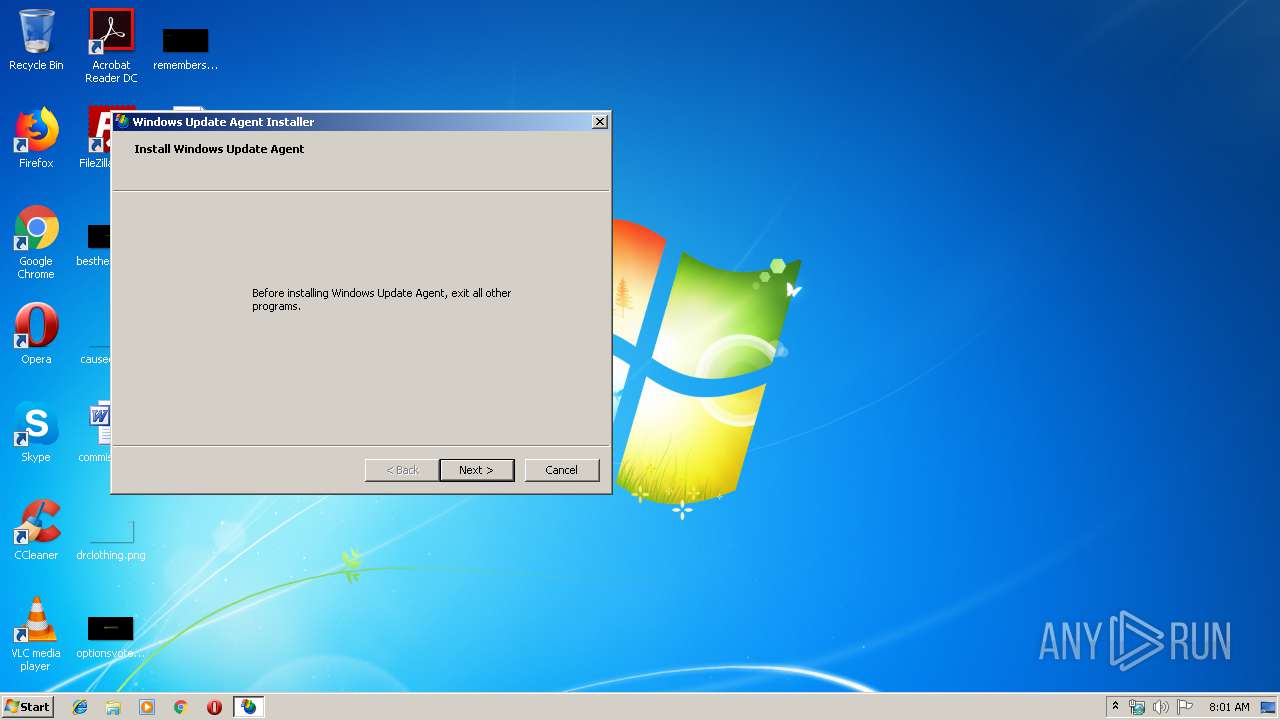
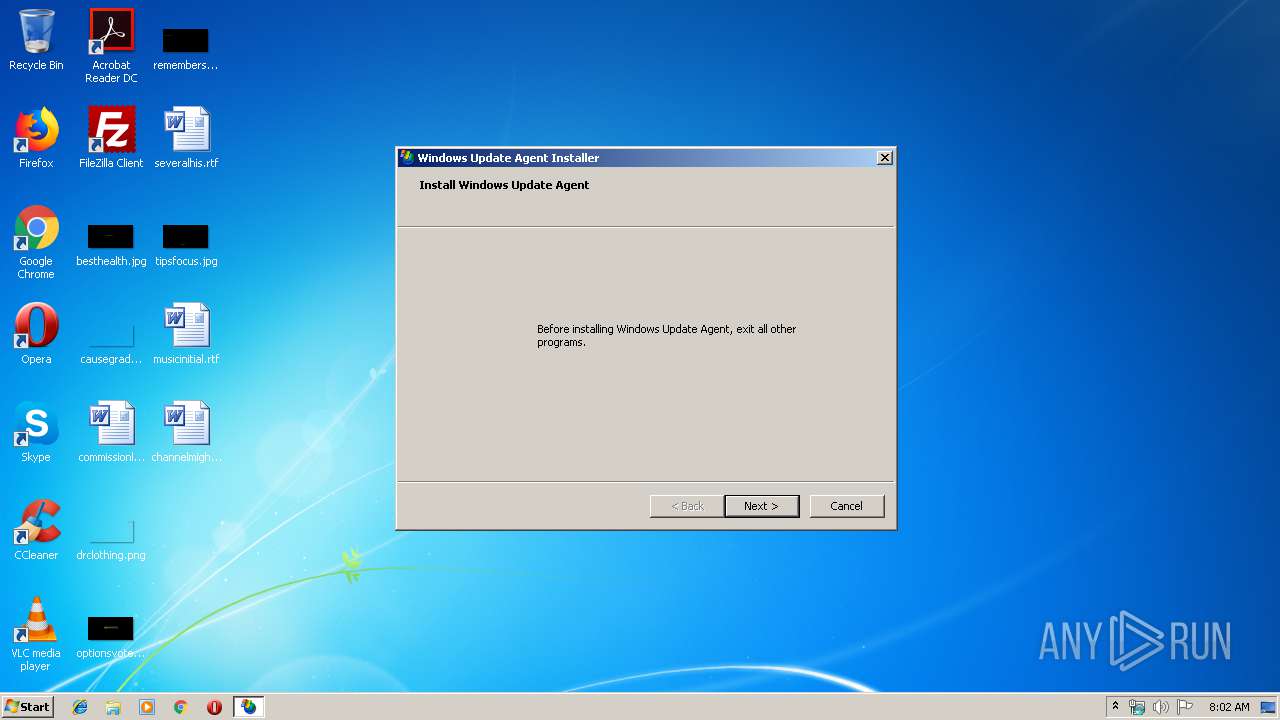
| download: | WindowsUpdateAgent30-x86.exe |
| Full analysis: | https://app.any.run/tasks/62303f3f-9181-47af-8237-61c40fa1f71a |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 07:01:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F723820B8656E82958FA7ED854A7EEFE |
| SHA1: | 50186EC913A4896A92D72E5E5384693BF3A71182 |
| SHA256: | B2512E0C2786F72ED41559580261C782A13FB5EA7FE23878873F83ECAEEEC25F |
| SSDEEP: | 196608:JCYrZoYags7mTwGklC0ZLeTWrDccd4sieKCfO7:JCgZJdHkl7ZJd4sVKJ7 |
MALICIOUS
Application was dropped or rewritten from another process
- wusetup.exe (PID: 3596)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 2816)
- DrvInst.exe (PID: 3860)
Searches for installed software
- wusetup.exe (PID: 3596)
- DllHost.exe (PID: 2816)
Executed as Windows Service
- vssvc.exe (PID: 4016)
Executable content was dropped or overwritten
- WindowsUpdateAgent30-x86.exe (PID: 2200)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 4016)
Dropped object may contain Bitcoin addresses
- WindowsUpdateAgent30-x86.exe (PID: 2200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | MS generic-sfx Cabinet File Unpacker (32/64bit MSCFU) (82.5) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (7.3) |
| .exe | | | Win64 Executable (generic) (6.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.5) |
| .exe | | | Win32 Executable (generic) (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2005:06:28 18:55:01+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 31232 |
| InitializedDataSize: | 72704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5a45 |
| OSVersion: | 5.2 |
| ImageVersion: | 5.2 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.2.29.0 |
| ProductVersionNumber: | 6.2.29.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Self-Extracting Cabinet |
| FileVersion: | 6.2.0029.0 (SRV03_QFE.031113-0918) |
| InternalName: | SFXCAB.EXE |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | SFXCAB.EXE |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.2.0029.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Jun-2005 16:55:01 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Self-Extracting Cabinet |
| FileVersion: | 6.2.0029.0 (SRV03_QFE.031113-0918) |
| InternalName: | SFXCAB.EXE |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | SFXCAB.EXE |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.2.0029.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 28-Jun-2005 16:55:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00007982 | 0x00007A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61008 |
.data | 0x0000A000 | 0x000110D4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.513491 |
.rsrc | 0x0001C000 | 0x00000988 | 0x0066CE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99967 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.5279 | 904 | UNKNOWN | English - United States | RT_VERSION |
100 | 3.0946 | 282 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.9591 | 224 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
msvcrt.dll |
ntdll.dll |
Total processes
44
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2200 | "C:\Users\admin\AppData\Local\Temp\WindowsUpdateAgent30-x86.exe" | C:\Users\admin\AppData\Local\Temp\WindowsUpdateAgent30-x86.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Self-Extracting Cabinet Exit code: 0 Version: 6.2.0029.0 (SRV03_QFE.031113-0918) Modules
| |||||||||||||||
| 2816 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3596 | c:\95f2a22b31ec5089dcb17509054f\wusetup.exe | c:\95f2a22b31ec5089dcb17509054f\wusetup.exe | — | WindowsUpdateAgent30-x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Setup Exit code: 0 Version: 7.4.7600.226 (winmain_wtr_wsus3sp2(wmbla).090806-1834) Modules
| |||||||||||||||
| 3700 | "C:\Users\admin\AppData\Local\Temp\WindowsUpdateAgent30-x86.exe" | C:\Users\admin\AppData\Local\Temp\WindowsUpdateAgent30-x86.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Self-Extracting Cabinet Exit code: 3221226540 Version: 6.2.0029.0 (SRV03_QFE.031113-0918) Modules
| |||||||||||||||
| 3860 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot22" "" "" "695c3f483" "00000000" "000005B8" "000002D4" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4016 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
340
Read events
167
Write events
172
Delete events
1
Modification events
| (PID) Process: | (3596) wusetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000084BBD8D46E68D5010C0E0000E00D0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3596) wusetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000084BBD8D46E68D5010C0E0000E00D0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4016) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000941938D56E68D501B00F0000380D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4016) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000941938D56E68D501B00F000020080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4016) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000941938D56E68D501B00F000010090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4016) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000941938D56E68D501B00F000018090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3596) wusetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 24 | |||
| (PID) Process: | (3596) wusetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000D22D2CD56E68D5010C0E0000E00D0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3596) wusetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D22D2CD56E68D5010C0E0000840C0000E80300000100000000000000000000003883AA308A84294EBE2CCBF77A853ED70000000000000000 | |||
| (PID) Process: | (3596) wusetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000560544D56E68D5010C0E0000840C0000E80300000000000000000000000000003883AA308A84294EBE2CCBF77A853ED70000000000000000 | |||
Executable files
157
Suspicious files
7
Text files
80
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2200 | WindowsUpdateAgent30-x86.exe | C:\95f2a22b31ec5089dcb17509054f\WUClient-SelfUpdate-ActiveX.cab | compressed | |
MD5:232CCCBB86D2AFAE9B60C42D23D885B9 | SHA256:F2D9F27A725B6AEC105B42D434EFA683D3B8A85F87B87A47A846703C5166163A | |||
| 2200 | WindowsUpdateAgent30-x86.exe | C:\95f2a22b31ec5089dcb17509054f\cdm.dll | executable | |
MD5:5627047F35EA56A7ED8E513434B45D6C | SHA256:1A055C9D9C99DA731AC2F4AABA13B28ABD1CC6E45196FB52298B6164D907A9BD | |||
| 2200 | WindowsUpdateAgent30-x86.exe | C:\95f2a22b31ec5089dcb17509054f\WUClient-SelfUpdate-Core-TopLevel.cab | compressed | |
MD5:FB59D11E7CE0880CD564CFE1E60933C0 | SHA256:92514168119F26A7149FEB0C01C5DF39EC75700DDE193EFCBF5644DD992A0942 | |||
| 2200 | WindowsUpdateAgent30-x86.exe | C:\95f2a22b31ec5089dcb17509054f\WUClient-SelfUpdate-Aux-TopLevel.cab | compressed | |
MD5:0A0FE198EFE05D6FA8F4DC48DD8CAAD3 | SHA256:12F355D099956D93817AC4F249242FDA428F9FED7B03B03438D019384D3F2101 | |||
| 2200 | WindowsUpdateAgent30-x86.exe | C:\95f2a22b31ec5089dcb17509054f\wuapi.dll.mui_ar | executable | |
MD5:FCD9F6A1575F561175763CF5BADDC68B | SHA256:57D7E569464FFEFDF9BAAD3F90FEE6F29CAA648EB1513A72CA1C87E8C8A4E35F | |||
| 2200 | WindowsUpdateAgent30-x86.exe | C:\95f2a22b31ec5089dcb17509054f\msxml3.dll | executable | |
MD5:E7A3FCB568797785750308DD6DB2BDC0 | SHA256:E56FAAC4EA3C7C392FDE178851599EE4DF244B0AF743F8D2239EB093704AFA71 | |||
| 2200 | WindowsUpdateAgent30-x86.exe | C:\95f2a22b31ec5089dcb17509054f\wuapi.dll.mui_el | executable | |
MD5:9B5BB7DDF4BAD4B06138448DA6DE89FB | SHA256:72AB1B6891B08D1CC781E58F0CDBE11C7DF34942B241E34EE165224F4C6EE422 | |||
| 2200 | WindowsUpdateAgent30-x86.exe | C:\95f2a22b31ec5089dcb17509054f\wuapi.dll.mui_fr | executable | |
MD5:813C46354D3771E829B5350611B3F2DE | SHA256:B0ACD1E2968F84D2128BAE0CB304B0D4FA92BD45E98F8C64CF5EBA0AA5523ECC | |||
| 2200 | WindowsUpdateAgent30-x86.exe | C:\95f2a22b31ec5089dcb17509054f\wuapi.dll.mui_de | executable | |
MD5:4D8E7E2AAB4DC36E3C4E91E4CD5F020F | SHA256:49F4698BB700B07F351F5A9EF89AEECECC93077D5CFB5AE7FD72F4307F69EB18 | |||
| 2200 | WindowsUpdateAgent30-x86.exe | C:\95f2a22b31ec5089dcb17509054f\wuapi.dll.mui_fi | executable | |
MD5:7566307C21A344FDDBB52B407A5D410F | SHA256:D428743C5E7258B60903A1AC27962D8FCA4F3E8D2391F5A36BF49664B6848670 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report