| File name: | UTWSecure-8JL4b.KsEz8SCz.exe |
| Full analysis: | https://app.any.run/tasks/b3fb9935-1758-46a7-88ab-8a729e4e8ca0 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 03:30:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 8856121233E1D16D761B19347DE76CF0 |
| SHA1: | 0BC0C1B66565F17CA42069FD58F8306EF31A622E |
| SHA256: | B1DDB966D30E5F16D361D01D5FE303E6D0B980D0D64D1C5A93C3791B15D5B0A9 |
| SSDEEP: | 1536:ohNeDLHPUVkKo2cgigKIhTnH2QjCdqQsWQcdUkBbfqQNK3:vDLHcVkKo2cZgKIhTH2U+lU2bfqv |
MALICIOUS
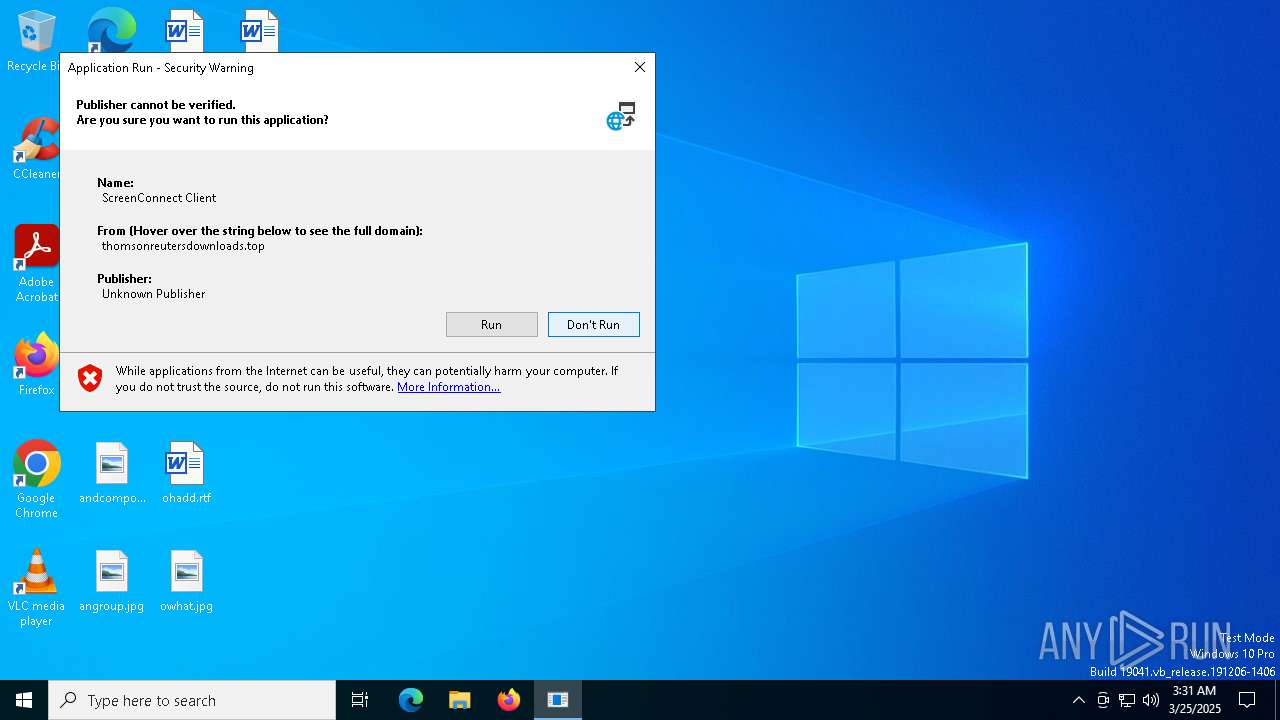
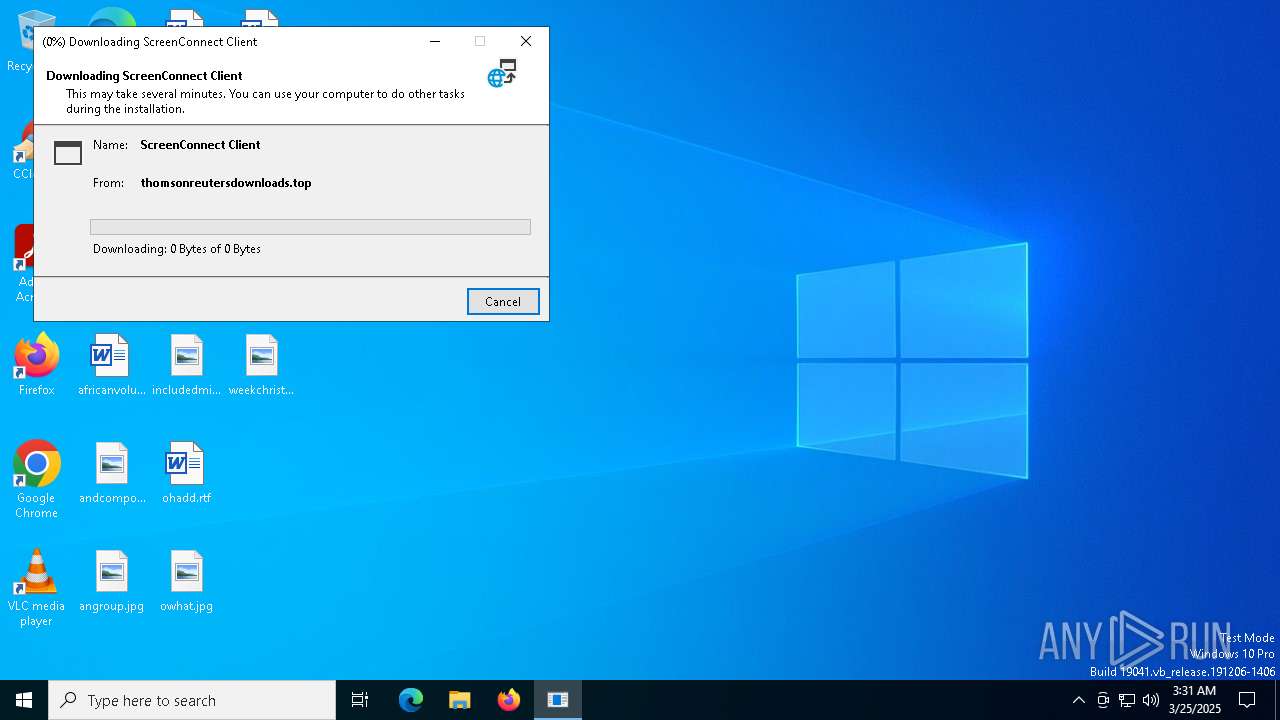
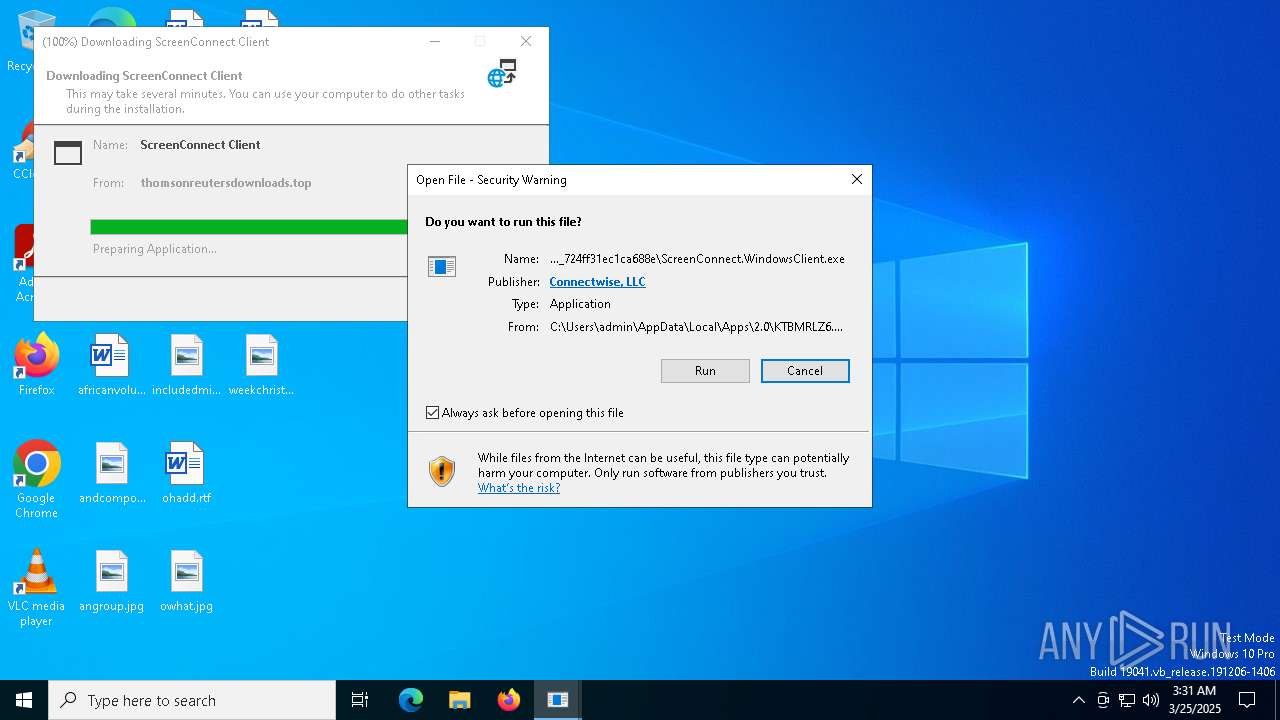
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 1348)
SUSPICIOUS
Adds/modifies Windows certificates
- UTWSecure-8JL4b.KsEz8SCz.exe (PID: 6656)
- dfsvc.exe (PID: 6476)
Reads Internet Explorer settings
- dfsvc.exe (PID: 6476)
Executable content was dropped or overwritten
- dfsvc.exe (PID: 6476)
The process creates files with name similar to system file names
- dfsvc.exe (PID: 6476)
Reads security settings of Internet Explorer
- dfsvc.exe (PID: 6476)
- ScreenConnect.WindowsClient.exe (PID: 8100)
- ScreenConnect.ClientService.exe (PID: 7192)
- ScreenConnect.ClientService.exe (PID: 1348)
- ScreenConnect.WindowsClient.exe (PID: 2692)
Reads the date of Windows installation
- dfsvc.exe (PID: 6476)
- ScreenConnect.WindowsClient.exe (PID: 8100)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 1348)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 1348)
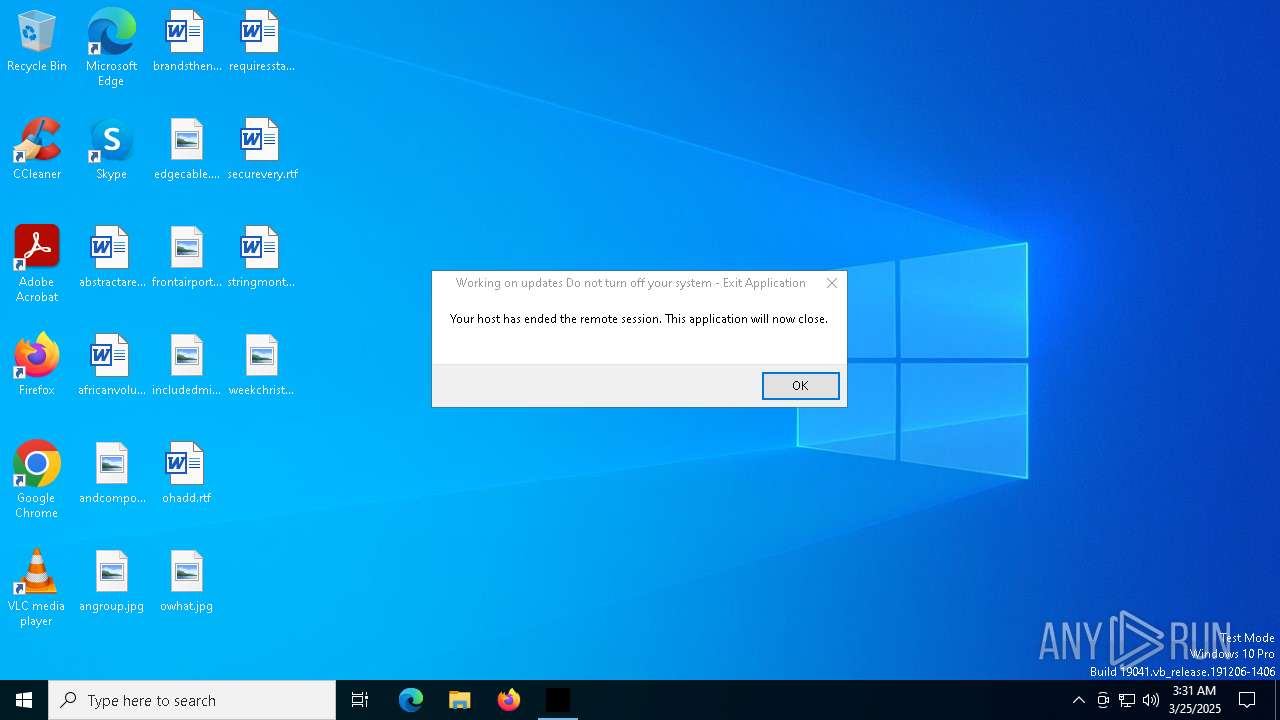
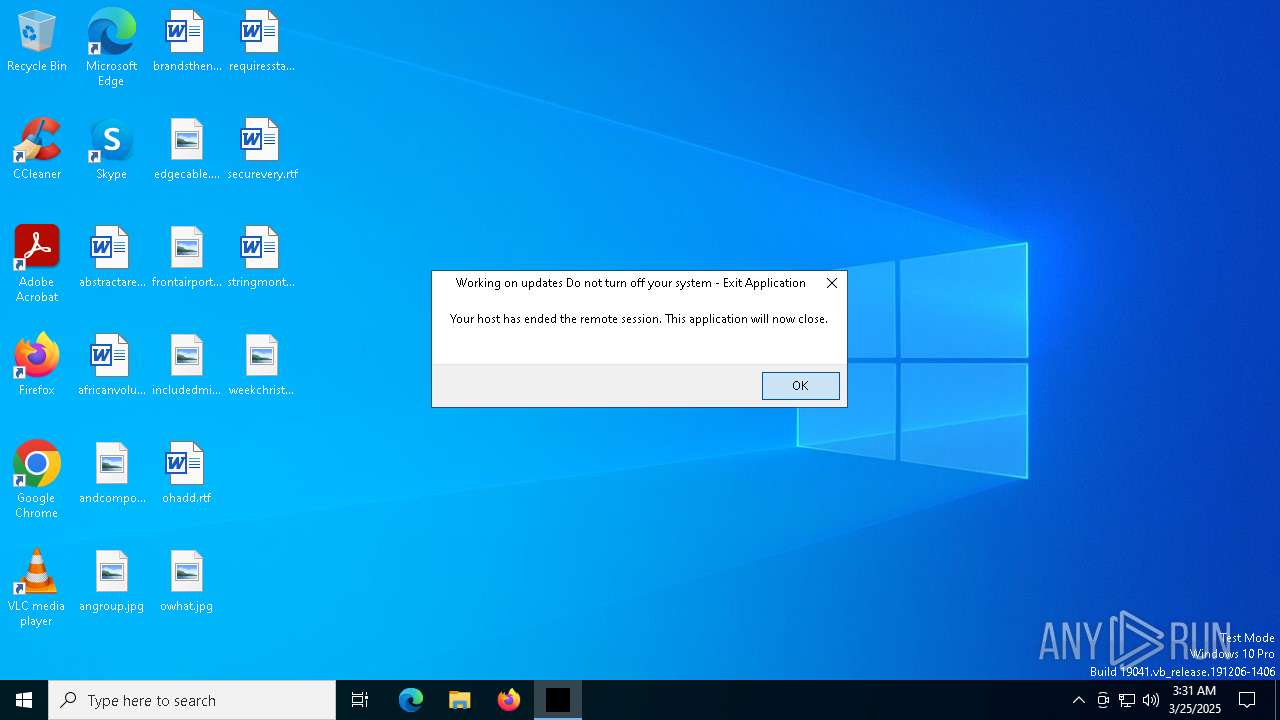
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 1348)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 1348)
Executes application which crashes
- UTWSecure-8JL4b.KsEz8SCz.exe (PID: 6656)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 1348)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 1348)
INFO
Checks supported languages
- UTWSecure-8JL4b.KsEz8SCz.exe (PID: 6656)
- dfsvc.exe (PID: 6476)
- ScreenConnect.WindowsClient.exe (PID: 8100)
- ScreenConnect.ClientService.exe (PID: 7192)
- ScreenConnect.ClientService.exe (PID: 1348)
- ScreenConnect.WindowsClient.exe (PID: 2692)
Reads the machine GUID from the registry
- UTWSecure-8JL4b.KsEz8SCz.exe (PID: 6656)
- dfsvc.exe (PID: 6476)
- ScreenConnect.WindowsClient.exe (PID: 8100)
- ScreenConnect.ClientService.exe (PID: 7192)
- ScreenConnect.ClientService.exe (PID: 1348)
- ScreenConnect.WindowsClient.exe (PID: 2692)
Reads the computer name
- UTWSecure-8JL4b.KsEz8SCz.exe (PID: 6656)
- dfsvc.exe (PID: 6476)
- ScreenConnect.WindowsClient.exe (PID: 8100)
- ScreenConnect.ClientService.exe (PID: 7192)
- ScreenConnect.ClientService.exe (PID: 1348)
- ScreenConnect.WindowsClient.exe (PID: 2692)
Creates files or folders in the user directory
- dfsvc.exe (PID: 6476)
- ScreenConnect.WindowsClient.exe (PID: 8100)
- ScreenConnect.ClientService.exe (PID: 1348)
- WerFault.exe (PID: 7660)
Disables trace logs
- dfsvc.exe (PID: 6476)
Checks proxy server information
- dfsvc.exe (PID: 6476)
Reads Environment values
- dfsvc.exe (PID: 6476)
Reads the software policy settings
- dfsvc.exe (PID: 6476)
Process checks whether UAC notifications are on
- dfsvc.exe (PID: 6476)
Create files in a temporary directory
- dfsvc.exe (PID: 6476)
Process checks computer location settings
- dfsvc.exe (PID: 6476)
- ScreenConnect.WindowsClient.exe (PID: 8100)
SCREENCONNECT has been detected
- ScreenConnect.ClientService.exe (PID: 1348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:10:28 17:41:07+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.39 |
| CodeSize: | 40448 |
| InitializedDataSize: | 32768 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1489 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
147
Monitored processes
10
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1348 | "C:\Users\admin\AppData\Local\Apps\2.0\KTBMRLZ6.OMQ\905NTEGO.BHB\scre..tion_25b0fbb6ef7eb094_0018.0003_724ff31ec1ca688e\ScreenConnect.ClientService.exe" "?e=Support&y=Guest&h=thomsonreutersdownloads.top&p=8041&s=eaf81b02-d927-4cf9-a4f8-cf9a2d199f59&k=BgIAAACkAABSU0ExAAgAAAEAAQD1W3QkRozKvHbxOzHZ60LN2Onx63ixMjV0I%2fiVjID2EQttPnUbI4XRXXTmYv2LUHgFOQkNLUmXzCeOcCQqIvl6lH7Wtn%2btUsklcjtKk4T9spnJMJM7okgw3kolxg5ndVp1c3e9iwsk%2btaIqOpMnWmGGQ1dfyvoBR3H9DrznmEnLdGOyry0nWf5C7SVweMe7E9R4X34nLFJc4gaA5mB3uGNoLntNBMeZIrtzJGfuZSEMyJIWnR0kkgWkgjOxz5gPqKQSYNiT5J2cPSNSg%2bZr3ZTsR5MZJ1%2bUzor2Z5y6MbFI1vr4Fe3jNjep9zldiqjpJtIwGAE%2bCLxPL0Ztymv2DjH&r=&i=NewPageCoded" "5" | C:\Users\admin\AppData\Local\Apps\2.0\KTBMRLZ6.OMQ\905NTEGO.BHB\scre..tion_25b0fbb6ef7eb094_0018.0003_724ff31ec1ca688e\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Version: 24.3.7.9067 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | "C:\Users\admin\AppData\Local\Apps\2.0\KTBMRLZ6.OMQ\905NTEGO.BHB\scre..tion_25b0fbb6ef7eb094_0018.0003_724ff31ec1ca688e\ScreenConnect.WindowsClient.exe" "RunRole" "22ab56ff-1028-4d3f-857a-b324ce3de58a" "User" | C:\Users\admin\AppData\Local\Apps\2.0\KTBMRLZ6.OMQ\905NTEGO.BHB\scre..tion_25b0fbb6ef7eb094_0018.0003_724ff31ec1ca688e\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Exit code: 0 Version: 24.3.7.9067 Modules
| |||||||||||||||
| 6476 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\dfsvc.exe" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\dfsvc.exe | UTWSecure-8JL4b.KsEz8SCz.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ClickOnce Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 6656 | "C:\Users\admin\Downloads\UTWSecure-8JL4b.KsEz8SCz.exe" | C:\Users\admin\Downloads\UTWSecure-8JL4b.KsEz8SCz.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 7192 | "C:\Users\admin\AppData\Local\Apps\2.0\KTBMRLZ6.OMQ\905NTEGO.BHB\scre..tion_25b0fbb6ef7eb094_0018.0003_724ff31ec1ca688e\ScreenConnect.ClientService.exe" "?e=Support&y=Guest&h=thomsonreutersdownloads.top&p=8041&s=eaf81b02-d927-4cf9-a4f8-cf9a2d199f59&k=BgIAAACkAABSU0ExAAgAAAEAAQD1W3QkRozKvHbxOzHZ60LN2Onx63ixMjV0I%2fiVjID2EQttPnUbI4XRXXTmYv2LUHgFOQkNLUmXzCeOcCQqIvl6lH7Wtn%2btUsklcjtKk4T9spnJMJM7okgw3kolxg5ndVp1c3e9iwsk%2btaIqOpMnWmGGQ1dfyvoBR3H9DrznmEnLdGOyry0nWf5C7SVweMe7E9R4X34nLFJc4gaA5mB3uGNoLntNBMeZIrtzJGfuZSEMyJIWnR0kkgWkgjOxz5gPqKQSYNiT5J2cPSNSg%2bZr3ZTsR5MZJ1%2bUzor2Z5y6MbFI1vr4Fe3jNjep9zldiqjpJtIwGAE%2bCLxPL0Ztymv2DjH&r=&i=NewPageCoded" "5" | C:\Users\admin\AppData\Local\Apps\2.0\KTBMRLZ6.OMQ\905NTEGO.BHB\scre..tion_25b0fbb6ef7eb094_0018.0003_724ff31ec1ca688e\ScreenConnect.ClientService.exe | ScreenConnect.WindowsClient.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 24.3.7.9067 Modules
| |||||||||||||||
| 7300 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7332 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7660 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6656 -s 336 | C:\Windows\SysWOW64\WerFault.exe | — | UTWSecure-8JL4b.KsEz8SCz.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8100 | "C:\Users\admin\AppData\Local\Apps\2.0\KTBMRLZ6.OMQ\905NTEGO.BHB\scre..tion_25b0fbb6ef7eb094_0018.0003_724ff31ec1ca688e\ScreenConnect.WindowsClient.exe" | C:\Users\admin\AppData\Local\Apps\2.0\KTBMRLZ6.OMQ\905NTEGO.BHB\scre..tion_25b0fbb6ef7eb094_0018.0003_724ff31ec1ca688e\ScreenConnect.WindowsClient.exe | — | dfsvc.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Exit code: 0 Version: 24.3.7.9067 Modules
| |||||||||||||||
Total events
10 321
Read events
10 122
Write events
168
Delete events
31
Modification events
| (PID) Process: | (6476) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: KGWE1EAABTZ7R46N30QXC2Q1 | |||
| (PID) Process: | (6476) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete value | Name: | ComponentStore_RandomString |
Value: KGWE1EAABTZ7R46N30QXC2Q1 | |||
| (PID) Process: | (6476) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6476) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: KTBMRLZ6OMQ905NTEGOBHBTH | |||
| (PID) Process: | (6476) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0\StateManager |
| Operation: | write | Name: | StateStore_RandomString |
Value: 1VPJWDQMMG9XZ8KWNYKEQCV9 | |||
| (PID) Process: | (6476) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6476) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6476) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6476) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6476) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
16
Suspicious files
21
Text files
27
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6476 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:1F00D8738706D6BDC84E76203C94522F | SHA256:9B87375856F51B72EEB7C8FD3F72818ABDB83B84587C6F20602864E552B1D9CB | |||
| 6476 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\C6QR3A58.XJP\QGLBA1KW.D5K\ScreenConnect.WindowsClient.exe.manifest | xml | |
MD5:7F68A01C2FEA1C80A75E287BB36D6B43 | SHA256:2E0E46F395D5A6440F179B61C4008ABF3D72CFCDA705A543C8EE18B41D37B025 | |||
| 6476 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\C6QR3A58.XJP\QGLBA1KW.D5K\ScreenConnect.WindowsBackstageShell.exe.config | xml | |
MD5:728175E20FFBCEB46760BB5E1112F38B | SHA256:87C640D3184C17D3B446A72D5F13D643A774B4ECC7AFBEDFD4E8DA7795EA8077 | |||
| 6476 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\C6QR3A58.XJP\QGLBA1KW.D5K\ScreenConnect.WindowsBackstageShell.exe | executable | |
MD5:AFA97CAF20F3608799E670E9D6253247 | SHA256:E25F32BA3FA32FD0DDD99EB65B26835E30829B5E4B58573690AA717E093A5D8F | |||
| 6476 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:31EC75457BF32239A2387786822797F6 | SHA256:D7A0115BB889901342A2510B025A65E7130E6811A30A28A7CCAAE17B0E7323F0 | |||
| 6476 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\C6QR3A58.XJP\QGLBA1KW.D5K\ScreenConnect.WindowsFileManager.exe | executable | |
MD5:1AEE526DC110E24D1399AFFCCD452AB3 | SHA256:EBD04A4540D6E76776BD58DEEA627345D0F8FBA2C04CC65BE5E979A8A67A62A1 | |||
| 6476 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\C6QR3A58.XJP\QGLBA1KW.D5K\ScreenConnect.ClientService.exe | executable | |
MD5:75B21D04C69128A7230A0998086B61AA | SHA256:F1B5C000794F046259121C63ED37F9EFF0CFE1258588ECA6FD85E16D3922767E | |||
| 6476 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\C6QR3A58.XJP\QGLBA1KW.D5K\ScreenConnect.WindowsFileManager.exe.config | xml | |
MD5:728175E20FFBCEB46760BB5E1112F38B | SHA256:87C640D3184C17D3B446A72D5F13D643A774B4ECC7AFBEDFD4E8DA7795EA8077 | |||
| 6476 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\C6QR3A58.XJP\QGLBA1KW.D5K\ScreenConnect.WindowsClient.exe.config | xml | |
MD5:728175E20FFBCEB46760BB5E1112F38B | SHA256:87C640D3184C17D3B446A72D5F13D643A774B4ECC7AFBEDFD4E8DA7795EA8077 | |||
| 6476 | dfsvc.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1693682860-607145093-2874071422-1001\932a2db58c237abd381d22df4c63a04a_bb926e54-e3ca-40fd-ae90-2764341e7792 | binary | |
MD5:D2DED43CE07BFCE4D1C101DFCAA178C8 | SHA256:8EEE9284E733B9D4F2E5C43F71B81E27966F5CD8900183EB3BB77A1F1160D050 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
25
DNS requests
14
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
6476 | dfsvc.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
6476 | dfsvc.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAuTYAUbzPZmQpmJmNW6l84%3D | unknown | — | — | unknown |
7464 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | unknown |
6476 | dfsvc.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | unknown |
4896 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
4896 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2432 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6476 | dfsvc.exe | 45.126.208.193:443 | thomsonreutersdownloads.top | RELIABLESITE | US | unknown |
6476 | dfsvc.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | unknown |
6544 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| unknown |
google.com |
| unknown |
crl.microsoft.com |
| unknown |
thomsonreutersdownloads.top |
| unknown |
ocsp.digicert.com |
| unknown |
login.live.com |
| unknown |
client.wns.windows.com |
| unknown |
arc.msn.com |
| unknown |
slscr.update.microsoft.com |
| unknown |
www.microsoft.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
1348 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |