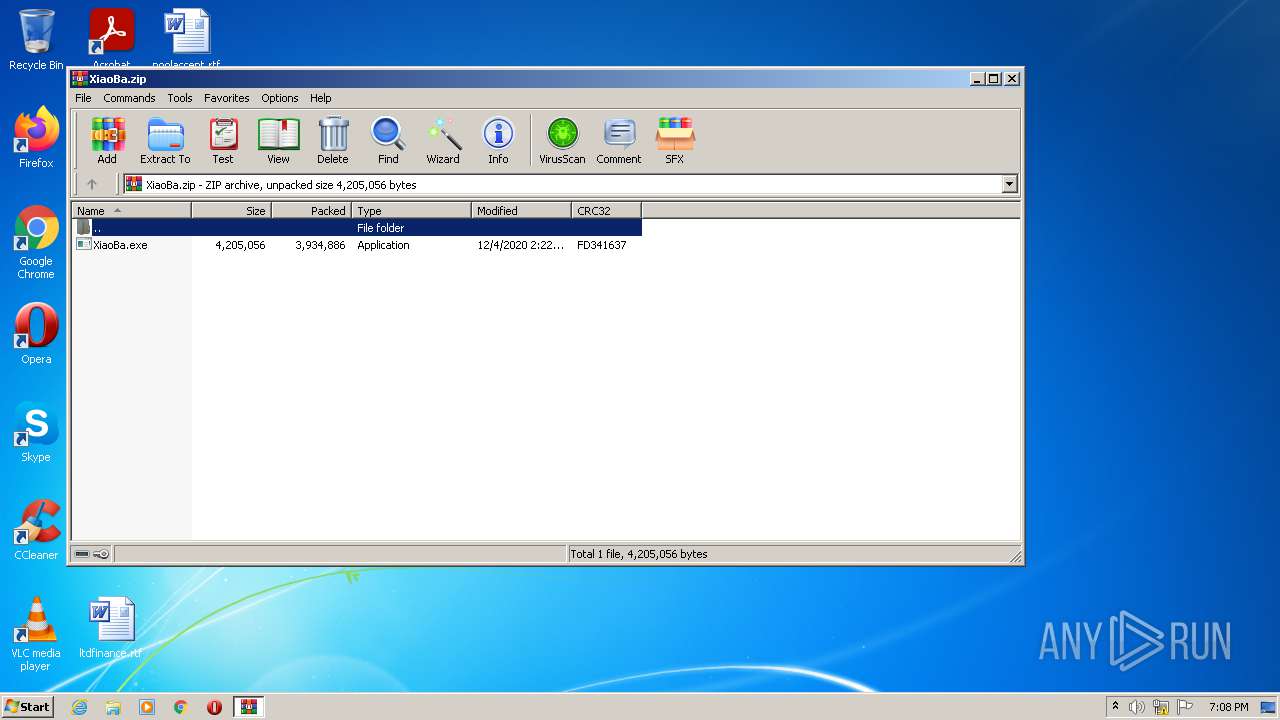
| File name: | XiaoBa.zip |
| Full analysis: | https://app.any.run/tasks/1eafe937-7954-4374-ae2c-4c6f6bca6382 |
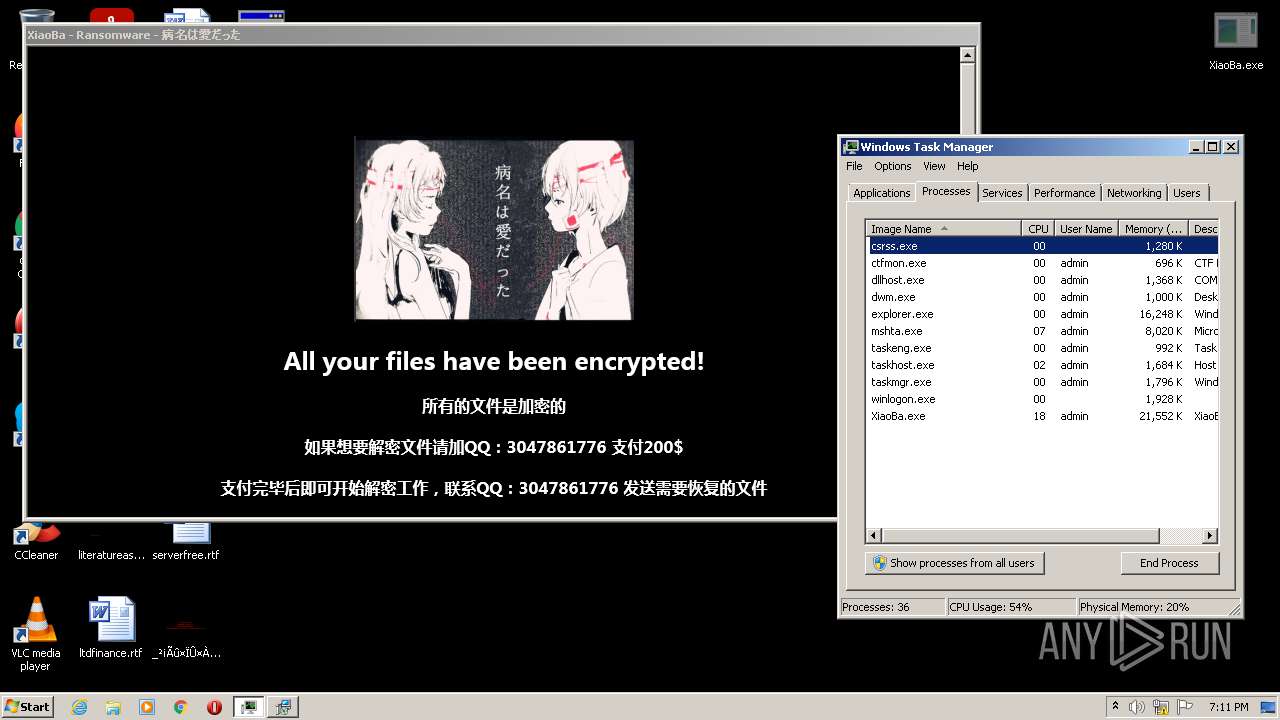
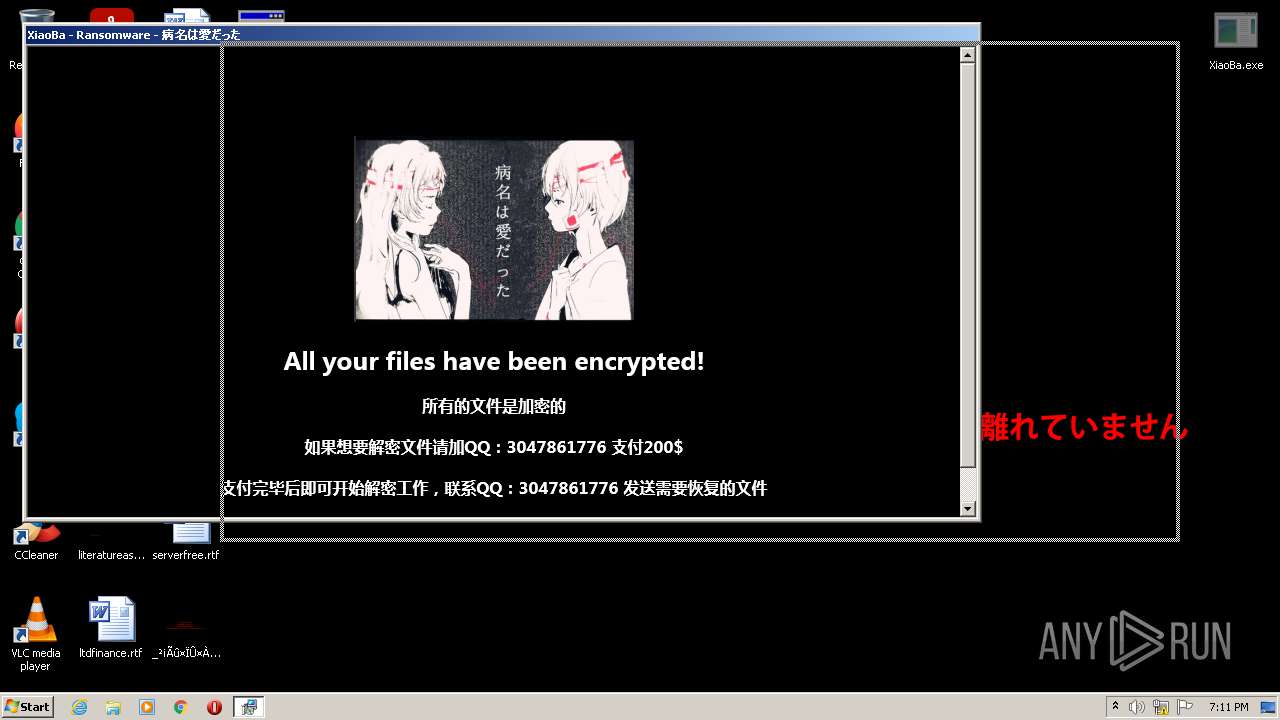
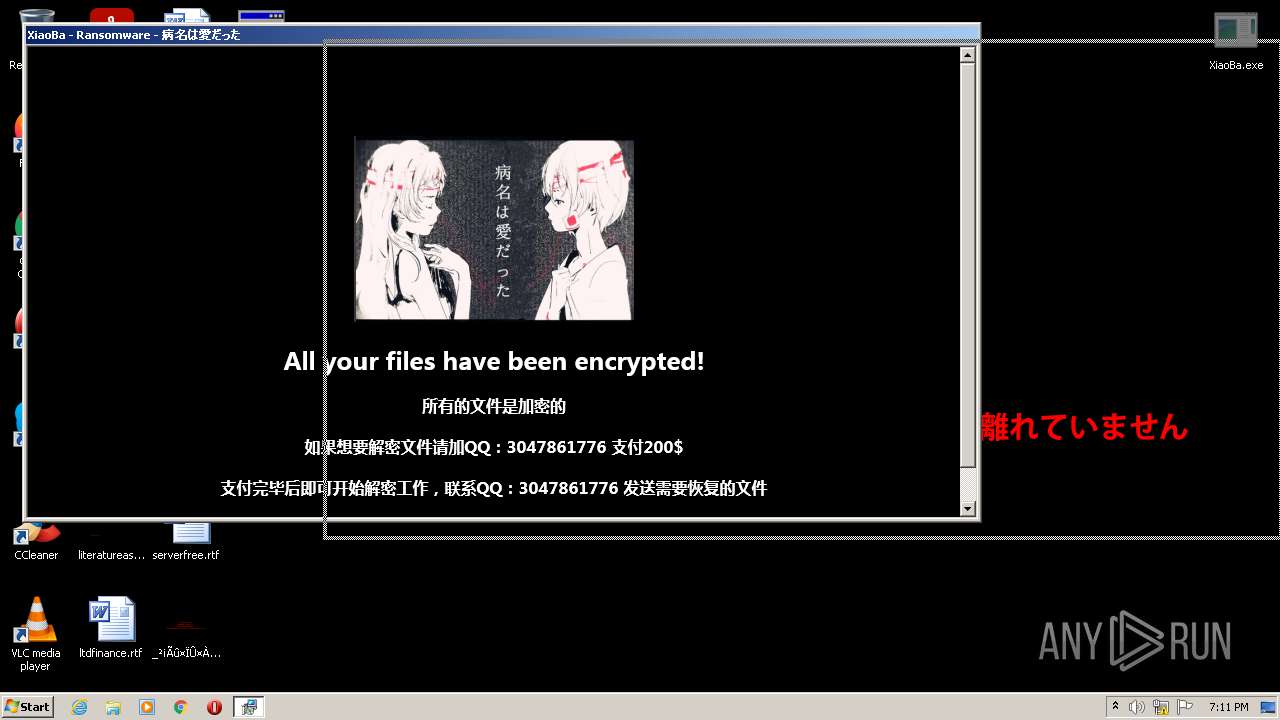
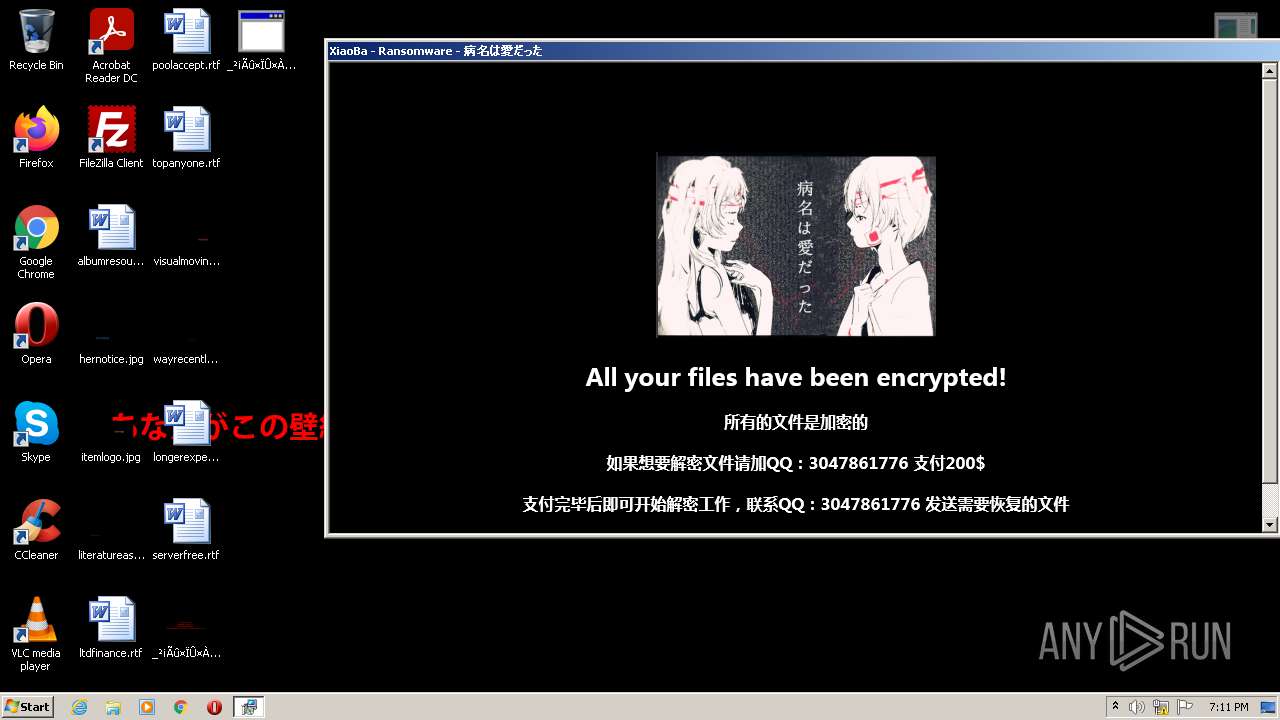
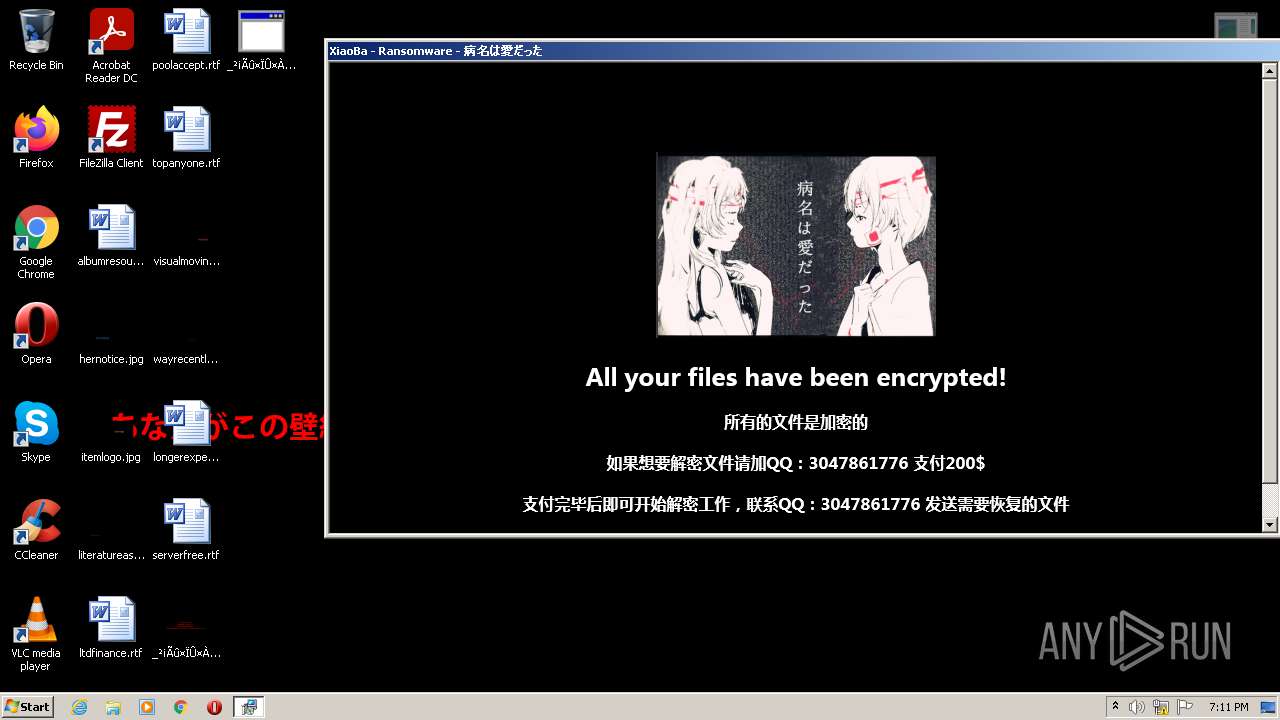
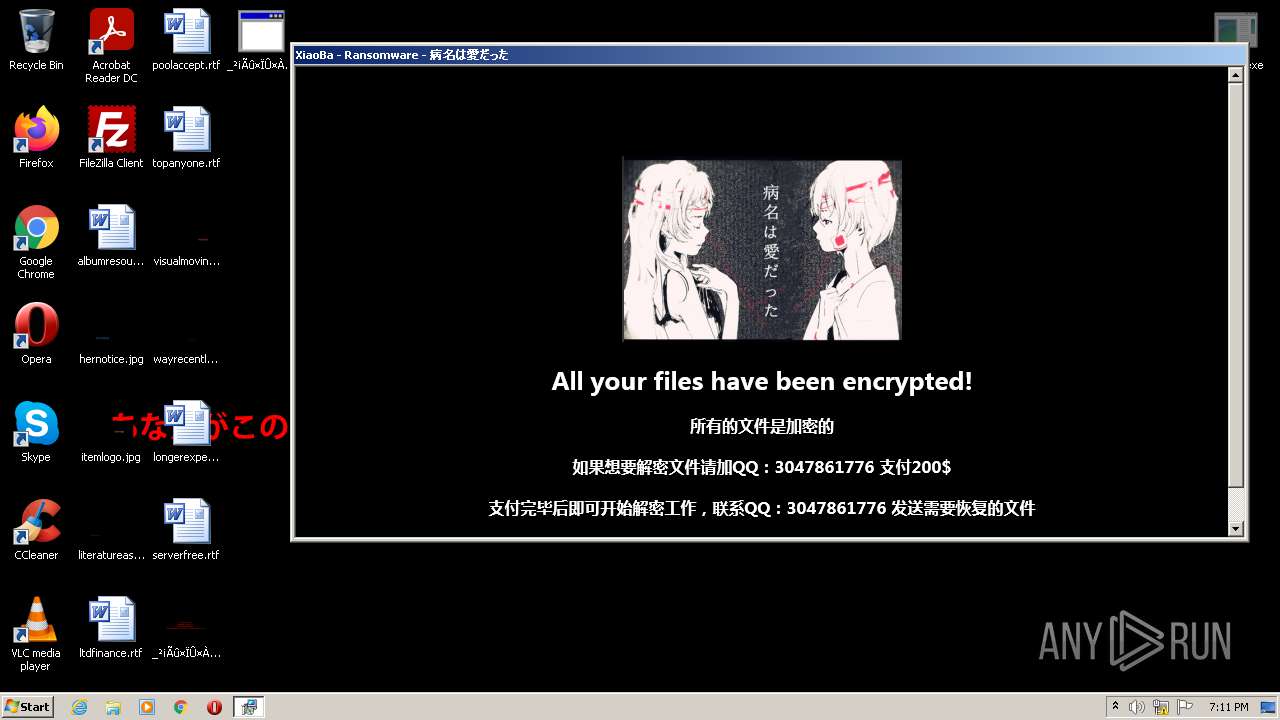
| Verdict: | Malicious activity |
| Analysis date: | November 19, 2021, 19:08:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D3F87E222B8C031978993167CED8C28E |
| SHA1: | 1BFA55107F54699E6417A686A43518974F6E6272 |
| SHA256: | B2759F034CA9BAA743A9BCAB422319C795CADE5451A6446C2AD28FCC743BCBF5 |
| SSDEEP: | 98304:PhU+/J8DrwqX+MuvGMjkBXJzT/RARtsZGx7Tm:pF/J8/TfUyB1j+8um |
MALICIOUS
Application was dropped or rewritten from another process
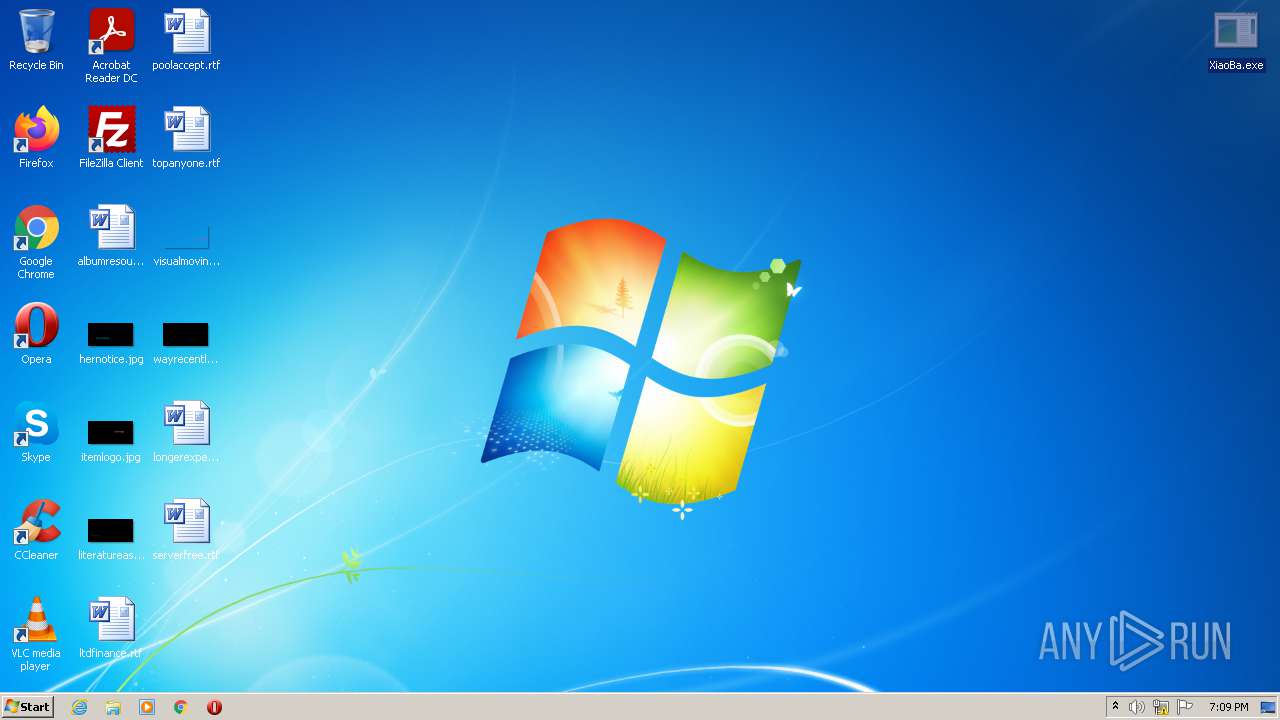
- XiaoBa.exe (PID: 3800)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 3280)
- XiaoBa.exe (PID: 3800)
- mshta.exe (PID: 692)
Checks supported languages
- WinRAR.exe (PID: 3280)
- mshta.exe (PID: 692)
- XiaoBa.exe (PID: 3800)
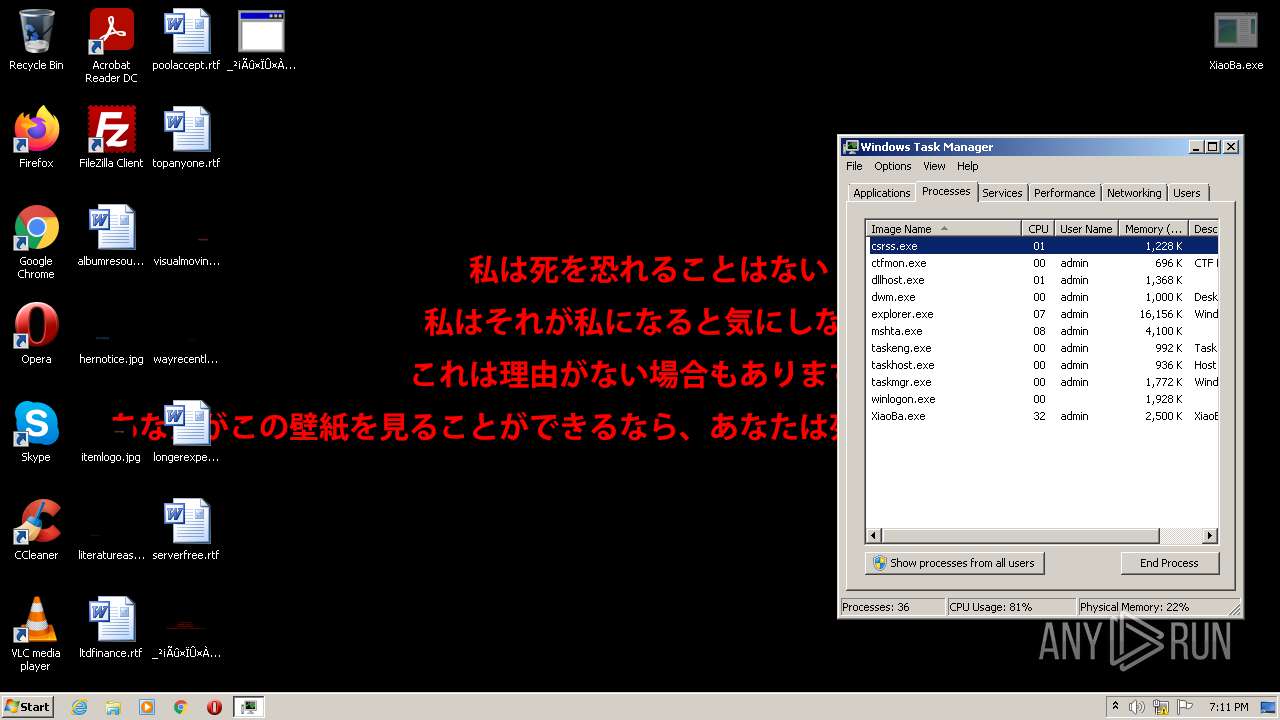
Starts MSHTA.EXE for opening HTA or HTMLS files
- XiaoBa.exe (PID: 3800)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3280)
Reads Microsoft Outlook installation path
- mshta.exe (PID: 692)
Creates files in the Windows directory
- XiaoBa.exe (PID: 3800)
INFO
Checks supported languages
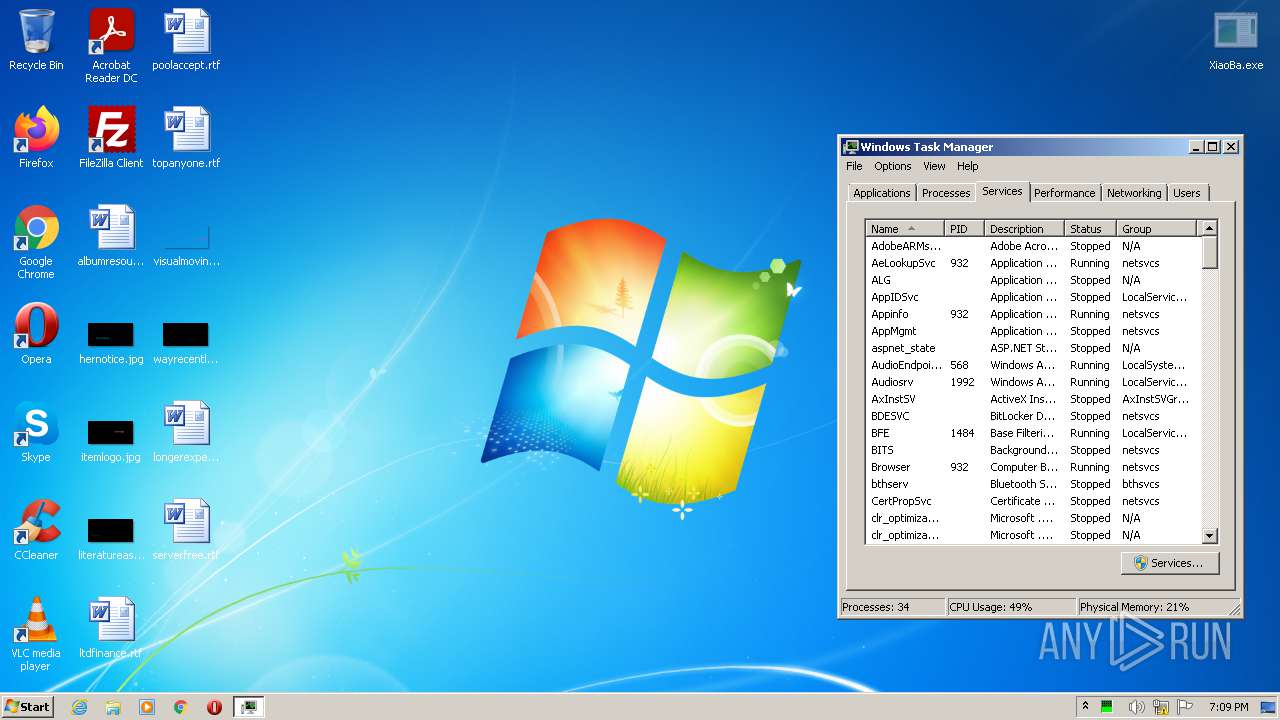
- taskmgr.exe (PID: 3636)
Reads the computer name
- taskmgr.exe (PID: 3636)
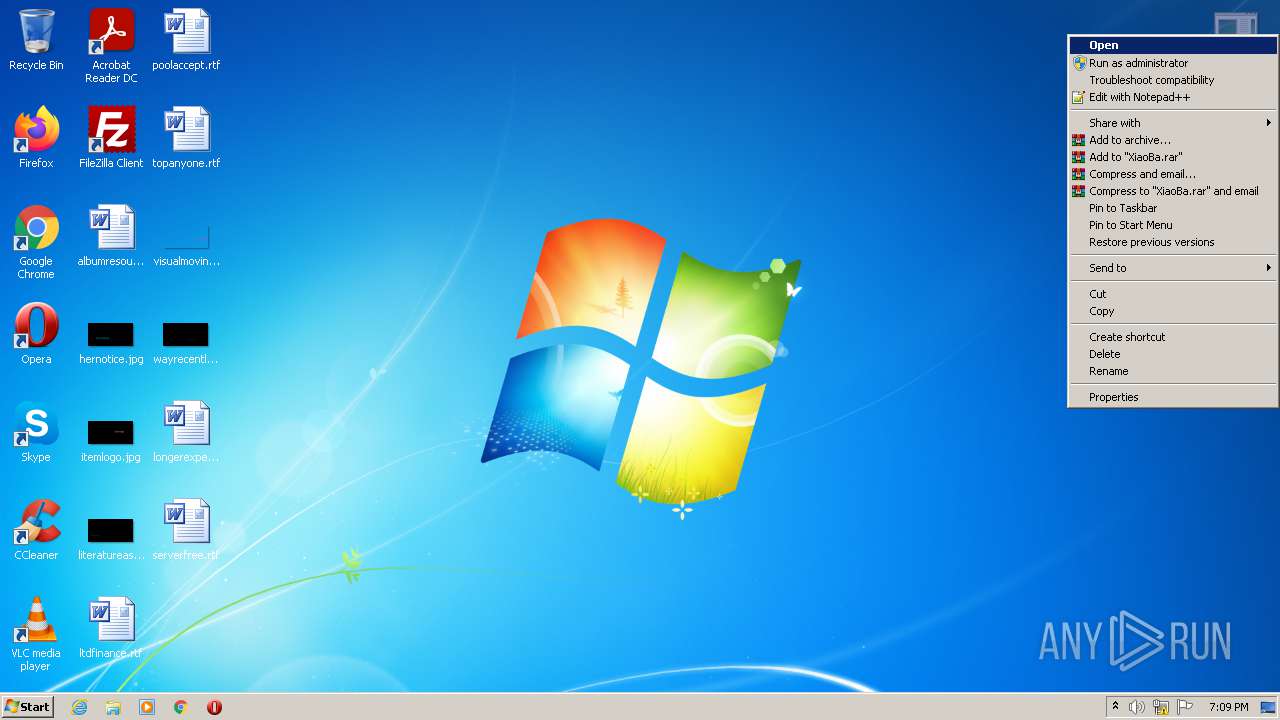
Manual execution by user
- XiaoBa.exe (PID: 3800)
- taskmgr.exe (PID: 3636)
Reads internet explorer settings
- mshta.exe (PID: 692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:12:04 22:22:20 |
| ZipCRC: | 0xfd341637 |
| ZipCompressedSize: | 3934886 |
| ZipUncompressedSize: | 4205056 |
| ZipFileName: | XiaoBa.exe |
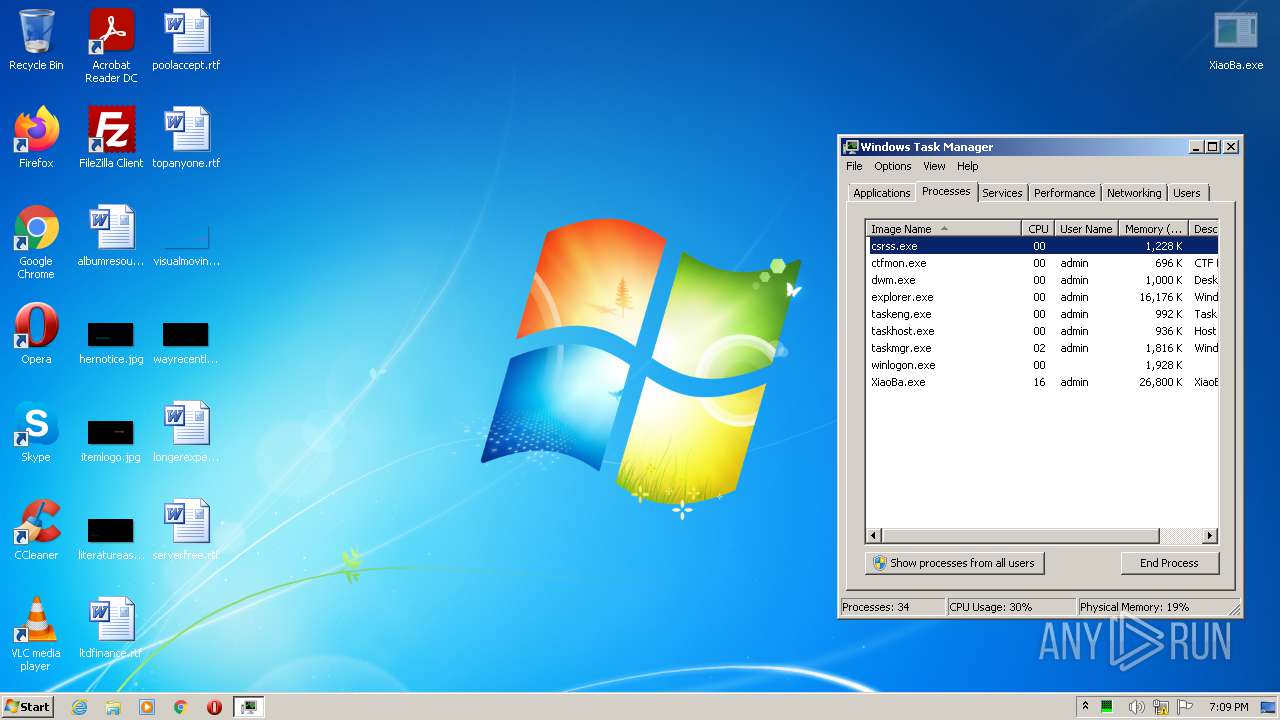
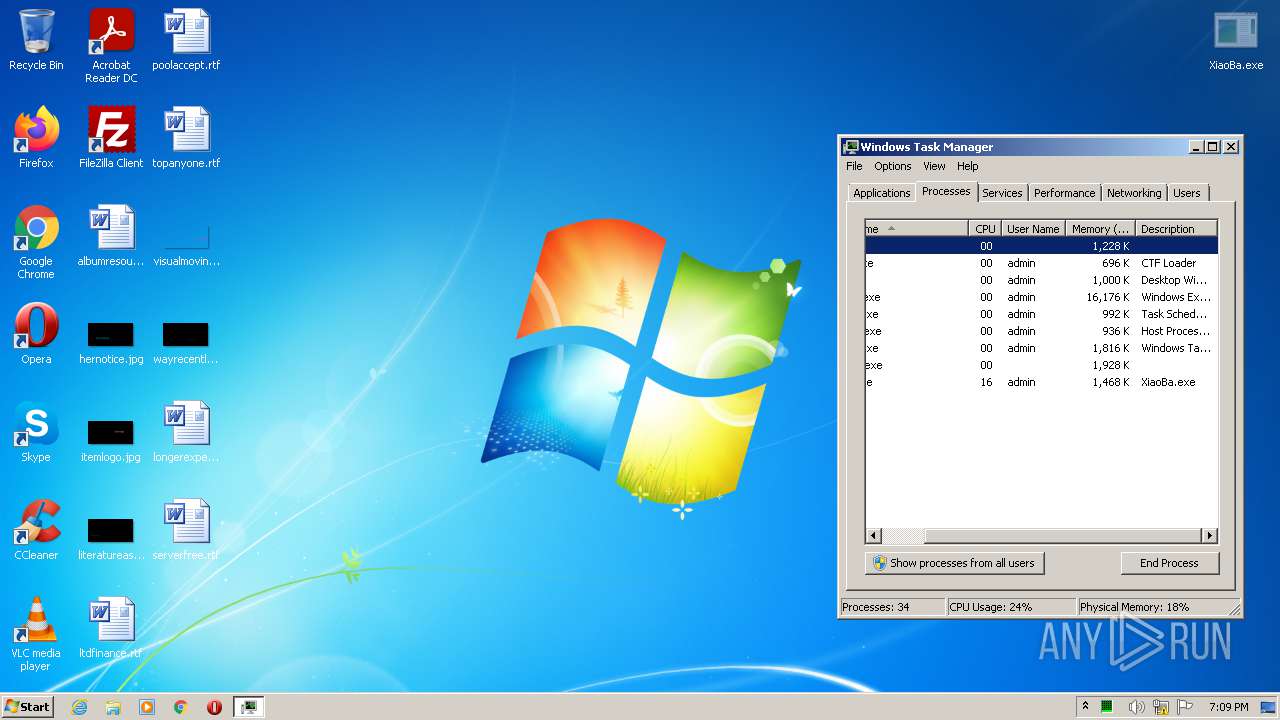
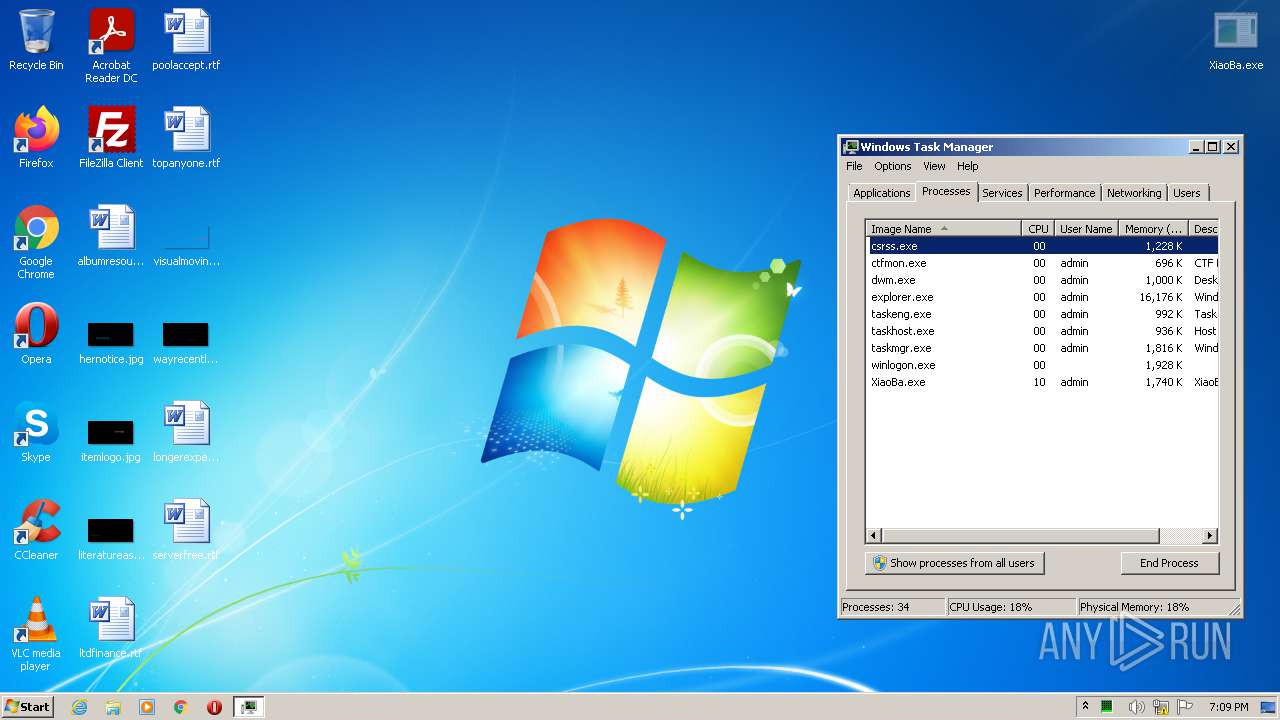
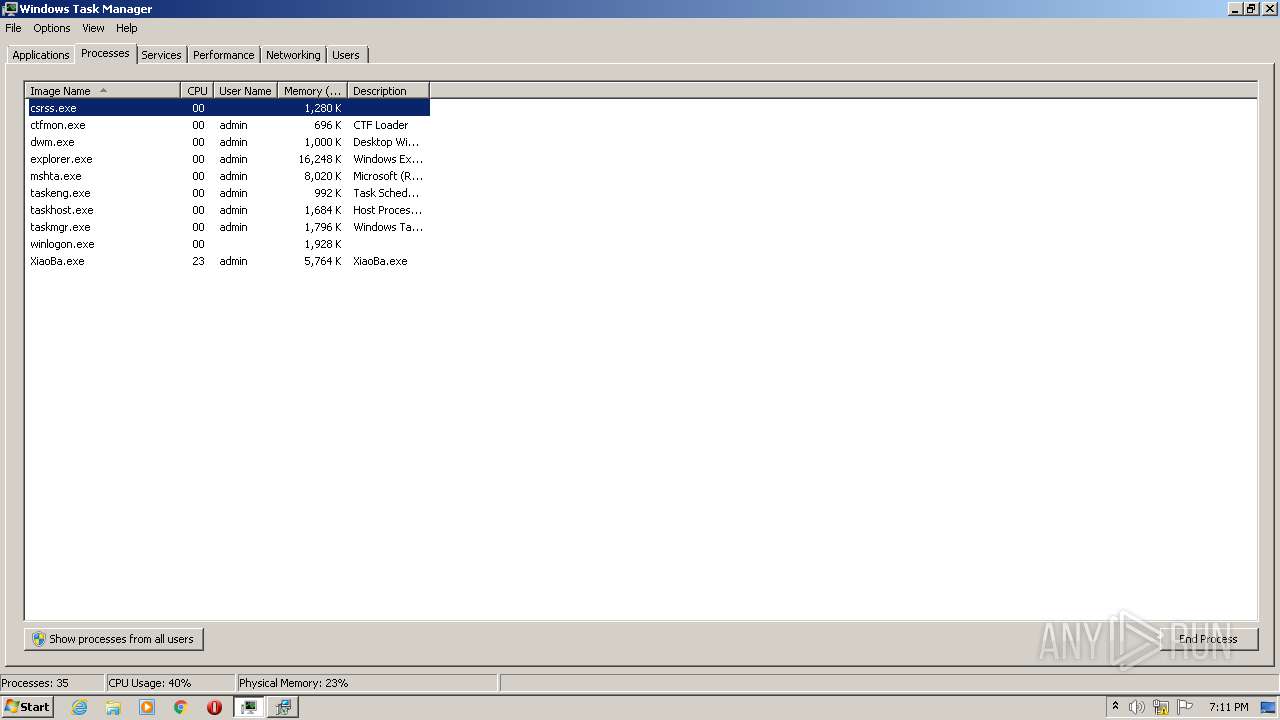
Total processes
43
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 692 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\Desktop\_�����ϐۤ��ä�_.hta" | C:\Windows\System32\mshta.exe | — | XiaoBa.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
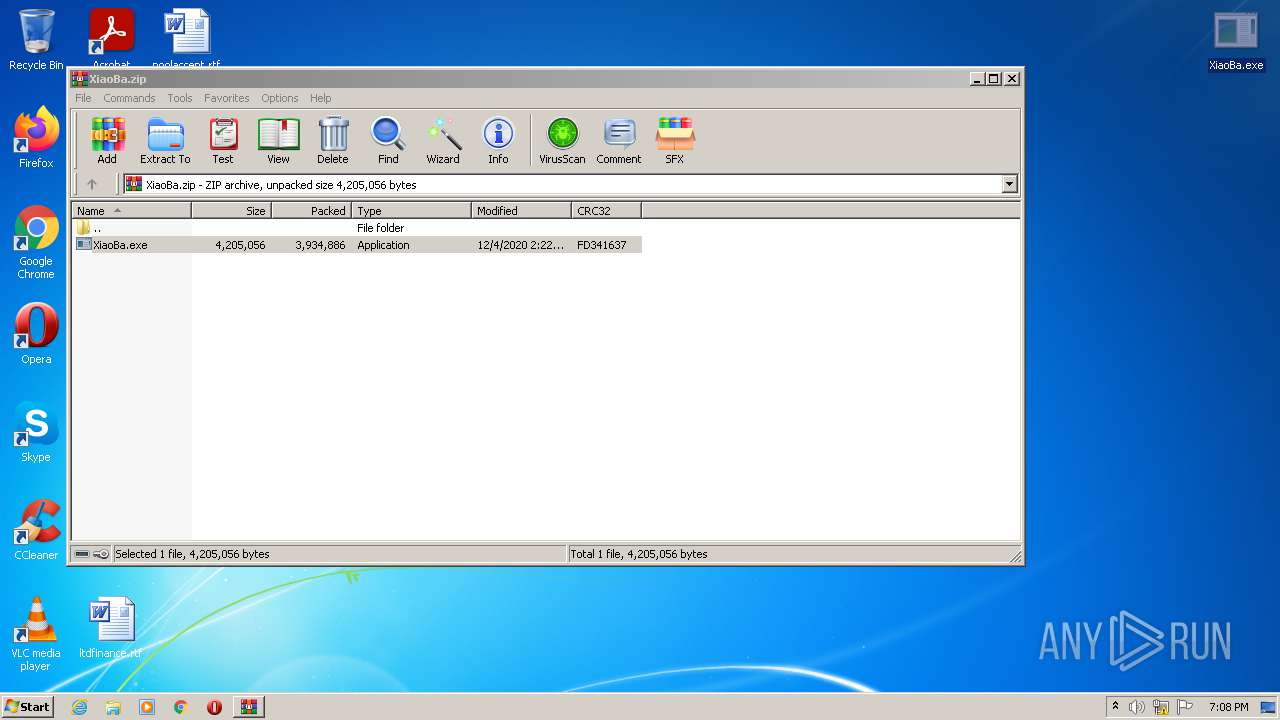
| 3280 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\XiaoBa.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3636 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3800 | "C:\Users\admin\Desktop\XiaoBa.exe" | C:\Users\admin\Desktop\XiaoBa.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 897
Read events
1 832
Write events
65
Delete events
0
Modification events
| (PID) Process: | (3280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3280) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\XiaoBa.zip | |||
| (PID) Process: | (3280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
1
Suspicious files
558
Text files
7
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3800 | XiaoBa.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccLR.cab | — | |
MD5:— | SHA256:— | |||
| 3800 | XiaoBa.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccLR.cab.�����ϐۤ��ä�[QQ-3047861776].XiaoBa | — | |
MD5:— | SHA256:— | |||
| 3800 | XiaoBa.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccLR.cab | — | |
MD5:— | SHA256:— | |||
| 3800 | XiaoBa.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccLR.cab.�����ϐۤ��ä�[QQ-3047861776].XiaoBa | — | |
MD5:— | SHA256:— | |||
| 3800 | XiaoBa.exe | C:\autoexec.bat.�����ϐۤ��ä�[QQ-3047861776].XiaoBa | binary | |
MD5:5CBA86C73B332412F9AF8AB25C472D74 | SHA256:3C98E53217F230DCF3A23FA3465713AA098D0EC7008EBAB384F9EED17CA695C7 | |||
| 3800 | XiaoBa.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\desktop.ini.�����ϐۤ��ä�[QQ-3047861776].XiaoBa | ini | |
MD5:A526B9E7C716B3489D8CC062FBCE4005 | SHA256:E1B9CE9B57957B1A0607A72A057D6B7A9B34EA60F3F8AA8F38A3AF979BD23066 | |||
| 3800 | XiaoBa.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.msi.�����ϐۤ��ä�[QQ-3047861776].XiaoBa | binary | |
MD5:51D3141A0B494A396EABC17DC571A956 | SHA256:E3BA3AD56A1EBC8780112CB06759CECC712708BC262CB7FF60D1AE59F6BD1B3A | |||
| 3800 | XiaoBa.exe | C:\autoexec.bat | binary | |
MD5:5CBA86C73B332412F9AF8AB25C472D74 | SHA256:3C98E53217F230DCF3A23FA3465713AA098D0EC7008EBAB384F9EED17CA695C7 | |||
| 3800 | XiaoBa.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.msi | binary | |
MD5:51D3141A0B494A396EABC17DC571A956 | SHA256:E3BA3AD56A1EBC8780112CB06759CECC712708BC262CB7FF60D1AE59F6BD1B3A | |||
| 3800 | XiaoBa.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-500\desktop.ini.�����ϐۤ��ä�[QQ-3047861776].XiaoBa | ini | |
MD5:A526B9E7C716B3489D8CC062FBCE4005 | SHA256:E1B9CE9B57957B1A0607A72A057D6B7A9B34EA60F3F8AA8F38A3AF979BD23066 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report