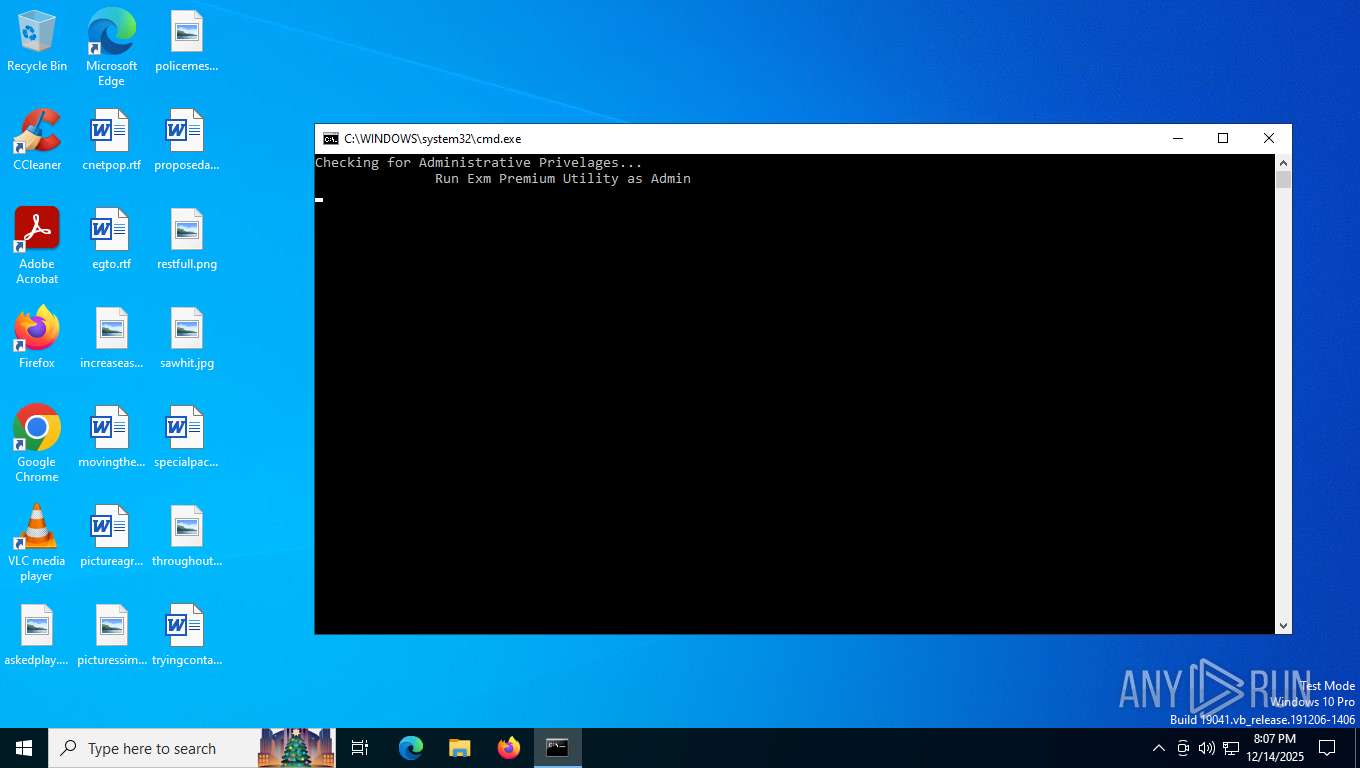
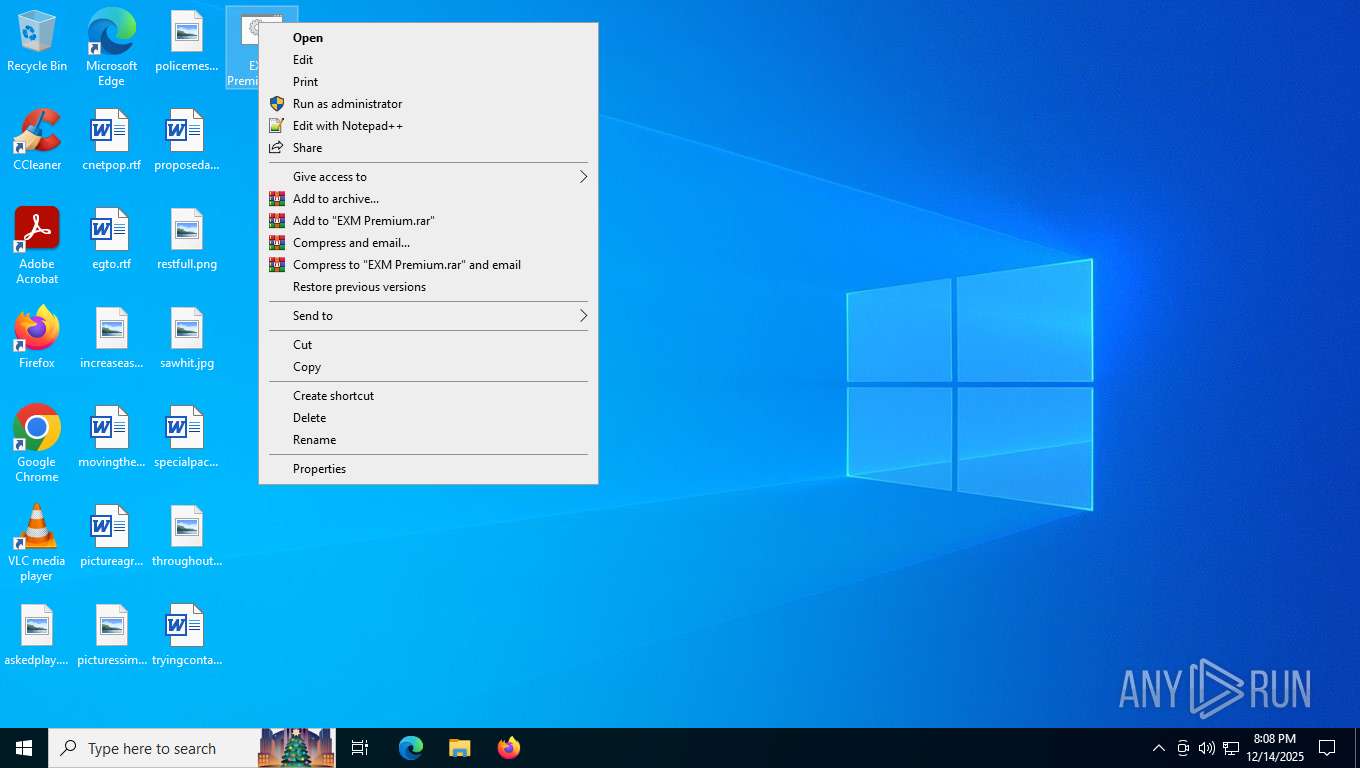
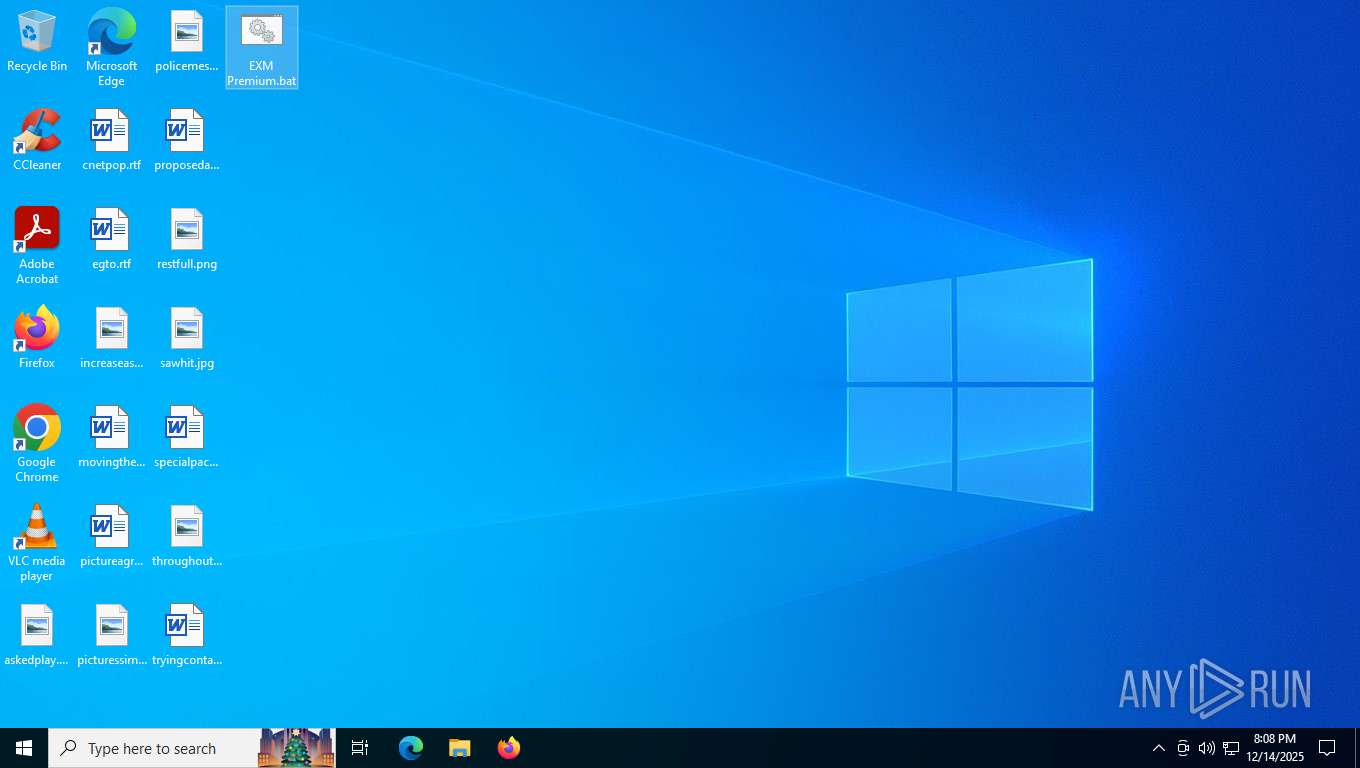
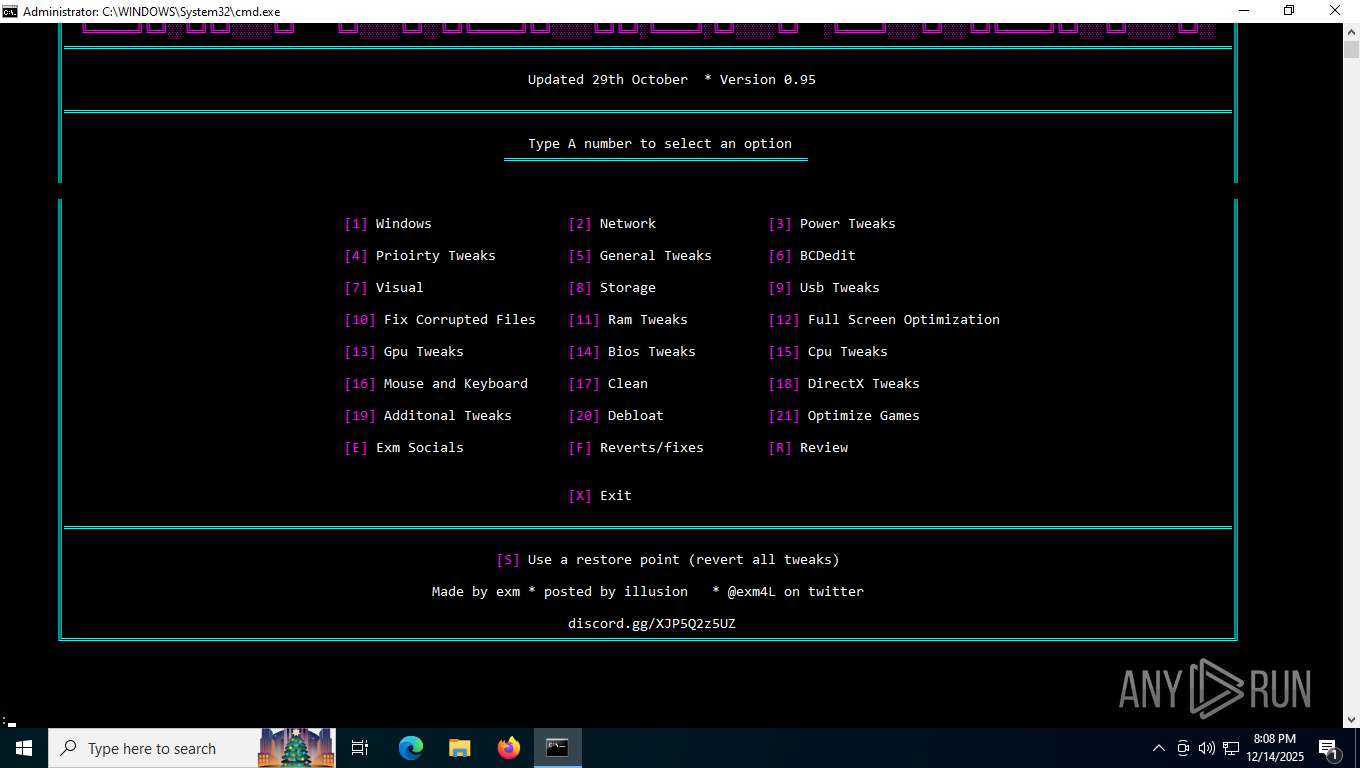
| File name: | EXM Premium.bat |
| Full analysis: | https://app.any.run/tasks/10e44fc9-13ee-47ef-9d31-4818b29568c7 |
| Verdict: | Malicious activity |
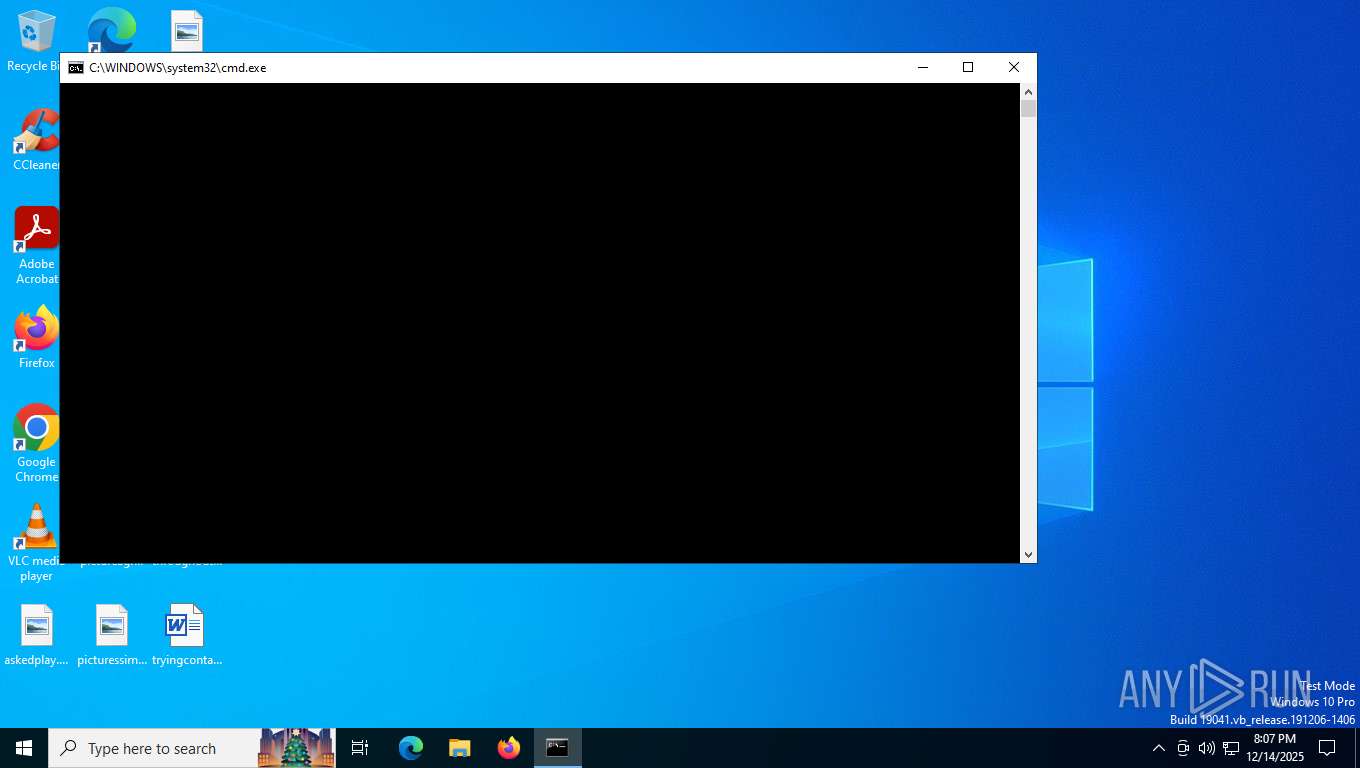
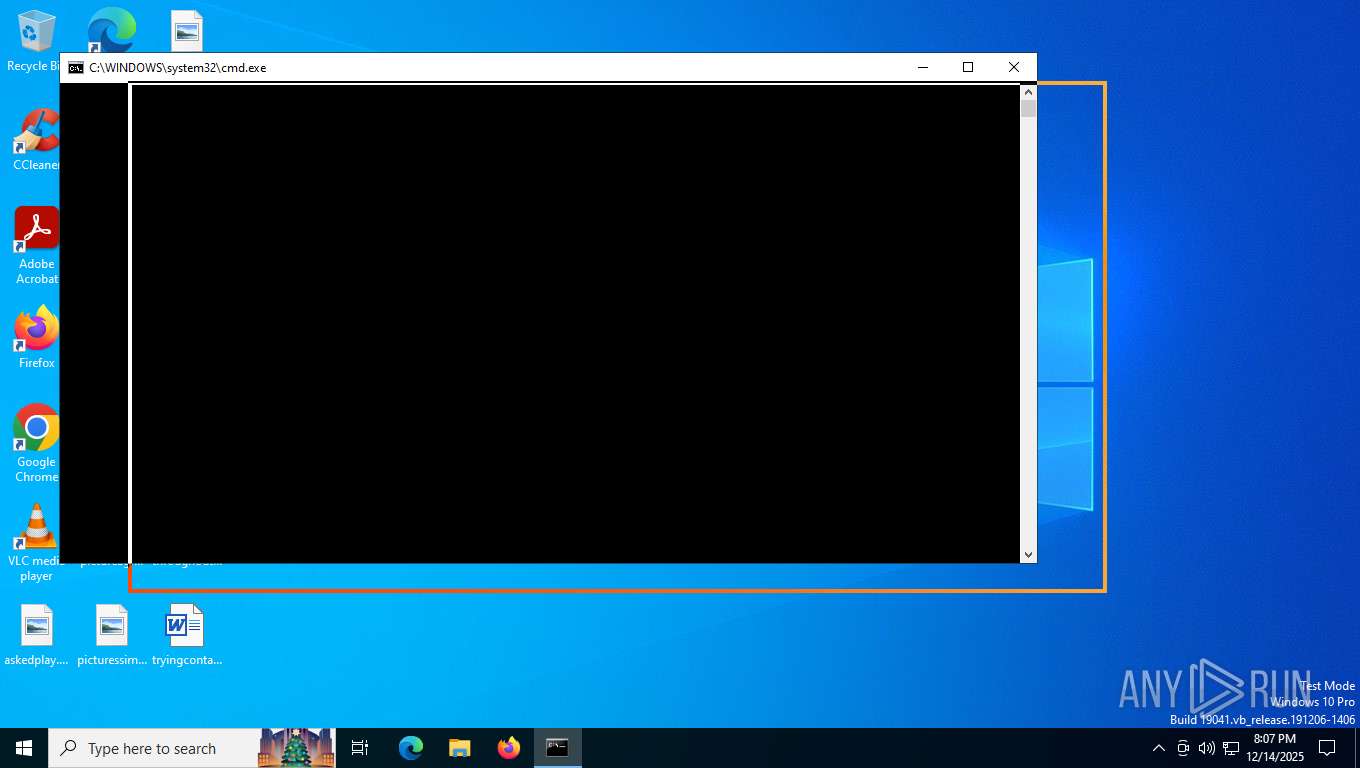
| Analysis date: | December 14, 2025, 20:07:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with CRLF line terminators, with escape sequences |
| MD5: | C84CC50F06ADA53B3D5CFD19318A738F |
| SHA1: | C1A0CD35FD7E57CBA3B7E7A4F0CAB32E388D367D |
| SHA256: | B26A009EBE2967899016FD6A75314433757373ECCF4F029800677962A488F5FB |
| SSDEEP: | 3072:WxVGzQbmbkAqA2xH7VkKEn14IZVvisLur+K3:WxVGiVNEn14IZVvisL43 |
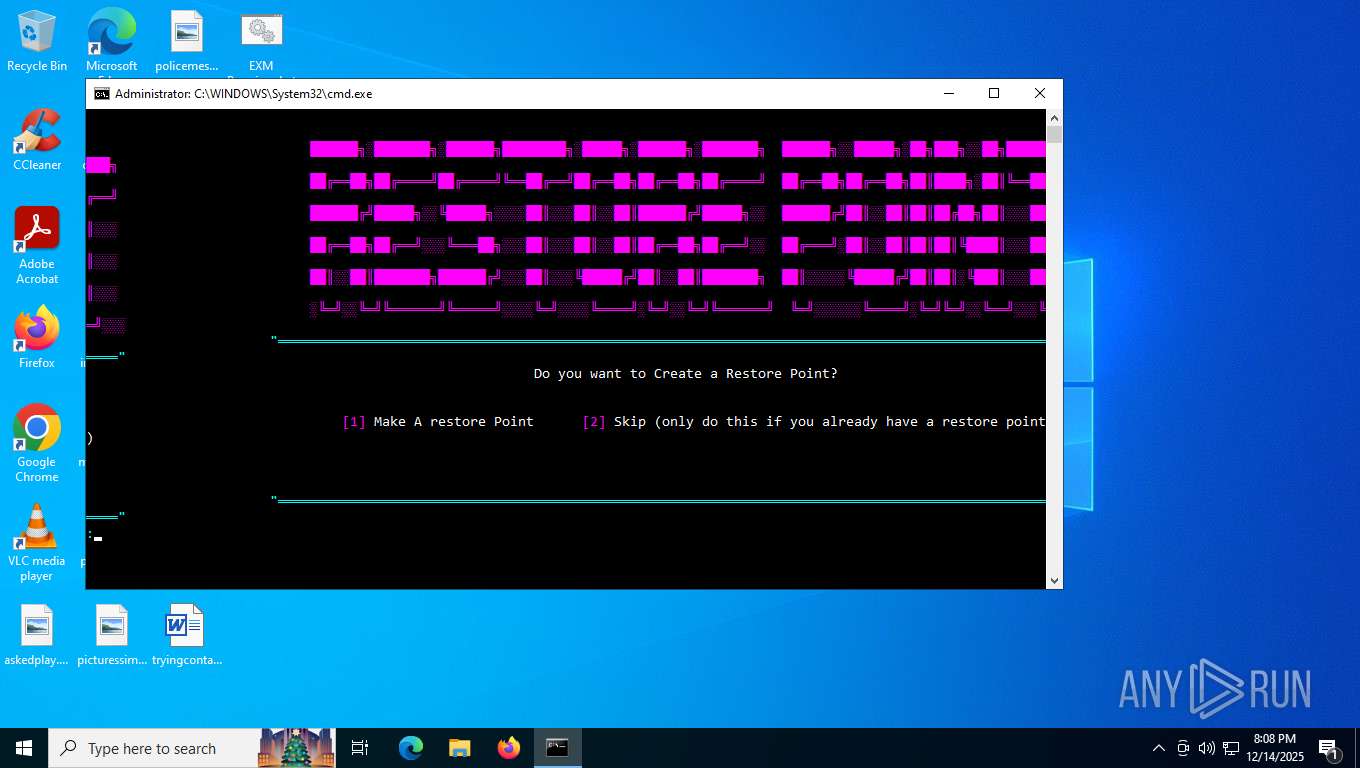
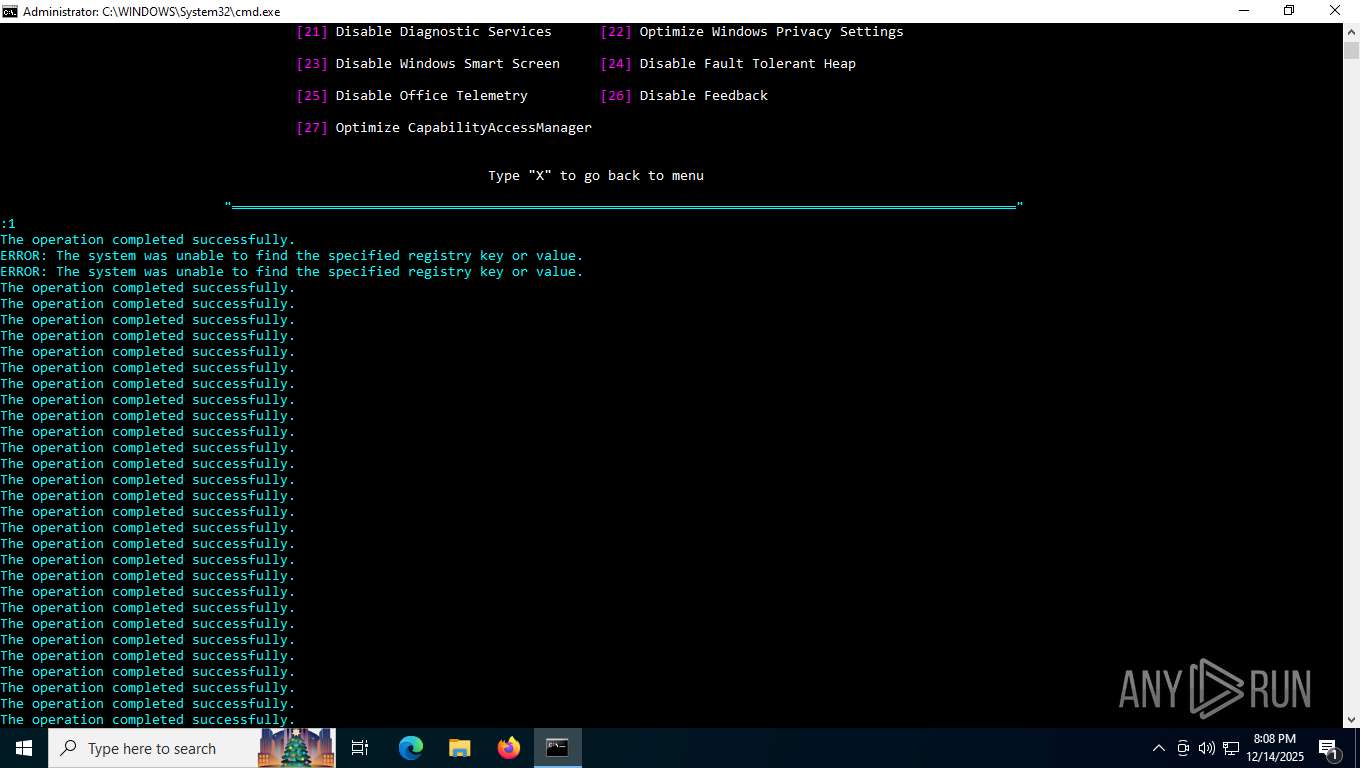
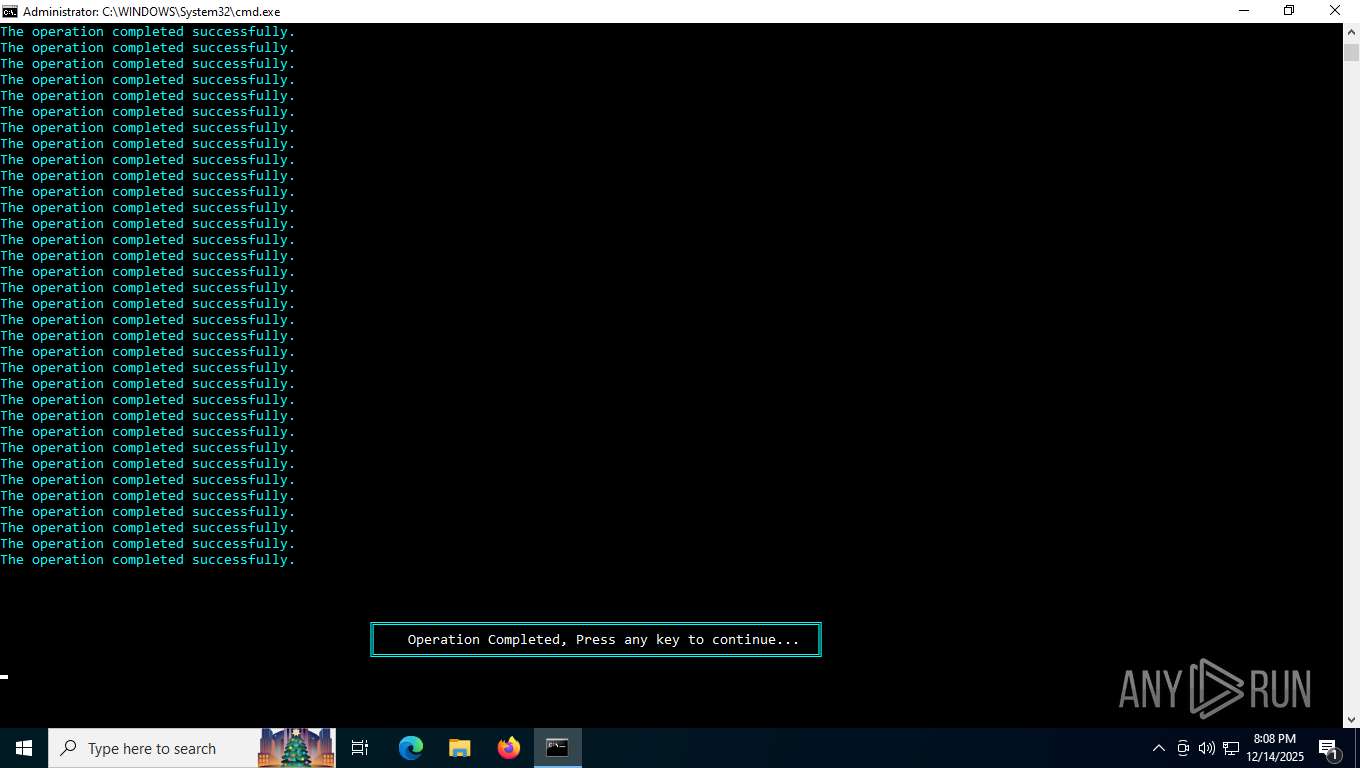
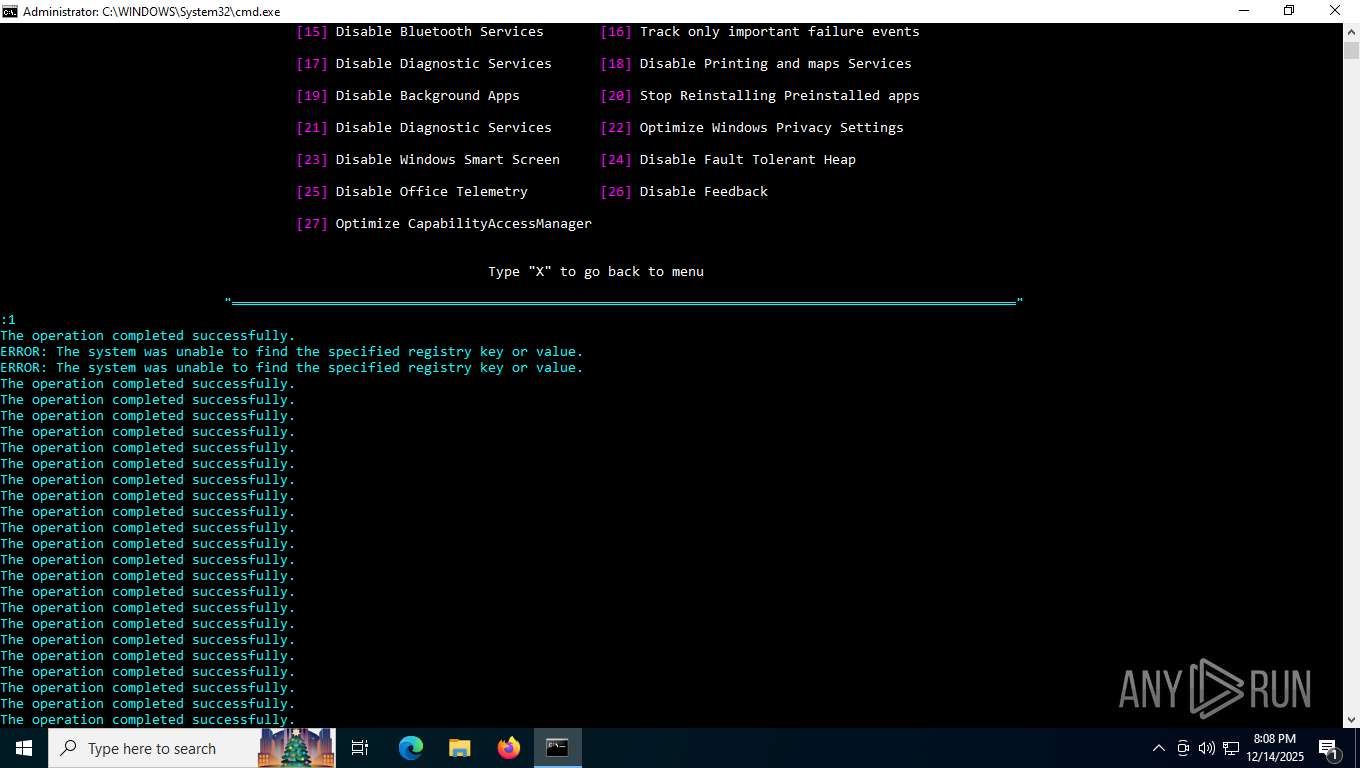
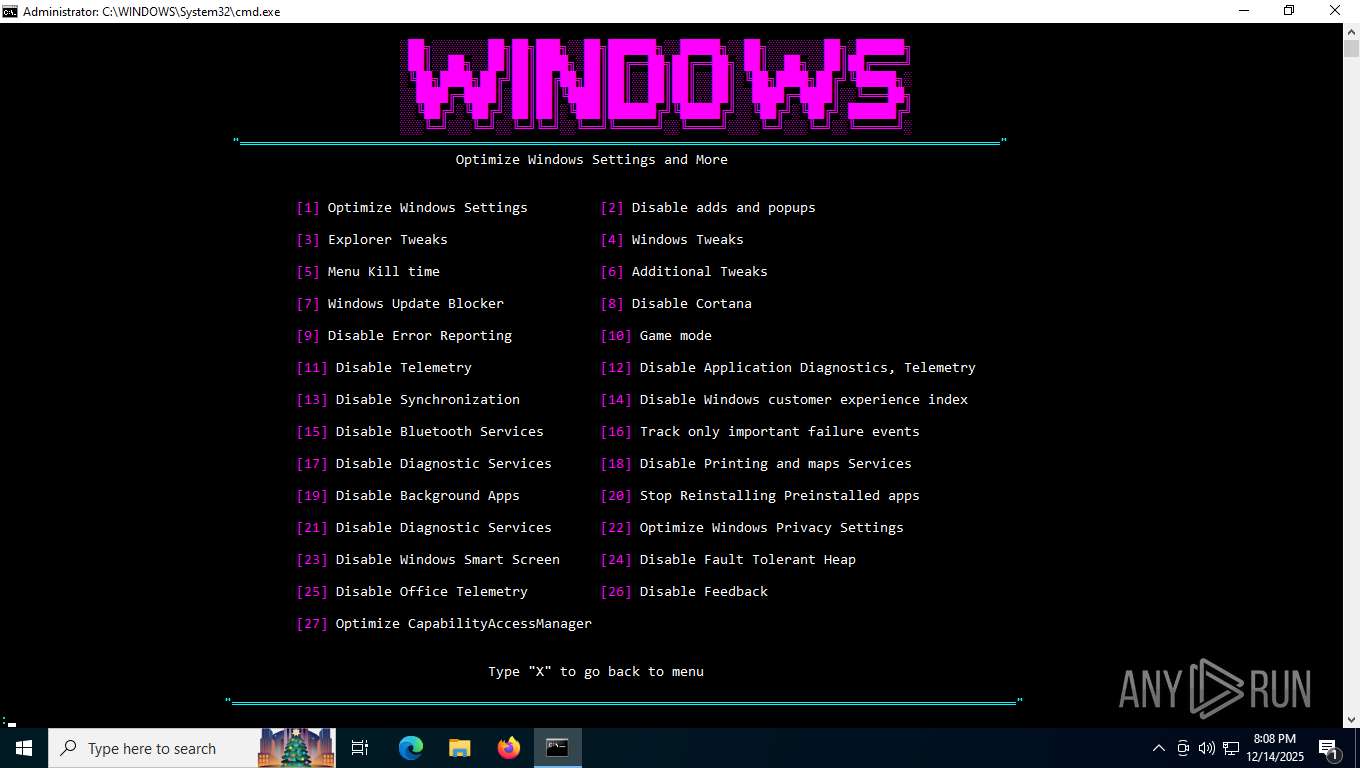
MALICIOUS
Changes powershell execution policy (Unrestricted)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7208)
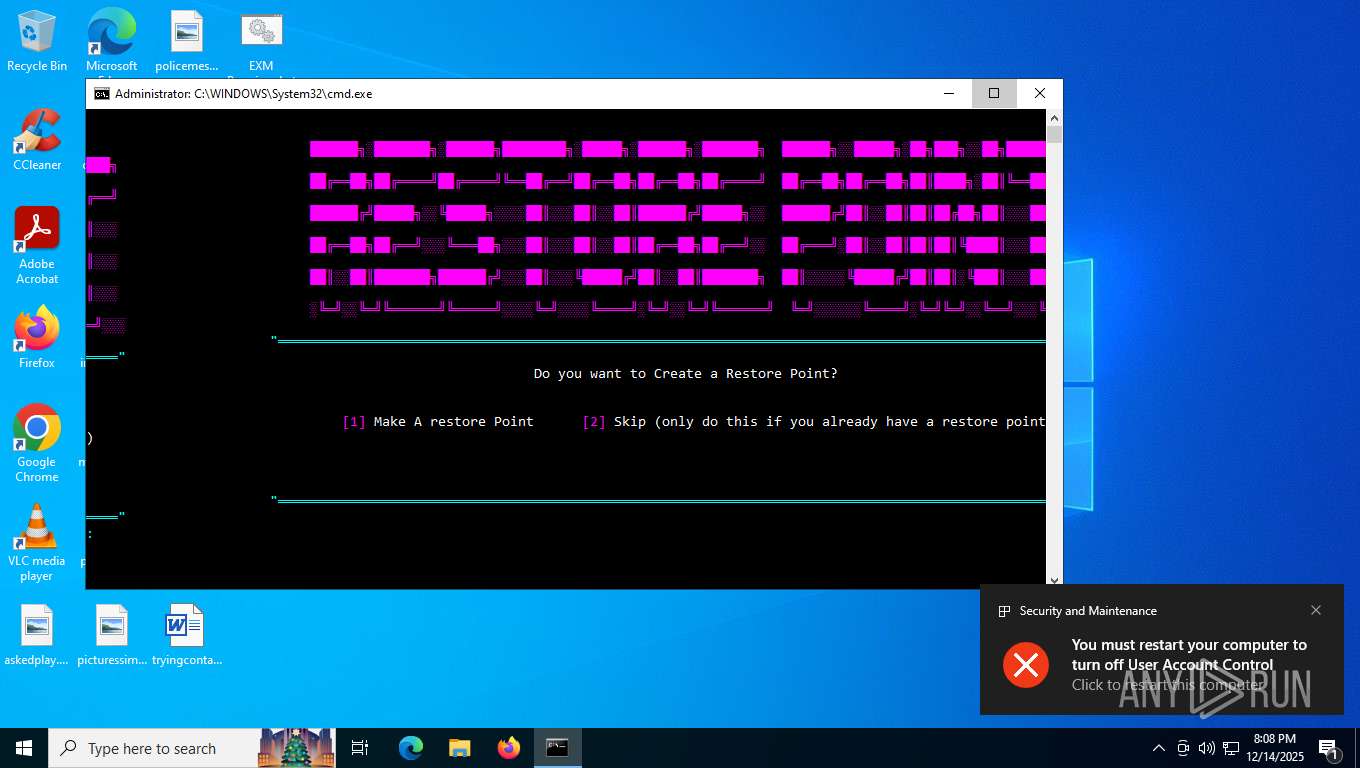
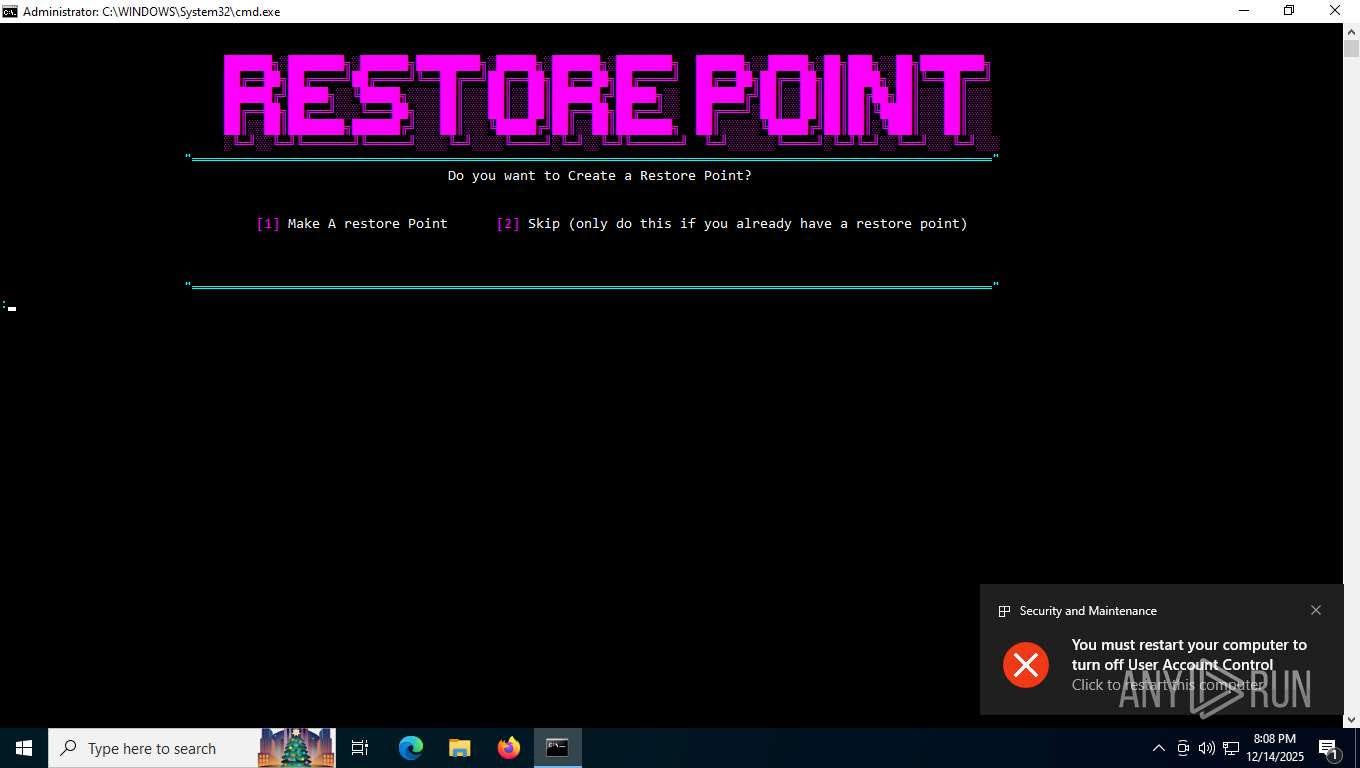
UAC/LUA settings modification
- reg.exe (PID: 7636)
Changes the autorun value in the registry
- reg.exe (PID: 6896)
Changes the Windows auto-update feature
- reg.exe (PID: 7892)
SUSPICIOUS
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7208)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7208)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7208)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7208)
The process hide an interactive prompt from the user
- cmd.exe (PID: 7460)
Uses WMIC.EXE to obtain user accounts information
- cmd.exe (PID: 6484)
- cmd.exe (PID: 7872)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6484)
- cmd.exe (PID: 7872)
Application launched itself
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7208)
Starts application with an unusual extension
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7208)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 6244)
Executable content was dropped or overwritten
- powershell.exe (PID: 6244)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7208)
INFO
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7596)
- powershell.exe (PID: 7896)
Changes the display of characters in the console
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7208)
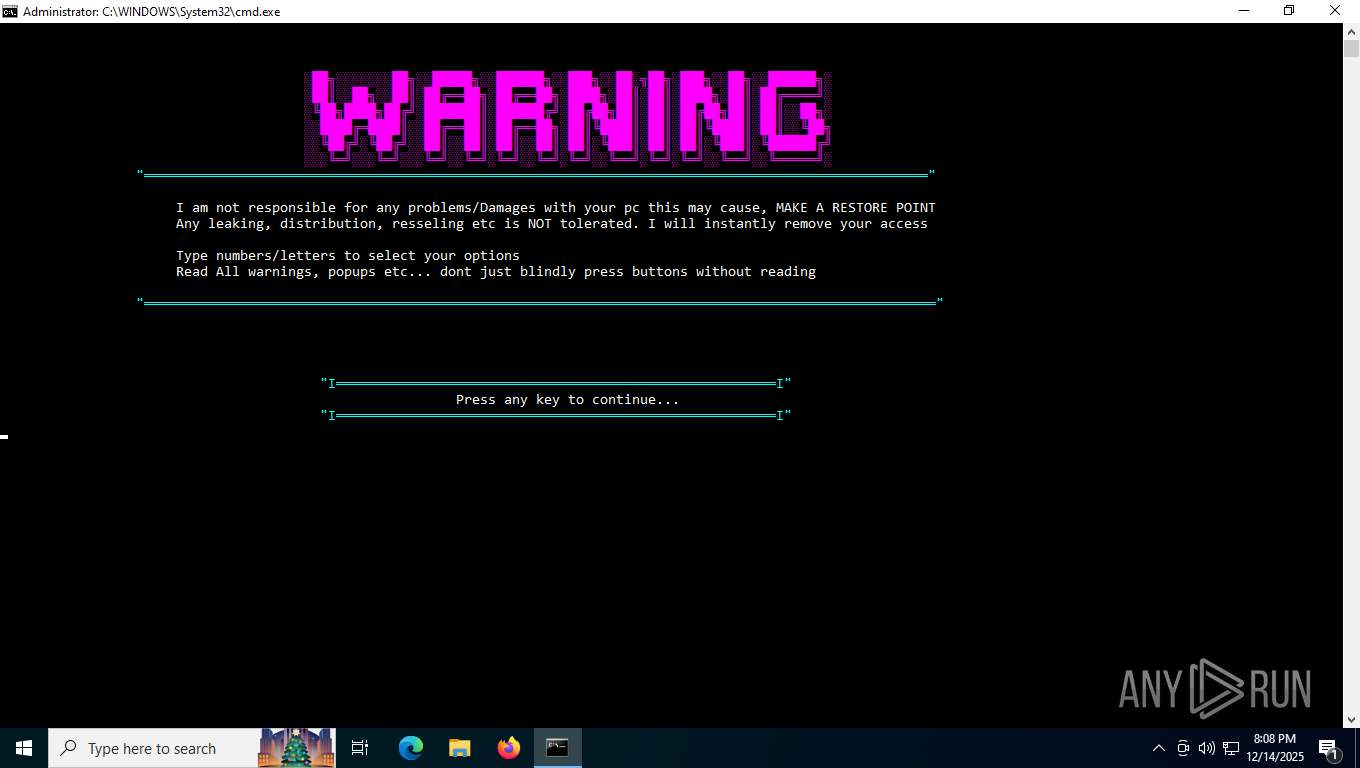
Manual execution by a user
- cmd.exe (PID: 7208)
- nvidiaProfileInspector.exe (PID: 4284)
- nvidiaProfileInspector.exe (PID: 4140)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7264)
- WMIC.exe (PID: 7884)
Checks supported languages
- chcp.com (PID: 4992)
- chcp.com (PID: 7496)
- curl.exe (PID: 3568)
- chcp.com (PID: 8016)
- nvidiaProfileInspector.exe (PID: 4284)
- chcp.com (PID: 2940)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6244)
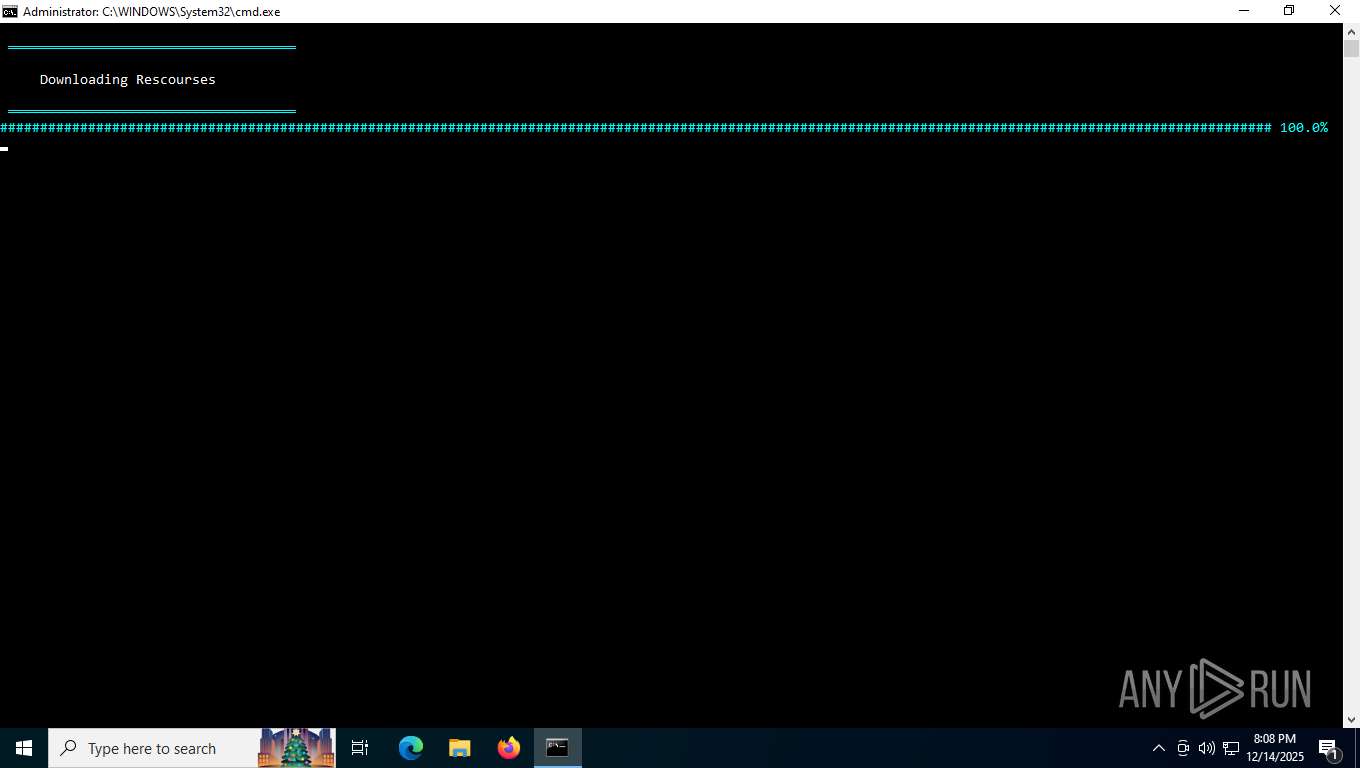
Execution of CURL command
- cmd.exe (PID: 7208)
Create files in a temporary directory
- curl.exe (PID: 3568)
Reads the computer name
- curl.exe (PID: 3568)
- nvidiaProfileInspector.exe (PID: 4284)
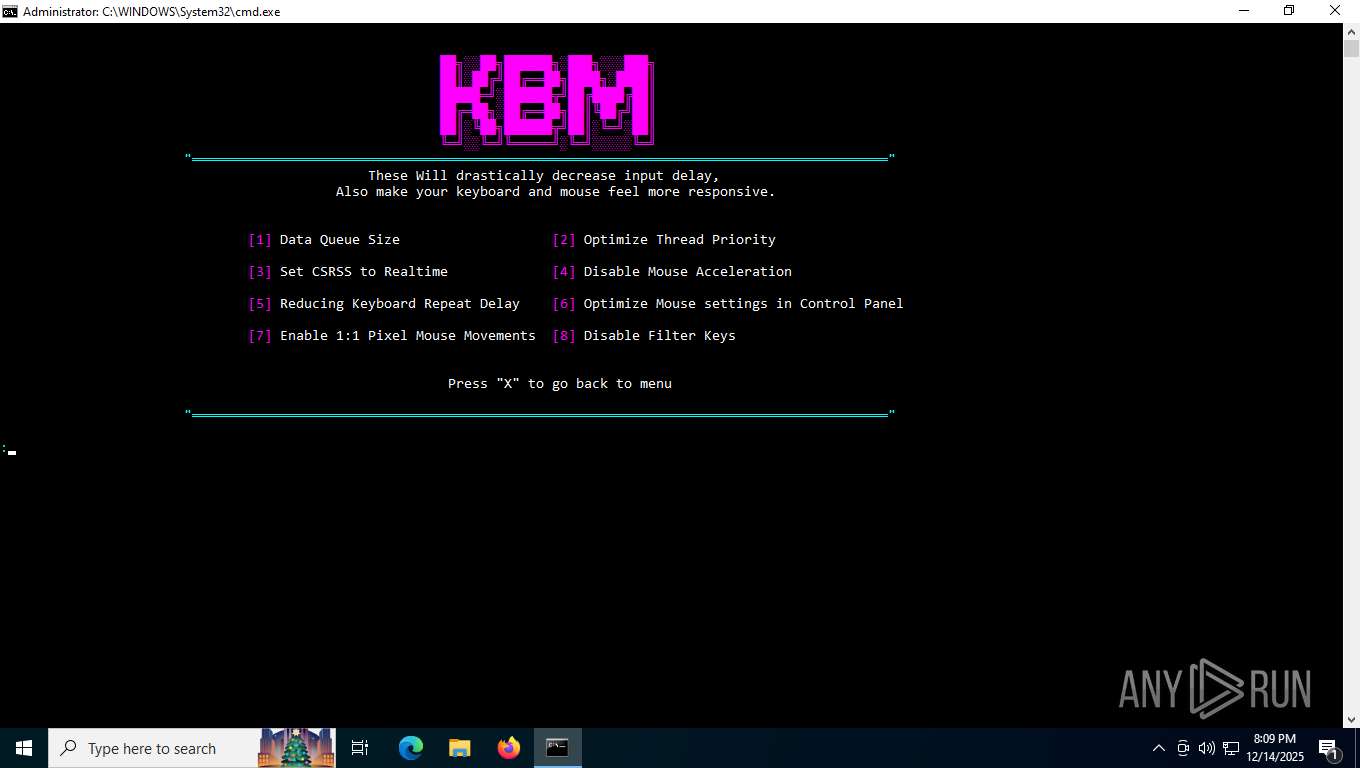
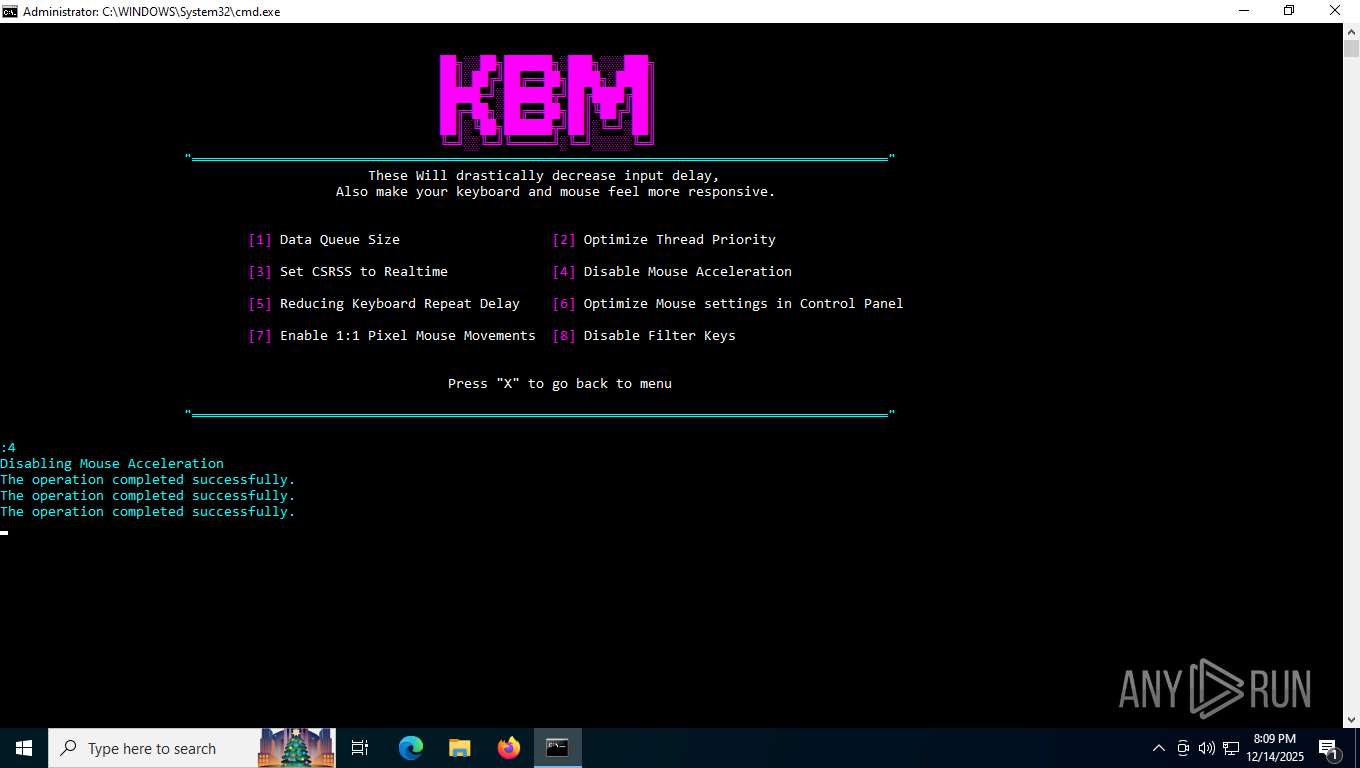
Reads mouse settings
- reg.exe (PID: 5172)
- reg.exe (PID: 6852)
- reg.exe (PID: 3136)
- reg.exe (PID: 7304)
- reg.exe (PID: 3180)
- reg.exe (PID: 4920)
- reg.exe (PID: 1204)
- reg.exe (PID: 4788)
- reg.exe (PID: 2308)
Checks proxy server information
- slui.exe (PID: 1388)
Launching a file from a Registry key
- reg.exe (PID: 6896)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6244)
Reads the machine GUID from the registry
- nvidiaProfileInspector.exe (PID: 4284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
246
Monitored processes
98
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 224 | Reg.exe add "HKLM\SOFTWARE\Policies\Microsoft\Windows\DataCollection" /v "AllowDeviceNameInTelemetry" /t REG_DWORD /d "0" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | timeout /t 1 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 932 | Reg.exe add "HKLM\SOFTWARE\Policies\Google\Chrome" /v "BackgroundModeEnabled" /t REG_DWORD /d "0" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | timeout /t 1 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
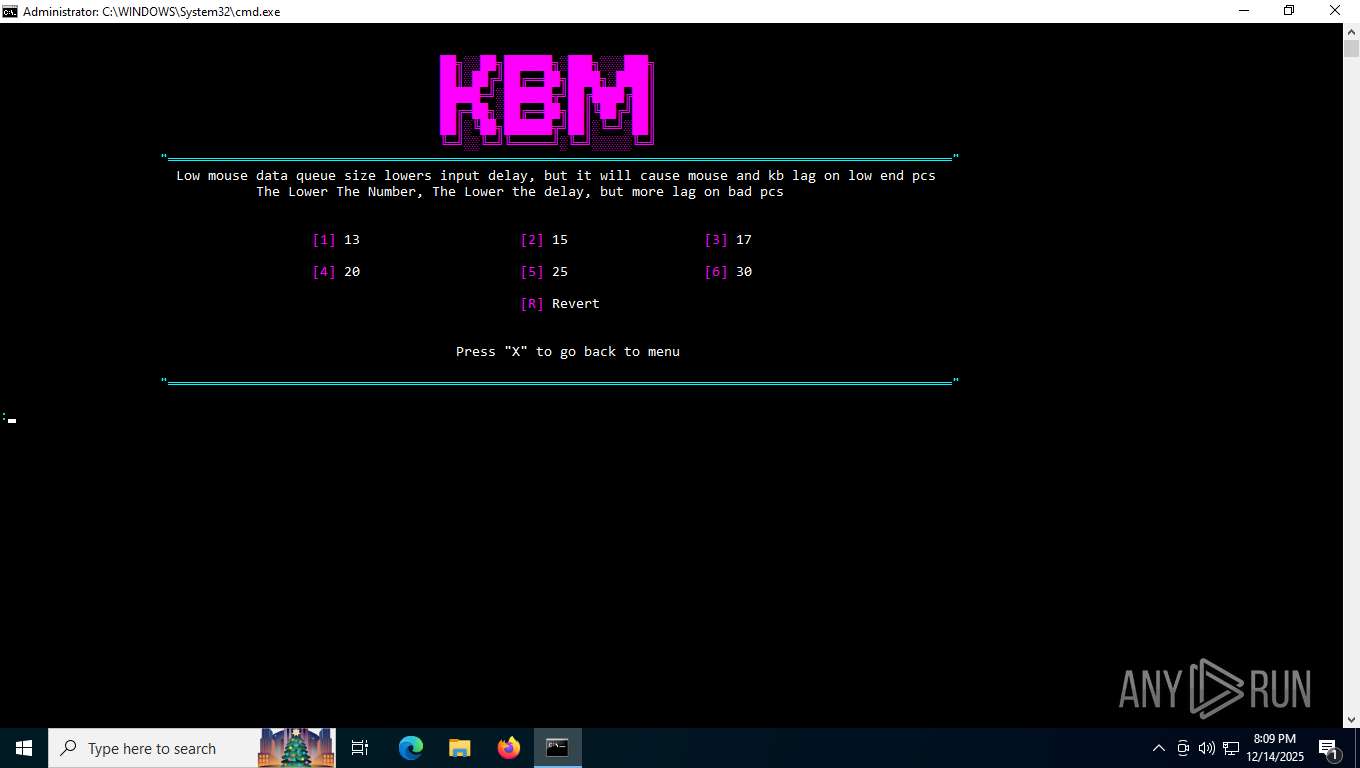
| 1204 | Reg.exe add "HKCU\Control Panel\Mouse" /v "MouseThreshold1" /t REG_SZ /d "0" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
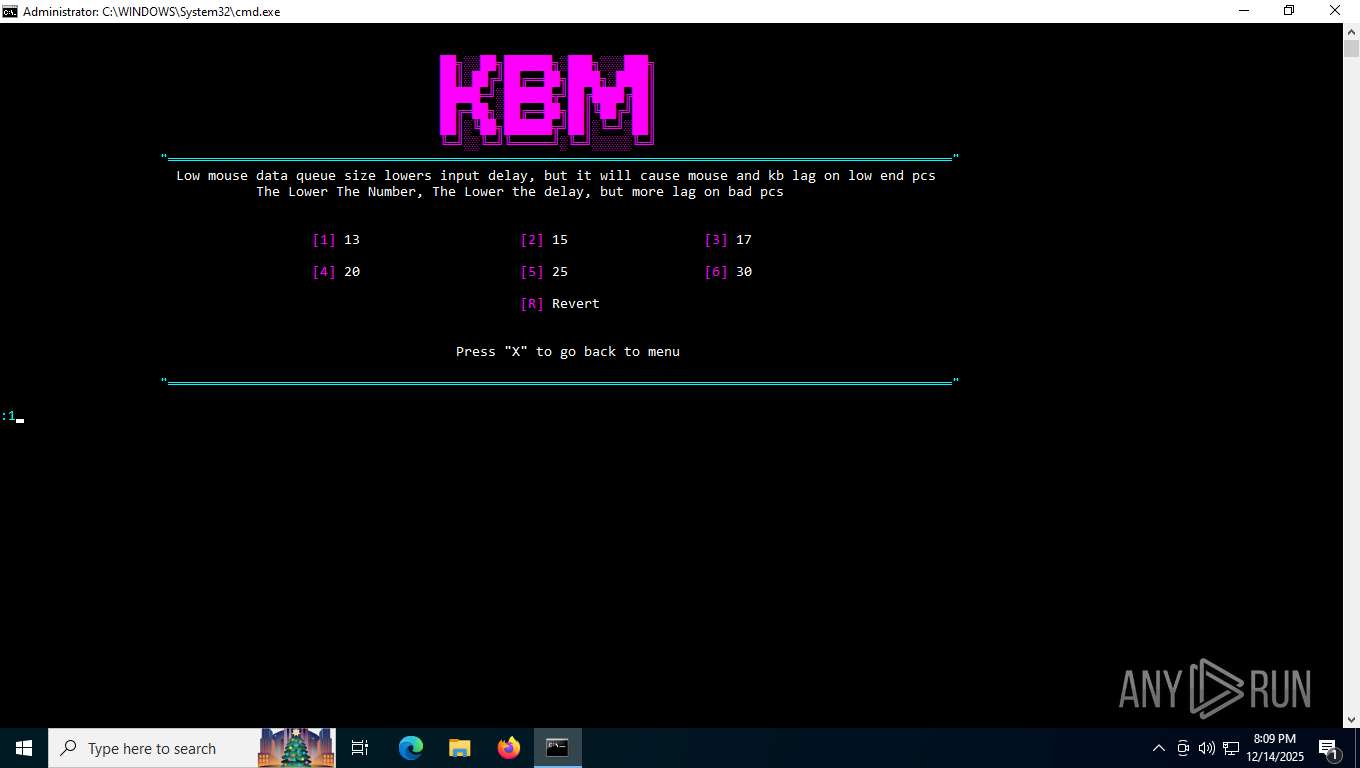
| 1316 | Reg.exe add "HKLM\SYSTEM\CurrentControlSet\Services\mouclass\Parameters" /v "MouseDataQueueSize" /t REG_DWORD /d "19" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1908 | timeout 2 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2036 | Reg.exe add "HKLM\SYSTEM\CurrentControlSet\Services\kbdclass\Parameters" /v "KeyboardDataQueueSize" /t REG_DWORD /d "19" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2144 | Reg.exe add "HKLM\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Policies\DataCollection" /v "AllowTelemetry" /t REG_DWORD /d "0" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 278
Read events
23 221
Write events
56
Delete events
1
Modification events
| (PID) Process: | (2416) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SystemRestore |
| Operation: | write | Name: | SystemRestorePointCreationFrequency |
Value: 0 | |||
| (PID) Process: | (7612) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP\Clients |
| Operation: | write | Name: | {09F7EDC5-294E-4180-AF6A-FB0E6A0E9513} |
Value: \\?\Volume{2f5c5e72-85a9-11eb-90a8-9a9b76358421}\:(C%3A) | |||
| (PID) Process: | (7612) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP\Leases |
| Operation: | delete value | Name: | {09F7EDC5-294E-4180-AF6A-FB0E6A0E9513} |
Value: | |||
| (PID) Process: | (7636) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (4028) ShellExperienceHost.exe | Key: | \REGISTRY\A\{cf794bb5-e32c-00f9-e0a2-f966e6332ab2}\LocalState |
| Operation: | write | Name: | PeekBadges |
Value: 5B005D00000086469464356DDC01 | |||
| (PID) Process: | (8116) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Google\Chrome |
| Operation: | write | Name: | StartupBoostEnabled |
Value: 0 | |||
| (PID) Process: | (932) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Google\Chrome |
| Operation: | write | Name: | BackgroundModeEnabled |
Value: 0 | |||
| (PID) Process: | (2360) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Multimedia\Audio |
| Operation: | write | Name: | UserDuckingPreference |
Value: 3 | |||
| (PID) Process: | (2308) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Mouse |
| Operation: | write | Name: | MouseSpeed |
Value: 0 | |||
| (PID) Process: | (4920) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Mouse |
| Operation: | write | Name: | MouseThreshold1 |
Value: 0 | |||
Executable files
1
Suspicious files
2
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7596 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:402A4FF77CEB78E911B40C146408250D | SHA256:C4B7549781D2159C3D4B89C93B328C67BD394AA6C29B7706CBEB37C3A2D28B62 | |||
| 7596 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_scqrl2pj.uoh.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6244 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xjsiyiqm.15u.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6244 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dnpvd15x.s0u.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6244 | powershell.exe | C:\Exm\NvidiaProfileInspector\Reference.xml | xml | |
MD5:48A4E5B434EDBD8A466658695EDB6B21 | SHA256:512CE2C34D28514730E90369F2E08E9DE49D24944C610A5336A7B69C1A2FE35E | |||
| 7896 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_n5ms1hfw.uob.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7896 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_55rxc3rc.vbz.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3568 | curl.exe | C:\Users\admin\AppData\Local\Temp\nvidiaProfileInspector.zip | compressed | |
MD5:8A571C3CEFC0C3C6F080AAF569E21B64 | SHA256:6815AA27E92A84CDD1A6C35DD37553B79E922D3F1F3AD6D74D49A737C0036AA4 | |||
| 6244 | powershell.exe | C:\Exm\NvidiaProfileInspector\nvidiaProfileInspector.exe.config | xml | |
MD5:B987C34A41F202A7453E3C8971E40556 | SHA256:9D1AC1797BDEFD5C040ED737A213D55C492276B00CB78201A2183C0A2C868749 | |||
| 7452 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_53wfapeh.o1o.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
30
DNS requests
21
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | unknown | — | — | whitelisted |
7852 | SIHClient.exe | GET | 200 | 40.69.42.241:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
4724 | svchost.exe | POST | 200 | 40.126.31.73:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
4724 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7852 | SIHClient.exe | GET | 200 | 74.178.240.61:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
7852 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
3568 | curl.exe | GET | 302 | 140.82.121.3:443 | https://github.com/Orbmu2k/nvidiaProfileInspector/releases/latest/download/nvidiaProfileInspector.zip | unknown | — | — | whitelisted |
3568 | curl.exe | GET | 302 | 140.82.121.3:443 | https://github.com/Orbmu2k/nvidiaProfileInspector/releases/download/2.4.0.27/nvidiaProfileInspector.zip | unknown | — | — | whitelisted |
6056 | svchost.exe | GET | 200 | 184.24.77.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6056 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6192 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 184.86.251.5:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
4724 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4724 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
6056 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6056 | svchost.exe | 184.24.77.14:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |