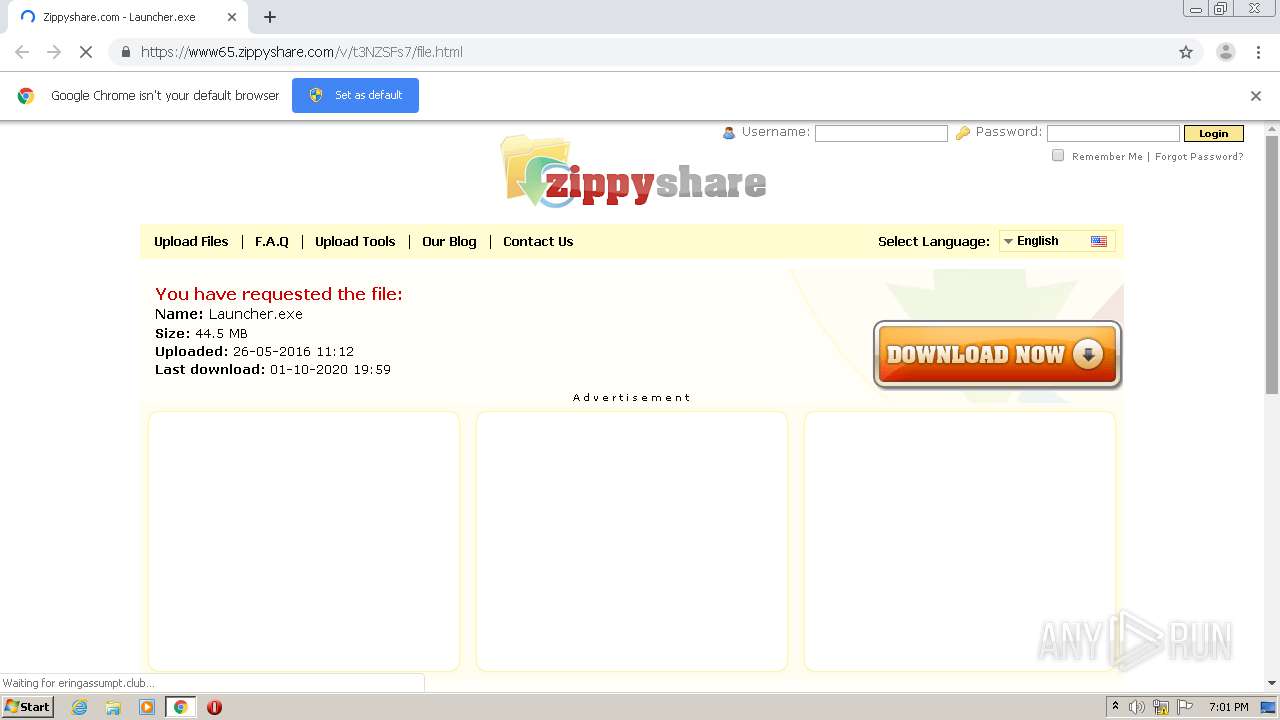
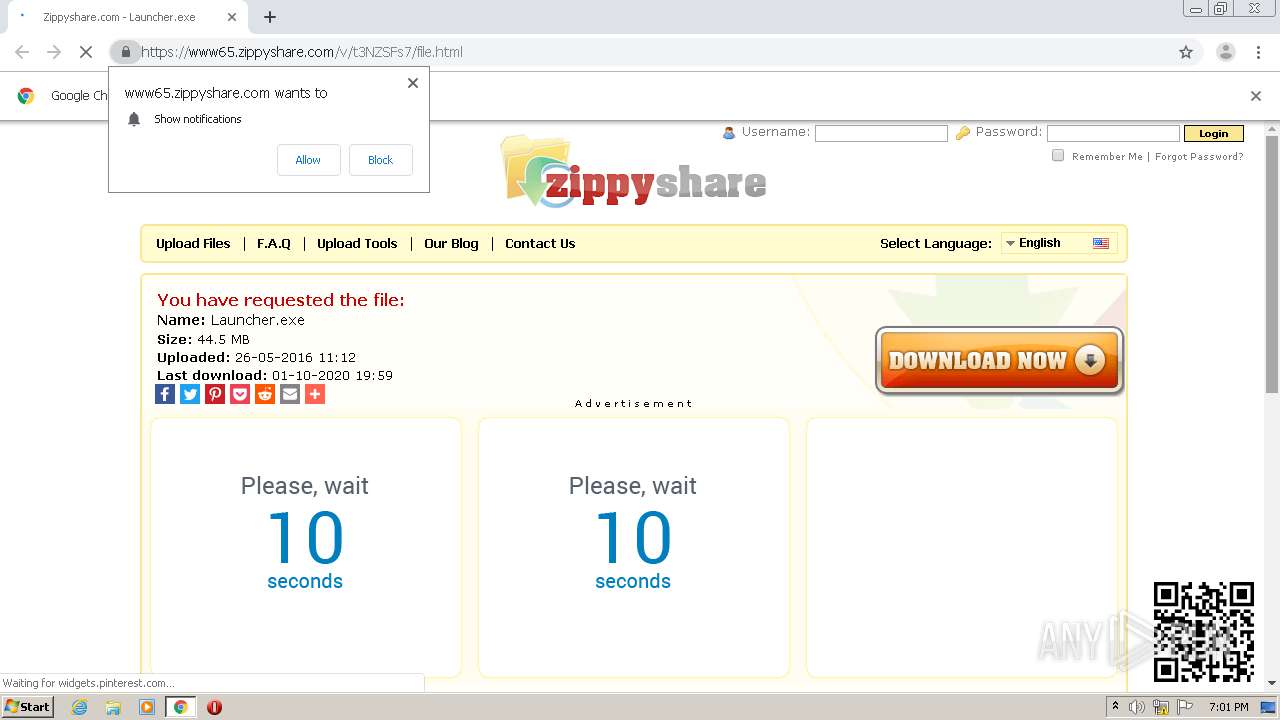
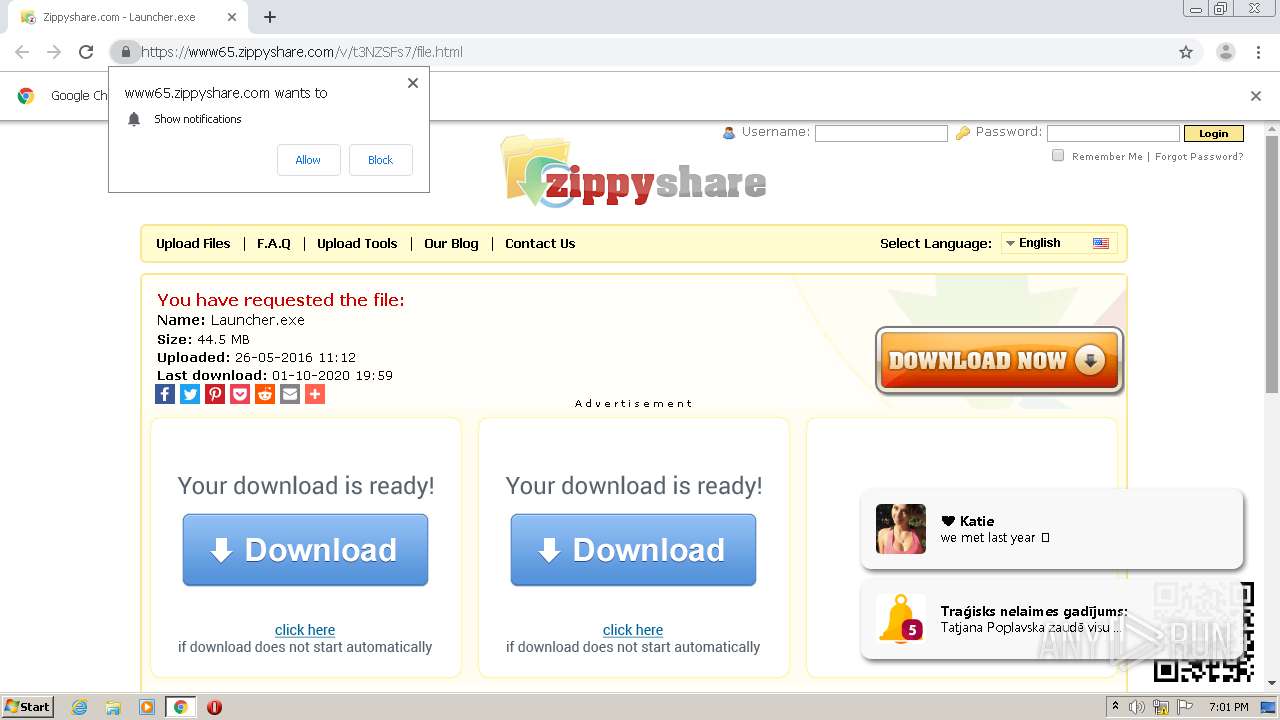
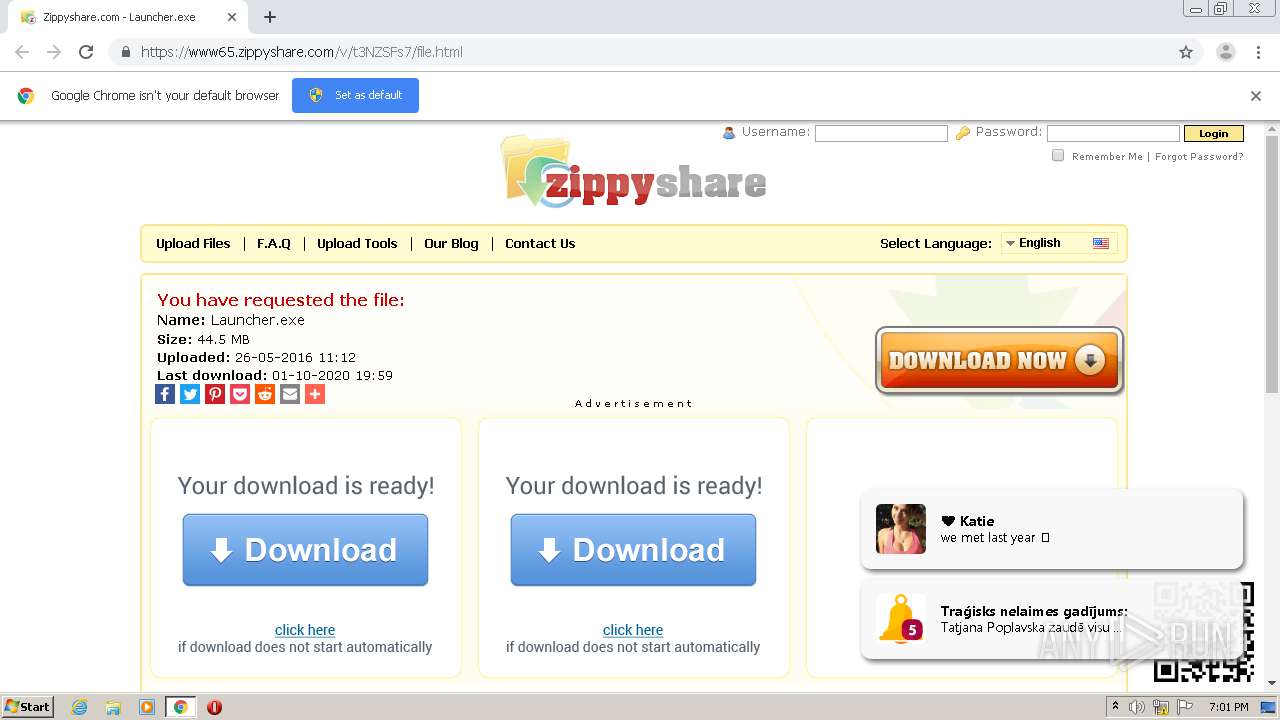
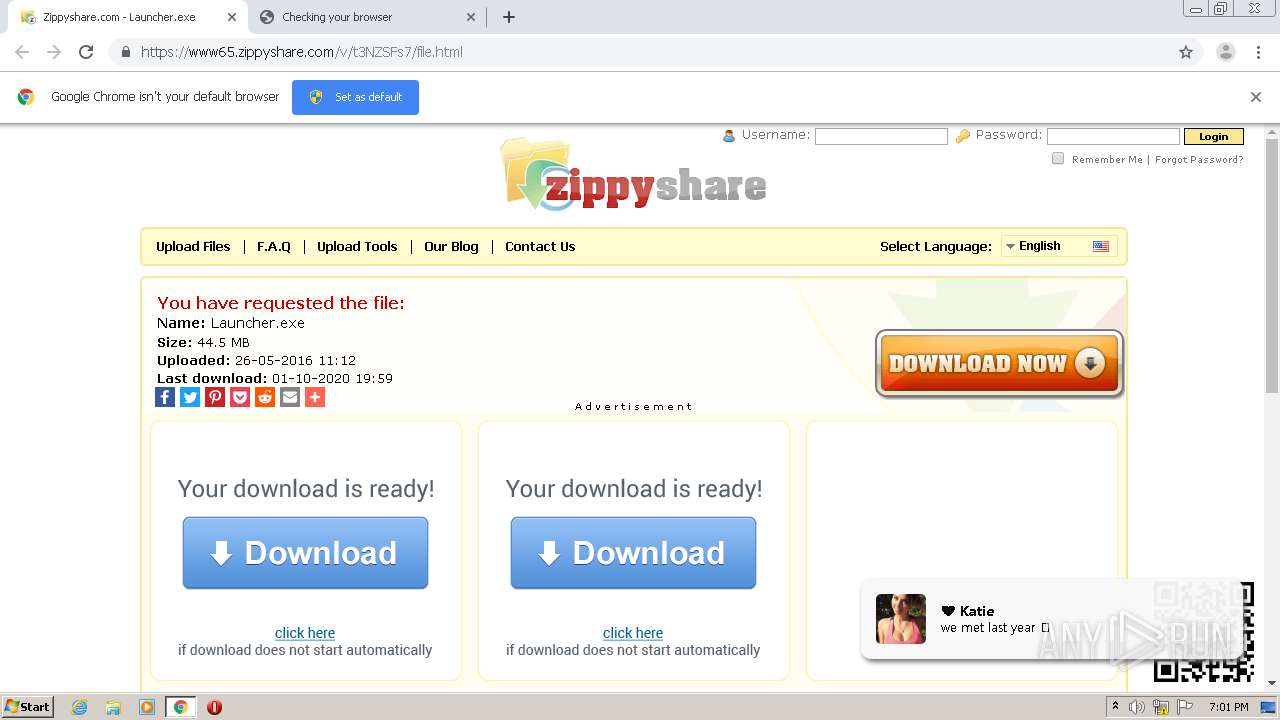
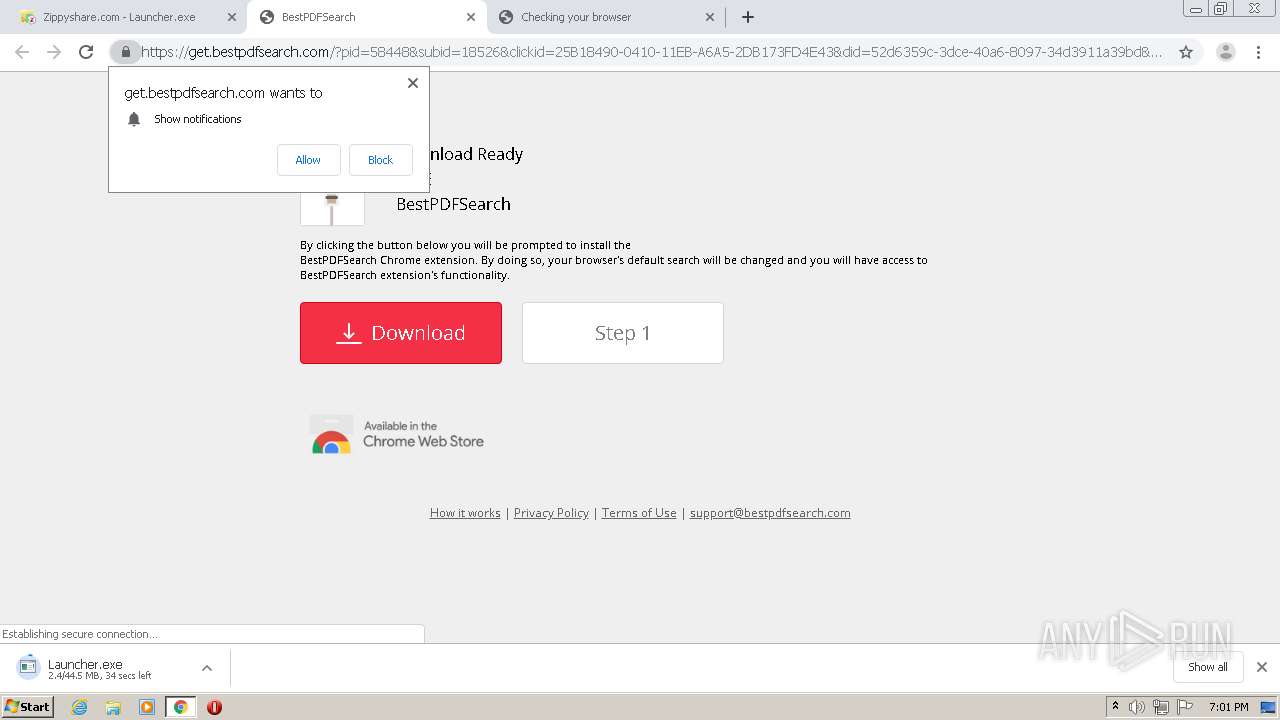
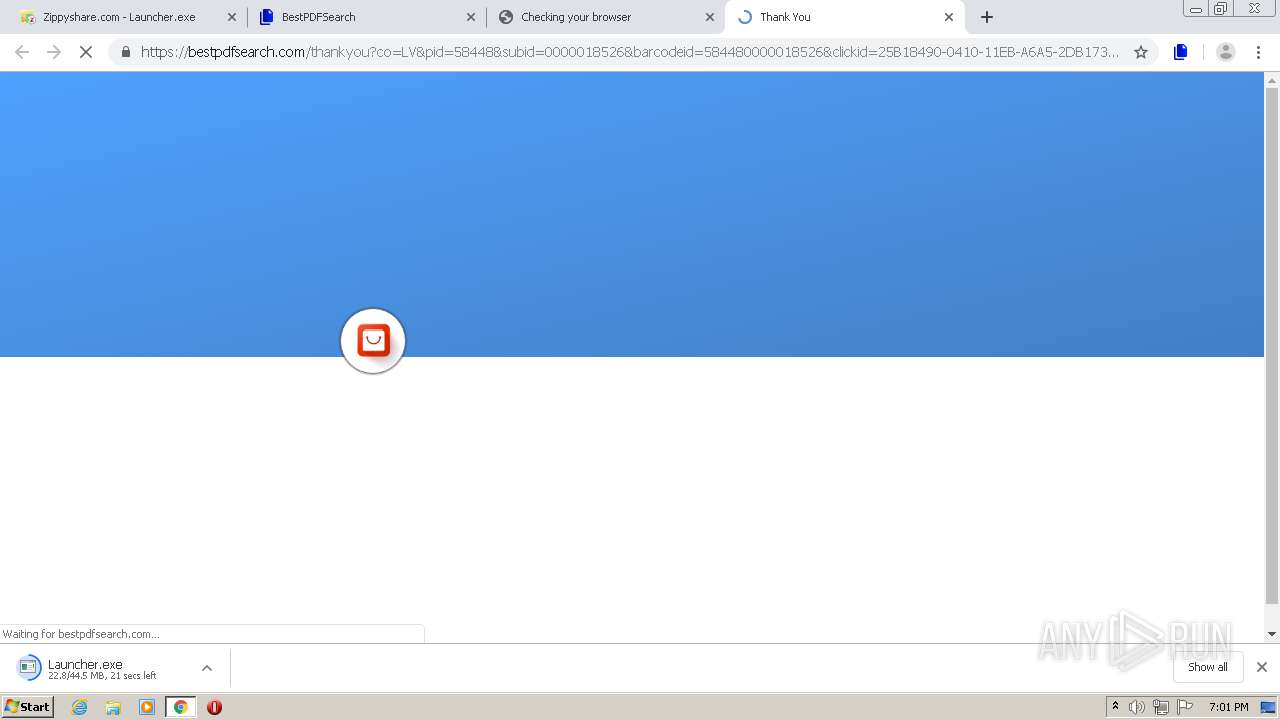
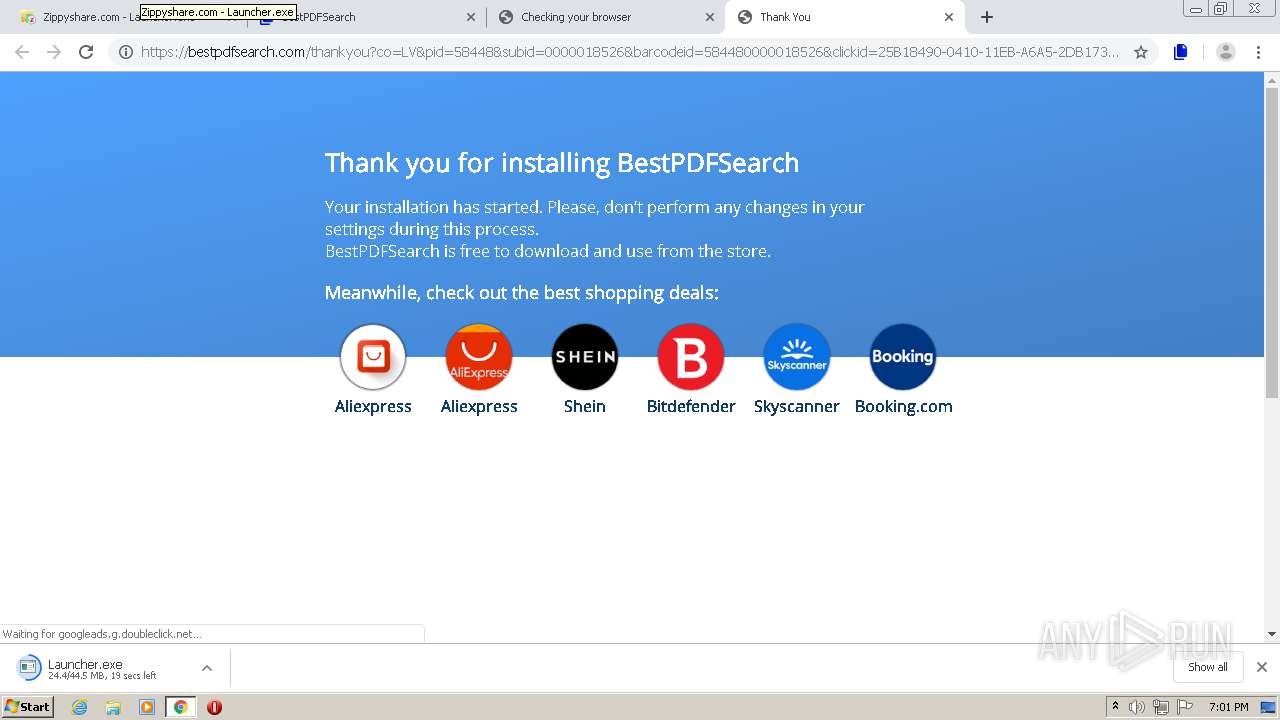
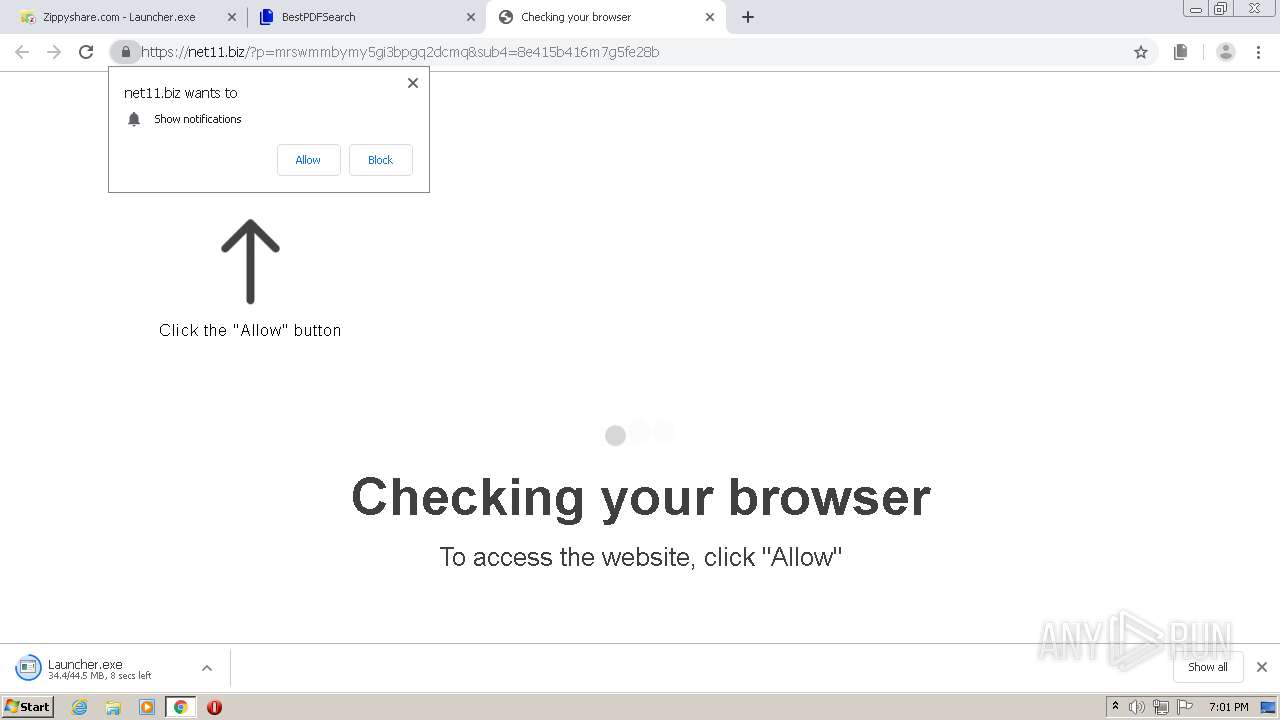
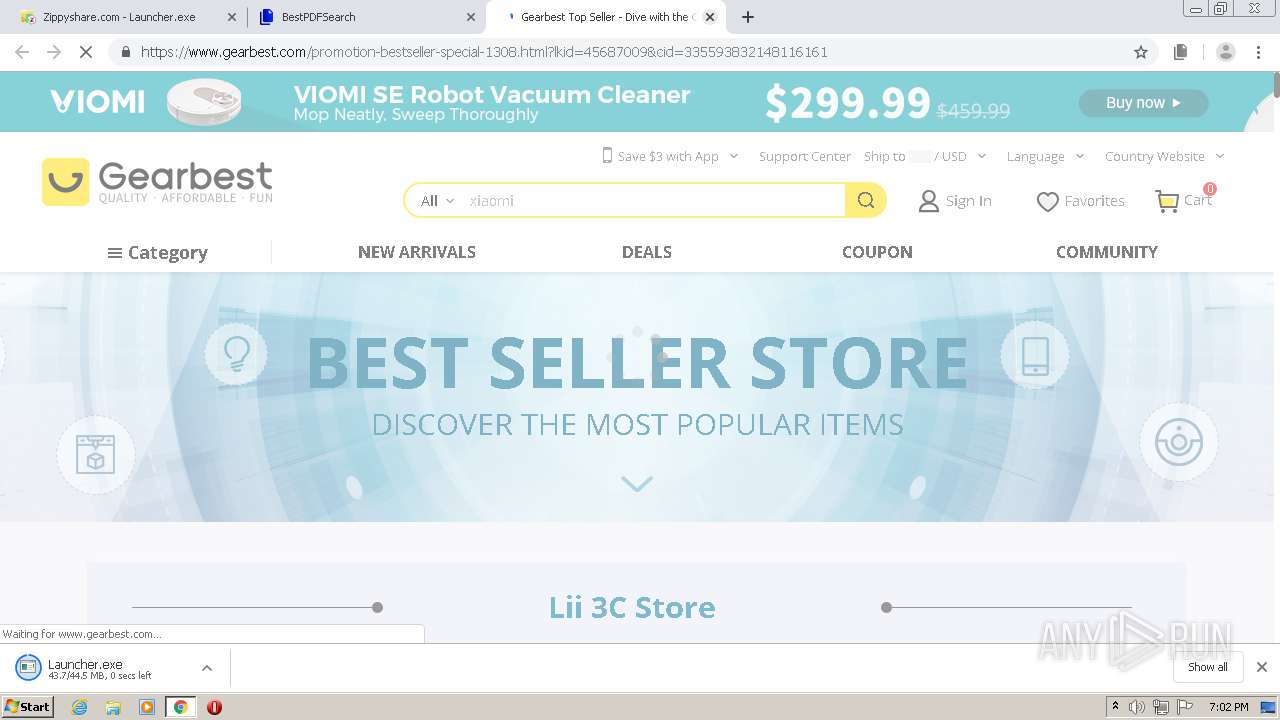
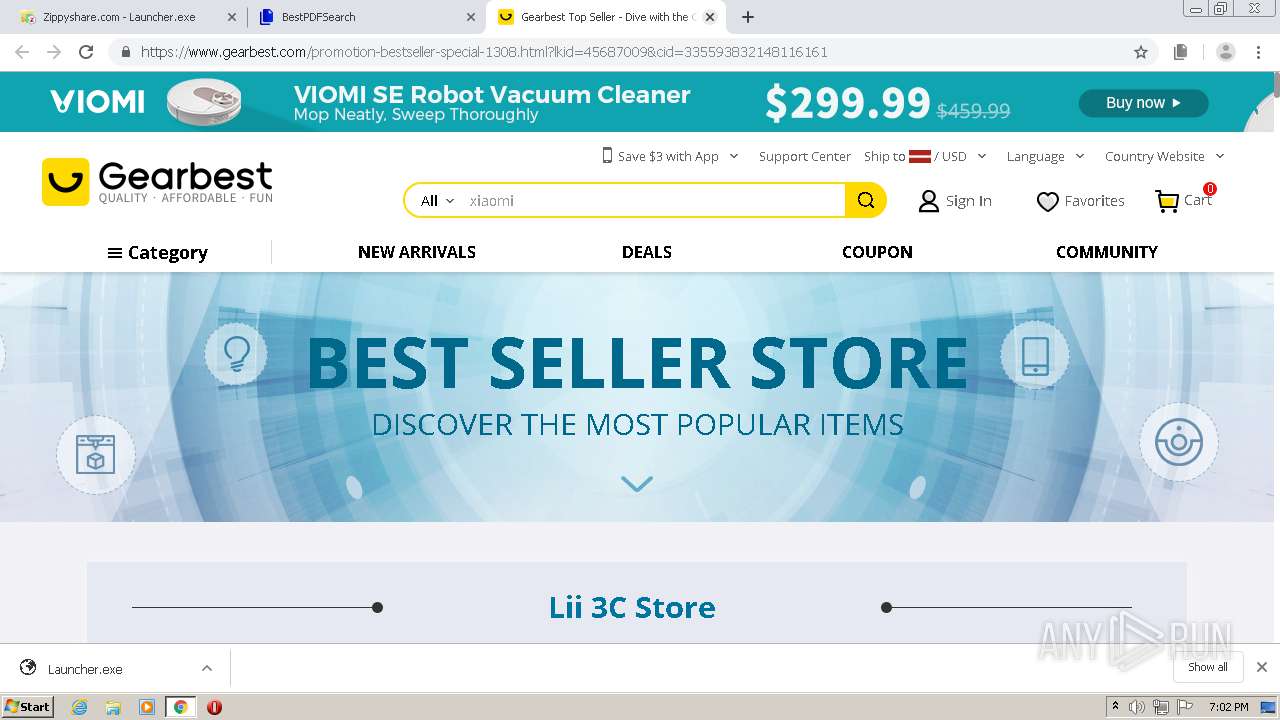
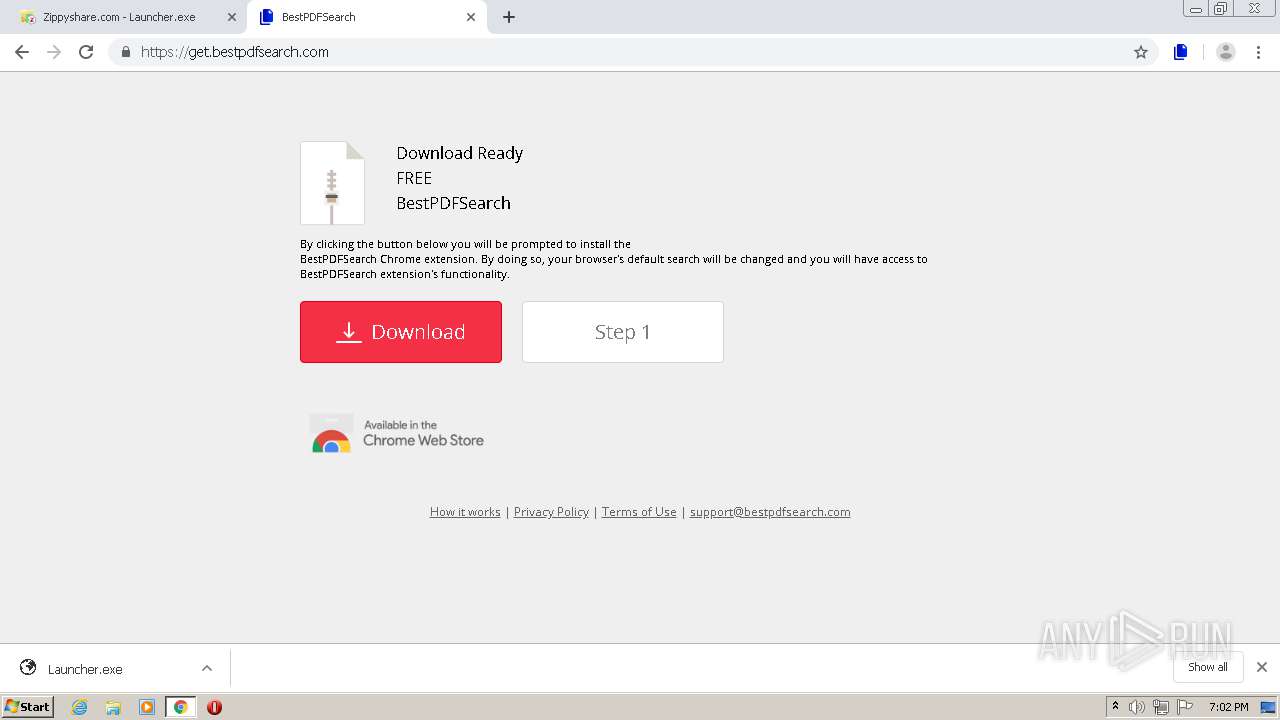
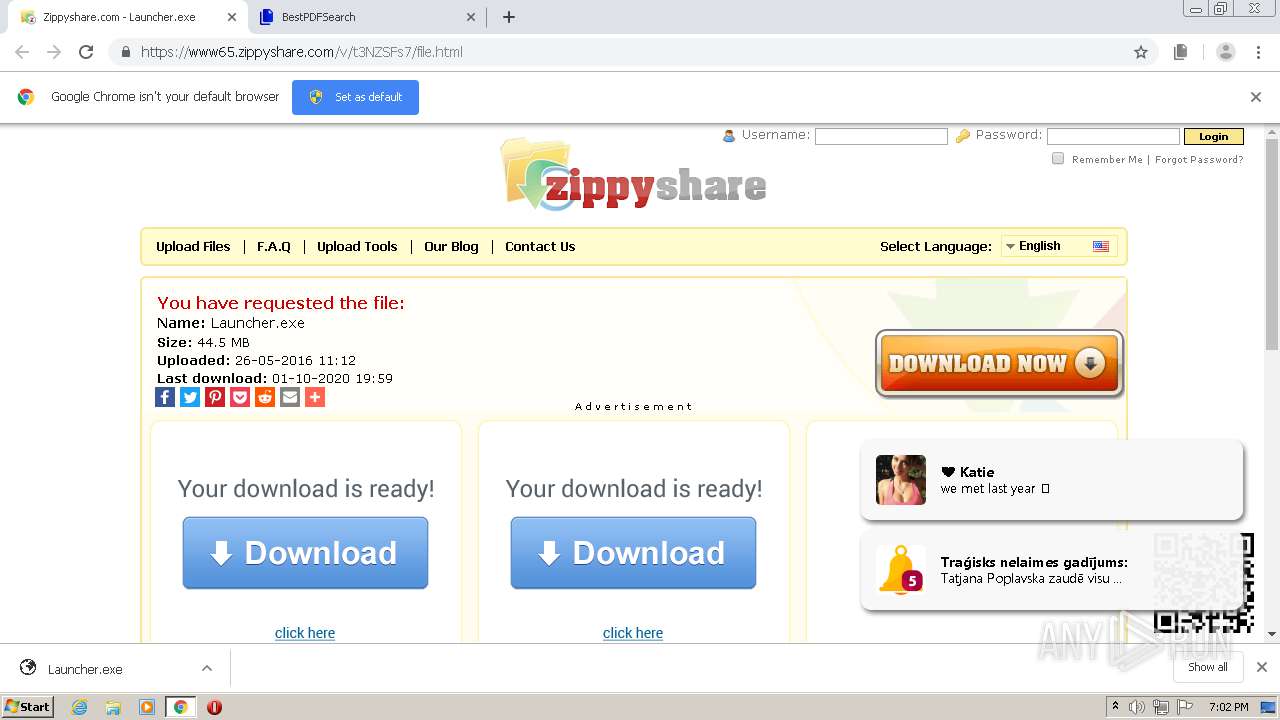
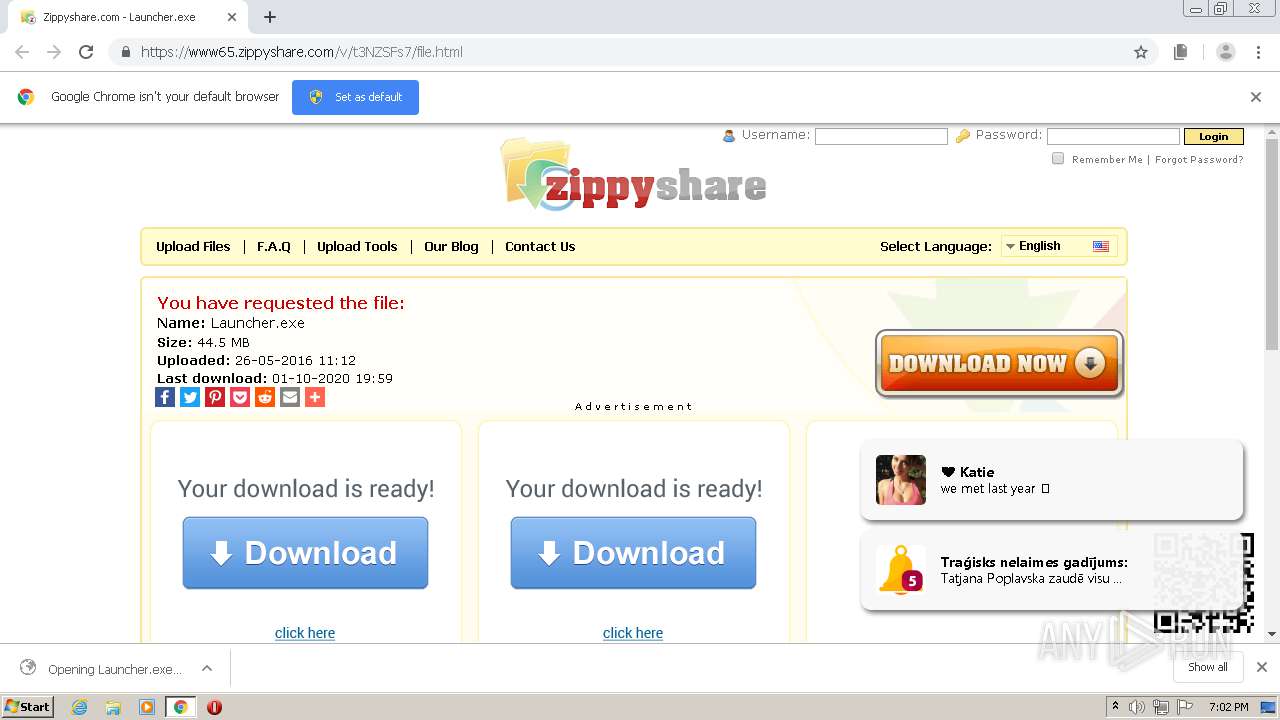
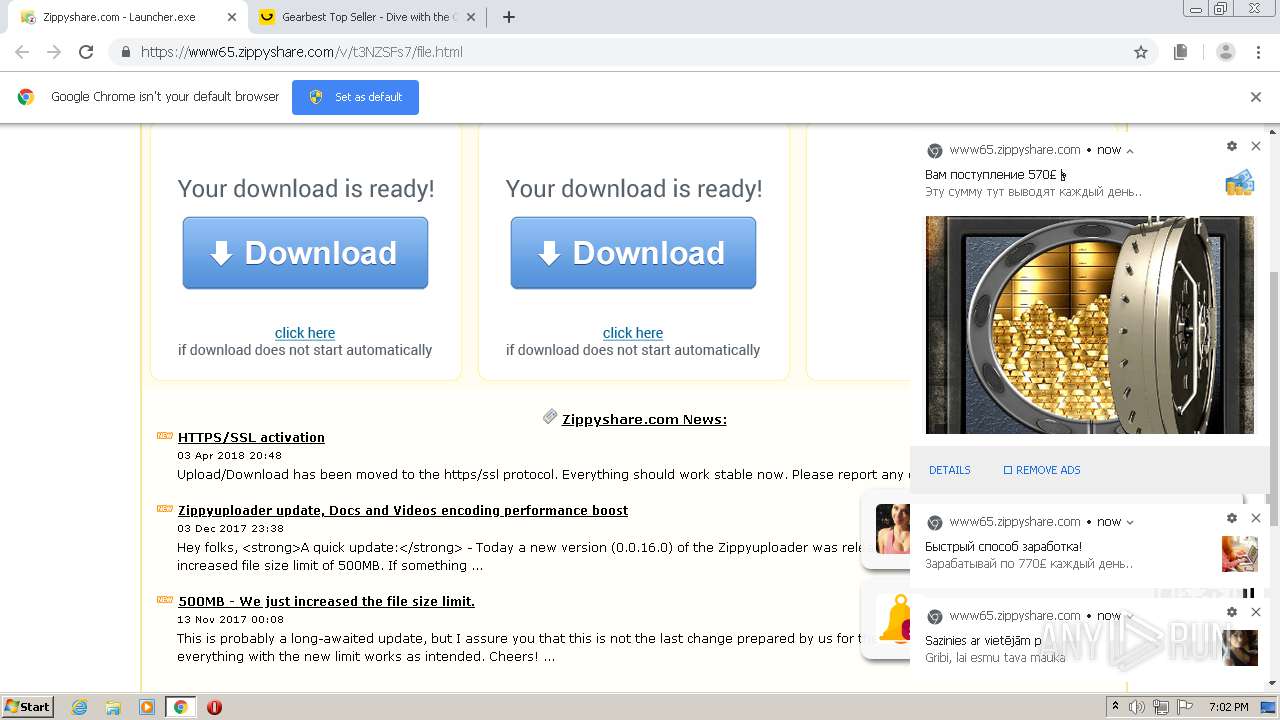
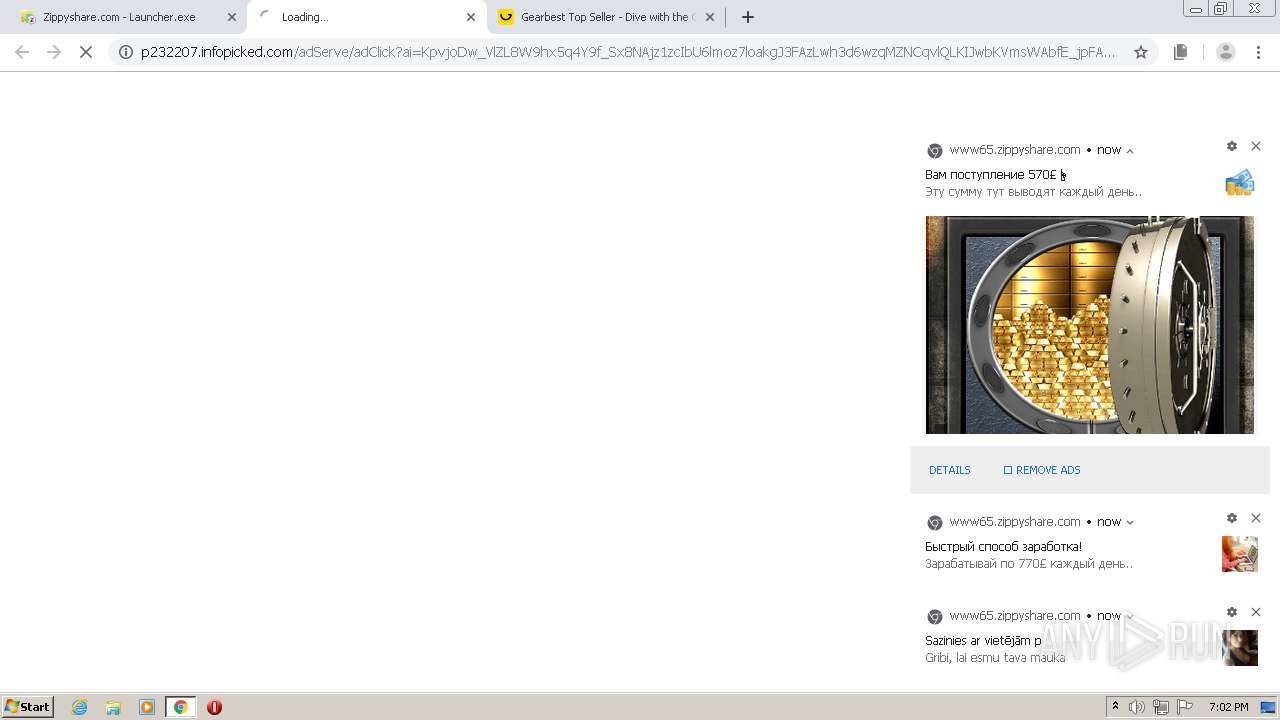
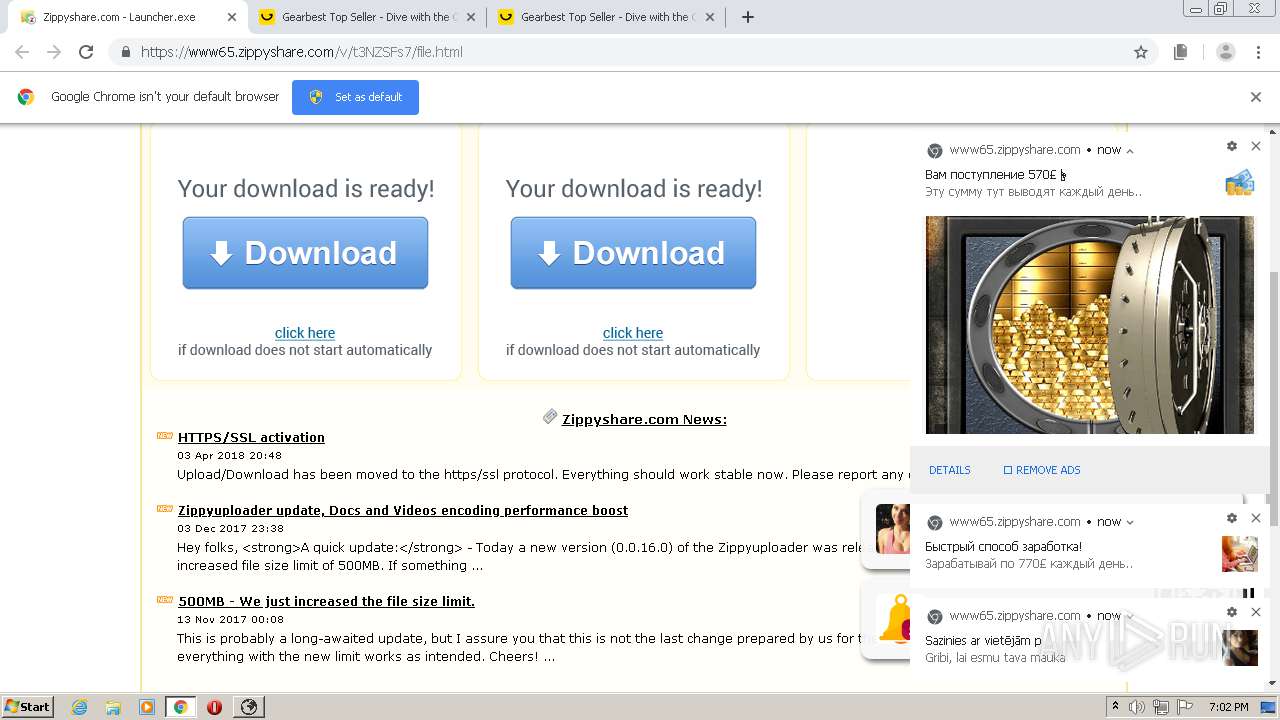
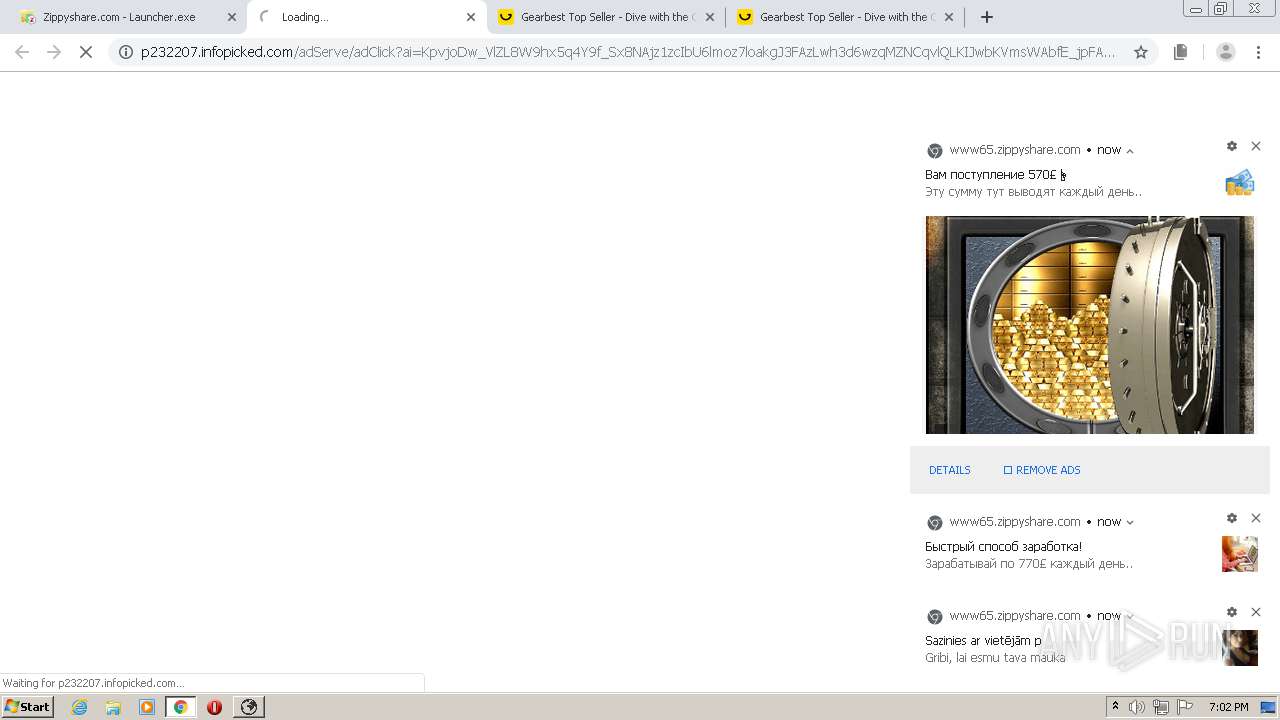
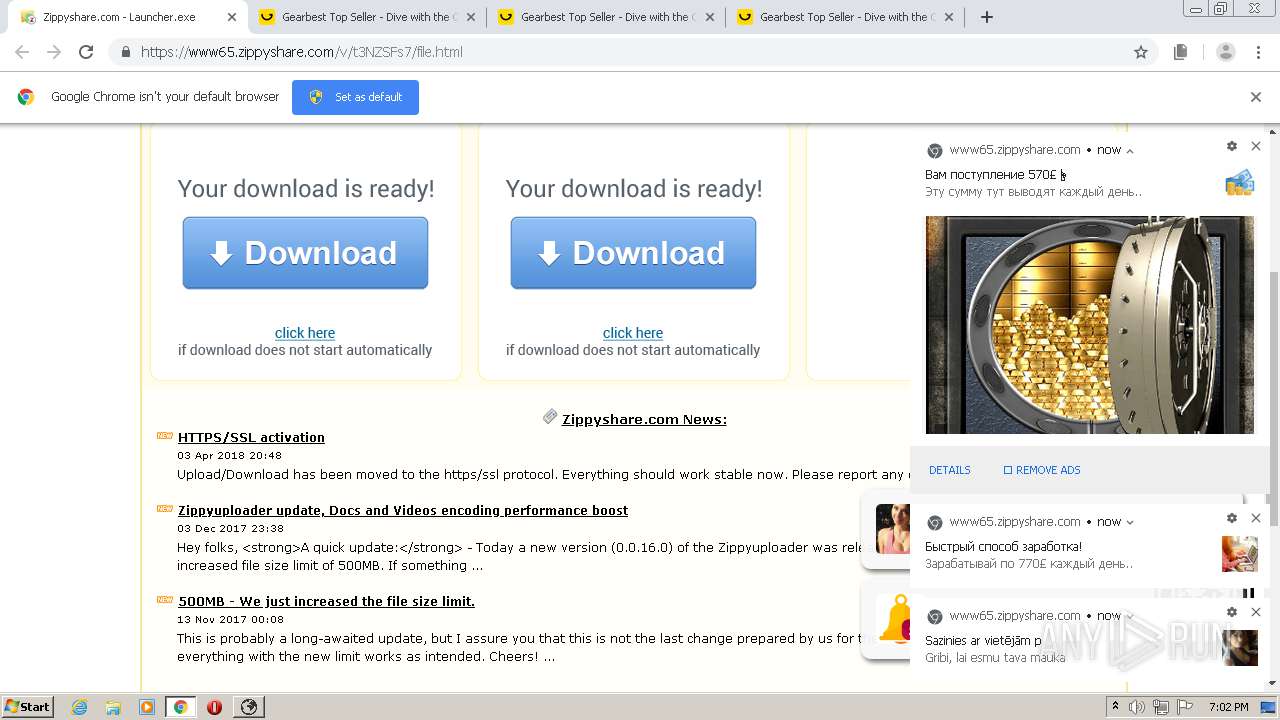
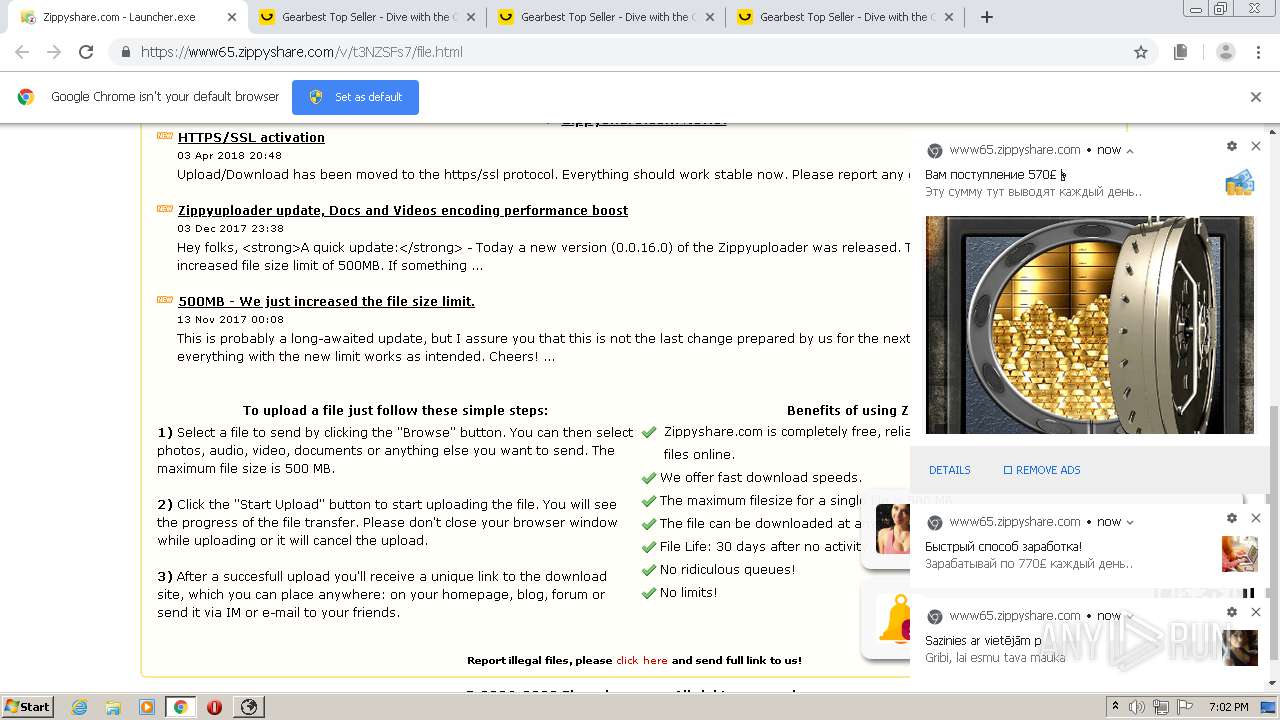
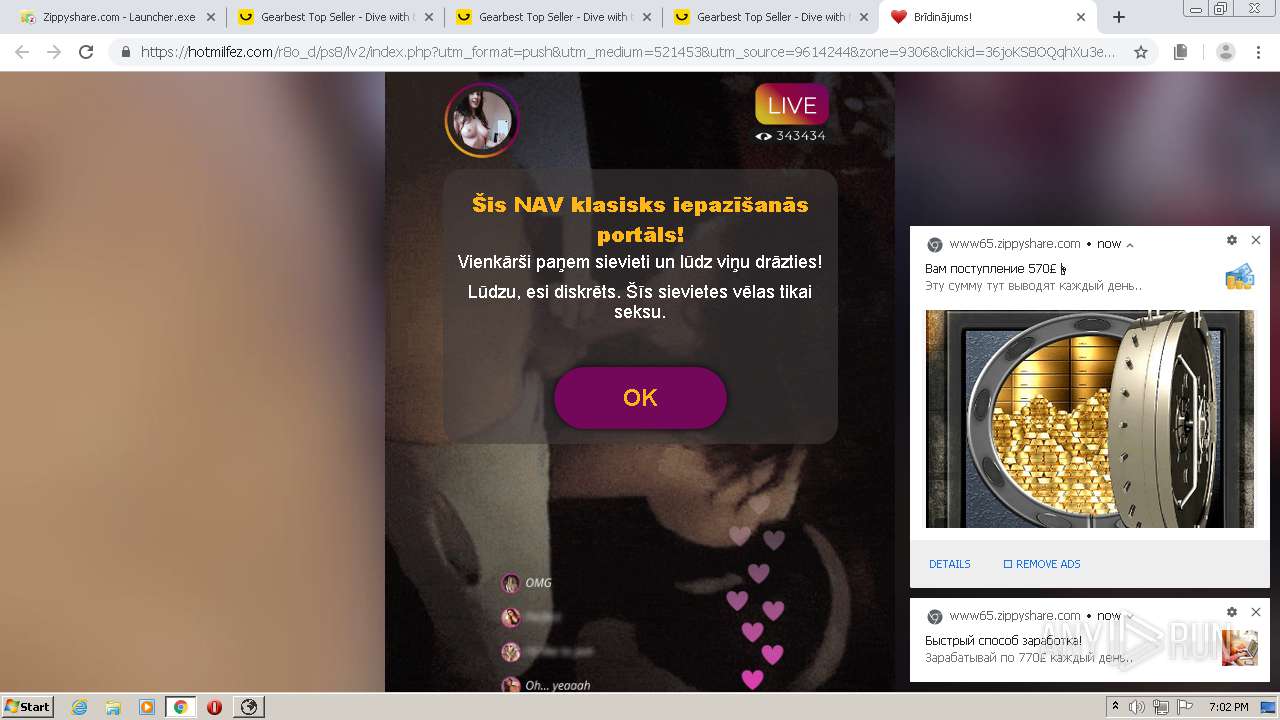
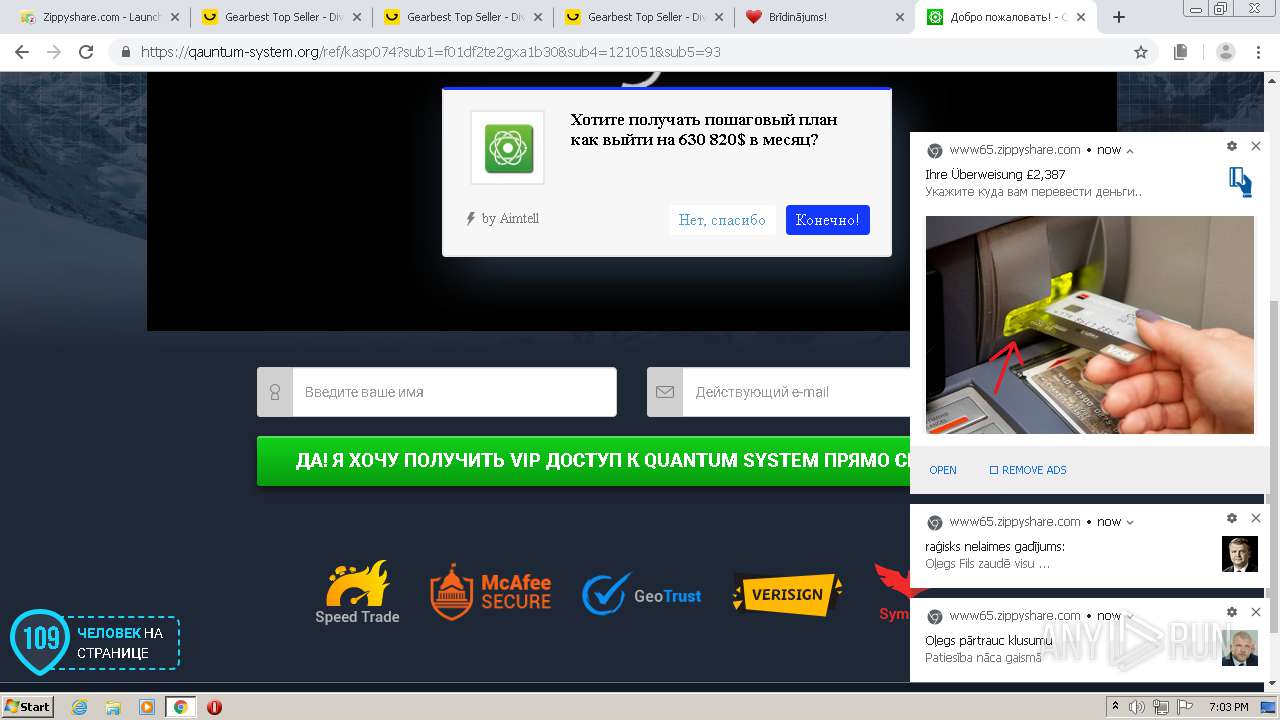
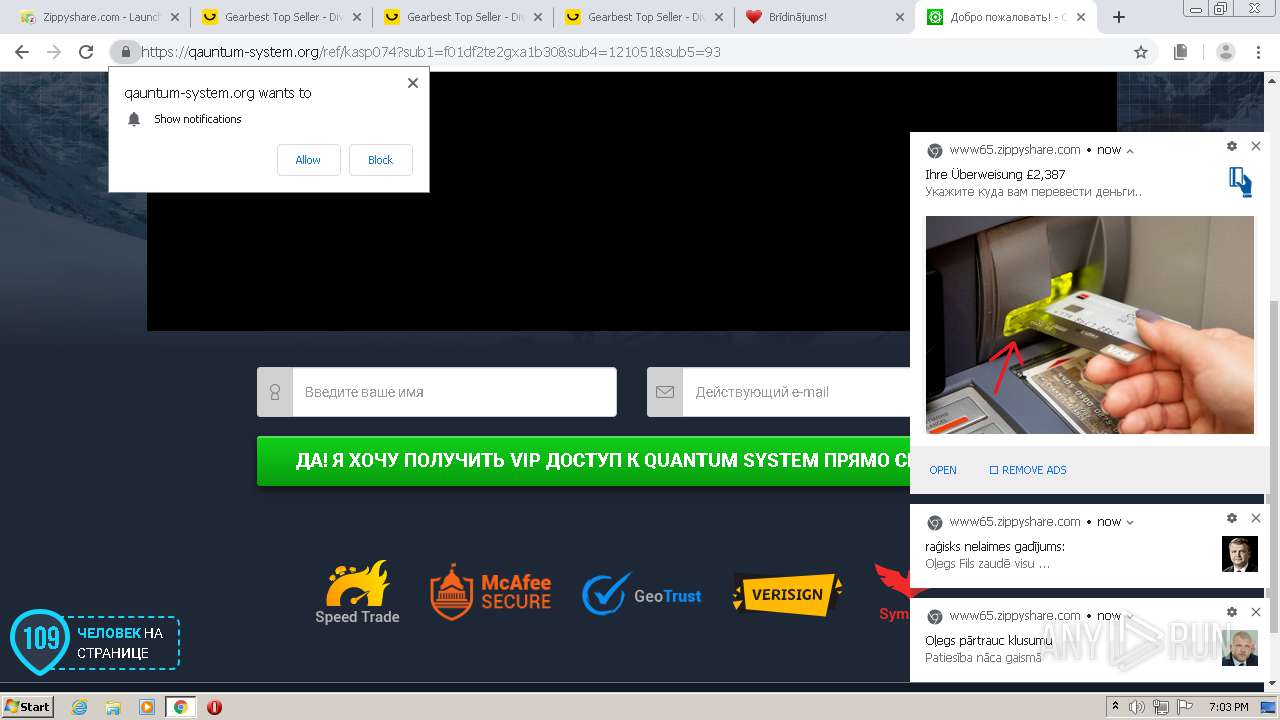
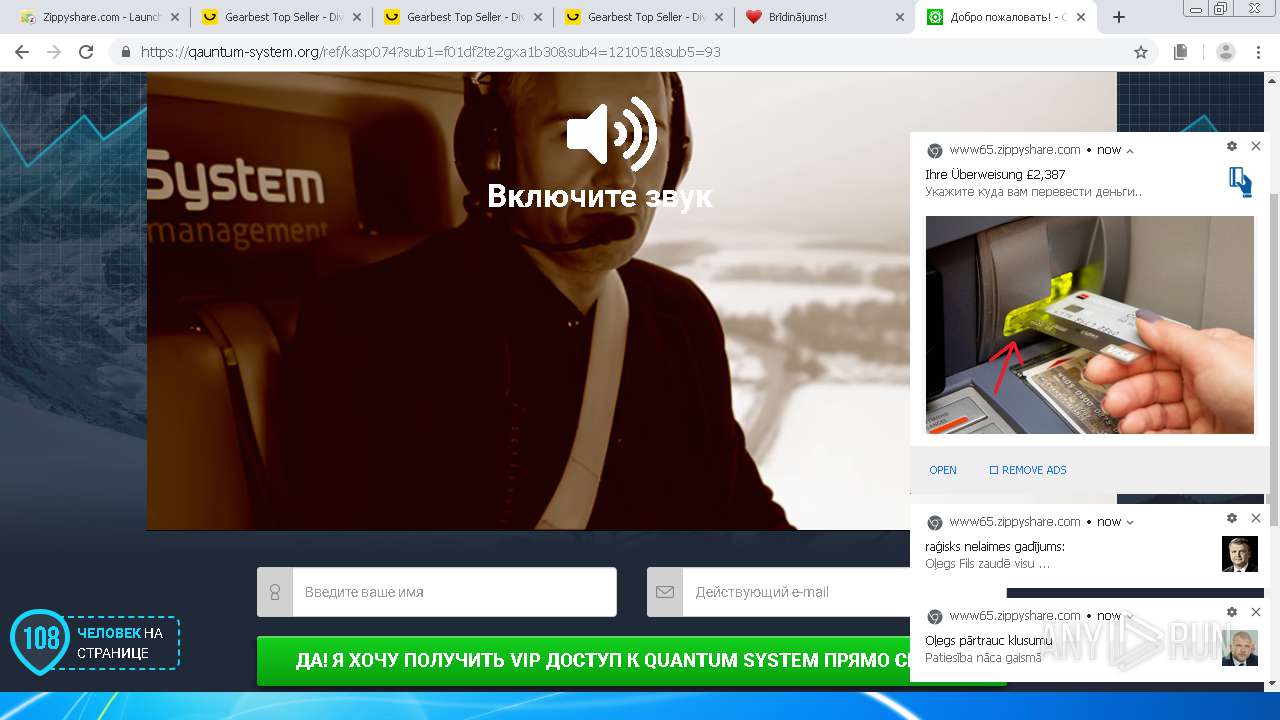
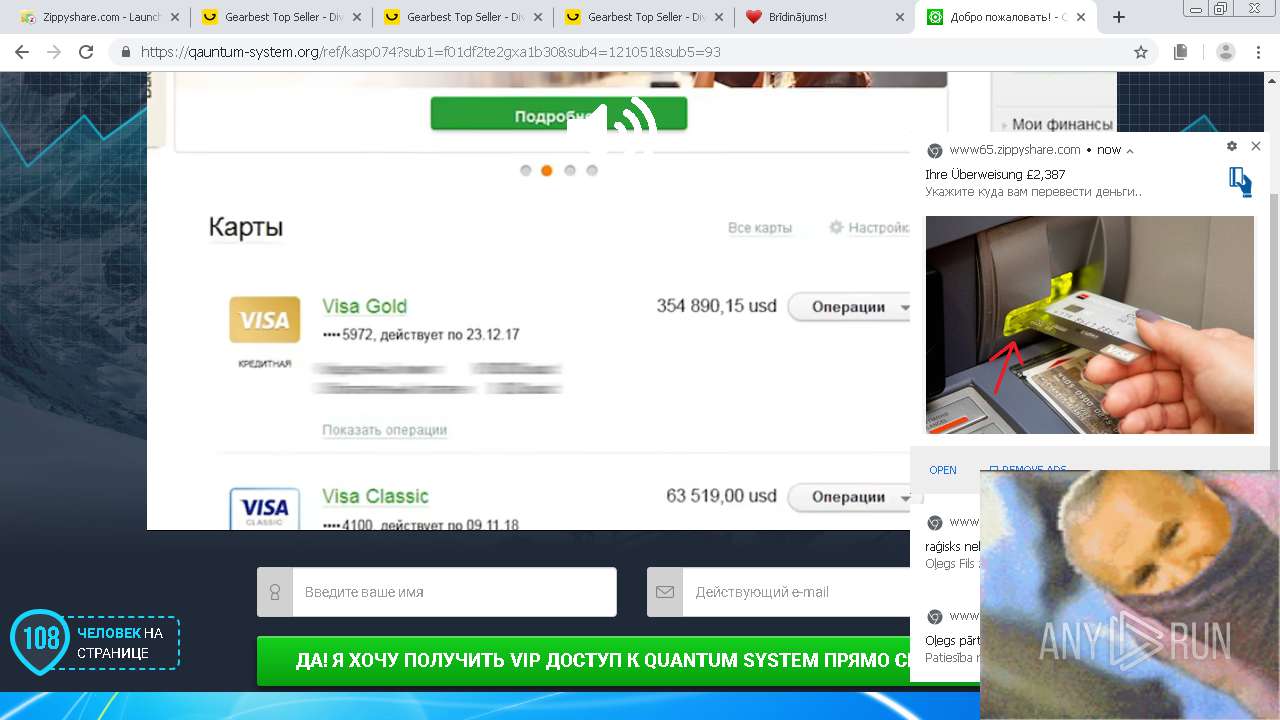
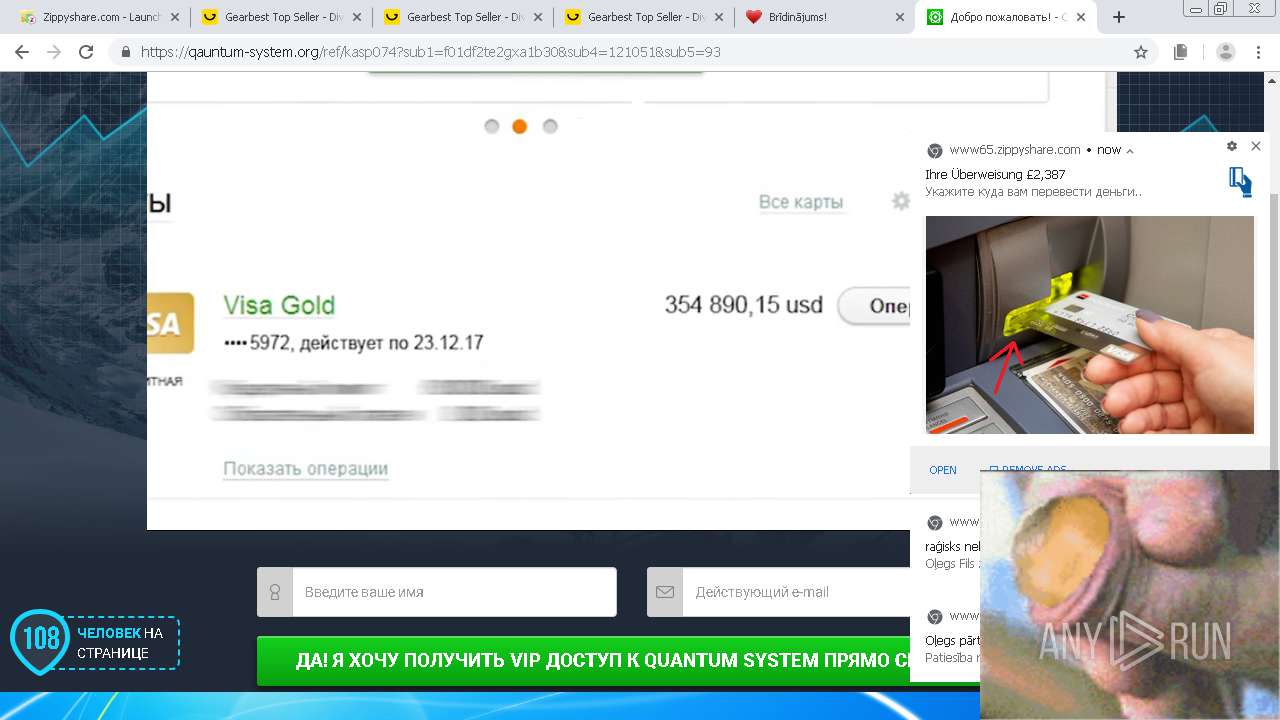
| URL: | https://www65.zippyshare.com/v/t3NZSFs7/file.html |
| Full analysis: | https://app.any.run/tasks/2b656f06-9e16-4ae9-b6c1-ec9d4ba4e6c5 |
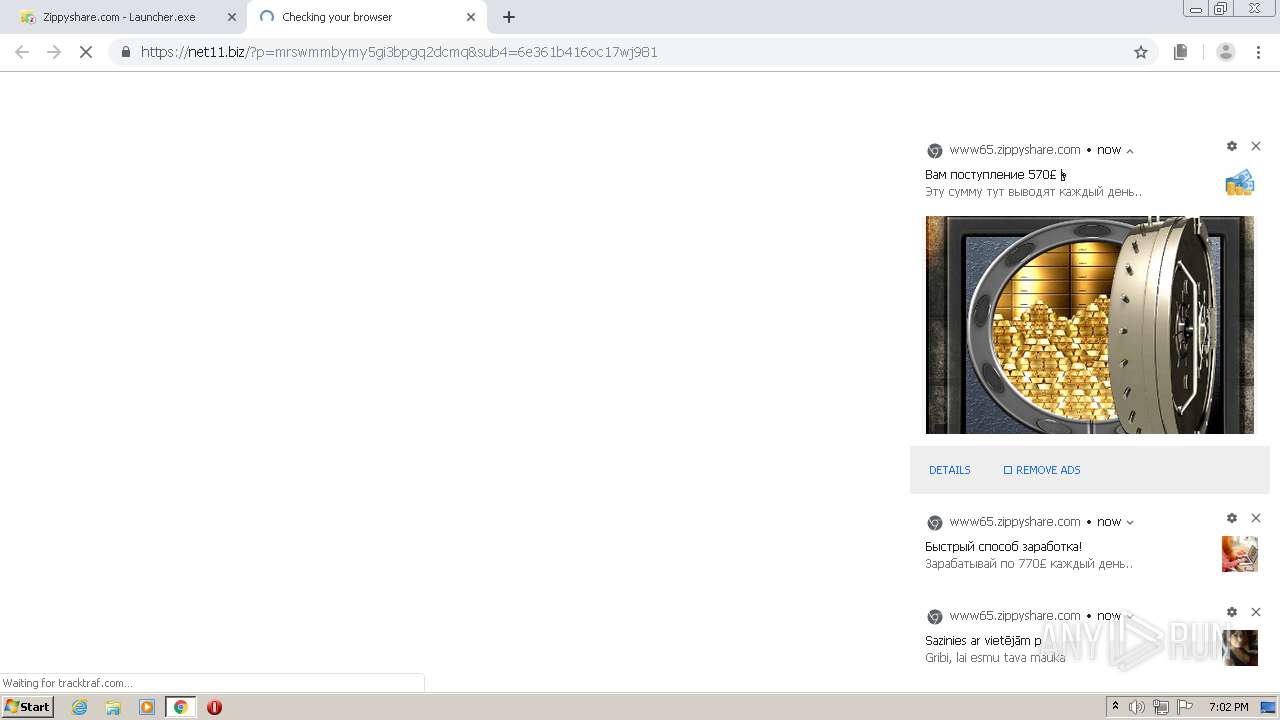
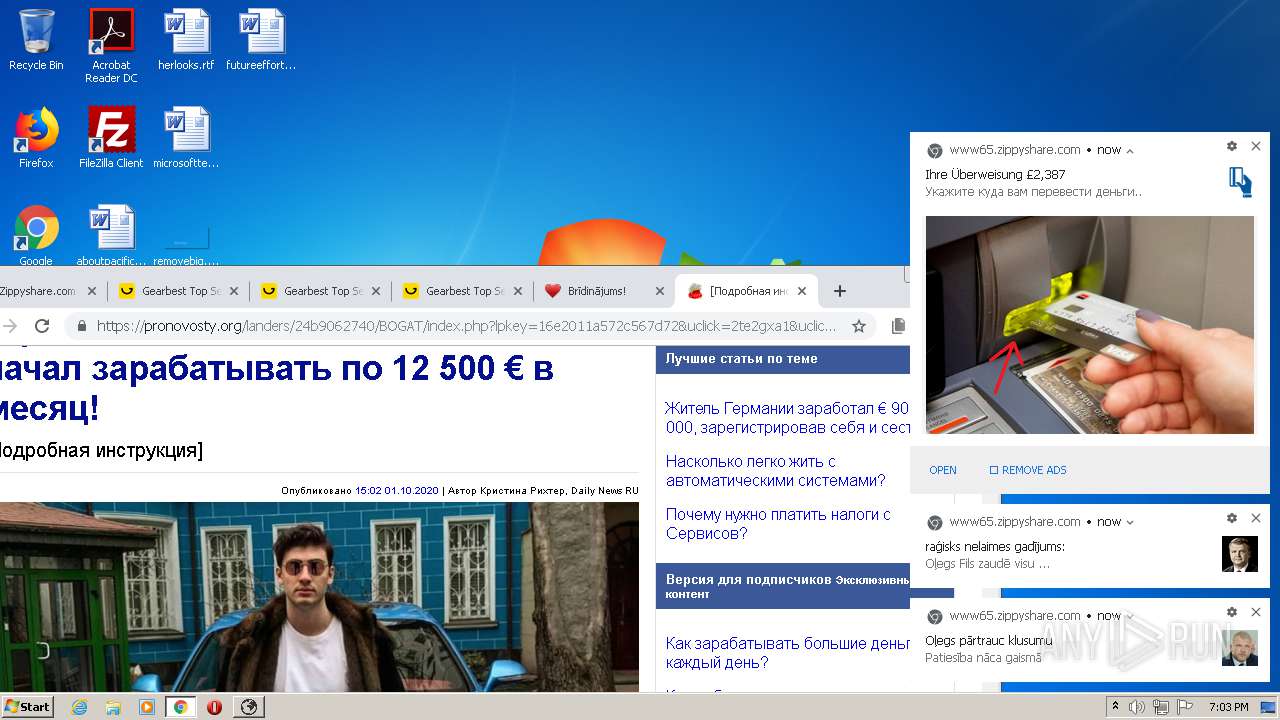
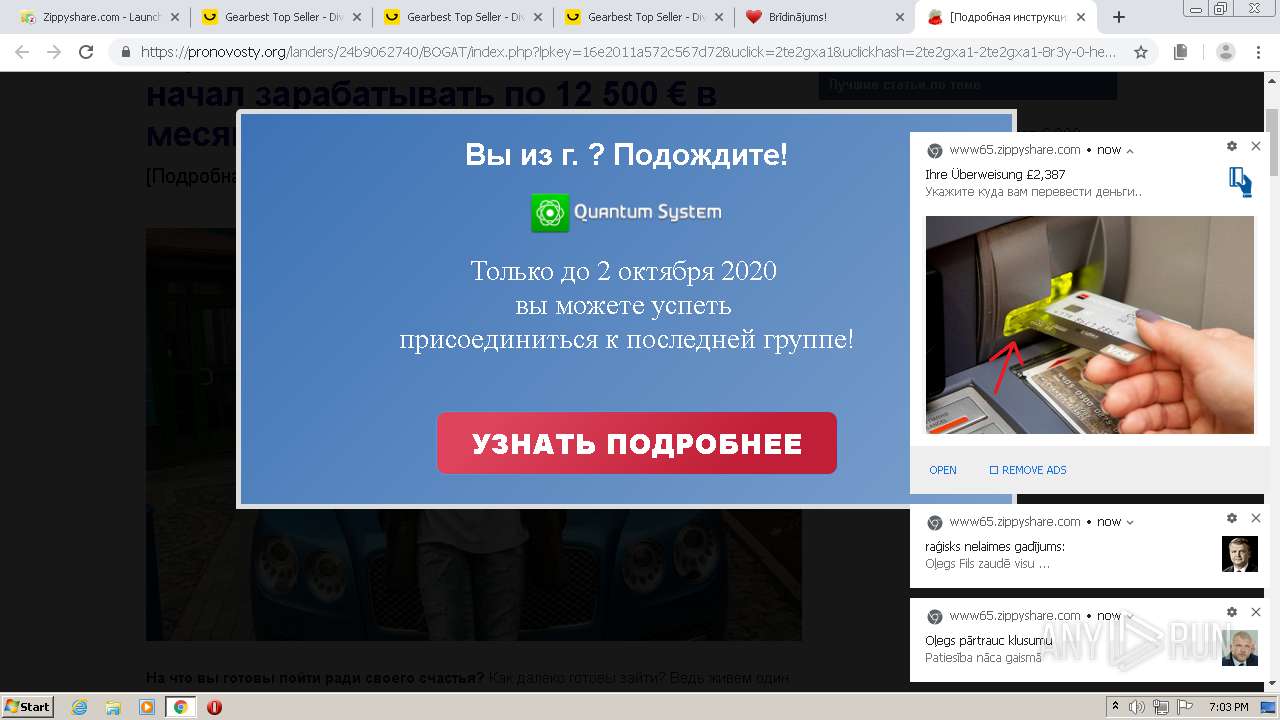
| Verdict: | Malicious activity |
| Analysis date: | October 01, 2020, 18:00:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C792D3B2105D2A7347A4C6C64D5A22BE |
| SHA1: | BA435DD841BC2DF927551996C24E9EA6F837D3BF |
| SHA256: | B1D6F9D1AA14BFA98E5420B1E5B34A8F7EDA3675D72E0D2F56463DDED18795F3 |
| SSDEEP: | 3:N8DSTAwGKjKwAgWJ:2OTAwGjPRJ |
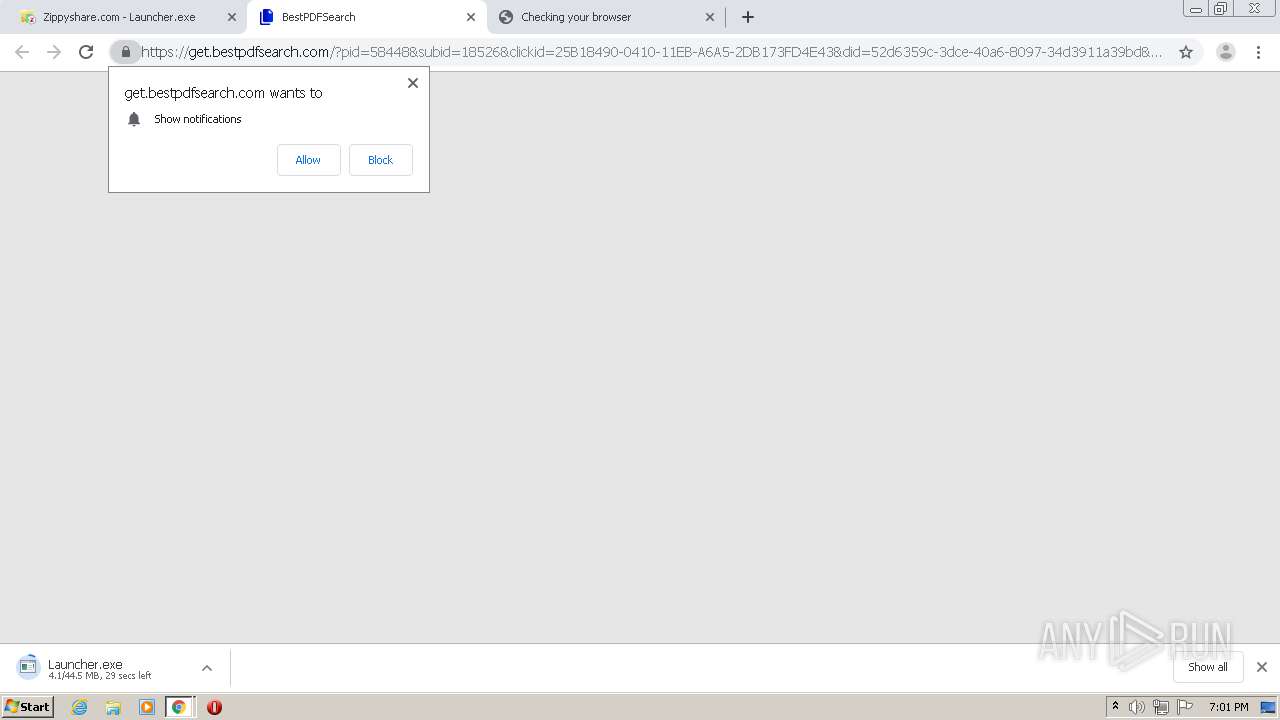
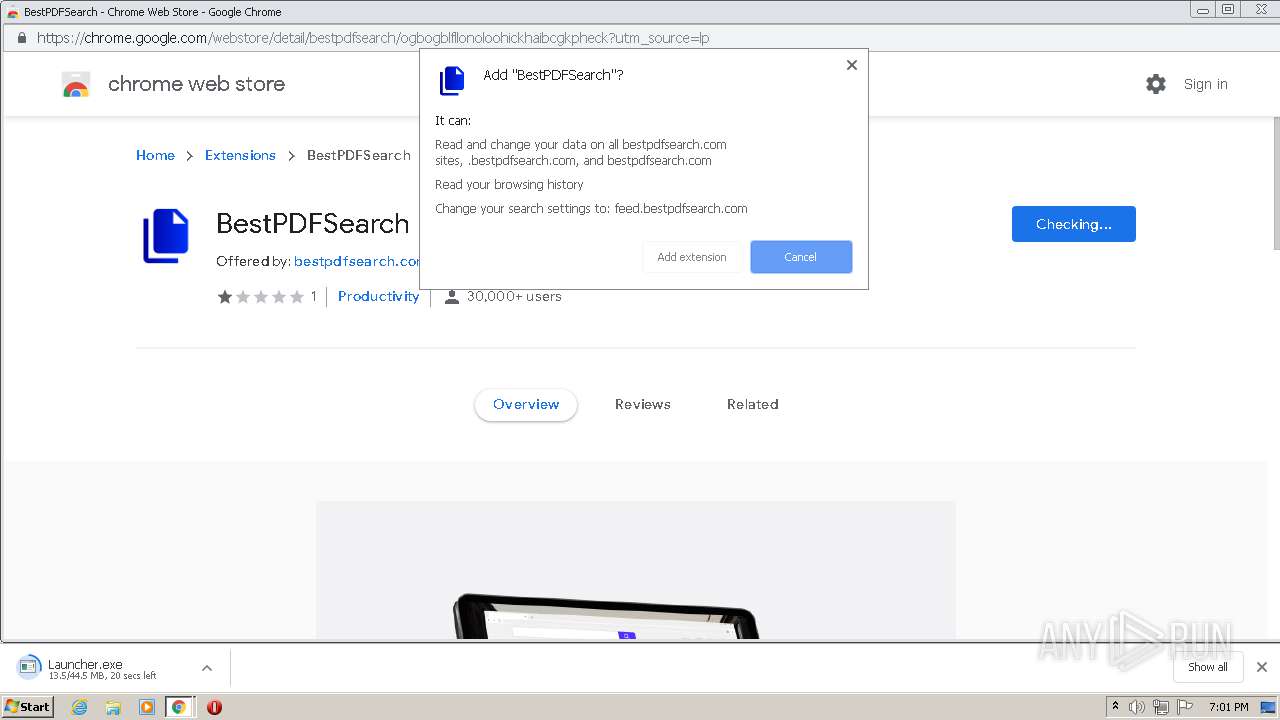
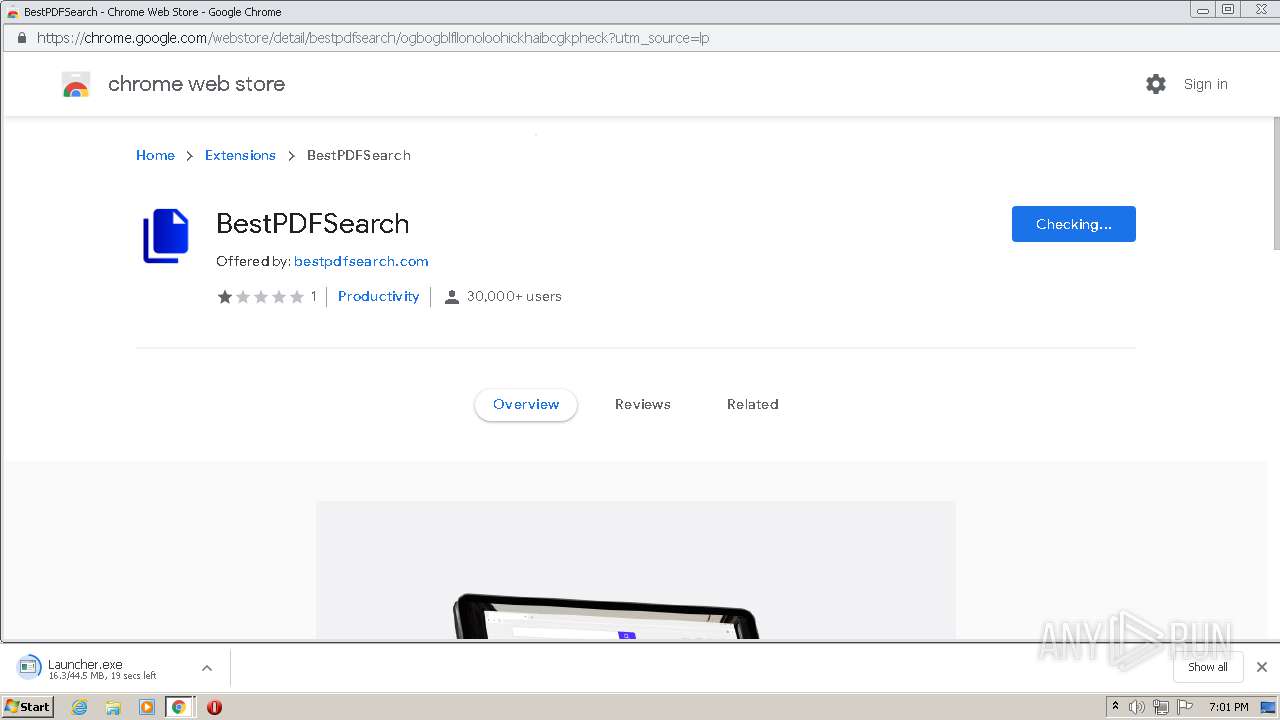
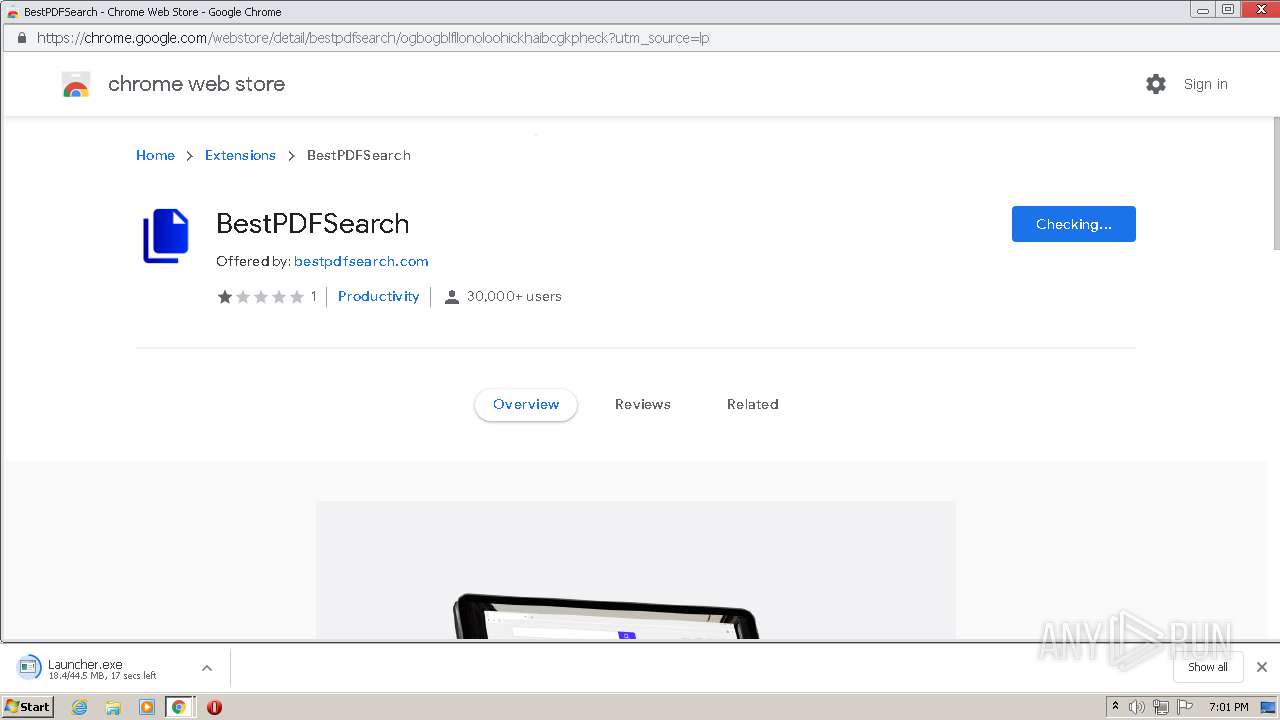
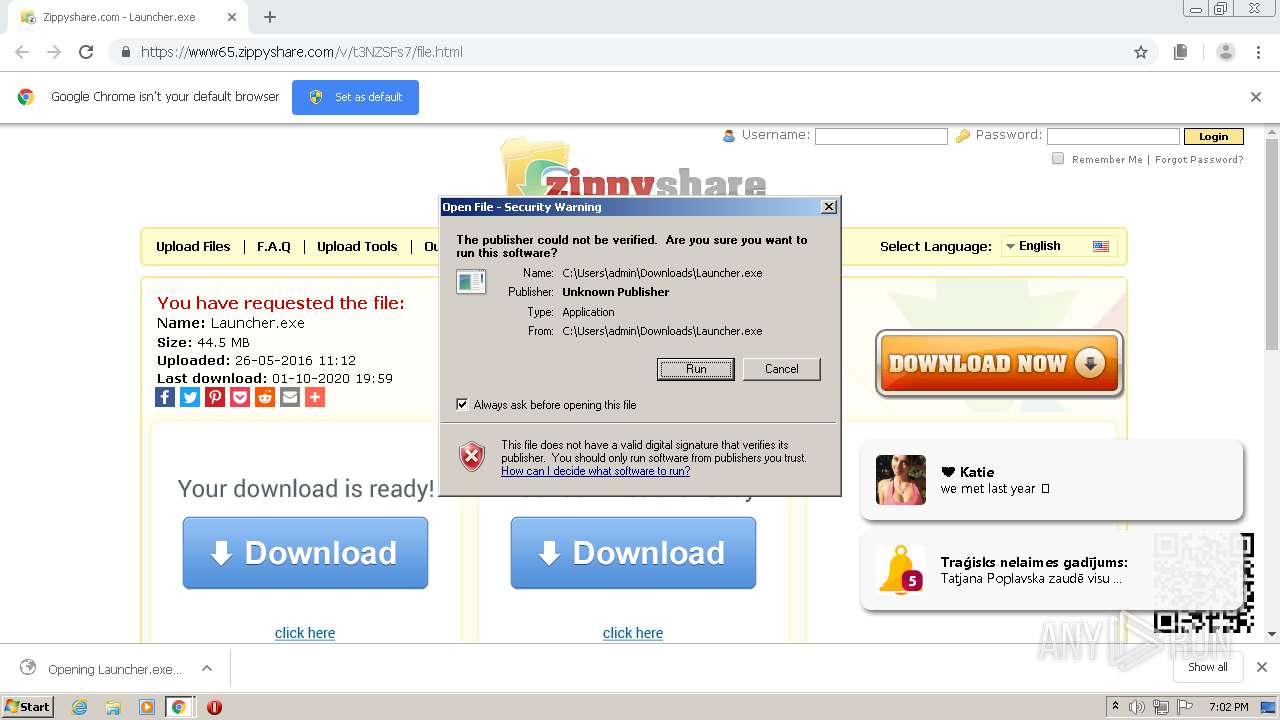
MALICIOUS
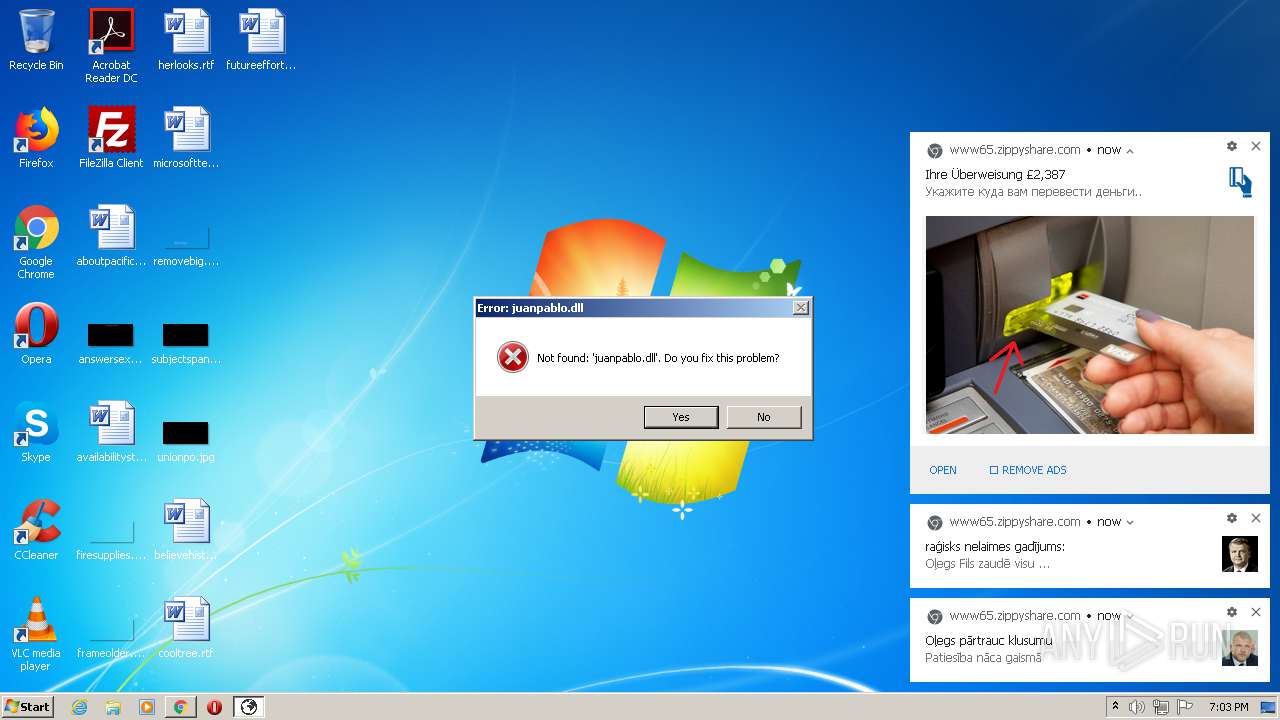
Application was dropped or rewritten from another process
- Launcher.exe (PID: 3356)
Changes the autorun value in the registry
- NVIDIA Update.exe (PID: 2776)
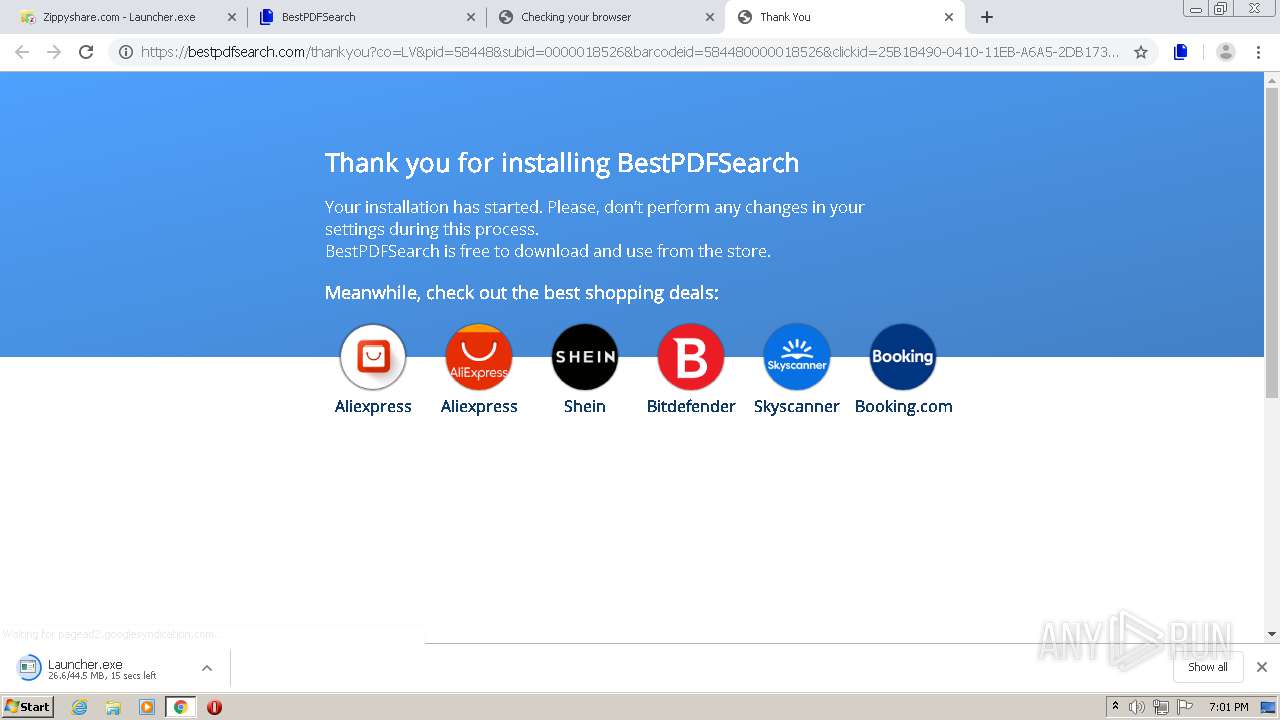
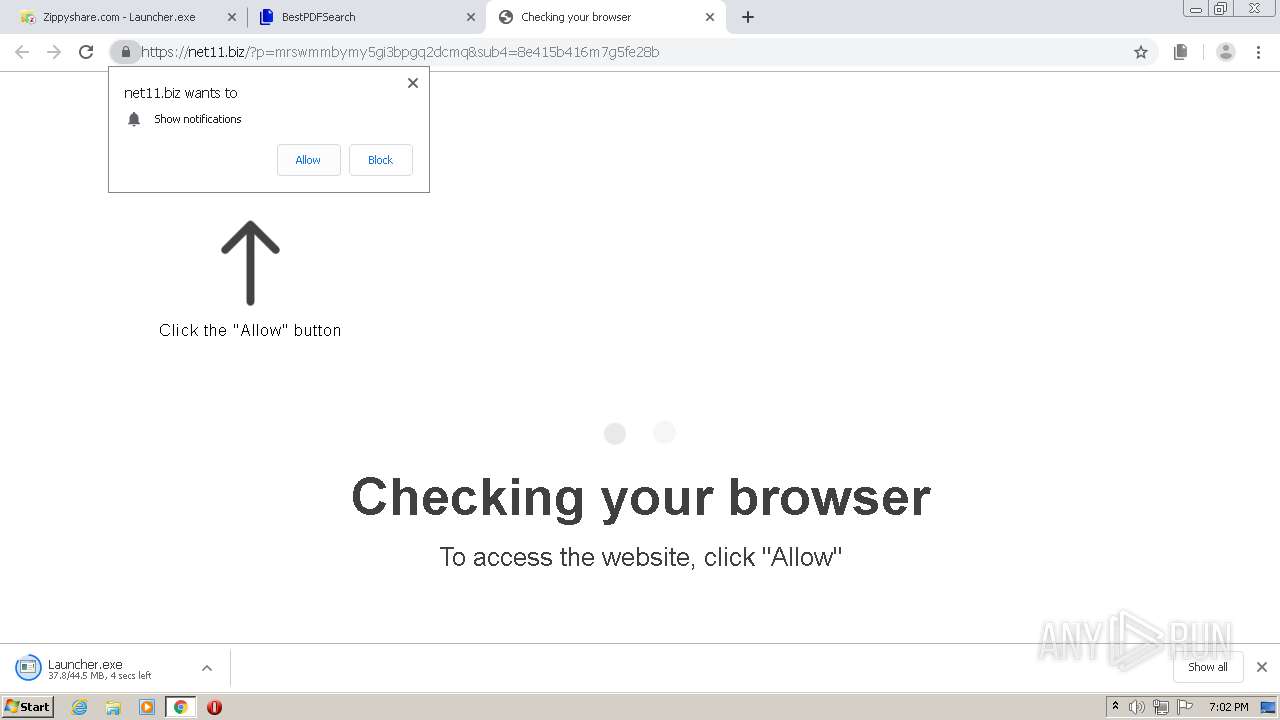
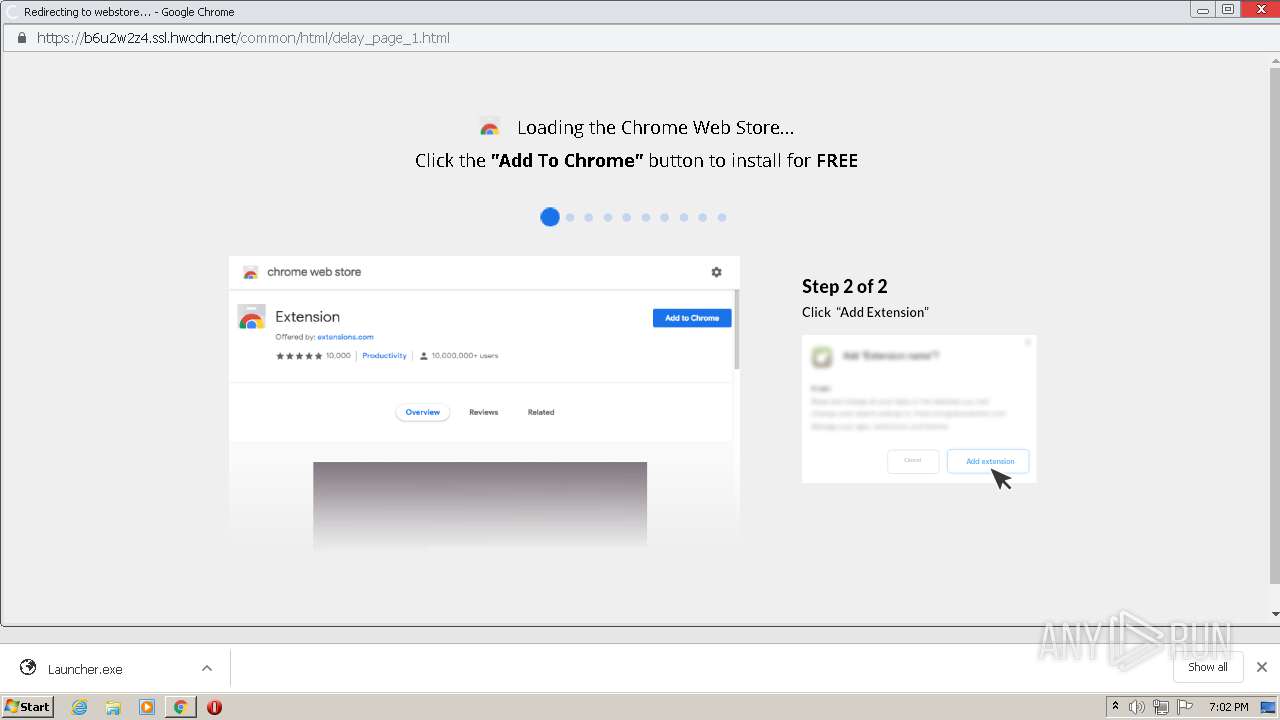
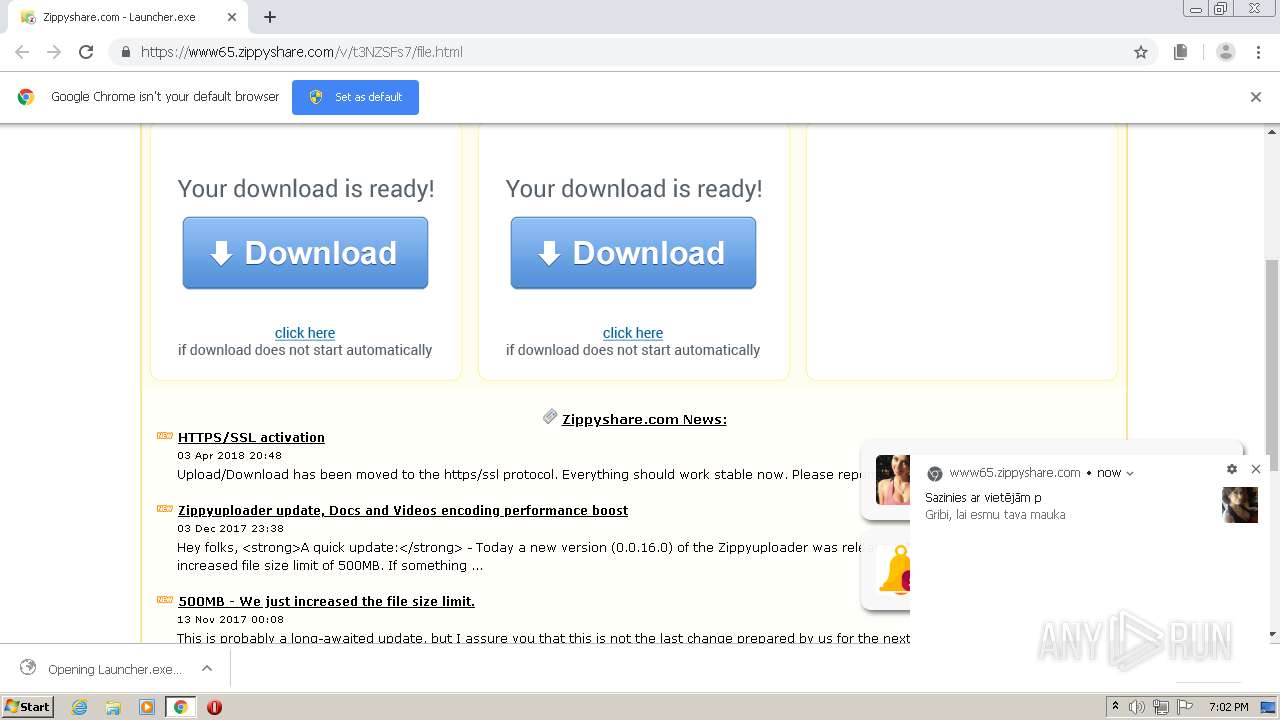
SUSPICIOUS
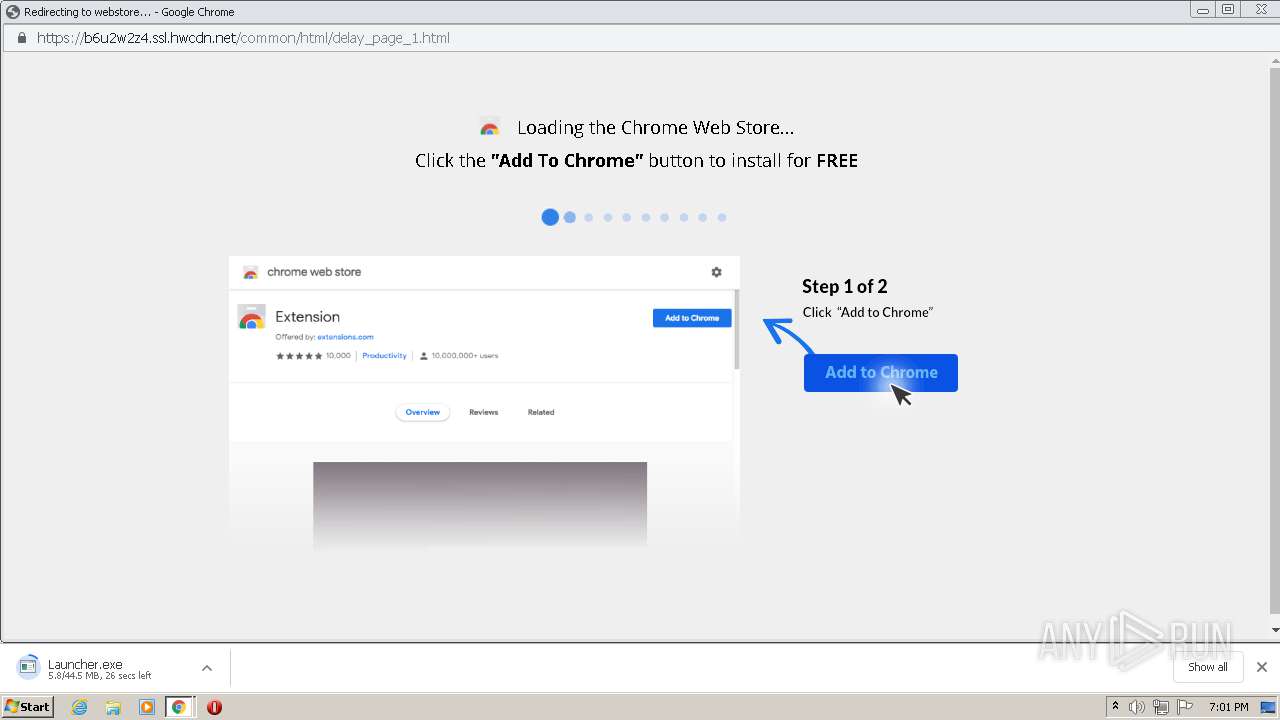
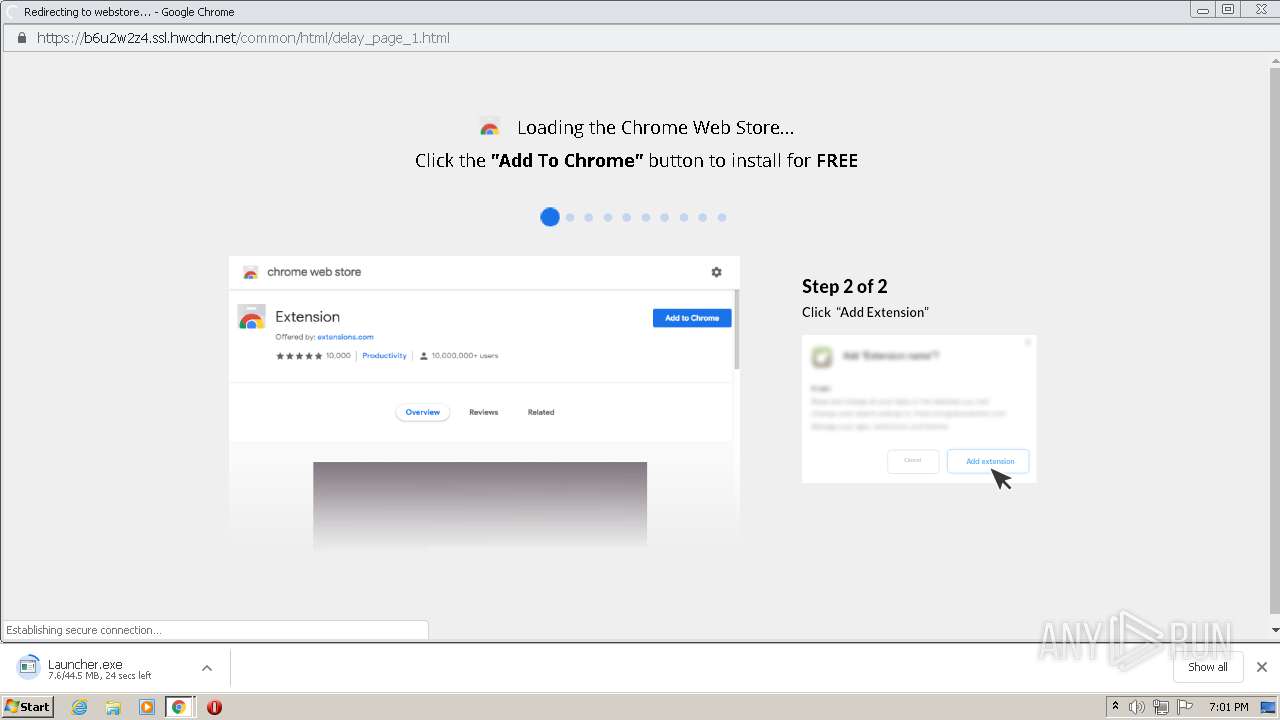
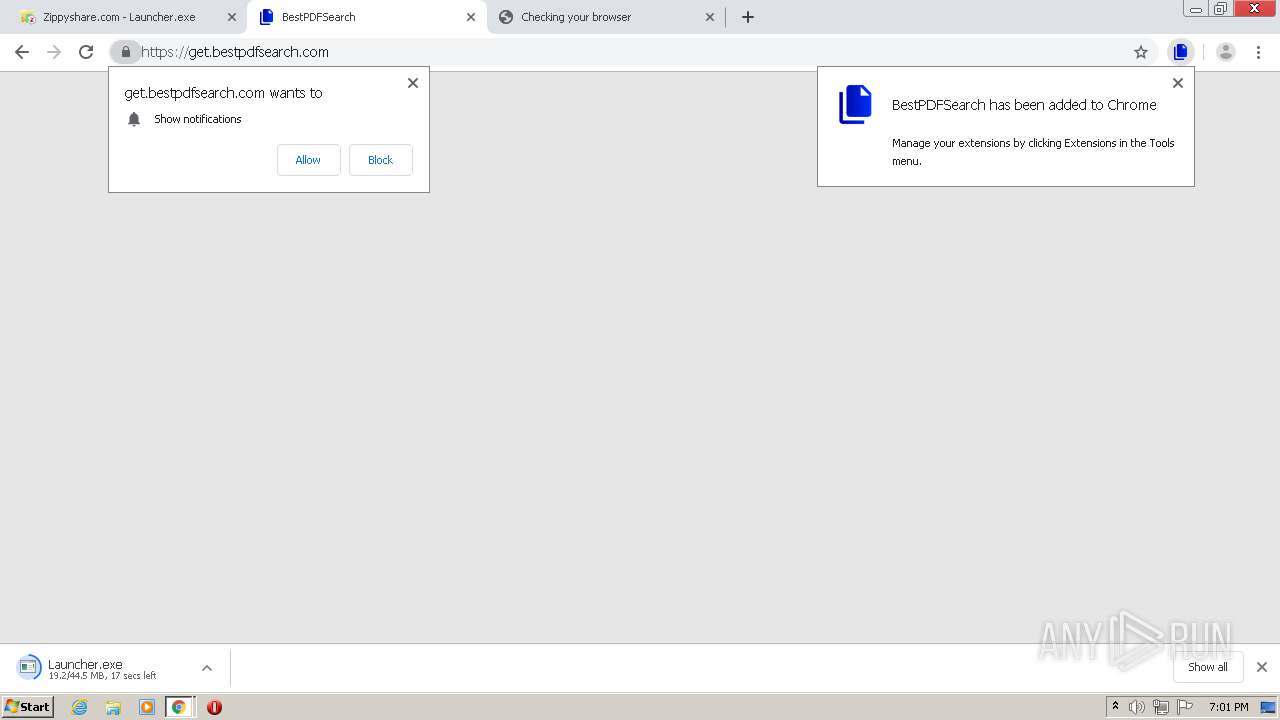
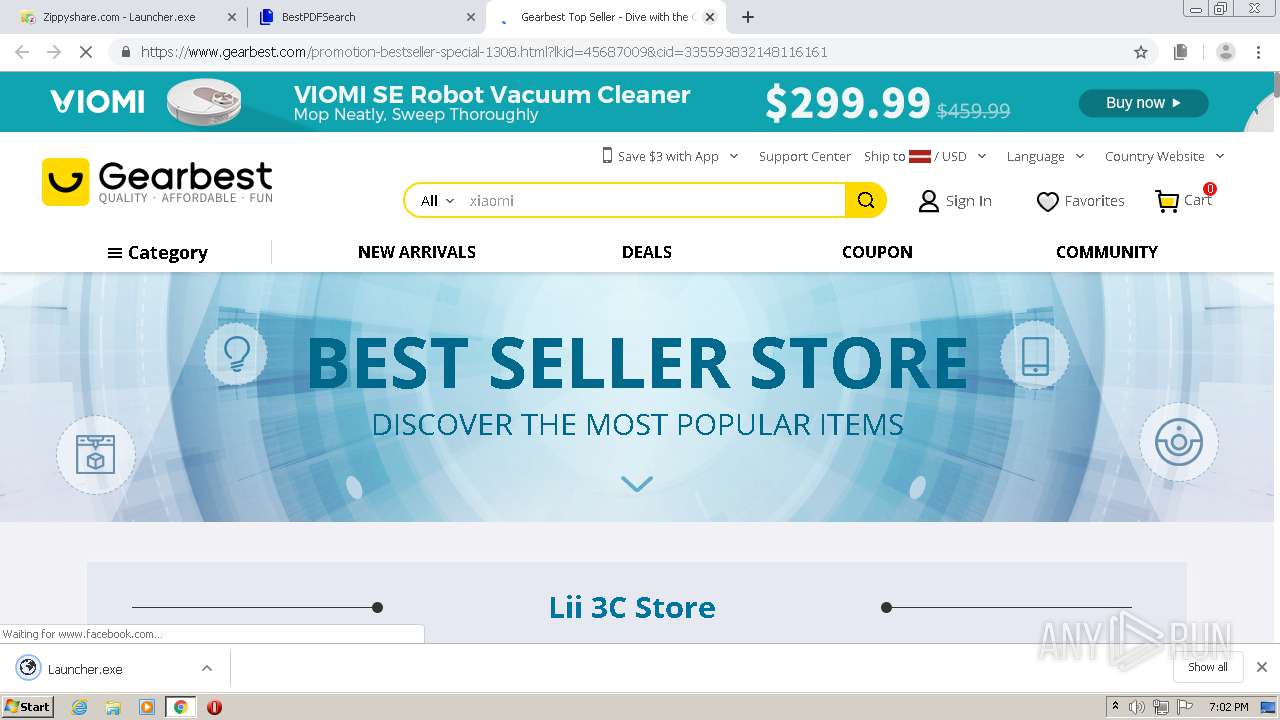
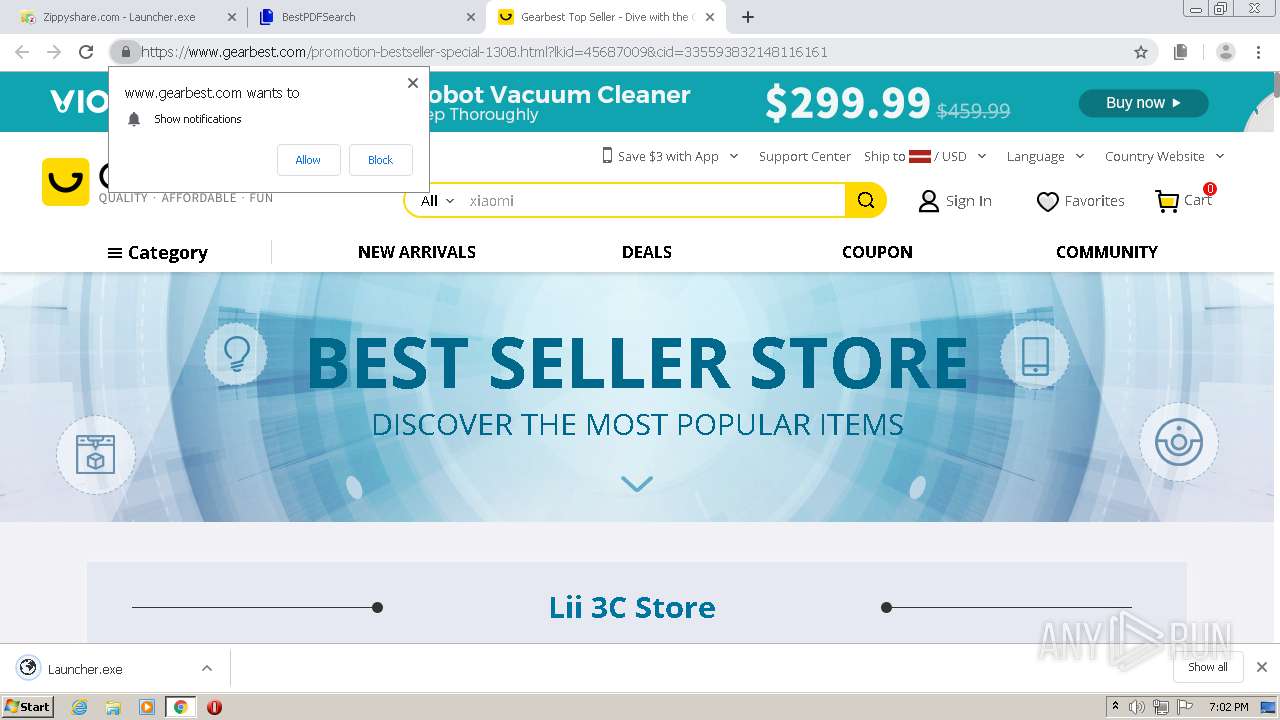
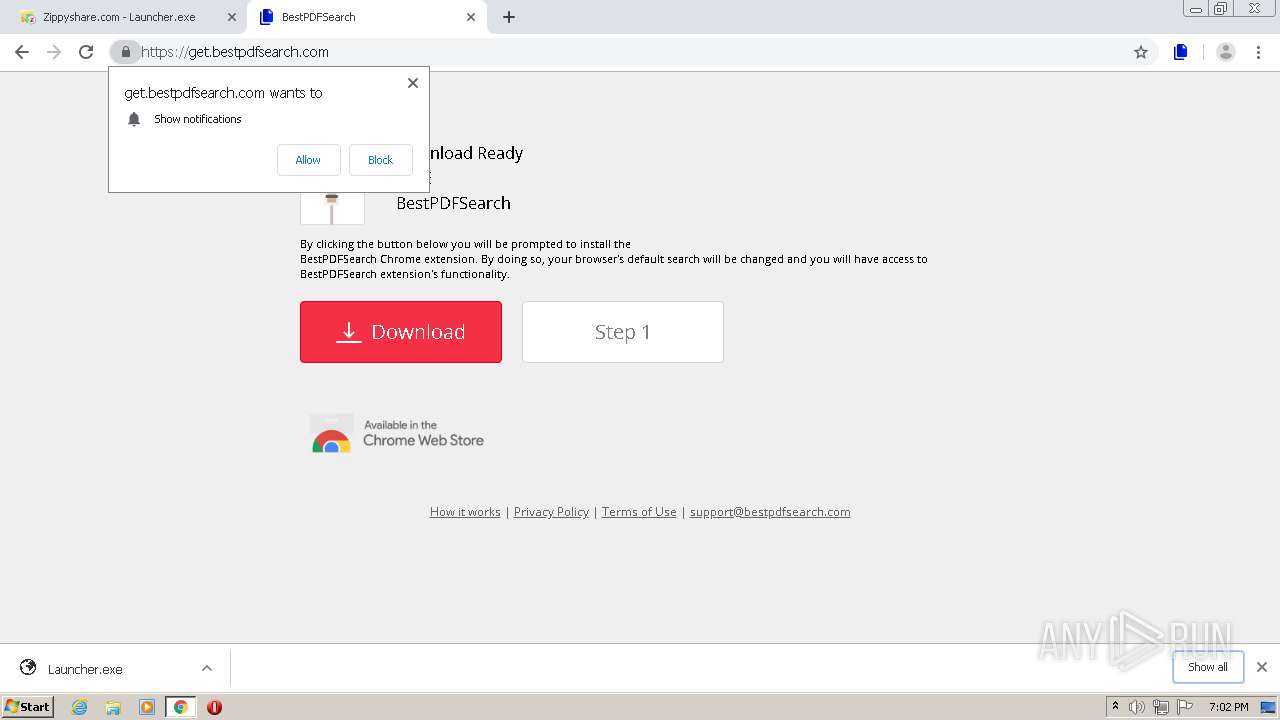
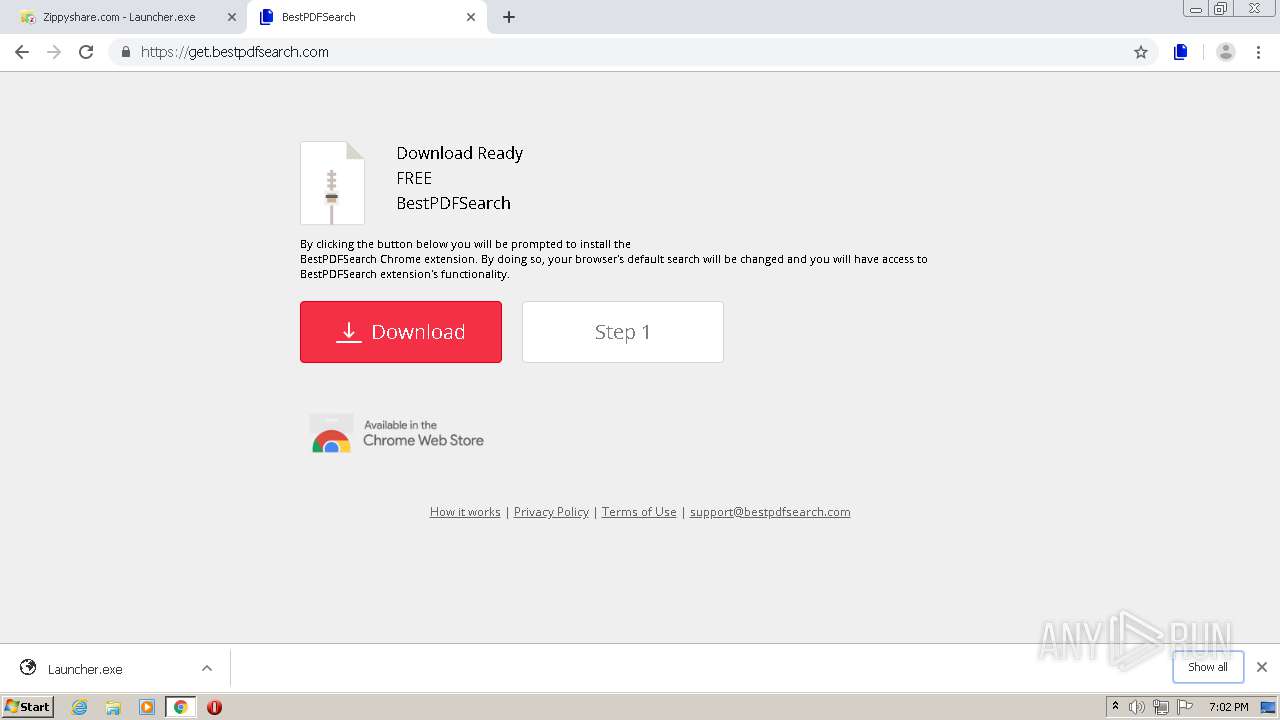
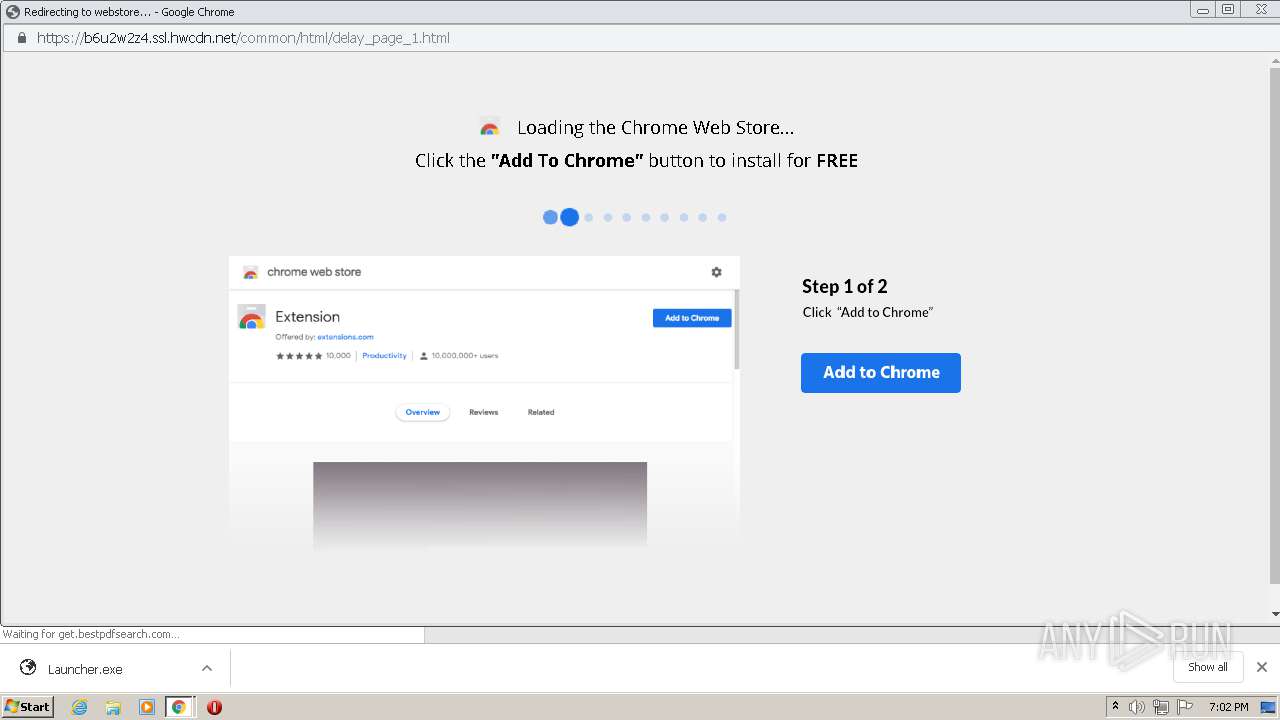
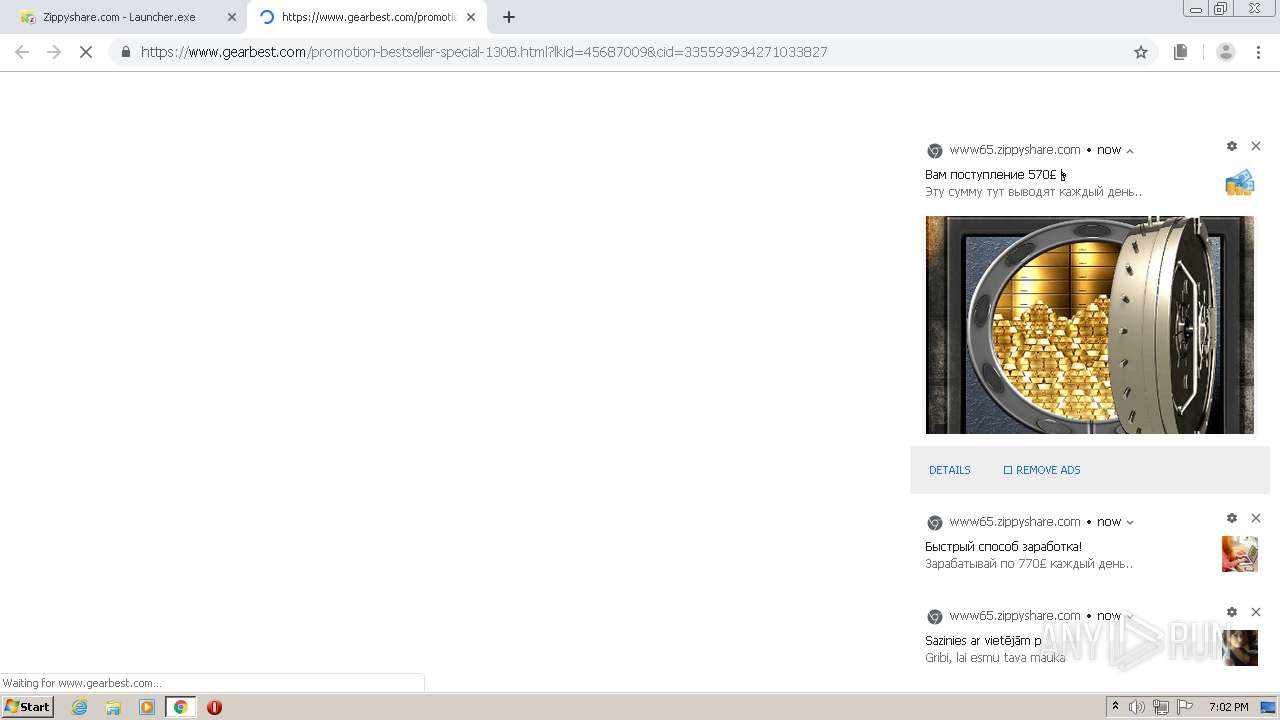
Executable content was dropped or overwritten
- chrome.exe (PID: 2572)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2572)
Creates files in the user directory
- Launcher.exe (PID: 3356)
Reads internet explorer settings
- NVIDIA Update.exe (PID: 2776)
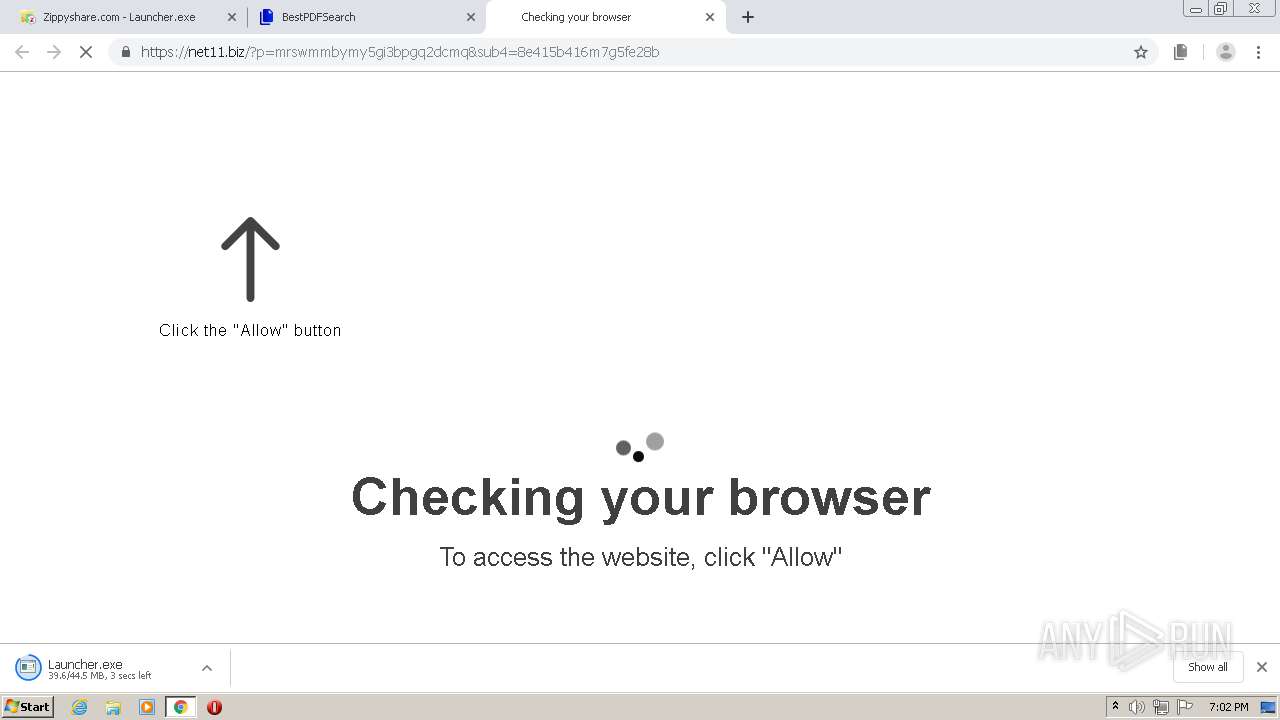
INFO
Reads the hosts file
- chrome.exe (PID: 2572)
- chrome.exe (PID: 2260)
Reads Internet Cache Settings
- chrome.exe (PID: 2572)
Creates files in the user directory
- chrome.exe (PID: 2572)
Application launched itself
- chrome.exe (PID: 2572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
109
Monitored processes
72
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,1251562272687877319,9907264324115891354,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3568270031633012968 --renderer-client-id=58 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,1251562272687877319,9907264324115891354,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3974355722064143571 --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=944,1251562272687877319,9907264324115891354,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1979226788354742901 --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,1251562272687877319,9907264324115891354,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6870324132605853702 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2420 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,1251562272687877319,9907264324115891354,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7399352934027329998 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2368 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,1251562272687877319,9907264324115891354,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4908652190427789844 --mojo-platform-channel-handle=4268 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,1251562272687877319,9907264324115891354,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2484201440712224211 --mojo-platform-channel-handle=4672 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,1251562272687877319,9907264324115891354,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3774340997258524525 --renderer-client-id=55 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,1251562272687877319,9907264324115891354,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10429074280737783299 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 629
Read events
1 402
Write events
222
Delete events
5
Modification events
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2572-13246048861206500 |
Value: 259 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
356
Text files
236
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F76195D-A0C.pma | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b2042e77-bd94-4067-af8d-351b0036261c.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF1aad0a.TMP | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1aacac.TMP | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1aaceb.TMP | text | |
MD5:— | SHA256:— | |||
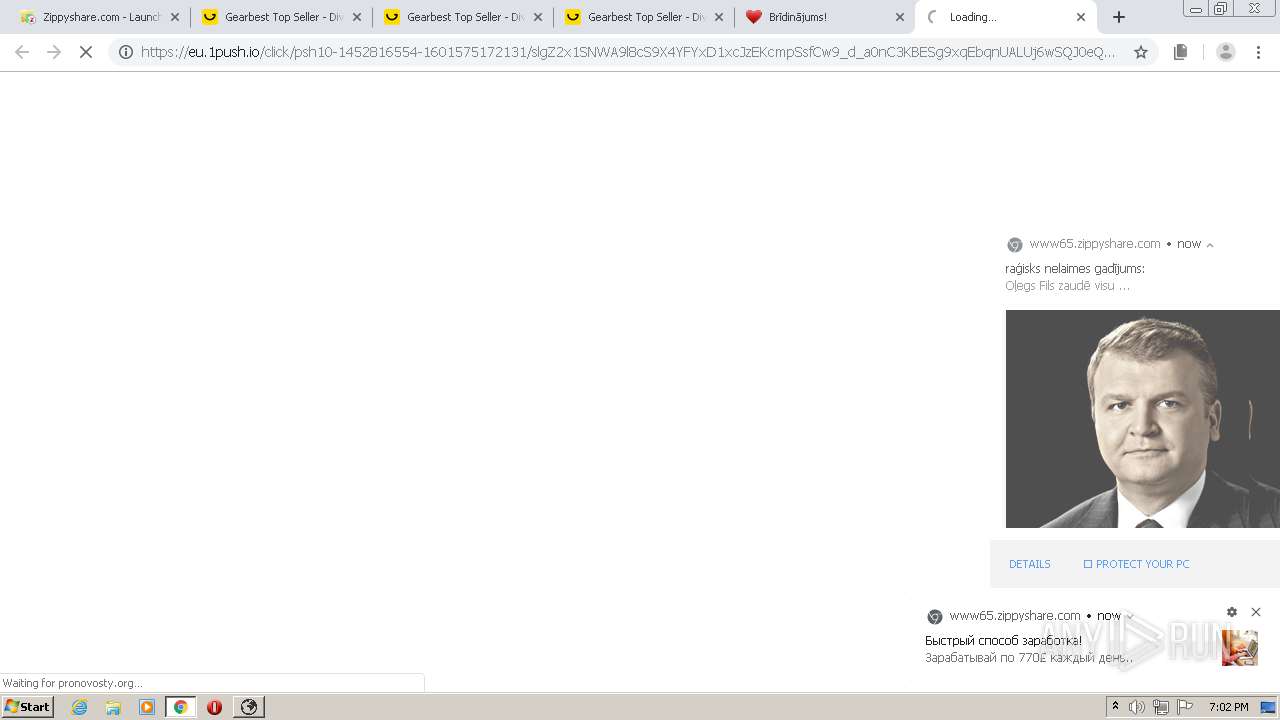
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
220
DNS requests
139
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
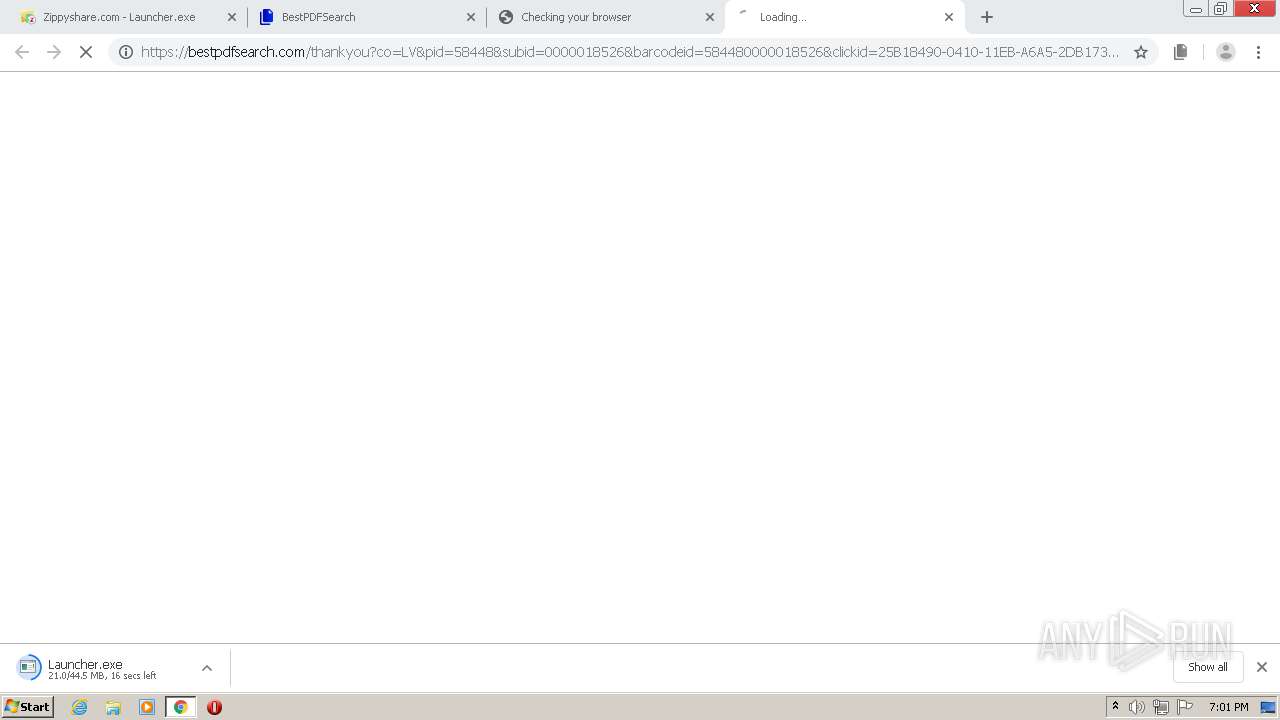
2260 | chrome.exe | GET | 200 | 34.96.99.173:80 | http://imptrk.siteplug.com/impTrk.php?enk1=ec5127b99adee07834649de37a61155840cfe61077165c2ebc43e92ae5dff47fd85ae3c949af9fae14a4fbe71a3cbaf945c886fb5f7184fc6845bb452e760f1e4212c2ca210f16d5d996f34ca7d3c4a40ce3e92c0ff59c3d0a8c9e79d0b197e6&enk2=d646714913aba435ffd0f01f410b174c22bd07ffdfa5272f1a21a45f20ded13b63b139c4f5789c88596260c3c32a5768b429c7b666ad8ddb824842ffccfc48f7703d419ee8a36c4234f52d22a08f9fd01e841f6665ef916a65362d5600b74c01829a5eedec2fb8bc1ac3d548cee924395054acb0dfab4b9ee62af310affea744ecbb0d617a0a20634689915f106675dc7deeb3827e63b1bfdcec19b4a434f1889cc5b9cb68379767&ccd=lv&stc=9089e074-bcf1-11e0-ba9c-0022195874fe&cin=riga&mcd=0&cic=141001 | US | — | — | suspicious |
2260 | chrome.exe | GET | 200 | 34.96.99.173:80 | http://imptrk.siteplug.com/impTrk.php?enk1=ec5127b99adee07834649de37a61155840cfe61077165c2ebc43e92ae5dff47fd85ae3c949af9faec11a4539c265514945c886fb5f7184fc6845bb452e760f1e4212c2ca210f16d5d996f34ca7d3c4a40ce3e92c0ff59c3d4c13c1e79bc2d95b&enk2=d646714913aba435ffd0f01f410b174c22bd07ffdfa5272fc27bb95ba7e6b3f8919e674a8f6c928acc96ee95bad0ae9d25ad0337d55111106a65755993fbc343c723f4b7d660821c85156842e7c30ee1ca98c3df73d6d8cfb83864ae53adcdfd057746f160f6e812ae563f23408093183a269e0652f4f163c01721823110111d2be4c4205ec1da4fecaf87ccf061d22f2ab4ca83ba0e09e44a92006370d45768&ccd=lv&stc=9089e074-bcf1-11e0-ba9c-0022195874fe&cin=riga&mcd=0&cic=141001 | US | — | — | suspicious |
2260 | chrome.exe | GET | 200 | 34.96.99.173:80 | http://imptrk.siteplug.com/impTrk.php?enk1=ec5127b99adee07834649de37a61155840cfe61077165c2ebc43e92ae5dff47fd85ae3c949af9faed4957f757577a62345c886fb5f7184fc6845bb452e760f1e4212c2ca210f16d5d996f34ca7d3c4a40ce3e92c0ff59c3d20d6570d2b0d8a89&enk2=d646714913aba435ffd0f01f410b174c22bd07ffdfa5272f8d3eb742ecb02c66b41c4c05b86c2a3151424cbbfda1f0c85a44dd661a63d63de0bff2601b0861cc55b3d63bd2211777d7fd8a8d39301362a229f2f05cd50d7563e8f6f87dcf6de923bf431246b18d3534e1abc645166b81e307c3d28962303a45328cf5d85b75c7700e2b1810fa99fef0cf57a0b46eef52a4f3d16ef5dec76cfdd71b01a9e78644108d314d4504e39d&ccd=lv&stc=9089e074-bcf1-11e0-ba9c-0022195874fe&cin=riga&mcd=0&cic=141001 | US | — | — | suspicious |
2260 | chrome.exe | GET | 200 | 34.96.99.173:80 | http://imptrk.siteplug.com/impTrk.php?enk1=ec5127b99adee07834649de37a61155840cfe61077165c2ebc43e92ae5dff47fd85ae3c949af9fae5ca71983e786eab145c886fb5f7184fc6845bb452e760f1e4212c2ca210f16d5d996f34ca7d3c4a40ce3e92c0ff59c3d2ffdc9b691e93bc8&enk2=d646714913aba435ffd0f01f410b174c22bd07ffdfa5272f4edda1a4d55ef99a3464f594299233172faa14c6680085ca2b0c0bc14718ff160f15b4507370c85b95f135d255a9be0e93e742354b94ad3827faf92084df15e23beb01dd331c2c3a2a8f43b8711ae784305b173db0ccc813ff9b4a473df2a191559444d78f43d01f5bd0fc9481b9597a94f46de014306c3de877e5af34a34cdd5b21dd26888ef1cf41ba2142e163f456&ccd=lv&stc=9089e074-bcf1-11e0-ba9c-0022195874fe&cin=riga&mcd=0&cic=141001 | US | — | — | suspicious |
2260 | chrome.exe | GET | 200 | 34.96.99.173:80 | http://imptrk.siteplug.com/impTrk.php?enk1=ec5127b99adee07834649de37a61155840cfe61077165c2ebc43e92ae5dff47fd85ae3c949af9faead8073df4406660445c886fb5f7184fc6845bb452e760f1e4212c2ca210f16d5d996f34ca7d3c4a40ce3e92c0ff59c3d8ae89be36fb3dbf0&enk2=d646714913aba435ffd0f01f410b174c22bd07ffdfa5272f9a19c5304b62595780db7bf4d586f008ba3e8d447e3c59465a44dd661a63d63de0bff2601b0861cc9c5f733b63fb698fd7fd8a8d39301362a229f2f05cd50d7563e8f6f87dcf6de923bf431246b18d3534e1abc645166b81e307c3d28962303a45328cf5d85b75c7700e2b1810fa99fef0cf57a0b46eef52a4f3d16ef5dec76ca653c4ac3dc9378d108d314d4504e39d&ccd=lv&stc=9089e074-bcf1-11e0-ba9c-0022195874fe&cin=riga&mcd=0&cic=141001 | US | — | — | suspicious |
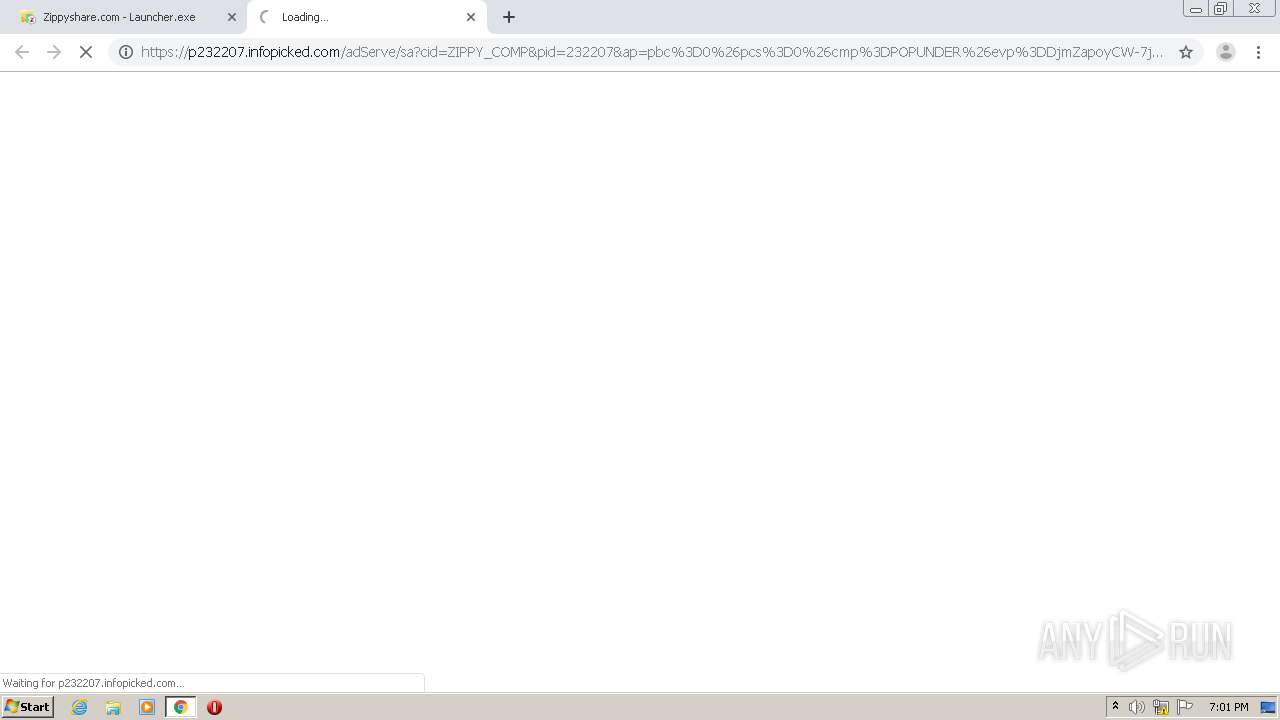
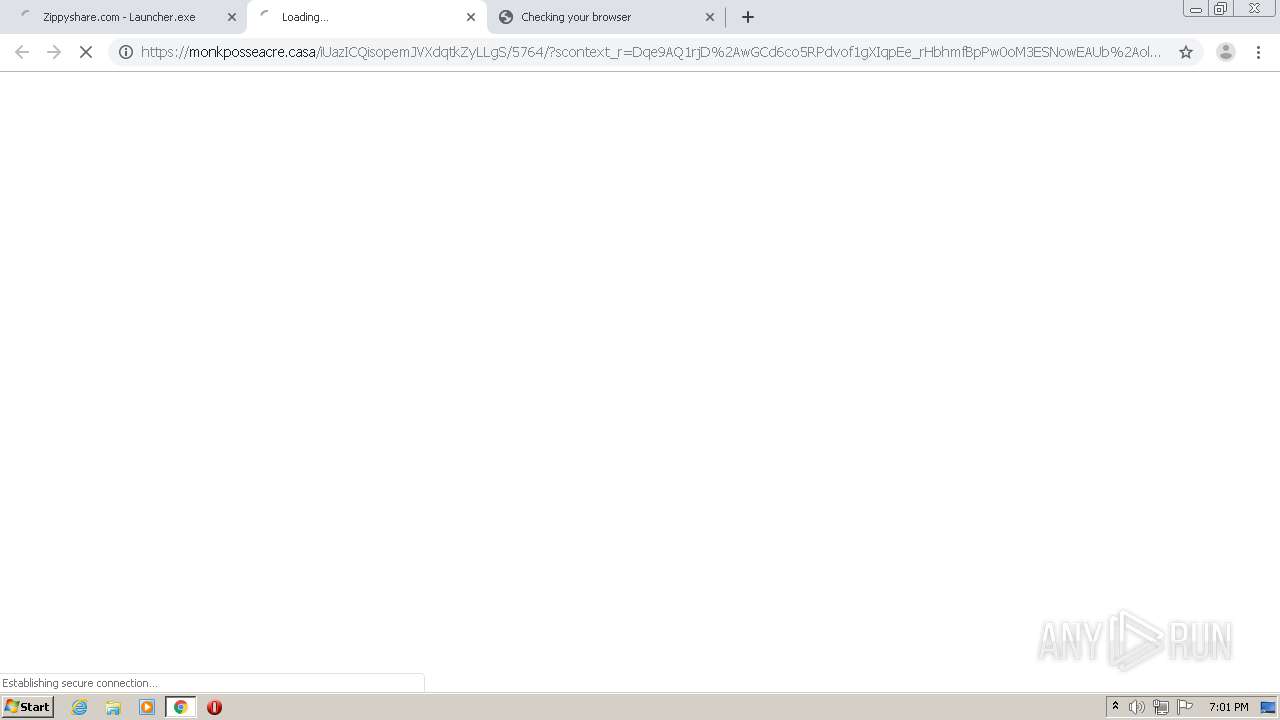
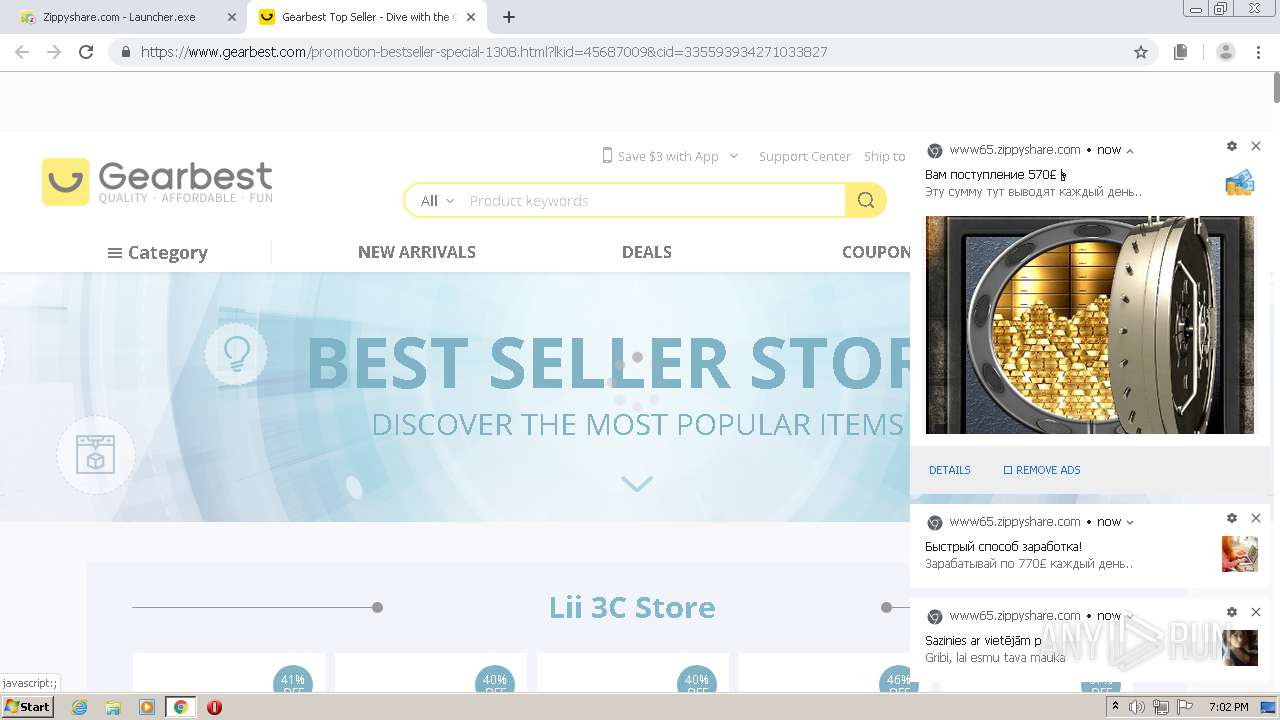
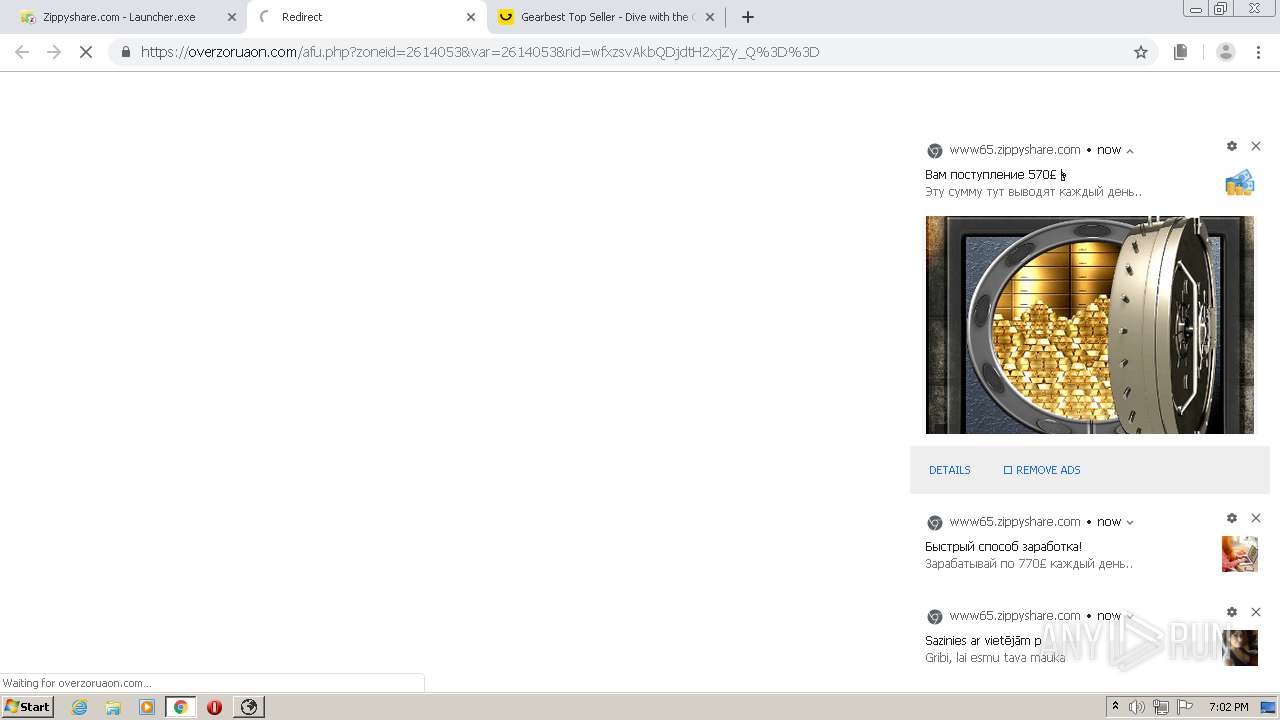
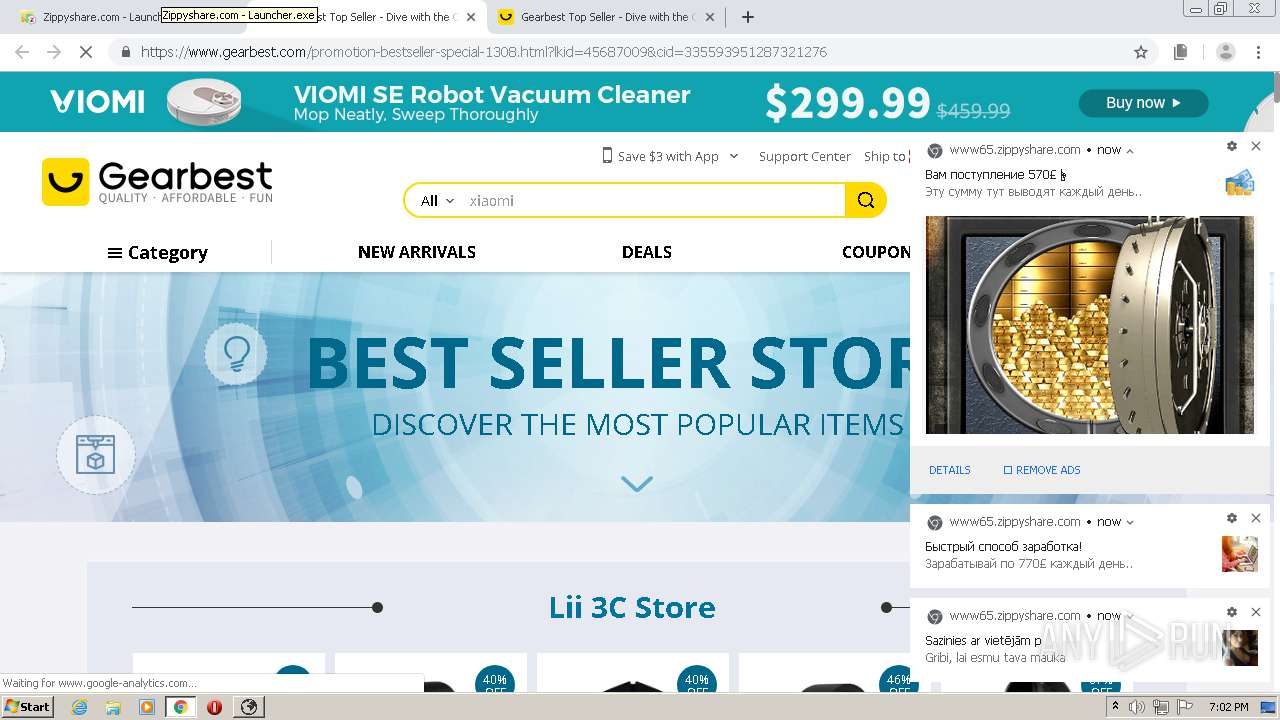
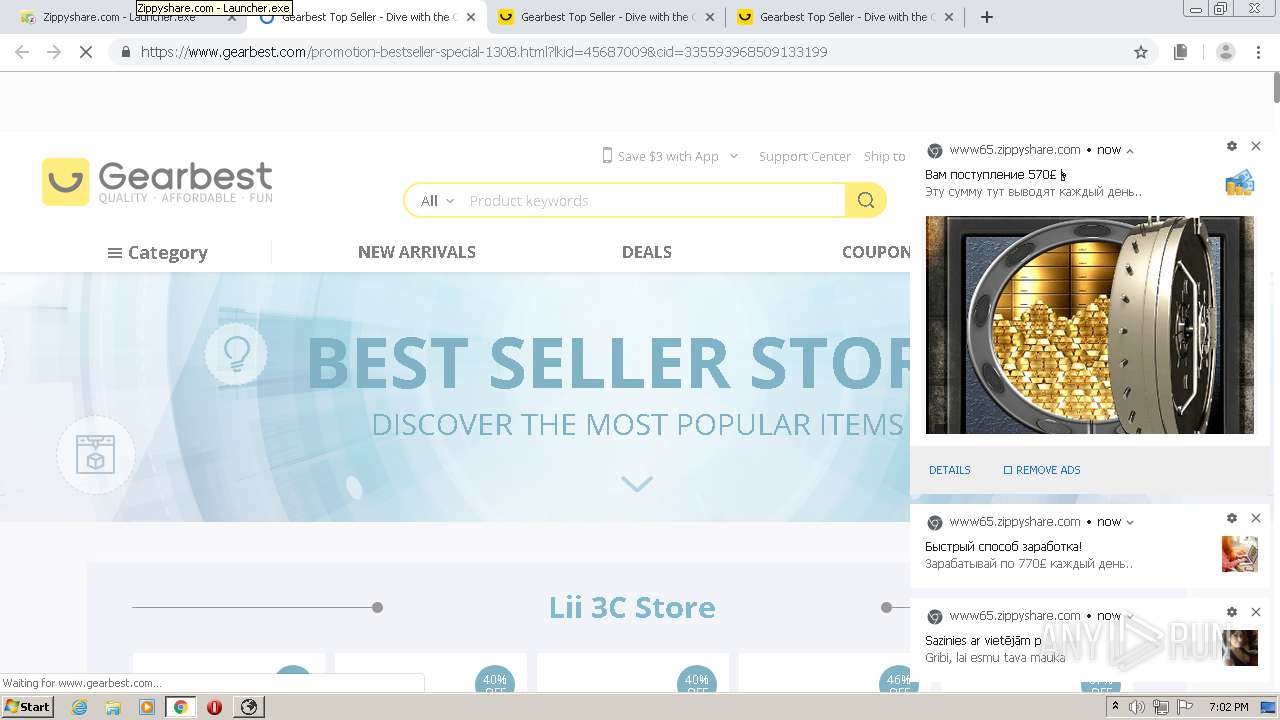
2260 | chrome.exe | GET | 302 | 173.192.101.24:80 | http://p232207.infopicked.com/adServe/adClick?ai=KpvjoDw_VlZL8W9hx5q4Y9f_Sx8NAjz1zcIbU6lmoz7loakgJ3FAzLwh3d6wzqMZNCqvlQLKIJwbKVmsWAbfE_jpFAkfeIvZZRyHh1YT9r9XUsYi9dmc9OAg_slvBKGmnluymHZt2_O6gZ1hp6CkQQk66YJSDK1fViq_0jkAZ7Xy7rwTL1F3TNtmHa-sXA6BXP6n_paJdUfYHBXOP_rLZQFXoLONZP203jyqlqOT0ltuwEC7dnUo2xBh-nBk7TUUA_ErvI1TLh9urSPk3OokR53iHZnBO9wPN2aRlCqoFtRg60HmHH2SS2DKxn059B3ZXnSKeHHS_4Xi6ie-_d9-HhtaaSBUh8HAf6gmL4f0BkOrPTnlZuKYCpPlenXhQ25Iy592p-a9_iJNSbrEf2nmJ-u6-dJOaNBnxWfBO_Pgkf9Lj9hxf0SJk34fQt6HtErsI8CjmB24NUgtgv-zBshMS3xOyvhjTCQzmp3zKspYVrnp-OGBQW3exAhKJncPyYXs8m-KbVlLlquPnISuWTEdRJx5L7KGCWRFUWNFyyPsNurVo64vPAXoOmaJ1nv1bZfR7Rnpwr15-joX4QgE4uJ9KxhZILtDpse8OSQb1_9zUHqaGfuACCumAyYNb-iWwdA0&ui=DjmZapoyCW-7j49PMlfT8AcsWc8-Vo_0IaIc3yOo5HLO-6Xqvz-KnWGsc4h6QmKzIMXhdXB-6dM&ap=cmp%3DBANNER%26evp%3DDjmZapoyCW-7j49PMlfT8AcsWc8-Vo_0p83UPqokcA6fjDPgmXGS9n0c3txgRlDR%26sjv%3D95.0%26ctid%3D0%26th%3D572%26tw%3D1280%26inco%3D0%26tip%3DZippyshare.com%2520-%2520Launcher.exe&referrer=https%253A%252F%252Fwww65.zippyshare.com%252Fv%252Ft3NZSFs7%252Ffile.html&popeye=bXg9MTMxJm15PTEwNiZjeD0xNDAmY3k9MTMyJnc9MTI4MCZoPTU2OSZjPTEmcz0xJnQ9NzQ1MjMmaT0wJm89LTYwJnNvX2ZiPS0xJnNvX2dvPS0xJnNvX2dwPS0xJnNvX3R3PS0xJnNwPTAwMDAwMDAwMDAxMDAwMDAwMDAwMDAwJm1tX21uPTkmbW1fYXM9MC4yOTkwMzE4MDcyMTk4MDk3NiZtbV9hZD0zOS44ODk1MTExMTQwMTcxNSZtbV9tdD0zNTU0LjAwMDAwMDAwMDEwMiZtbV9zYz01OSZtbV9zZGM9MjAmbmNycz00&olive=1 | US | — | — | suspicious |
2260 | chrome.exe | GET | 302 | 173.192.101.24:80 | http://p232207.infopicked.com/adServe/adClick?ai=KpvjoDw_VlZL8W9hx5q4Y9f_Sx8NAjz1zcIbU6lmoz7loakgJ3FAzLwh3d6wzqMZNCqvlQLKIJwbKVmsWAbfE_jpFAkfeIvZZRyHh1YT9r9XUsYi9dmc9LmGXT92KMKrRyRAL7lI8yZ0wVccNi0OPlJUB4cCMpzhDdfKilmZiov-29LJmEHdmZ7b6Qy9a1mHSF-z0hVrtQbMCnJTdRtOXJjfh-QPg_VJlZVWnx1WqHRHvXQitwK2iGqZXDZsz_u03ZCtkdI9tx2Wu3TrgOl_p-vaI8tzj08R3Wu1THSntWiNgG3rNadZFVh6v1bXdPNRpyjC6Ed4TyPznEhR0BMGwdh6sItLiqLtHV9NLf16czz2UkK4809QJM77peq_P4qdXdx7D-8Tsr6xyqlJB7ZxEp-qFZn5gpnPqtE9sbJicJzkAjQn1lMdyLfUif8W1d8e3qJc1ShqKPF8U_pI8bMSKMbaeKnrDeGMw0G6uuZyUxrzVVlMvpZOzxY7hA_5WLvNVxyS7a71gJUA0kMx9nCQzxusqsnFf0HtebN_6JwPMLK5kygdpabC421p2h3hBQbnXQPnuWlBamafsemDjSNYZRxMAa3TZ9E0d2FuuG4Q1Maog1-YabtN32IXUvDNPgiE&ui=DjmZapoyCW-7j49PMlfT8AcsWc8-Vo_0IaIc3yOo5HLO-6Xqvz-KnWnUpGdmN0cqIMXhdXB-6dM&ap=cmp%3DBANNER%26evp%3DDjmZapoyCW-7j49PMlfT8AcsWc8-Vo_0p83UPqokcA6fjDPgmXGS9q4SUzTnUcS8%26sjv%3D95.0%26ctid%3D0%26th%3D572%26tw%3D1280%26inco%3D0%26tip%3DZippyshare.com%2520-%2520Launcher.exe&referrer=https%253A%252F%252Fwww65.zippyshare.com%252Fv%252Ft3NZSFs7%252Ffile.html&popeye=bXg9MjAwJm15PTE1OSZjeD0xMzYmY3k9MTA2Jnc9MTI4MCZoPTU2OSZjPTEmcz0xJnQ9Nzg4MTkmaT0wJm89LTYwJnNvX2ZiPS0xJnNvX2dvPS0xJnNvX2dwPS0xJnNvX3R3PS0xJnNwPTAwMDAwMDAwMDAxMDAwMDAwMDAwMDAwJm1tX21uPTkmbW1fYXM9MC4yOTkwMzE4MDcyMTk4MDk3NiZtbV9hZD0zOS44ODk1MTExMTQwMTcxNSZtbV9tdD0zNTU0LjAwMDAwMDAwMDEwMiZtbV9zYz01OSZtbV9zZGM9MjAmbmNycz00&olive=1 | US | — | — | suspicious |
2260 | chrome.exe | GET | 302 | 173.192.101.24:80 | http://p232207.infopicked.com/adServe/adClick?ai=KpvjoDw_VlZL8W9hx5q4Y9f_Sx8NAjz1zcIbU6lmoz7loakgJ3FAzLwh3d6wzqMZNCqvlQLKIJwbKVmsWAbfE_jpFAkfeIvZZRyHh1YT9r9XUsYi9dmc9LmGXT92KMKrRyRAL7lI8yZ0wVccNi0OPlJUB4cCMpzhDdfKilmZiov-29LJmEHdmZ7b6Qy9a1mHSF-z0hVrtQbMCnJTdRtOXJjfh-QPg_VJlZVWnx1WqHRHvXQitwK2iGqZXDZsz_u03ZCtkdI9tx2Wu3TrgOl_p-vaI8tzj08R3Wu1THSntWiNgG3rNadZFVh6v1bXdPNRpyjC6Ed4TyPznEhR0BMGwdh6sItLiqLtHV9NLf16czz2UkK4809QJM77peq_P4qdXdx7D-8Tsr6xyqlJB7ZxEp-qFZn5gpnPqtE9sbJicJzkAjQn1lMdyLfUif8W1d8e3qJc1ShqKPF8U_pI8bMSKMbaeKnrDeGMw0G6uuZyUxrzVVlMvpZOzxY7hA_5WLvNVxyS7a71gJUA0kMx9nCQzxusqsnFf0HtebN_6JwPMLK5kygdpabC421p2h3hBQbnXQPnuWlBamafsemDjSNYZRxMAa3TZ9E0d2FuuG4Q1Maog1-YabtN32IXUvDNPgiE&ui=DjmZapoyCW-7j49PMlfT8AcsWc8-Vo_0IaIc3yOo5HLO-6Xqvz-KnWnUpGdmN0cqIMXhdXB-6dM&ap=cmp%3DBANNER%26evp%3DDjmZapoyCW-7j49PMlfT8AcsWc8-Vo_0p83UPqokcA6fjDPgmXGS9q4SUzTnUcS8%26sjv%3D95.0%26ctid%3D0%26th%3D572%26tw%3D1280%26inco%3D0%26tip%3DZippyshare.com%2520-%2520Launcher.exe&referrer=https%253A%252F%252Fwww65.zippyshare.com%252Fv%252Ft3NZSFs7%252Ffile.html&popeye=bXg9MjAwJm15PTE1OSZjeD0xNDAmY3k9MjEwJnc9MTI4MCZoPTU2OSZjPTEmcz0xJnQ9ODI2MDEmaT0wJm89LTYwJnNvX2ZiPS0xJnNvX2dvPS0xJnNvX2dwPS0xJnNvX3R3PS0xJnNwPTAwMDAwMDAwMDAxMDAwMDAwMDAwMDAwJm1tX21uPTEwJm1tX2FzPTAuMjgyMzQ3NDgyODA2OTQ5NzcmbW1fYWQ9MzguNjg0MTAwOTY5MjIzNzM1Jm1tX210PTM3OTkmbW1fc2M9NjMmbW1fc2RjPTIxJm5jcnM9NA%3D%3D&olive=1 | US | — | — | suspicious |
2260 | chrome.exe | GET | 304 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2260 | chrome.exe | 13.226.156.191:443 | ds88pc0kw6cvc.cloudfront.net | — | US | unknown |
2260 | chrome.exe | 173.192.101.24:443 | p232207.clksite.com | SoftLayer Technologies Inc. | US | suspicious |
2260 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 46.166.139.196:443 | www65.zippyshare.com | NForce Entertainment B.V. | NL | unknown |
2260 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 13.226.156.53:443 | d10lumateci472.cloudfront.net | — | US | unknown |
2260 | chrome.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
2260 | chrome.exe | 172.217.23.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 35.190.68.123:443 | www.maxonclick.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 172.255.6.128:443 | mooantink.com | — | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www65.zippyshare.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ds88pc0kw6cvc.cloudfront.net |
| whitelisted |
d10lumateci472.cloudfront.net |
| whitelisted |
p232207.clksite.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
www.maxonclick.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
mooantink.com |
| suspicious |
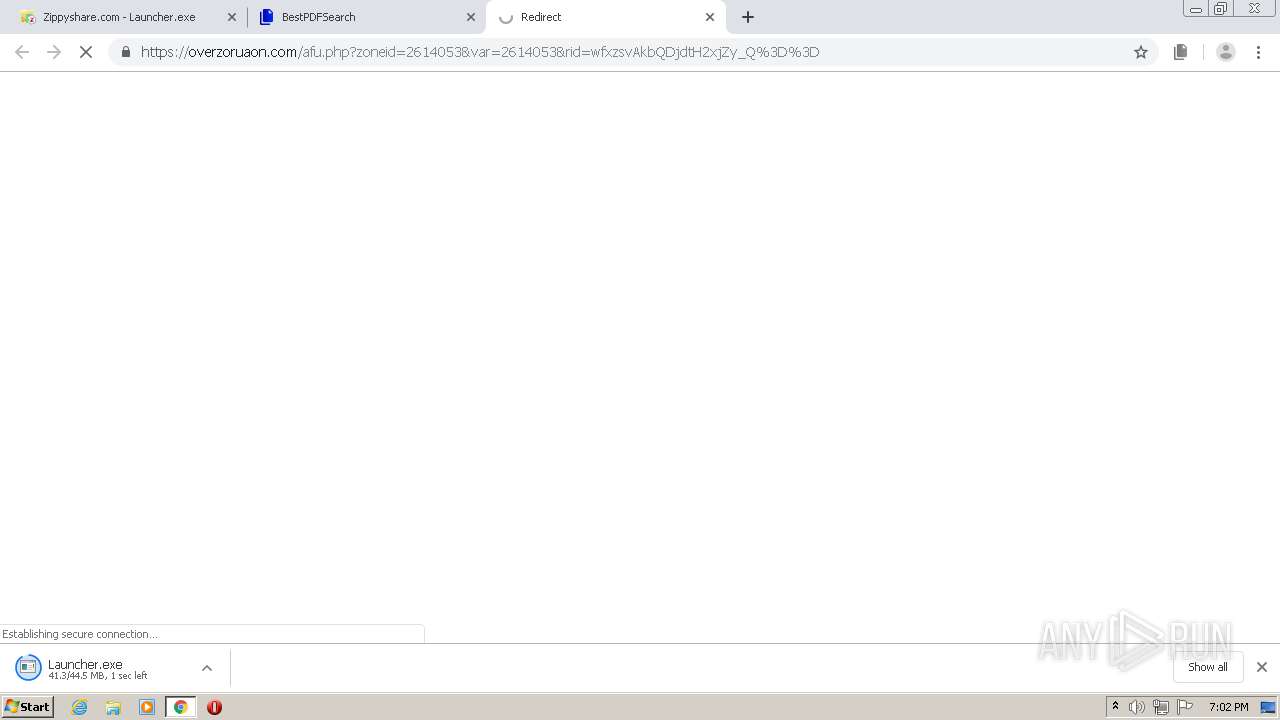
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |