| File name: | SCP_087_B_setup.exe |
| Full analysis: | https://app.any.run/tasks/b0cb6edf-8ef6-4056-ba01-d50964684763 |
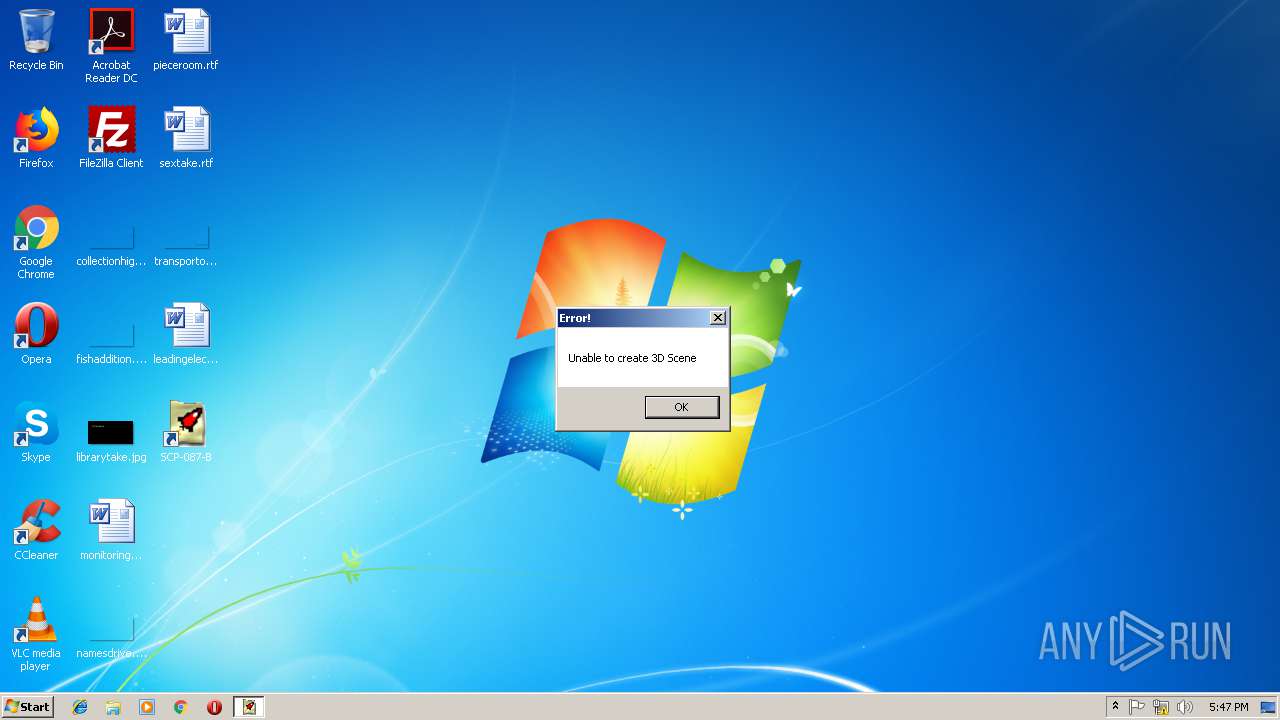
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 17:46:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | D1F37704EBA9452C4A4732D42D30222D |
| SHA1: | B26C3B1A43F27DD4F86D123EAA23DD282E019F1B |
| SHA256: | B2312FBB61551C5B57F5F2C7E690749BE9D8C26C0EBF2FEA37DA7ED82448A759 |
| SSDEEP: | 49152:DsFlsws9pQLqUKdpsbA+yQnkhNtkKJV4t0jasESIPr+K8MxsU3joxtzS5:usb/Q43unaDhjaK0SK8XRS5 |
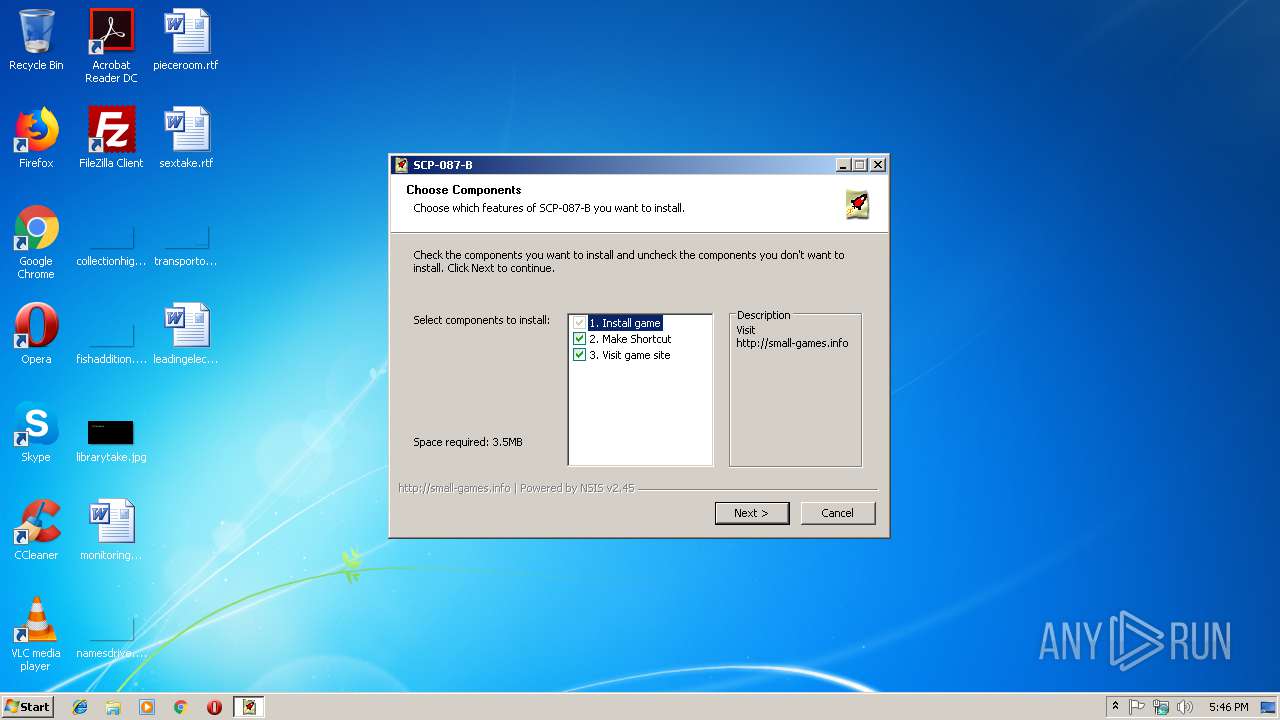
MALICIOUS
Application was dropped or rewritten from another process
- SCP-087-B.exe (PID: 4052)
- SCP-087-B.exe (PID: 2392)
SUSPICIOUS
Executable content was dropped or overwritten
- SCP_087_B_setup.exe (PID: 3692)
Check for Java to be installed
- iexplore.exe (PID: 2292)
INFO
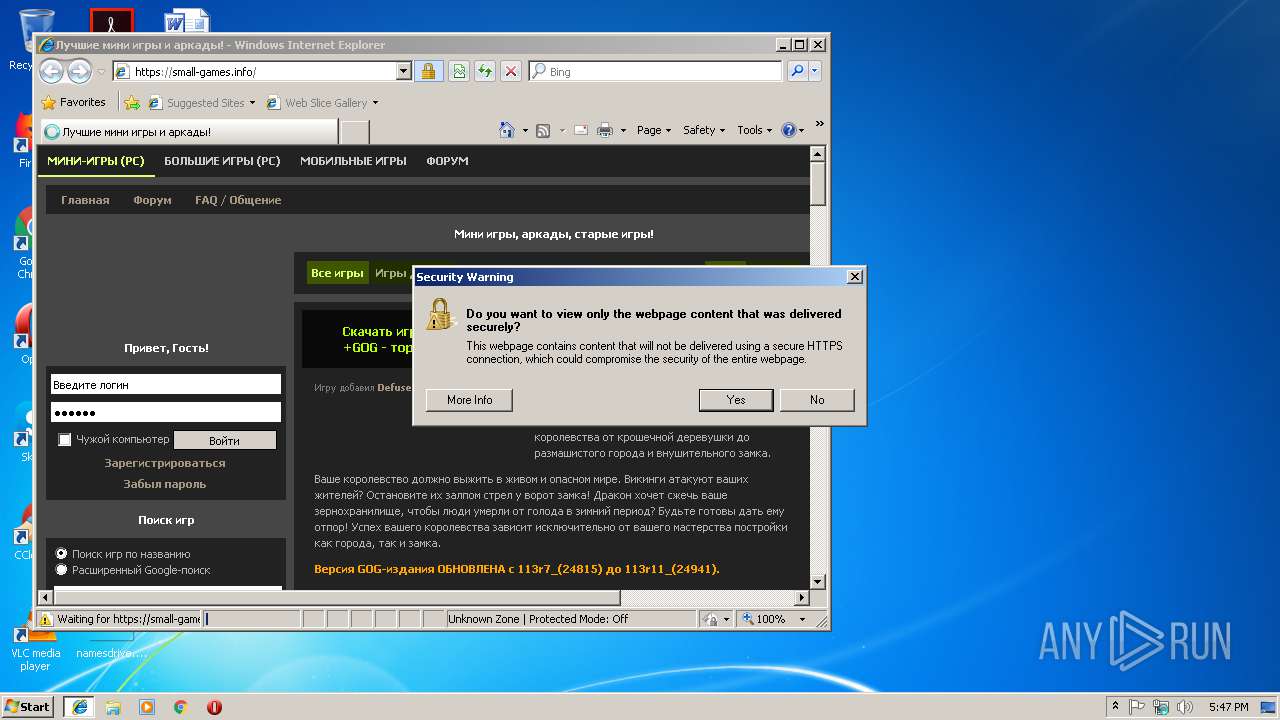
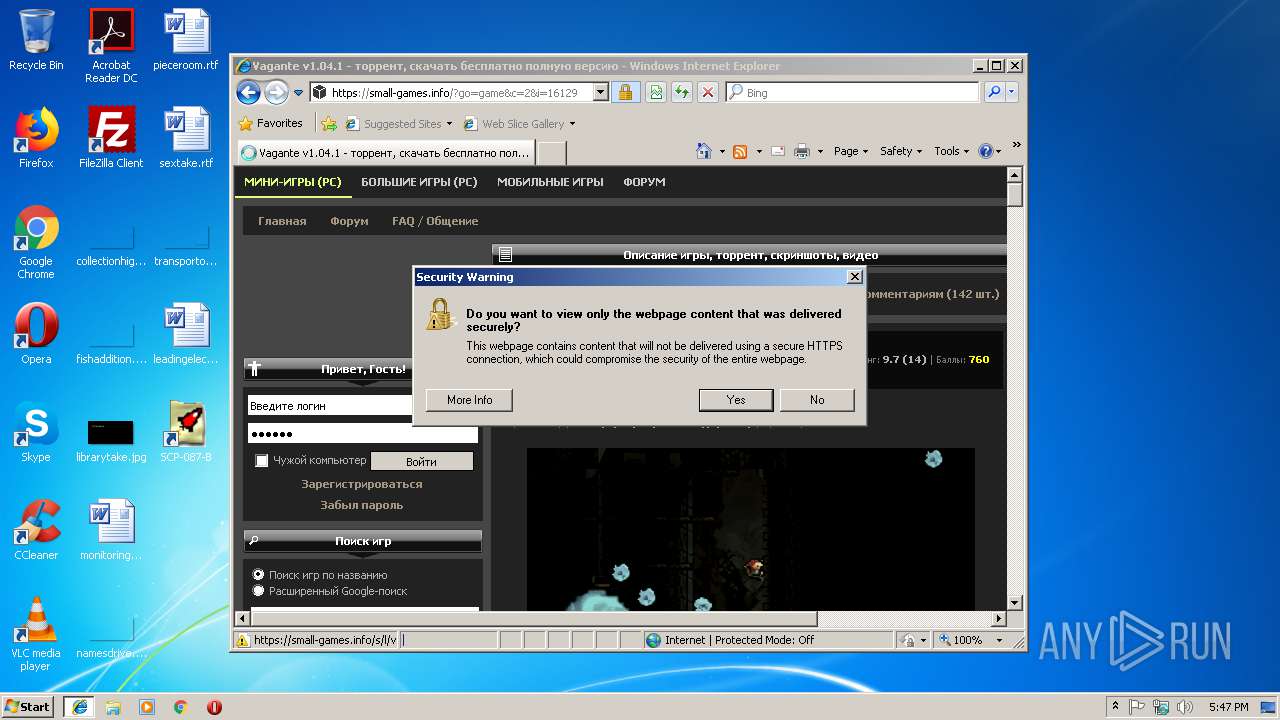
Changes internet zones settings
- iexplore.exe (PID: 2292)
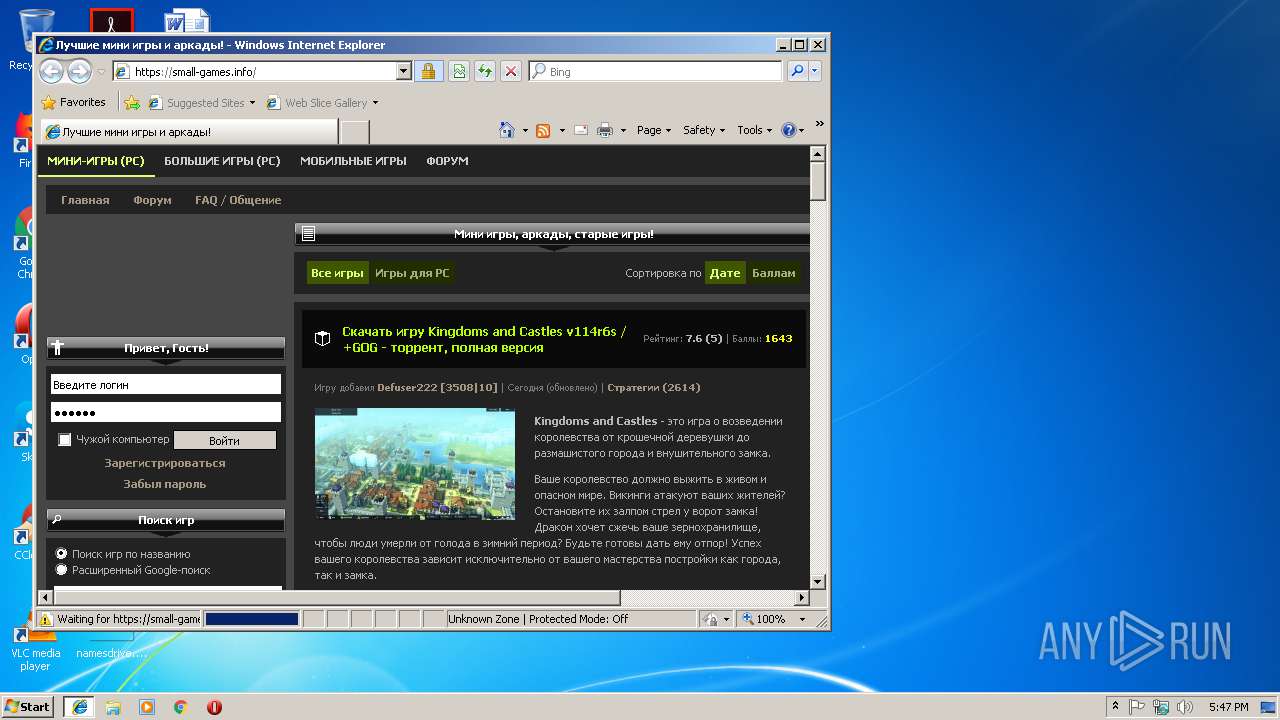
Creates files in the user directory
- iexplore.exe (PID: 3796)
Reads Internet Cache Settings
- iexplore.exe (PID: 3796)
Changes settings of System certificates
- iexplore.exe (PID: 3796)
Reads internet explorer settings
- iexplore.exe (PID: 3796)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:06:06 23:41:48+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23040 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30cb |
| OSVersion: | 4 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Jun-2009 21:41:48 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 06-Jun-2009 21:41:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000058D2 | 0x00005A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4331 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17976 |
.data | 0x00009000 | 0x0001AF78 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.6178 |
.ndata | 0x00024000 | 0x00012000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00036000 | 0x00004950 | 0x00004A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.97443 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10609 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 0 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 3.02435 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70992 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
41
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2292 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2392 | "C:\Games\SCP-087-B\SCP-087-B.exe" | C:\Games\SCP-087-B\SCP-087-B.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3168 | "C:\Users\admin\AppData\Local\Temp\SCP_087_B_setup.exe" | C:\Users\admin\AppData\Local\Temp\SCP_087_B_setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3692 | "C:\Users\admin\AppData\Local\Temp\SCP_087_B_setup.exe" | C:\Users\admin\AppData\Local\Temp\SCP_087_B_setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3796 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2292 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4052 | "C:\Games\SCP-087-B\SCP-087-B.exe" | C:\Games\SCP-087-B\SCP-087-B.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
984
Read events
812
Write events
169
Delete events
3
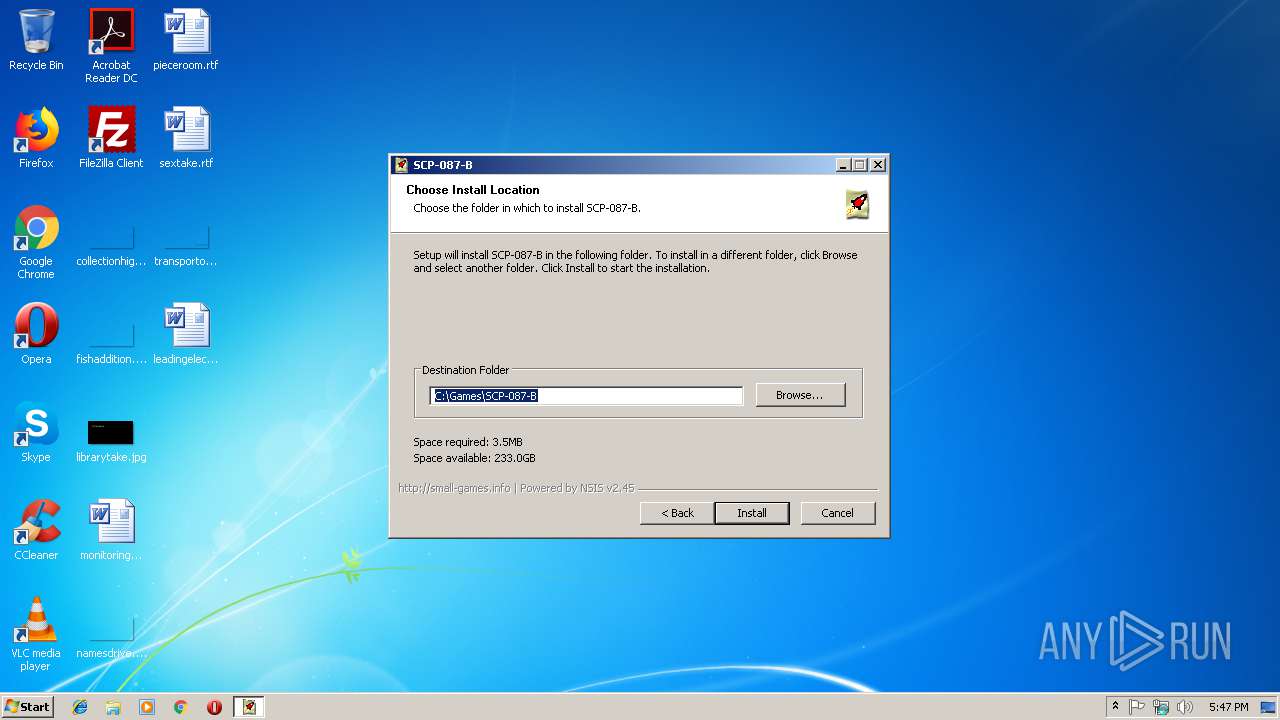
Modification events
| (PID) Process: | (3692) SCP_087_B_setup.exe | Key: | HKEY_CURRENT_USER\Software\SmallGamesInfo |
| Operation: | write | Name: | Dir |
Value: C:\Games\SCP-087-B | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3692) SCP_087_B_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FBF23B40-E3F0-101B-8488-00AA003E56F8} {000214E4-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000B4C399F8B1C7D401 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\AdminActive |
| Operation: | write | Name: | {365E2715-33A5-11E9-AA93-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
Executable files
2
Suspicious files
3
Text files
143
Unknown types
39
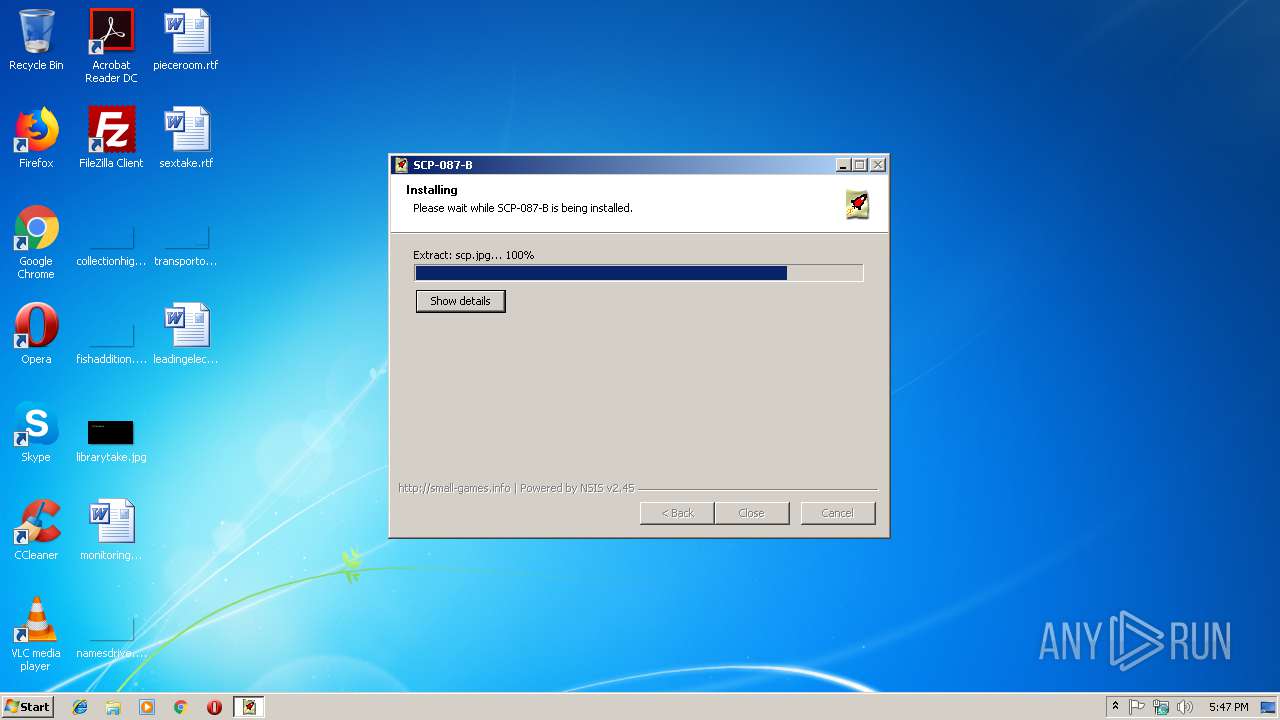
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3692 | SCP_087_B_setup.exe | C:\Games\SCP-087-B\ambient1.ogg | ogg | |
MD5:— | SHA256:— | |||
| 3692 | SCP_087_B_setup.exe | C:\Games\SCP-087-B\ambient4.ogg | ogg | |
MD5:— | SHA256:— | |||
| 3692 | SCP_087_B_setup.exe | C:\Games\SCP-087-B\609.ogg | ogg | |
MD5:— | SHA256:— | |||
| 3692 | SCP_087_B_setup.exe | C:\Games\SCP-087-B\ambient5.ogg | ogg | |
MD5:— | SHA256:— | |||
| 3692 | SCP_087_B_setup.exe | C:\Games\SCP-087-B\609.jpg | image | |
MD5:— | SHA256:— | |||
| 3692 | SCP_087_B_setup.exe | C:\Games\SCP-087-B\breath.ogg | ogg | |
MD5:— | SHA256:— | |||
| 3692 | SCP_087_B_setup.exe | C:\Games\SCP-087-B\concretefloor.jpg | image | |
MD5:— | SHA256:— | |||
| 3692 | SCP_087_B_setup.exe | C:\Games\SCP-087-B\behind.ogg | ogg | |
MD5:— | SHA256:— | |||
| 3692 | SCP_087_B_setup.exe | C:\Games\SCP-087-B\ambient2.ogg | ogg | |
MD5:— | SHA256:— | |||
| 3692 | SCP_087_B_setup.exe | C:\Games\SCP-087-B\brickwall.jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
86
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
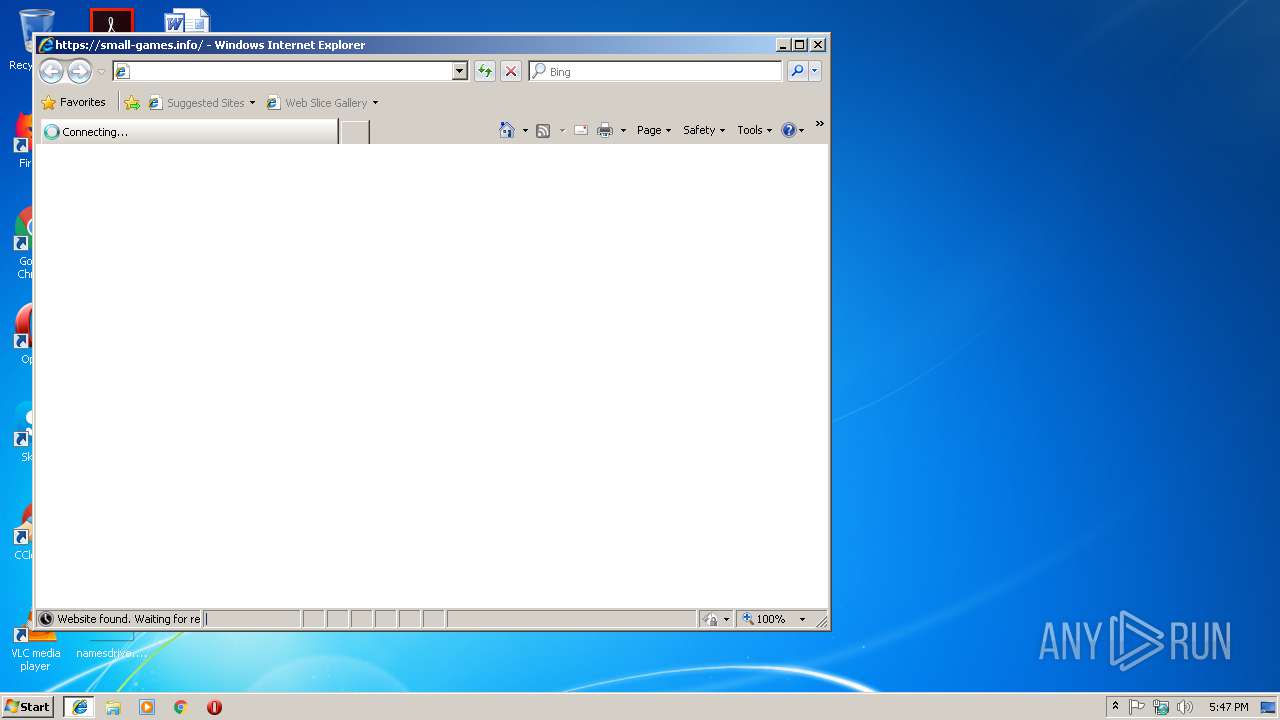
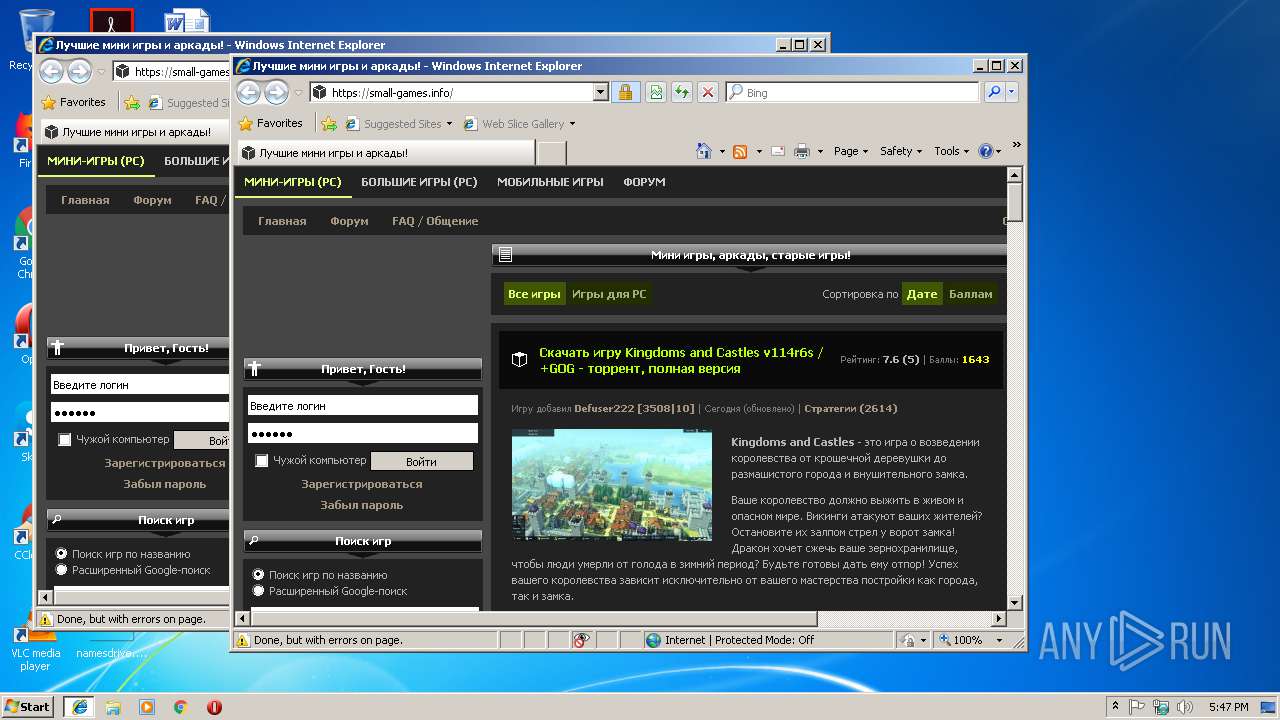
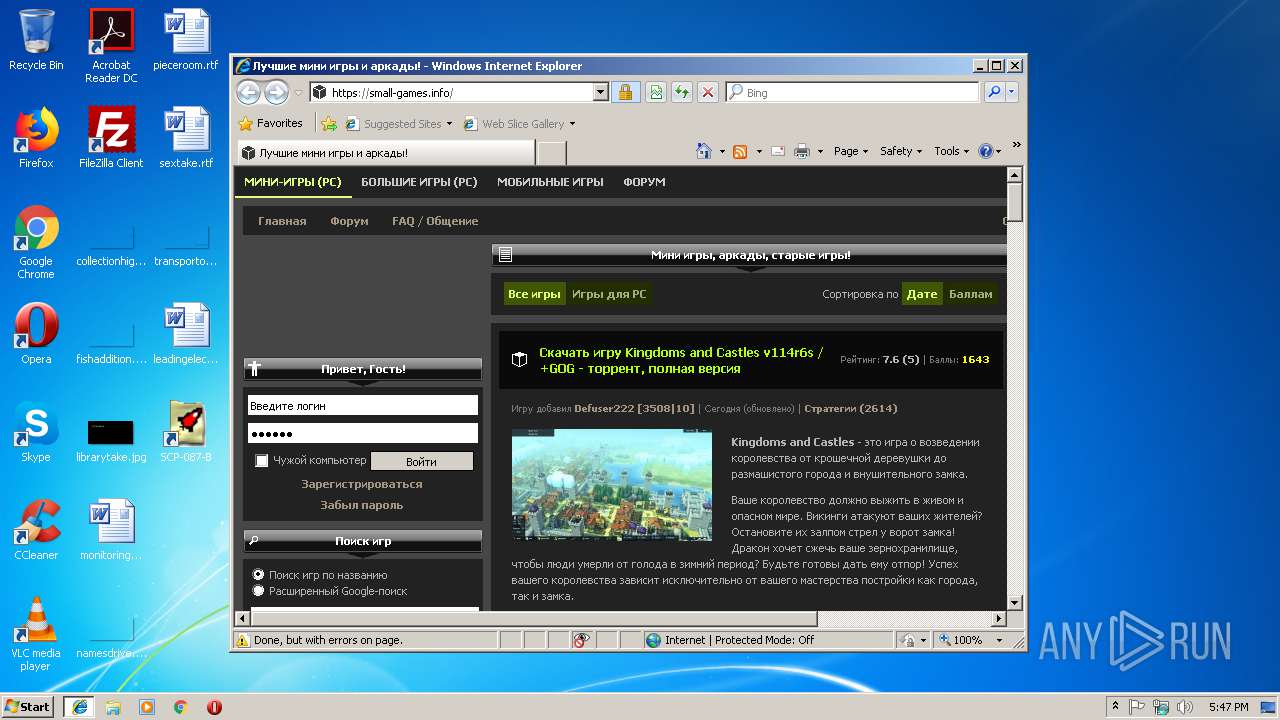
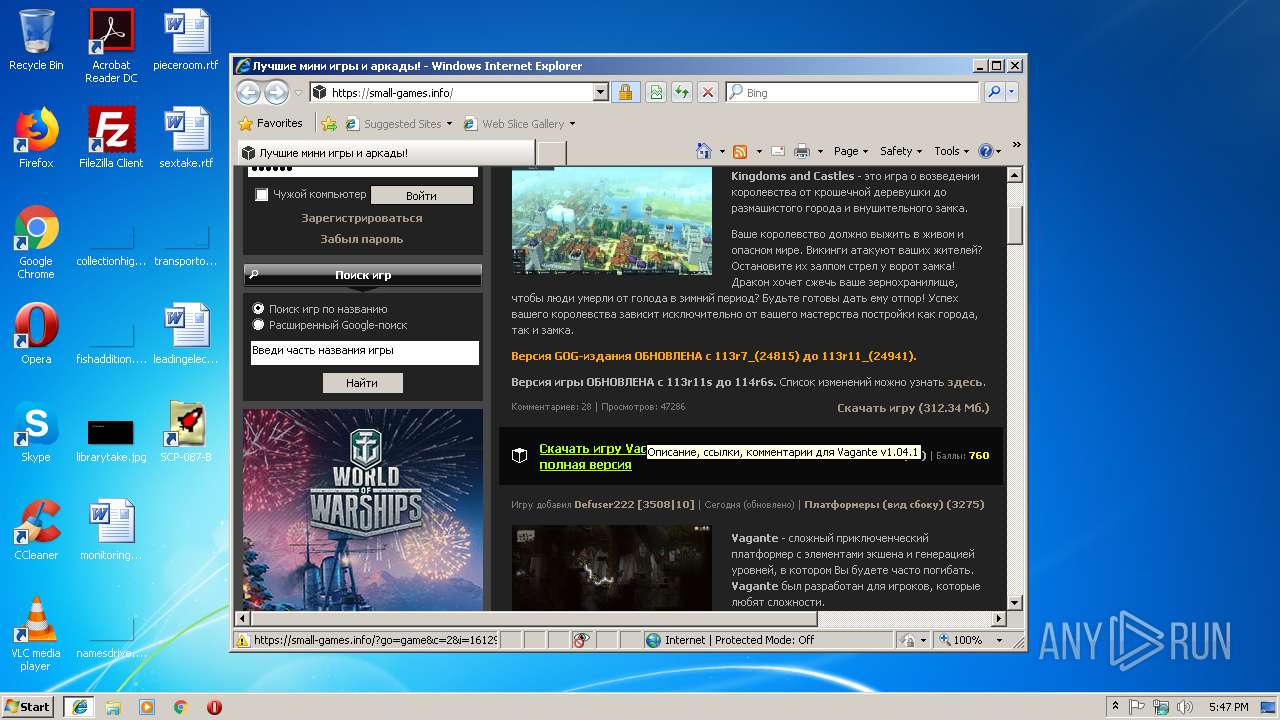
3796 | iexplore.exe | GET | 301 | 62.112.9.123:80 | http://small-games.info/ | NL | html | 233 b | whitelisted |
2292 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2292 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3796 | iexplore.exe | 62.112.9.123:80 | small-games.info | WorldStream B.V. | NL | unknown |
3796 | iexplore.exe | 172.217.18.170:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3796 | iexplore.exe | 172.217.22.46:443 | apis.google.com | Google Inc. | US | whitelisted |
3796 | iexplore.exe | 185.172.149.132:443 | cdn4.iconfinder.com | proinity GmbH | DE | suspicious |
3796 | iexplore.exe | 87.240.190.67:443 | vk.com | VKontakte Ltd | RU | suspicious |
3796 | iexplore.exe | 88.212.201.207:443 | counter.yadro.ru | United Network LLC | RU | unknown |
3796 | iexplore.exe | 93.158.134.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
3796 | iexplore.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3796 | iexplore.exe | 172.217.22.8:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
small-games.info |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
cdn4.iconfinder.com |
| whitelisted |
i.ytimg.com |
| whitelisted |
mc.yandex.ru |
| whitelisted |
apis.google.com |
| whitelisted |
counter.yadro.ru |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
accounts.google.com |
| shared |