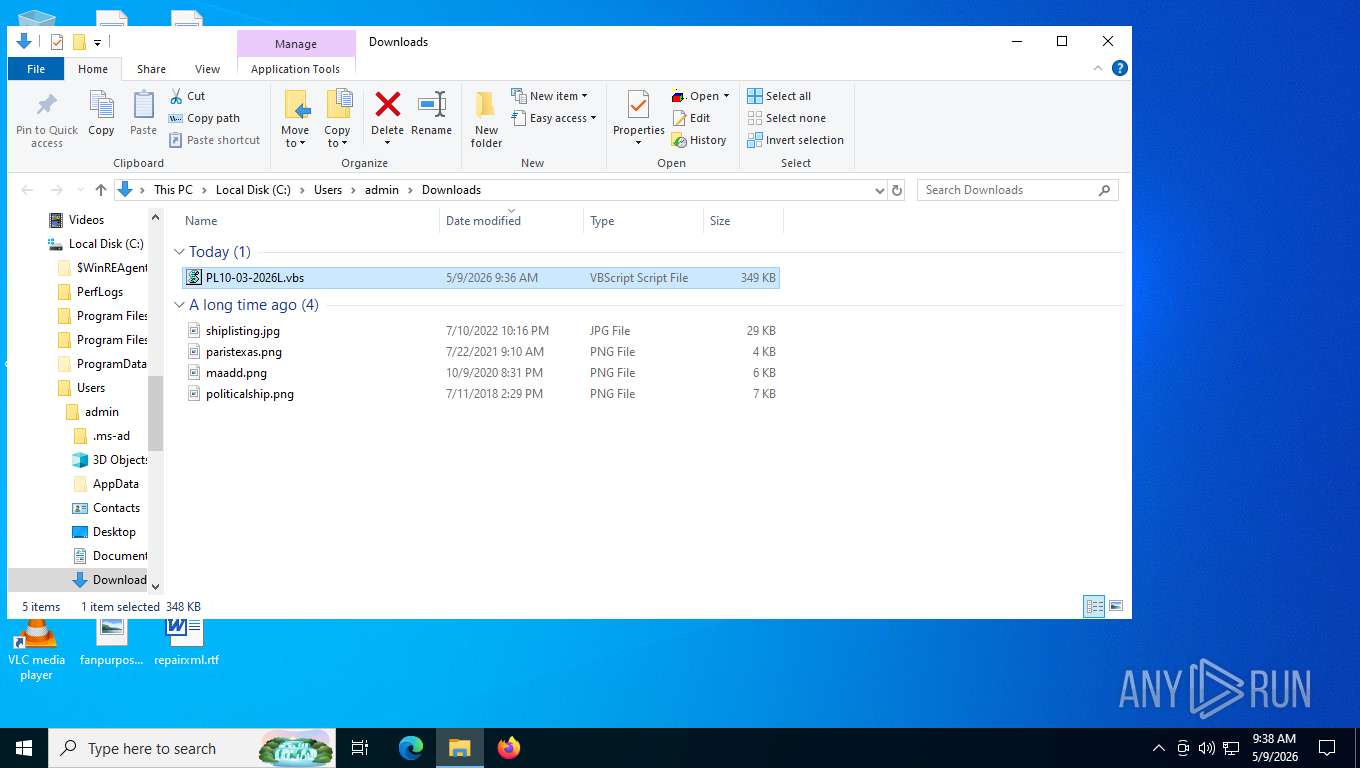
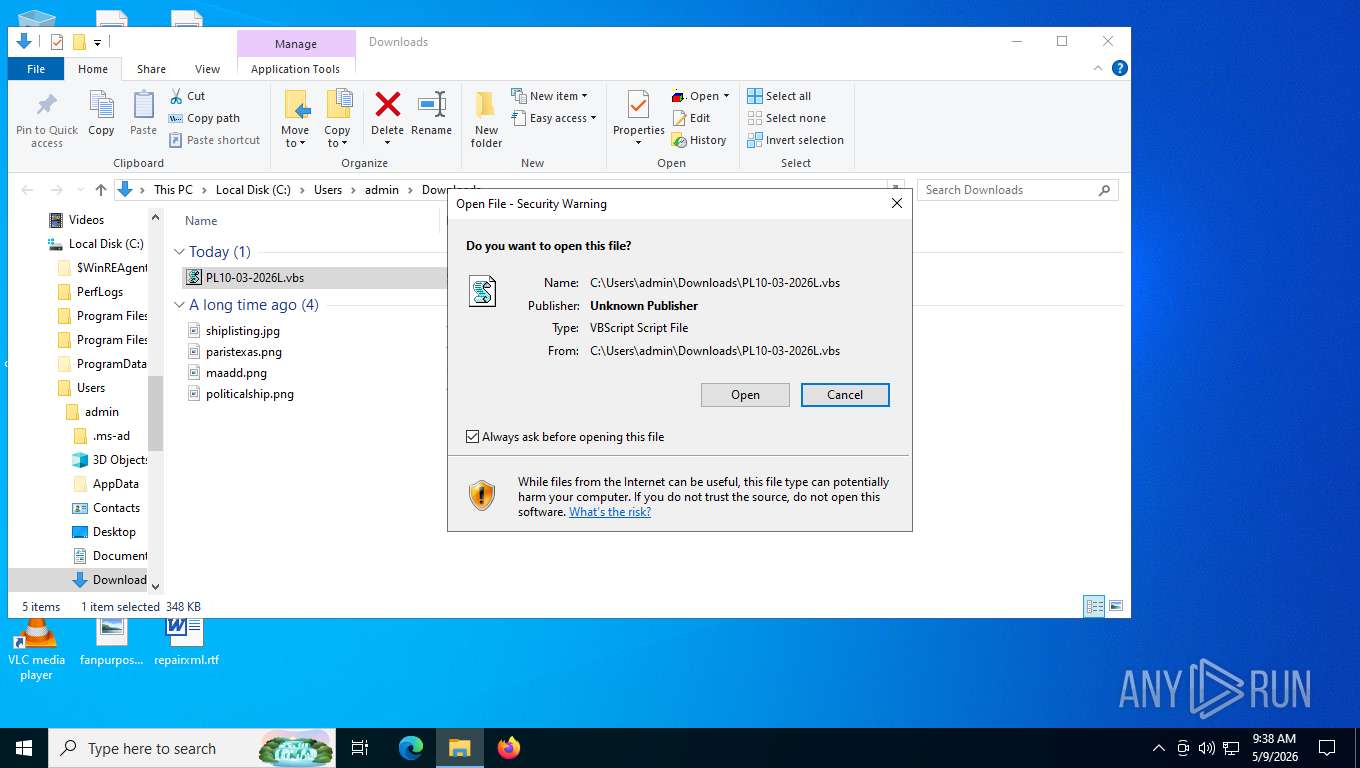
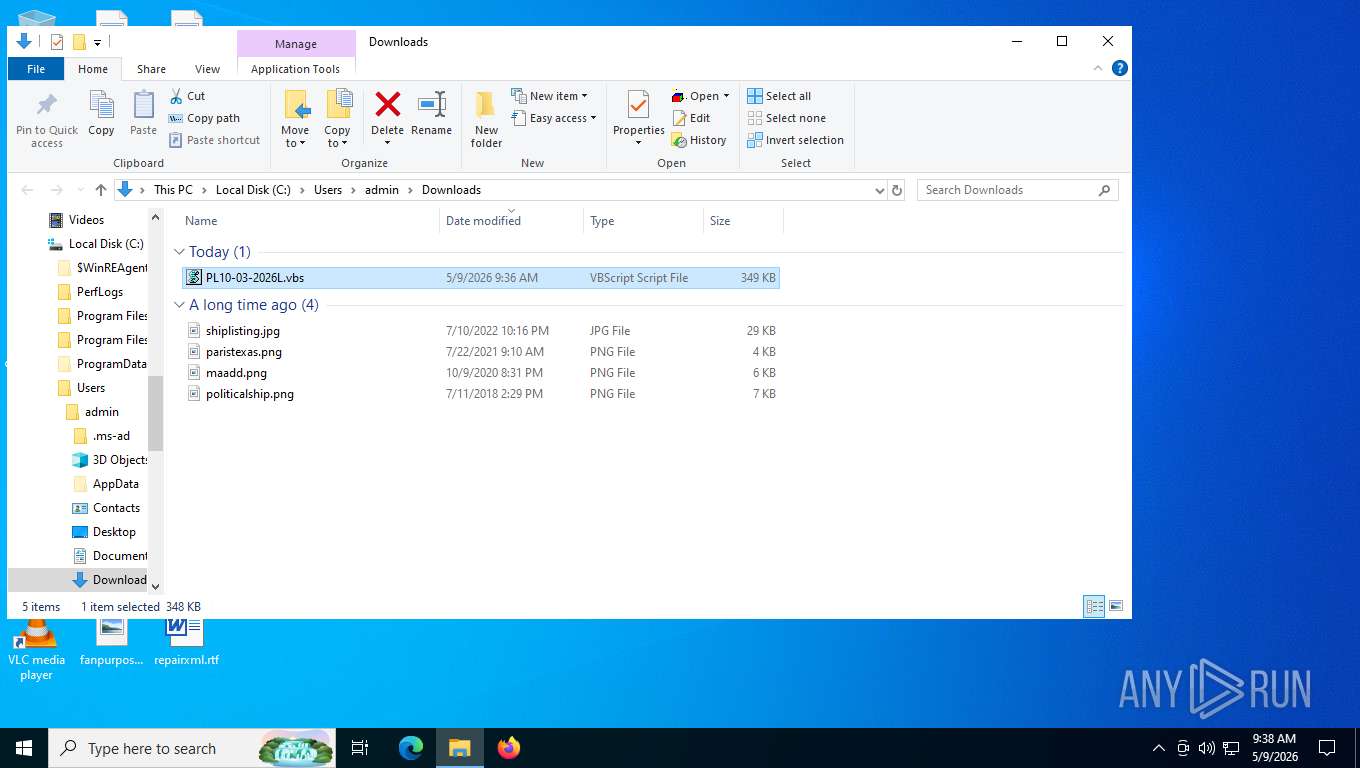
Launching a file from the Downloads directory
- msedge.exe (PID: 5196)
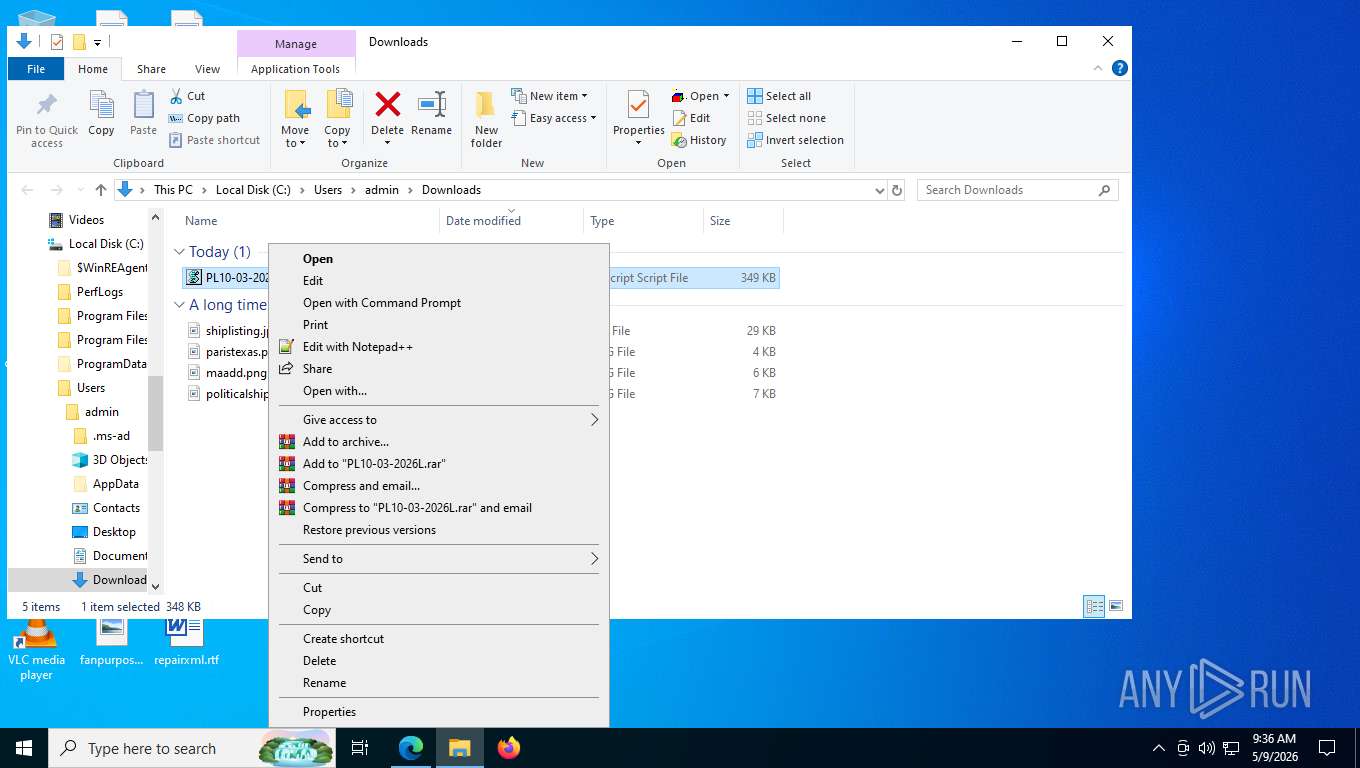
Manual execution by a user
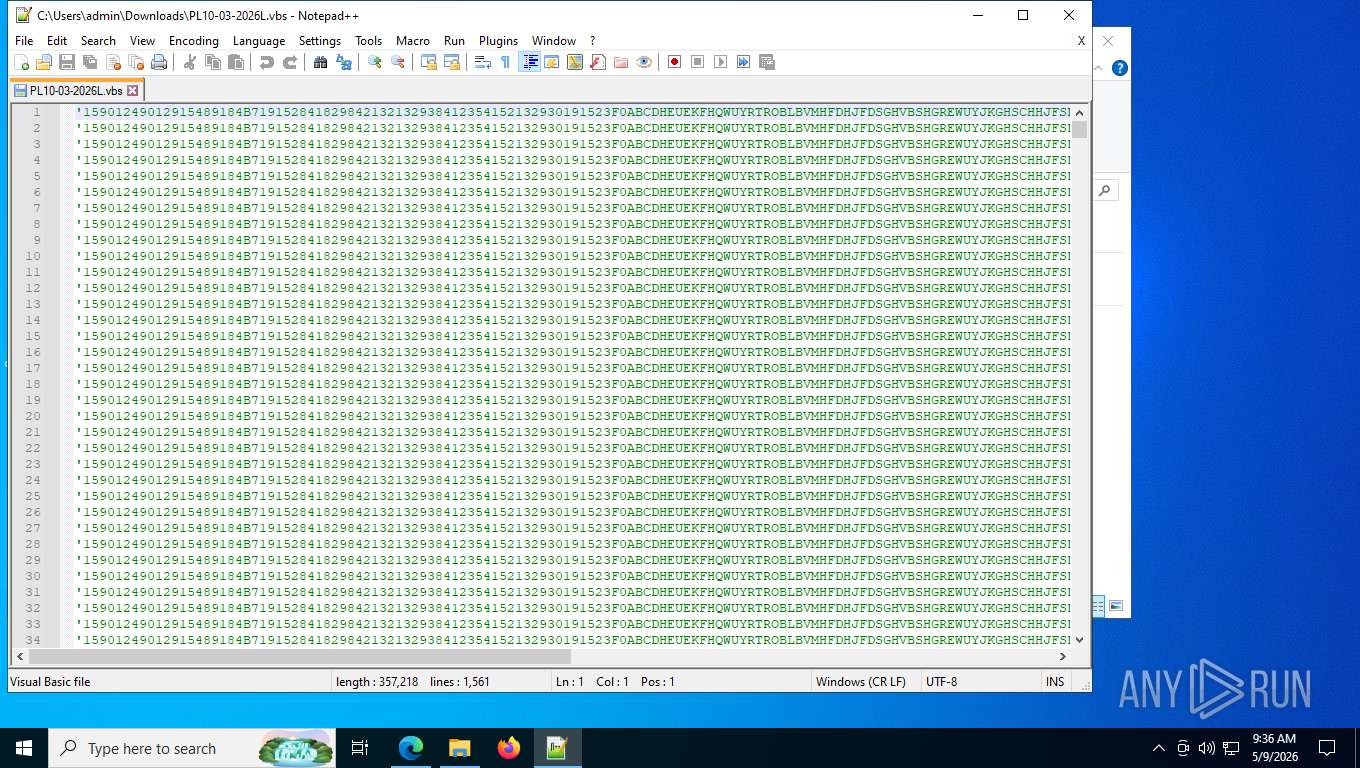
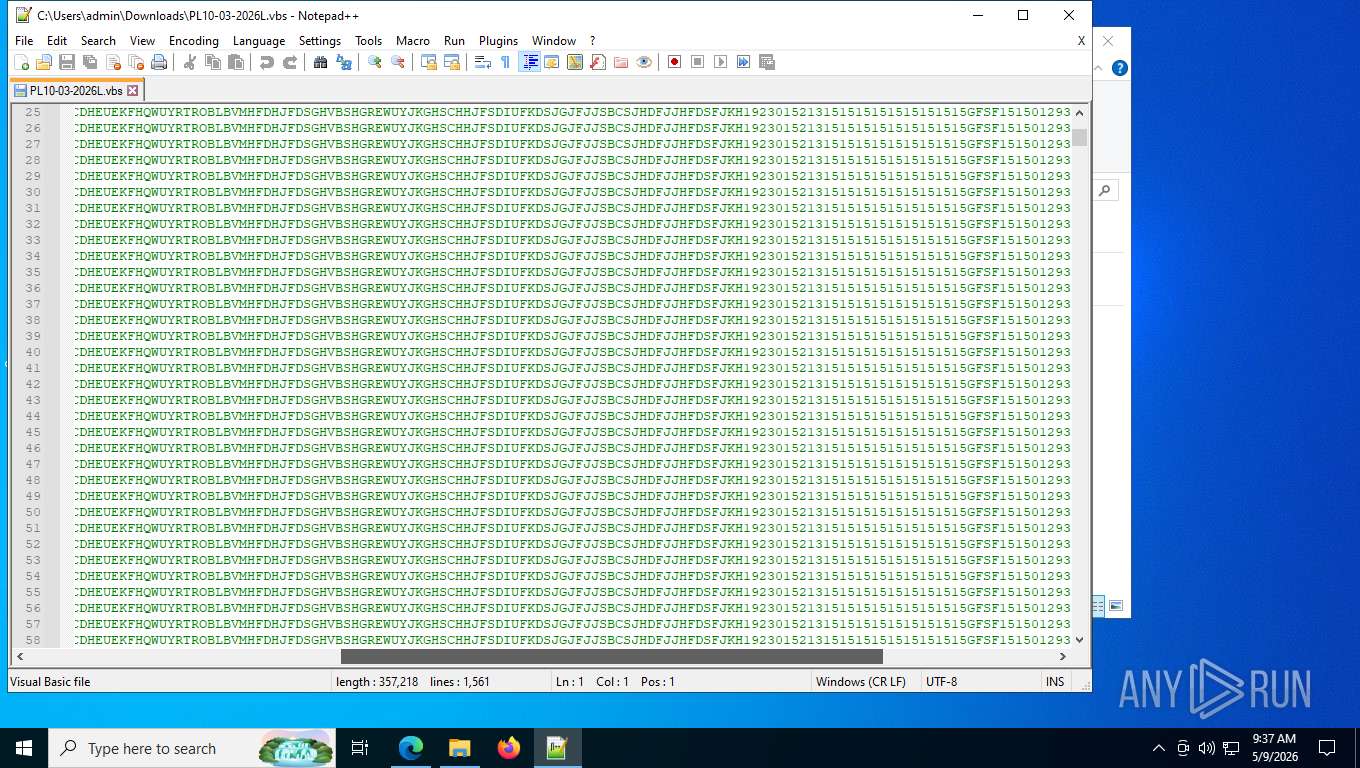
- notepad++.exe (PID: 8272)
- wscript.exe (PID: 8868)
- wscript.exe (PID: 9132)
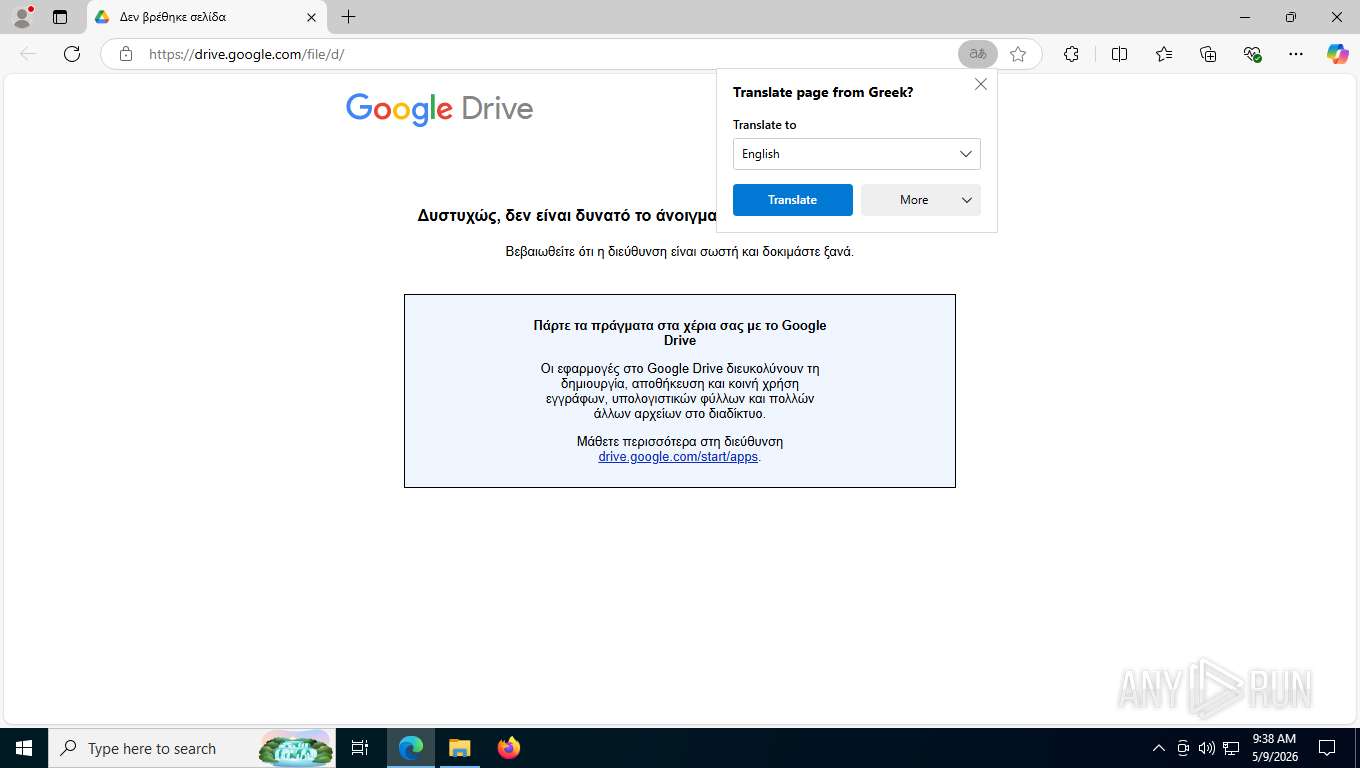
Attempting to use file storage service
- wscript.exe (PID: 8868)
The sample compiled with english language support
- wscript.exe (PID: 8868)
There is functionality for taking screenshot (YARA)
- wscript.exe (PID: 8868)
Create files in a temporary directory
- java.exe (PID: 3008)
- java.exe (PID: 7992)
Creates files or folders in the user directory
- java.exe (PID: 3008)
- java.exe (PID: 7992)
Launching a file from a Registry key
- reg.exe (PID: 5160)
- reg.exe (PID: 6844)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6448)
- WMIC.exe (PID: 8060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
217
Monitored processes
78
Malicious processes
2
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1176 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3656,i,4602889773111448281,1146070098690420690,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3816 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1500 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=25 --always-read-main-dll --field-trial-handle=5592,i,4602889773111448281,1146070098690420690,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5964 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1500 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5700,i,12199120513864074682,5865076760218850708,262144 --variations-seed-version --mojo-platform-channel-handle=5668 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1684 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5848,i,4602889773111448281,1146070098690420690,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6332 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1724 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6136,i,4602889773111448281,1146070098690420690,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5952 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2092 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5712,i,12199120513864074682,5865076760218850708,262144 --variations-seed-version --mojo-platform-channel-handle=5780 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2232 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2332 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2332 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4872,i,15230100928658885559,10835276325571670203,262144 --variations-seed-version --mojo-platform-channel-handle=4824 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
14 753
Read events
14 743
Write events
10
Delete events
0
Modification events
| (PID) Process: | (8868) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (8868) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8868) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8868) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5160) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | AutoRunKey |
Value: C:\Users\Public\voicepress\bin\javaw.exe -jar C:\Users\admin\AppData\Roaming\DATA\1778333882900.png | |||
| (PID) Process: | (9132) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (9132) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (9132) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (9132) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6844) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | AutoRunKey |
Value: C:\Users\Public\voicepress\bin\javaw.exe -jar C:\Users\admin\AppData\Roaming\DATA\1778333884979.png | |||
Executable files
187
Suspicious files
379
Text files
609
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFdff5f.TMP | — | |
MD5:— | SHA256:— | |||
| 5196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFdff5f.TMP | — | |
MD5:— | SHA256:— | |||
| 5196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFdff6f.TMP | — | |
MD5:— | SHA256:— | |||
| 5196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFdff6f.TMP | — | |
MD5:— | SHA256:— | |||
| 5196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFdff7f.TMP | — | |
MD5:— | SHA256:— | |||
| 5196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
493
TCP/UDP connections
125
DNS requests
154
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4324 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:YbYdBtcN2b5faJbss9DmyQXL7gN6KbtWJC_h4CO8Q9M&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
5532 | SearchApp.exe | GET | 200 | 23.11.40.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | NL | binary | 312 b | whitelisted |
4324 | msedge.exe | GET | 304 | 150.171.28.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
5532 | SearchApp.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 924 b | whitelisted |
4324 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 132 b | whitelisted |
4324 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
4324 | msedge.exe | GET | 200 | 150.171.109.193:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
4324 | msedge.exe | GET | 200 | 52.123.243.207:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.14 Kb | whitelisted |
4324 | msedge.exe | GET | 404 | 185.15.59.240:443 | https://upload.wikimedia.org/wikipedia/commons/8/87/Adobe_Acrobat_DC_logo_2020.png | US | text | 97 b | unknown |
4324 | msedge.exe | GET | 200 | 45.55.35.48:443 | https://0985938.loclx.io/ | US | html | 7.27 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
8044 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | SearchApp.exe | 92.123.104.56:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
5532 | SearchApp.exe | 23.11.40.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
5532 | SearchApp.exe | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
4324 | msedge.exe | 52.123.243.207:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4324 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
0985938.loclx.io |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4324 | msedge.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] DNS Query Reverse Proxy Domain Sevice (loclx .io) |
4324 | msedge.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] DNS Query Reverse Proxy Domain Sevice (loclx .io) |
4324 | msedge.exe | Misc activity | ET INFO Observed Network Tunneling Service Domain (loclx .io) in TLS SNI |
4324 | msedge.exe | Misc activity | ET INFO Observed Network Tunneling Service Domain (loclx .io) in TLS SNI |
4324 | msedge.exe | Misc activity | ET INFO Observed Network Tunneling Service Domain (loclx .io) in TLS SNI |
4324 | msedge.exe | Misc activity | ET INFO Observed Network Tunneling Service Domain (loclx .io) in TLS SNI |
4324 | msedge.exe | Misc activity | ET INFO Observed Network Tunneling Service Domain (loclx .io) in TLS SNI |
8044 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
8868 | wscript.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
2232 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|