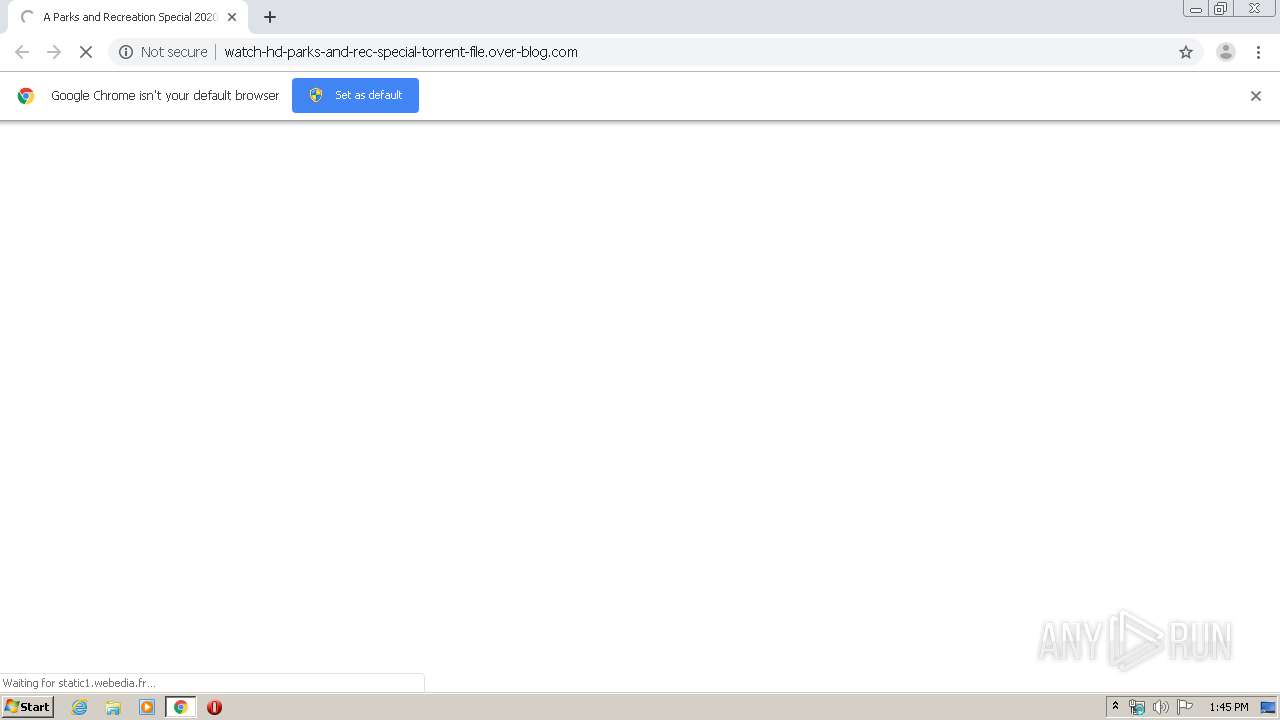
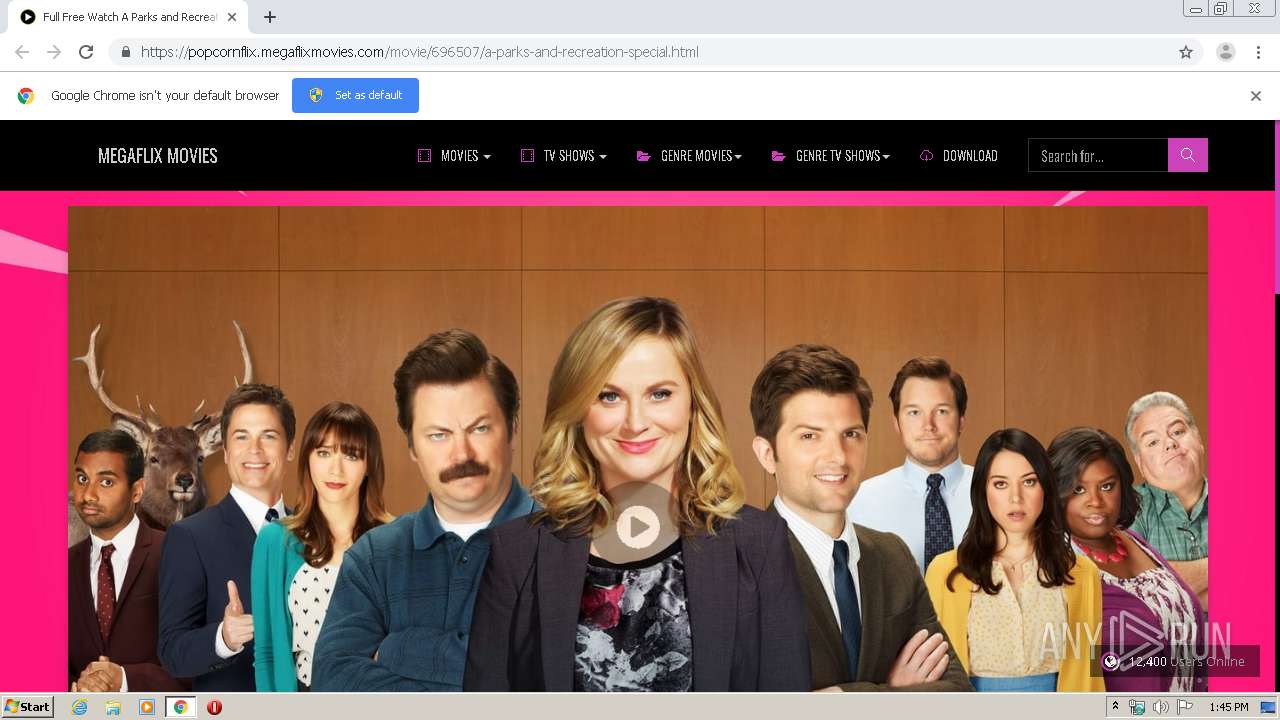
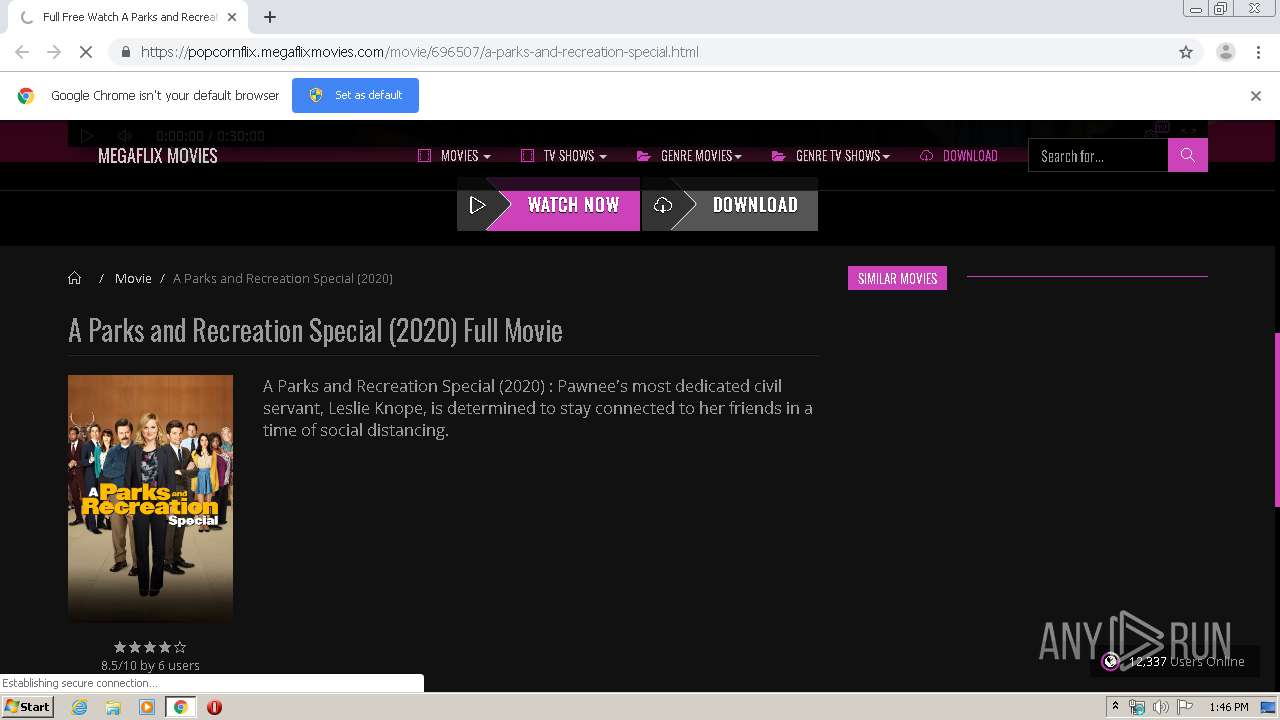
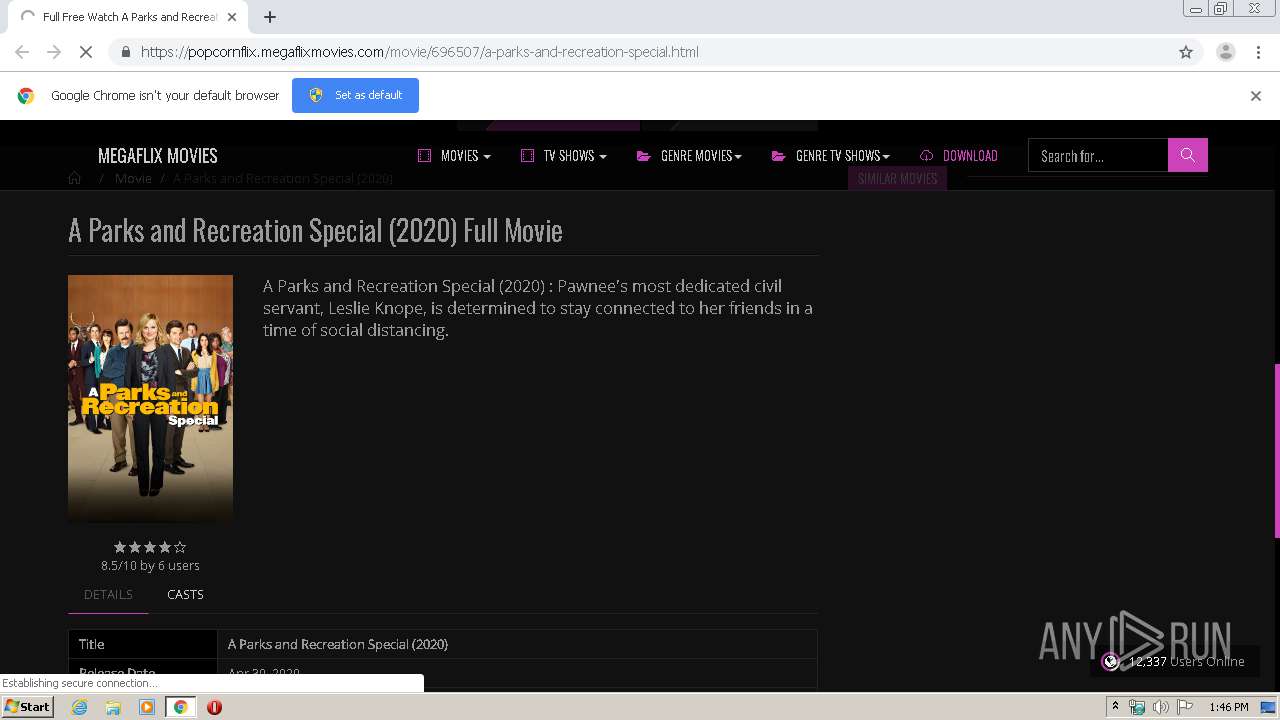
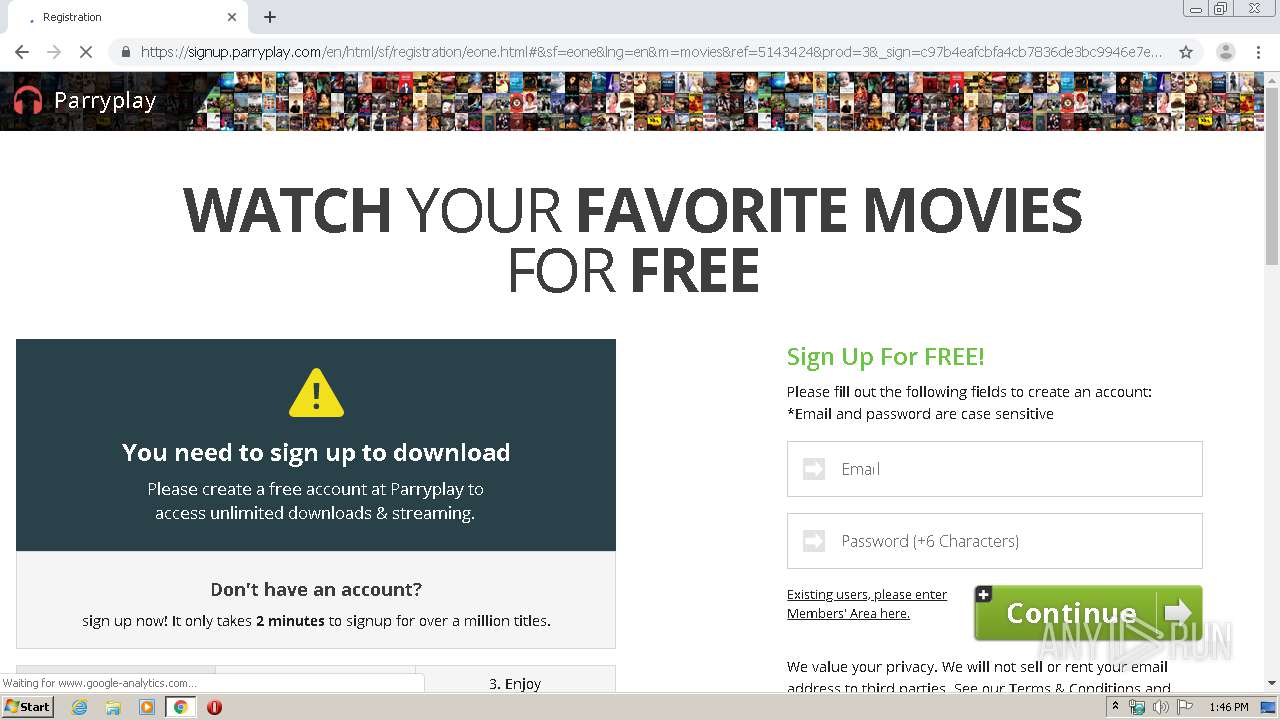
| URL: | http://watch-hd-parks-and-rec-special-torrent-file.over-blog.com |
| Full analysis: | https://app.any.run/tasks/0624c8f8-e37b-4f84-a440-39b8c284dc42 |
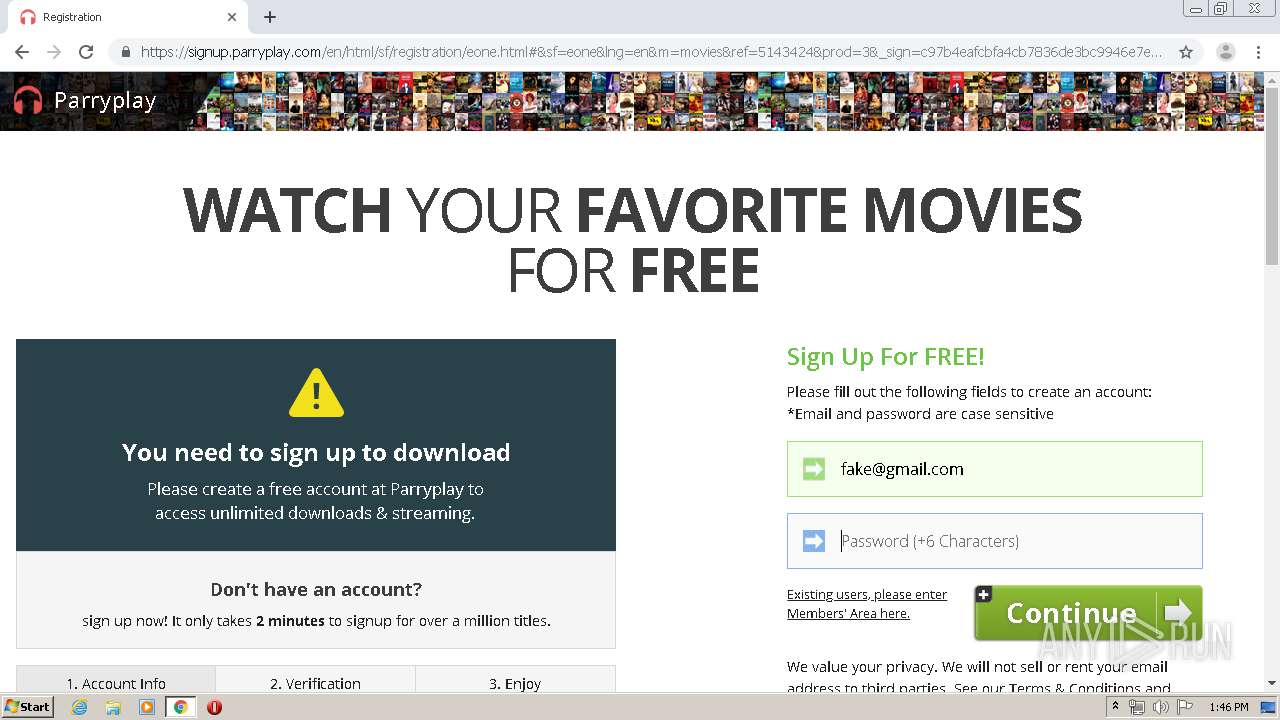
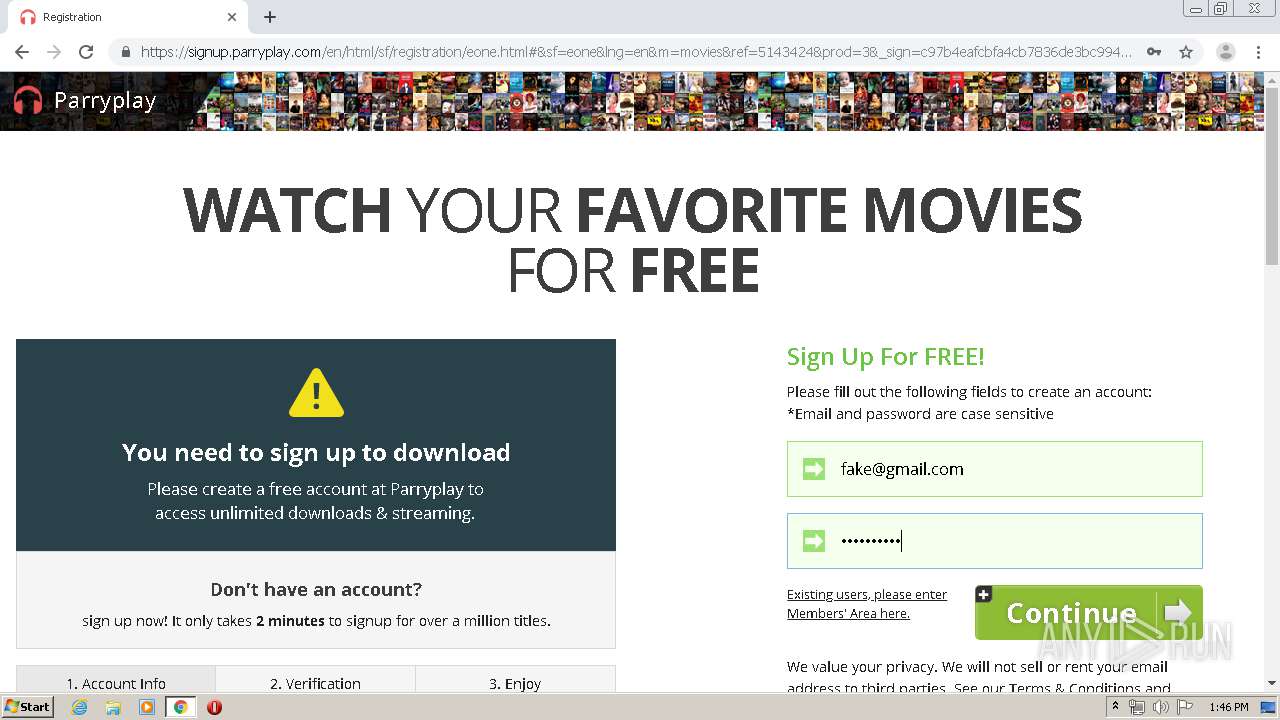
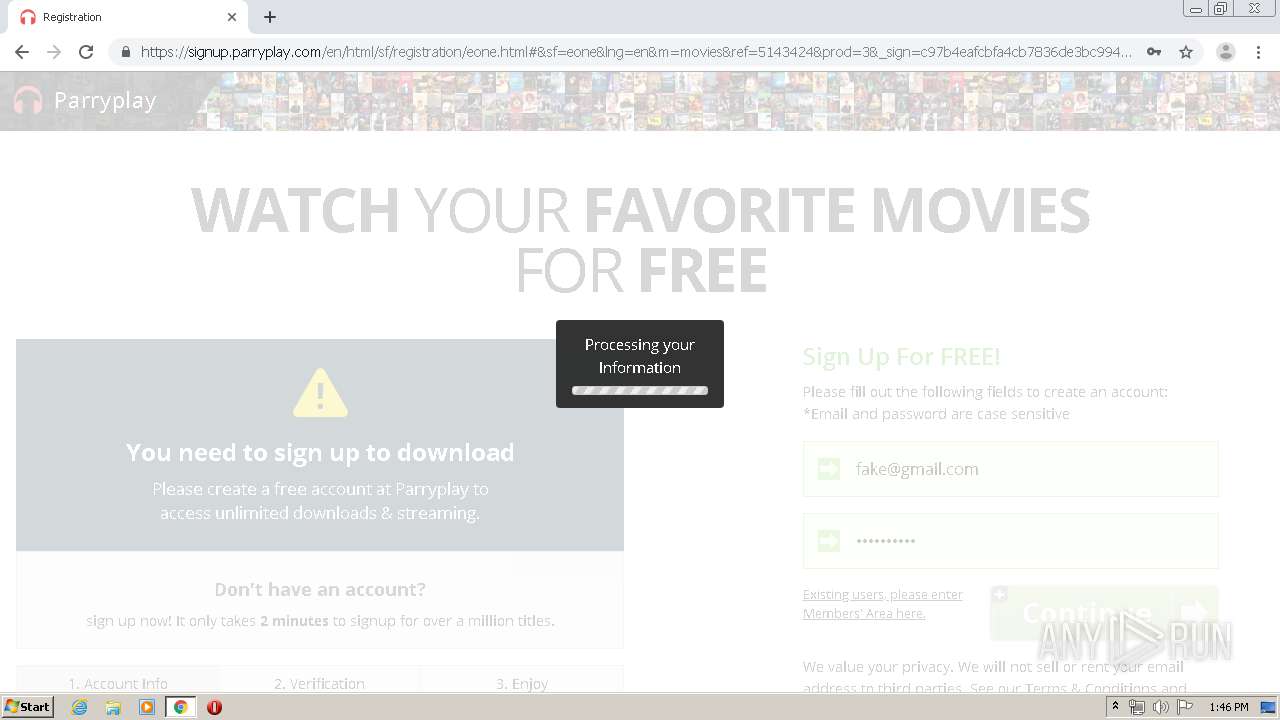
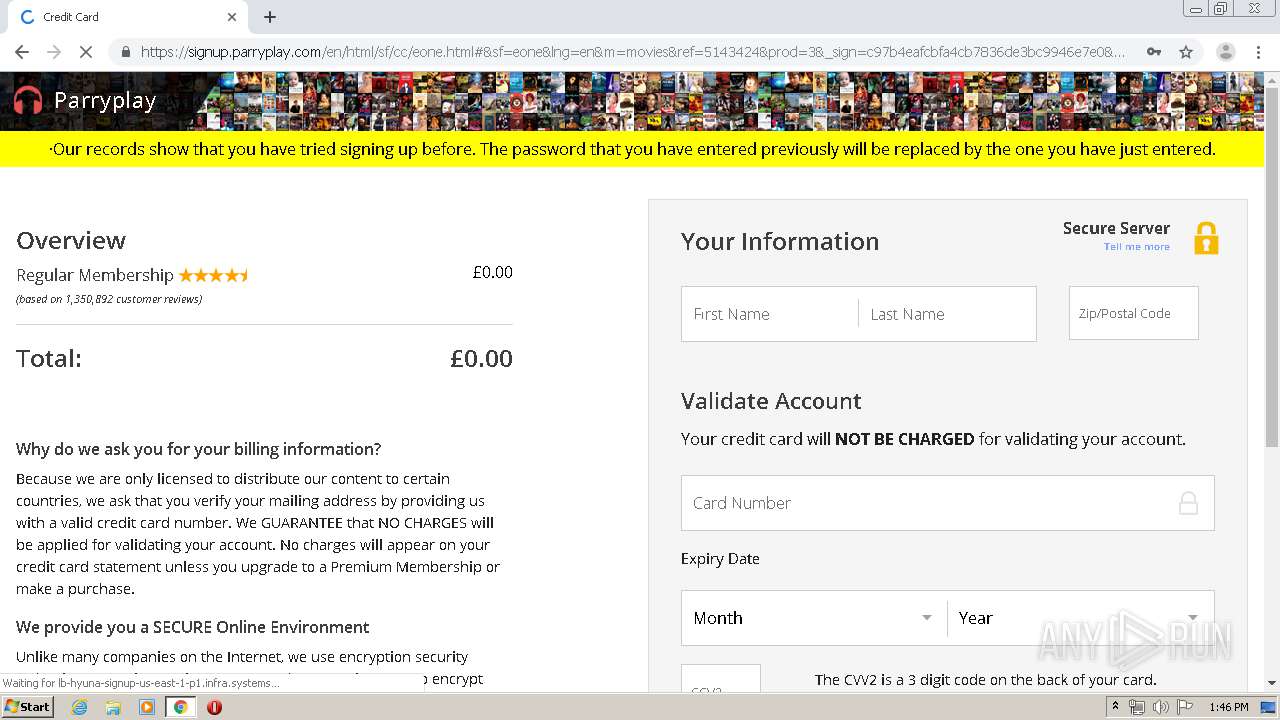
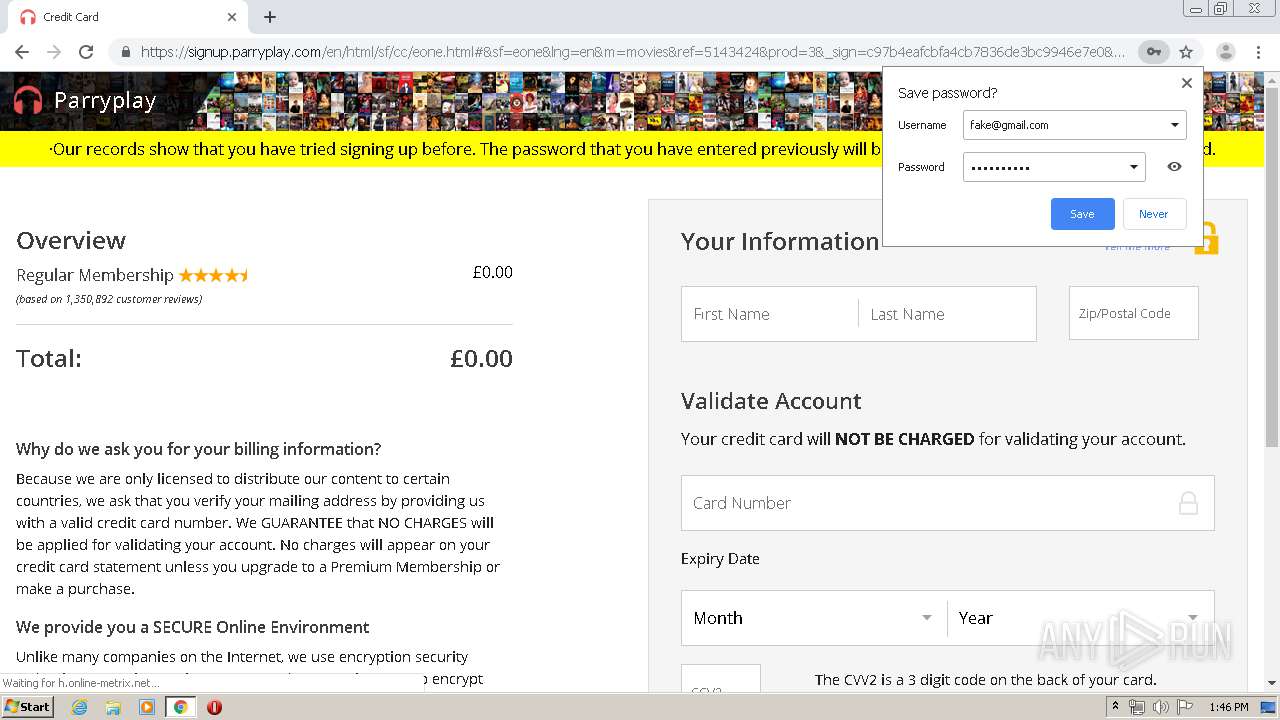
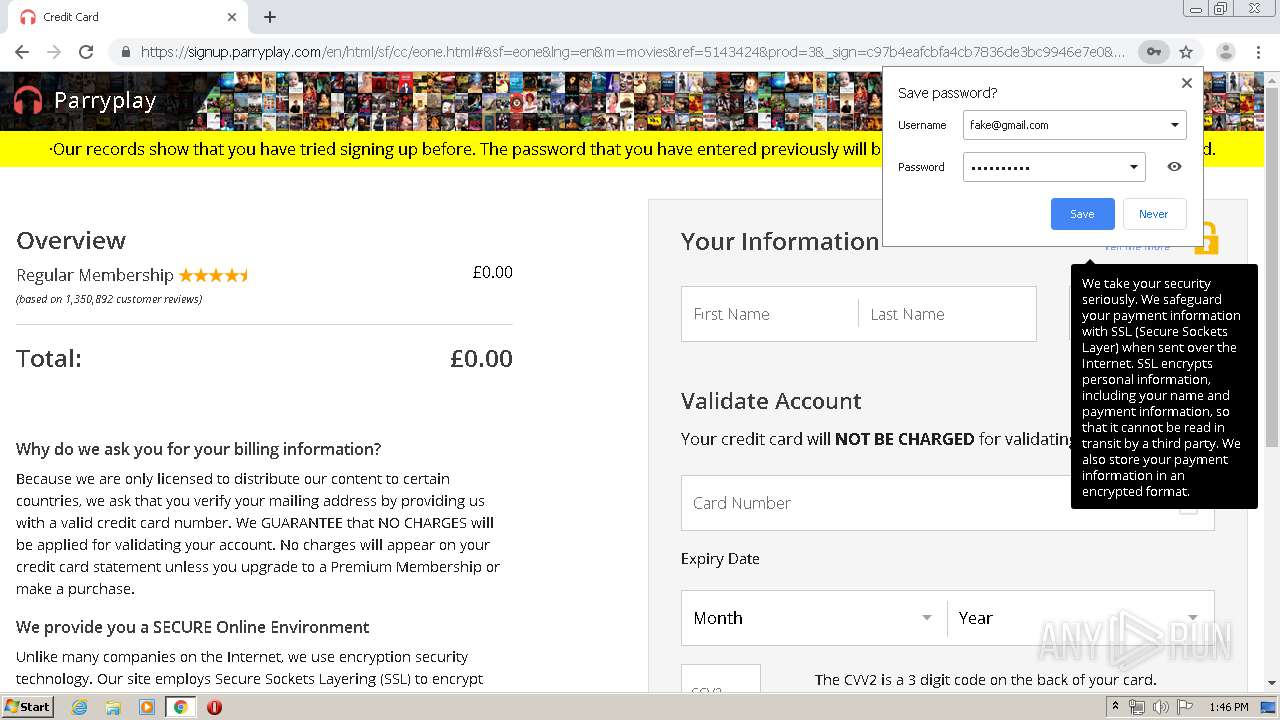
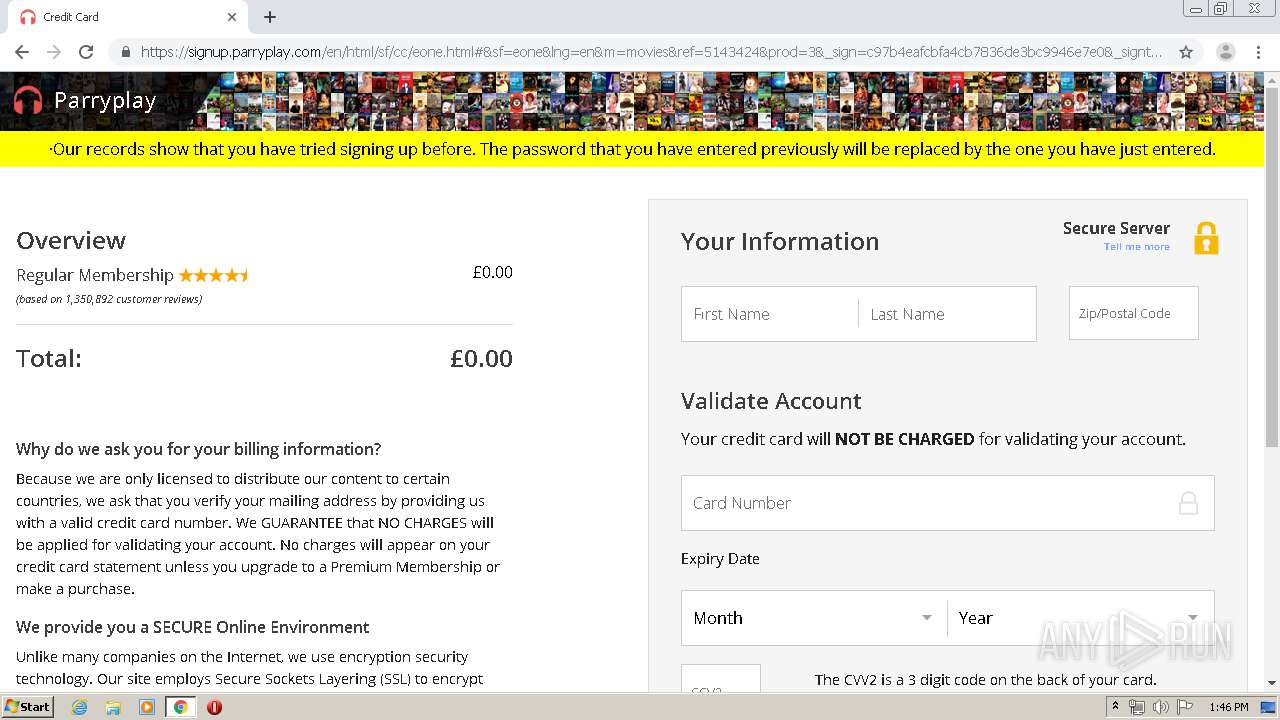
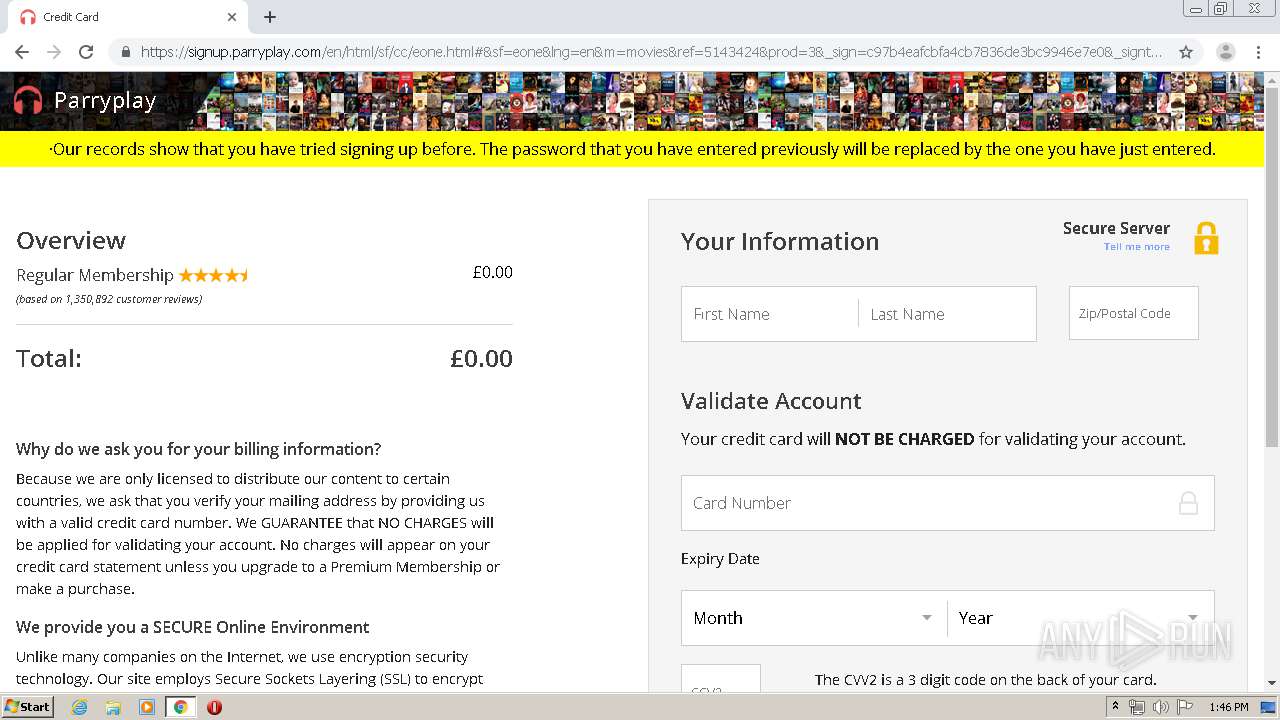
| Verdict: | Malicious activity |
| Analysis date: | May 11, 2020, 12:45:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A75E119BD9238A29C40BDEC28D743AF1 |
| SHA1: | 142F1B38C59F956C17B4C9A7CCD21DE7B6F59361 |
| SHA256: | B25945CB7E3899CEA43482684B6803F54209B90BFF900954BCD7D8A7822F2DAC |
| SSDEEP: | 3:N1KJEhgW5UjISAuuRIDMDPlIn:CKGP2zR+kPlIn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
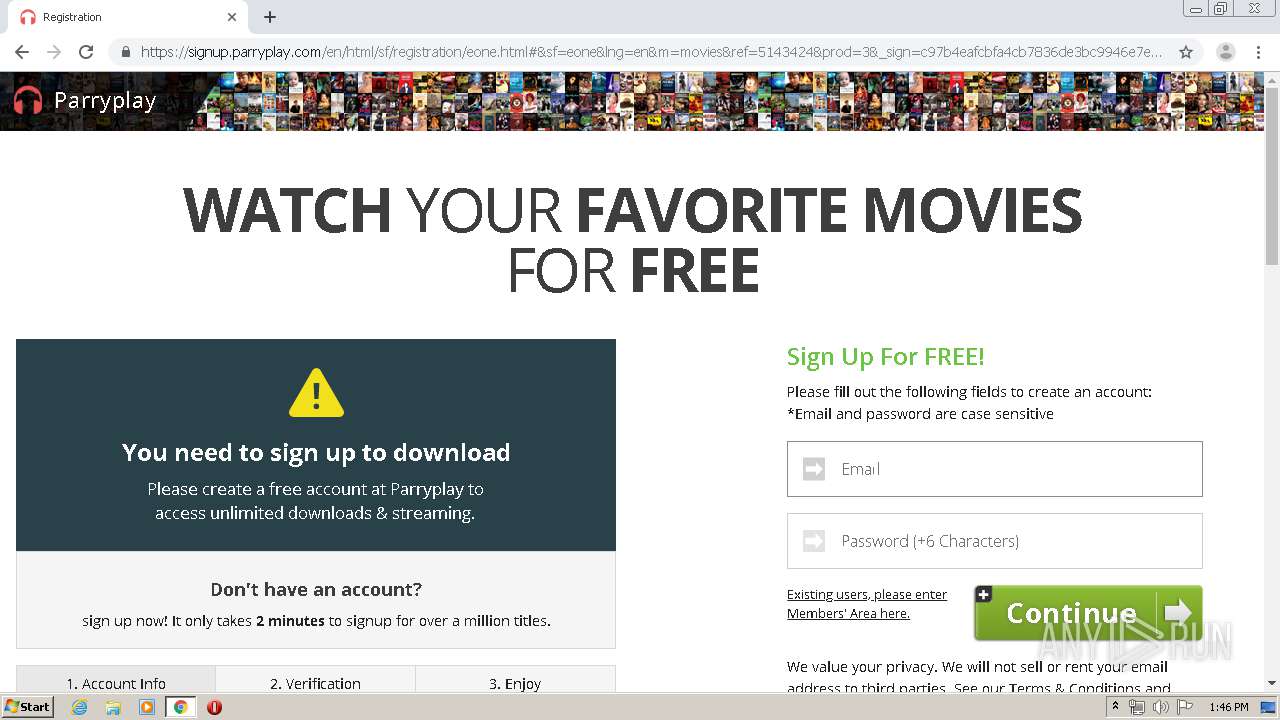
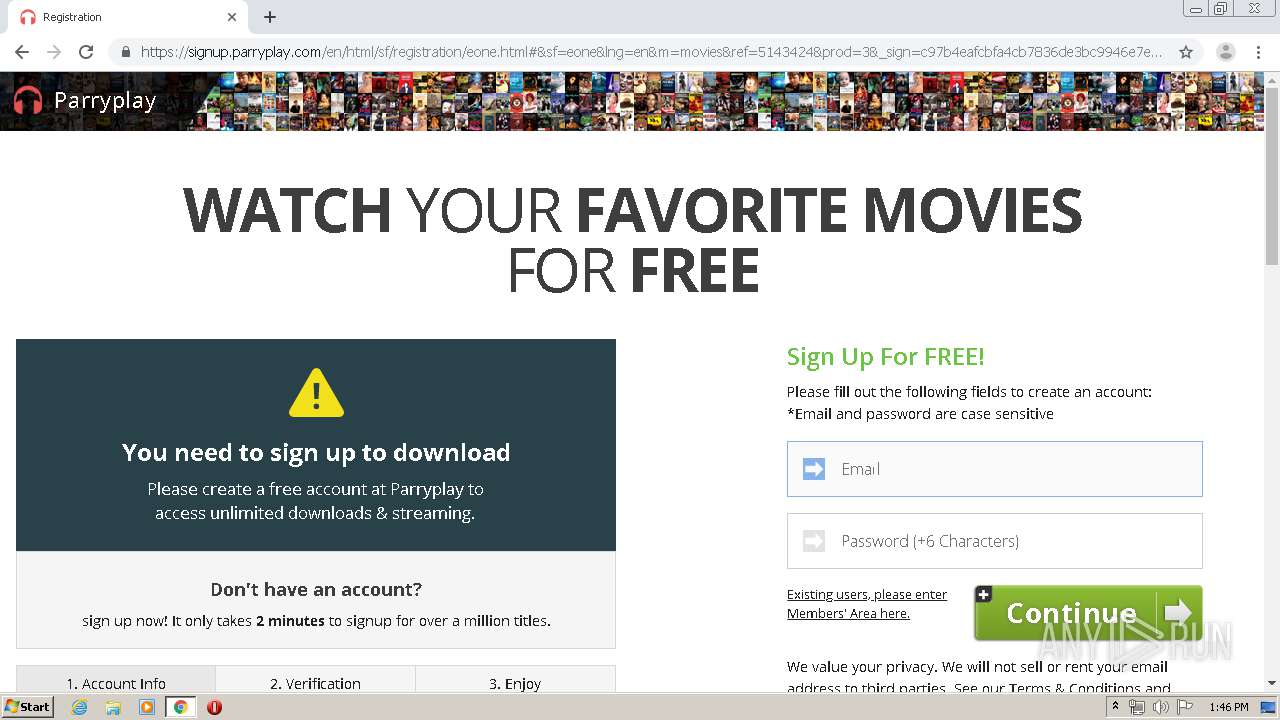
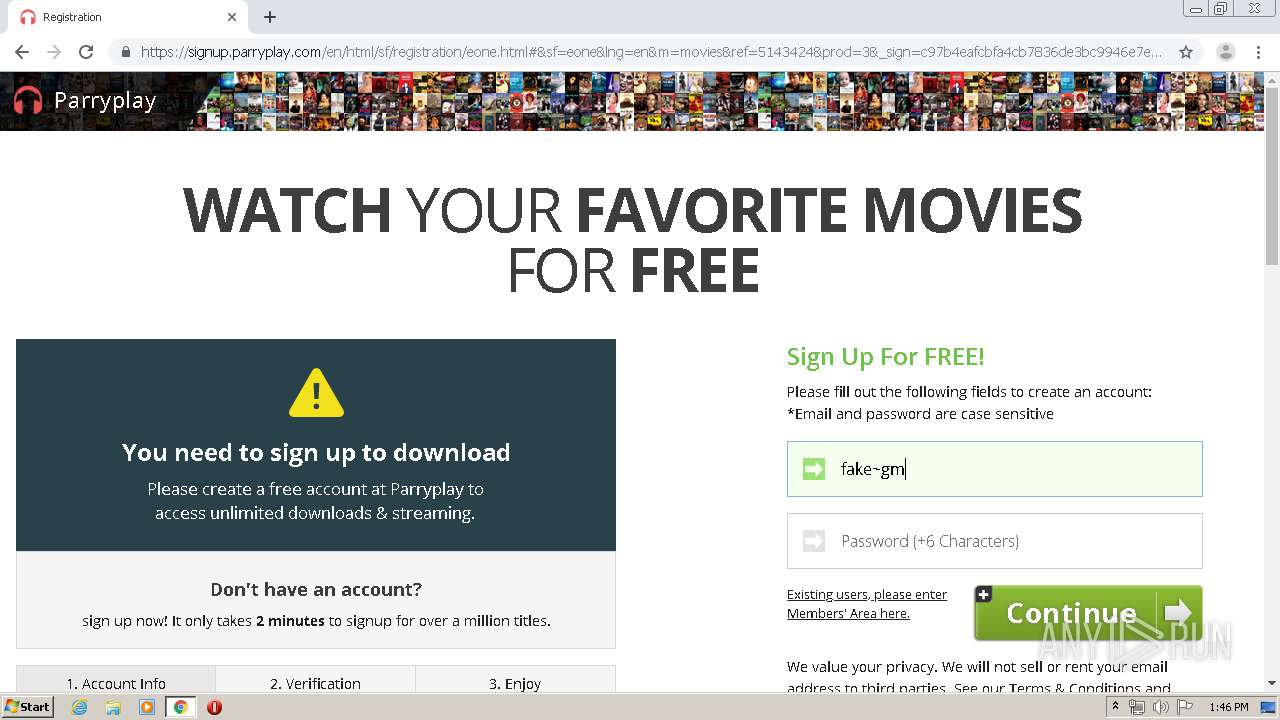
Application launched itself
- chrome.exe (PID: 576)
Reads the hosts file
- chrome.exe (PID: 576)
- chrome.exe (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
25
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://watch-hd-parks-and-rec-special-torrent-file.over-blog.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,10437084164996767003,2683957367181563007,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=928351395903137107 --mojo-platform-channel-handle=2492 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,10437084164996767003,2683957367181563007,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6341164345221490407 --mojo-platform-channel-handle=4184 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,10437084164996767003,2683957367181563007,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14460766077239053291 --mojo-platform-channel-handle=3964 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,10437084164996767003,2683957367181563007,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4254146933008329236 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,10437084164996767003,2683957367181563007,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10895908204864040454 --mojo-platform-channel-handle=2348 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,10437084164996767003,2683957367181563007,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=9829166175169213196 --mojo-platform-channel-handle=1632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,10437084164996767003,2683957367181563007,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=289477231077547028 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3380 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,10437084164996767003,2683957367181563007,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2460458497431265077 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,10437084164996767003,2683957367181563007,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4848126965928478544 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2756 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
675
Read events
578
Write events
92
Delete events
5
Modification events
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 576-13233674731919500 |
Value: 259 | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (576) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
67
Text files
136
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EB948EC-240.pma | — | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3a17071e-3b40-41c4-bf21-e040d20f1d15.tmp | — | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa873e6.TMP | text | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:9543068B6751E1F3E11F91D72EE78D95 | SHA256:D060AD21AE6E04CB58668CAA52ADFCA573E018102CC07554D2ED3EAE11AB7785 | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa87425.TMP | text | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa8753e.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
121
DNS requests
51
Threats
3
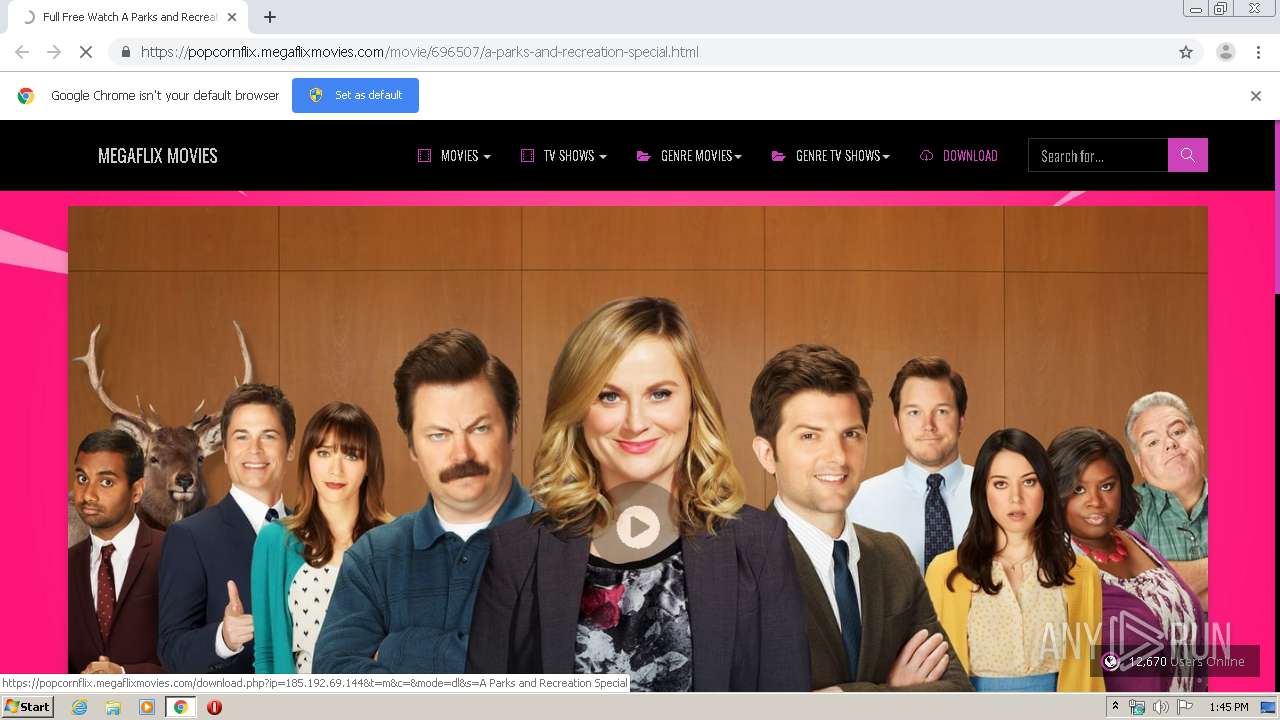
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
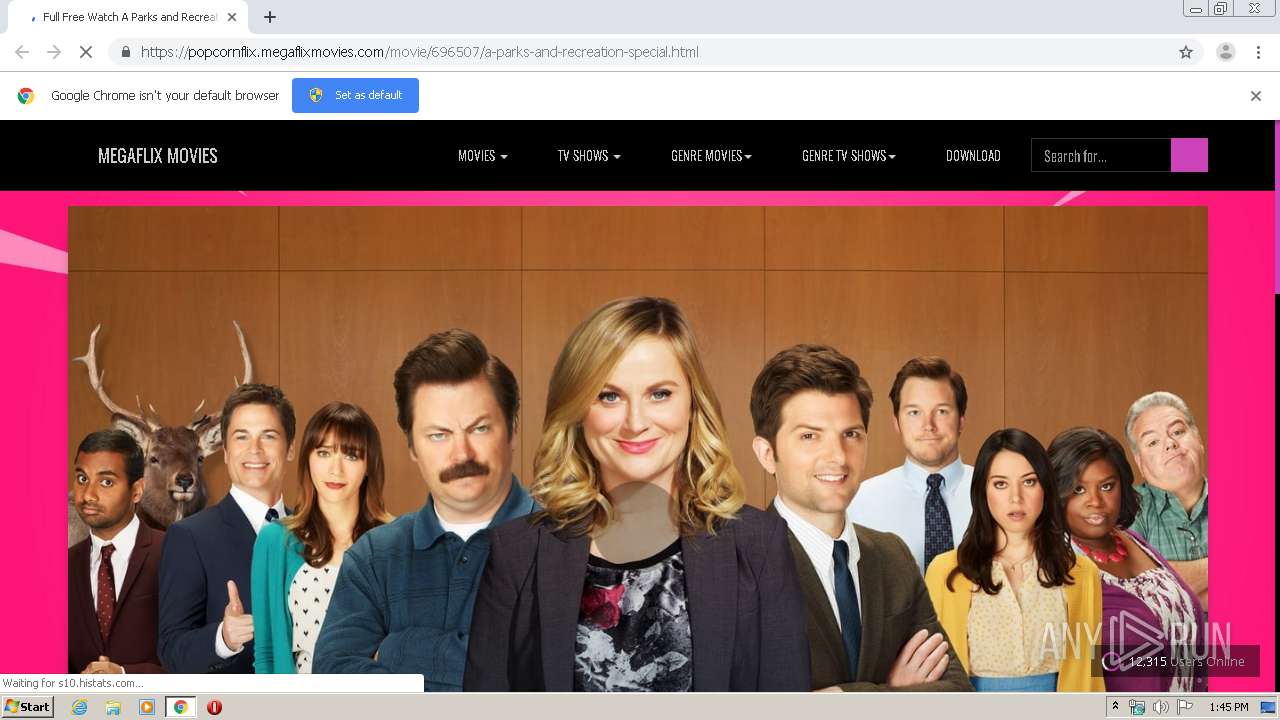
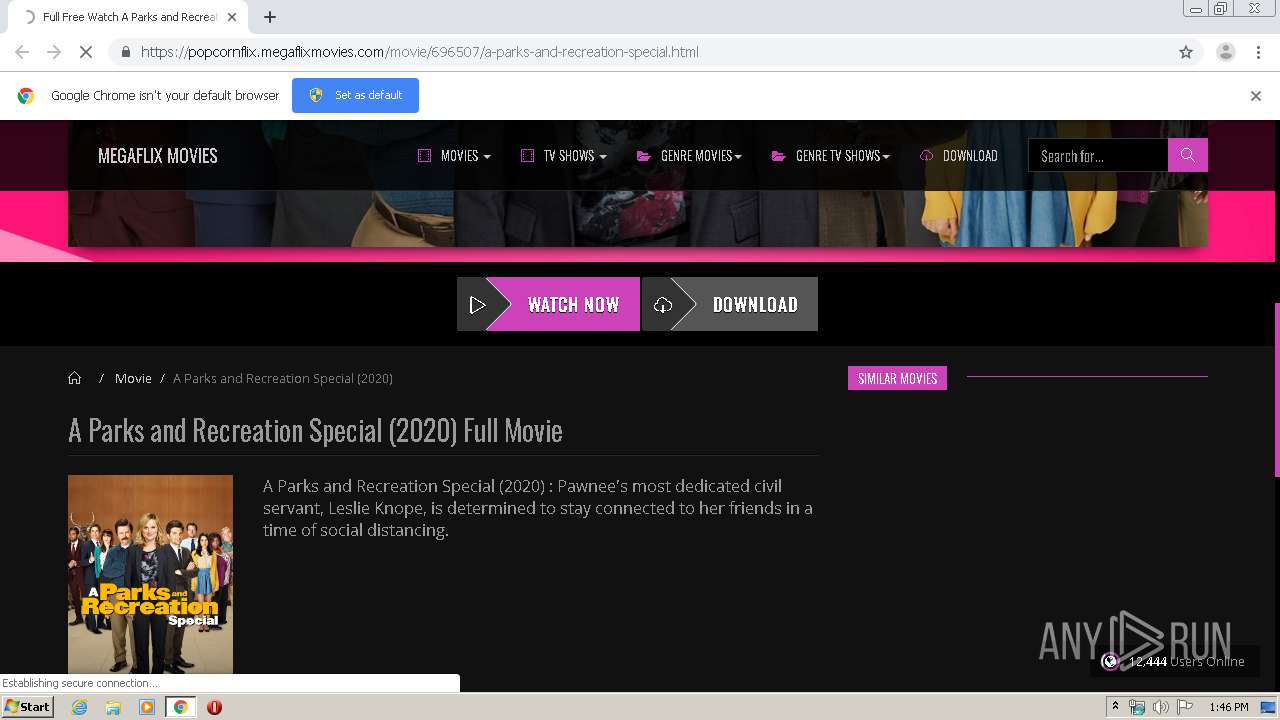
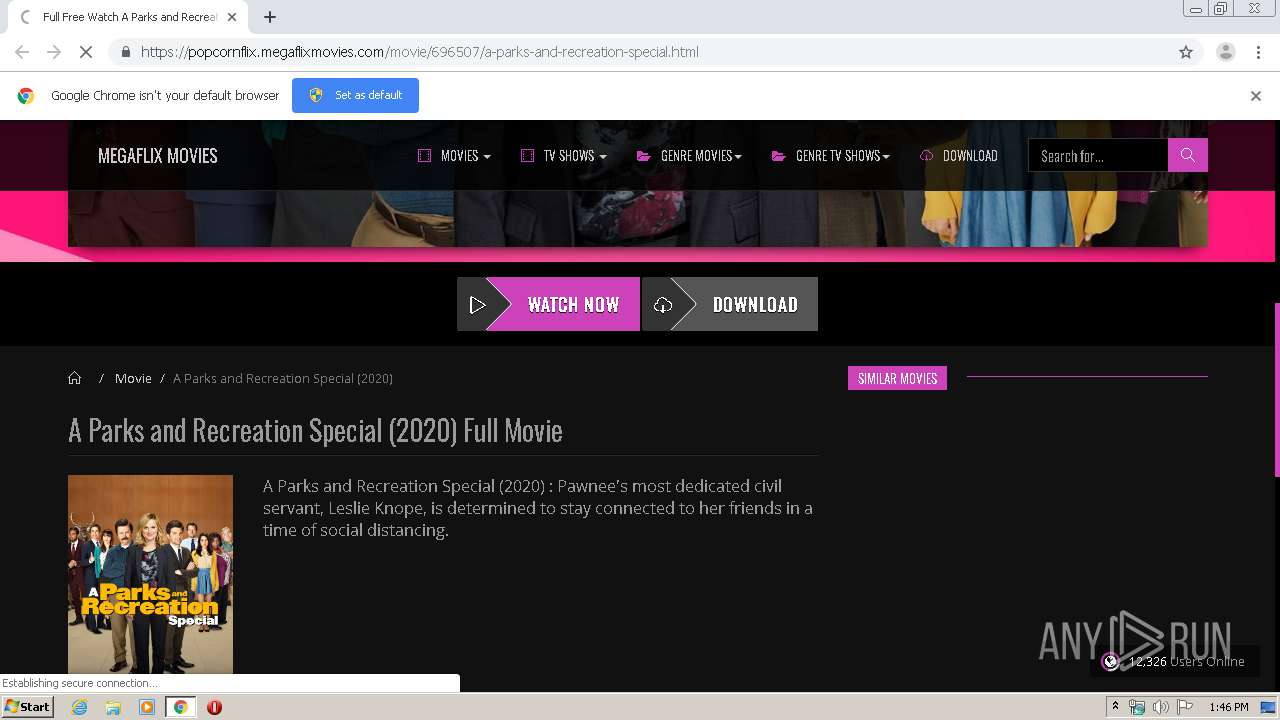
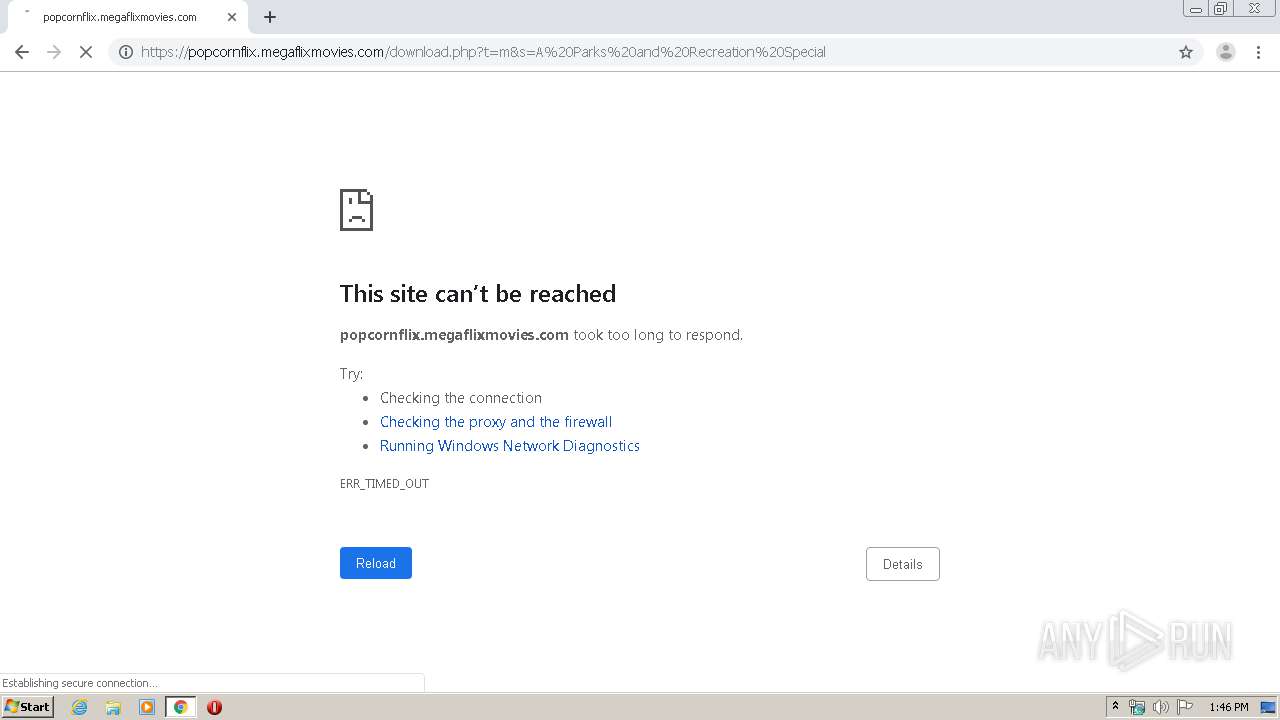
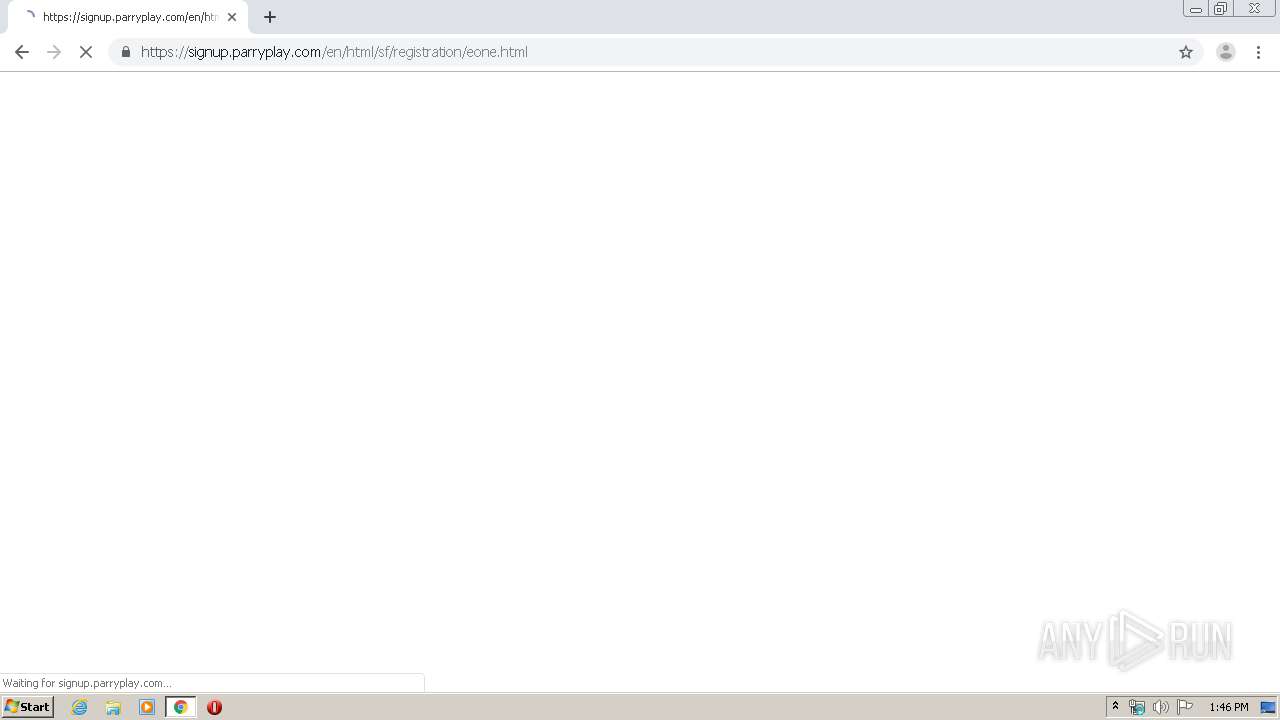
2580 | chrome.exe | GET | — | 185.128.239.39:80 | http://watch-hd-parks-and-rec-special-torrent-file.over-blog.com/ | FR | — | — | suspicious |
2580 | chrome.exe | GET | — | 185.128.239.53:80 | http://assets.over-blog-kiwi.com/b/blog/bundles/overblogblogblog/js/ads.js?v1.4.8.0 | FR | — | — | whitelisted |
2580 | chrome.exe | GET | — | 185.128.239.80:80 | http://resize.over-blog.com/800x500-ct.jpg?https://i1.wp.com/image.tmdb.org/t/p/w500/nOqZfjoY4XfryYIka1nWRi5tnIr.jpg | FR | — | — | whitelisted |
2580 | chrome.exe | GET | 200 | 185.128.239.53:80 | http://assets.over-blog-kiwi.com/b/blog/bundles/overblogblogblog/css/ob-style.css?v1.4.8.0 | FR | text | 30.7 Kb | whitelisted |
2580 | chrome.exe | GET | 200 | 185.128.239.53:80 | http://assets.over-blog-kiwi.com/b/blog/bundles/overblogblogblog/js/h.js?v1.4.8.0 | FR | text | 3.82 Kb | whitelisted |
2580 | chrome.exe | GET | 200 | 172.217.21.234:80 | http://fonts.googleapis.com/css?family=Open%20Sans:400,700 | US | text | 642 b | whitelisted |
2580 | chrome.exe | GET | 200 | 185.128.239.53:80 | http://assets.over-blog-kiwi.com/b/blog/build/main.d1b414d0.js | FR | text | 23.2 Kb | whitelisted |
2580 | chrome.exe | GET | 200 | 185.128.239.80:80 | http://resize.over-blog.com/100x100-ct.jpg?http://assets.over-blog.com/t/cedistic/camera.png | FR | image | 1.37 Kb | whitelisted |
2580 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAy%2BK8lPT%2B%2Fr4u1gFxGeJoE%3D | US | der | 471 b | whitelisted |
2580 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2580 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 185.128.239.39:80 | — | L'Odyssee Interactive Jeuxvideo.com, SAS | FR | unknown |
— | — | 104.16.132.229:80 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
2580 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.21.234:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 185.128.239.53:80 | assets.over-blog-kiwi.com | L'Odyssee Interactive Jeuxvideo.com, SAS | FR | unknown |
— | — | 185.128.239.53:80 | assets.over-blog-kiwi.com | L'Odyssee Interactive Jeuxvideo.com, SAS | FR | unknown |
2580 | chrome.exe | 185.114.5.132:443 | static1.webedia.fr | L'Odyssee Interactive Jeuxvideo.com, SAS | FR | unknown |
2580 | chrome.exe | 194.126.157.29:443 | w.estat.com | Mediametrie-estat | FR | suspicious |
— | — | 185.128.239.54:80 | connect.over-blog.com | L'Odyssee Interactive Jeuxvideo.com, SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
watch-hd-parks-and-rec-special-torrent-file.over-blog.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
assets.over-blog-kiwi.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
cdn.linearicons.com |
| shared |
fonts.googleapis.com |
| whitelisted |
connect.over-blog.com |
| whitelisted |
static1.webedia.fr |
| unknown |
w.estat.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2580 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2580 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2580 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |