| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/882a17e6-7f8d-4252-8cf8-bb5bfd479973 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 02:08:43 |
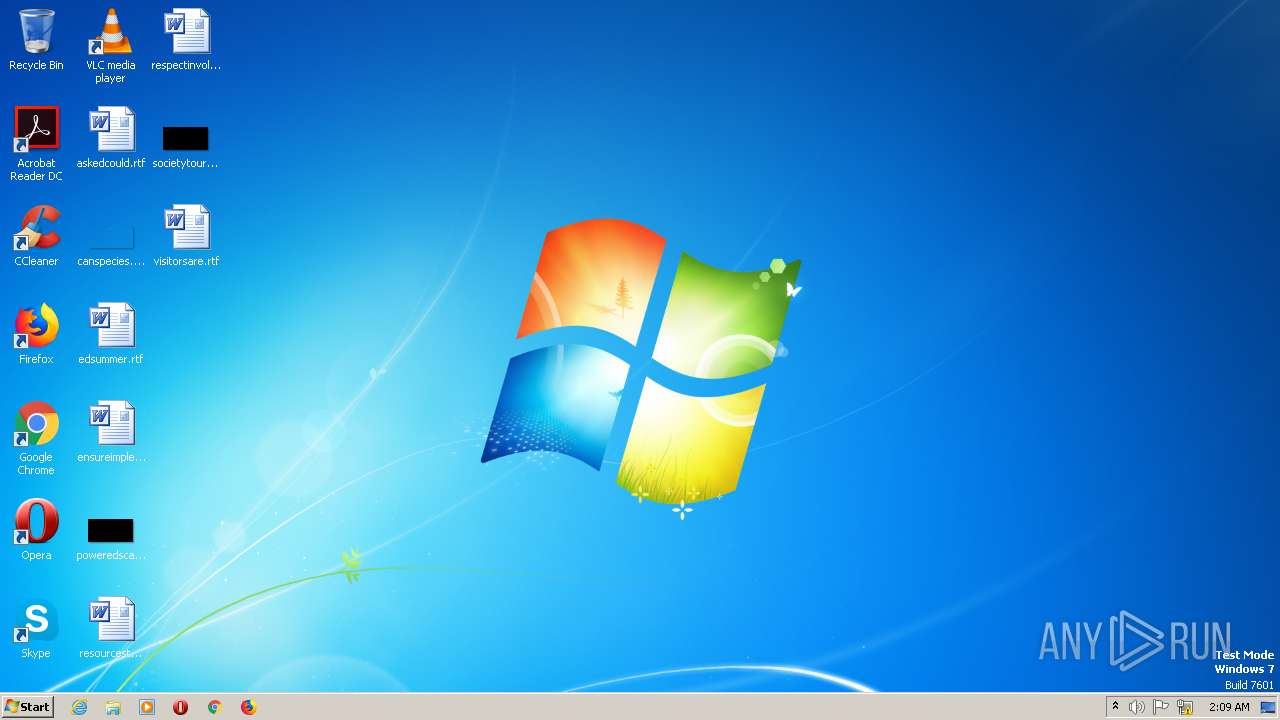
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 71D7642A17F565F951D4AD1883F65C7B |
| SHA1: | 26311D285CDBC64E368AFB40F1509E0369314DB7 |
| SHA256: | B1DCBE40B8C9E76486412C5FA3EF326EB1BB0289691E4022BA8DDE878816FDF6 |
| SSDEEP: | 3072:qSs2lQFOot8XlD8RiZROpCRZ6m5C0IDJ6XZpQ5reDT8nugc3XZpxwWM7vy:llQovlDQpYZj5C0KJUzS8T8nGyV |
MALICIOUS
Application was injected by another process
- explorer.exe (PID: 1928)
Runs injected code in another process
- setup.exe (PID: 1920)
SUSPICIOUS
Executable content was dropped or overwritten
- explorer.exe (PID: 1928)
Reads the Internet Settings
- explorer.exe (PID: 1928)
The process executes via Task Scheduler
- jbhtujv (PID: 696)
INFO
Checks supported languages
- setup.exe (PID: 1920)
- jbhtujv (PID: 696)
Creates files or folders in the user directory
- explorer.exe (PID: 1928)
The process checks LSA protection
- explorer.exe (PID: 1928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductName: | Imba |
|---|---|
| LegalCopyright: | Copyright (C) 2023, shmaer |
| InternalName: | GodGuest |
| FilesVersion: | 19.62.99 |
| CharacterSet: | Unknown (01F2) |
| LanguageCode: | Manipuri |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Unknown (0x20461) |
| FileFlags: | (none) |
| FileFlagsMask: | 0x121a |
| ProductVersionNumber: | 26.0.0.0 |
| FileVersionNumber: | 2.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x9460 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 496640 |
| CodeSize: | 202240 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2022:07:04 03:21:39+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Jul-2022 03:21:39 |
| Detected languages: |
|
| Debug artifacts: |
|
| FilesVersion: | 19.62.99 |
| InternalName: | GodGuest |
| LegalCopyright: | Copyright (C) 2023, shmaer |
| ProductName: | Imba |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 04-Jul-2022 03:21:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000314F4 | 0x00031600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.42973 |
.data | 0x00033000 | 0x0006FA3C | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.47973 |
.rsrc | 0x000A3000 | 0x00007180 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.68741 |
.reloc | 0x000AB000 | 0x000024F6 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.50257 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.33869 | 460 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 4.85792 | 2216 | UNKNOWN | Spanish - Mexico | RT_ICON |
3 | 4.69237 | 1736 | UNKNOWN | Spanish - Mexico | RT_ICON |
4 | 4.27344 | 1384 | UNKNOWN | Spanish - Mexico | RT_ICON |
5 | 3.66578 | 9640 | UNKNOWN | Spanish - Mexico | RT_ICON |
6 | 3.75997 | 4264 | UNKNOWN | Spanish - Mexico | RT_ICON |
7 | 3.78583 | 2440 | UNKNOWN | Spanish - Mexico | RT_ICON |
8 | 3.86078 | 1128 | UNKNOWN | Spanish - Mexico | RT_ICON |
22 | 3.18508 | 588 | UNKNOWN | UNKNOWN | RT_STRING |
23 | 3.22732 | 628 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
WINHTTP.dll |
Total processes
34
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 696 | C:\Users\admin\AppData\Roaming\jbhtujv | C:\Users\admin\AppData\Roaming\jbhtujv | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1920 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1928 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
300
Read events
296
Write events
4
Delete events
0
Modification events
| (PID) Process: | (1928) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{01979c6a-42fa-414c-b8aa-eee2c8202018}.check.100 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB010000002C63AF80A6AE514E8E5F5AD740560F840000000002000000000010660000000100002000000024CB95F1F7D78447E0C8319DC503C07C36C86A9550CB710051C8D19EB09826D7000000000E8000000002000020000000D9A9800B1F7A12A34509AE4479B3FA2B7E55BED3E25034407AAB2758B78364BEB0000000B32577DC3BA7094EA2E3AE39CC39482220145587C09BC7C4DF6D2D3844AADEACC3D784661DEDFB7C5C6CCB07AC76F156716BC8E34A7F468A1E10BF4548C1370447A46D3DCDB63A8B970740D9EA670FE26BCD2BFB30BF379E1E64E798B4635C8AABCA869972952172F7DDC3543253E2D156EBEBF5F40085006EA35049B59BC6A2C9E7D30B2B4AAC5B1911F3417F14DE7610372BA7AF146404D026E16BEB19D30D5B67F385973F8AB7D338D927FAF9E49440000000FA5CE70883661D4CE45F4BED274E47F22FAC293E2DF762BB821A9B7A1E4D20E31C82095F541B2014DE7513E39DC50717F96DDB7F8DC417DE581E33585411E85D | |||
| (PID) Process: | (1928) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB010000002C63AF80A6AE514E8E5F5AD740560F840000000002000000000010660000000100002000000014F75E68FD9F0032EAD326486AFD81C2AD59C520AFD5A9B887CB9846879B87B8000000000E80000000020000200000008DCBB1D1C897479C863F50EE0A2ABDFCD0F574B6E611956F0432D2F51AD53629300000000C69D971182631510AB82B185476A5C7DA1A7795B8E5B3D2D9D06CB3AE319A810E9A0E25CEDC5C2C5A15F19310402CE4400000007F5925DCD17884C8D2485712DF089C0A226AA7241BD86F02D6A04B70F2ACCBFFF3251679696BA5358D89C50BDDAE7C90E014A5726BBFEBDF634F9B64BA8F1619 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1928 | explorer.exe | C:\Users\admin\AppData\Roaming\jbhtujv | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.195.240.101:80 | hutnilior.net | SEDO GmbH | DE | malicious |
1928 | explorer.exe | 188.114.97.3:80 | potunulit.org | CLOUDFLARENET | NL | malicious |
— | — | 188.114.96.3:80 | potunulit.org | CLOUDFLARENET | NL | malicious |
1928 | explorer.exe | 91.195.240.101:80 | hutnilior.net | SEDO GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
potunulit.org |
| malicious |
dns.msftncsi.com |
| shared |
hutnilior.net |
| malicious |
bulimu55t.net |
| malicious |
soryytlic4.net |
| malicious |