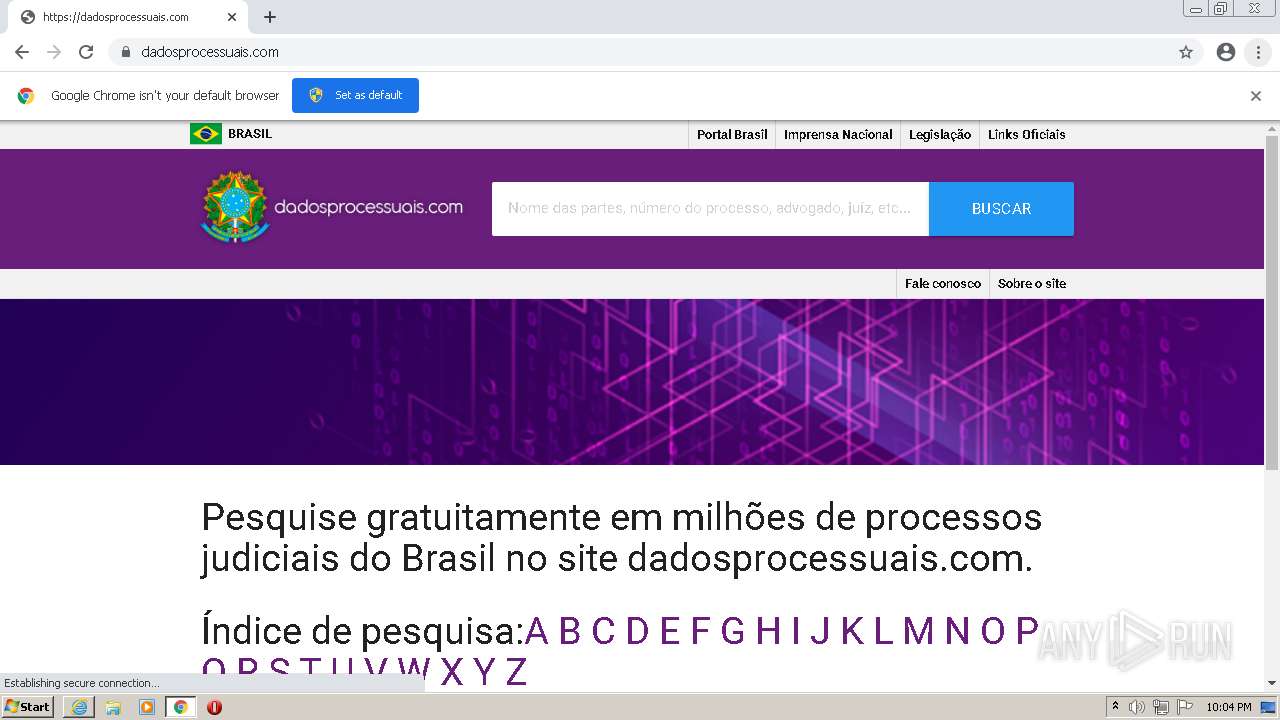
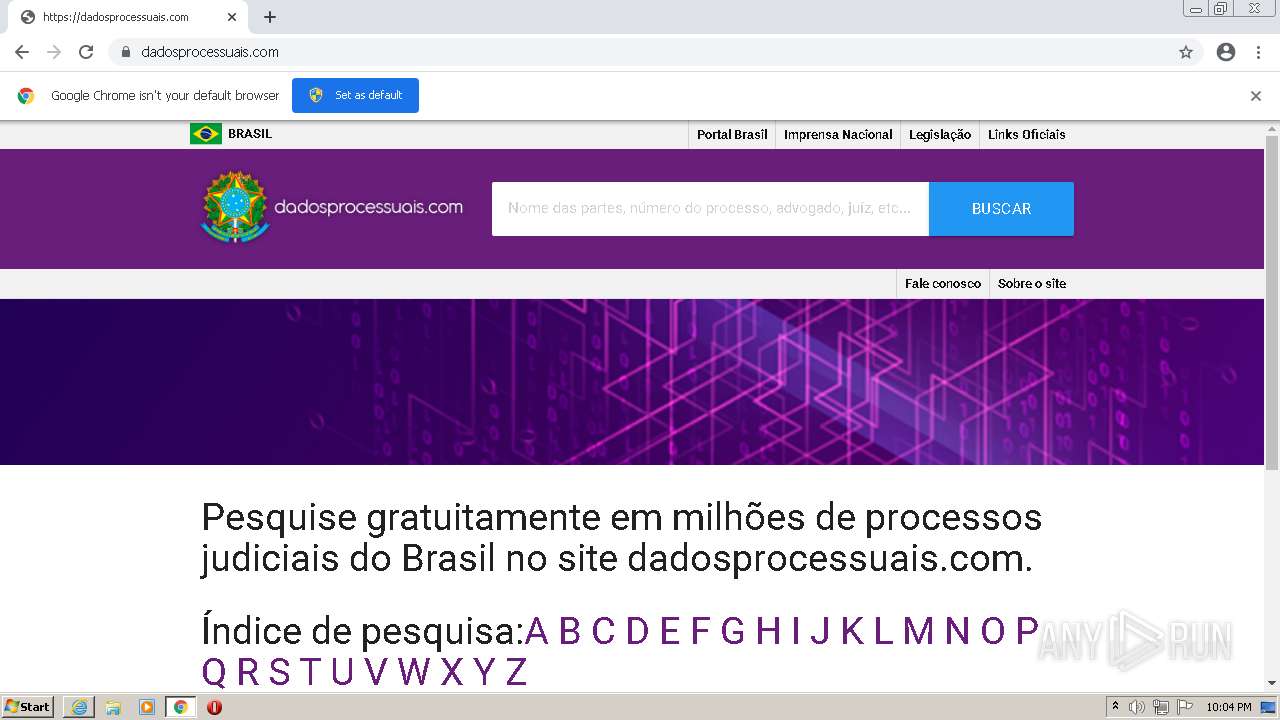
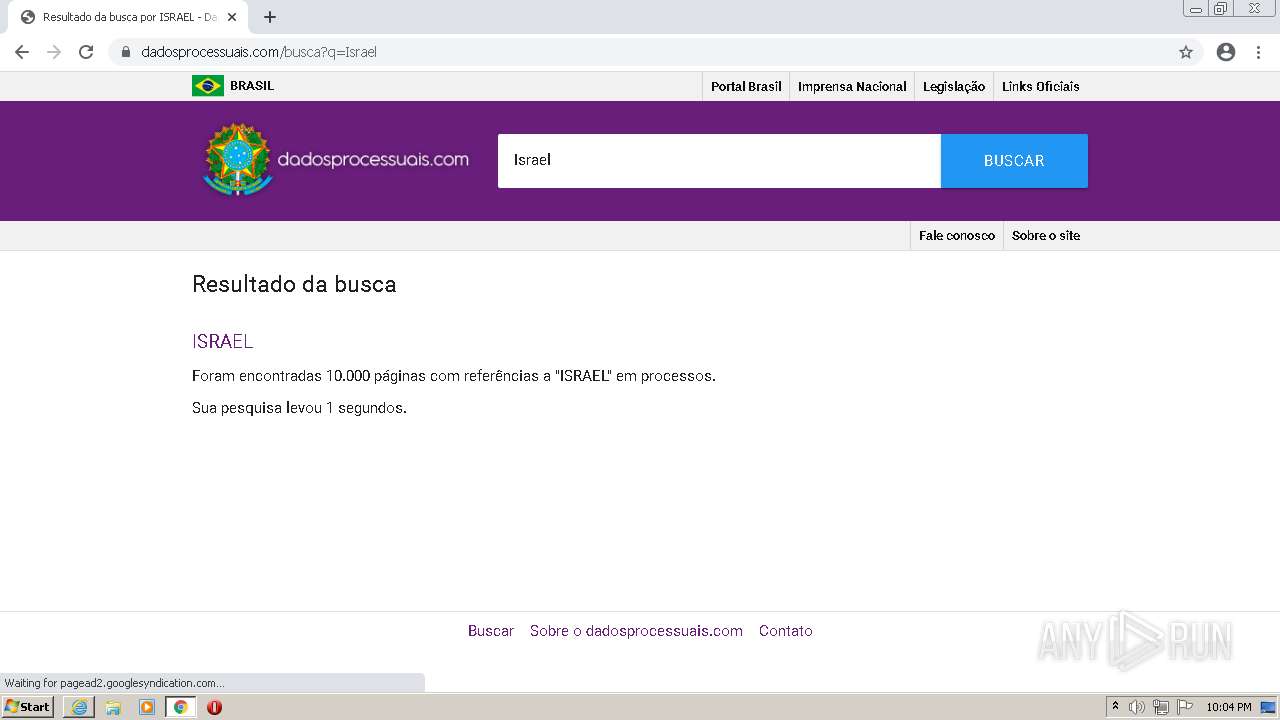
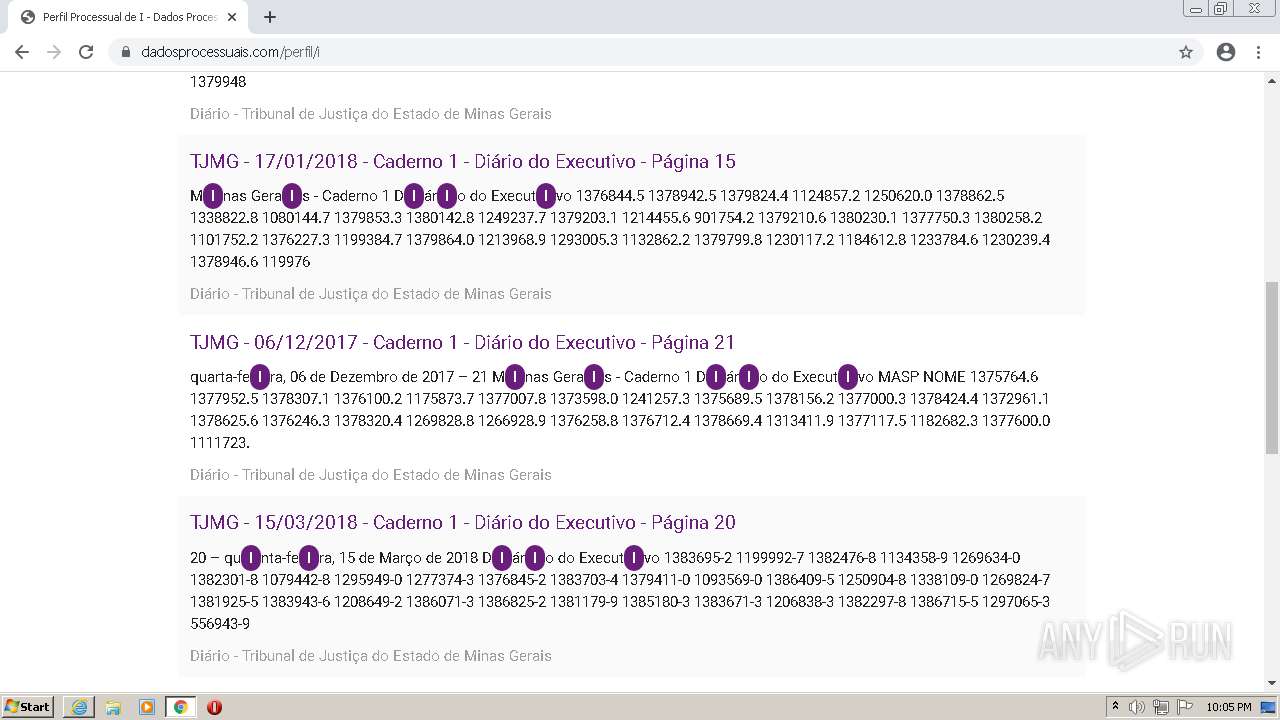
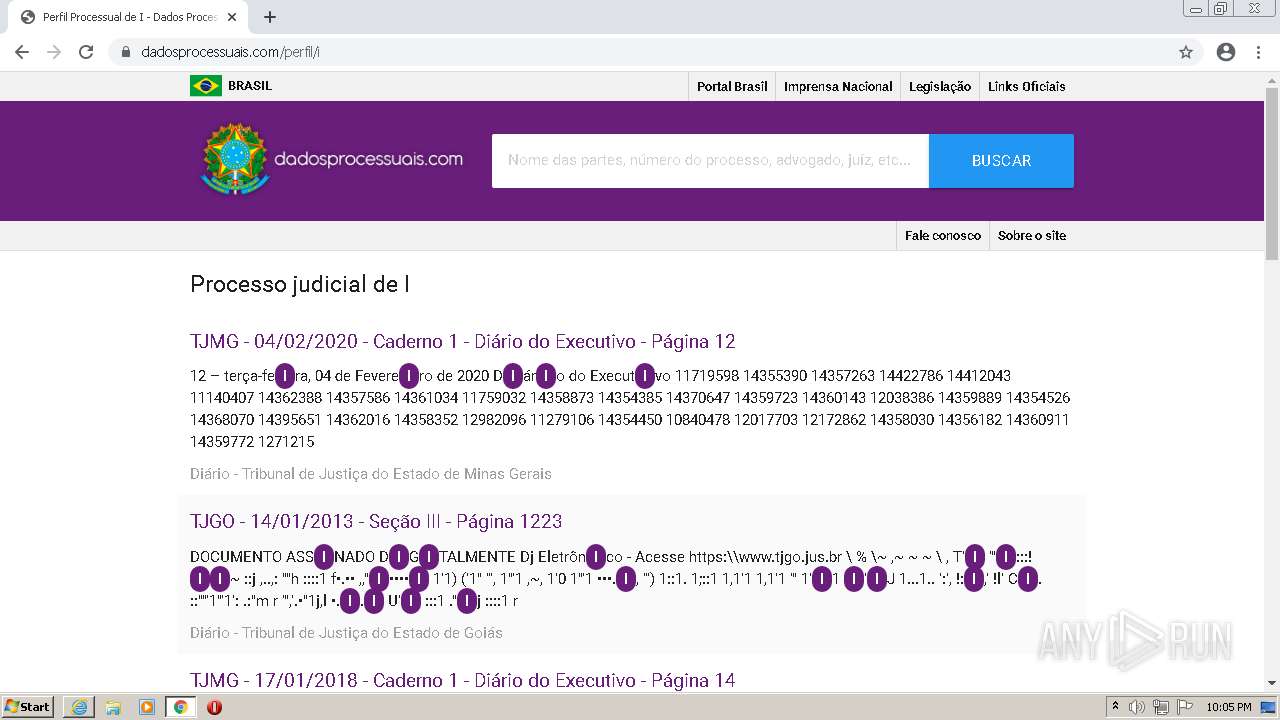
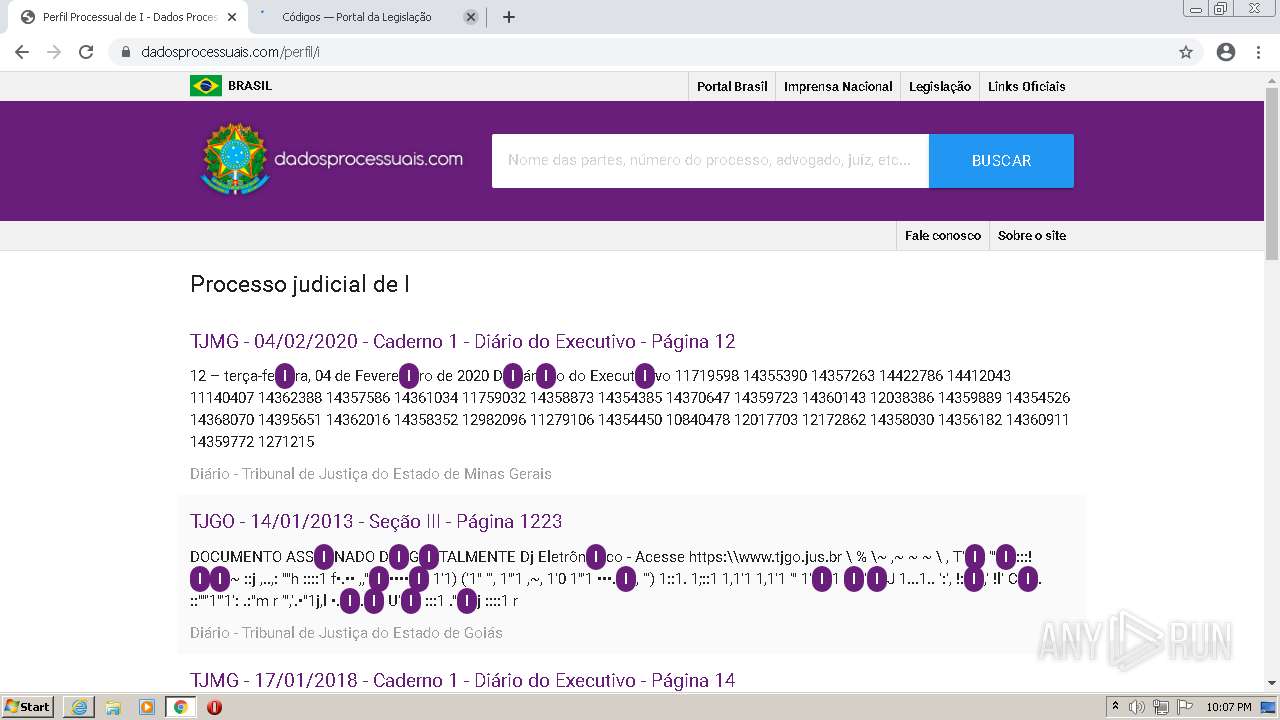
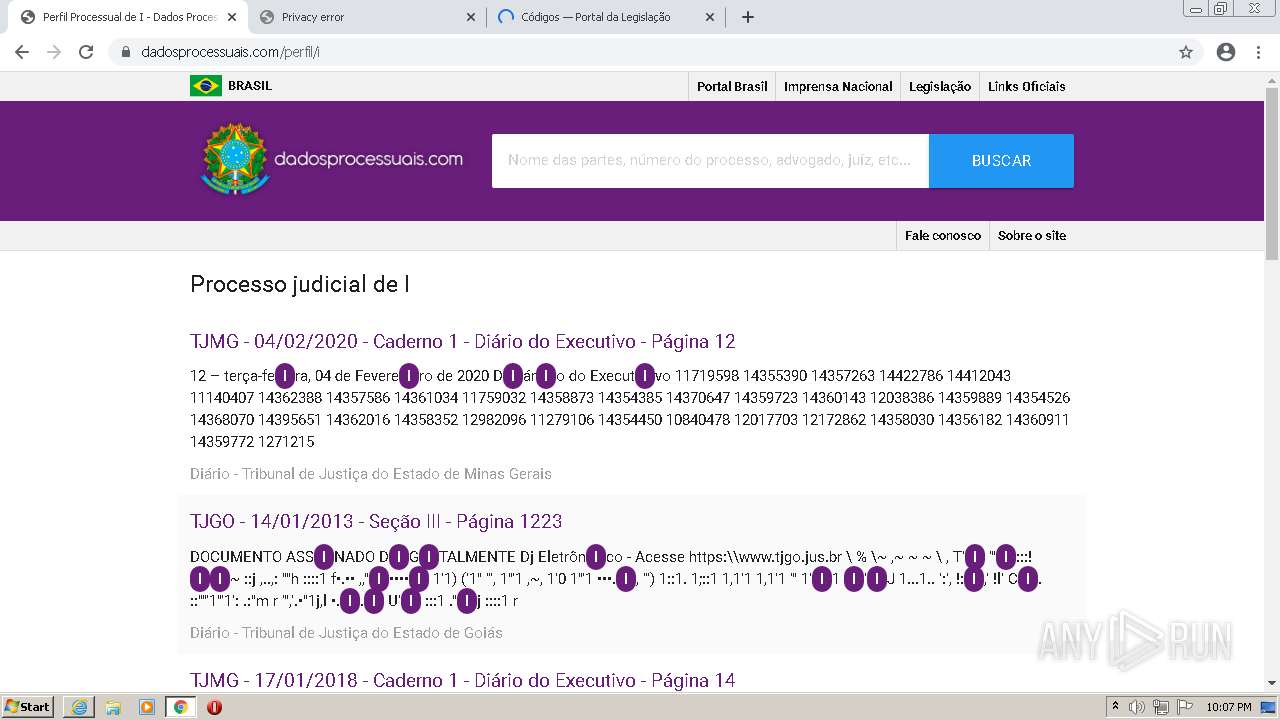
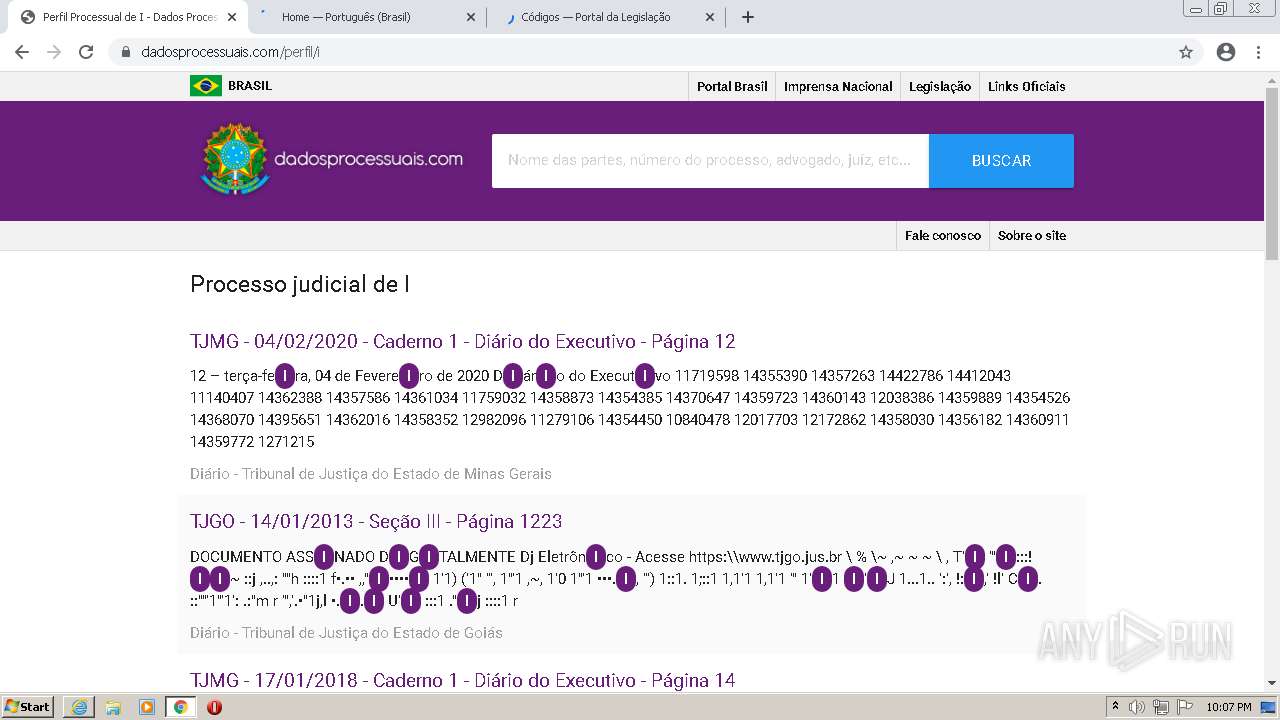
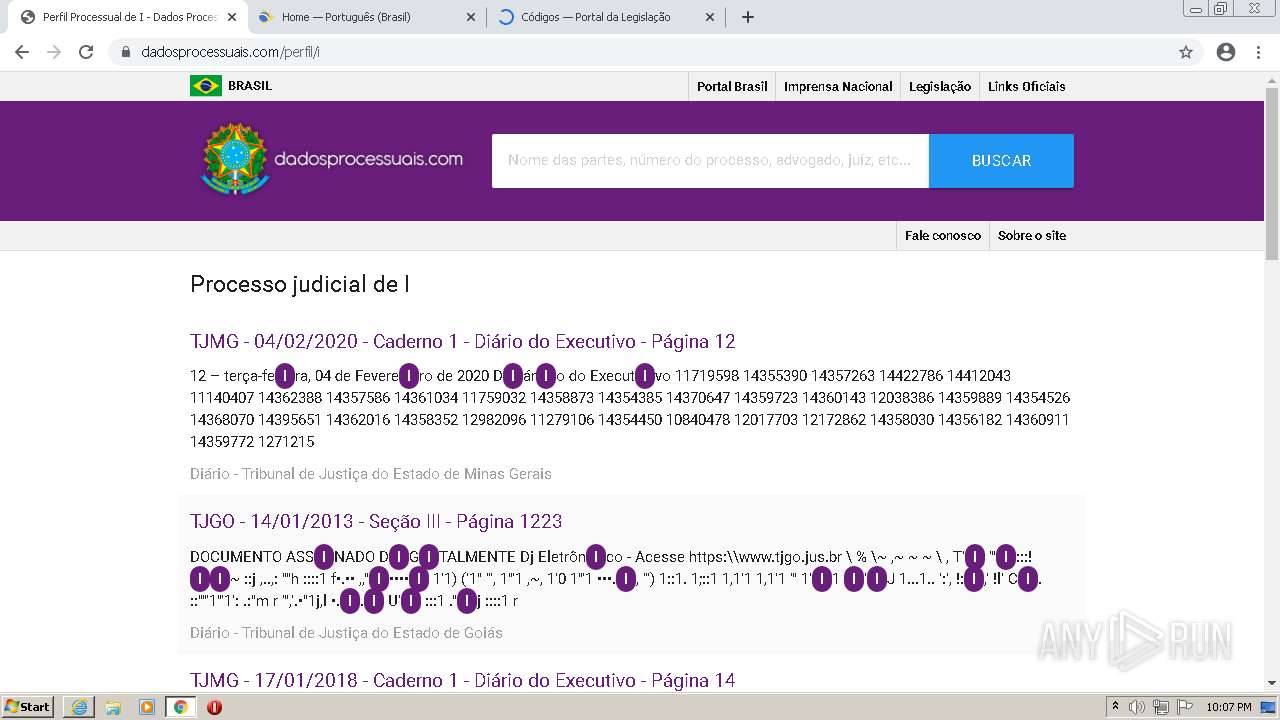
| URL: | https://dadosprocessuais.com/ |
| Full analysis: | https://app.any.run/tasks/e3463fc0-12c6-4d67-82a4-c6d66e9ded8d |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 21:03:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 735A017FE6C4013414C92BEA065C86E1 |
| SHA1: | 47E7F2F3FFEA4EDF9FCAE7C7F2969A7849ACB4FD |
| SHA256: | B1BDA6D007D94DDF5E1DBFC17DF80323F5F8F890C35E67EBF51517FABD4568FB |
| SSDEEP: | 3:N8c8LWaKK:2cEWaKK |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 2088)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3040)
Modifies files in Chrome extension folder
- chrome.exe (PID: 424)
Drops a file with a compile date too recent
- chrome.exe (PID: 2088)
Executable content was dropped or overwritten
- chrome.exe (PID: 2088)
INFO
Reads the computer name
- iexplore.exe (PID: 3164)
- iexplore.exe (PID: 3040)
- chrome.exe (PID: 1280)
- chrome.exe (PID: 424)
- chrome.exe (PID: 2740)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 1580)
- chrome.exe (PID: 1988)
- chrome.exe (PID: 3020)
- chrome.exe (PID: 2452)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 4036)
Checks supported languages
- iexplore.exe (PID: 3040)
- iexplore.exe (PID: 3164)
- chrome.exe (PID: 1280)
- chrome.exe (PID: 424)
- chrome.exe (PID: 2872)
- chrome.exe (PID: 2740)
- chrome.exe (PID: 1472)
- chrome.exe (PID: 1952)
- chrome.exe (PID: 544)
- chrome.exe (PID: 1580)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 1376)
- chrome.exe (PID: 2980)
- chrome.exe (PID: 1424)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 2552)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2868)
- chrome.exe (PID: 1660)
- chrome.exe (PID: 508)
- chrome.exe (PID: 3420)
- chrome.exe (PID: 1128)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 2116)
- chrome.exe (PID: 3020)
- chrome.exe (PID: 3116)
- chrome.exe (PID: 2716)
- chrome.exe (PID: 1988)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 3020)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 2452)
- chrome.exe (PID: 508)
- chrome.exe (PID: 3632)
- chrome.exe (PID: 3936)
- chrome.exe (PID: 444)
- chrome.exe (PID: 3480)
- chrome.exe (PID: 3120)
- chrome.exe (PID: 2080)
- chrome.exe (PID: 1992)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 3316)
- chrome.exe (PID: 1160)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 948)
- chrome.exe (PID: 656)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 3764)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 884)
- chrome.exe (PID: 508)
- chrome.exe (PID: 1236)
- chrome.exe (PID: 1796)
- chrome.exe (PID: 3852)
- chrome.exe (PID: 3736)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 1268)
- chrome.exe (PID: 1316)
- chrome.exe (PID: 2484)
- chrome.exe (PID: 1304)
- chrome.exe (PID: 4036)
- chrome.exe (PID: 2264)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 1288)
- chrome.exe (PID: 2088)
- chrome.exe (PID: 1844)
- chrome.exe (PID: 1500)
- chrome.exe (PID: 4036)
- chrome.exe (PID: 2780)
- chrome.exe (PID: 1236)
- chrome.exe (PID: 3988)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 3640)
- chrome.exe (PID: 1736)
Reads settings of System Certificates
- iexplore.exe (PID: 3164)
- chrome.exe (PID: 1280)
- iexplore.exe (PID: 3040)
Application launched itself
- iexplore.exe (PID: 3164)
- chrome.exe (PID: 424)
Changes internet zones settings
- iexplore.exe (PID: 3164)
Manual execution by user
- chrome.exe (PID: 424)
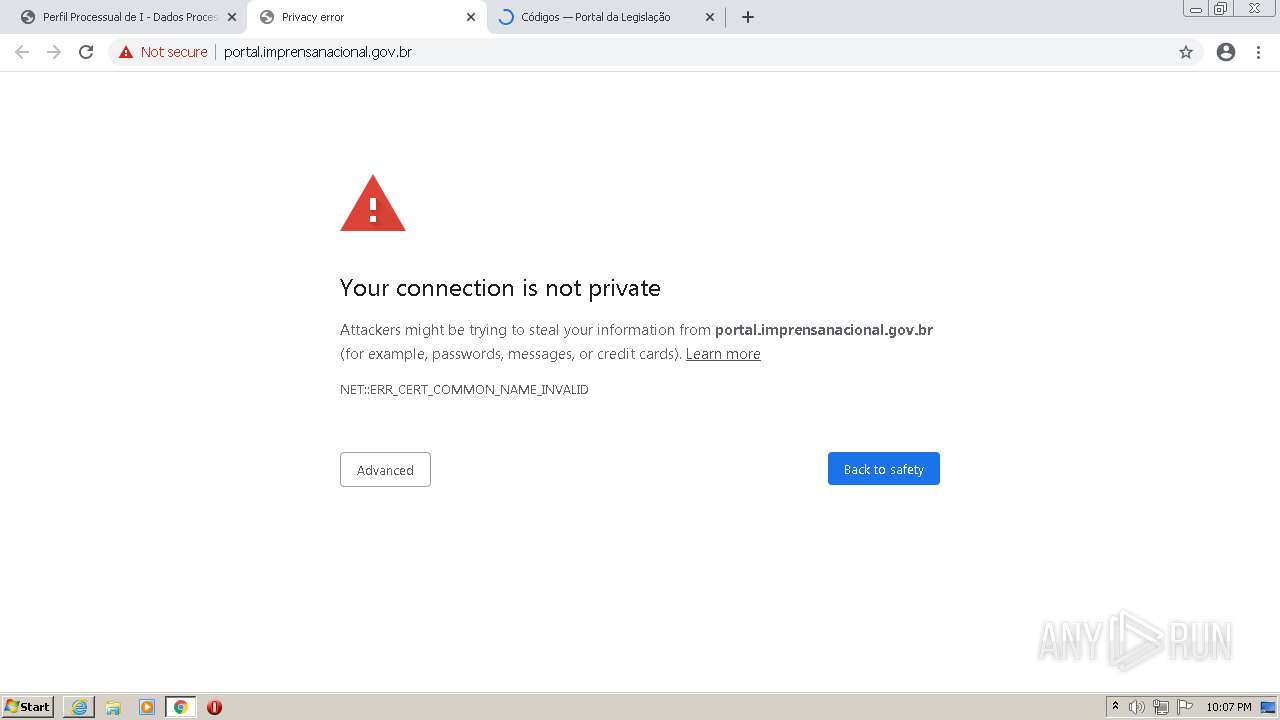
Checks Windows Trust Settings
- iexplore.exe (PID: 3164)
- iexplore.exe (PID: 3040)
Reads internet explorer settings
- iexplore.exe (PID: 3040)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3164)
Reads the date of Windows installation
- chrome.exe (PID: 3020)
Drops Coronavirus (possible) decoy
- chrome.exe (PID: 1280)
Changes settings of System certificates
- iexplore.exe (PID: 3164)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
112
Monitored processes
77
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,17005249360746461419,443462407202677528,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3528 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,17005249360746461419,443462407202677528,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3528 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,17005249360746461419,443462407202677528,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,17005249360746461419,443462407202677528,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=51 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3824 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,17005249360746461419,443462407202677528,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,17005249360746461419,443462407202677528,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3884 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,17005249360746461419,443462407202677528,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=49 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2400 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,17005249360746461419,443462407202677528,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,17005249360746461419,443462407202677528,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2200 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
32 367
Read events
32 002
Write events
355
Delete events
10
Modification events
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 193934016 | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30977679 | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 494096516 | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30977679 | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
400
Text files
329
Unknown types
58
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62F6C05A-1A8.pma | — | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 1280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF12a909.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
140
TCP/UDP connections
173
DNS requests
101
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3040 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCsaQm9IjtQWwpY0PgImSGA | US | der | 472 b | whitelisted |
3040 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGT2qXP4YCwoCiwRsjbPa6U%3D | US | der | 471 b | whitelisted |
3040 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3040 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3040 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr5/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQiD0S5cIHyfrLTJ1fvAkJWflH%2B2QQUPeYpSJvqB8ohREom3m7e0oPQn1kCDQHuXyKVQkkF%2BQGRqNw%3D | US | der | 1.26 Kb | whitelisted |
3040 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEApXfuD0XkDcvTEeB3da6O8%3D | US | der | 279 b | whitelisted |
3040 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3040 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHUeP1PjGFkz6V8I7O6tApc%3D | US | der | 1.41 Kb | whitelisted |
3040 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEHpVlZrETqnzCo8pyfMBrBs%3D | US | der | 471 b | whitelisted |
3040 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDKpro7juH4phJoDwMJZHJr | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
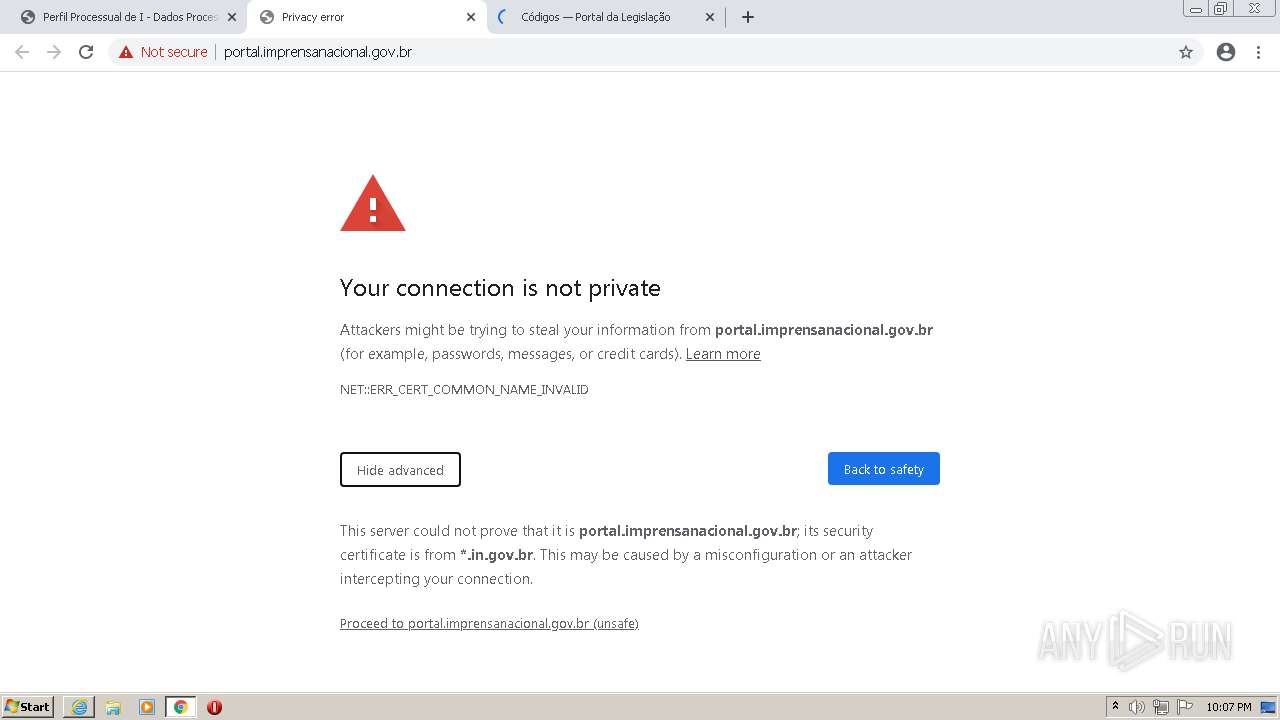
3040 | iexplore.exe | 188.114.97.12:443 | dadosprocessuais.com | Cloudflare Inc | US | malicious |
3164 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3164 | iexplore.exe | 178.79.242.0:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | DE | whitelisted |
3164 | iexplore.exe | 178.79.242.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | DE | malicious |
3164 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3040 | iexplore.exe | 188.114.96.12:443 | dadosprocessuais.com | Cloudflare Inc | US | malicious |
1280 | chrome.exe | 142.250.74.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
1280 | chrome.exe | 142.250.184.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1280 | chrome.exe | 142.250.186.173:443 | accounts.google.com | Google Inc. | US | suspicious |
1280 | chrome.exe | 216.58.212.164:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dadosprocessuais.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1280 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
1280 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1280 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1280 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1280 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1280 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |