| download: | /errias/XWorm-Rat-Remote-Administration-Tool-/main/dnlib.exe |
| Full analysis: | https://app.any.run/tasks/66f00639-3a63-481d-8722-a295123939d8 |
| Verdict: | Malicious activity |
| Analysis date: | August 31, 2024, 16:01:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | ACABB7806ADD665B05E0F037C7811D4E |
| SHA1: | B9770D63E1FAFD4FCA6F781ACC4FBDCACC20E402 |
| SHA256: | B21EE2A87FB039C27B78ABCB6BB3605D315B683B5F1CC25F3A9183B420BEFDE1 |
| SSDEEP: | 192:BH8KE2uzqUu5kOvY0HRFnGlfEaPOPvx/T0YmYV52GmNN3hvwZX7xVL:xbBYwPv1T0YmeoGmb3hvwZX7xV |
MALICIOUS
Bypass User Account Control (Modify registry)
- dnlib.exe (PID: 3672)
Bypass User Account Control (fodhelper)
- fodhelper.exe (PID: 5532)
Scans artifacts that could help determine the target
- disas.exe (PID: 1124)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 3272)
SUSPICIOUS
The executable file from the user directory is run by the CMD process
- dnlib.exe (PID: 3672)
Reads security settings of Internet Explorer
- dnlib.exe (PID: 3672)
- WinFileAkByp.exe (PID: 2068)
- disas.exe (PID: 1124)
- PwMn.exe (PID: 2508)
Checks Windows Trust Settings
- dnlib.exe (PID: 3672)
- WinFileAkByp.exe (PID: 2068)
- disas.exe (PID: 1124)
- PwMn.exe (PID: 2508)
Changes default file association
- dnlib.exe (PID: 3672)
Executable content was dropped or overwritten
- dnlib.exe (PID: 3672)
- WinFileAkByp.exe (PID: 2068)
- disas.exe (PID: 1124)
Reads the date of Windows installation
- dnlib.exe (PID: 3672)
- WinFileAkByp.exe (PID: 2068)
- PwMn.exe (PID: 2508)
Process drops legitimate windows executable
- WinFileAkByp.exe (PID: 2068)
Drops the executable file immediately after the start
- WinFileAkByp.exe (PID: 2068)
- disas.exe (PID: 1124)
- dnlib.exe (PID: 3672)
The process drops C-runtime libraries
- WinFileAkByp.exe (PID: 2068)
Starts CMD.EXE for commands execution
- shdtsk.exe (PID: 1932)
INFO
Checks supported languages
- dnlib.exe (PID: 3672)
- WinFileAkByp.exe (PID: 2068)
- disas.exe (PID: 1124)
- PwMn.exe (PID: 2508)
- shdtsk.exe (PID: 1932)
- rnp.exe (PID: 3140)
Create files in a temporary directory
- dnlib.exe (PID: 3672)
- WinFileAkByp.exe (PID: 2068)
- disas.exe (PID: 1124)
- PwMn.exe (PID: 2508)
Reads the computer name
- dnlib.exe (PID: 3672)
- WinFileAkByp.exe (PID: 2068)
- disas.exe (PID: 1124)
- PwMn.exe (PID: 2508)
Reads Environment values
- dnlib.exe (PID: 3672)
- WinFileAkByp.exe (PID: 2068)
- PwMn.exe (PID: 2508)
Disables trace logs
- dnlib.exe (PID: 3672)
- WinFileAkByp.exe (PID: 2068)
Reads the software policy settings
- dnlib.exe (PID: 3672)
- WinFileAkByp.exe (PID: 2068)
- disas.exe (PID: 1124)
Reads the machine GUID from the registry
- dnlib.exe (PID: 3672)
- WinFileAkByp.exe (PID: 2068)
- disas.exe (PID: 1124)
- PwMn.exe (PID: 2508)
Process checks computer location settings
- dnlib.exe (PID: 3672)
- WinFileAkByp.exe (PID: 2068)
- PwMn.exe (PID: 2508)
Checks proxy server information
- dnlib.exe (PID: 3672)
- WinFileAkByp.exe (PID: 2068)
- disas.exe (PID: 1124)
Reads security settings of Internet Explorer
- fodhelper.exe (PID: 5532)
Reads Microsoft Office registry keys
- fodhelper.exe (PID: 5532)
Checks if a key exists in the options dictionary (POWERSHELL)
- WinFileAkByp.exe (PID: 2068)
The process uses the downloaded file
- WinFileAkByp.exe (PID: 2068)
- dnlib.exe (PID: 3672)
- PwMn.exe (PID: 2508)
Creates files or folders in the user directory
- disas.exe (PID: 1124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:08:28 00:46:16+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 5632 |
| InitializedDataSize: | 6656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x35ce |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.1.2 |
| ProductVersionNumber: | 1.0.1.2 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | PowerShell2Exe |
| CompanyName: | Zander Tools |
| FileDescription: | PowerShell-Wrapper |
| FileVersion: | 1.0.1.2 |
| InternalName: | 4rsd1gne.exe |
| LegalCopyright: | Copyright © 2023 by Roger Zander |
| OriginalFileName: | 4rsd1gne.exe |
| ProductName: | PowerShell to EXE converter |
| ProductVersion: | 1.0.1.2 |
| AssemblyVersion: | 1.0.1.2 |
Total processes
148
Monitored processes
18
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1124 | "C:\Users\admin\AppData\Local\Temp\disas.exe" | C:\Users\admin\AppData\Local\Temp\disas.exe | WinFileAkByp.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1656 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1932 | C:\Users\admin\AppData\Local\Temp\shdtsk.exe | C:\Users\admin\AppData\Local\Temp\shdtsk.exe | — | disas.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2068 | "C:\Users\admin\AppData\Local\Temp\WinFileAkByp.exe" | C:\Users\admin\AppData\Local\Temp\WinFileAkByp.exe | fodhelper.exe | ||||||||||||
User: admin Company: Zander Tools Integrity Level: HIGH Description: PowerShell-Wrapper Exit code: 1 Version: 1.0.1.2 Modules
| |||||||||||||||
| 2080 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WinFileAkByp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
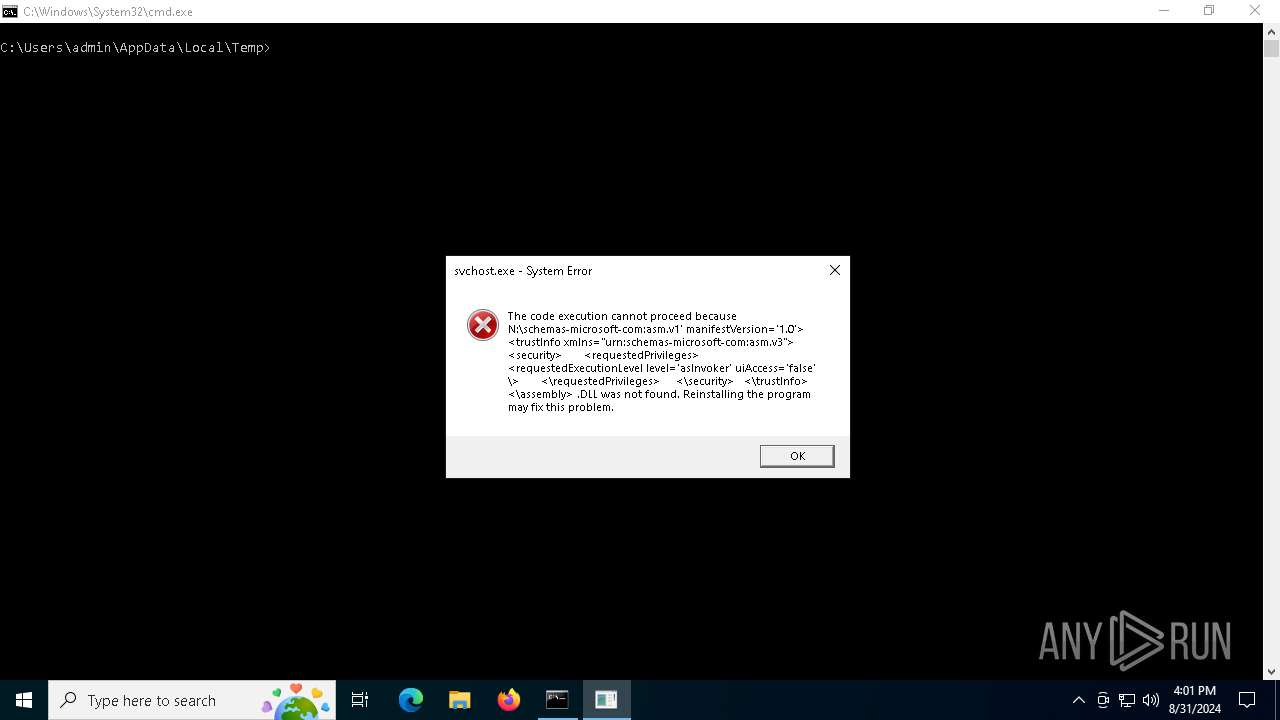
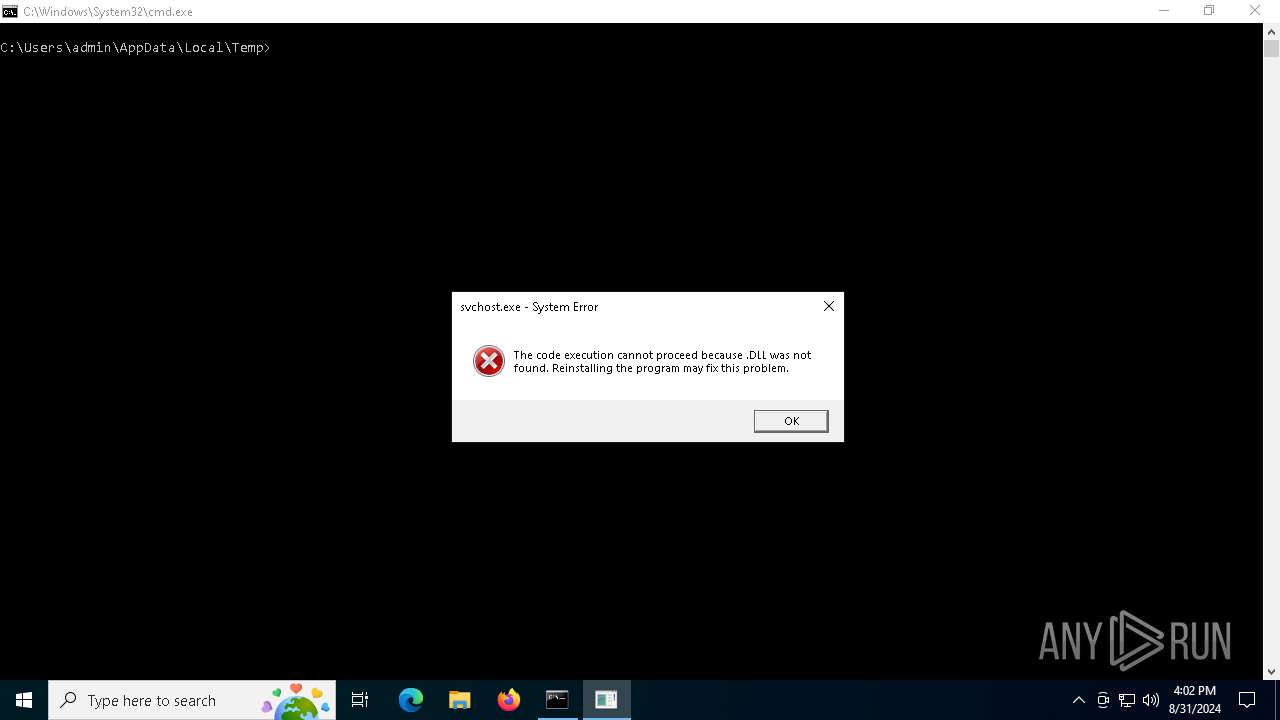
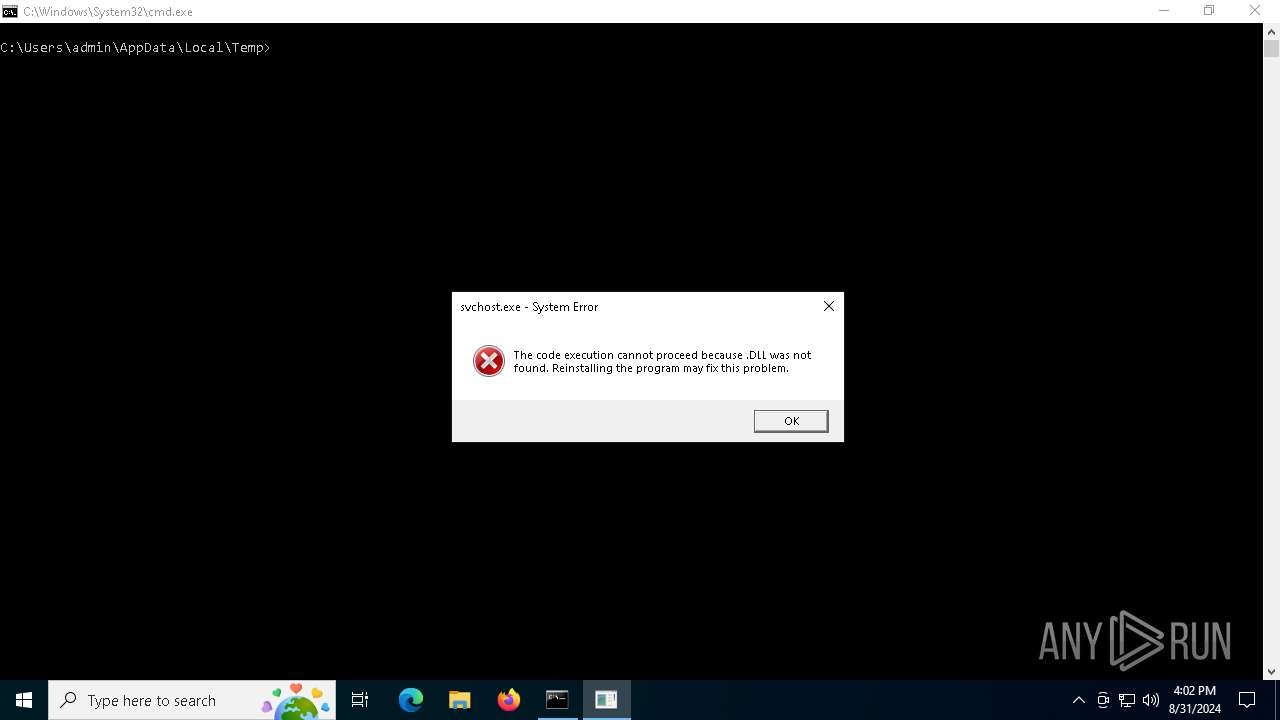
| 2492 | "C:\Windows\System32\svchost.exe" | C:\Windows\System32\svchost.exe | — | rnp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 3221225781 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2508 | C:\Users\admin\AppData\Local\Temp\PwMn.exe | C:\Users\admin\AppData\Local\Temp\PwMn.exe | — | disas.exe | |||||||||||
User: admin Company: Zander Tools Integrity Level: HIGH Description: PowerShell-Wrapper Exit code: 0 Version: 1.0.1.2 Modules
| |||||||||||||||
| 3140 | "C:\Users\admin\AppData\Local\Temp\rnp.exe" C:\\Users\\admin\\AppData\\Local\\Temp\\sff.exe C:\Windows\System32\svchost.exe | C:\Users\admin\AppData\Local\Temp\rnp.exe | — | PwMn.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3272 | C:\WINDOWS\system32\cmd.exe /c schtasks /create /tn "Svchst" /tr "C:\Users\%username%\AppData\Local\Temp\PwMn.exe" /sc onlogon /RL HIGHEST /f | C:\Windows\System32\cmd.exe | shdtsk.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
19 579
Read events
19 512
Write events
67
Delete events
0
Modification events
| (PID) Process: | (3672) dnlib.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dnlib_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3672) dnlib.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dnlib_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (3672) dnlib.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dnlib_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3672) dnlib.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dnlib_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (3672) dnlib.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dnlib_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (3672) dnlib.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dnlib_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3672) dnlib.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dnlib_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3672) dnlib.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dnlib_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3672) dnlib.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dnlib_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (3672) dnlib.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dnlib_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
12
Suspicious files
8
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2068 | WinFileAkByp.exe | C:\Windows\System32\ucrtbased.dll | executable | |
MD5:C3130CFB00549A5A92DA60E7F79F5FC9 | SHA256:EEE42EABC546E5AA760F8DF7105FCF505ABFFCB9EC4BF54398436303E407A3F8 | |||
| 1124 | disas.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\D0E1C4B6144E7ECAB3F020E4A19EFC29_B5F77004C894173A10E3A199871D2D90 | binary | |
MD5:797A06C5FC5D4FD4CDAA6465244D44FD | SHA256:E74FBAF6ED22850CEED605B452E87E9E60037B9FD24C32B0B4EEBD3216F7A68F | |||
| 3672 | dnlib.exe | C:\Users\admin\AppData\Local\Temp\WinFileAkByp.exe | executable | |
MD5:D775AD182DF6B57F3E2F6286CB2FAC4A | SHA256:B365718D9941BFF75175A5C3FF0FD5B772274EA245BAC69D31ACDE10A28FF3BC | |||
| 1124 | disas.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A66A8DB907BADC9D16AD67B2FBFFDD5C | binary | |
MD5:03A714A51C252298BC34E46DE67BC777 | SHA256:510C6D02A3C517889353790BC1DEEC145BB6C8E53F57BDF753EA77BA285AAE5F | |||
| 1124 | disas.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_89854CA6A0F0936A4D2ECA78845CEA25 | binary | |
MD5:EDD61286A59DB1A135E7A072B3206AC9 | SHA256:30E56F85DC06E9F3A8B35CF937D95DDB1EB575BE24073426D0362EBDD9FA9714 | |||
| 1124 | disas.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_89854CA6A0F0936A4D2ECA78845CEA25 | der | |
MD5:BA135410D4319508DA4468E953F364BE | SHA256:B6A5F8EBA6A4B5F672E48CED42334B0071D6EA083952F7C19F4F4AF600301A4A | |||
| 1124 | disas.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D0E1C4B6144E7ECAB3F020E4A19EFC29_B5F77004C894173A10E3A199871D2D90 | binary | |
MD5:5010FCB845E3B4E7739B2F7965824318 | SHA256:9F8691FFAF54F027EE8FE4D91C7A809A2044BBFEDAA486AD8B056675ECB499C7 | |||
| 1124 | disas.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_49536AB5156BDD74EFF881D01C36A419 | binary | |
MD5:5D8974B2A7A7D1F5FE03444E4395E016 | SHA256:C538358CA01995CBDD846E943B8734EA62692D7956150479CF4701A87EB6EF41 | |||
| 3672 | dnlib.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rxe3bx0n.jvn.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1124 | disas.exe | C:\Users\admin\AppData\Local\Temp\sff.exe | executable | |
MD5:E40EB702F369E5DECFB33B3D78BD4B0C | SHA256:16A2ABE3F4F2C005E206318CAF37A366E0084FA8CA8561F3642FA0B4F2F04A7E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
33
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1124 | disas.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | — | — | whitelisted |
1124 | disas.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | whitelisted |
1780 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1124 | disas.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
1124 | disas.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CEE4o94a2bBo7lCzSxA63QqU%3D | unknown | — | — | whitelisted |
7156 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7156 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6056 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6400 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3672 | dnlib.exe | 140.82.121.3:443 | github.com | GITHUB | US | shared |
3672 | dnlib.exe | 185.199.110.133:443 | raw.githubusercontent.com | FASTLY | US | shared |
2068 | WinFileAkByp.exe | 140.82.121.3:443 | github.com | GITHUB | US | shared |
2068 | WinFileAkByp.exe | 185.199.110.133:443 | raw.githubusercontent.com | FASTLY | US | shared |
6056 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1124 | disas.exe | 140.82.121.3:443 | github.com | GITHUB | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| shared |
raw.githubusercontent.com |
| shared |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |