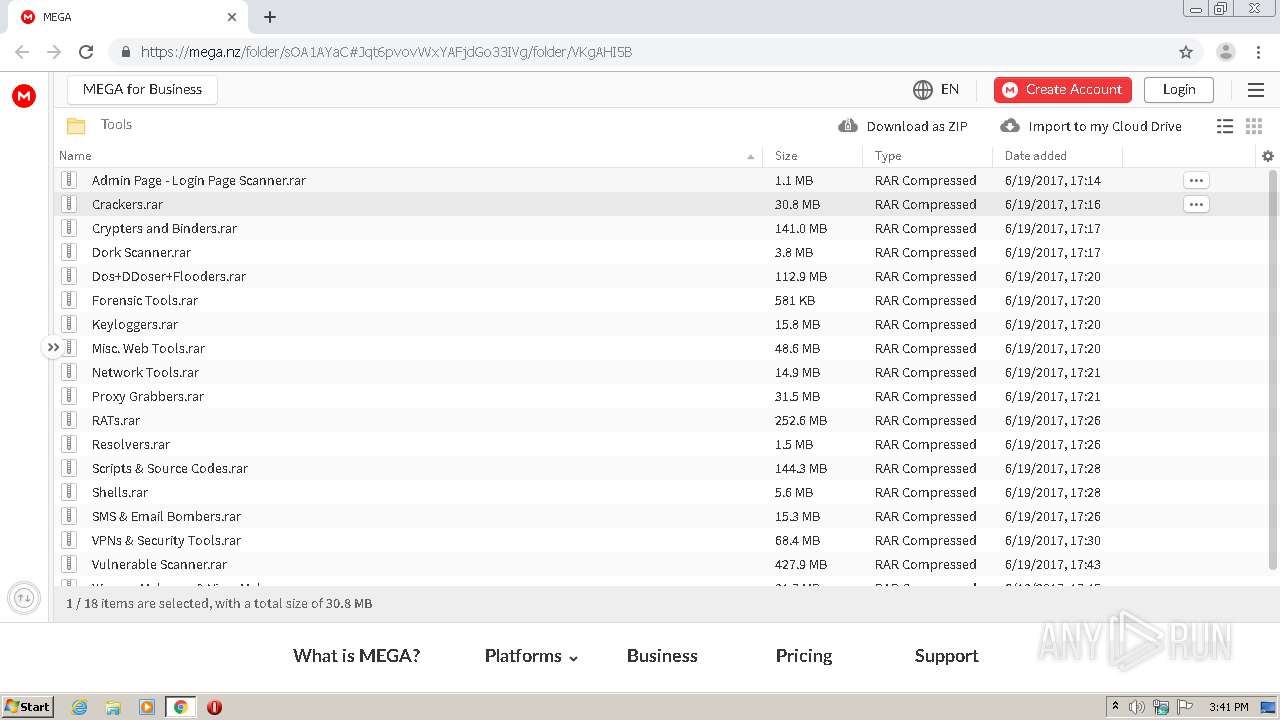
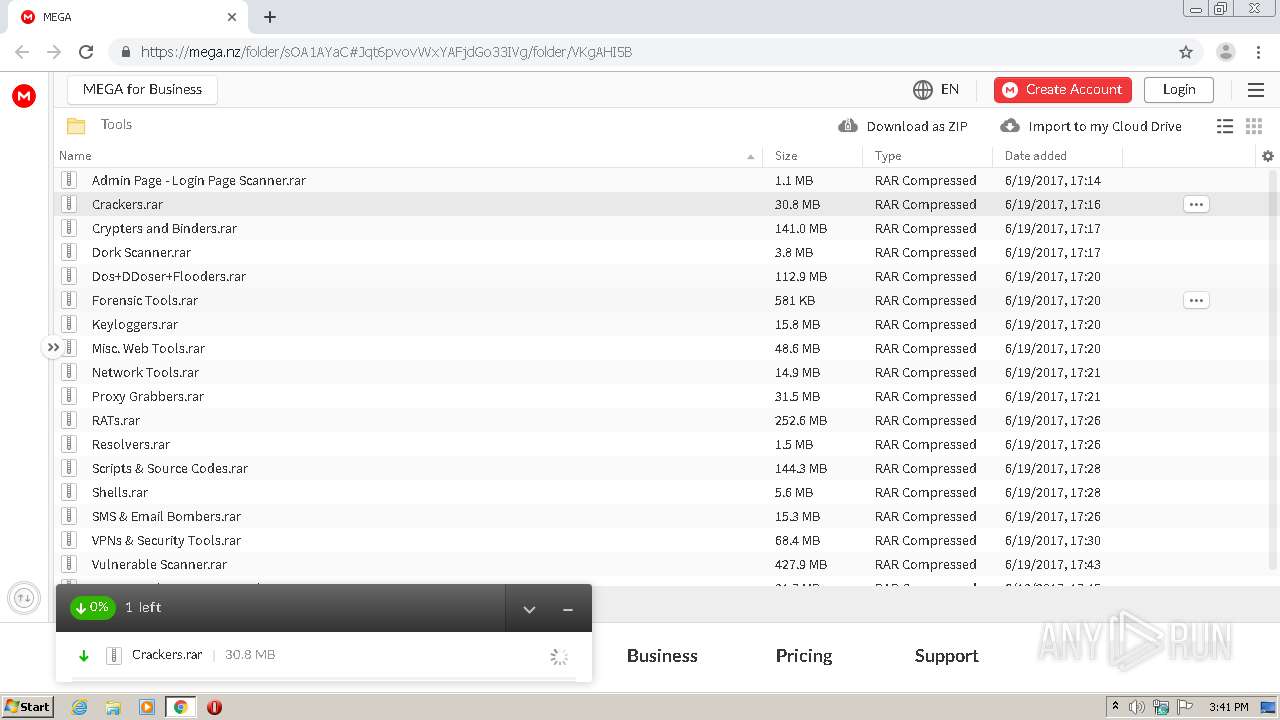
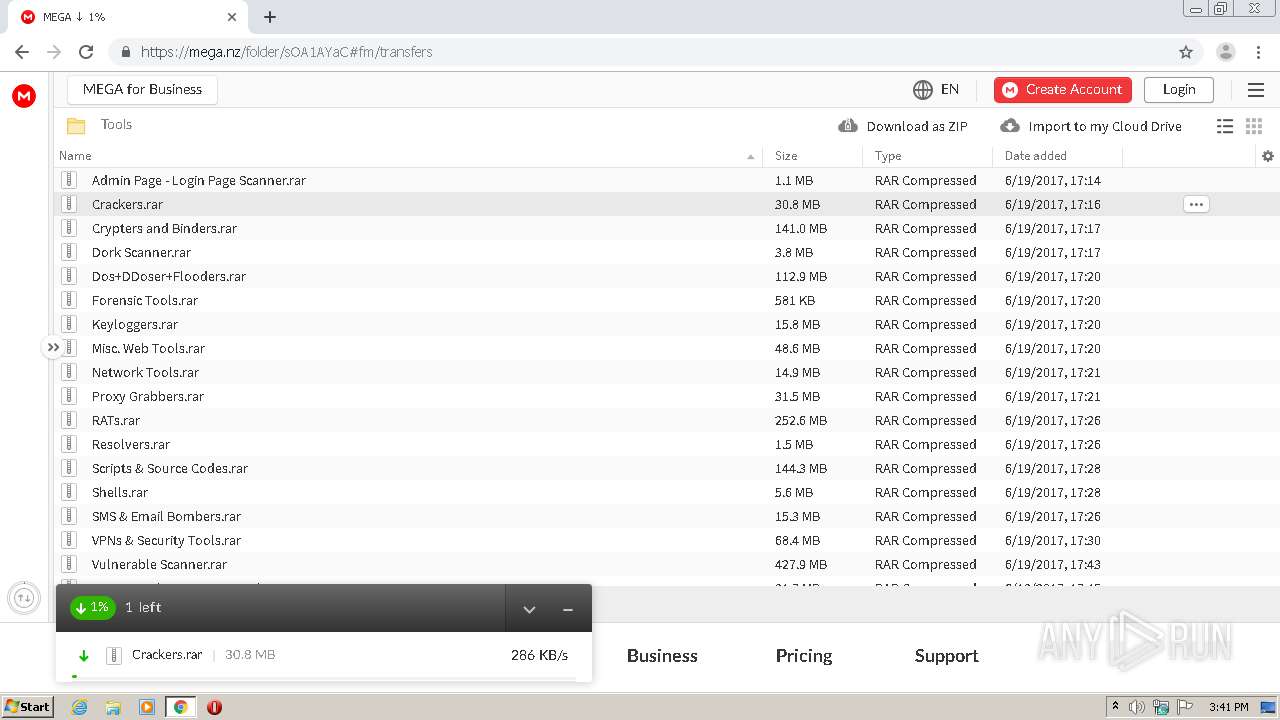
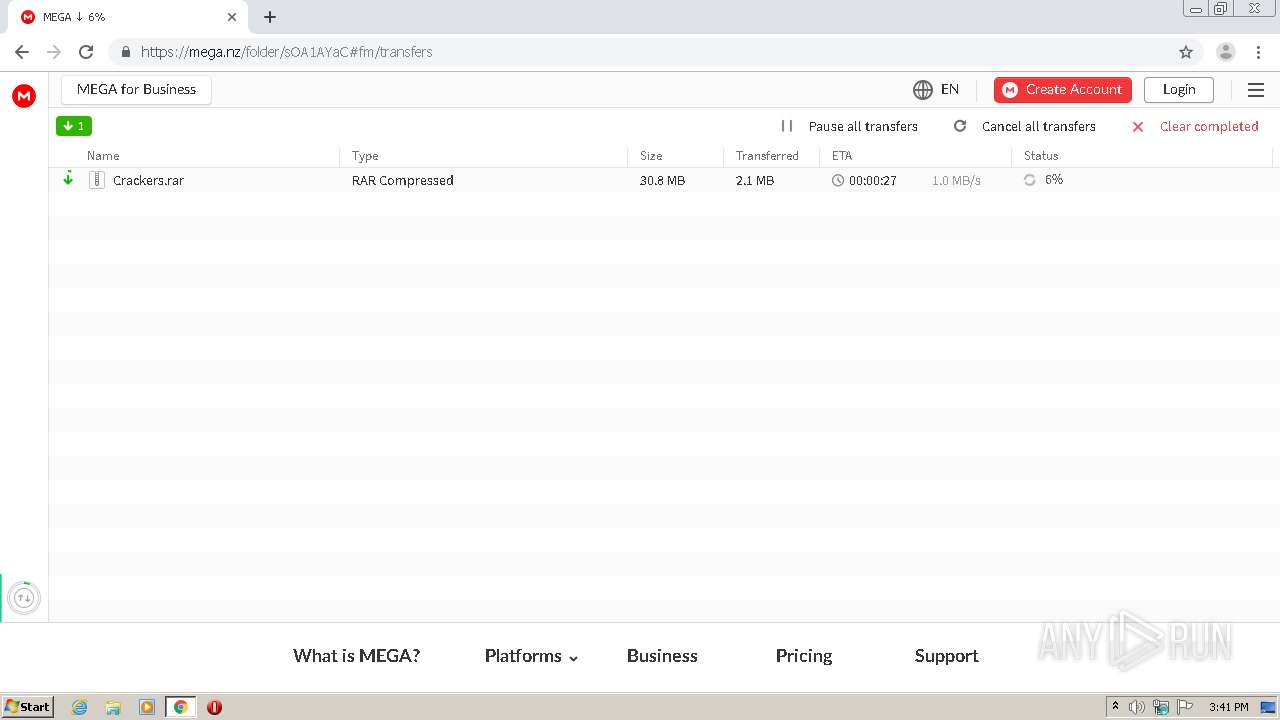
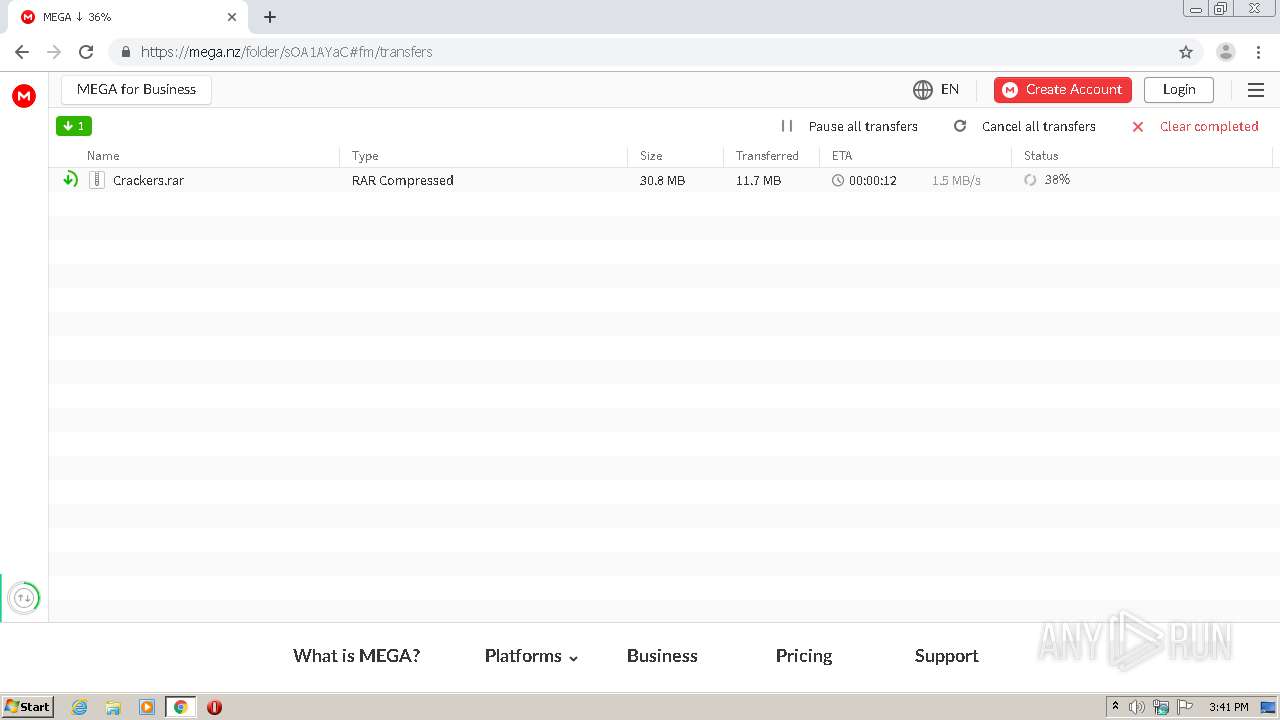
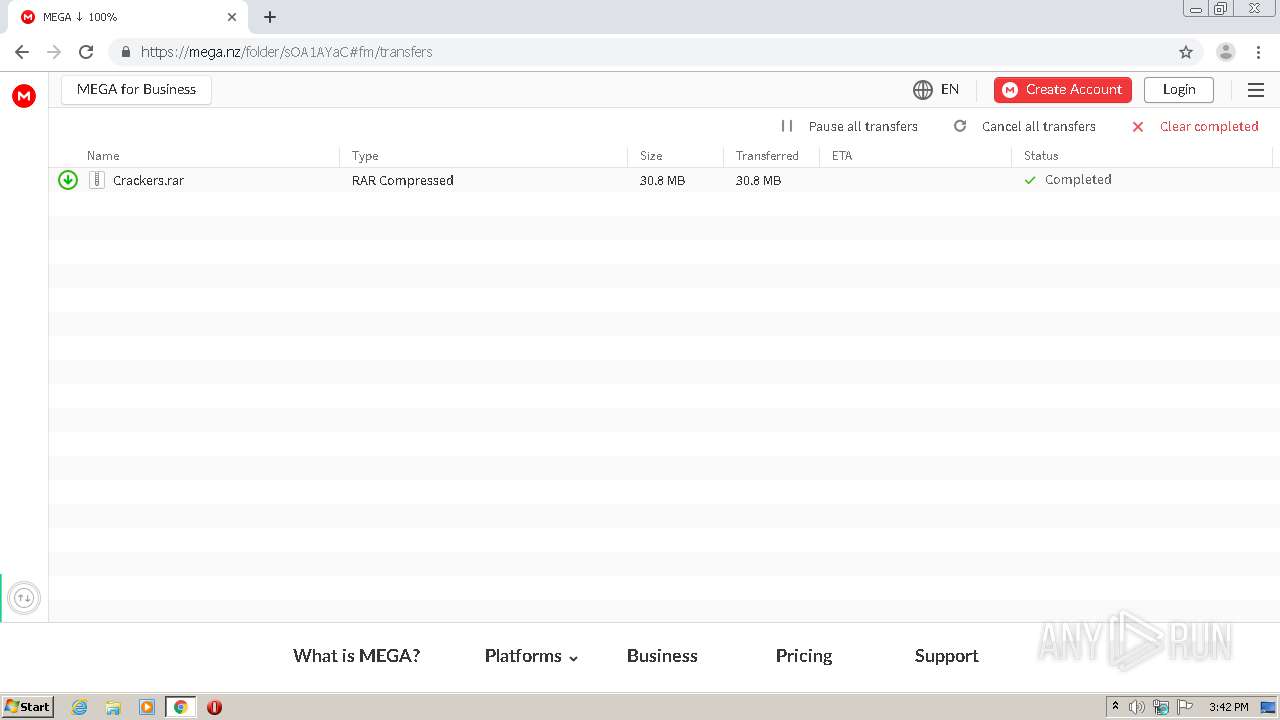
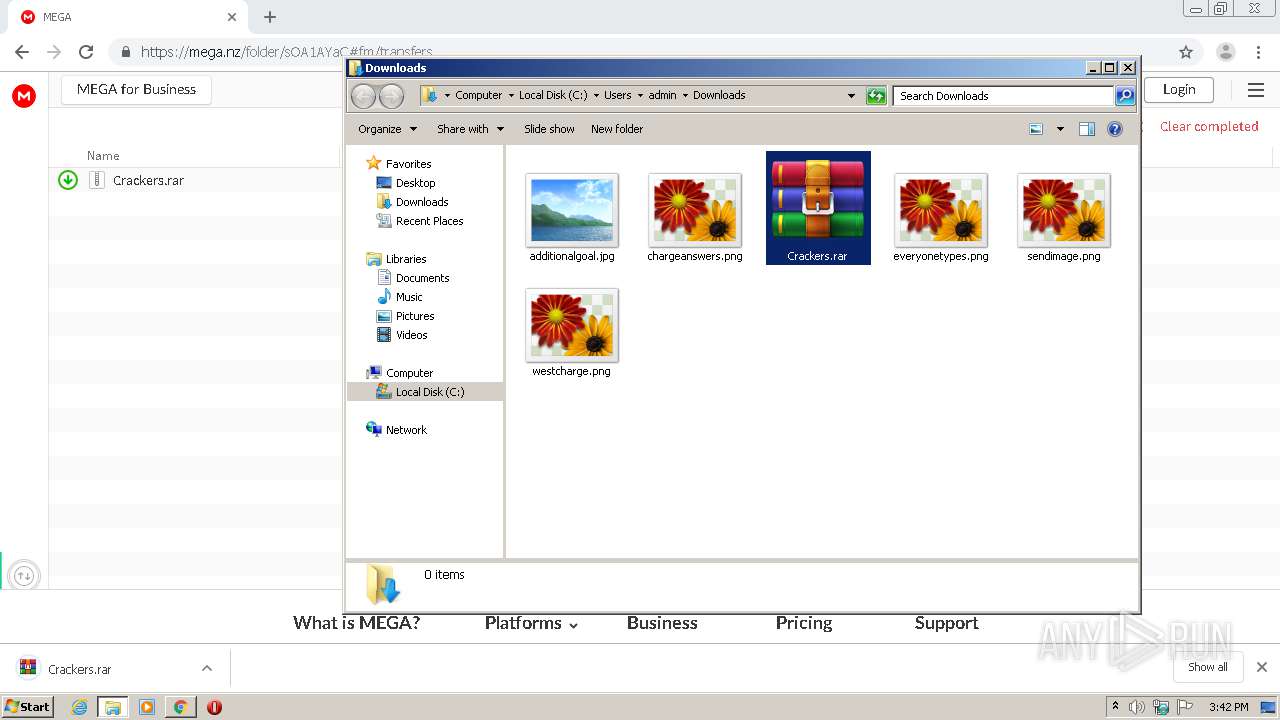
| URL: | https://mega.nz/folder/sOA1AYaC#Jqt6pvovWxYAFjdGo33IVg/file/pLhzhTrA |
| Full analysis: | https://app.any.run/tasks/55dacfc9-e6d5-444d-97a3-f7faf965e315 |
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2020, 14:41:15 |
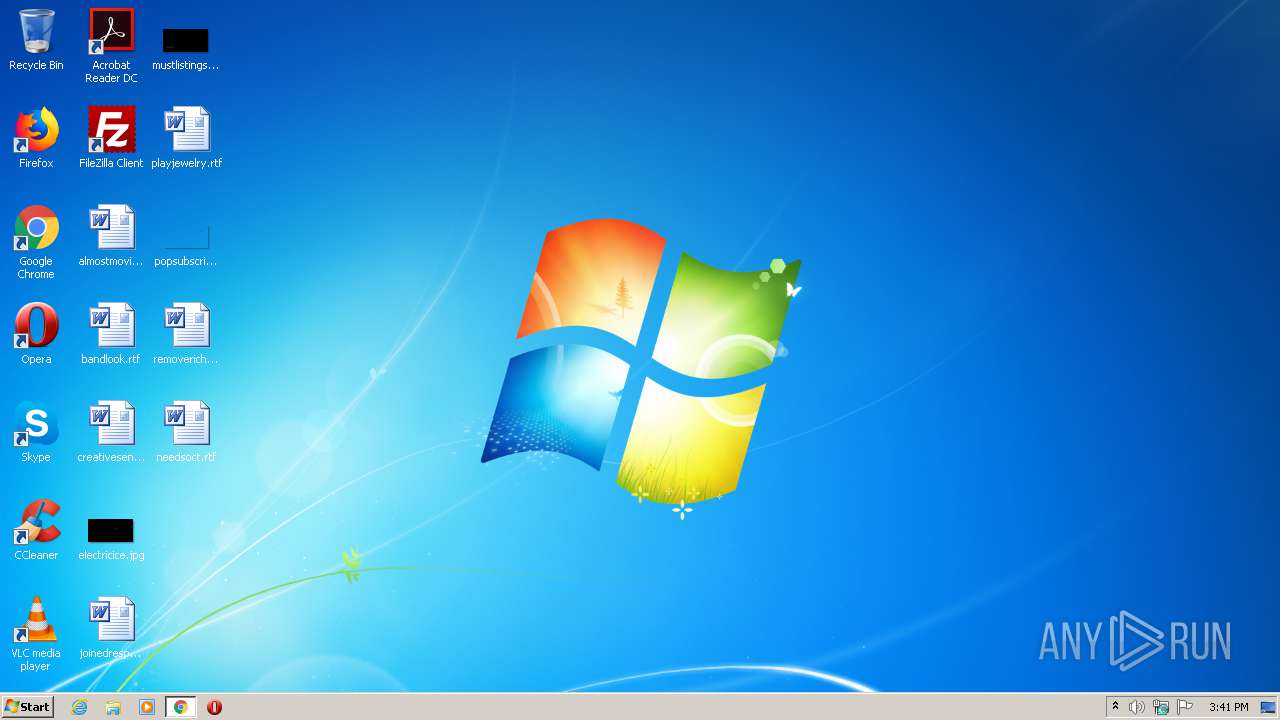
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DF26674AA194789E4975397E6DD18DB7 |
| SHA1: | C056E8B3FFBF62D9F924405334926102603744F9 |
| SHA256: | B22821F799C9116FDC2AF70CE68EA0B119A193A782DD36495CA55777E475E5A4 |
| SSDEEP: | 3:N8X/iuyKWUOmvtvPanWl0:266RR0f |
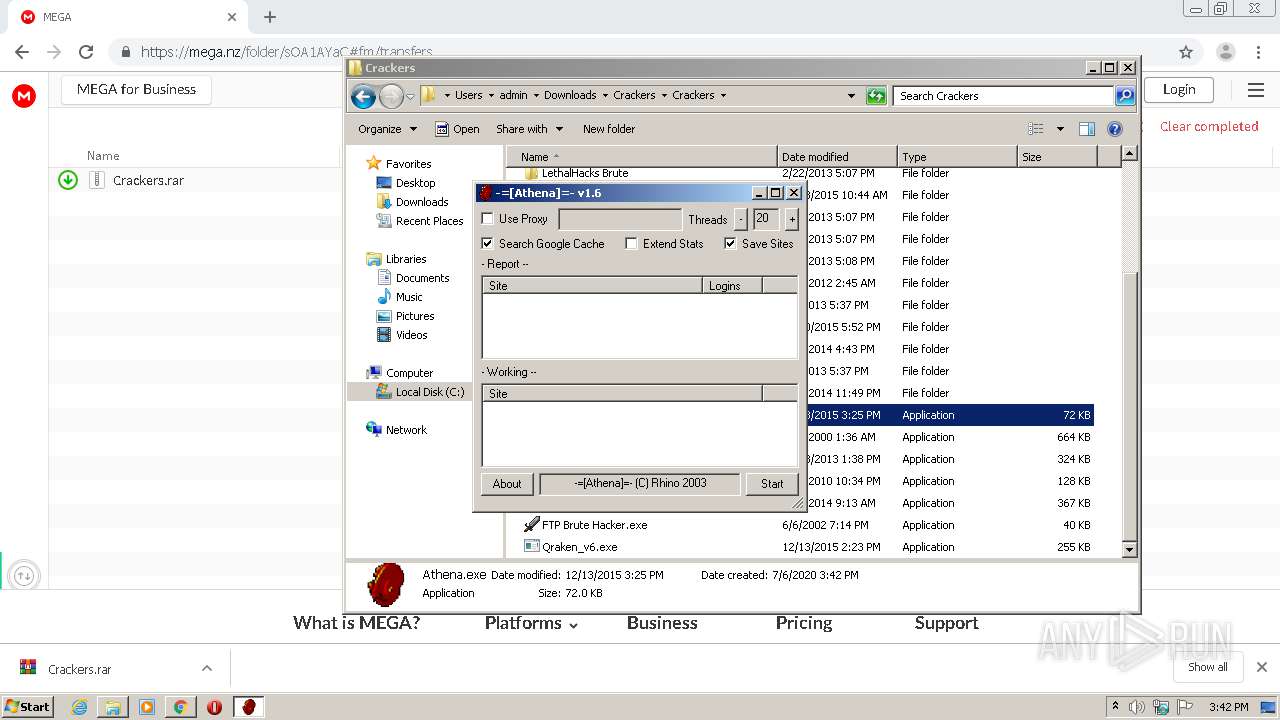
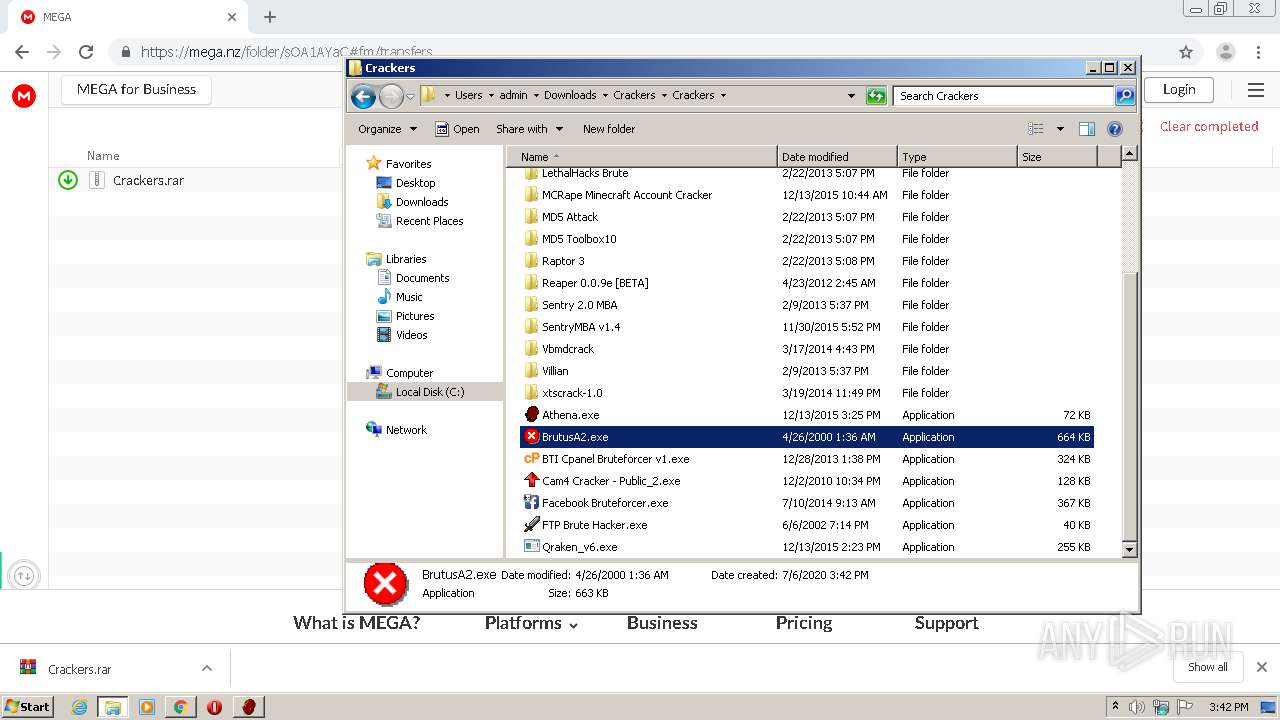
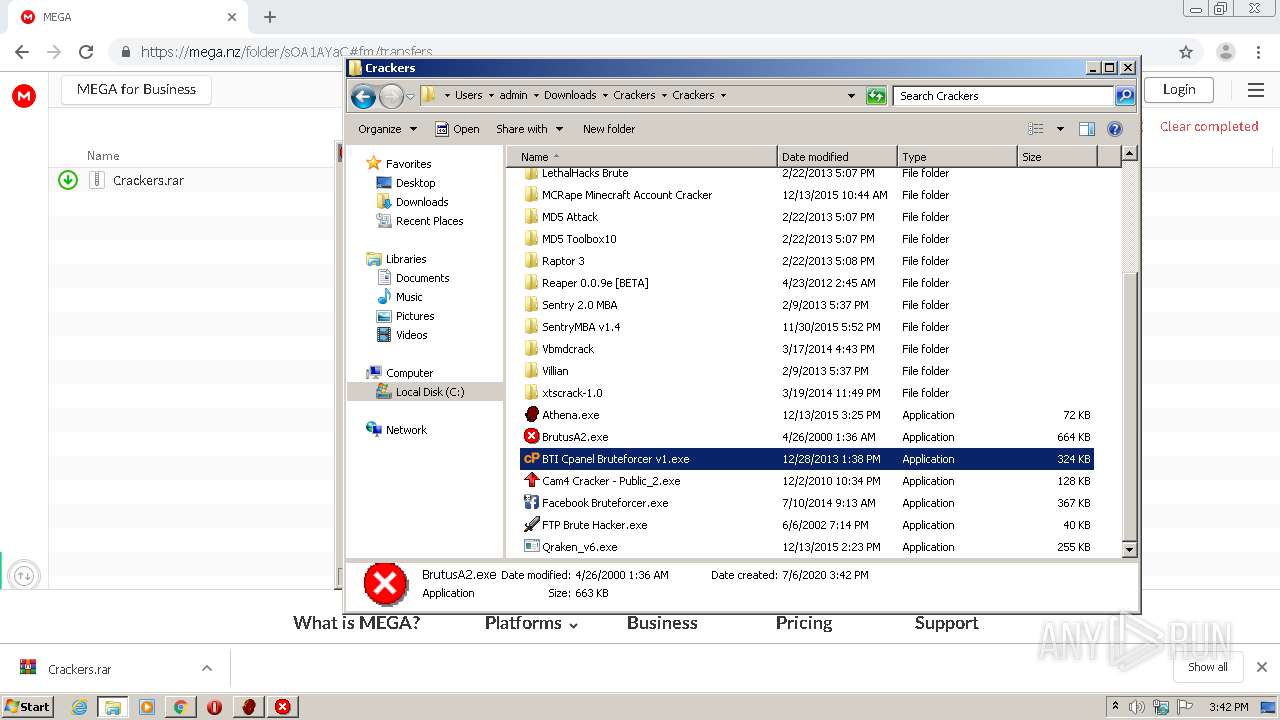
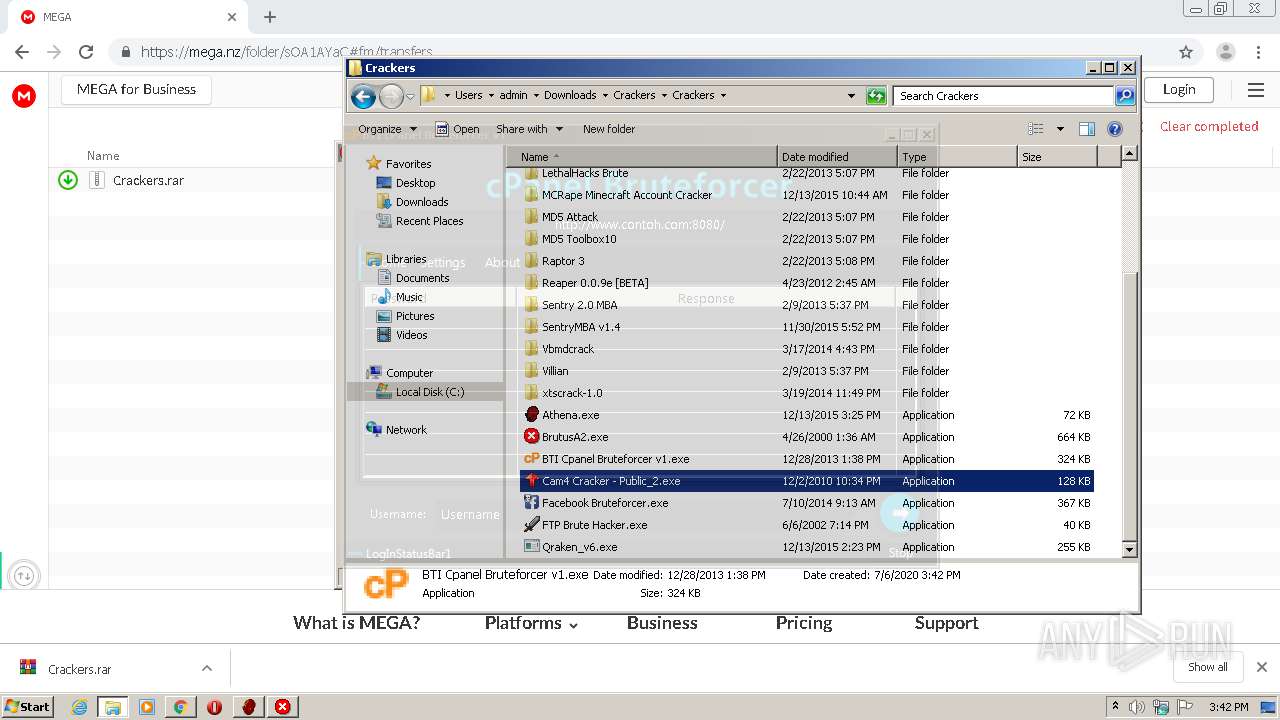
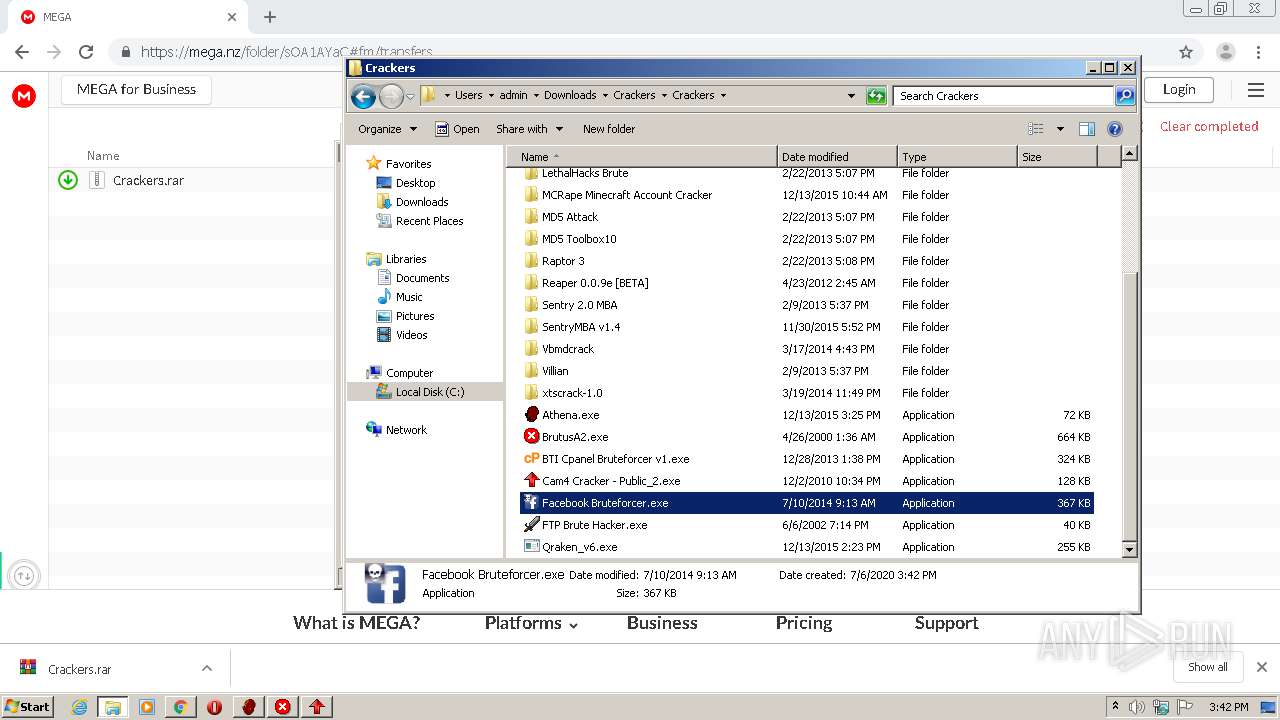
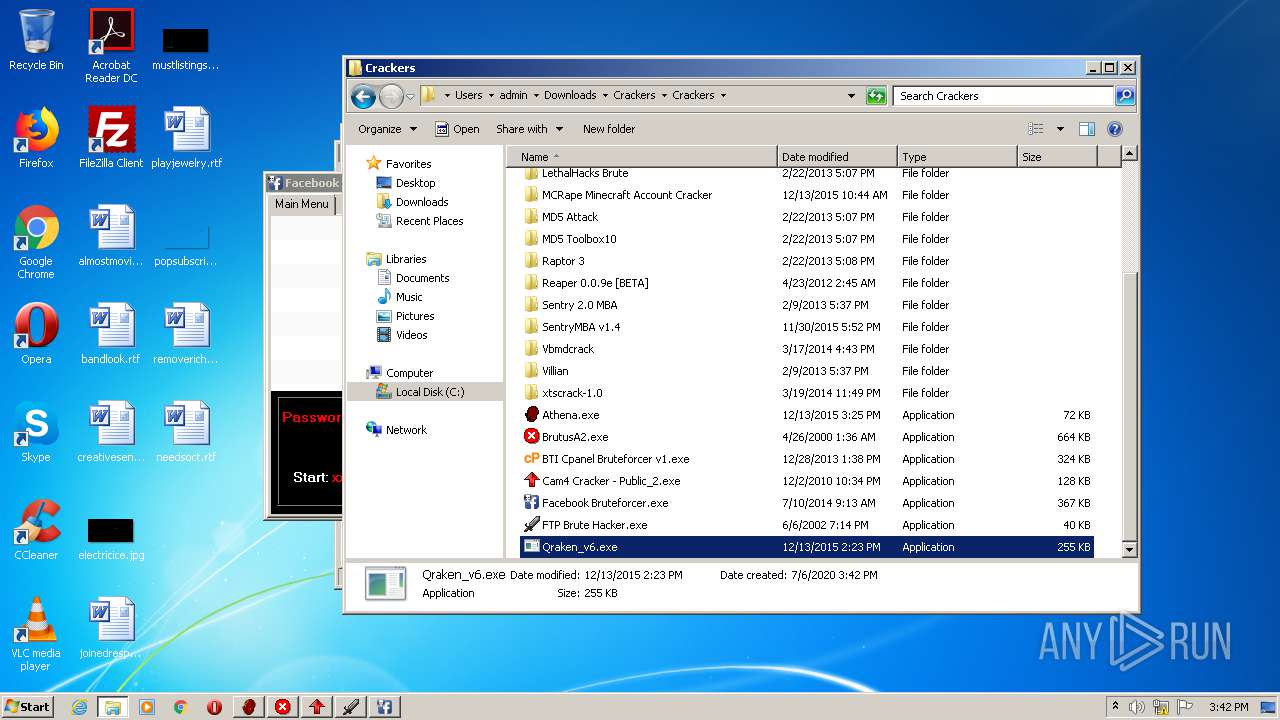
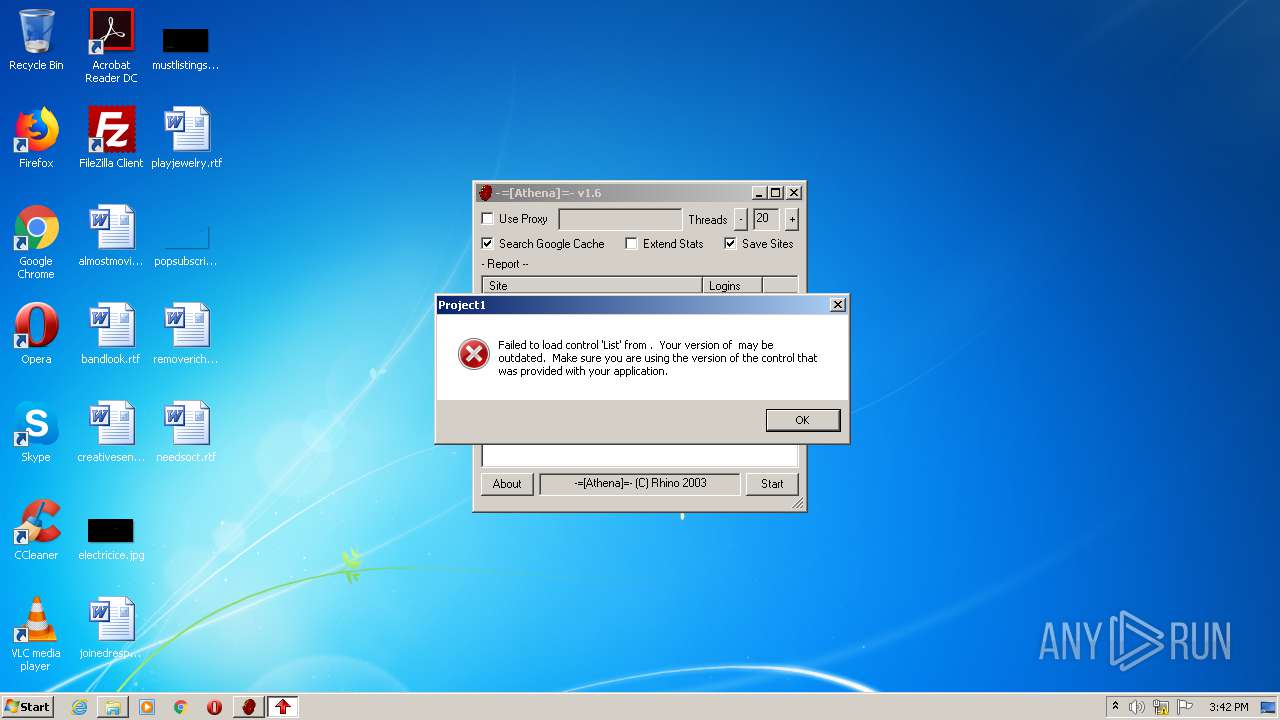
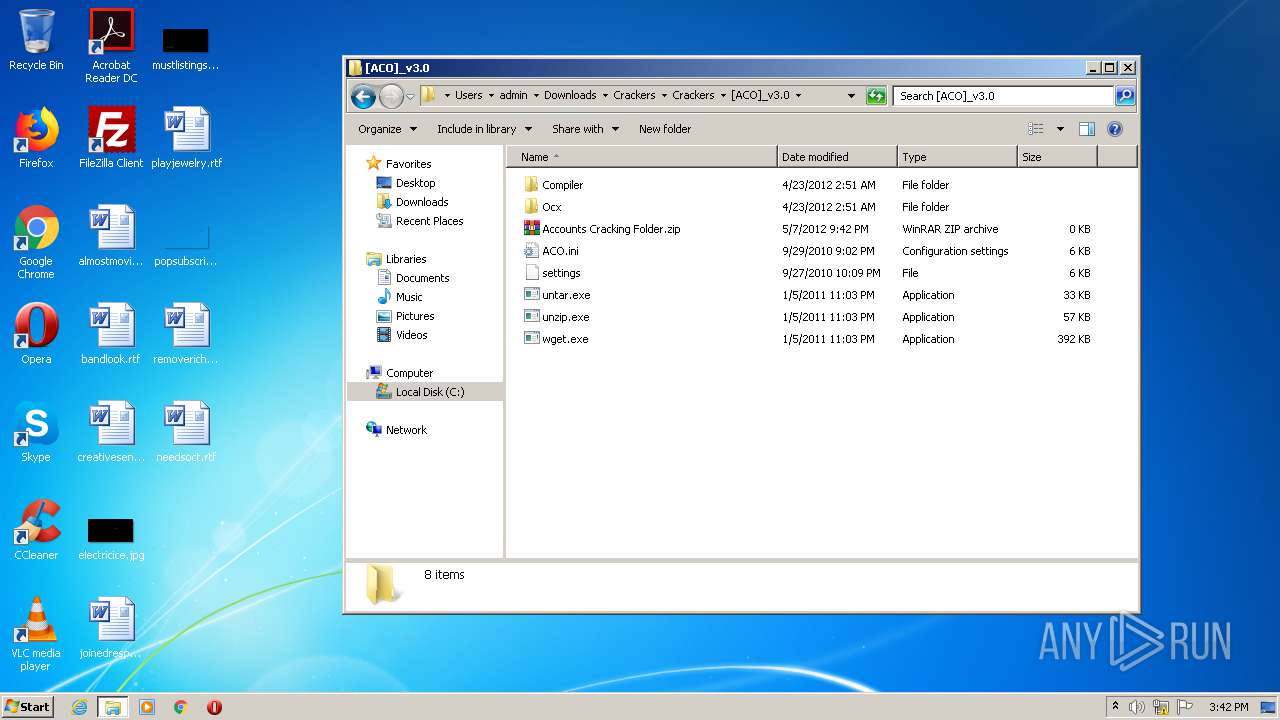
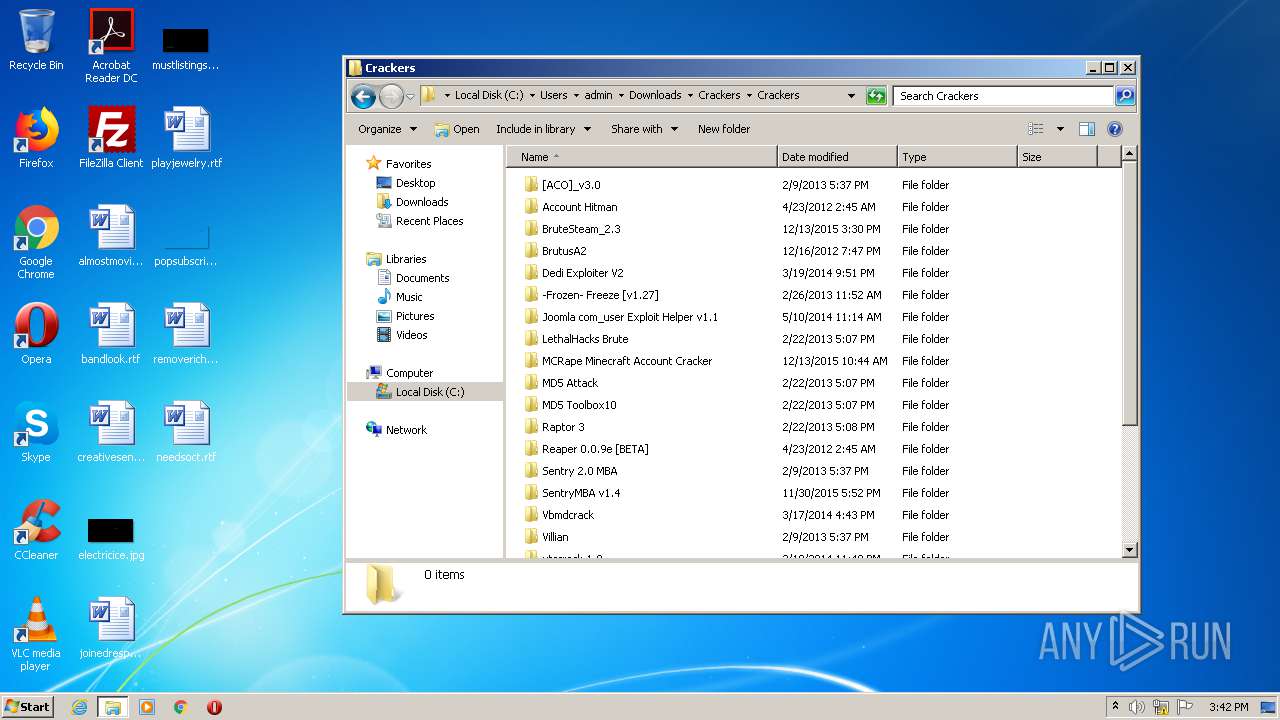
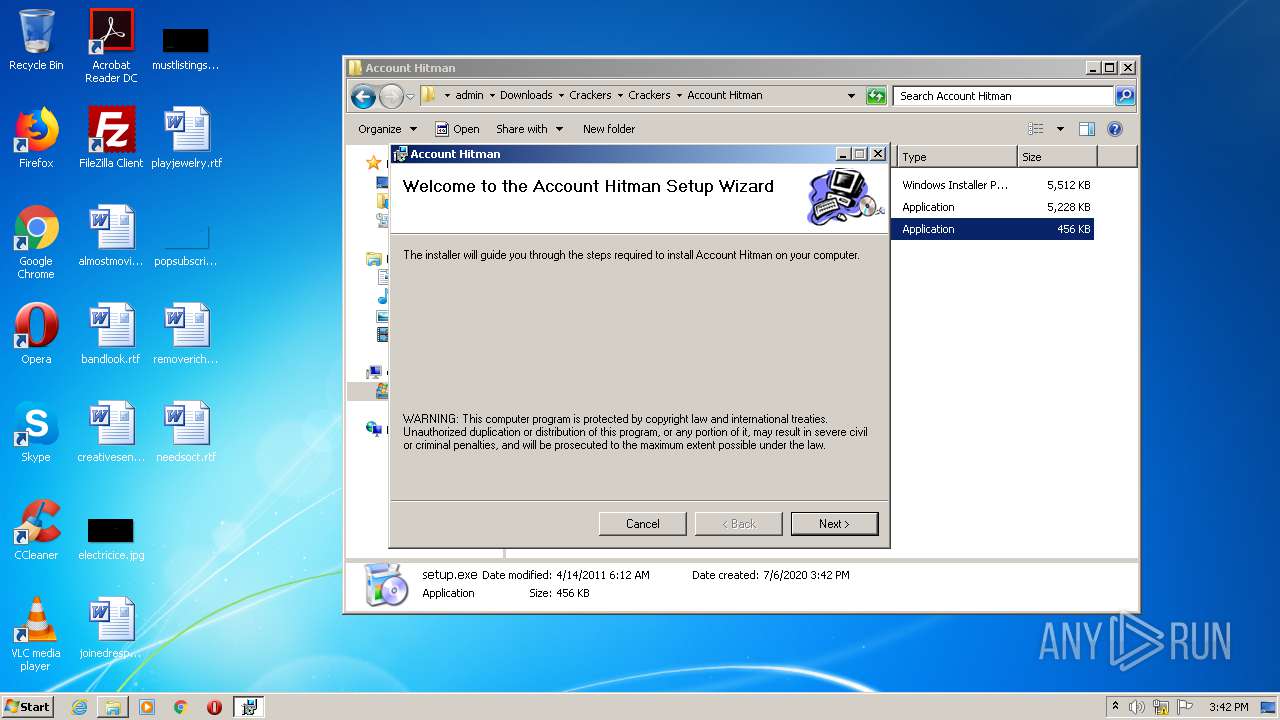
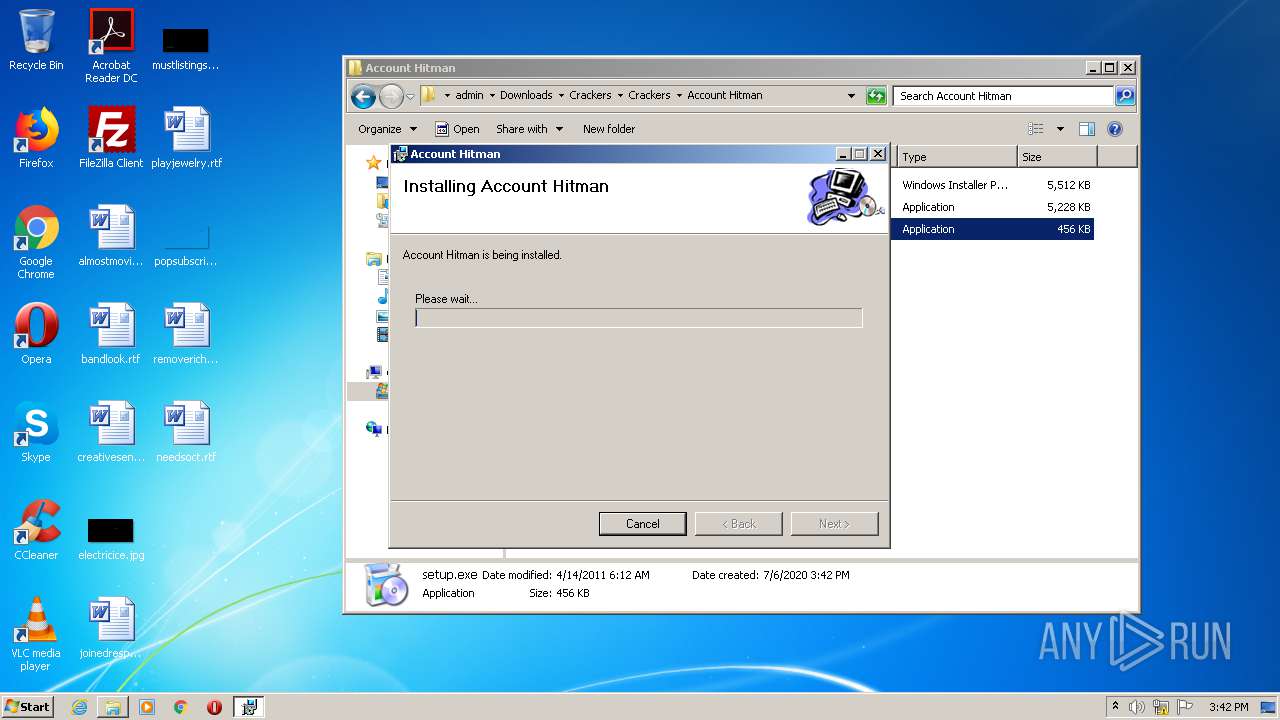
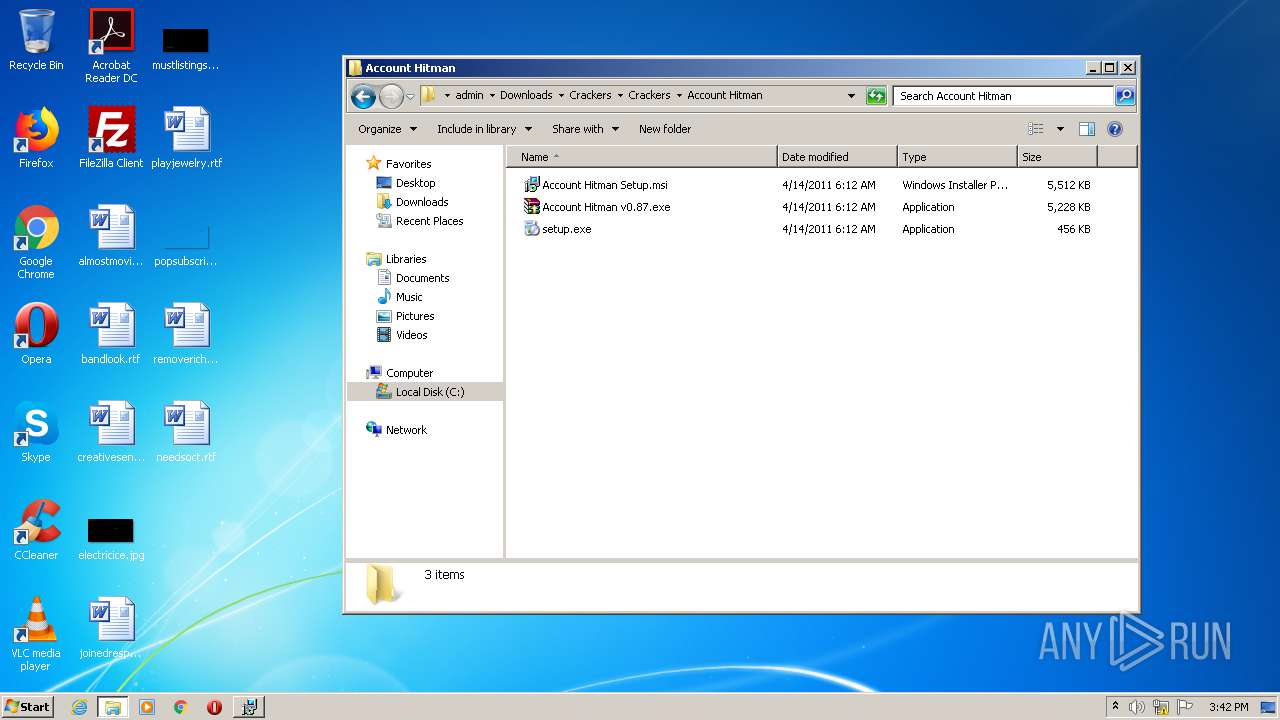
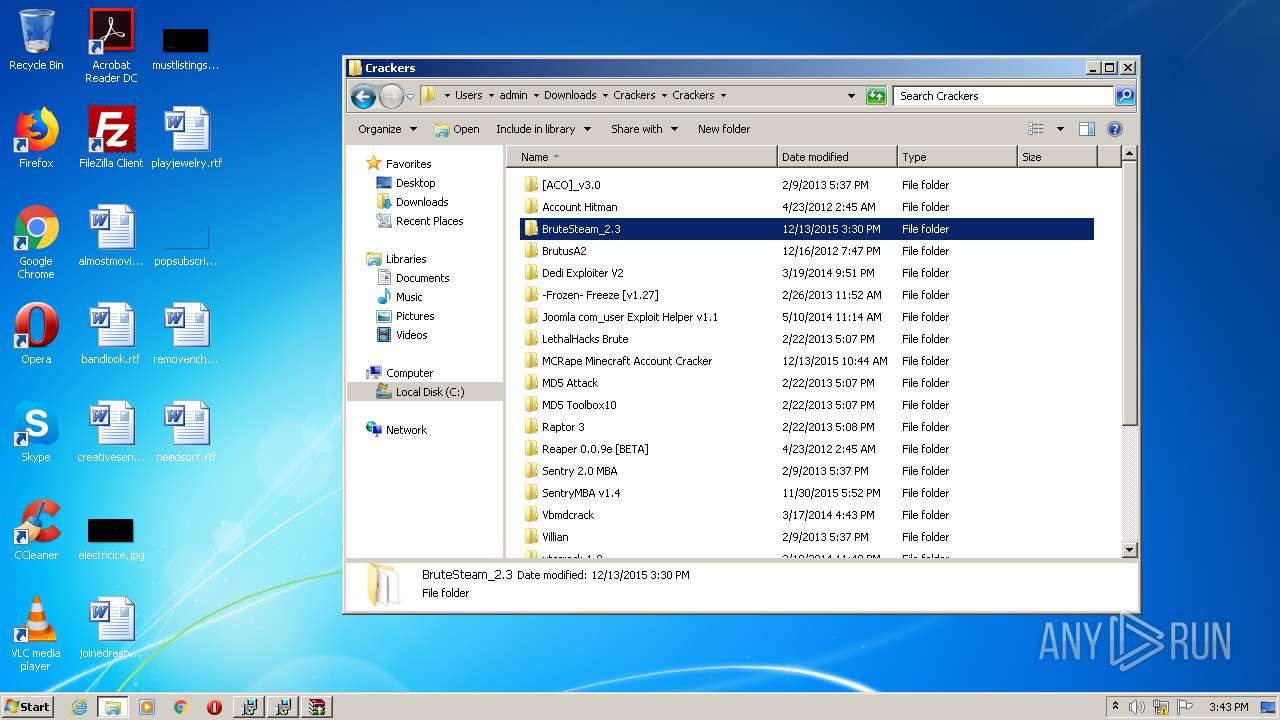
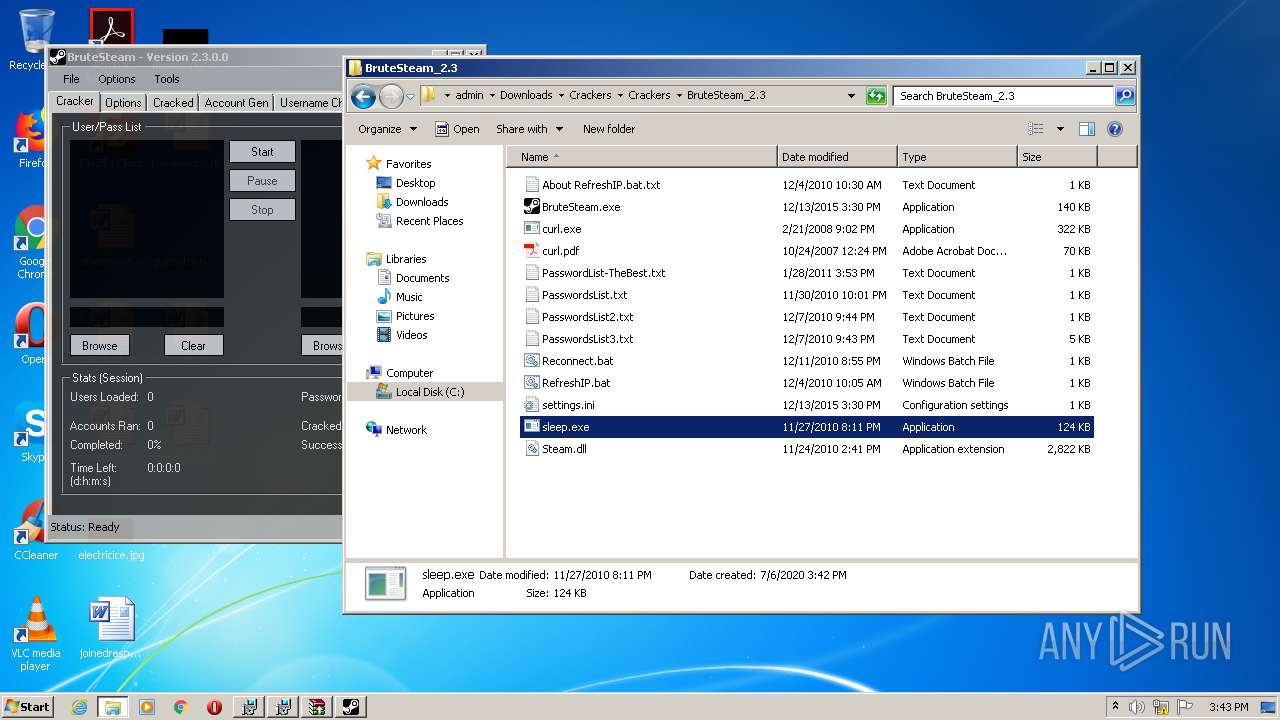
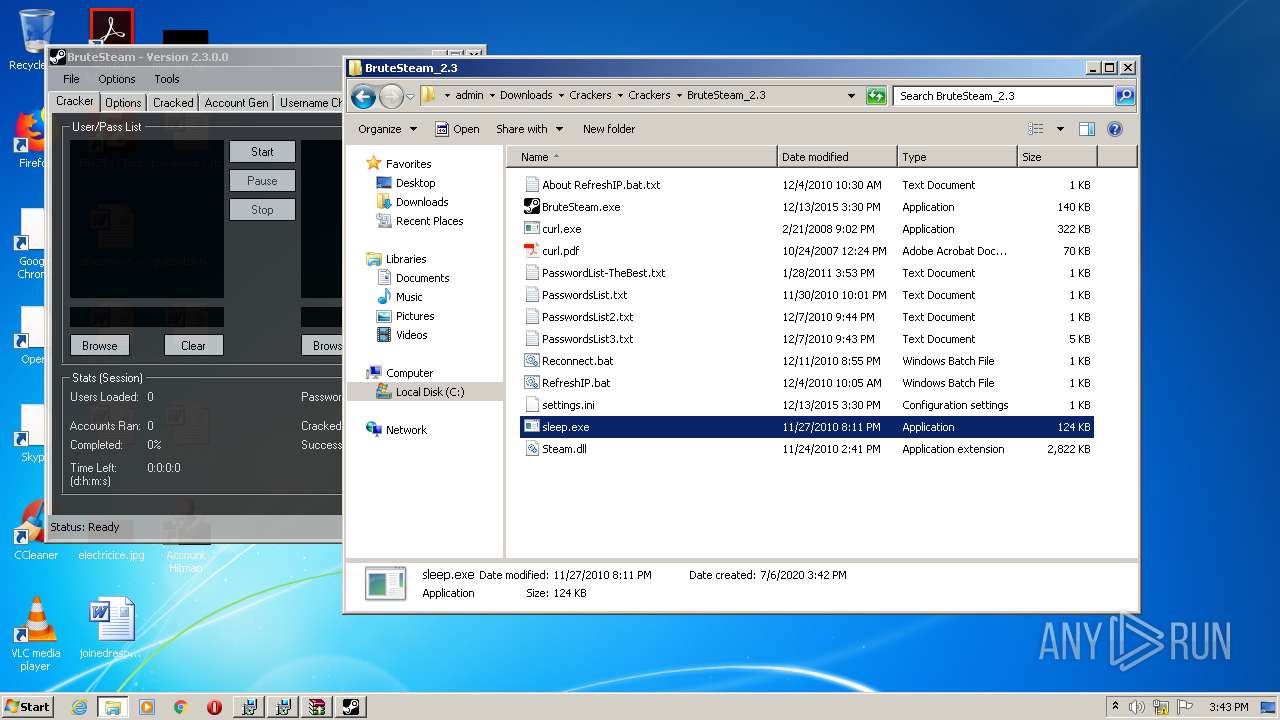
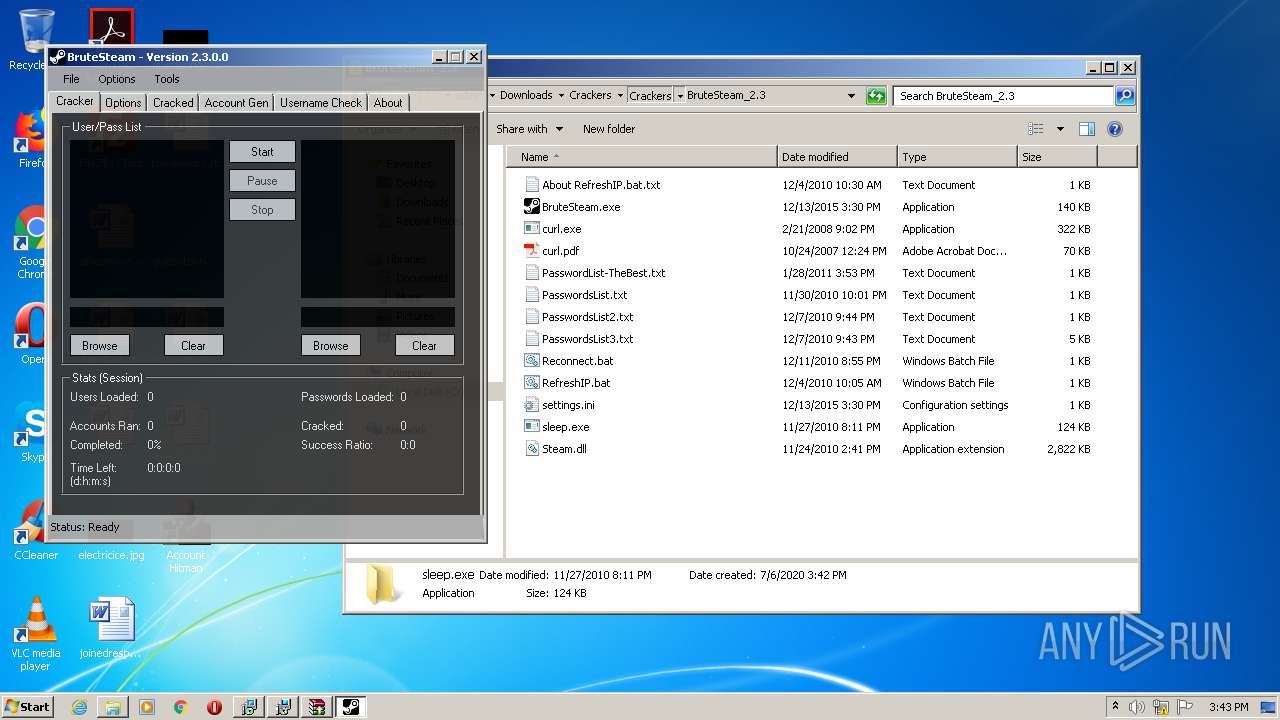
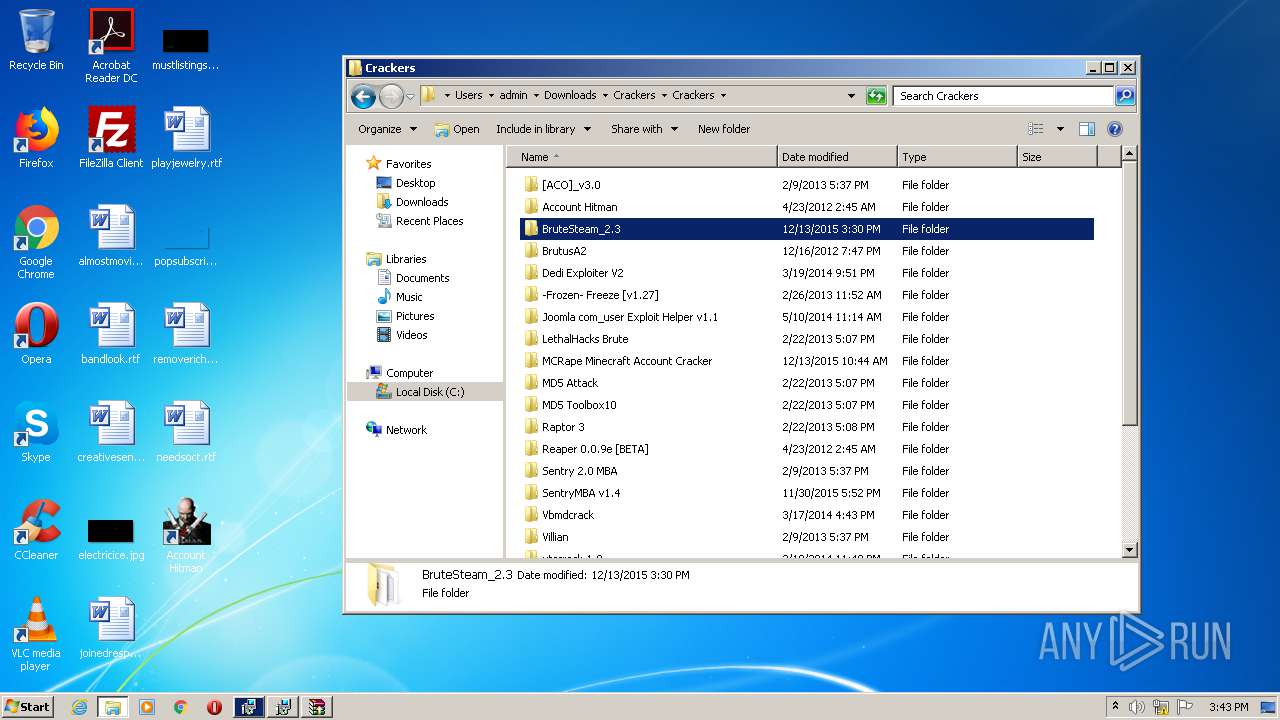
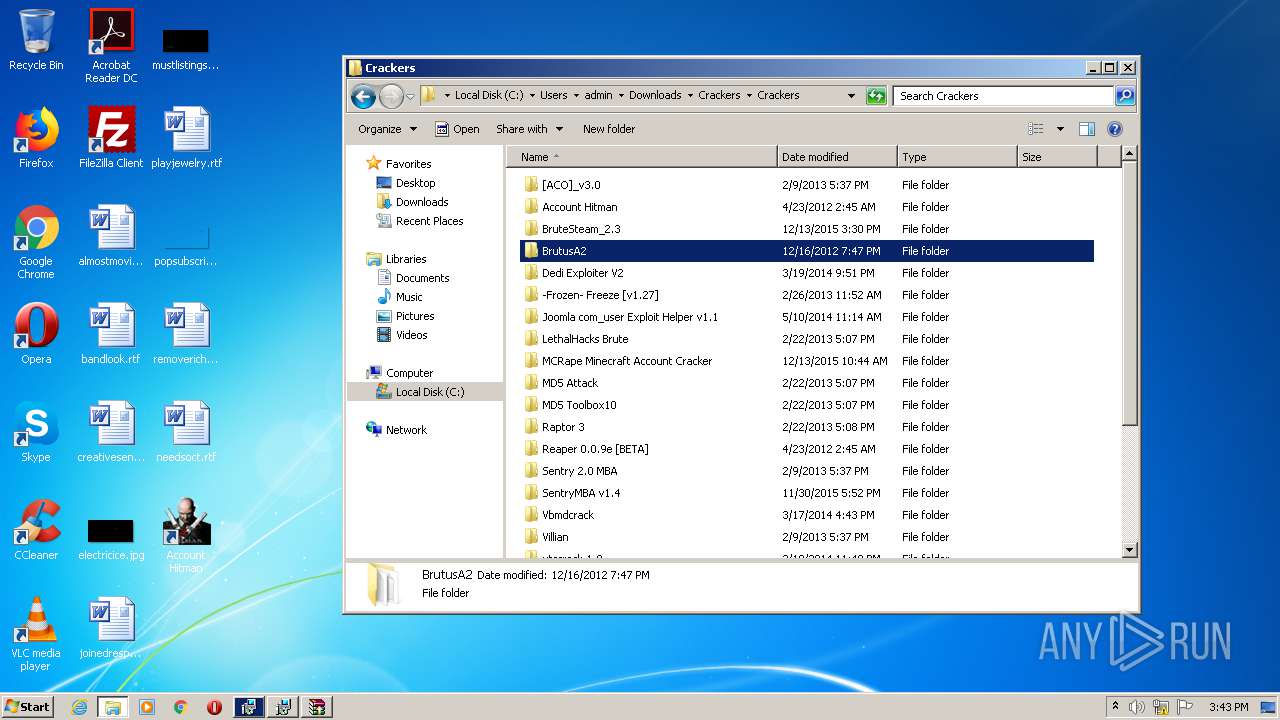
MALICIOUS
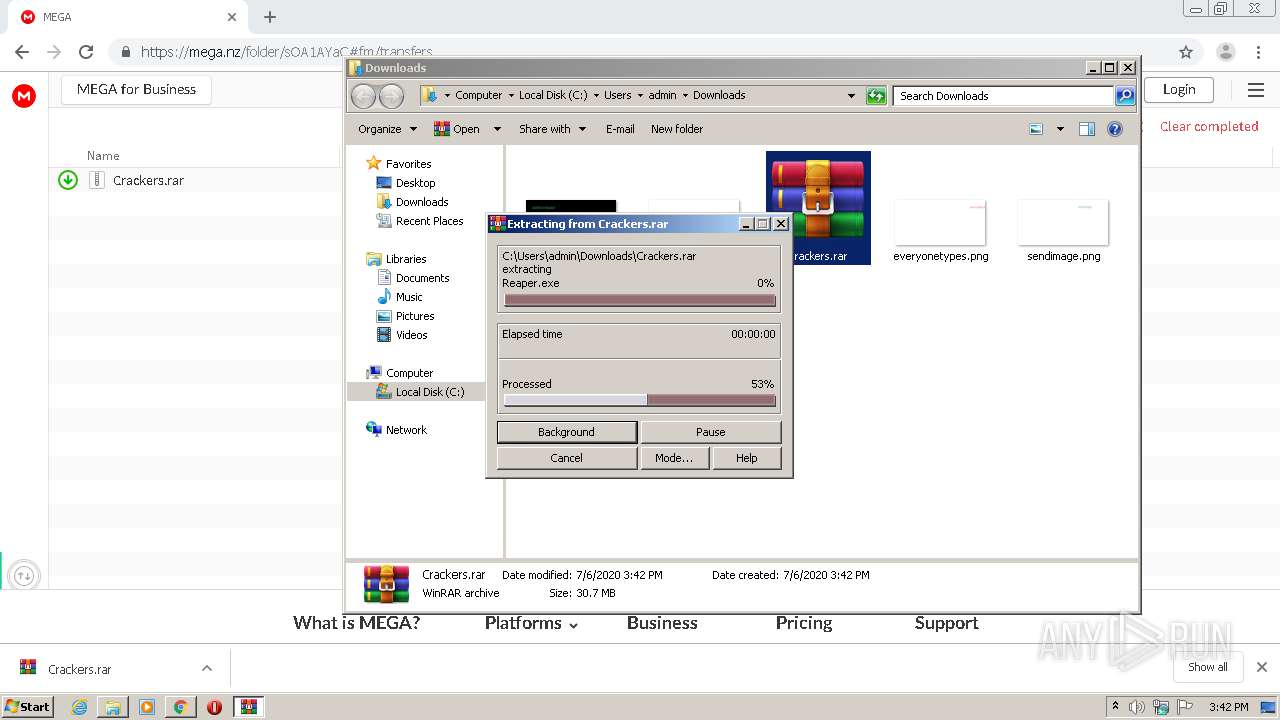
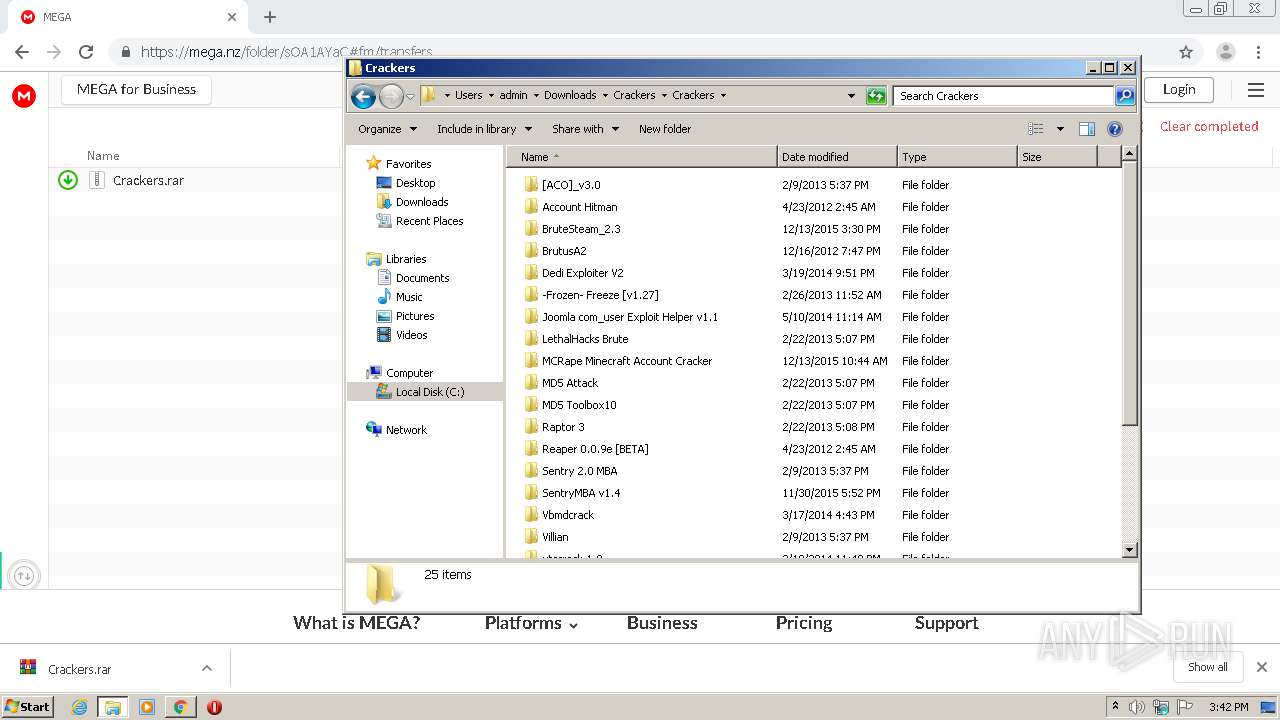
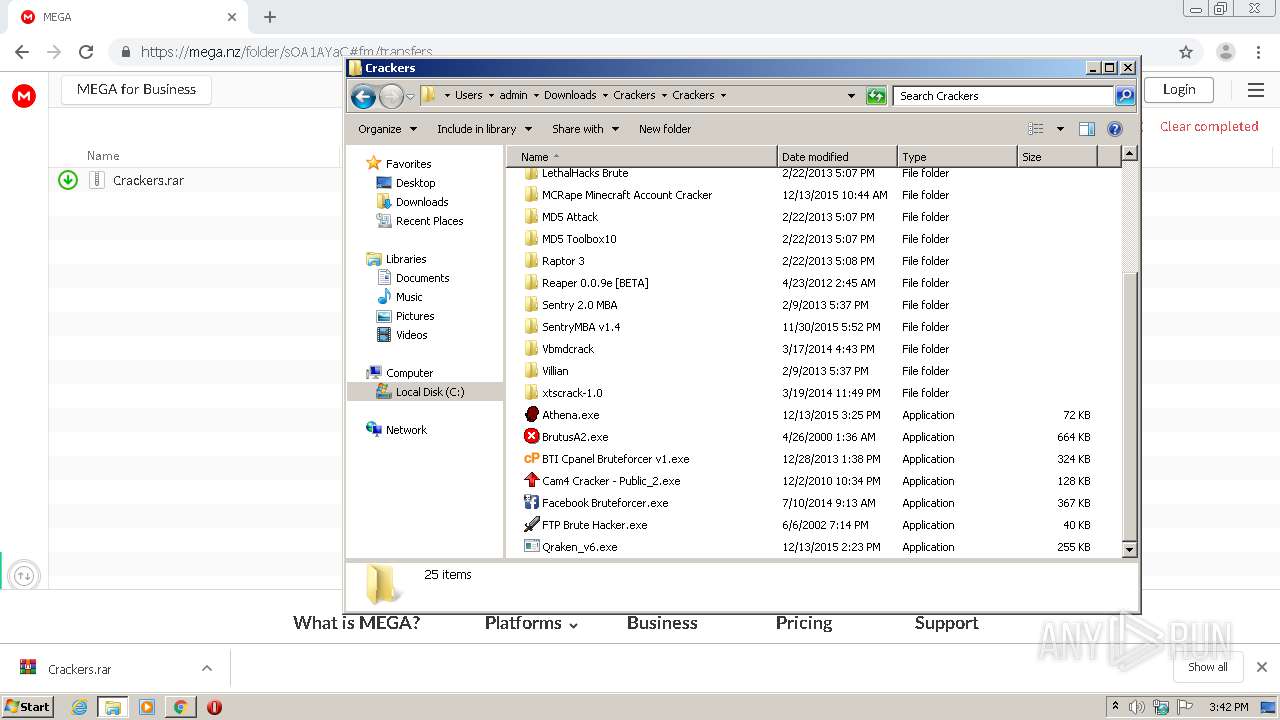
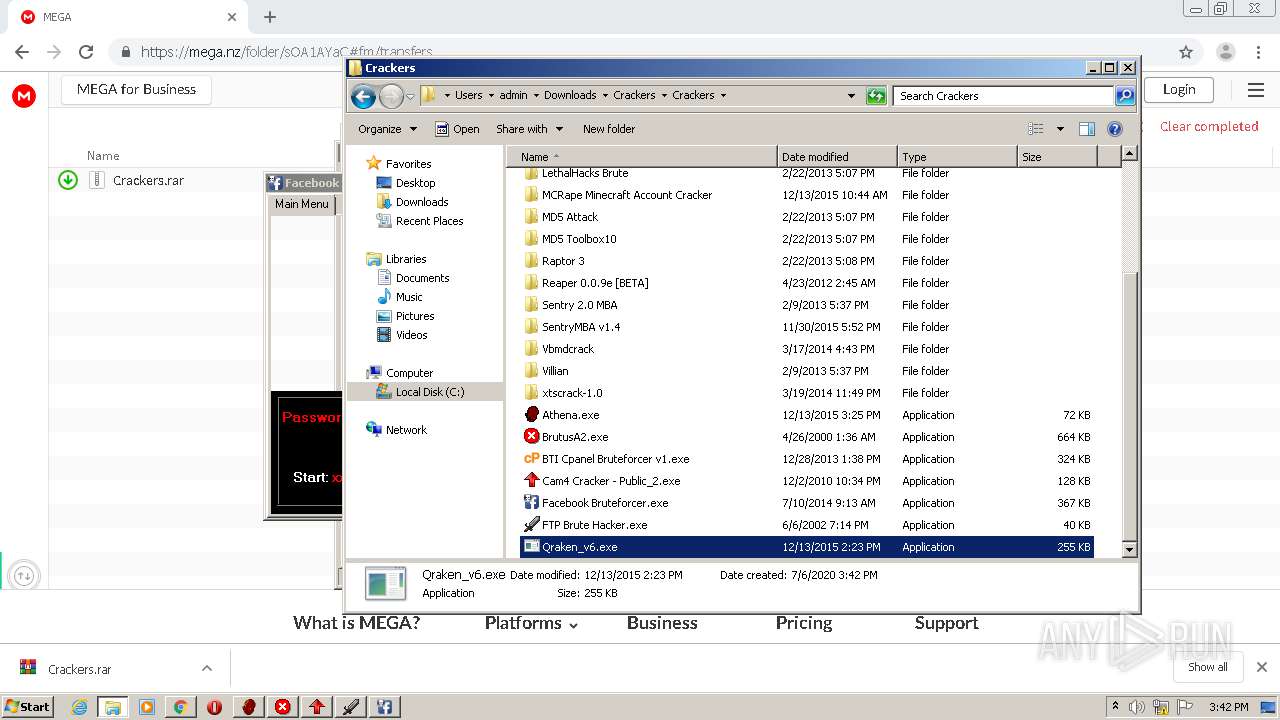
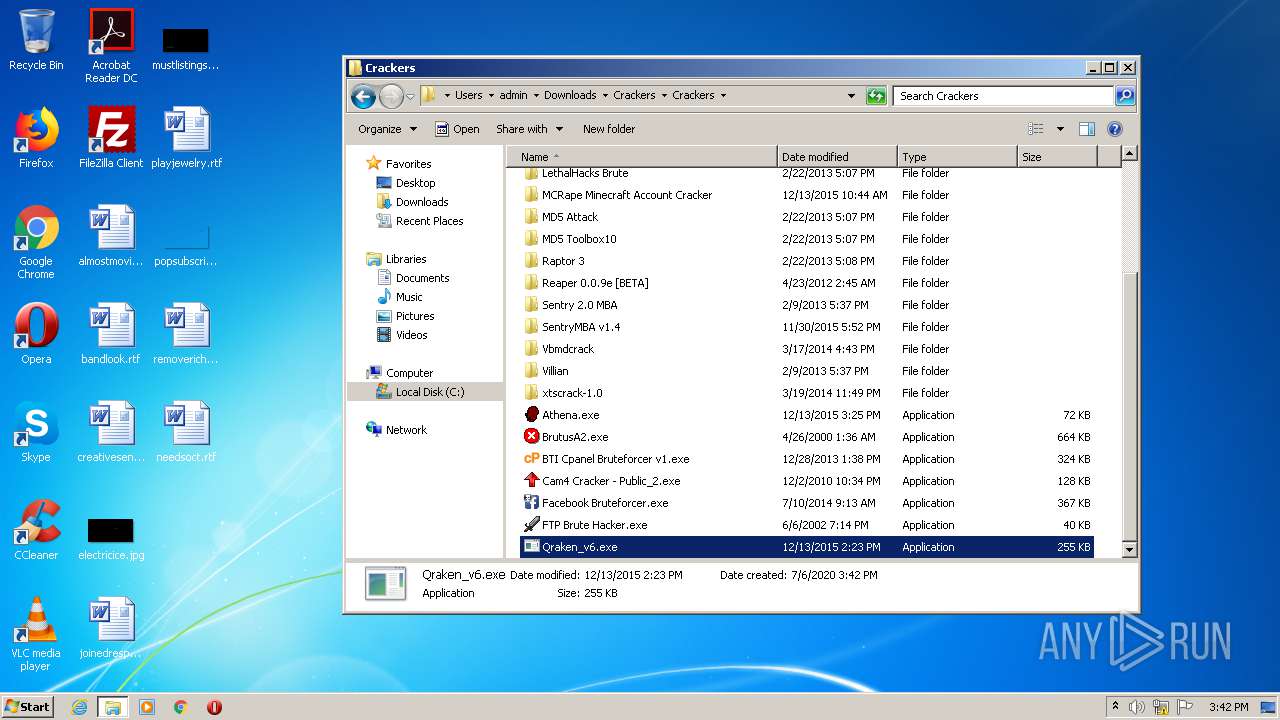
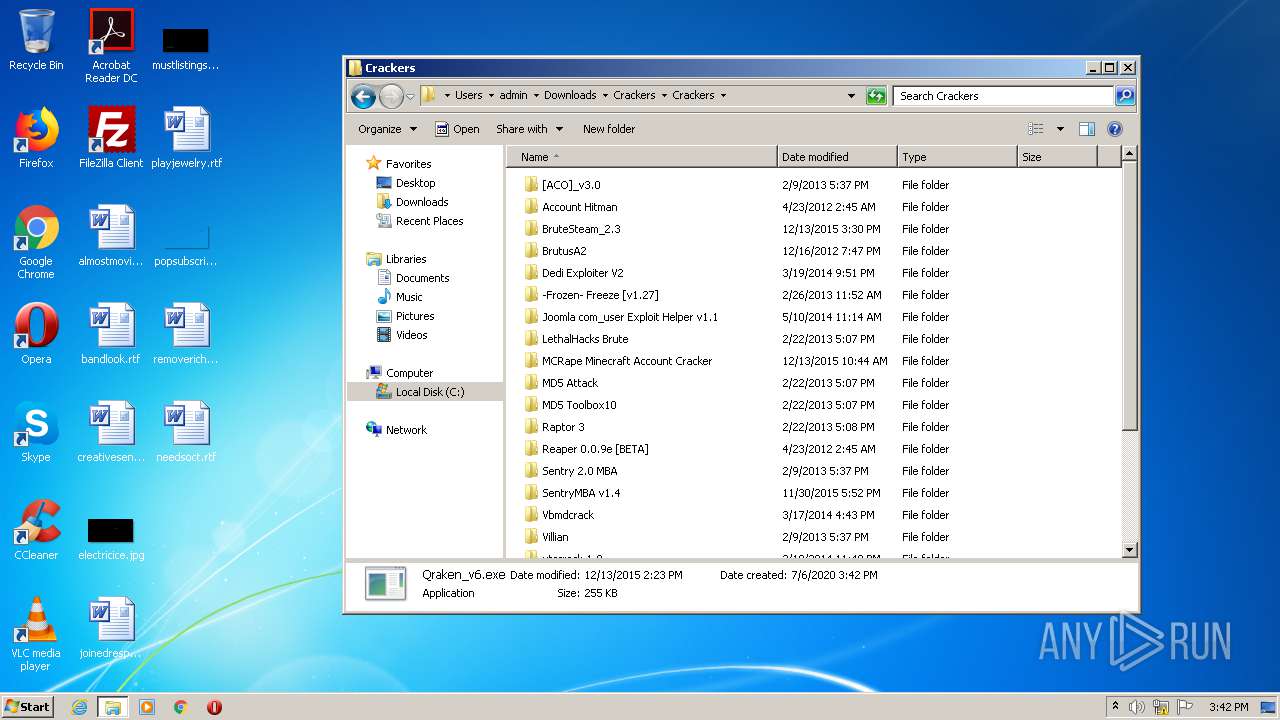
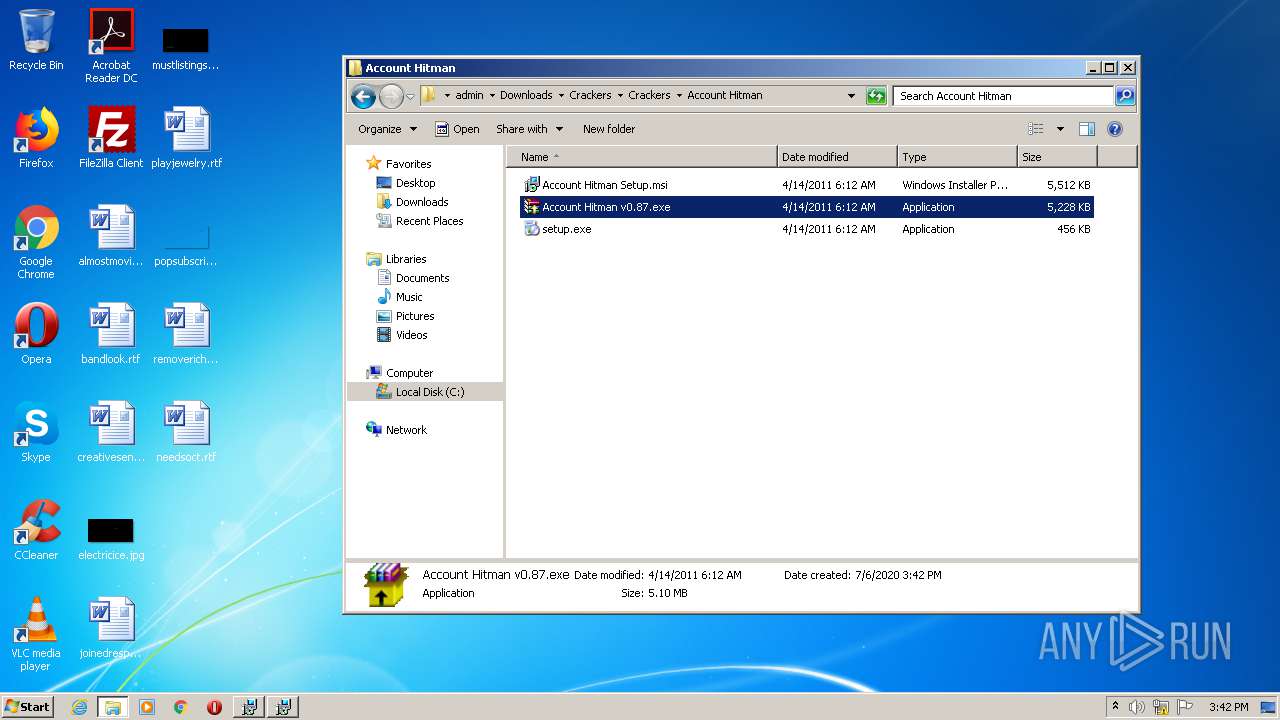
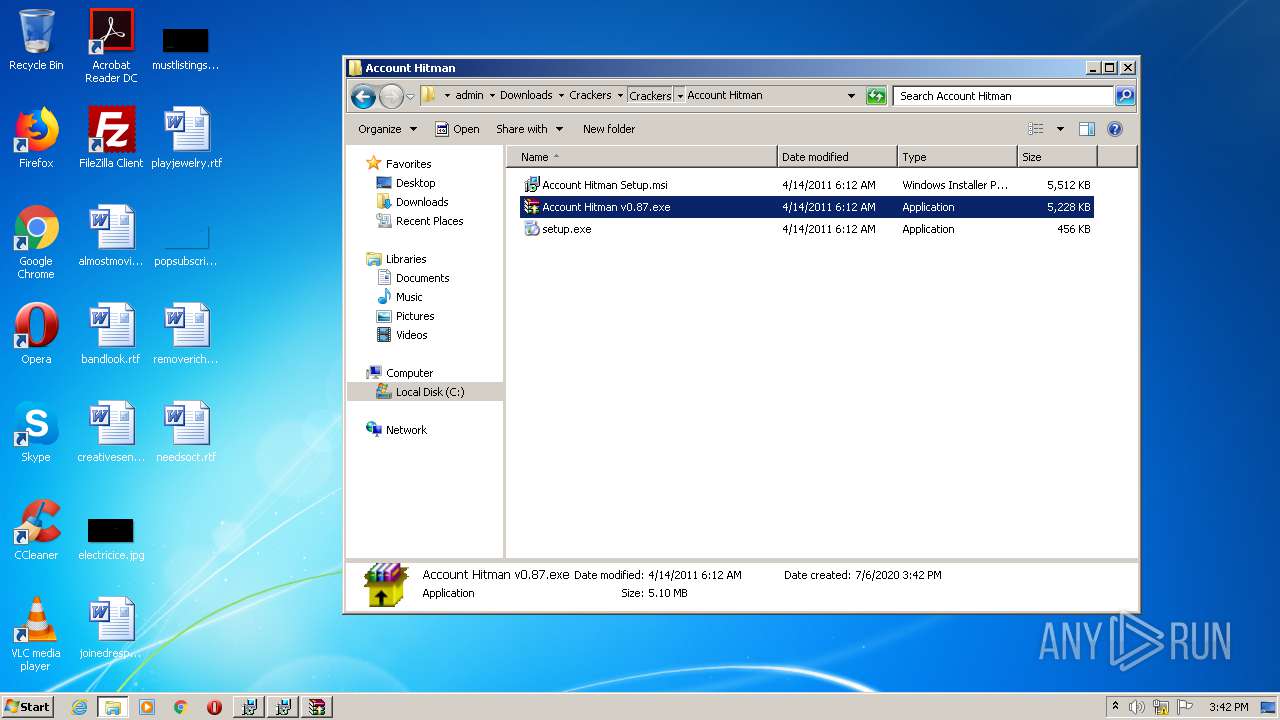
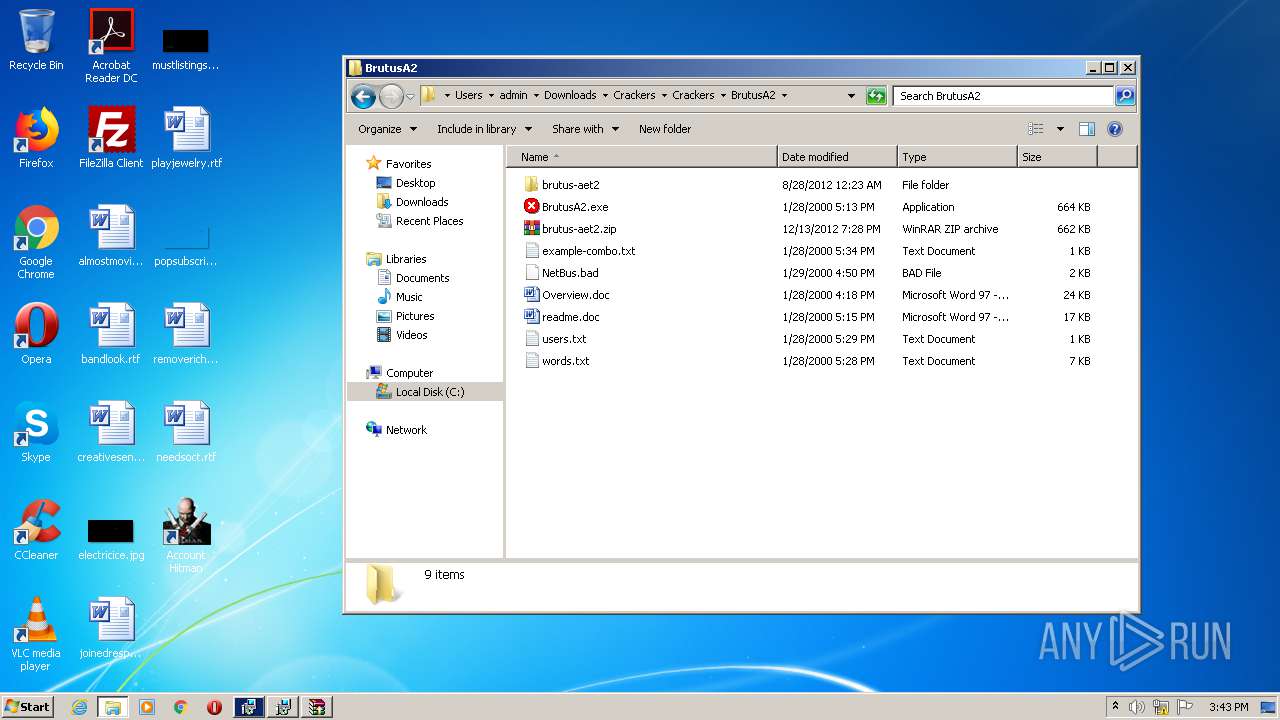
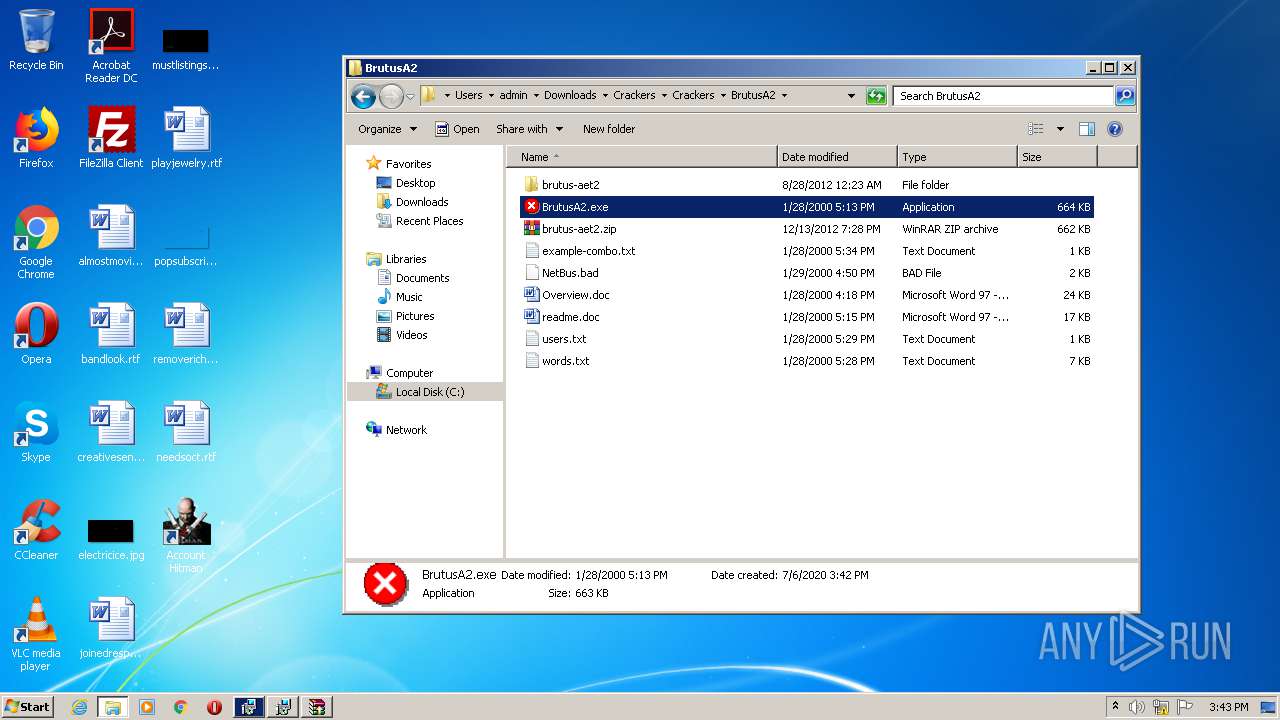
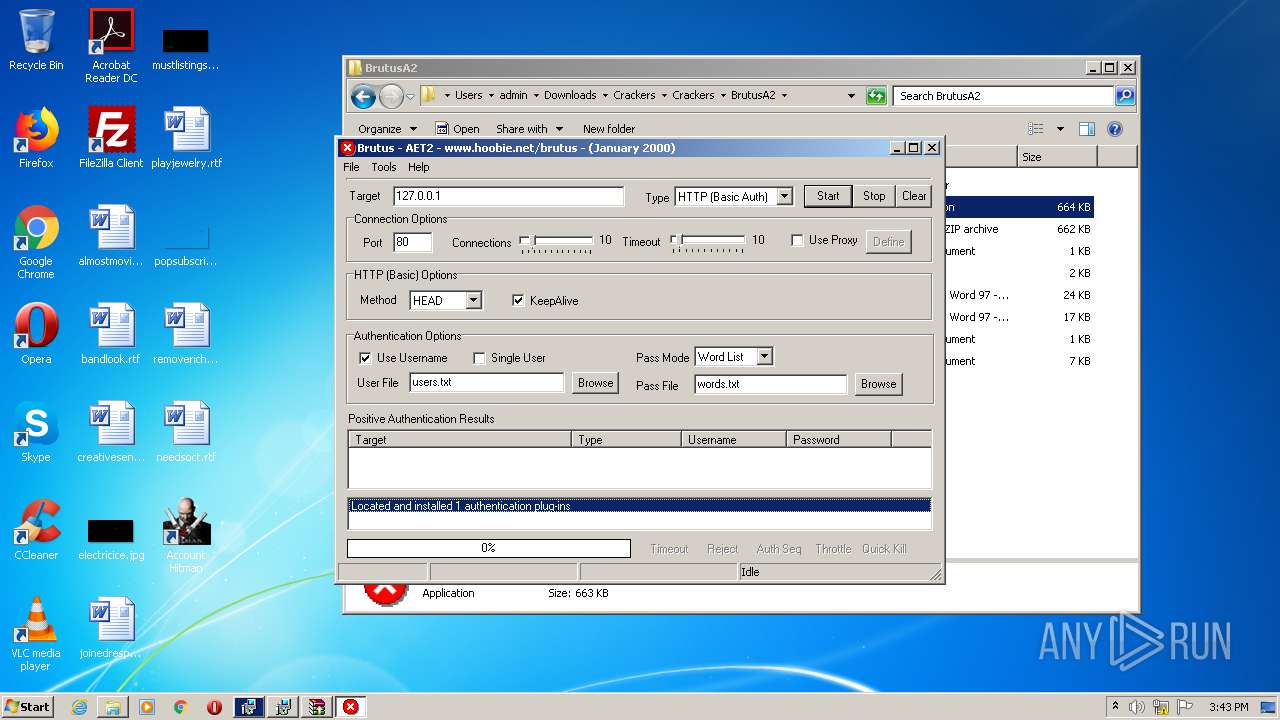
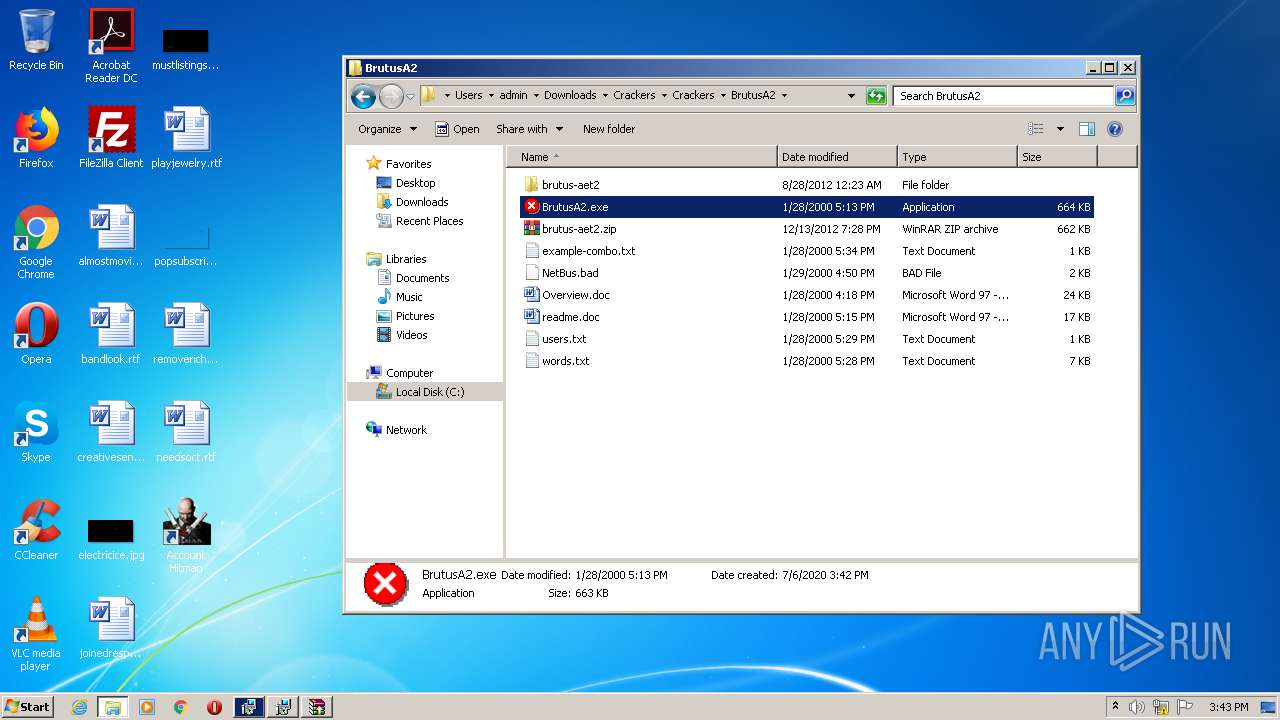
Application was dropped or rewritten from another process
- Athena.exe (PID: 2784)
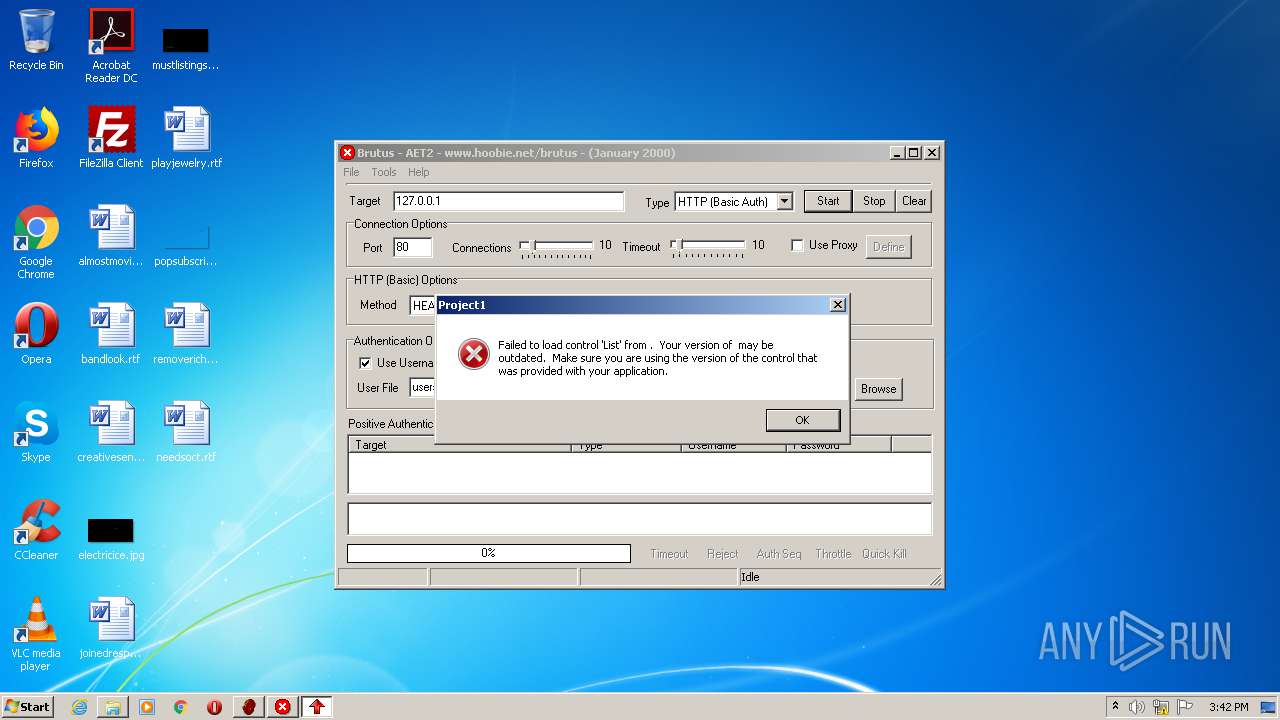
- BrutusA2.exe (PID: 2368)
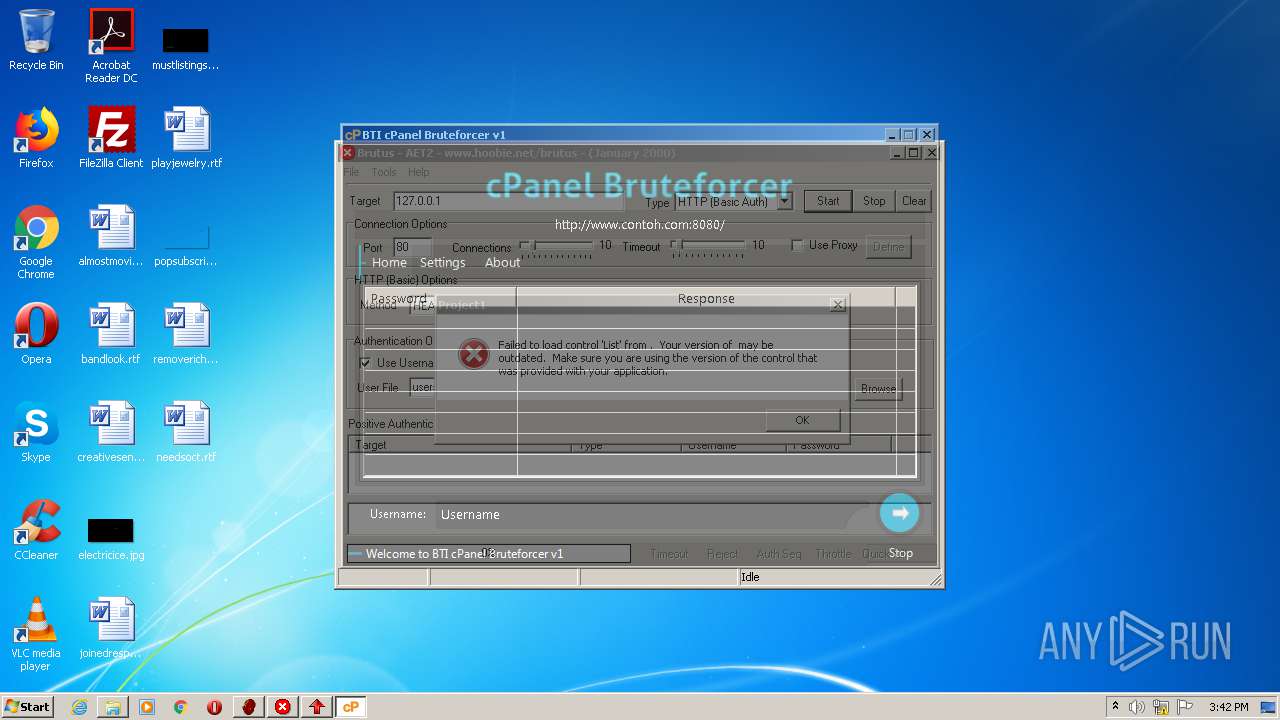
- BTI Cpanel Bruteforcer v1.exe (PID: 3844)
- Cam4 Cracker - Public_2.exe (PID: 1432)
- Facebook Bruteforcer.exe (PID: 1476)
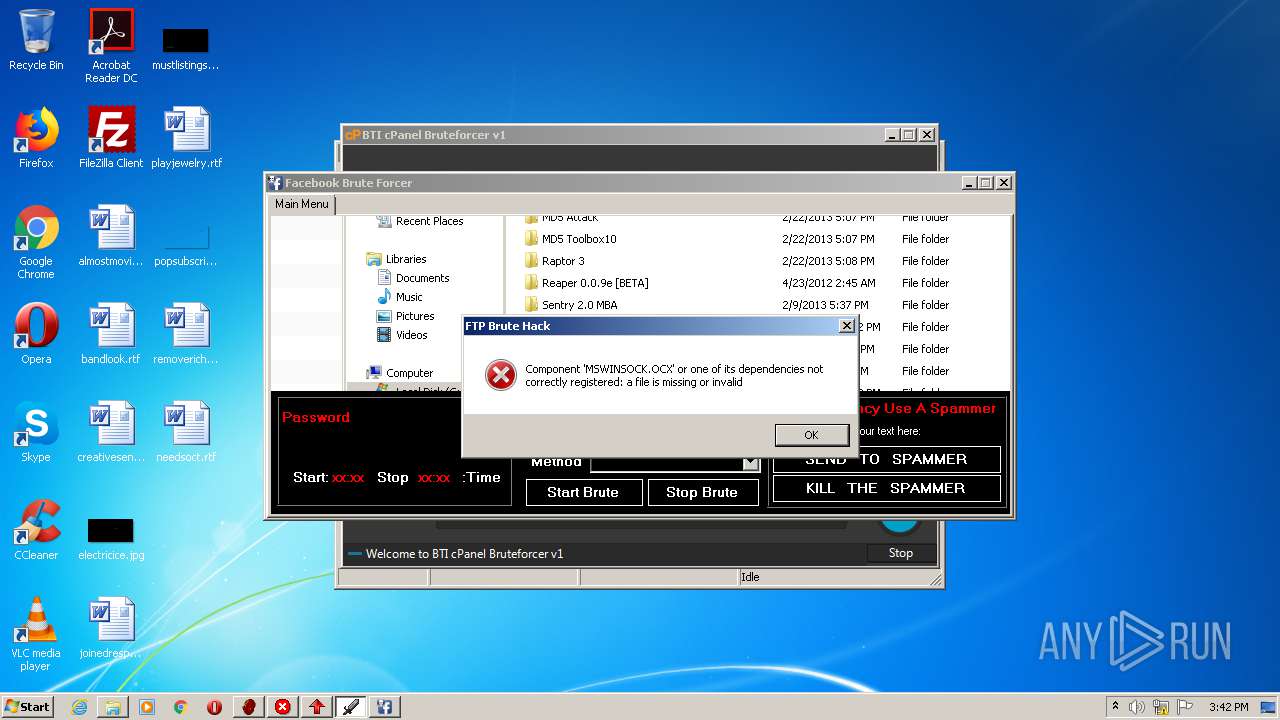
- FTP Brute Hacker.exe (PID: 3372)
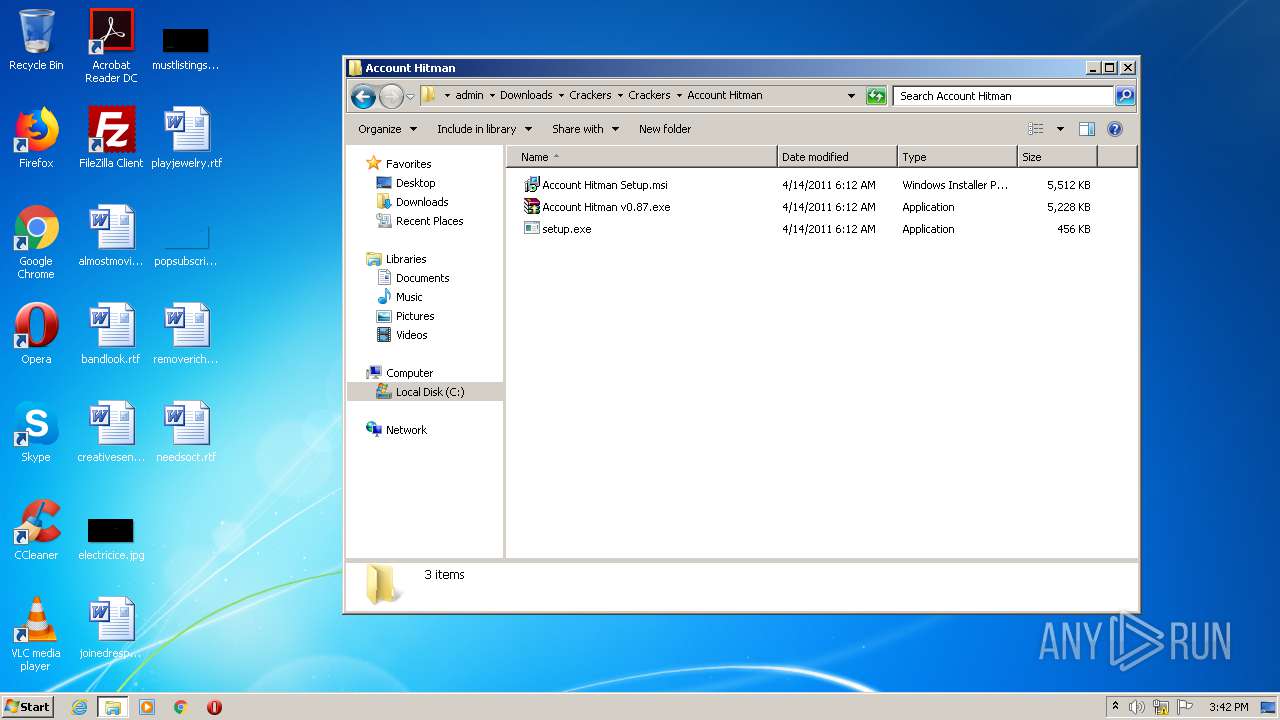
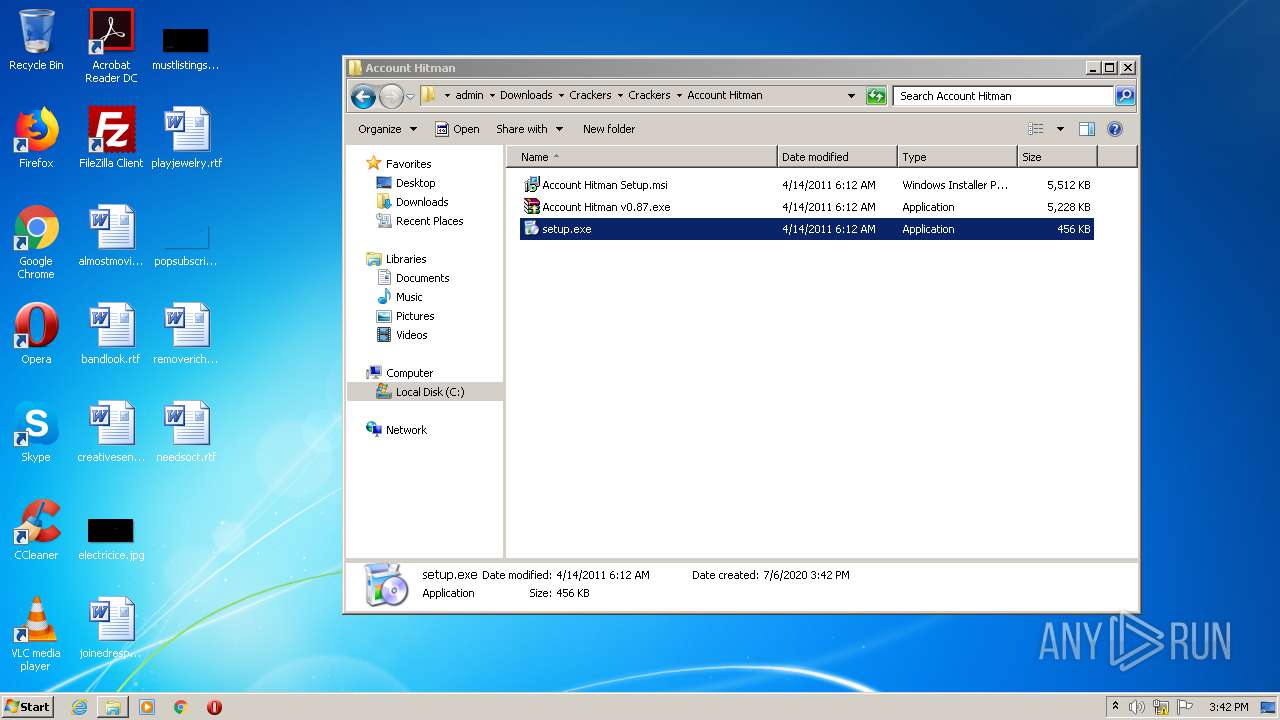
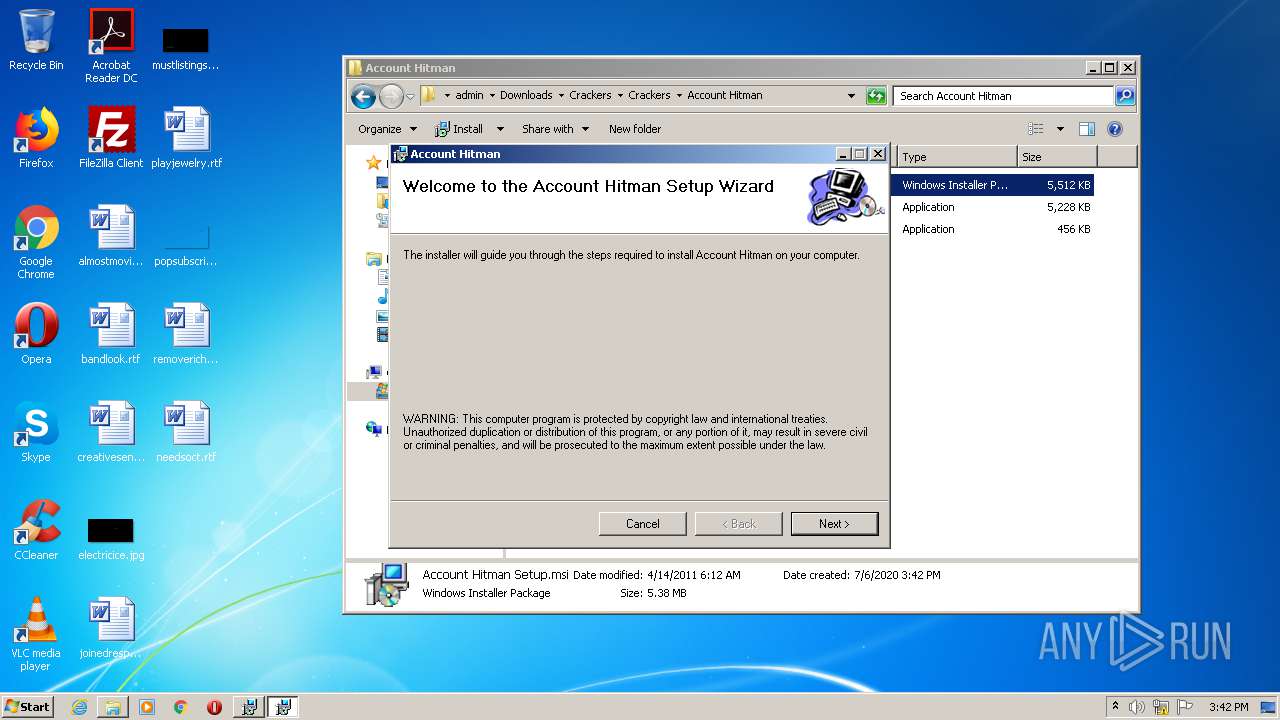
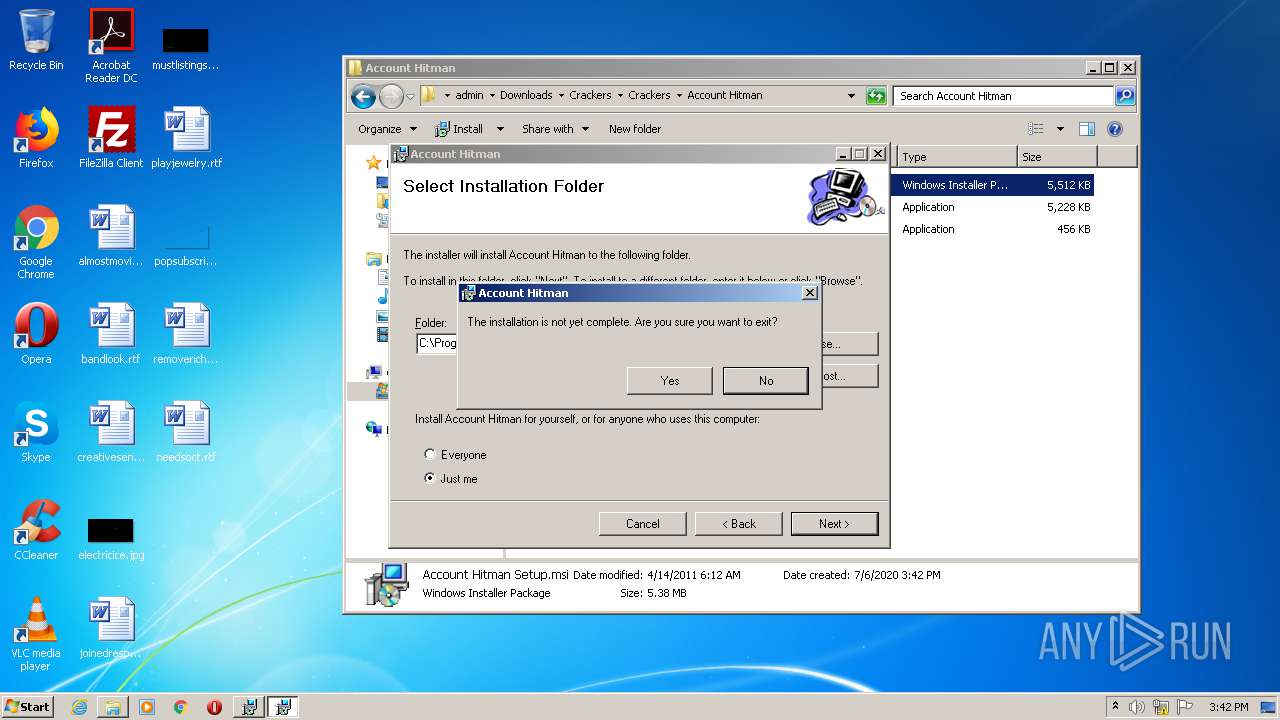
- setup.exe (PID: 2148)
- Account Hitman v0.87.exe (PID: 4008)
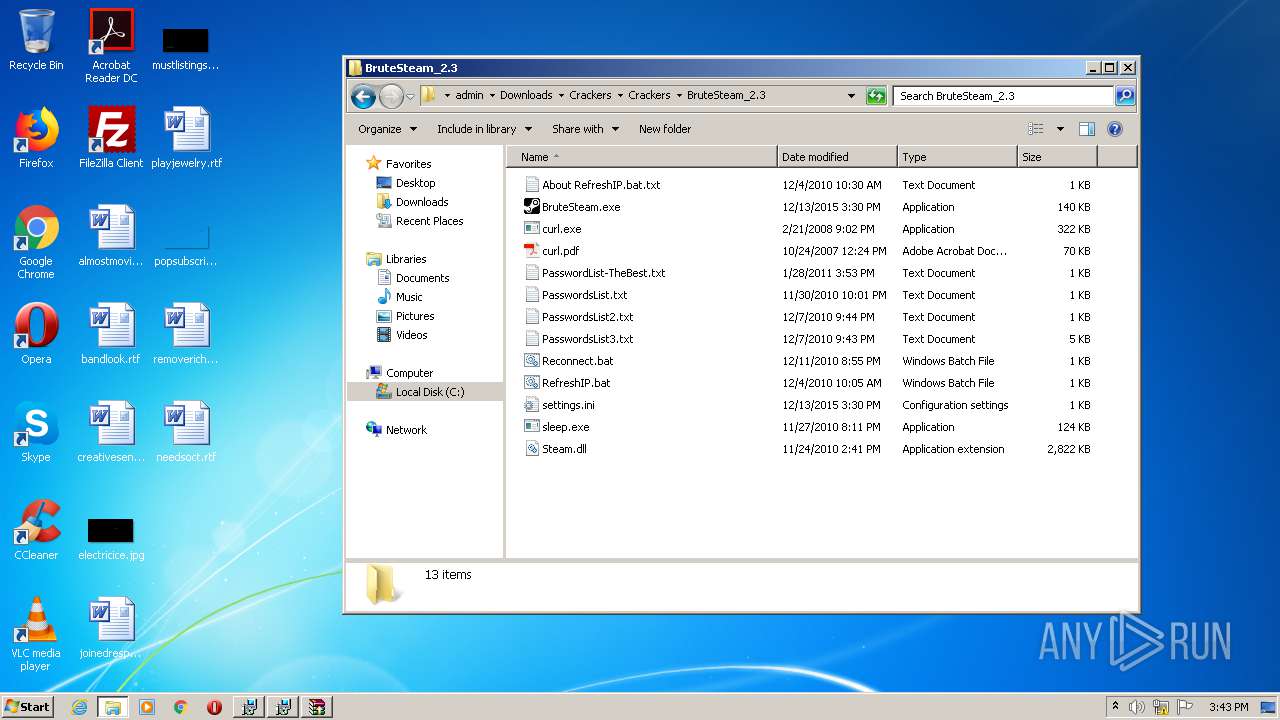
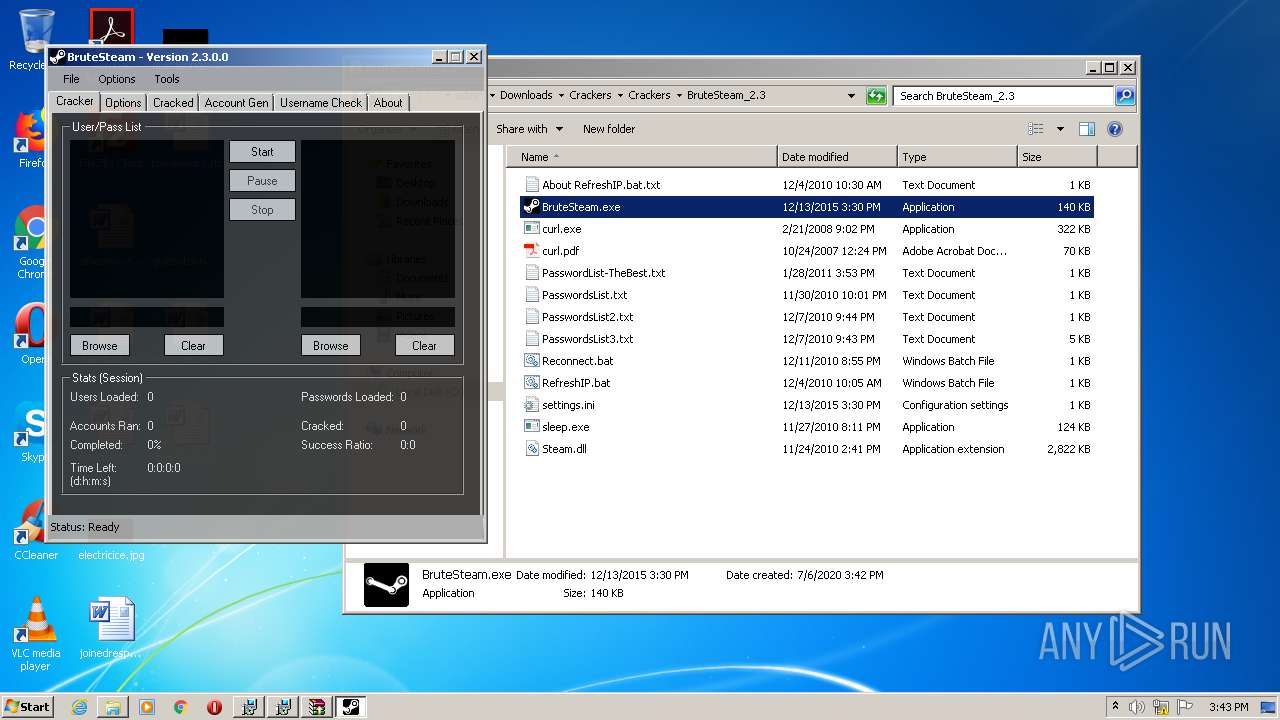
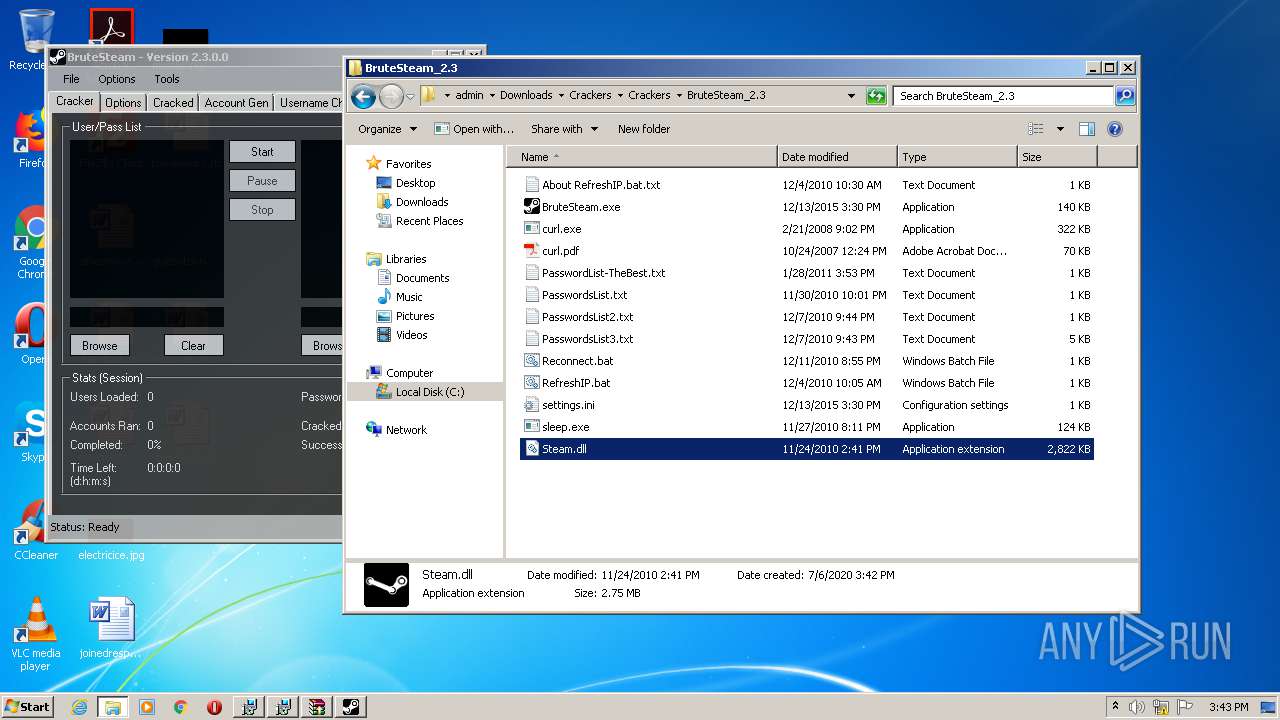
- BruteSteam.exe (PID: 3812)
- sleep.exe (PID: 2296)
- BrutusA2.exe (PID: 2504)
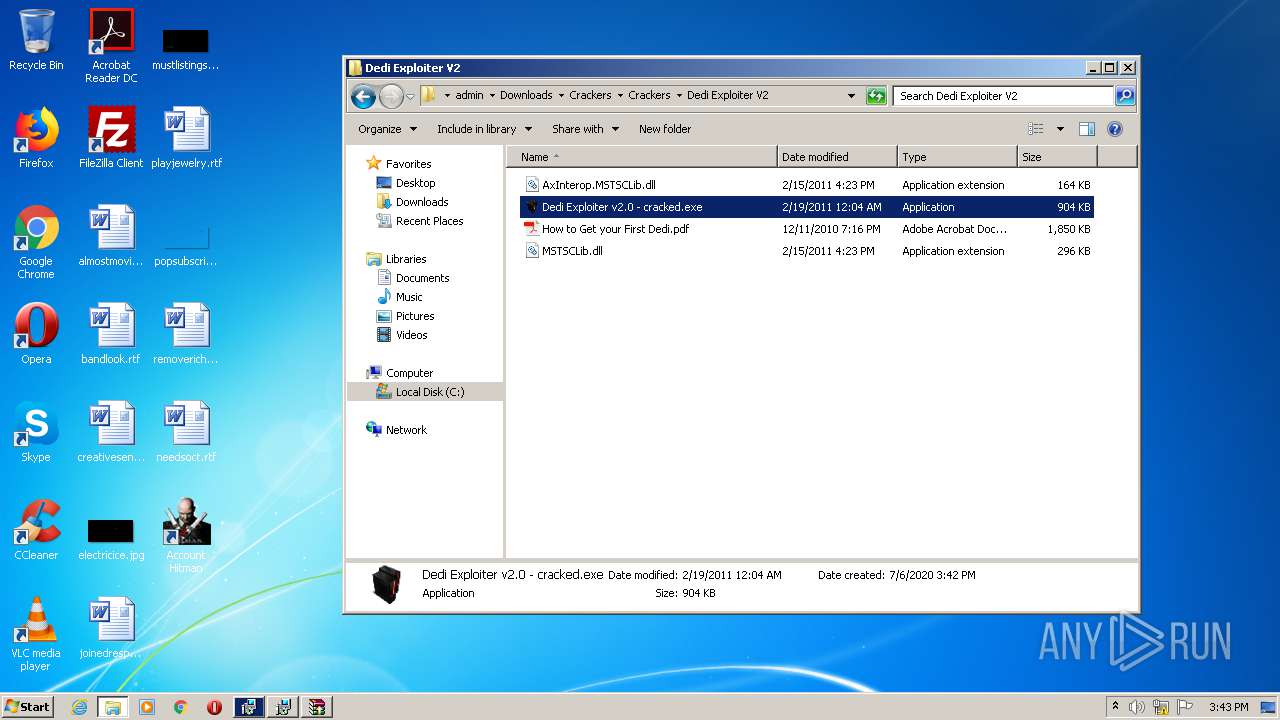
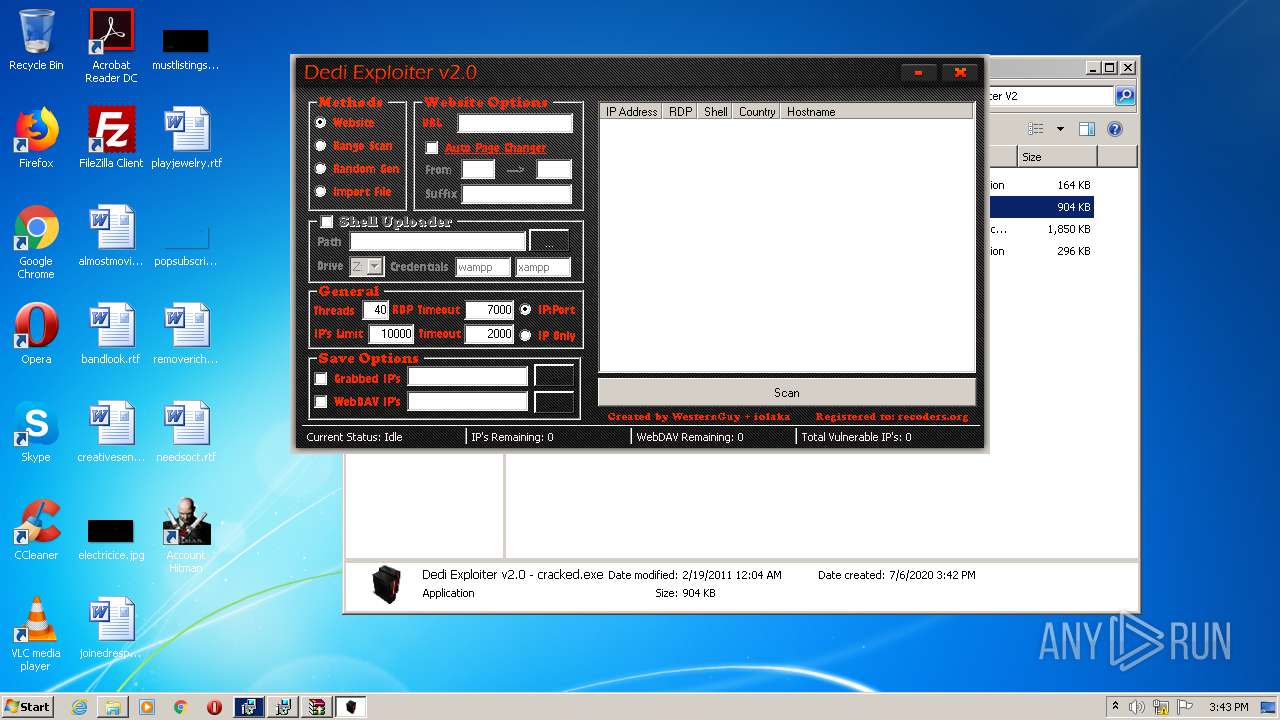
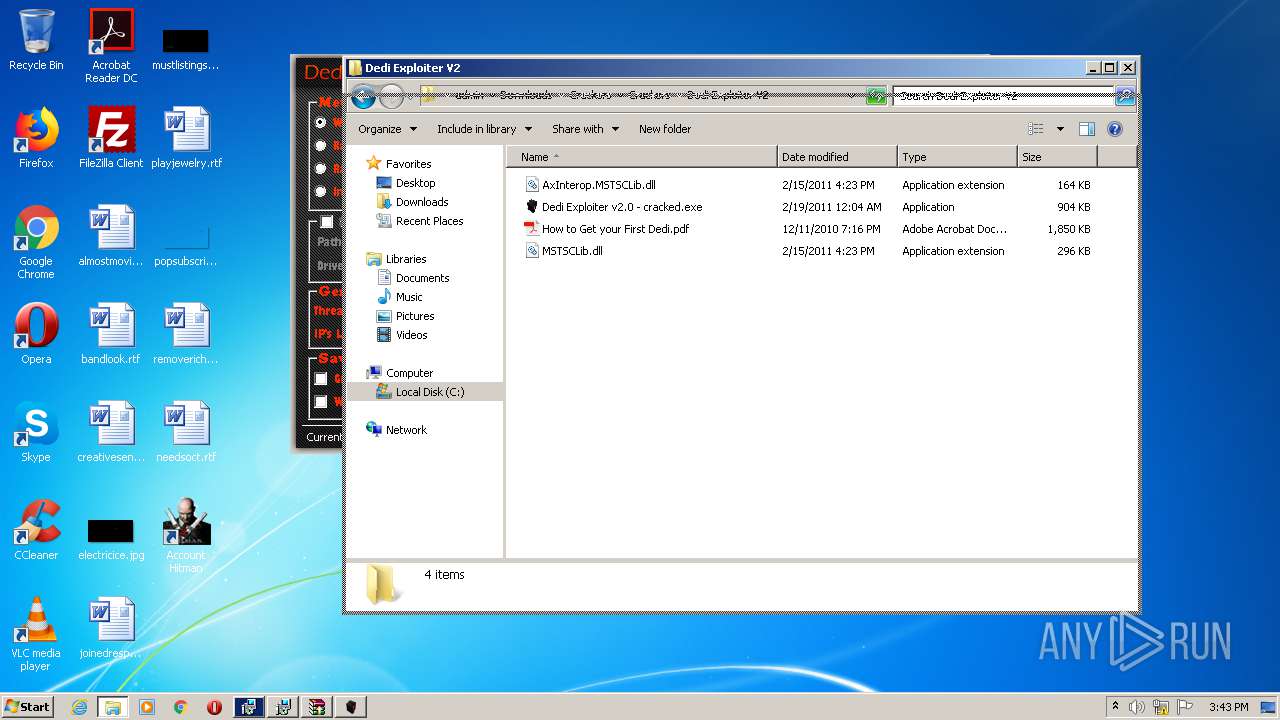
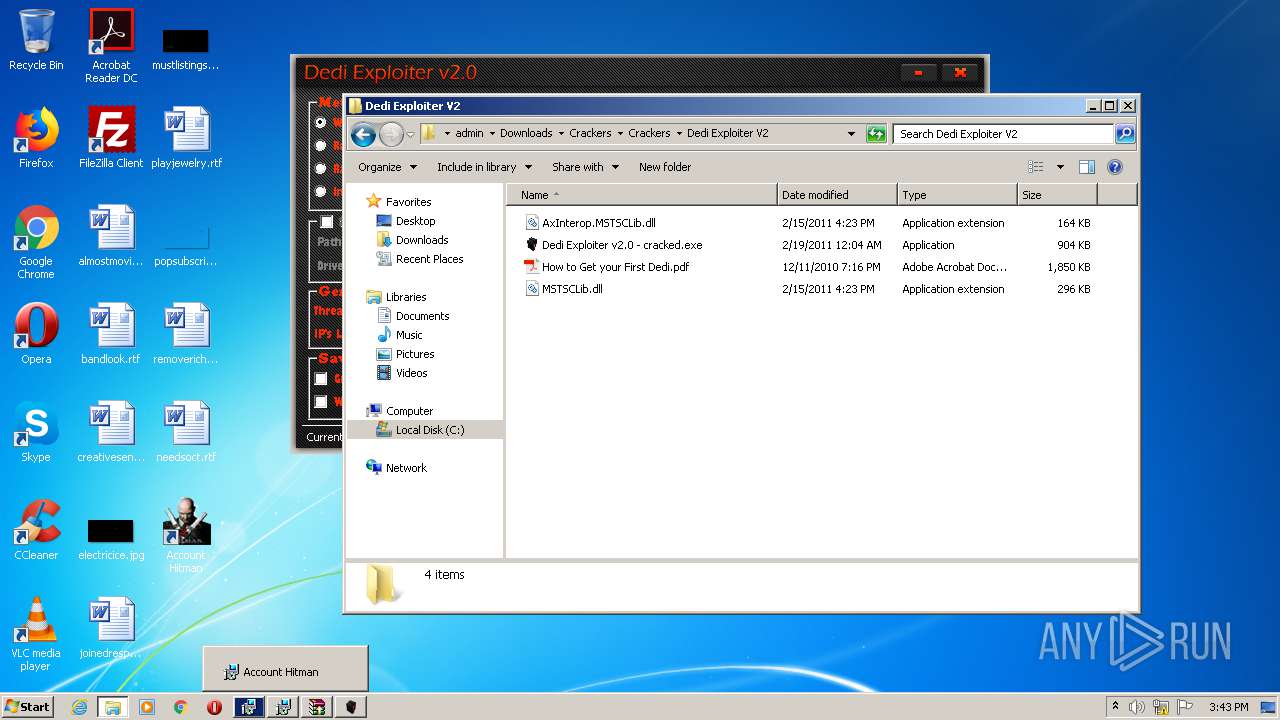
- Dedi Exploiter v2.0 - cracked.exe (PID: 1928)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3564)
- explorer.exe (PID: 308)
- Dedi Exploiter v2.0 - cracked.exe (PID: 1928)
Actions looks like stealing of personal data
- explorer.exe (PID: 308)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2268)
Creates files in the user directory
- explorer.exe (PID: 308)
- msiexec.exe (PID: 4028)
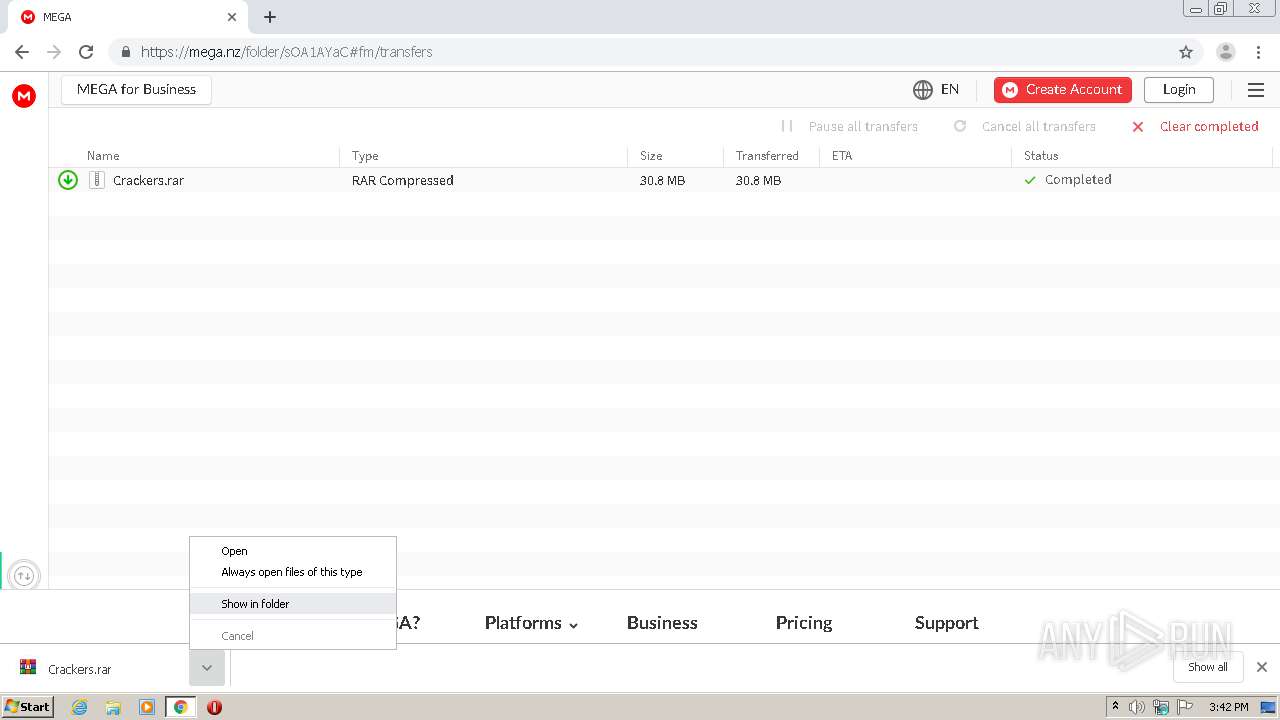
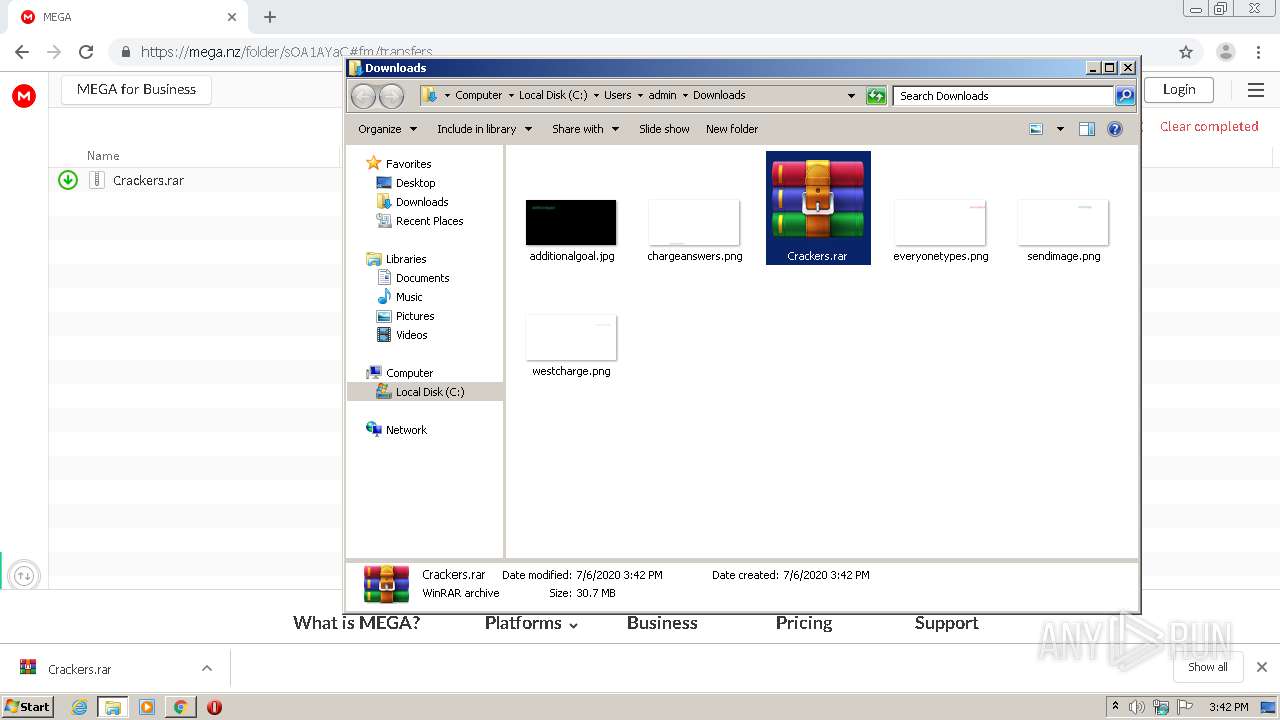
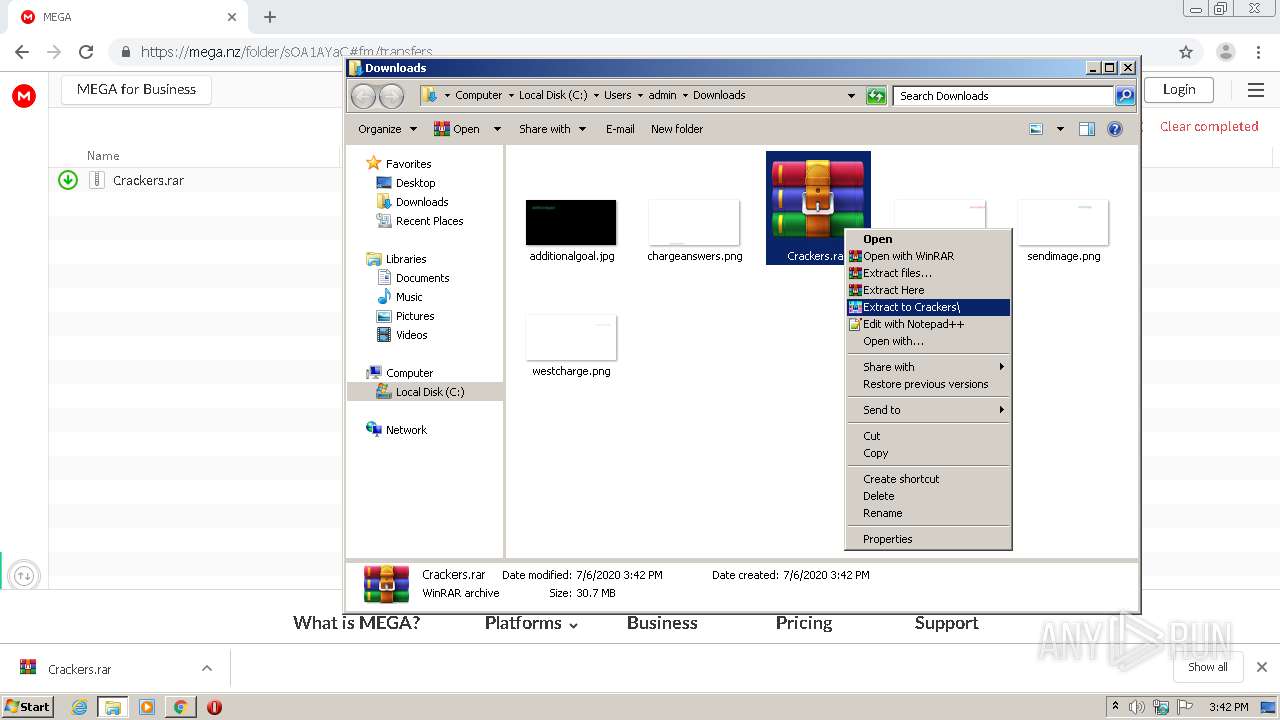
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3444)
- msiexec.exe (PID: 3912)
- msiexec.exe (PID: 3736)
- msiexec.exe (PID: 4028)
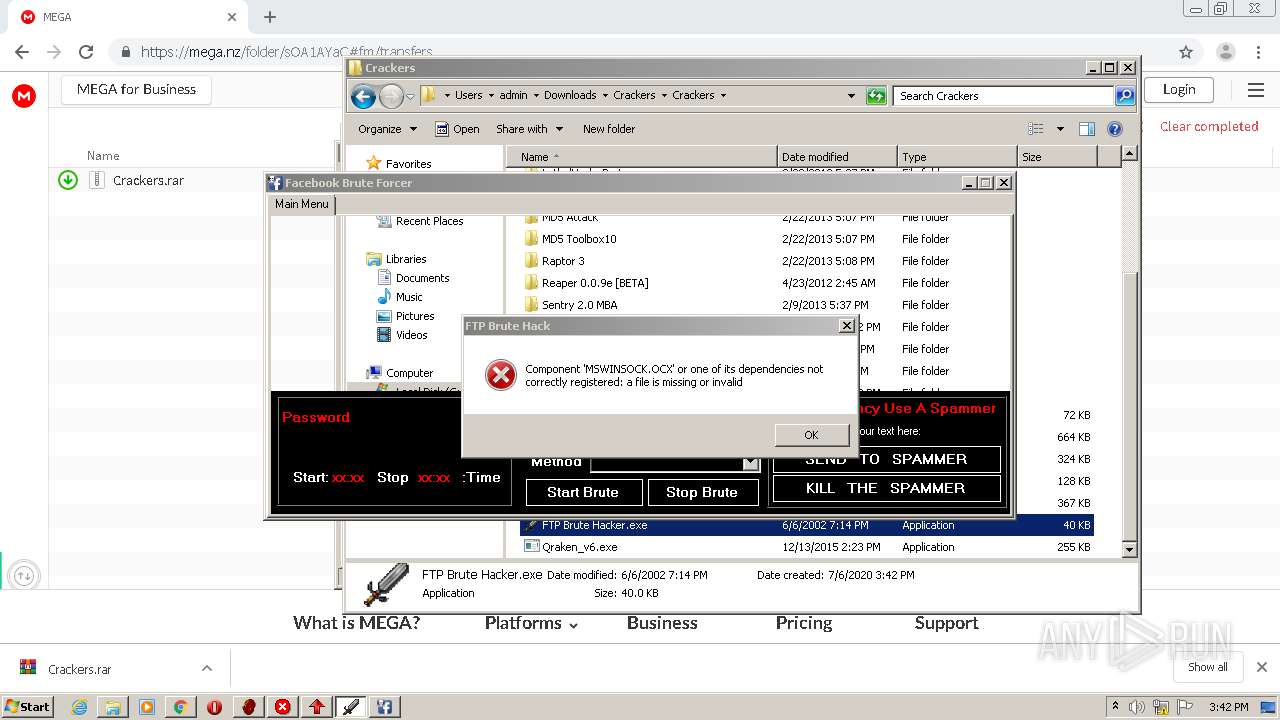
Reads internet explorer settings
- Facebook Bruteforcer.exe (PID: 1476)
- Account Hitman v0.87.exe (PID: 4008)
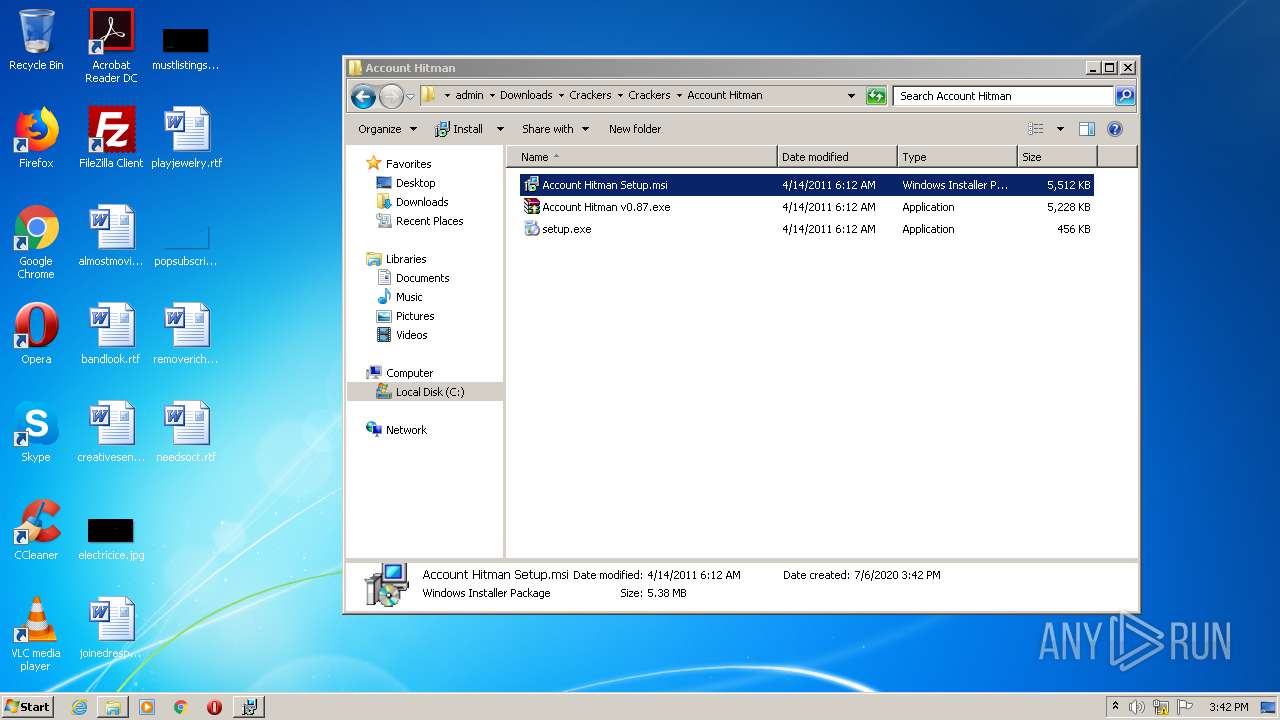
Executed as Windows Service
- vssvc.exe (PID: 4068)
Reads Internet Cache Settings
- Account Hitman v0.87.exe (PID: 4008)
- Facebook Bruteforcer.exe (PID: 1476)
Starts Microsoft Installer
- explorer.exe (PID: 308)
INFO
Application launched itself
- chrome.exe (PID: 2268)
- msiexec.exe (PID: 4028)
Reads the hosts file
- chrome.exe (PID: 2268)
- chrome.exe (PID: 1660)
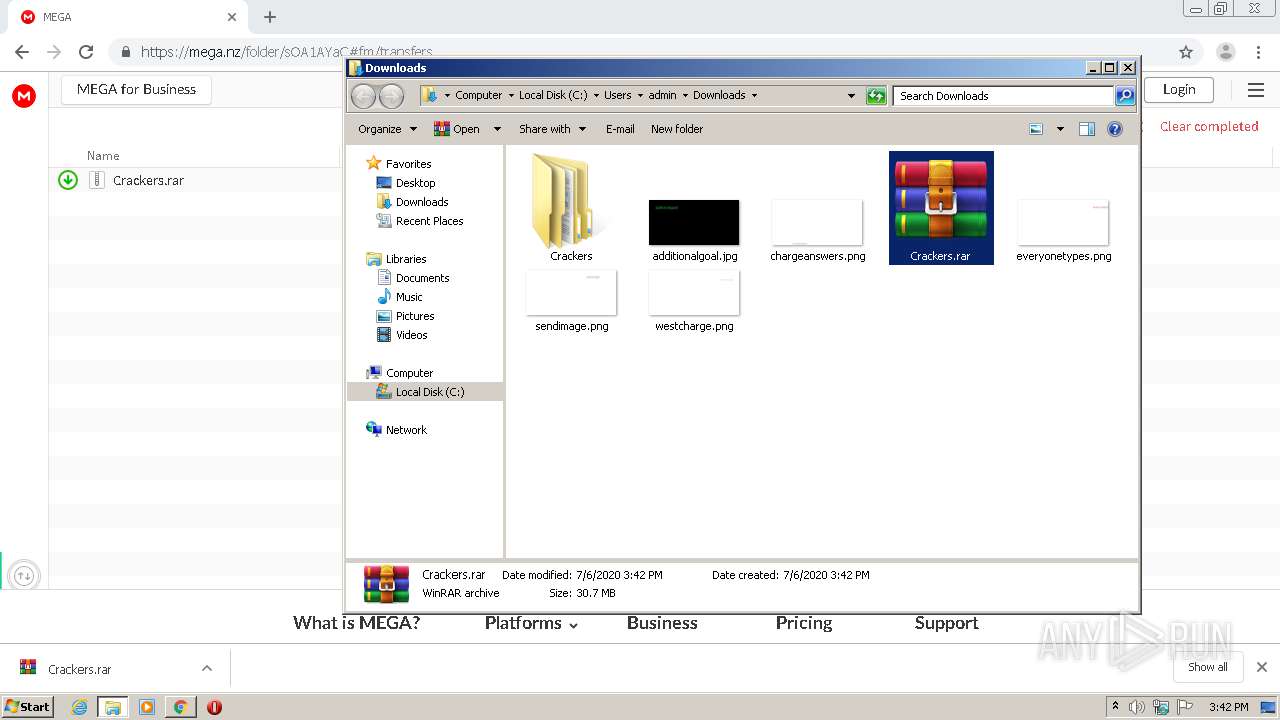
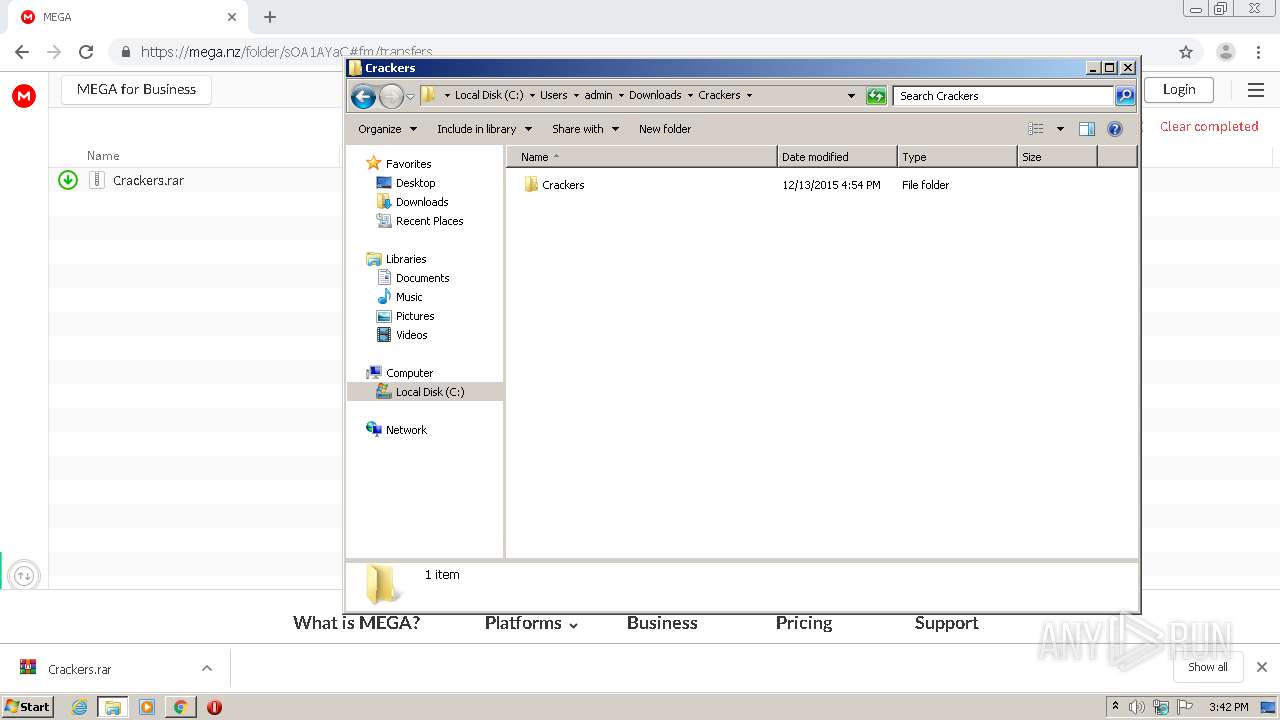
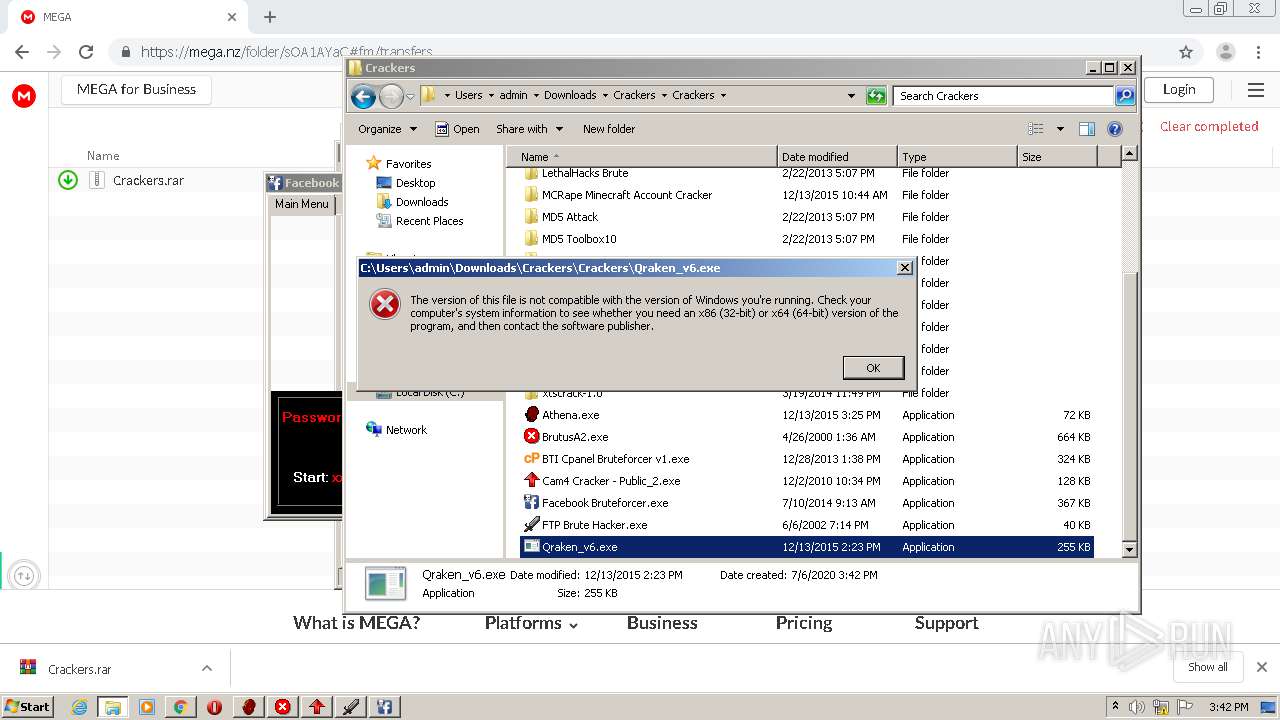
Manual execution by user
- WinRAR.exe (PID: 3444)
- Athena.exe (PID: 2784)
- BrutusA2.exe (PID: 2368)
- BTI Cpanel Bruteforcer v1.exe (PID: 3844)
- Cam4 Cracker - Public_2.exe (PID: 1432)
- Facebook Bruteforcer.exe (PID: 1476)
- Account Hitman v0.87.exe (PID: 4008)
- msiexec.exe (PID: 3736)
- FTP Brute Hacker.exe (PID: 3372)
- setup.exe (PID: 2148)
- BruteSteam.exe (PID: 3812)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3444)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 1440)
- MsiExec.exe (PID: 860)
- MsiExec.exe (PID: 2884)
Reads settings of System Certificates
- Facebook Bruteforcer.exe (PID: 1476)
Low-level read access rights to disk partition
- vssvc.exe (PID: 4068)
Dropped object may contain TOR URL's
- Facebook Bruteforcer.exe (PID: 1476)
Creates files in the program directory
- msiexec.exe (PID: 4028)
Creates a software uninstall entry
- msiexec.exe (PID: 4028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
95
Monitored processes
48
Malicious processes
11
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,3545986063666226138,10574780786035347883,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12370442906510247258 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,3545986063666226138,10574780786035347883,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12377970237205876061 --mojo-platform-channel-handle=3932 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,3545986063666226138,10574780786035347883,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2602230524241984132 --mojo-platform-channel-handle=3912 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2276 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 860 | C:\Windows\system32\MsiExec.exe -Embedding 81D9343C5EBB6785B61B996EBA3CD1A8 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,3545986063666226138,10574780786035347883,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6012153258682403259 --mojo-platform-channel-handle=4636 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f68a9d0,0x6f68a9e0,0x6f68a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1432 | "C:\Users\admin\Downloads\Crackers\Crackers\Cam4 Cracker - Public_2.exe" | C:\Users\admin\Downloads\Crackers\Crackers\Cam4 Cracker - Public_2.exe | — | explorer.exe | |||||||||||
User: admin Company: Cairns'Development Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1440 | C:\Windows\system32\MsiExec.exe -Embedding CF24745156DB8127ADC40381465E0051 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 351
Read events
4 904
Write events
1 411
Delete events
36
Modification events
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (768) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2268-13238520089624750 |
Value: 259 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
76
Suspicious files
86
Text files
378
Unknown types
45
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F03381A-8DC.pma | — | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4276e414-ab17-4084-9ea2-0c6b464f4724.tmp | — | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF168aff.TMP | text | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF168b1e.TMP | text | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF168aff.TMP | text | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF168cd3.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
55
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1476 | Facebook Bruteforcer.exe | GET | 302 | 185.60.216.35:80 | http://www.facebook.com/ | IE | — | — | whitelisted |
1476 | Facebook Bruteforcer.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAvDFCfAY7E%2FPiG8%2BRSODrQ%3D | US | der | 471 b | whitelisted |
1476 | Facebook Bruteforcer.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA6O%2BBjVXZc2rpJ%2B516RAgc%3D | US | der | 471 b | whitelisted |
1476 | Facebook Bruteforcer.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
1660 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 527 b | whitelisted |
1660 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 532 b | whitelisted |
1660 | chrome.exe | GET | 200 | 159.148.69.143:80 | http://r4---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1594046274&mv=u&mvi=3&pl=24&shardbypass=yes | LV | crx | 293 Kb | whitelisted |
1660 | chrome.exe | GET | 200 | 159.148.69.141:80 | http://r2---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1594046274&mv=u&mvi=1&pl=24&shardbypass=yes | LV | crx | 823 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1660 | chrome.exe | 31.216.148.10:443 | mega.nz | Datacenter Luxembourg S.A. | LU | unknown |
1660 | chrome.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
1660 | chrome.exe | 172.217.16.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
1660 | chrome.exe | 172.217.21.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1660 | chrome.exe | 159.148.69.143:80 | r4---sn-a5uoxu-gpme.gvt1.com | LATNET SERVISS Ltd. | LV | whitelisted |
1660 | chrome.exe | 94.24.37.12:443 | gfs206n102.userstorage.mega.co.nz | — | RO | unknown |
1660 | chrome.exe | 172.217.18.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1660 | chrome.exe | 89.44.169.134:443 | eu.static.mega.co.nz | Datacenter Luxembourg S.A. | LU | suspicious |
1660 | chrome.exe | 172.217.18.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1476 | Facebook Bruteforcer.exe | 185.60.216.35:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
mega.nz |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
g.api.mega.co.nz |
| shared |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |