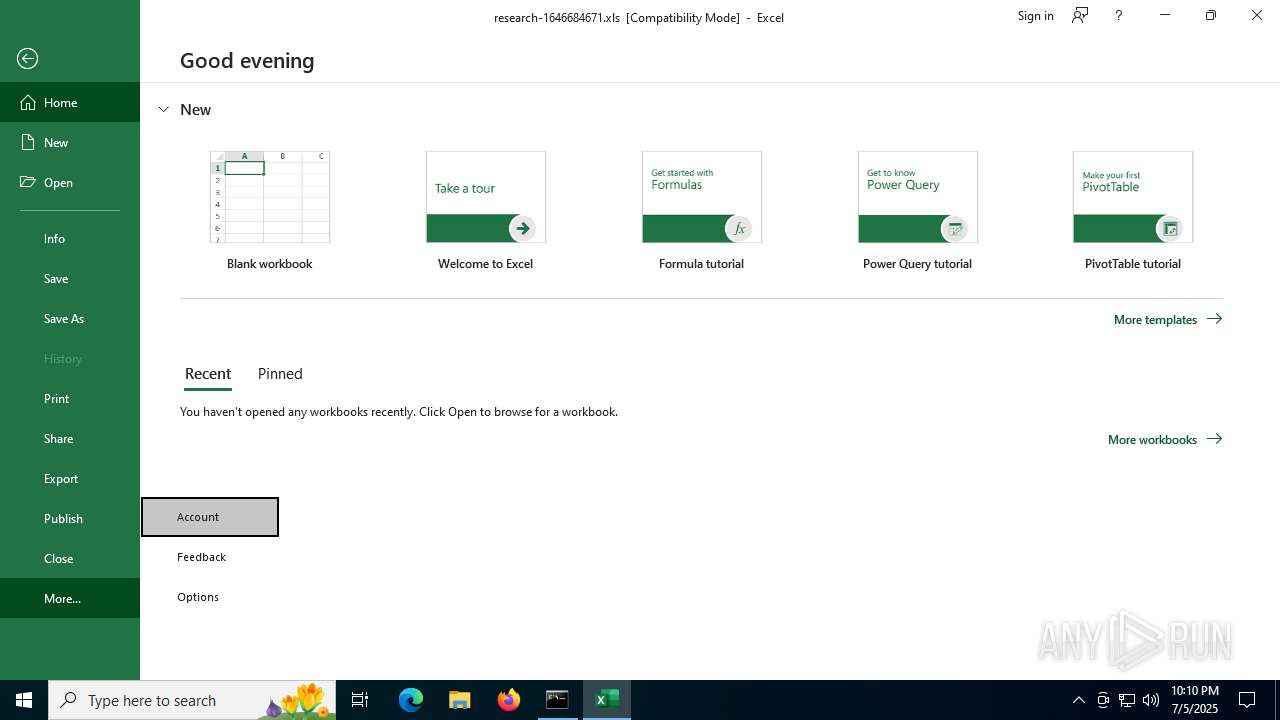
| File name: | research-1646684671.xls |
| Full analysis: | https://app.any.run/tasks/c0e403fc-5649-42ae-9be7-4cd740165651 |
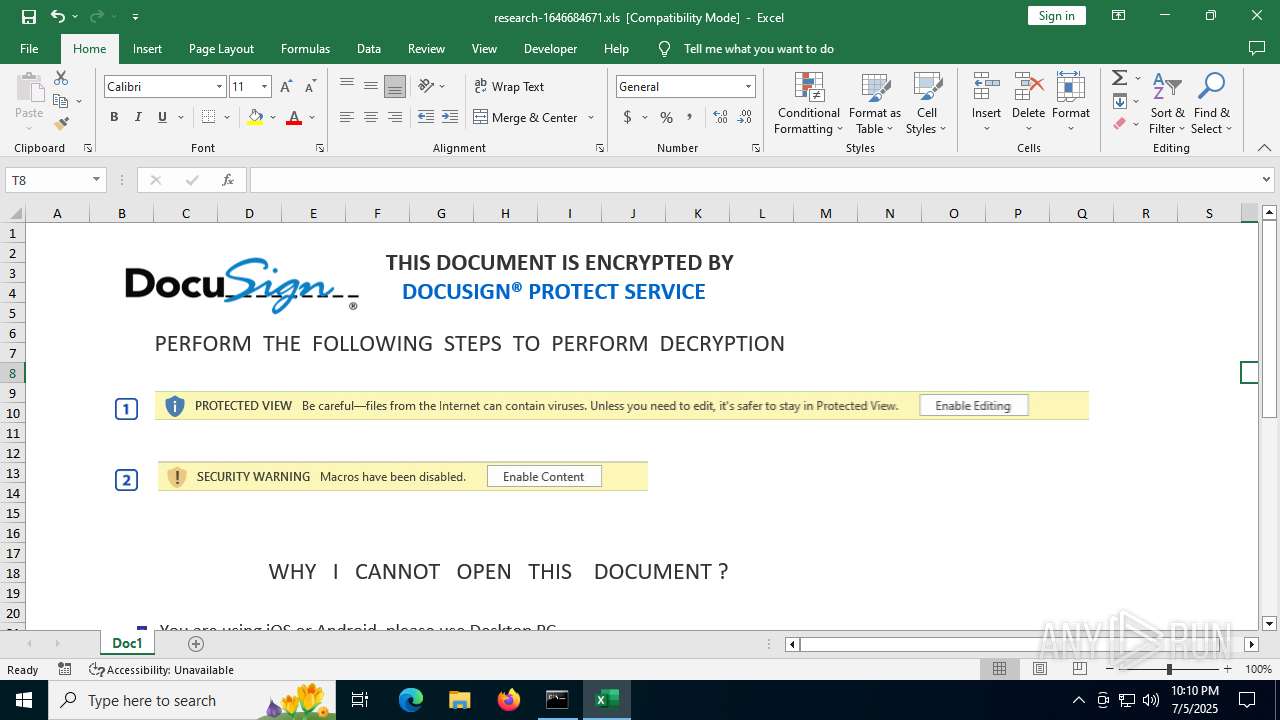
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2025, 22:09:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Last Saved By: Amanda, Name of Creating Application: Microsoft Excel, Create Time/Date: Fri Jun 5 18:17:20 2015, Last Saved Time/Date: Sun Jun 13 09:24:55 2021, Security: 0 |
| MD5: | 927005139A0BE61EFE849C715D875DD2 |
| SHA1: | 0F6A91916941D85B69E5320873A5D1C45055BC4E |
| SHA256: | B23491EDE17F9A5B7D6AD27D3051A2224C214A5AFA2139E5147BD26319577F85 |
| SSDEEP: | 6144:Hknl9oBdySAx76F6XeyTVtW/9Ny9ABnl5/PBgxOHjuM9Mq:jl5/WxIjL |
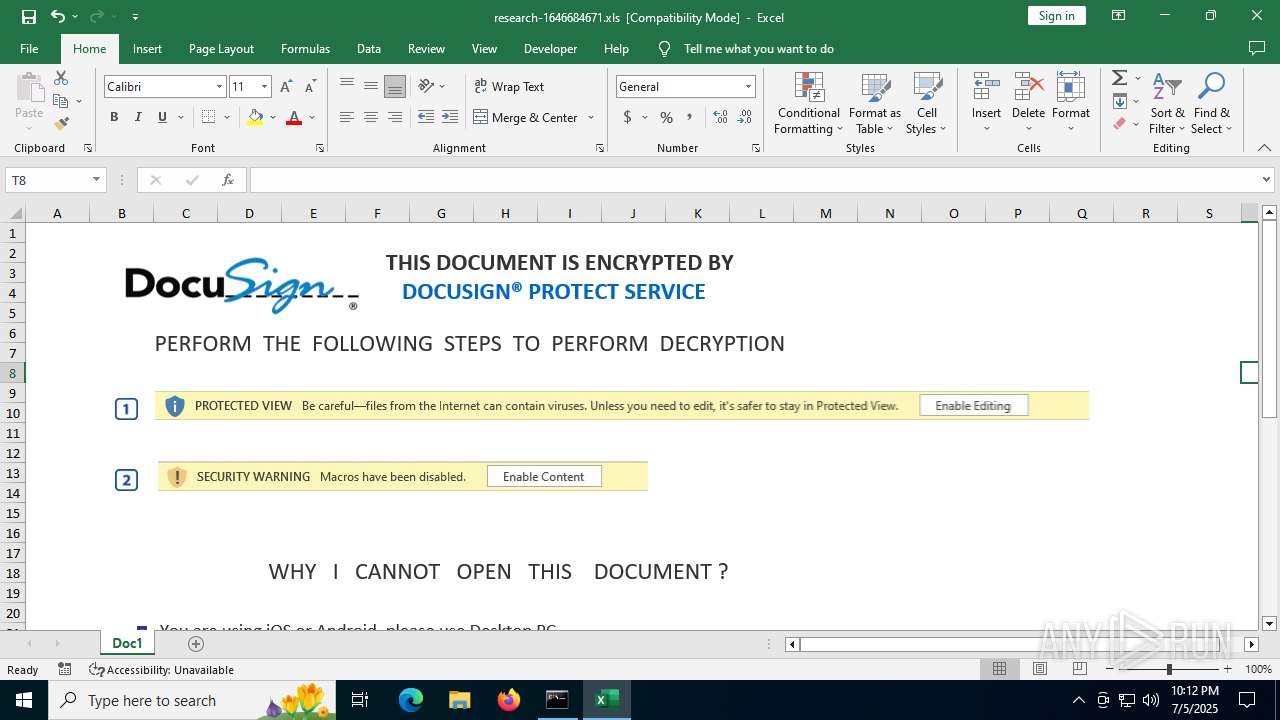
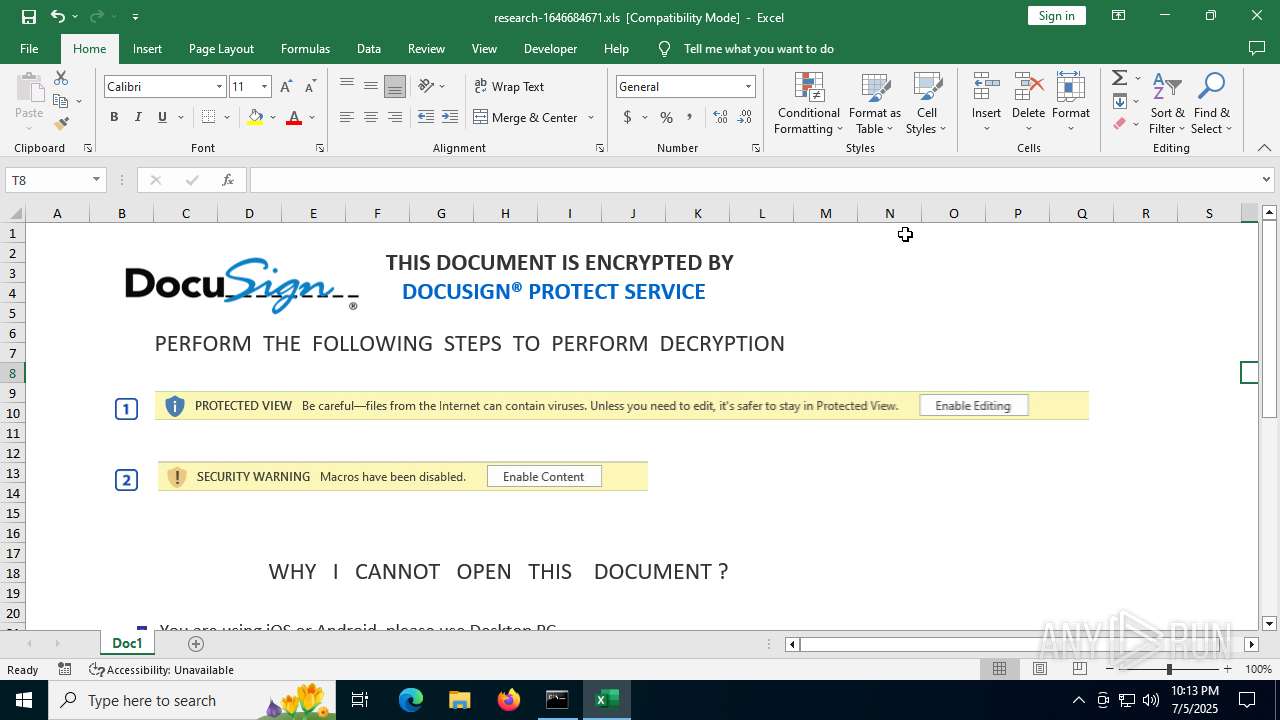
MALICIOUS
Calls Win API functions (MACROS)
- EXCEL.EXE (PID: 3872)
Registers / Runs the DLL via REGSVR32.EXE
- EXCEL.EXE (PID: 3872)
Unusual execution from MS Office
- EXCEL.EXE (PID: 3872)
SUSPICIOUS
Sets XML DOM element text (SCRIPT)
- splwow64.exe (PID: 7160)
INFO
Checks proxy server information
- slui.exe (PID: 32)
Reads the software policy settings
- slui.exe (PID: 32)
Reads security settings of Internet Explorer
- splwow64.exe (PID: 7160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| Author: | - |
|---|---|
| LastModifiedBy: | Amanda |
| Software: | Microsoft Excel |
| CreateDate: | 2015:06:05 18:17:20 |
| ModifyDate: | 2021:06:13 09:24:55 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
Total processes
149
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2632 | regsvr32 -s ..\iroto1.dll | C:\Windows\System32\regsvr32.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 3 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3872 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" "C:\Users\admin\AppData\Local\Temp\research-1646684671.xls" | C:\Program Files\Microsoft Office\root\Office16\EXCEL.EXE | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 3960 | regsvr32 -s ..\iroto.dll | C:\Windows\System32\regsvr32.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 3 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7100 | "C:\Windows\System32\cmd.exe" /k C:\Users\admin\AppData\Local\Temp\research-1646684671.xls | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7160 | C:\WINDOWS\splwow64.exe 8192 | C:\Windows\splwow64.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Print driver host for applications Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 510
Read events
9 089
Write events
391
Delete events
30
Modification events
| (PID) Process: | (7100) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.xls\OpenWithProgids |
| Operation: | write | Name: | Excel.Sheet.8 |
Value: | |||
| (PID) Process: | (7100) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {97E467B4-98C6-4F19-9588-161B7773D6F6} {886D8EEB-8CF2-4446-8D02-CDBA1DBDCF99} 0xFFFF |
Value: 0100000000000000BD51108DF9EDDB01 | |||
| (PID) Process: | (3872) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 1 |
Value: 01D014000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (3872) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\EXCEL\3872 |
| Operation: | write | Name: | 0 |
Value: 0B0E10A224B8D46E3135498346784DE7F1A738230046F8B6B88999BFFBED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511A01ED2120965007800630065006C002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (3872) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | /}! |
Value: 2F7D2100200F00000100000000000000C9E53291F9EDDB0100000000 | |||
| (PID) Process: | (3872) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Excel |
| Operation: | write | Name: | ImmersiveWorkbookDirtySentinel |
Value: 0 | |||
| (PID) Process: | (3872) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Excel |
| Operation: | write | Name: | ExcelPreviousSessionId |
Value: {D4B824A2-316E-4935-8346-784DE7F1A738} | |||
| (PID) Process: | (3872) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (3872) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (3872) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
Executable files
0
Suspicious files
14
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3872 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\7A574868-A5BF-4BDF-972F-51B6152E54E0 | xml | |
MD5:1C247B904684DE186E59A9600B7A4CBD | SHA256:953FBDF248FF47FB462A403C9D9DAD7EEB1F353A52039D81F8BFC18128AC8B1B | |||
| 3872 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Content\Anonymous\Insights.json | binary | |
MD5:27DE4610F1C60FB98C32ED04FC36DEBF | SHA256:2C18844DE2409E879FFA682F22620B24C08ACFEBC4C3334977C487DB1ABC8245 | |||
| 3872 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\936F10BC72DB0BC0181957BCF75D6817 | binary | |
MD5:4B78F92C14AFDFD84057ABCDA693B60F | SHA256:AEEE047AEA4D3F8584B1084A86A00C5A2292E8F7751A66C2F2050C5F9C10E9B3 | |||
| 3872 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\936F10BC72DB0BC0181957BCF75D6817 | binary | |
MD5:EB6BB0B956E7AFA12A997E1A2ACA29F3 | SHA256:8047BA8A85E52550D2497DA2C1596F9E32786E02DF0C67D2A6EA0C77A9D64414 | |||
| 3872 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\DTS\en-US{048BED7F-D470-4E8B-8F16-8B272335B00B}\{051A496F-9648-4144-AC6B-53E55E5058CC}f55c55a7-da9a-4c2f-92dd-8ff9898da780-mt170217a7-48cf-4ff0-9744-d702d9da30d2.png | image | |
MD5:37804E17E5A26C0386910F002A3D2B68 | SHA256:7BA110AA9A934605C16607AEFDA2CC65F8DBE326A027713E35E318C3A5F75B70 | |||
| 3872 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:AFF943D57E55EDA2F87FB8887534CD8C | SHA256:E0F790E1DB11601E714861BA2CEBE1CF4B295FB03E499E9B1623D194DDD556F9 | |||
| 3872 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\DTS\en-US{048BED7F-D470-4E8B-8F16-8B272335B00B}\{989C42BF-4F5B-491E-AC5D-982D01BBC8F2}4a338106-c311-4f96-9f1f-46c7bd18d2f2-mt1b288106-1def-439e-b4fd-20377786f140.png | image | |
MD5:76E73323E39193FA92E986FE8CABF623 | SHA256:2431B95E36F03F7D93B5EE8E4F00709F2F7133117DFF8F8C4E51ED820A7F02EF | |||
| 3872 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\DTS\en-US{048BED7F-D470-4E8B-8F16-8B272335B00B}\{FAF558C6-D73D-48B9-A972-BEC848C5B0C1}23777088-dfe8-49a7-9e8f-9eae94928477-mt0a0dd2ea-efdc-42f8-9f70-361ec709fd12.png | image | |
MD5:2DBD7E398283C10E5BF027DFAAC6B9C6 | SHA256:FF20B6C3433B4AE99C367A2210507F3D3F04C7FE3F044C3FB097349ABC2C33C9 | |||
| 3872 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Content\Anonymous\Insights.json.tmp | binary | |
MD5:27DE4610F1C60FB98C32ED04FC36DEBF | SHA256:2C18844DE2409E879FFA682F22620B24C08ACFEBC4C3334977C487DB1ABC8245 | |||
| 3872 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\DTS\en-US{048BED7F-D470-4E8B-8F16-8B272335B00B}\{9978CFAB-C935-437E-89AD-D512BE38869D}e5f69010-3152-4632-aecc-72cc19e02db7-mtb0da9805-3e8a-4e7b-bec3-69b0133a4394.png | image | |
MD5:3956E37AE7FDA175451D460E84CB30D9 | SHA256:CB4B7EE18A8E176CA4D0F298D3F6379F71F69A62AF5C33ED0C944C4F73418138 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
46
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3872 | EXCEL.EXE | GET | 200 | 104.18.21.213:80 | http://r11.c.lencr.org/29.crl | unknown | binary | 103 Kb | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
6320 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
3872 | EXCEL.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
856 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
856 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | ID | binary | 734 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4920 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3872 | EXCEL.EXE | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
3872 | EXCEL.EXE | 52.123.129.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3872 | EXCEL.EXE | 188.209.214.83:443 | nws.visionconsulting.ro | ROMARG SRL | RO | unknown |
3872 | EXCEL.EXE | 104.18.21.213:80 | r11.c.lencr.org | CLOUDFLARENET | — | whitelisted |
1268 | svchost.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
nws.visionconsulting.ro |
| unknown |
r11.c.lencr.org |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
royalpalm.sparkblue.lk |
| unknown |
messaging.lifecycle.office.com |
| whitelisted |