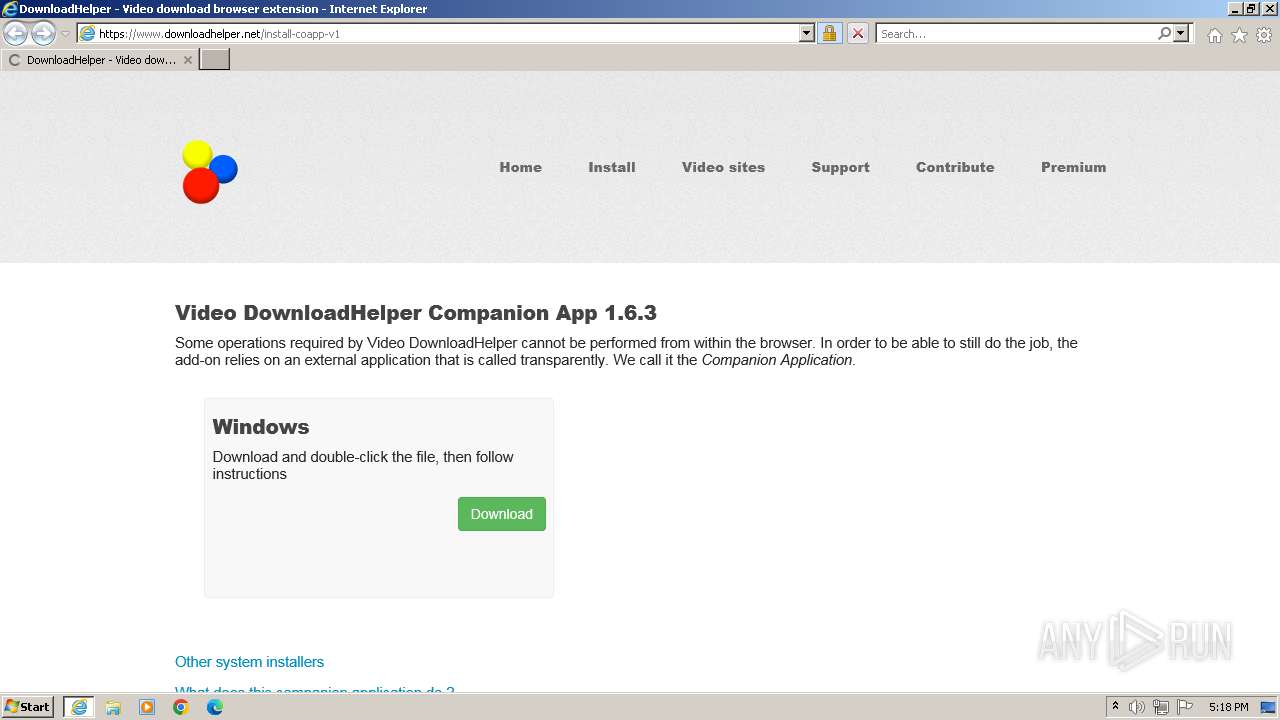
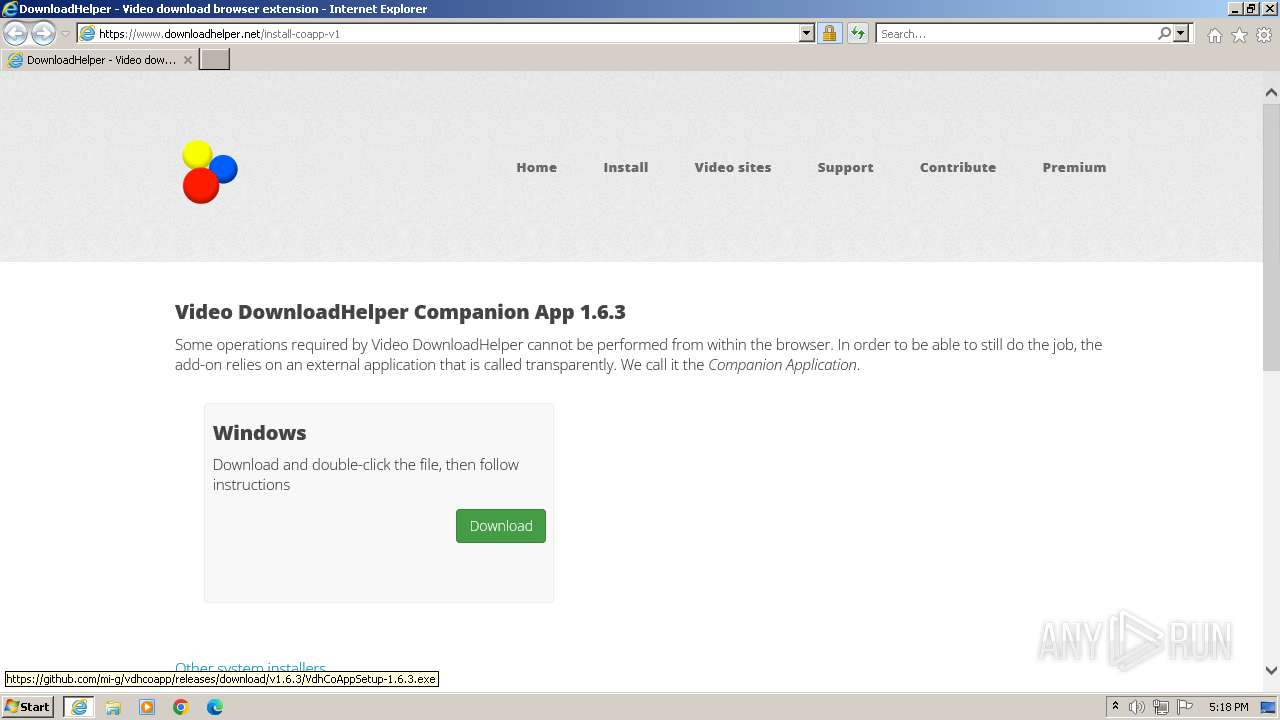
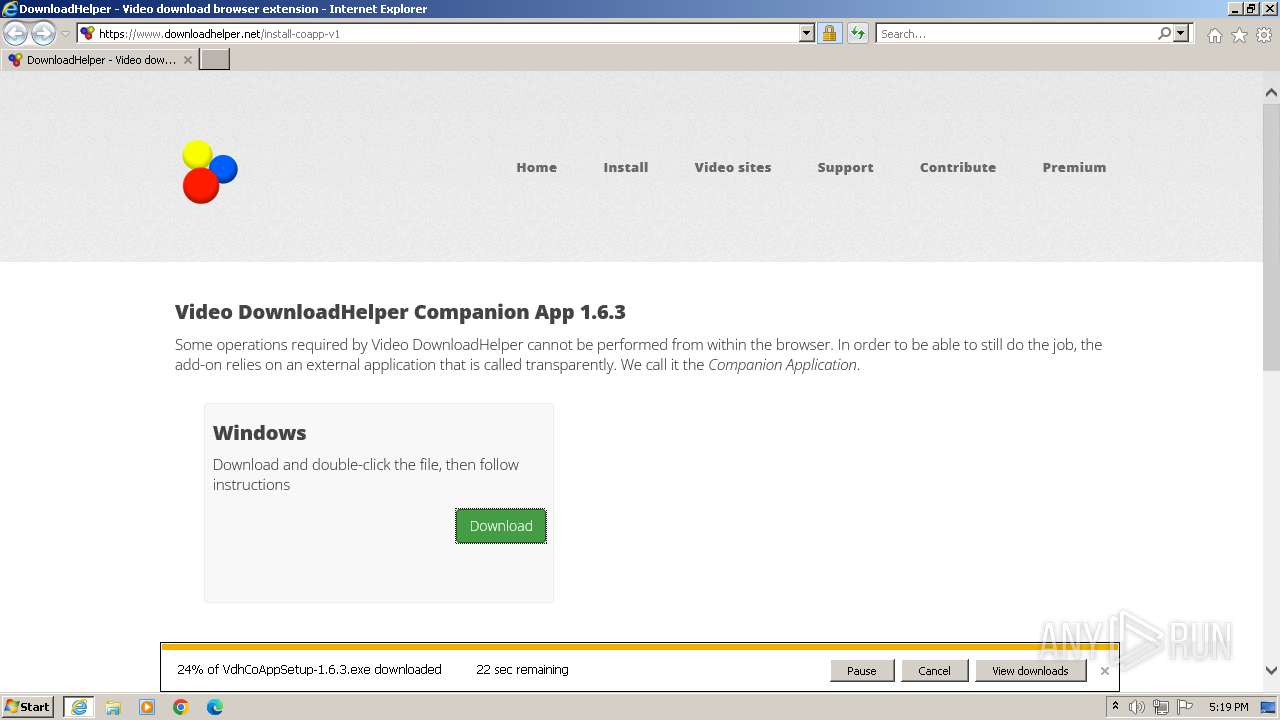
| URL: | https://www.downloadhelper.net/install-coapp-v1 |
| Full analysis: | https://app.any.run/tasks/bb2e7265-01fe-40f8-b041-161ad60fc5d4 |
| Verdict: | Malicious activity |
| Analysis date: | October 24, 2023, 16:18:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 53888D11477F8D8A240D26FE3FF8E4076F6648BD |
| SHA256: | B25C9D70900D7469619222B2C5BFA77C98D90DDBA7043C52A7F5D21085EC5397 |
| SSDEEP: | 3:N8DSL0QsVAXL0tygGGLn:2OLx0yL0tZGA |
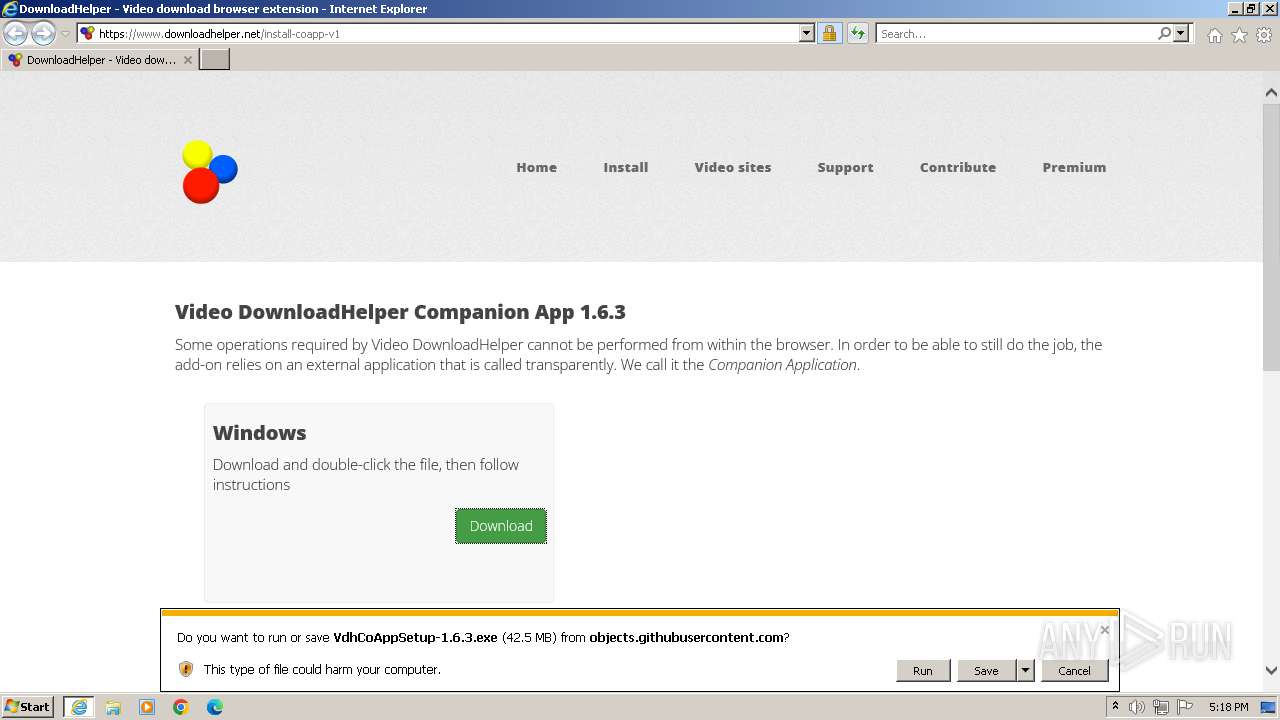
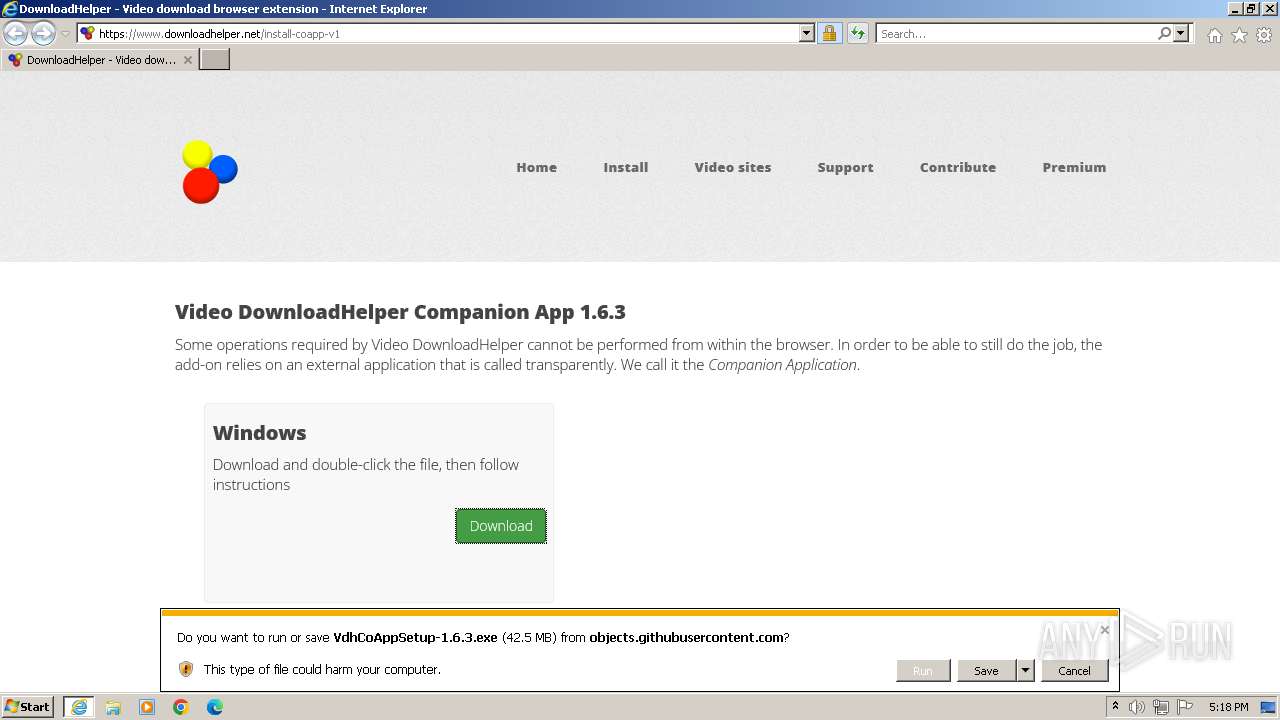
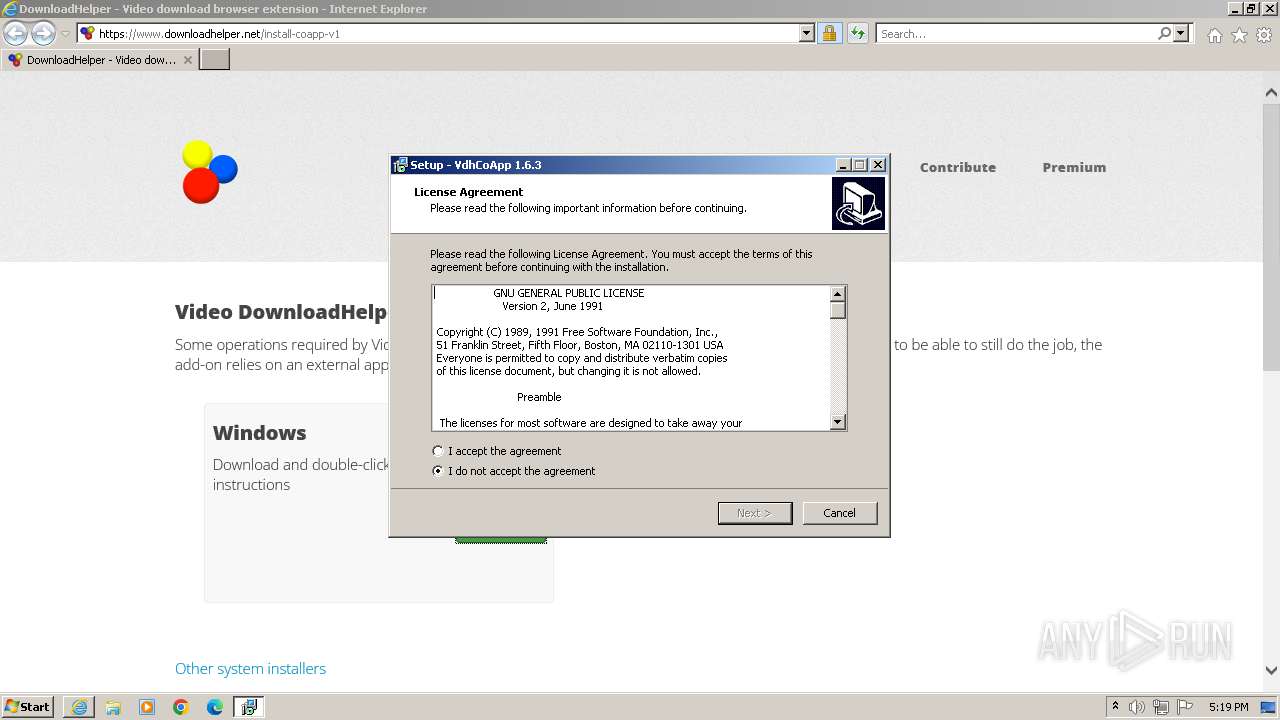
MALICIOUS
Application was dropped or rewritten from another process
- VdhCoAppSetup-1.6.3.exe (PID: 3648)
- VdhCoAppSetup-1.6.3.exe (PID: 2736)
Drops the executable file immediately after the start
- VdhCoAppSetup-1.6.3.exe (PID: 3648)
- VdhCoAppSetup-1.6.3.exe (PID: 2736)
- VdhCoAppSetup-1.6.3.tmp (PID: 1796)
SUSPICIOUS
Reads the Windows owner or organization settings
- VdhCoAppSetup-1.6.3.tmp (PID: 1796)
INFO
Drops the executable file immediately after the start
- iexplore.exe (PID: 3232)
Application launched itself
- iexplore.exe (PID: 3828)
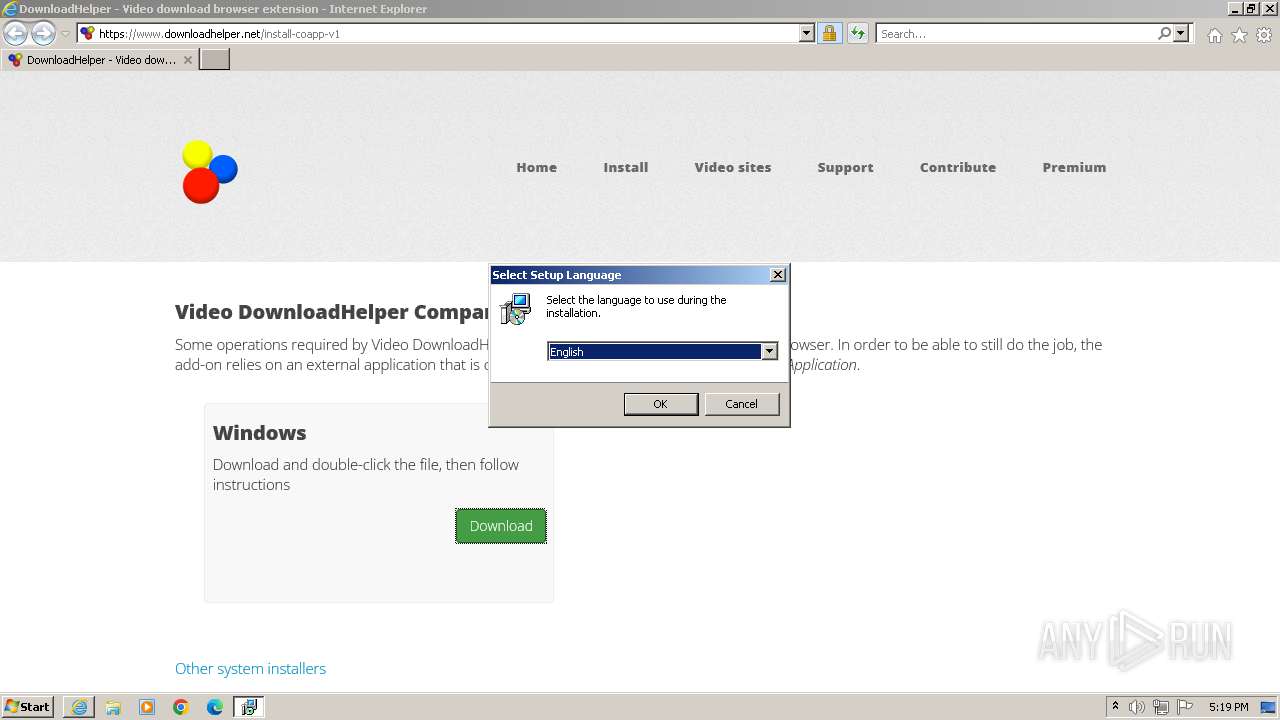
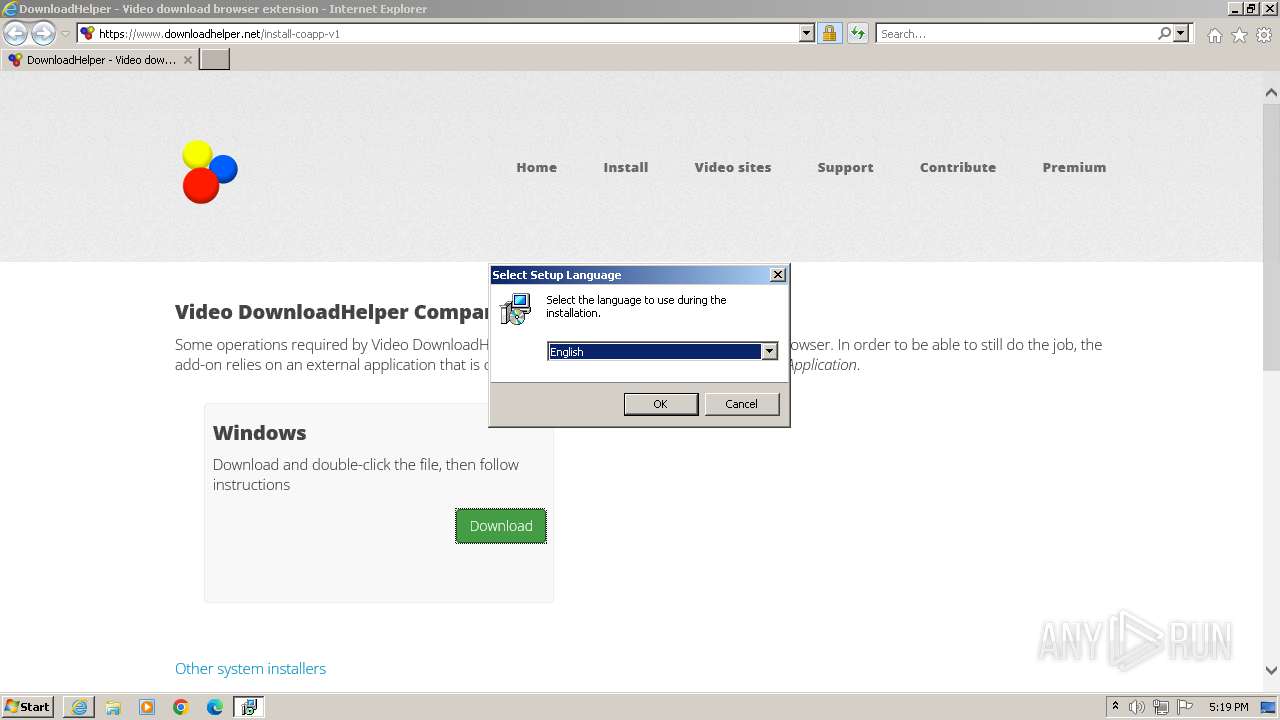
Checks supported languages
- VdhCoAppSetup-1.6.3.exe (PID: 3648)
- VdhCoAppSetup-1.6.3.tmp (PID: 3352)
- VdhCoAppSetup-1.6.3.exe (PID: 2736)
- VdhCoAppSetup-1.6.3.tmp (PID: 1796)
Create files in a temporary directory
- VdhCoAppSetup-1.6.3.exe (PID: 3648)
- VdhCoAppSetup-1.6.3.exe (PID: 2736)
Reads the computer name
- VdhCoAppSetup-1.6.3.tmp (PID: 3352)
- VdhCoAppSetup-1.6.3.tmp (PID: 1796)
Application was dropped or rewritten from another process
- VdhCoAppSetup-1.6.3.tmp (PID: 3352)
- VdhCoAppSetup-1.6.3.tmp (PID: 1796)
The process uses the downloaded file
- iexplore.exe (PID: 3828)
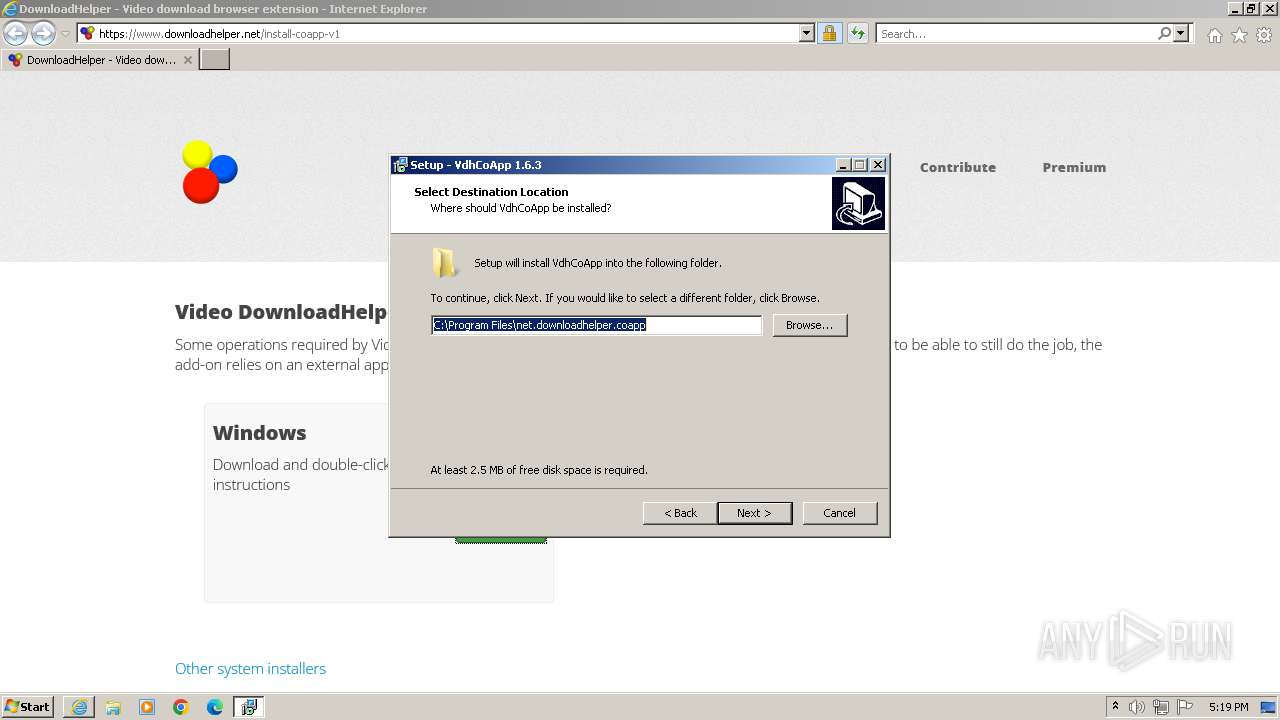
Creates files in the program directory
- VdhCoAppSetup-1.6.3.tmp (PID: 1796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1796 | "C:\Users\admin\AppData\Local\Temp\is-PA83O.tmp\VdhCoAppSetup-1.6.3.tmp" /SL5="$4034A,43872882,721408,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\VdhCoAppSetup-1.6.3.exe" /SPAWNWND=$6034E /NOTIFYWND=$110168 | C:\Users\admin\AppData\Local\Temp\is-PA83O.tmp\VdhCoAppSetup-1.6.3.tmp | — | VdhCoAppSetup-1.6.3.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2736 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\VdhCoAppSetup-1.6.3.exe" /SPAWNWND=$6034E /NOTIFYWND=$110168 | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\VdhCoAppSetup-1.6.3.exe | VdhCoAppSetup-1.6.3.tmp | ||||||||||||
User: admin Company: DownloadHelper Integrity Level: HIGH Description: VdhCoApp Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3232 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3828 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3352 | "C:\Users\admin\AppData\Local\Temp\is-H54UM.tmp\VdhCoAppSetup-1.6.3.tmp" /SL5="$110168,43872882,721408,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\VdhCoAppSetup-1.6.3.exe" | C:\Users\admin\AppData\Local\Temp\is-H54UM.tmp\VdhCoAppSetup-1.6.3.tmp | — | VdhCoAppSetup-1.6.3.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3648 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\VdhCoAppSetup-1.6.3.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\VdhCoAppSetup-1.6.3.exe | — | iexplore.exe | |||||||||||
User: admin Company: DownloadHelper Integrity Level: MEDIUM Description: VdhCoApp Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3828 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.downloadhelper.net/install-coapp-v1" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
17 640
Read events
17 559
Write events
75
Delete events
6
Modification events
| (PID) Process: | (3828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000056010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
79
Suspicious files
45
Text files
39
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:5FA0268A23B6536F7320C2D8DB5ACCF9 | SHA256:7EB473D2BE34A5111D1EBF3A50915C1C050E727304F55AAF90B11C787D3C276F | |||
| 3232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\logo-64[1].png | image | |
MD5:49E7471DA023C142CF08C178E33C4AEA | SHA256:9B62B2E05FF615DBB6709D2D68A52724C0CD9F7B45CEB1FCD07C3880E1D0665F | |||
| 3232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:F87046B43D82CDF64B8D867B1548BF3E | SHA256:90E5A2D50EE6FACA85774485FB03613947ED3F6D5C781B75A539E2AF7A87474D | |||
| 3232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\cache-fe2f7b3e934ddfc71715344505de8d18[1].js | text | |
MD5:21D53B234EBAC82FF4C12FB309FD763A | SHA256:6608C0010171F3C99B737379A8C7BBE1F1EDF76E28331170E8835762A7227D6D | |||
| 3232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\cache-82030eb4809a302791380e03b8dbc12e[1].css | text | |
MD5:51D8A627BE48B7AA8BFE498AB1A54790 | SHA256:7FFA28CB6257C2E8B23E3324607B8BC38CEE826BD67E48B254723E17C3543F98 | |||
| 3232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\install-coapp-v1[1].htm | html | |
MD5:B48622738F3378B9A58CFD6D553D4CF8 | SHA256:D8B4D16942D80B148F985DF6560FE2C09EF2E5180BDDEE0D3806F8500443819E | |||
| 3232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:A2EB2A6569ACC6DB9F3BC4CF72F39A89 | SHA256:9115DA958A0ED178238E8B2A58F9A71D2649A58E4C519B65AFFF358665F8C942 | |||
| 3232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\bg01[1].png | image | |
MD5:A622AAE59A4078C30AFDD4730CC6E9E7 | SHA256:D5BD22CB3C4050E97252BC32883B1A8FA2FB3EF5DE82A38A3004E99DF8FDAA2D | |||
| 3232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\bootstrap.min[1].css | text | |
MD5:2F624089C65F12185E79925BC5A7FC42 | SHA256:EECE6E0C65B7007AB0EB1B4998D36DAFE381449525824349128EFC3F86F4C91C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
36
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3828 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | US | binary | 313 b | unknown |
3232 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | binary | 1.47 Kb | unknown |
3232 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?088fea238d8b5b84 | GB | compressed | 4.66 Kb | unknown |
3232 | iexplore.exe | GET | 200 | 142.250.187.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | unknown |
3232 | iexplore.exe | GET | 200 | 142.250.187.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | unknown |
3232 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?bb07f2e034838e3f | GB | compressed | 4.66 Kb | unknown |
3232 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | binary | 471 b | unknown |
3232 | iexplore.exe | GET | 200 | 142.250.187.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCiqTpRpOc3bRIUpkAuvtnV | US | binary | 472 b | unknown |
3232 | iexplore.exe | GET | 200 | 142.250.187.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD50q2MxTvdnxLfPCm8%2F51a | US | binary | 472 b | unknown |
3232 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | US | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3232 | iexplore.exe | 172.67.75.206:443 | — | CLOUDFLARENET | US | unknown |
3232 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3232 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3232 | iexplore.exe | 142.250.184.142:443 | www.google-analytics.com | GOOGLE | US | whitelisted |
3232 | iexplore.exe | 142.250.184.138:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3232 | iexplore.exe | 104.18.10.207:443 | maxcdn.bootstrapcdn.com | CLOUDFLARENET | — | unknown |
3232 | iexplore.exe | 142.250.187.163:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3232 | iexplore.exe | 142.251.140.35:443 | fonts.gstatic.com | GOOGLE | US | unknown |
3232 | iexplore.exe | 216.58.213.104:443 | www.googletagmanager.com | GOOGLE | US | unknown |
3232 | iexplore.exe | 216.239.32.36:443 | region1.google-analytics.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
region1.google-analytics.com |
| whitelisted |
github.com |
| shared |