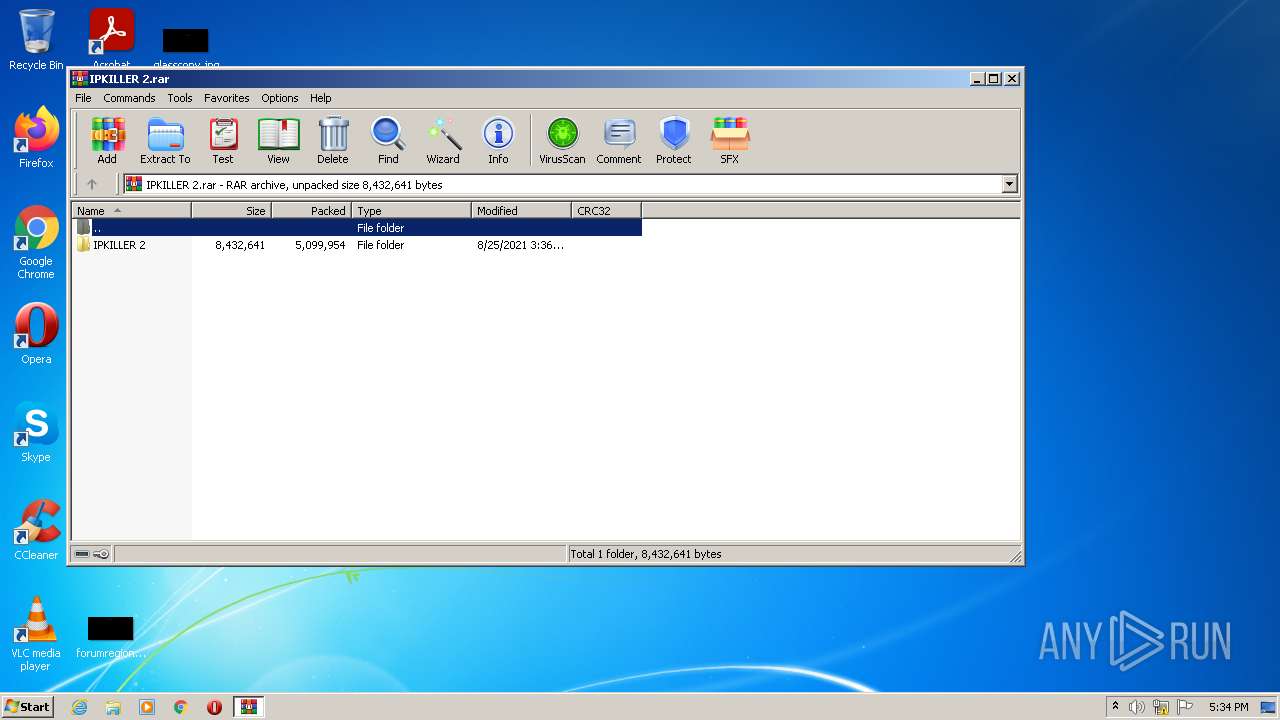
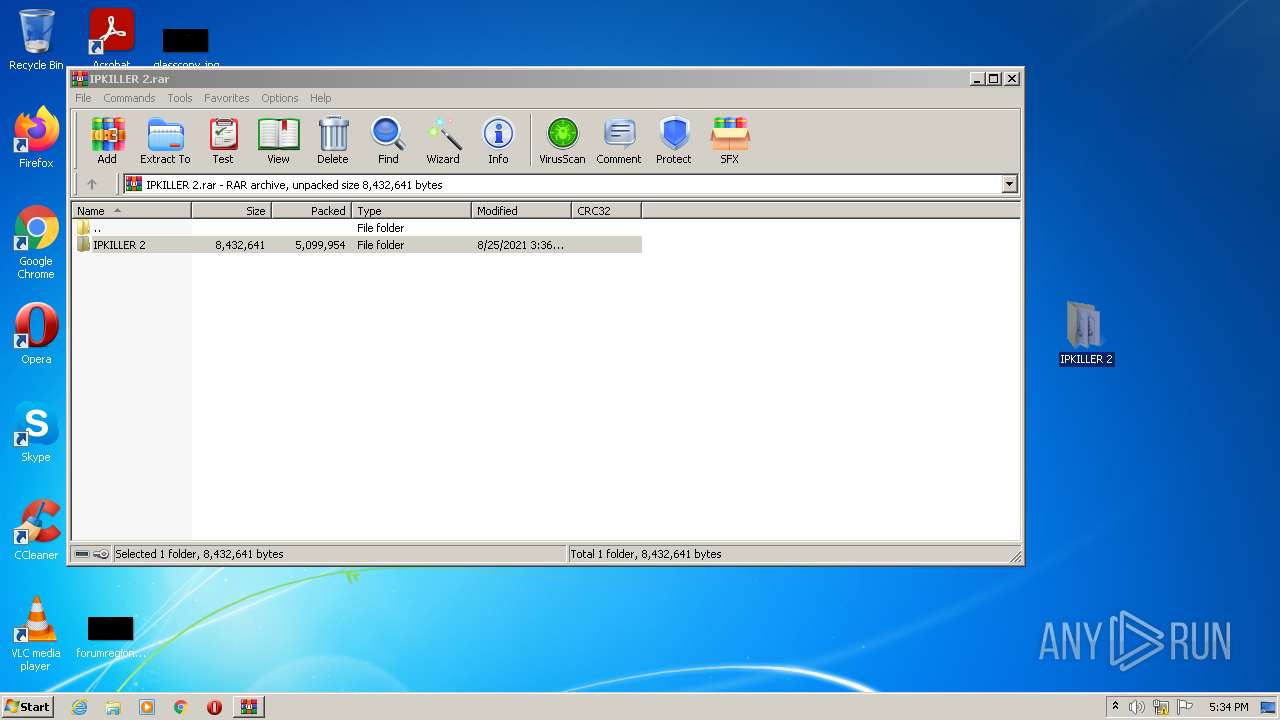
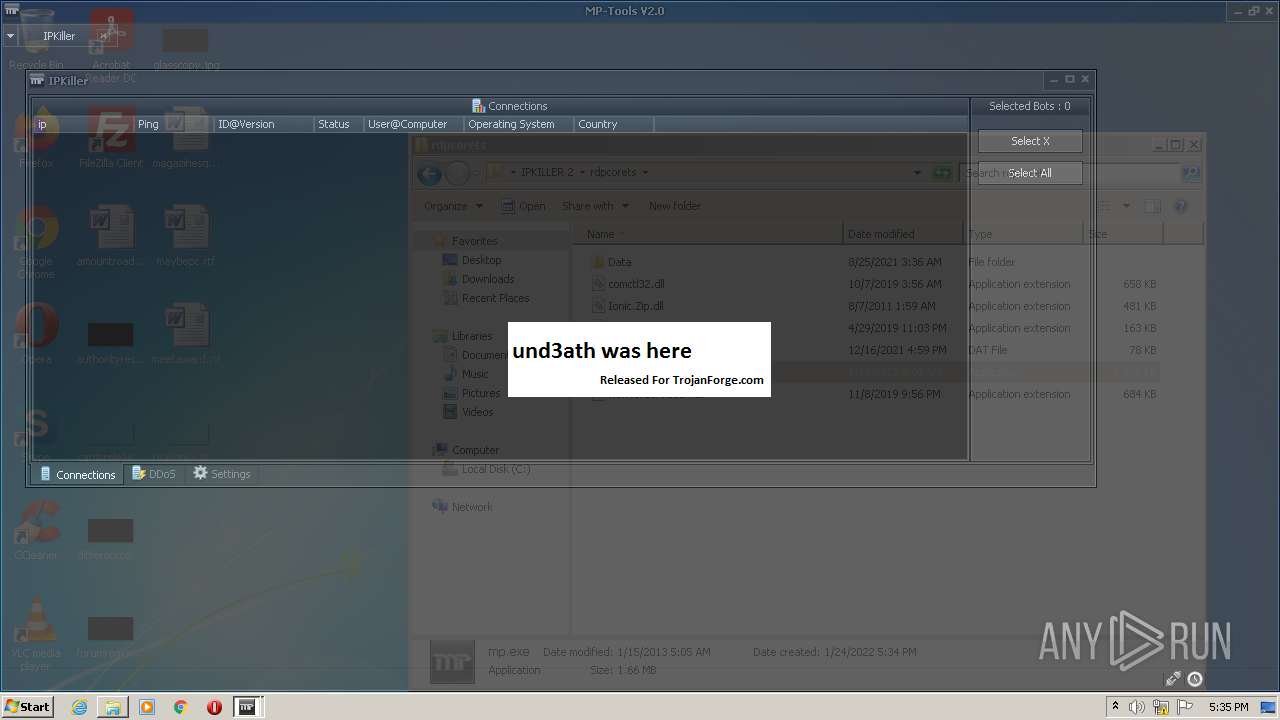
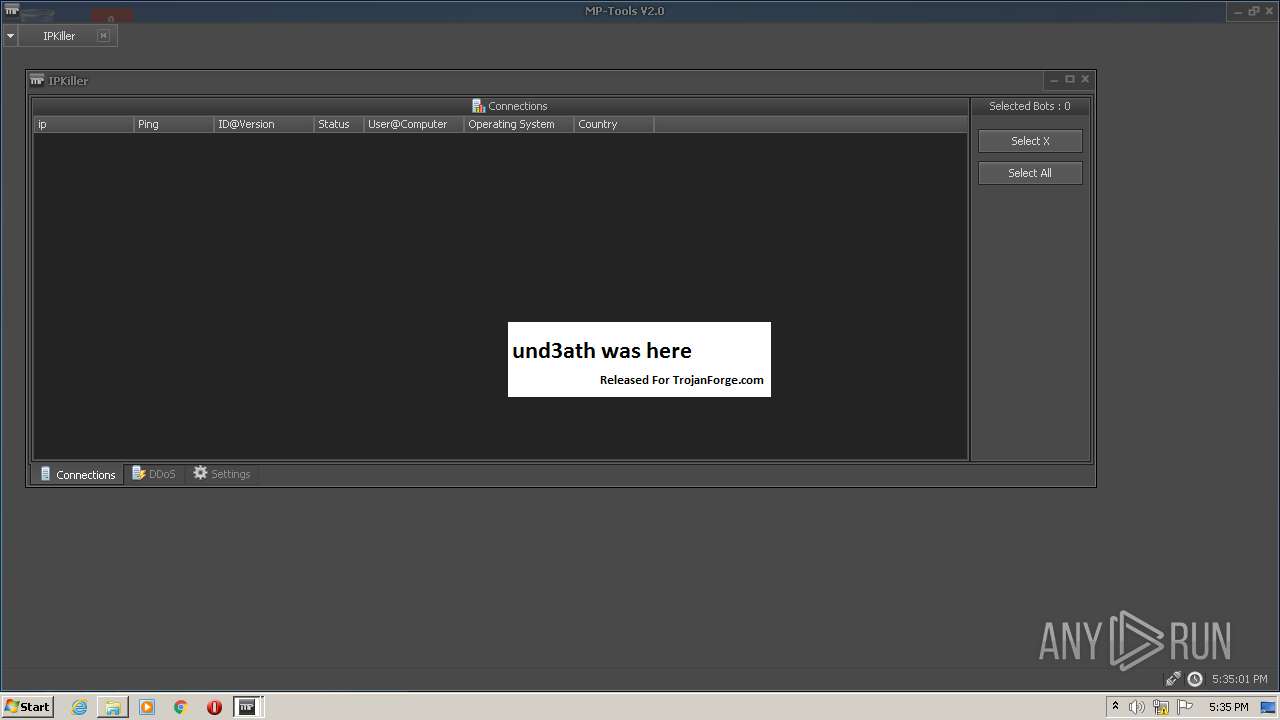
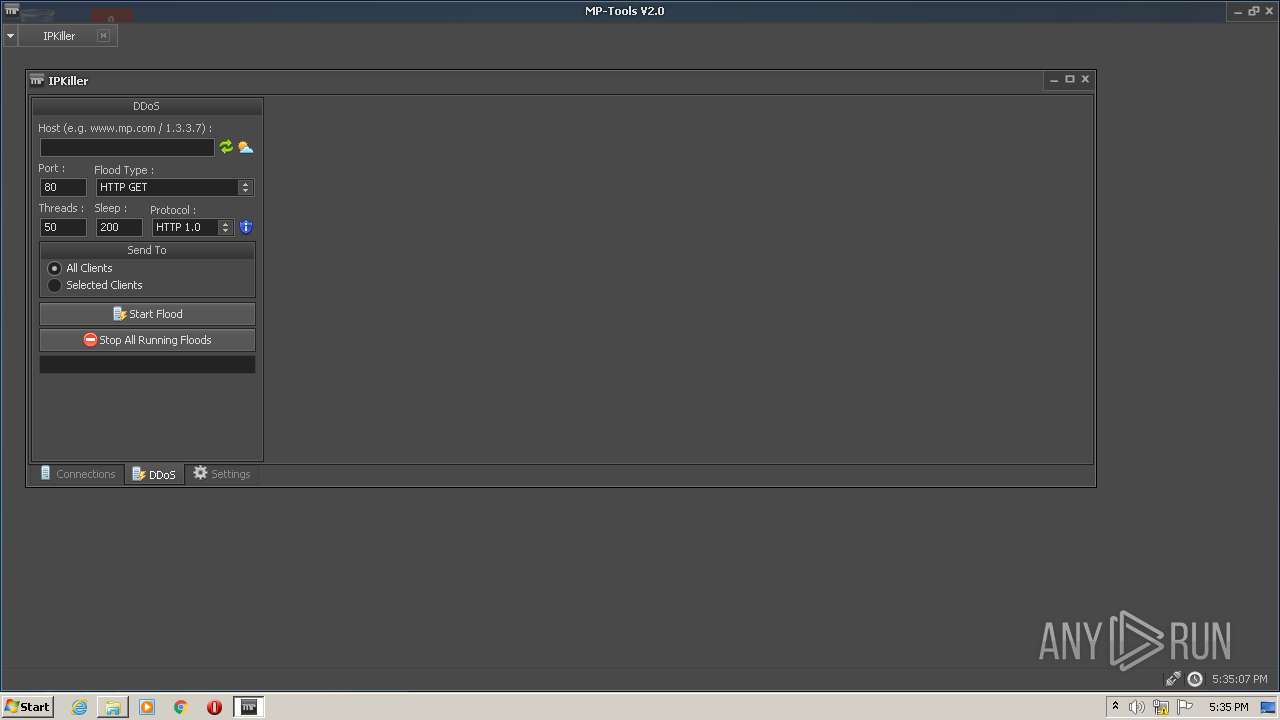
| File name: | IPKILLER 2.rar |
| Full analysis: | https://app.any.run/tasks/9d193d4b-2f0e-4a68-8b86-d94134992e1f |
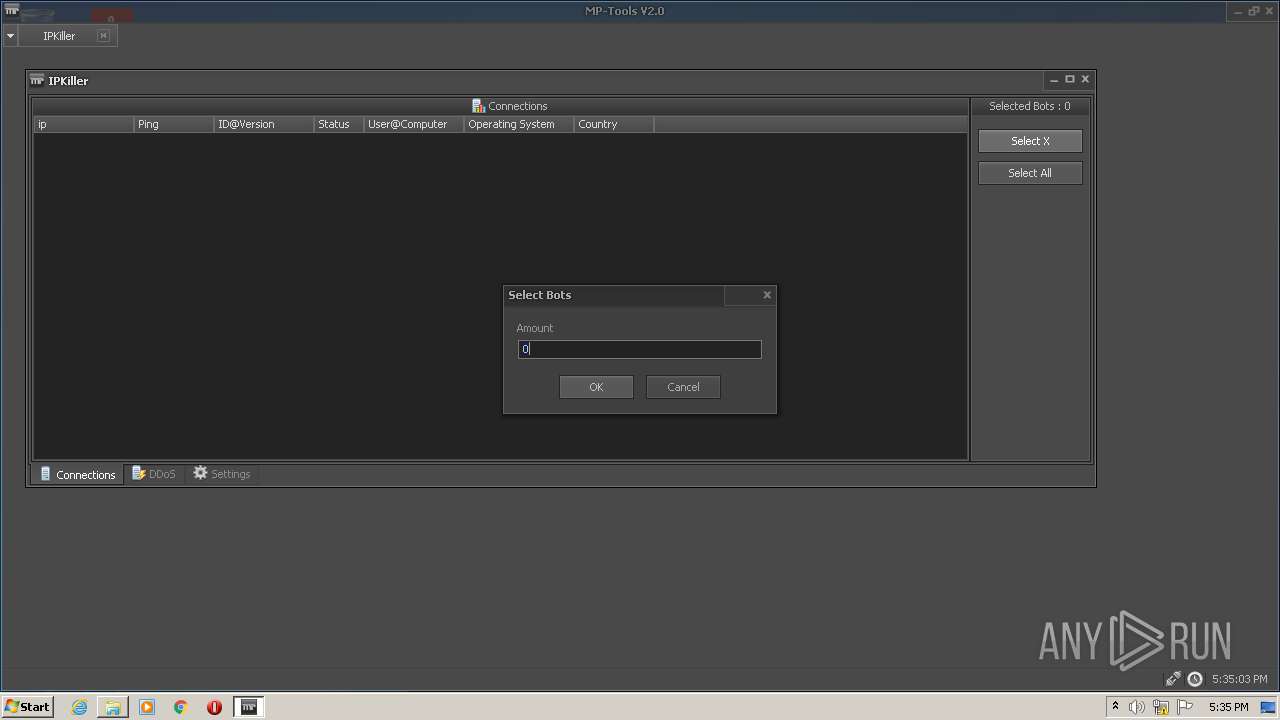
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 17:34:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | C7C2159E227067FBEC50B9D46E20245B |
| SHA1: | 3652C3A40C010F412910DE57634FCFF98C1E9CBE |
| SHA256: | B24C82C0B5F41C326FB7FB808398B2DDD5672BDCFC7DB9B9FC3ECF752AC2F507 |
| SSDEEP: | 98304:T2EwnfuQzvUAyB3BocmQ8Q6hIQzbJRUAXvO6a2rW4vPbZYPkPx:T2ES2QYAyjqR1IQPJ2AXrfXbZYcJ |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3712)
Application was dropped or rewritten from another process
- mp.exe (PID: 2604)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 3636)
- mp.exe (PID: 2604)
Checks supported languages
- WinRAR.exe (PID: 3636)
- mp.exe (PID: 2604)
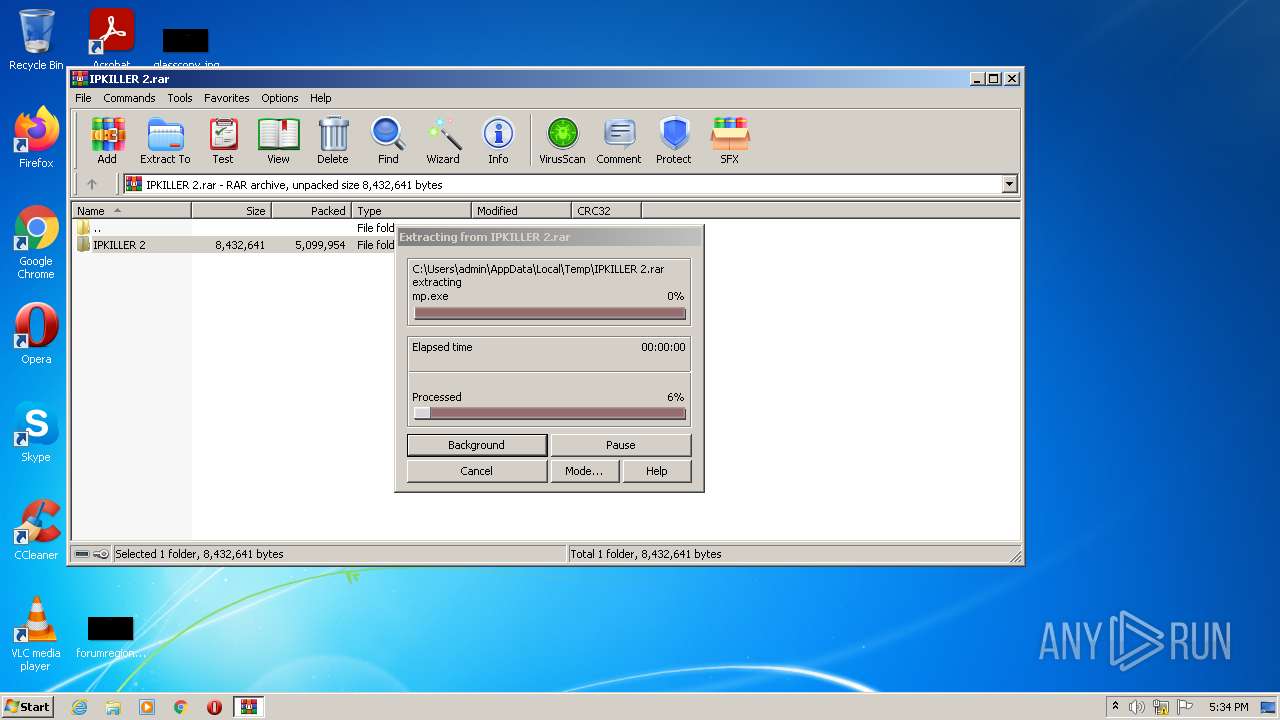
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3636)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3636)
Drops a file with too old compile date
- WinRAR.exe (PID: 3636)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3636)
INFO
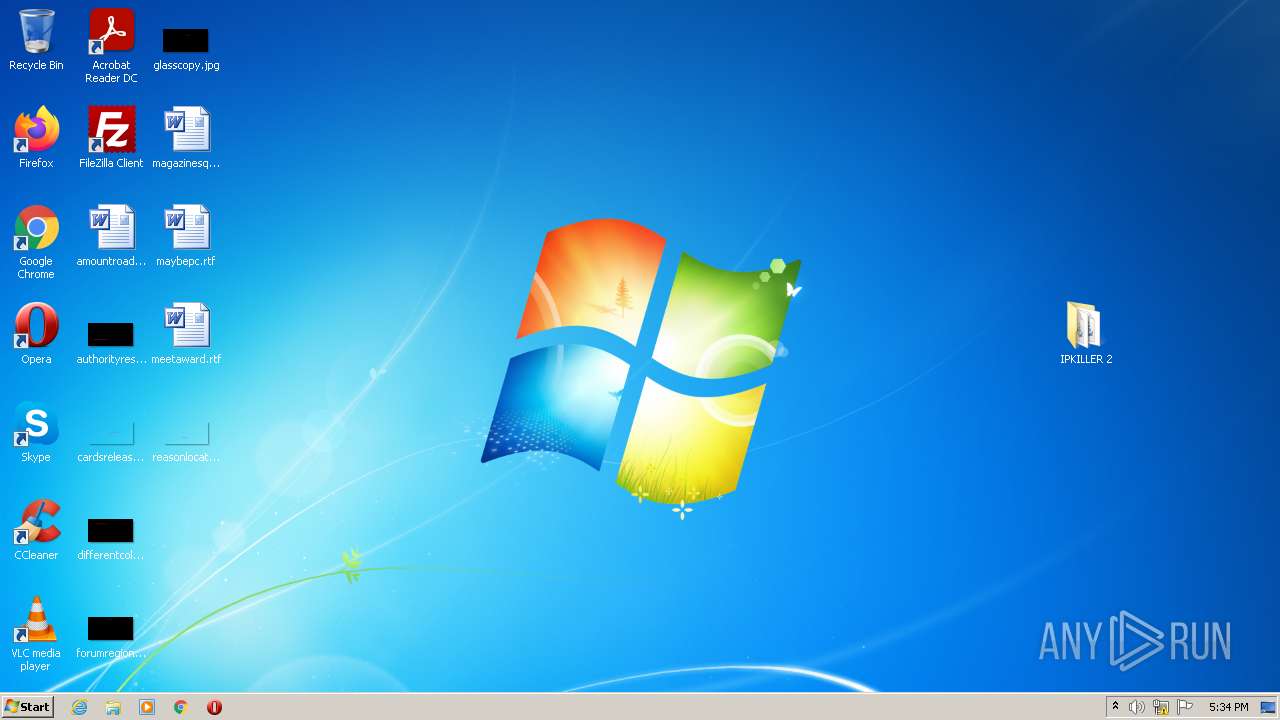
Manual execution by user
- mp.exe (PID: 2604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
36
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
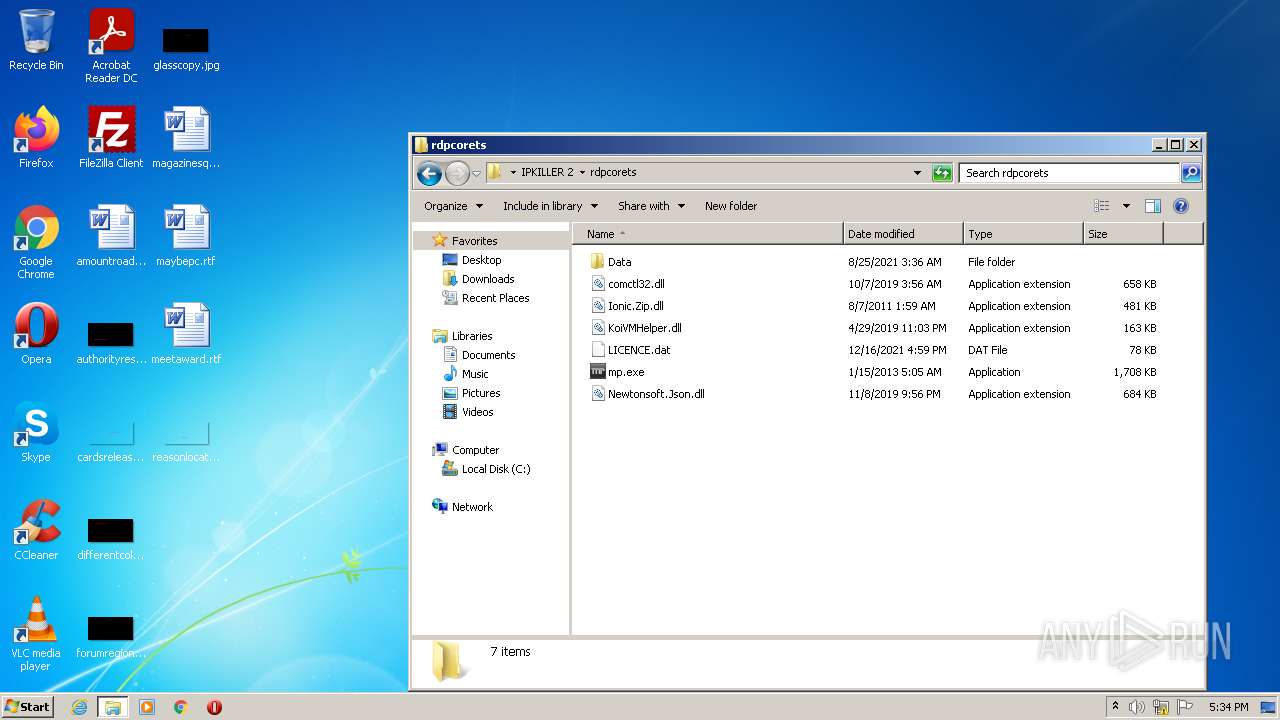
| 2604 | "C:\Users\admin\Desktop\IPKILLER 2\rdpcorets\mp.exe" | C:\Users\admin\Desktop\IPKILLER 2\rdpcorets\mp.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3636 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\IPKILLER 2.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3712 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
Total events
2 037
Read events
2 016
Write events
21
Delete events
0
Modification events
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\IPKILLER 2.rar | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
10
Suspicious files
3
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
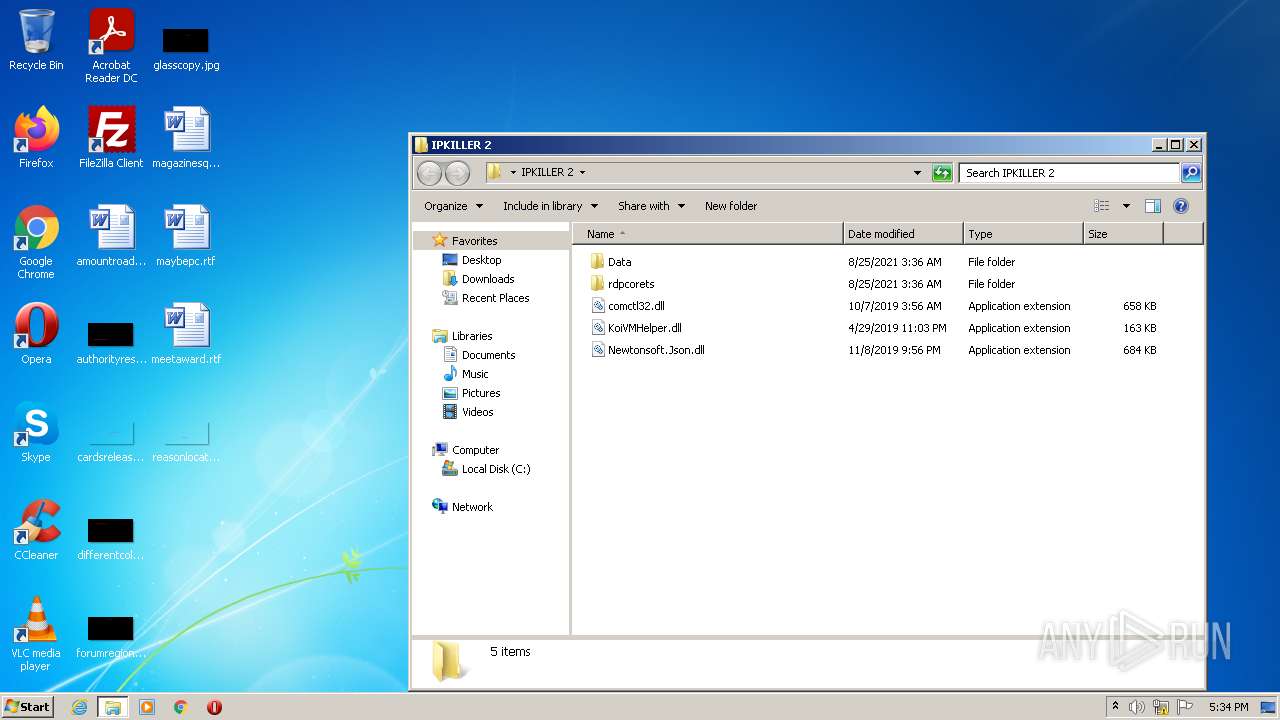
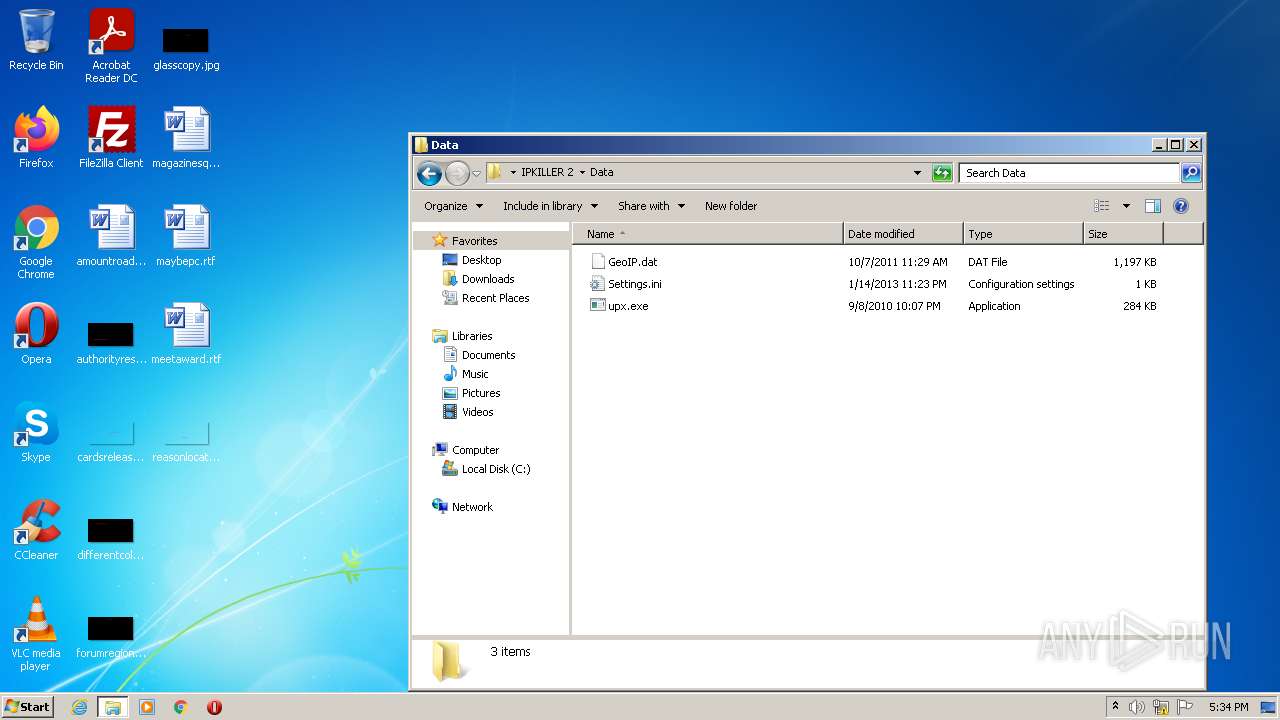
| 3636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3636.34517\IPKILLER 2\Data\upx.exe | executable | |
MD5:308F709A8F01371A6DD088A793E65A5F | SHA256:C0F9FAFFDF14AB2C853880457BE19A237B10F8986755F184ECFE21670076CB35 | |||
| 3636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3636.34517\IPKILLER 2\Data\GeoIP.dat | binary | |
MD5:C6D371AC18598838B61750E874E64400 | SHA256:03B4F8ACA1E4AB4FE526997FDFBE70FDC2CCA84FD95728716F7653173B48130B | |||
| 3636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3636.34517\IPKILLER 2\Data\Settings.ini | text | |
MD5:609316B918A9AA02F455D320A98550EA | SHA256:5153800E4E679B522B834EACC9DE172BBFFAD30230BF00C9A8EDF4046807EFA5 | |||
| 3636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3636.34517\IPKILLER 2\rdpcorets\Ionic.Zip.dll | executable | |
MD5:F6933BF7CEE0FD6C80CDF207FF15A523 | SHA256:17BB0C9BE45289A2BE56A5F5A68EC9891D7792B886E0054BC86D57FE84D01C89 | |||
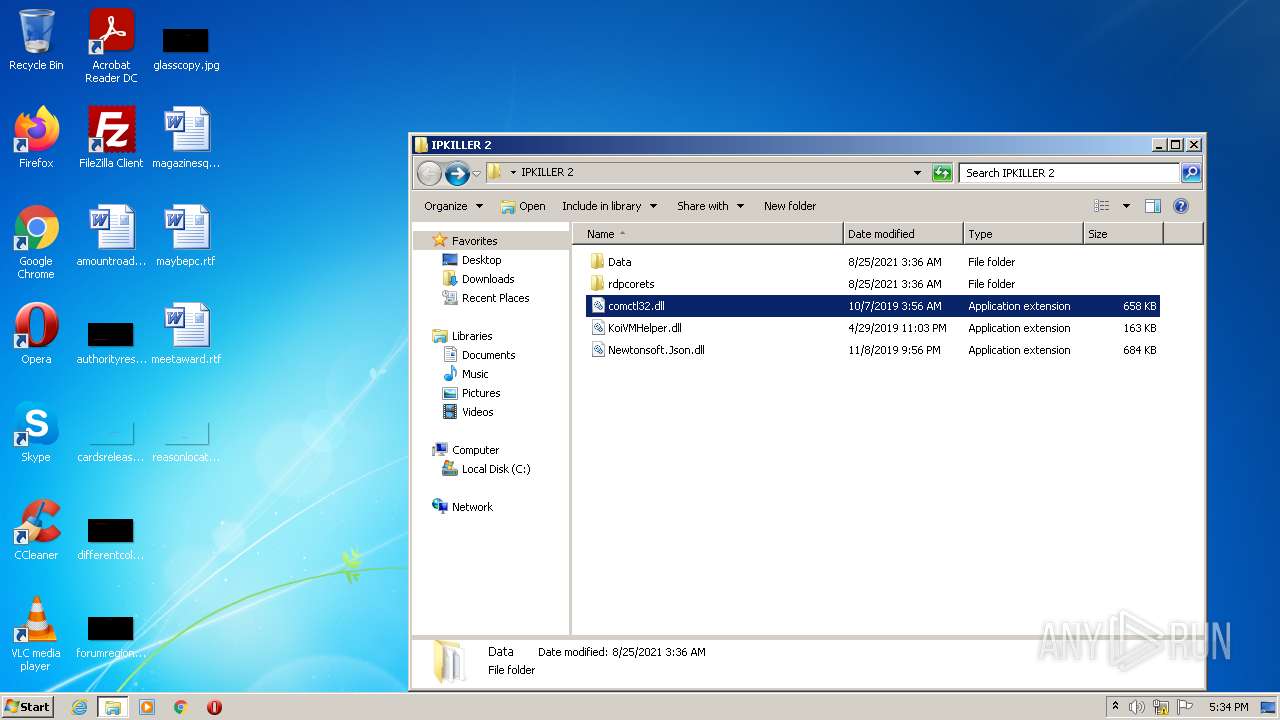
| 3636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3636.34517\IPKILLER 2\rdpcorets\comctl32.dll | executable | |
MD5:384D0D60981557B675E0EA94ECE3AB26 | SHA256:153DC459A73E102F60E62162F21B40F2CF666A9039B69D84DF3CFFB1EEEDEF66 | |||
| 3636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3636.34517\IPKILLER 2\rdpcorets\KoiVMHelper.dll | executable | |
MD5:DE0AB4C6D7B794CF05D92925C89B11B2 | SHA256:D2A8A294F524C54D00A3087946BFE08675C16ACCC93F2FBC2BC21EE67E598E36 | |||
| 3636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3636.34517\IPKILLER 2\Newtonsoft.Json.dll | executable | |
MD5:6815034209687816D8CF401877EC8133 | SHA256:7F912B28A07C226E0BE3ACFB2F57F050538ABA0100FA1F0BF2C39F1A1F1DA814 | |||
| 3636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3636.34517\IPKILLER 2\KoiVMHelper.dll | executable | |
MD5:DE0AB4C6D7B794CF05D92925C89B11B2 | SHA256:D2A8A294F524C54D00A3087946BFE08675C16ACCC93F2FBC2BC21EE67E598E36 | |||
| 3636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3636.34517\IPKILLER 2\rdpcorets\Data\GeoIP.dat | binary | |
MD5:C6D371AC18598838B61750E874E64400 | SHA256:03B4F8ACA1E4AB4FE526997FDFBE70FDC2CCA84FD95728716F7653173B48130B | |||
| 3636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3636.34517\IPKILLER 2\comctl32.dll | executable | |
MD5:384D0D60981557B675E0EA94ECE3AB26 | SHA256:153DC459A73E102F60E62162F21B40F2CF666A9039B69D84DF3CFFB1EEEDEF66 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report