| File name: | vcredist_x64.exe |
| Full analysis: | https://app.any.run/tasks/055136db-2ed6-4432-8832-88c7ee53721a |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2023, 16:41:50 |
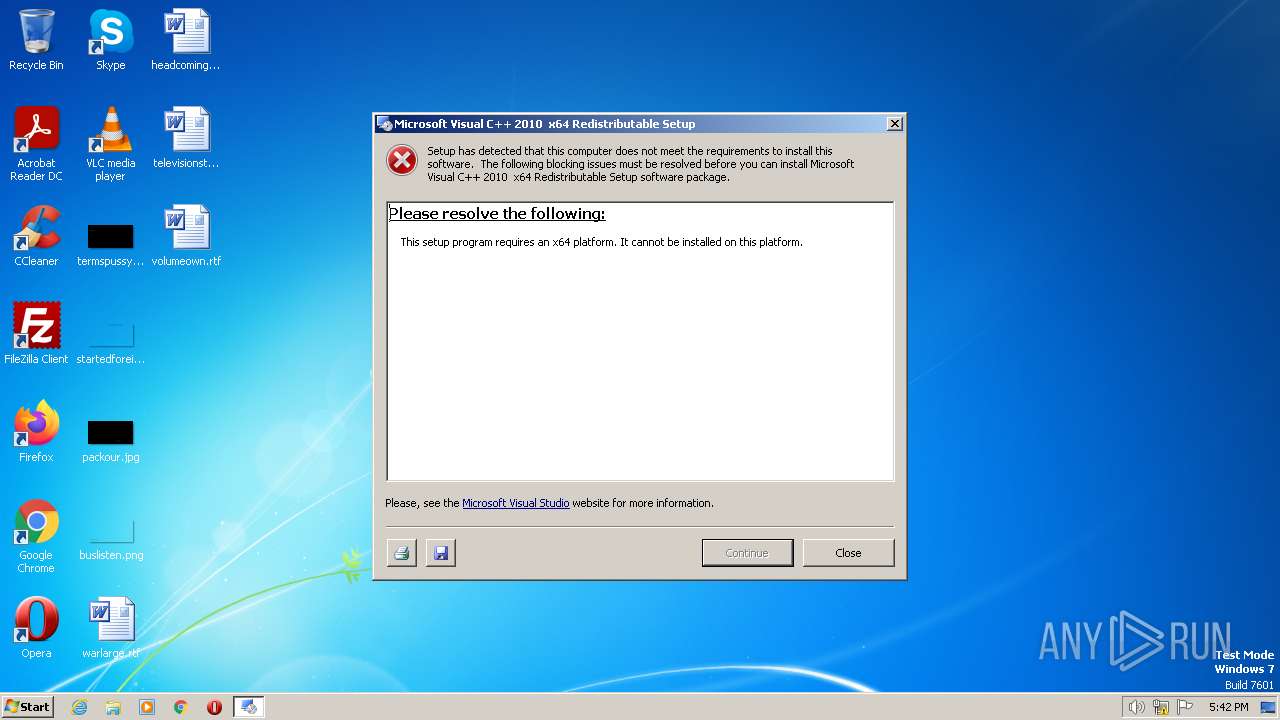
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | B29D4BE790ED16F3A312DEB410D9F14E |
| SHA1: | 556B6F5C9E0A8D053CB048C7015783936AE24ECE |
| SHA256: | B1EEBF6DA233E3941A74AFDD7F048D7CFD20E70F17D99F3BCBF614FF4847EAE5 |
| SSDEEP: | 98304:PsPj6quMcylIpk4nM6tmMUrfvEP0hcKju9Z/lTPU8UBHBKNpr1w36ZyL:0PjzDJ4M6tmXDsPKi1lTPmHipJwq4 |
MALICIOUS
Application was dropped or rewritten from another process
- Setup.exe (PID: 2696)
- vcredist_x64.exe (PID: 1280)
- vcredist_x64.exe (PID: 2328)
Loads dropped or rewritten executable
- Setup.exe (PID: 2696)
Actions looks like stealing of personal data
- vcredist_x64.exe (PID: 1144)
SUSPICIOUS
Reads the Internet Settings
- vcredist_x64.exe (PID: 1144)
Executable content was dropped or overwritten
- vcredist_x64.exe (PID: 2328)
- vcredist_x64.exe (PID: 1144)
INFO
Checks supported languages
- vcredist_x64.exe (PID: 1144)
- vcredist_x64.exe (PID: 2328)
- Setup.exe (PID: 2696)
Create files in a temporary directory
- vcredist_x64.exe (PID: 1144)
- Setup.exe (PID: 2696)
Reads the computer name
- vcredist_x64.exe (PID: 1144)
- vcredist_x64.exe (PID: 2328)
- Setup.exe (PID: 2696)
The process checks LSA protection
- vcredist_x64.exe (PID: 1144)
- vcredist_x64.exe (PID: 2328)
Reads the machine GUID from the registry
- vcredist_x64.exe (PID: 2328)
Reads Environment values
- vcredist_x64.exe (PID: 2328)
Reads CPU info
- Setup.exe (PID: 2696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 6 (75) |
|---|---|---|
| .exe | | | InstallShield setup (12.2) |
| .exe | | | Win32 Executable Delphi generic (4) |
| .scr | | | Windows screen saver (3.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.8) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x80e4 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 10752 |
| CodeSize: | 29696 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000722C | 0x00007400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51167 |
DATA | 0x00009000 | 0x00000218 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.1517 |
BSS | 0x0000A000 | 0x0000A899 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00015000 | 0x00000864 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.17386 |
.tls | 0x00016000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00017000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.20692 |
.reloc | 0x00018000 | 0x000005CC | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.44309 |
.rsrc | 0x00019000 | 0x00001400 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 2.7648 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 1.76037 | 4264 | UNKNOWN | Russian - Russia | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 6.90278 | 172 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 1.7815 | 20 | UNKNOWN | Russian - Russia | RT_GROUP_ICON |
Imports
advapi32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
41
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1144 | "C:\Users\admin\AppData\Local\Temp\vcredist_x64.exe" | C:\Users\admin\AppData\Local\Temp\vcredist_x64.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1280 | "C:\Users\admin\AppData\Local\Temp\3582-490\vcredist_x64.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\vcredist_x64.exe | — | vcredist_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2010 x64 Redistributable Setup Exit code: 3221226540 Version: 10.0.40219.01 Modules
| |||||||||||||||
| 2328 | "C:\Users\admin\AppData\Local\Temp\3582-490\vcredist_x64.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\vcredist_x64.exe | vcredist_x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2010 x64 Redistributable Setup Exit code: 0 Version: 10.0.40219.01 Modules
| |||||||||||||||
| 2696 | c:\065bc23c5bd60d7a7175ea7fa68f97\Setup.exe | C:\065bc23c5bd60d7a7175ea7fa68f97\Setup.exe | — | vcredist_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 0 Version: 10.0.40219.1 built by: SP1Rel Modules
| |||||||||||||||
Total events
830
Read events
822
Write events
8
Delete events
0
Modification events
| (PID) Process: | (1144) vcredist_x64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1144) vcredist_x64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1144) vcredist_x64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1144) vcredist_x64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
39
Suspicious files
1
Text files
47
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1144 | vcredist_x64.exe | C:\Users\admin\AppData\Local\Temp\3582-490\vcredist_x64.exe | executable | |
MD5:CBE0B05C11D5D523C2AF997D737C137B | SHA256:C6CD2D3F0B11DC2A604FFDC4DD97861A83B77E21709BA71B962A47759C93F4C8 | |||
| 2328 | vcredist_x64.exe | C:\065bc23c5bd60d7a7175ea7fa68f97\DHtmlHeader.html | html | |
MD5:CD131D41791A543CC6F6ED1EA5BD257C | SHA256:E139AF8858FE90127095AC1C4685BCD849437EF0DF7C416033554703F5D864BB | |||
| 2328 | vcredist_x64.exe | C:\065bc23c5bd60d7a7175ea7fa68f97\SetupUi.dll | executable | |
MD5:C744EC120E54027C57318C4720B4D6BE | SHA256:D1610B0A94A4DADC85EE32A7E5FFD6533EA42347D6F2D6871BEB03157B89A857 | |||
| 2328 | vcredist_x64.exe | C:\065bc23c5bd60d7a7175ea7fa68f97\watermark.bmp | image | |
MD5:1A5CAAFACFC8C7766E404D019249CF67 | SHA256:2E87D5742413254DB10F7BD0762B6CDB98FF9C46CA9ACDDFD9B1C2E5418638F2 | |||
| 2328 | vcredist_x64.exe | C:\065bc23c5bd60d7a7175ea7fa68f97\SetupUi.xsd | xml | |
MD5:2FADD9E618EFF8175F2A6E8B95C0CACC | SHA256:222211E8F512EDF97D78BC93E1F271C922D5E91FA899E092B4A096776A704093 | |||
| 2328 | vcredist_x64.exe | C:\065bc23c5bd60d7a7175ea7fa68f97\SetupEngine.dll | executable | |
MD5:A030C6B93740CBAA232FFAA08CCD3396 | SHA256:0507720D52AE856BBF5FF3F01172A390B6C19517CB95514CD53F4A59859E8D63 | |||
| 2328 | vcredist_x64.exe | C:\065bc23c5bd60d7a7175ea7fa68f97\Setup.exe | executable | |
MD5:9A1141FBCEEB2E196AE1BA115FD4BEE6 | SHA256:28563D908450EB7B7E9ED07A934E0D68135B5BB48E866E0A1C913BD776A44FEF | |||
| 2328 | vcredist_x64.exe | C:\065bc23c5bd60d7a7175ea7fa68f97\1041\SetupResources.dll | executable | |
MD5:00EBA8C995E91FA9C7A38221CC3C2AB2 | SHA256:DA2514F84A5249937DD439CB608B44D7A2C152D7D4F7B4F1D2B12DB22FB29DF5 | |||
| 2328 | vcredist_x64.exe | C:\065bc23c5bd60d7a7175ea7fa68f97\UiInfo.xml | xml | |
MD5:4F90FCEF3836F5FC49426AD9938A1C60 | SHA256:66A0299CE7EE12DD9FC2CFEAD3C3211E59BFB54D6C0627D044D44CEF6E70367B | |||
| 2328 | vcredist_x64.exe | C:\065bc23c5bd60d7a7175ea7fa68f97\1033\LocalizedData.xml | xml | |
MD5:5486FF60B072102EE3231FD743B290A1 | SHA256:5CA3ECAA12CA56F955D403CA93C4CB36A7D3DCDEA779FC9BDAA0CDD429DAB706 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3620 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |