| File name: | Compass Browser (1).exe |
| Full analysis: | https://app.any.run/tasks/b293a31a-2deb-4248-a1cb-964ec26b1218 |
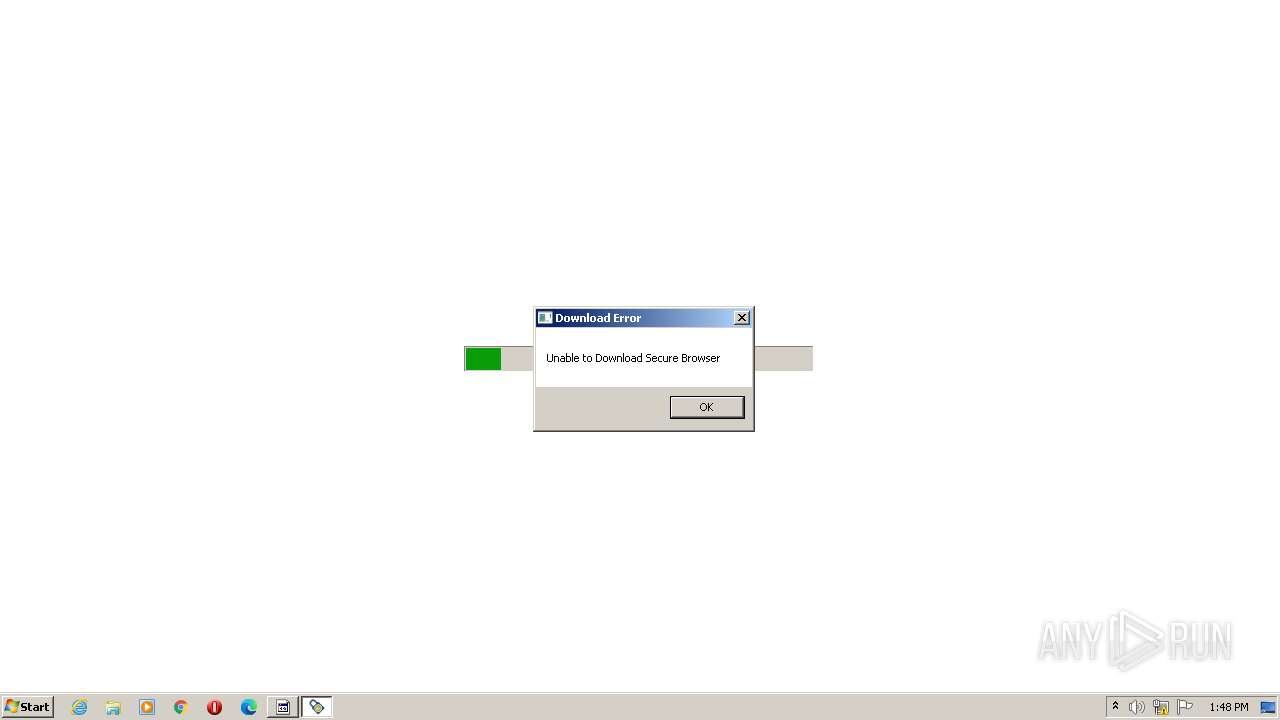
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2023, 12:47:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | ED98C74FF58AB3001A2CA821C90B9565 |
| SHA1: | 5E1D66497B261BBF4217B3CC28177AB76305544E |
| SHA256: | B225AEC599493469587852E4E70897747F631CFC1821644ED05F1C260FFDCA02 |
| SSDEEP: | 6144:xXzKdNY49u8rVcH+17CrRPXO3mKVx0dfelu:qa4ARHKCrRhKT0d1 |
MALICIOUS
Application was dropped or rewritten from another process
- ITS SB App Switch.exe (PID: 3656)
- ITS SB App Switch.exe (PID: 3880)
SUSPICIOUS
Reads the Internet Settings
- Compass Browser (1).exe (PID: 3264)
Executable content was dropped or overwritten
- Compass Browser (1).exe (PID: 3264)
Reads security settings of Internet Explorer
- Compass Browser (1).exe (PID: 3264)
Checks Windows Trust Settings
- Compass Browser (1).exe (PID: 3264)
Reads settings of System Certificates
- Compass Browser (1).exe (PID: 3264)
INFO
Create files in a temporary directory
- Compass Browser (1).exe (PID: 3264)
Checks supported languages
- Compass Browser (1).exe (PID: 3264)
- ITS SB App Switch.exe (PID: 3656)
The process checks LSA protection
- Compass Browser (1).exe (PID: 3264)
Reads the machine GUID from the registry
- Compass Browser (1).exe (PID: 3264)
Creates files or folders in the user directory
- Compass Browser (1).exe (PID: 3264)
Reads the computer name
- Compass Browser (1).exe (PID: 3264)
Checks proxy server information
- Compass Browser (1).exe (PID: 3264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| ProductVersion: | 2.5.0.2 |
|---|---|
| ProductName: | ITS GCO Bootstrap |
| OriginalFileName: | VerifyAndLaunch.exe |
| LegalCopyright: | (C) Internet Testing Systems |
| InternalName: | VerifyAndLaunch |
| FileVersion: | 2.5.0.2 |
| FileDescription: | ITS GCO Bootstrap |
| CompanyName: | Internet Testing Systems |
| Comments: | ITS GCO Bootstrap |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0017 |
| ProductVersionNumber: | 2.5.0.2 |
| FileVersionNumber: | 2.5.0.2 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x85b20 |
| UninitializedDataSize: | 376832 |
| InitializedDataSize: | 106496 |
| CodeSize: | 167936 |
| LinkerVersion: | 14.29 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2022:11:03 11:35:44+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Nov-2022 11:35:44 |
| Detected languages: |
|
| Comments: | ITS GCO Bootstrap |
| CompanyName: | Internet Testing Systems |
| FileDescription: | ITS GCO Bootstrap |
| FileVersion: | 2.5.0.2 |
| InternalName: | VerifyAndLaunch |
| LegalCopyright: | (C) Internet Testing Systems |
| OriginalFilename: | VerifyAndLaunch.exe |
| ProductName: | ITS GCO Bootstrap |
| ProductVersion: | 2.5.0.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 03-Nov-2022 11:35:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0005C000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0005D000 | 0x00029000 | 0x00028E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.90189 |
.rsrc | 0x00086000 | 0x0001A000 | 0x00019600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.41103 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.8565 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.80858 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.39981 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.01791 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 7.52806 | 593 | Latin 1 / Western European | English - United States | LAUNCHURL |
102 | 6.54709 | 149 | Latin 1 / Western European | English - United States | MESSAGE |
103 | 5.0865 | 47 | Latin 1 / Western European | English - United States | MESSAGETITLE |
105 | 2.80283 | 76 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
107 | 3.54659 | 13 | Latin 1 / Western European | English - United States | VERIFYVERSION |
Imports
ADVAPI32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WININET.dll |
ole32.dll |
Total processes
39
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3264 | "C:\Users\admin\AppData\Local\Temp\Compass Browser (1).exe" | C:\Users\admin\AppData\Local\Temp\Compass Browser (1).exe | explorer.exe | ||||||||||||
User: admin Company: Internet Testing Systems Integrity Level: MEDIUM Description: ITS GCO Bootstrap Exit code: 0 Version: 2.5.0.2 Modules
| |||||||||||||||
| 3656 | "C:\Users\admin\AppData\Local\Temp\ITS\WINCSECB\293\Production\ITS SB App Switch.exe" | C:\Users\admin\AppData\Local\Temp\ITS\WINCSECB\293\Production\ITS SB App Switch.exe | — | Compass Browser (1).exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3880 | "C:\Users\admin\AppData\Local\Temp\ITS\WINCSECB\293\Production\ITS SB App Switch.exe" | C:\Users\admin\AppData\Local\Temp\ITS\WINCSECB\293\Production\ITS SB App Switch.exe | — | Compass Browser (1).exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
4 194
Read events
4 150
Write events
44
Delete events
0
Modification events
| (PID) Process: | (3264) Compass Browser (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3264) Compass Browser (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3264) Compass Browser (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3264) Compass Browser (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3264) Compass Browser (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 2688 | |||
| (PID) Process: | (3264) Compass Browser (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3264) Compass Browser (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000040010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3264) Compass Browser (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3264) Compass Browser (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3264) Compass Browser (1).exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3264 | Compass Browser (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:B4C12064E247E370B92A8F22493B2FEF | SHA256:07F48640CA434EB9E97C4A3057B009033F32033D4102AFD704C795A3CC1F76CF | |||
| 3264 | Compass Browser (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\572BF21E454637C9F000BE1AF9B1E1A9 | binary | |
MD5:2E89092109F7C0C2C823A00E09B029EB | SHA256:9D765B633DA1890B1B162EC216F8C6281112A7C2A2582AE3FB4DB961C3E39A62 | |||
| 3264 | Compass Browser (1).exe | C:\Users\admin\AppData\Local\Temp\ITS\WINCSECB\293\Production\ITS SB App Switch.exe | executable | |
MD5:368332FCA74F48697D842C5F4698AE1D | SHA256:3A4A5B128C3A042010824FD33B719466B0D9320AA051CA3D5F1690124766AD59 | |||
| 3264 | Compass Browser (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:11CFE81DAB80AD3E7911B2219277BB59 | SHA256:AB5E0DFDE28F26767E4A2C996BC05836C509263FA337B0760CC90DFFB76BB471 | |||
| 3264 | Compass Browser (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\572BF21E454637C9F000BE1AF9B1E1A9 | binary | |
MD5:0CA7BFC7227AF6C21FB45D95FDC7D679 | SHA256:16078AFD05065BA3EC79F88980887A73B54E7C1300AC9B18097EA19616E32999 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
10
DNS requests
6
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3264 | Compass Browser (1).exe | GET | 200 | 104.18.14.101:80 | http://crl.comodoca.com/AAACertificateServices.crl | US | binary | 506 b | whitelisted |
3264 | Compass Browser (1).exe | GET | 200 | 104.18.15.101:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | binary | 2.18 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1068 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3264 | Compass Browser (1).exe | 8.248.149.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
3264 | Compass Browser (1).exe | 104.18.15.101:80 | ocsp.comodoca.com | CLOUDFLARENET | — | whitelisted |
3264 | Compass Browser (1).exe | 104.18.14.101:80 | ocsp.comodoca.com | CLOUDFLARENET | — | unknown |
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3264 | Compass Browser (1).exe | 64.106.220.213:443 | www.starttest.com | DATAPIPE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.starttest.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
crl.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report