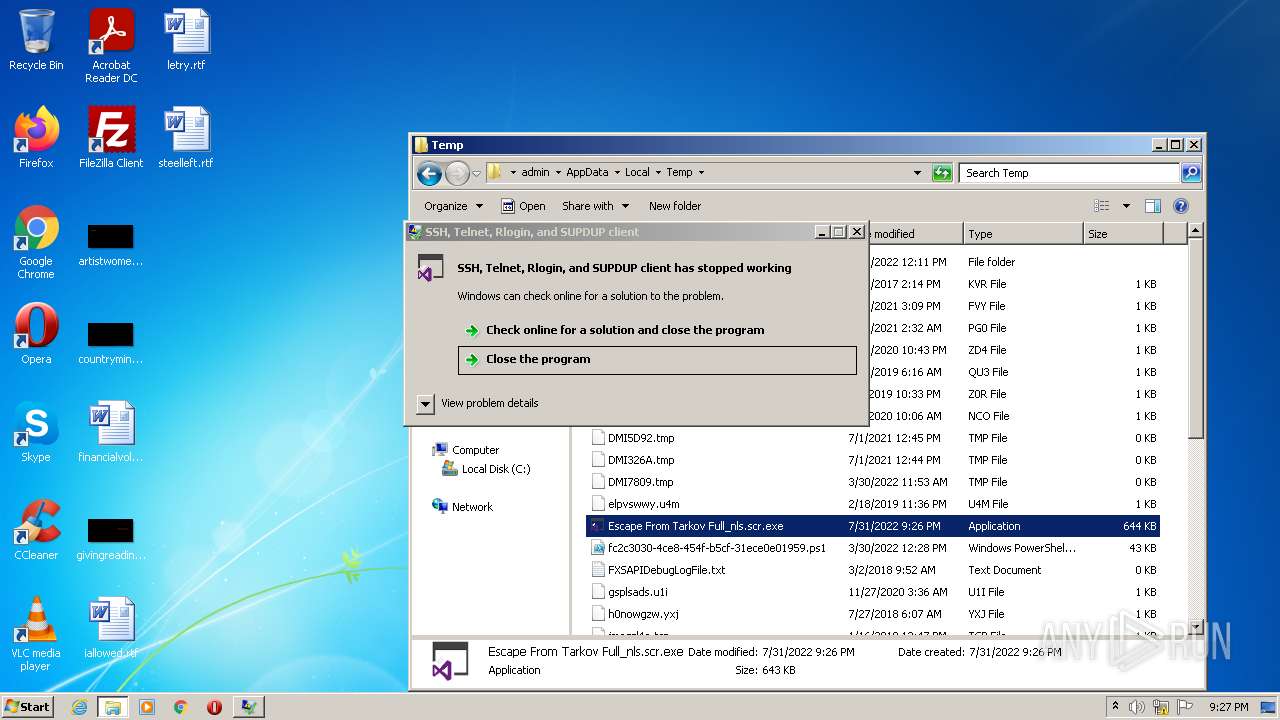
| File name: | Escape From Tarkov Full_nls.scr |
| Full analysis: | https://app.any.run/tasks/bbb07b49-635e-491b-9d1b-89831b80c95d |
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2022, 20:26:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 9FD996CE42D667BA01C902124BF95F6D |
| SHA1: | DB1A3B2FD8FAFDA32F8C7EBBA0BBE76E0C89697D |
| SHA256: | B19CBD208FDF60F9B9318BF8C4A5615AFA49D4C21BB9F620AAD14FB8D60D892B |
| SSDEEP: | 6144:b7fQzevfWMppNRMaSzBro8brQhXKHvfg2R2dfhUQieNyiVRnWt09zE:PZRpN8JB4uXfRWmZeNyiVRnWO2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the computer name
- Escape From Tarkov Full_nls.scr.exe (PID: 2452)
- Escape From Tarkov Full_nls.scr.exe (PID: 2076)
- Escape From Tarkov Full_nls.scr.exe (PID: 2108)
- powershell.exe (PID: 1604)
Checks supported languages
- Escape From Tarkov Full_nls.scr.exe (PID: 2452)
- Escape From Tarkov Full_nls.scr.exe (PID: 2108)
- Escape From Tarkov Full_nls.scr.exe (PID: 2076)
- powershell.exe (PID: 1604)
Reads the date of Windows installation
- powershell.exe (PID: 1604)
INFO
Checks supported languages
- explorer.exe (PID: 2716)
Reads the computer name
- explorer.exe (PID: 2716)
Manual execution by user
- explorer.exe (PID: 2716)
- Escape From Tarkov Full_nls.scr.exe (PID: 2108)
- Escape From Tarkov Full_nls.scr.exe (PID: 2076)
- powershell.exe (PID: 1604)
Checks Windows Trust Settings
- powershell.exe (PID: 1604)
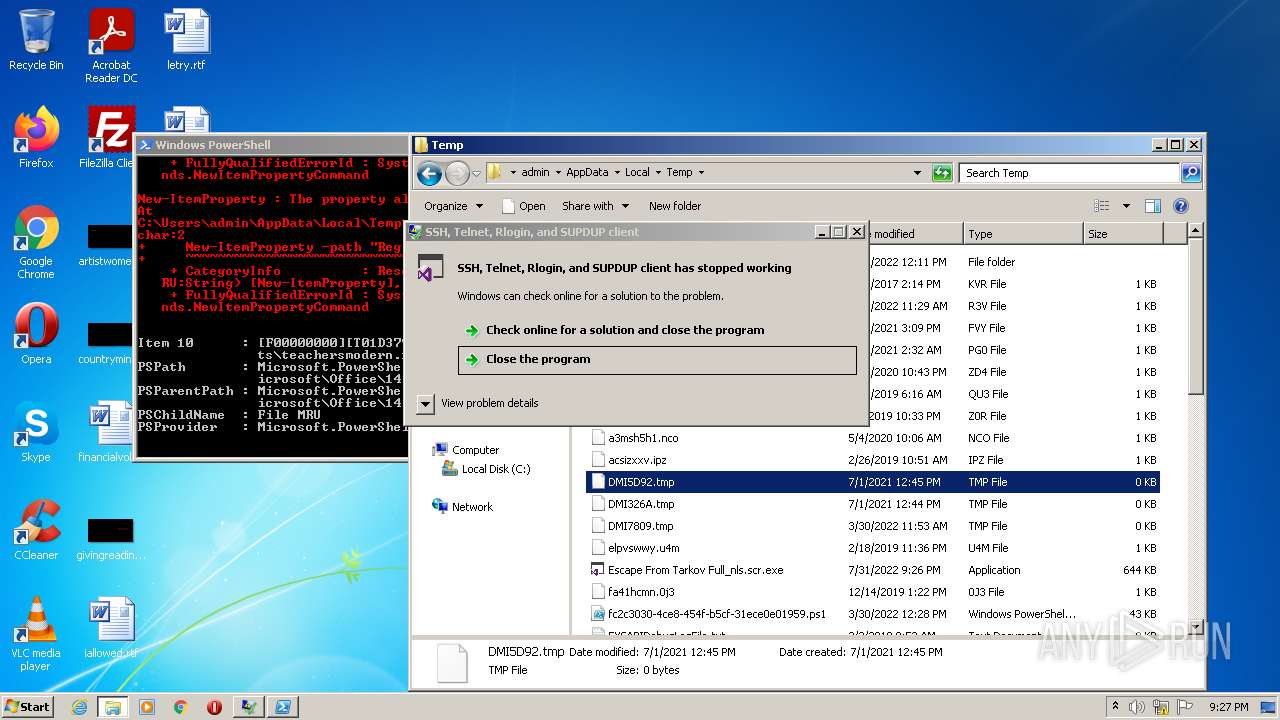
Reads Microsoft Office registry keys
- powershell.exe (PID: 1604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| AssemblyVersion: | 0.77.0.0 |
|---|---|
| ProductVersion: | 0.77.0.0 |
| ProductName: | PuTTY suite |
| OriginalFileName: | Tvgtizy.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © 1997-2022 Simon Tatham. |
| InternalName: | Tvgtizy.exe |
| FileVersion: | 0.77.0.0 |
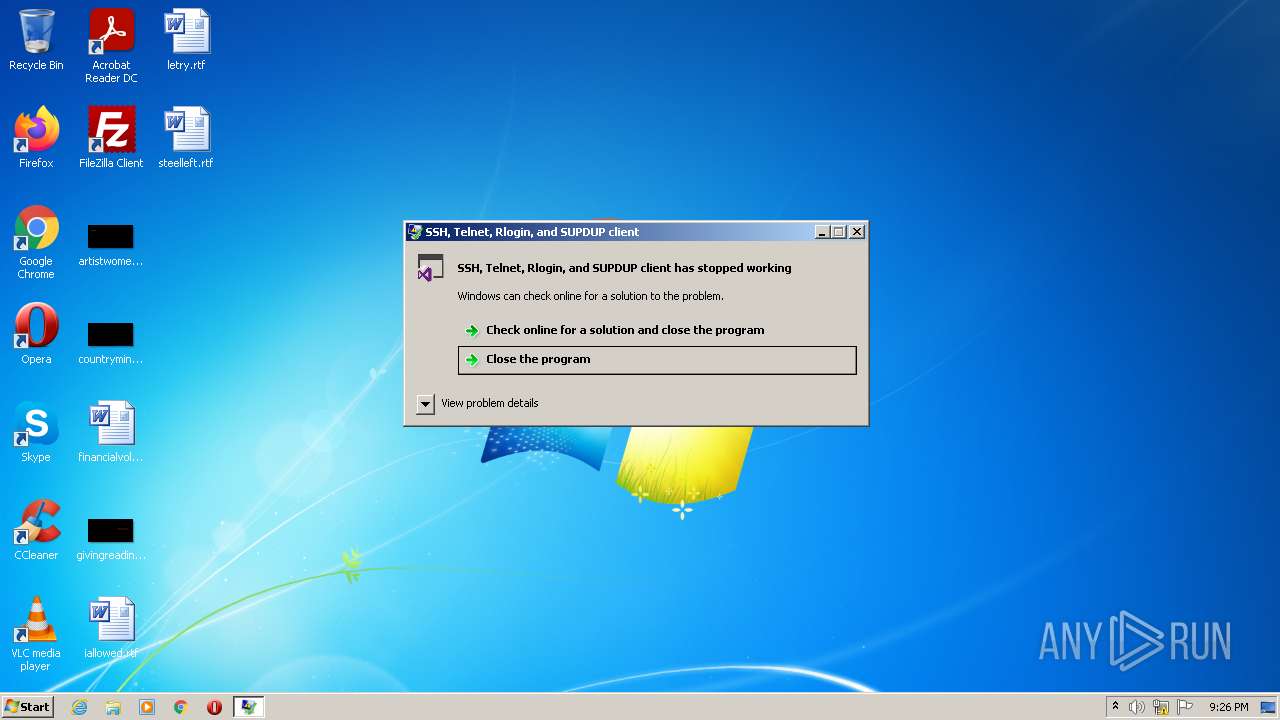
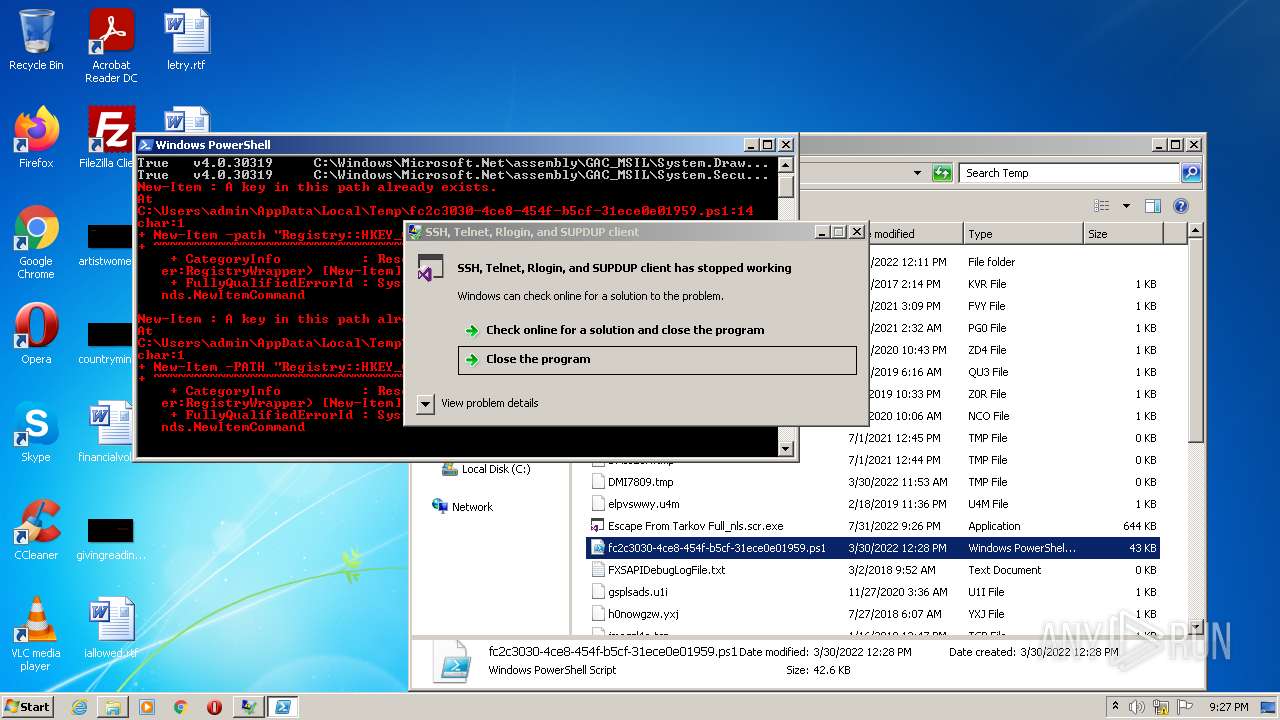
| FileDescription: | SSH, Telnet, Rlogin, and SUPDUP client |
| CompanyName: | Simon Tatham |
| Comments: | SSH, Telnet, Rlogin, and SUPDUP client |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.77.0.0 |
| FileVersionNumber: | 0.77.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x379e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 251904 |
| CodeSize: | 406528 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| TimeStamp: | 2053:06:26 05:31:45+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-May-1917 21:03:29 |
| Comments: | SSH, Telnet, Rlogin, and SUPDUP client |
| CompanyName: | Simon Tatham |
| FileDescription: | SSH, Telnet, Rlogin, and SUPDUP client |
| FileVersion: | 0.77.0.0 |
| InternalName: | Tvgtizy.exe |
| LegalCopyright: | Copyright © 1997-2022 Simon Tatham. |
| LegalTrademarks: | - |
| OriginalFilename: | Tvgtizy.exe |
| ProductName: | PuTTY suite |
| ProductVersion: | 0.77.0.0 |
| Assembly Version: | 0.77.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 20-May-1917 21:03:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000633BC | 0x00063400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.99726 |
.rsrc | 0x00066000 | 0x0003D4BE | 0x0003D600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.91457 |
.reloc | 0x000A4000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 2.01924 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
46
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
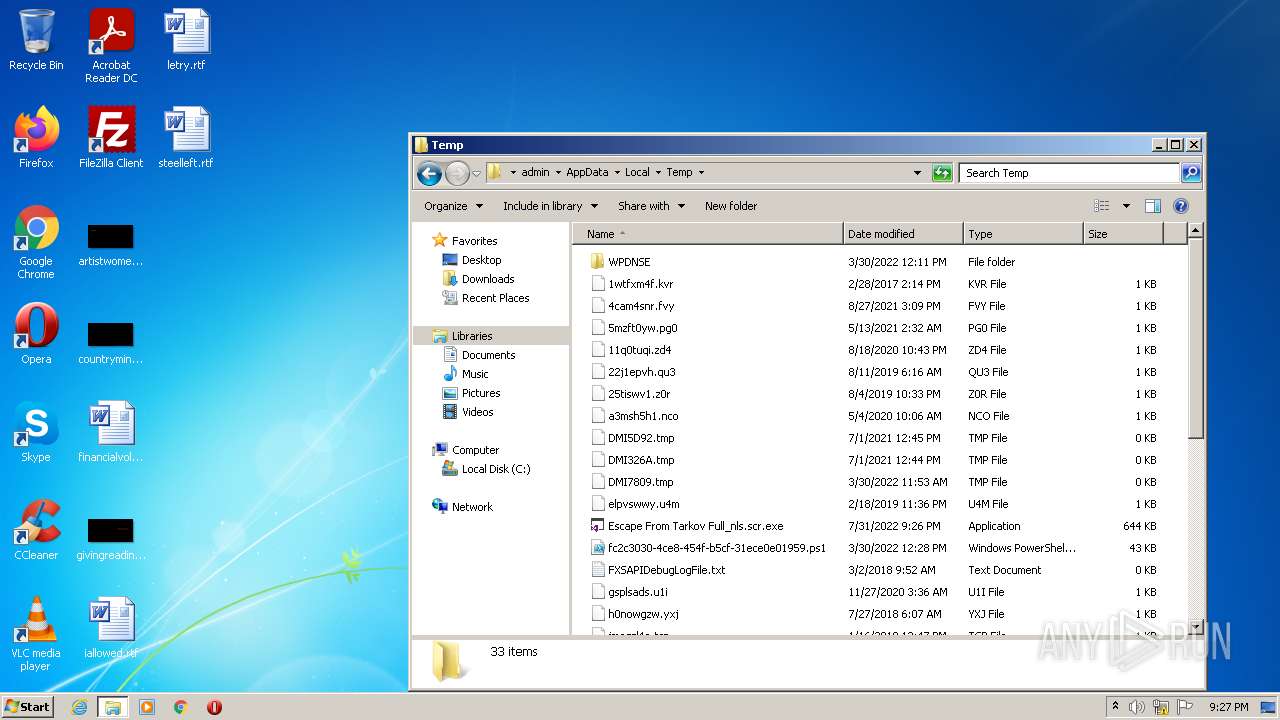
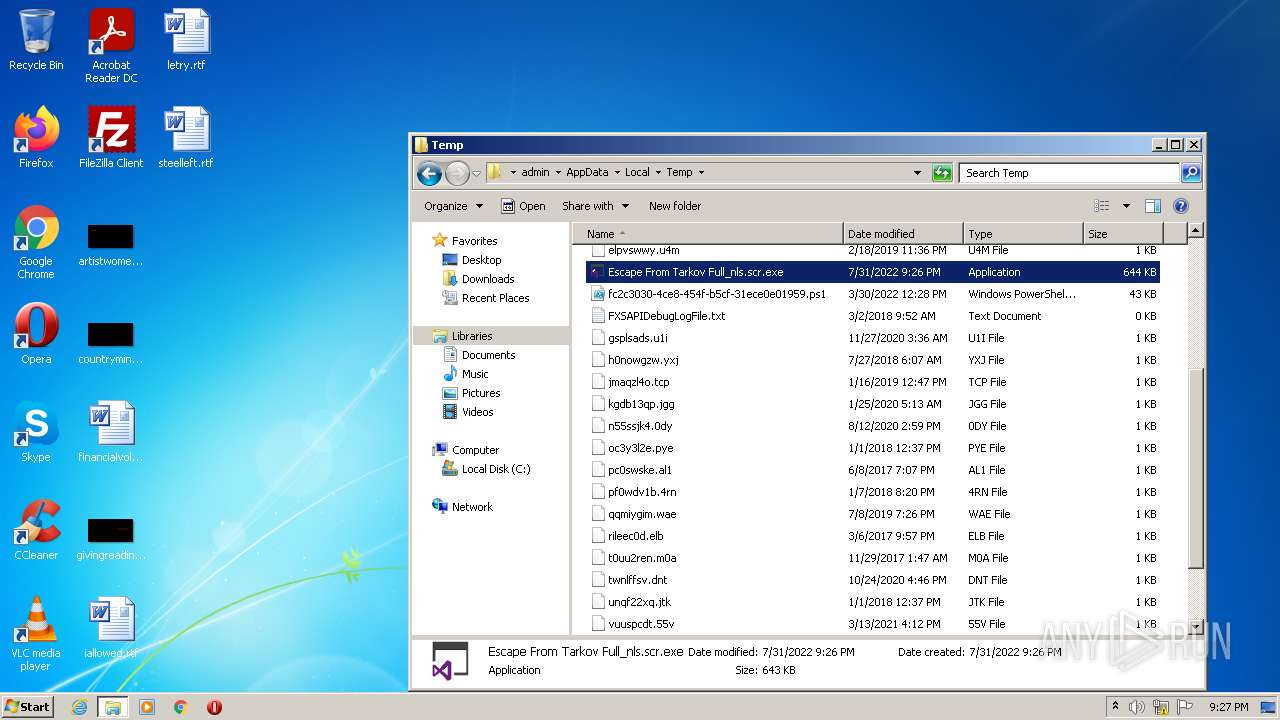
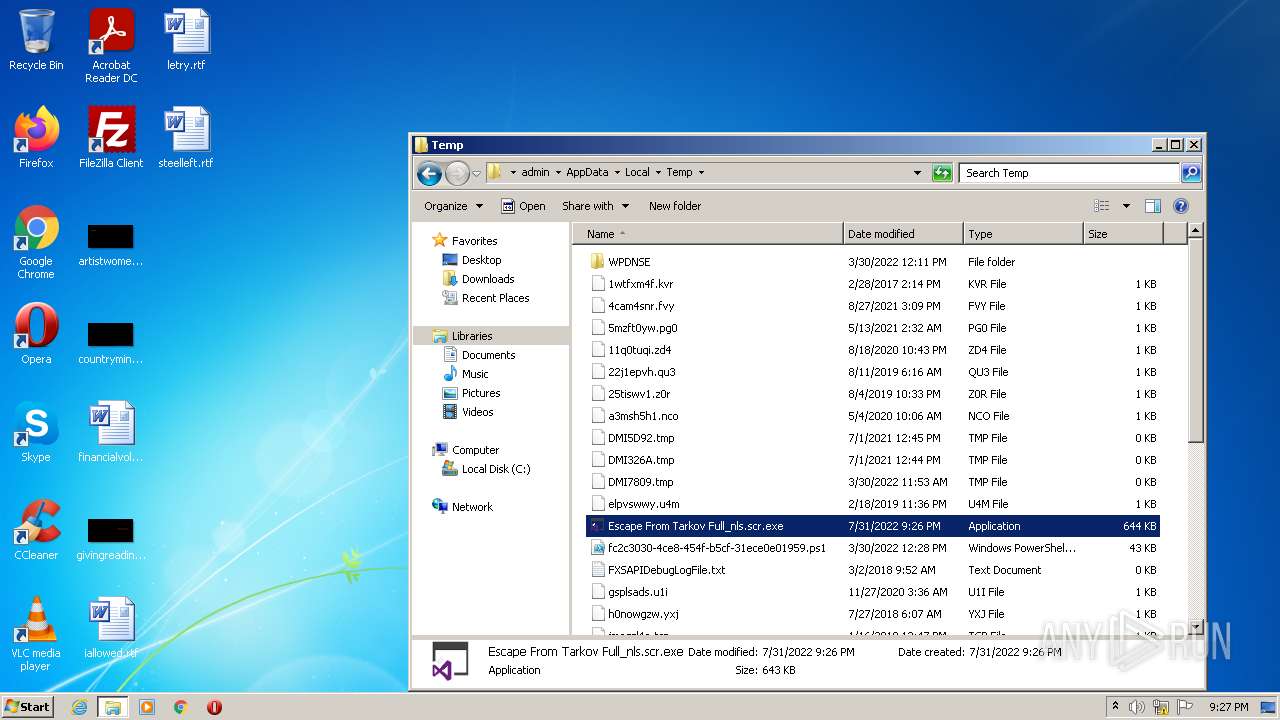
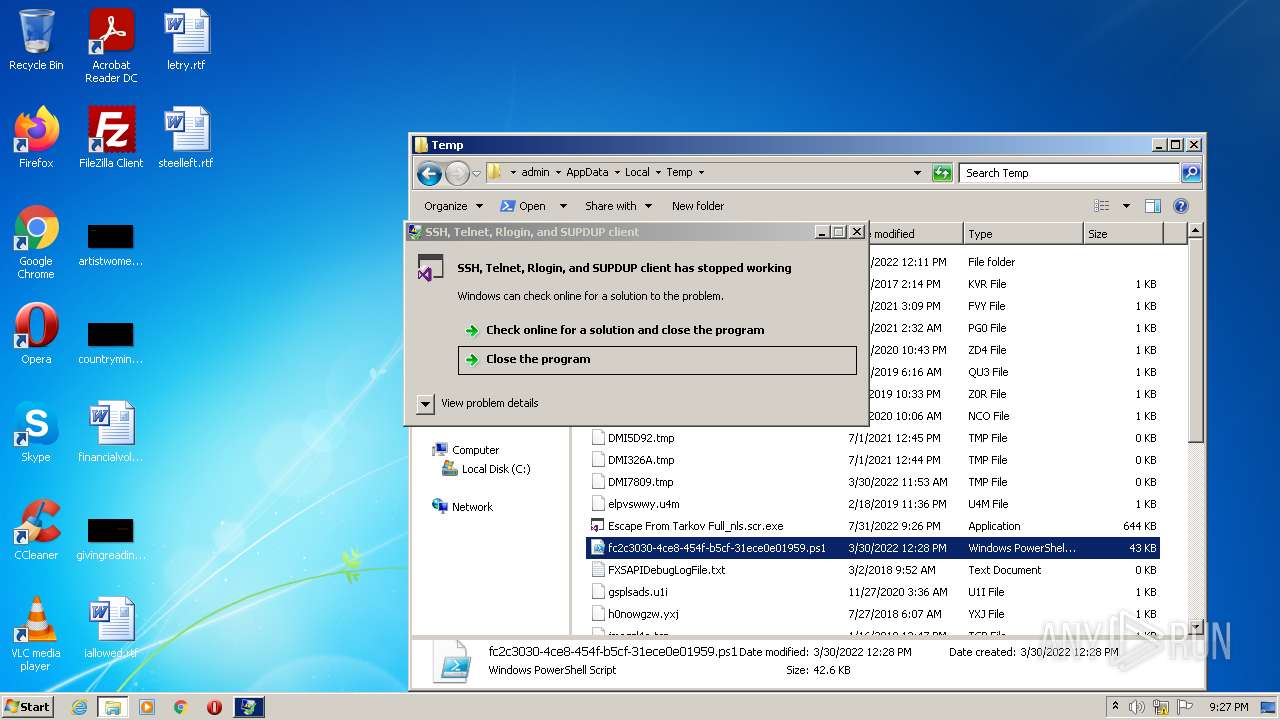
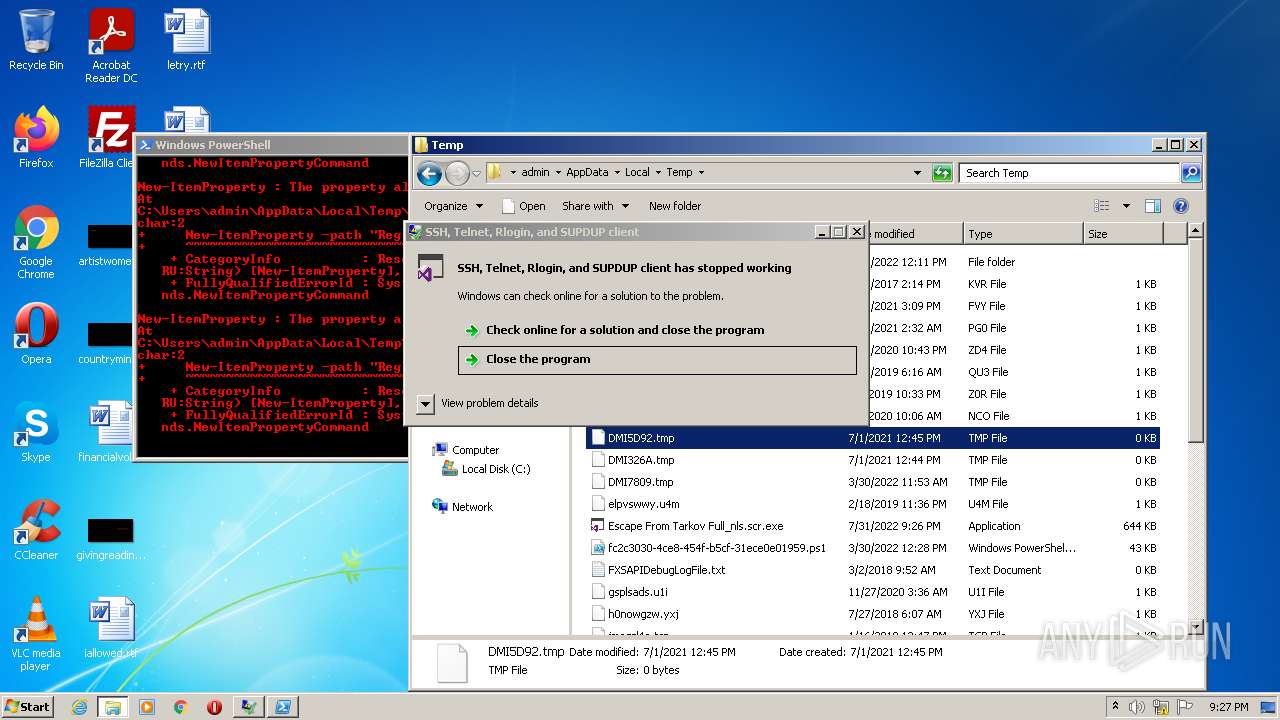
| 1604 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\fc2c3030-4ce8-454f-b5cf-31ece0e01959.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2076 | "C:\Users\admin\AppData\Local\Temp\Escape From Tarkov Full_nls.scr.exe" | C:\Users\admin\AppData\Local\Temp\Escape From Tarkov Full_nls.scr.exe | Explorer.EXE | ||||||||||||
User: admin Company: Simon Tatham Integrity Level: MEDIUM Description: SSH, Telnet, Rlogin, and SUPDUP client Exit code: 0 Version: 0.77.0.0 Modules
| |||||||||||||||
| 2108 | "C:\Users\admin\AppData\Local\Temp\Escape From Tarkov Full_nls.scr.exe" | C:\Users\admin\AppData\Local\Temp\Escape From Tarkov Full_nls.scr.exe | Explorer.EXE | ||||||||||||
User: admin Company: Simon Tatham Integrity Level: MEDIUM Description: SSH, Telnet, Rlogin, and SUPDUP client Exit code: 3762504530 Version: 0.77.0.0 Modules
| |||||||||||||||
| 2452 | "C:\Users\admin\AppData\Local\Temp\Escape From Tarkov Full_nls.scr.exe" | C:\Users\admin\AppData\Local\Temp\Escape From Tarkov Full_nls.scr.exe | Explorer.EXE | ||||||||||||
User: admin Company: Simon Tatham Integrity Level: MEDIUM Description: SSH, Telnet, Rlogin, and SUPDUP client Exit code: 3762504530 Version: 0.77.0.0 Modules
| |||||||||||||||
| 2716 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 222
Read events
2 150
Write events
72
Delete events
0
Modification events
| (PID) Process: | (1604) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1604) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1604) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1604) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1604) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1604) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\File MRU |
| Operation: | write | Name: | Item 10 |
Value: [F00000000][T01D37935759CDB00][O00000000]*C:\Users\admin\Documents\teachersmodern.rtf | |||
| (PID) Process: | (1604) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\IntelliForms\Storage2 |
| Operation: | write | Name: | 52A19BCDDD82861C191B287C7B94739F030367E1A3 |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB010000001465D66921EDC44B92F35A0CFC69486A00000000020000000000106600000001000020000000C6B82D3F3F1024B83F05C0A36963DCD94C21723806C1FF371BEC47441618E610000000000E8000000002000020000000ABC13203BED58D2D4BF1BCD6952FD39056A672971B1C2DCBC005C259F5EE9EE59000000032E40269425A4843A1F96C7D91D1129D4AF05A2E3436F97D9D98F9504C56543AE45A4CC0F18BE1C1EECF60AC252D86B4BDA6C5F6D7570834C4DD928567535E5F22DBD1D6A7135DA1E2F305F07A877B5D9AC8A055CBFF69B13098D6FD128DE111AD7F51B9B48AEB5DD749770656DE65DB169A3CF2C89BBE740664EC004968189779BAE3BFFF1601A1B03DA9AB6045926D400000002D3AF838650F0A0642D722F92A383D688F4479B97E4A5212561165C285ABD8DCD66A993E124255DAF0526337ECF4FAEA4F383F2A0A9C2E8C16CA37B668B3CB41 | |||
| (PID) Process: | (1604) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\IntelliForms\Storage2 |
| Operation: | write | Name: | 1DF0FB41C1273398FD9D3B4D8013C3997A5349274A |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB010000001465D66921EDC44B92F35A0CFC69486A00000000020000000000106600000001000020000000ECF4418DCFEFA4E5433AC1CE2898BB924E09CFE7CE60BB6DF3EAF0B3F2BE2E73000000000E8000000002000020000000A42371E2797F8B1EDD85E97D947B5518A222FC17374F8F5FC39ABF9F18660A6290000000107AFA925549A33C6CAF52E33B5A180D8D6AAE4D3417BA9488B545F2FFEC8AEE352A6AF5D58A9A58923C7D883AC5B0E0A7B1EA7E5D4AFE6C3ED6AF8CAFDA329B67AE43397E03DC7C0A6A99858EDF499A8594B626BA38B1DE2BCE05457814A3F12A9CE102FC69D28C671CD73C468C4A273AE8FF22B11ECF6E91B01F185BF613C0EA80DD44C4CEC51E79BE0546DCA9408A40000000234DA872BAEF30600308DAEB59A92E9462475A44245C95E1734667348621D4F1039C37210601539F88D0CDC008A26693E38A7CC3AA9C27C6BA51D7B5DC56A84F | |||
| (PID) Process: | (1604) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\IntelliForms\Storage2 |
| Operation: | write | Name: | 01DF7C71529474E2E9A3D344C72ACD206C590B0F69 |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB010000001465D66921EDC44B92F35A0CFC69486A0000000002000000000010660000000100002000000039C6A0E175DB9175C25187BCA993C8D83A44B53D82E35C14A54C685599CADAB2000000000E8000000002000020000000E38B28F4057FA7980B78040AF992CB0370DC011F43D66ABF47F3873EB0B0DB7590000000D33659C9ACA14B85CA84B60BD34CCBBBDF088B86C0C279627D4FAAF18C21A423126E3B349498CCDD75BEE4955228DF066AB58DA78A24C7C061F9394F9B82715E81B7688857B847E4BC6662295CC1E3D31C1A95DDA542A3E0D44C78D55799FA3BFFE6C1E0A8F8C6FB8B335CF2F2BA251BE1A727D2D2E7CD3D9D5F0B2B5C9B1C37893236AAC2E30C81D2DB18E7356CA8614000000089567F82C67DCC7AD7BC7ACEA120FBB6C9610880C6395C7400C37164A7F8AF0F5F7861FD63BEFE33B9FE438A074749FDD58E765B6B87AA7EA5415A7DFC765E58 | |||
| (PID) Process: | (1604) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\IntelliForms\Storage2 |
| Operation: | write | Name: | 1489F923C4DCA729178B3E3233458550D8DDDF2945 |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB010000001465D66921EDC44B92F35A0CFC69486A00000000020000000000106600000001000020000000152704BEDA52A82A8897C4834DE07CD0BC23E018F5A63564B4E632618C4865E0000000000E800000000200002000000044E43B842B960668617121353C65AFD6426FF51C699A30122D1B53D9A0F0D7329000000032B4D28ECDB506663202C020080BD42410CB7741CFF3E69458FBEAD0F3ACFDD9A816EC5EFE033E51A50CBDFBFC0A8142E7E1AE120C9230240FFC66965C799D31503EDAF386D53240E28E5FDACF150B56B39B316BA92F2484C180B907BA8E5EB511091B4135F0AAEF072F15429BCE56DE08693ED28E13E482C148BFF628EDBDABCC299820A7A4E7E51C8611FA5D37C579400000000E027F6D03C33CD6672D83540EEBED08B642685DDA446DEEA013B1F62D76EB458E10EB12B09EE7A46475619718185FAB76FD609F13871354663EC62CC8E0FEED | |||
Executable files
0
Suspicious files
21
Text files
28
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1604 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF102f30.TMP | binary | |
MD5:— | SHA256:— | |||
| 1604 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NM5XGJ2PAR6ZG89G5SWW.temp | binary | |
MD5:— | SHA256:— | |||
| 1604 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
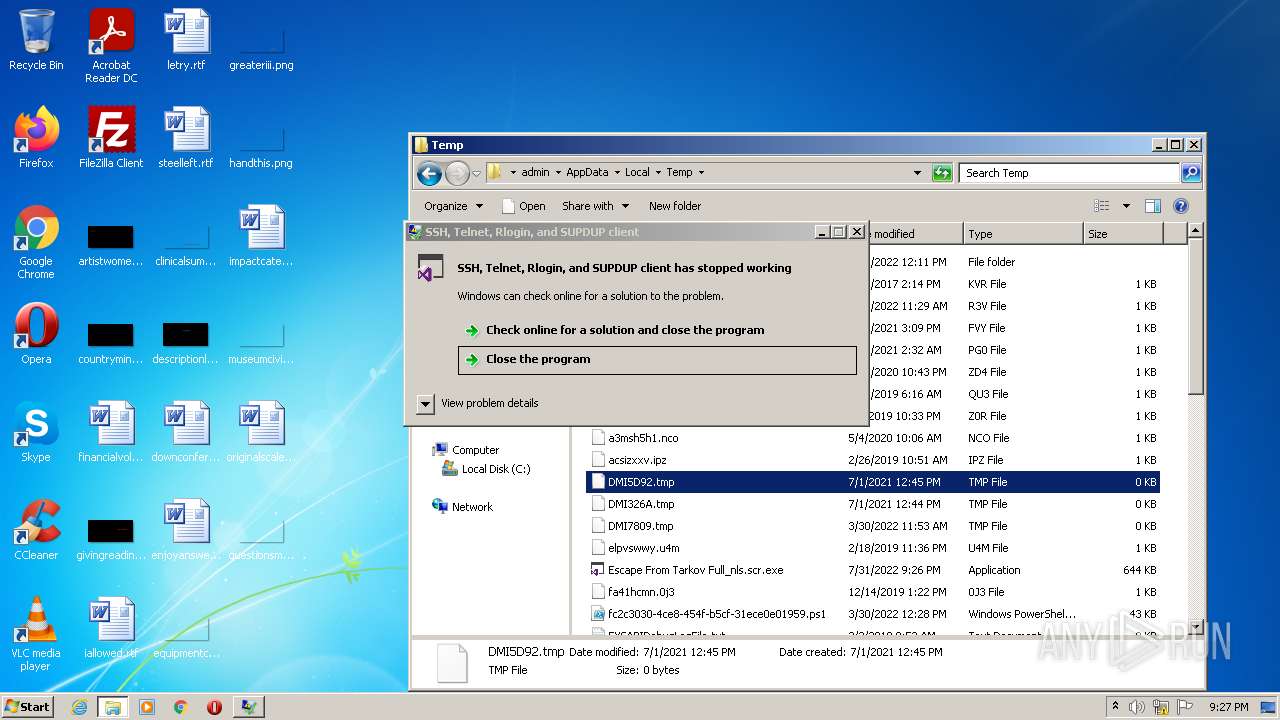
| 1604 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\clinicalsummary.png.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1604 | powershell.exe | C:\Users\admin\Desktop\clinicalsummary.png | image | |
MD5:— | SHA256:— | |||
| 1604 | powershell.exe | C:\Users\admin\Desktop\descriptionl.jpg | image | |
MD5:— | SHA256:— | |||
| 1604 | powershell.exe | C:\Users\admin\Desktop\downconference.rtf | text | |
MD5:— | SHA256:— | |||
| 1604 | powershell.exe | C:\Users\admin\Desktop\greateriii.png | image | |
MD5:— | SHA256:— | |||
| 1604 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\descriptionl.jpg.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1604 | powershell.exe | C:\Users\admin\Desktop\questionsmen.png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report